| File name: | cn1.exe |
| Full analysis: | https://app.any.run/tasks/528d9a87-d5bf-469d-aac0-e57cdb166645 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 20:07:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EAC4C88987A1050D16532161873DA362 |
| SHA1: | 78EEA8B88B639B766BC0D8959B737C898B57C612 |
| SHA256: | 35F8DD9CE038BC1EF09E71F7F3CA48E436323B171AC614287379274F141D5E15 |
| SSDEEP: | 12288:5aWkTV2UPTgypfTp37tKK55kXej6jiJfv/bwEhx9myvxRZCIeXG3a1McbU79u:5aXZ2UbpFhBzkXI8iFvhhxccbZxPmH |
MALICIOUS
Loads dropped or rewritten executable
- cn1.exe (PID: 1544)
Drops executable file immediately after starts
- cn1.exe (PID: 1544)
SUSPICIOUS
Reads the computer name
- cn1.exe (PID: 1544)
Checks supported languages
- cn1.exe (PID: 1544)
Drops a file with too old compile date
- cn1.exe (PID: 1544)
Executable content was dropped or overwritten
- cn1.exe (PID: 1544)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE Yoda's Crypter (63.7) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.7) |
| .exe | | | Win32 Executable (generic) (10.8) |
| .exe | | | Generic Win/DOS Executable (4.8) |
| .exe | | | DOS Executable Generic (4.8) |
EXIF
EXE
| LegalCopyright: | www.ccho.cc |
|---|---|
| FileVersion: | 8.63.2021.0928 |
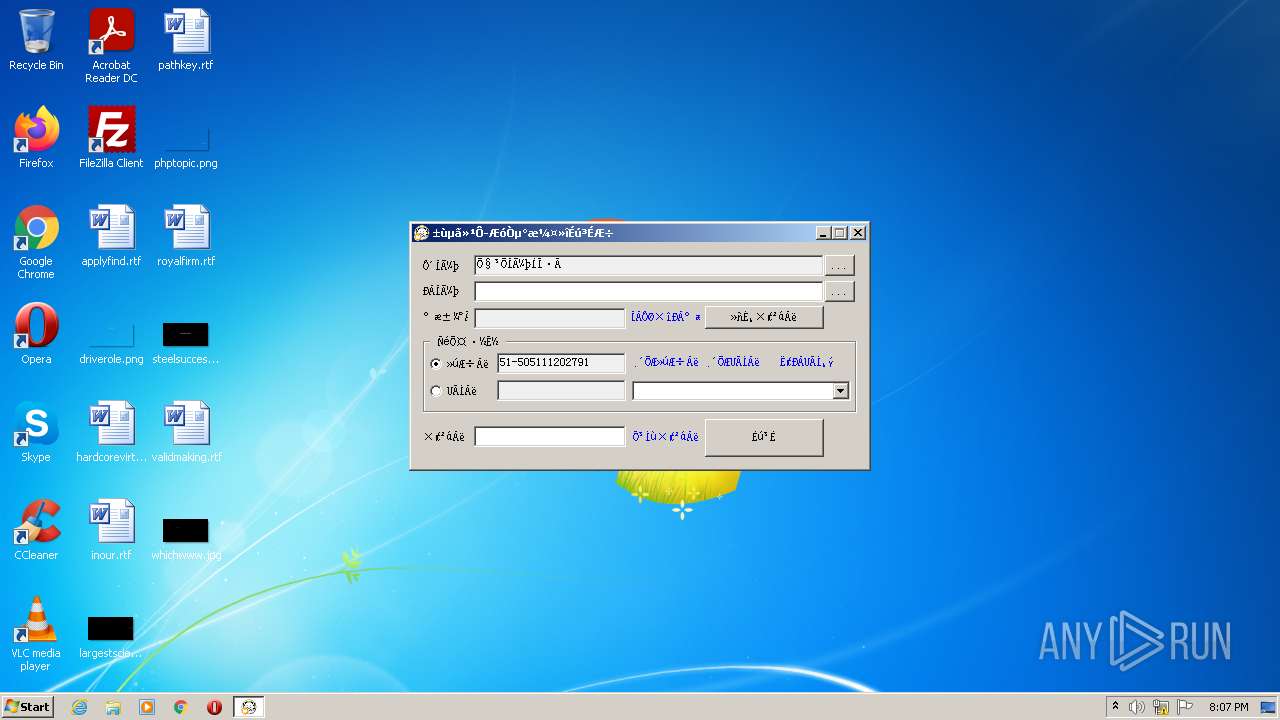
| FileDescription: | 冰点还原企业版激活生成器 |
| CompanyName: | www.ccho.cc |
| CharacterSet: | Windows, Chinese (Simplified) |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 8.63.2021.928 |
| FileVersionNumber: | 8.63.2021.928 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0xdab80 |
| UninitializedDataSize: | 872448 |
| InitializedDataSize: | 16384 |
| CodeSize: | 20480 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| TimeStamp: | 2015:01:02 04:45:54+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Jan-2015 03:45:54 |
| Detected languages: |
|
| CompanyName: | www.ccho.cc |
| FileDescription: | 冰点还原企业版激活生成器 |
| FileVersion: | 8.63.2021.0928 |
| LegalCopyright: | www.ccho.cc |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 02-Jan-2015 03:45:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
VMP0 | 0x00001000 | 0x000D5000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
VMP1 | 0x000D6000 | 0x00005000 | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.85189 |
.rsrc | 0x000DB000 | 0x00004000 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.93417 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.239 | 973 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 7.77733 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 7.76003 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 7.67498 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 7.60531 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 7.18688 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 3.03393 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 7.11432 | 300 | UNKNOWN | English - United States | RT_DIALOG |
106 | 6.96413 | 228 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1544 | "C:\Users\admin\AppData\Local\Temp\cn1.exe" | C:\Users\admin\AppData\Local\Temp\cn1.exe | Explorer.EXE | ||||||||||||
User: admin Company: www.ccho.cc Integrity Level: HIGH Description: ???????????? Exit code: 0 Version: 8.63.2021.0928 Modules
| |||||||||||||||
| 3004 | "C:\Users\admin\AppData\Local\Temp\cn1.exe" | C:\Users\admin\AppData\Local\Temp\cn1.exe | — | Explorer.EXE | |||||||||||
User: admin Company: www.ccho.cc Integrity Level: MEDIUM Description: ???????????? Exit code: 3221226540 Version: 8.63.2021.0928 Modules
| |||||||||||||||
Total events
693
Read events
693
Write events
0
Delete events
0
Modification events
Executable files
5
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1544 | cn1.exe | C:\Users\admin\AppData\Local\Temp\nsiE9AA.tmp\Crypto.dll | executable | |
MD5:5FC727C579F3C3B69CE0EB7F2EC7D48A | SHA256:B7B819DCF3AAED2774CECFA507F9BAEE47660B18758F7CB718BB5CB2D77947FA | |||
| 1544 | cn1.exe | C:\Users\admin\AppData\Local\Temp\nsiE9AA.tmp\smbios.dll | executable | |
MD5:16AA39ACC65DB6FE50D3CFD622BD6D3C | SHA256:4C3C932EF0EE4C18817A05634D4F2E84DC4B5A58C4EB61212EC0D20CCA2C2ACA | |||
| 1544 | cn1.exe | C:\Users\admin\AppData\Local\Temp\nsiE9AA.tmp\nsDialogs.dll | executable | |
MD5:AB73C0C2A23F913EABDC4CB24B75CBAD | SHA256:3D0060C5C9400A487DBEFE4AC132DD96B07D3A4BA3BADAB46A7410A667C93457 | |||
| 1544 | cn1.exe | C:\Users\admin\AppData\Local\Temp\nsiE9AA.tmp\HandleFileDragDrop.dll | executable | |
MD5:BFAD1BC3CEA7770A5D8FCE27E40D903C | SHA256:3517CD1B082A9C0A697304FB0B8CEA15AFBF36205563A2C03FED801589EC3A3B | |||
| 1544 | cn1.exe | C:\Users\admin\AppData\Local\Temp\nsiE9AA.tmp\System.dll | executable | |
MD5:B0C77267F13B2F87C084FD86EF51CCFC | SHA256:A0CAC4CF4852895619BC7743EBEB89F9E4927CCDB9E66B1BCD92A4136D0F9C77 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report