| File name: | Bandicam+Keygen.exe |
| Full analysis: | https://app.any.run/tasks/2af709e8-d4a4-4bc3-a973-3a050d4e6b5e |
| Verdict: | No threats detected |
| Analysis date: | February 24, 2019, 21:33:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E3B79A6E351FD452370B429D683F4921 |
| SHA1: | DFFC6C3E23B717F979C364C09BEFAABE77AB1C08 |
| SHA256: | 35F033E1268261DF19A9B08B6FB9E458F1D6EEA5C76F9A4C86D596457E3A13C6 |
| SSDEEP: | 6144:4SjV/iJ1oxh4+pu2C52ohE0iLcTsJfTBsu49Z5l7br6SUZrGCG5D:44dg1oxh4au2ShE0iNJfTv05l7nQZ6CC |
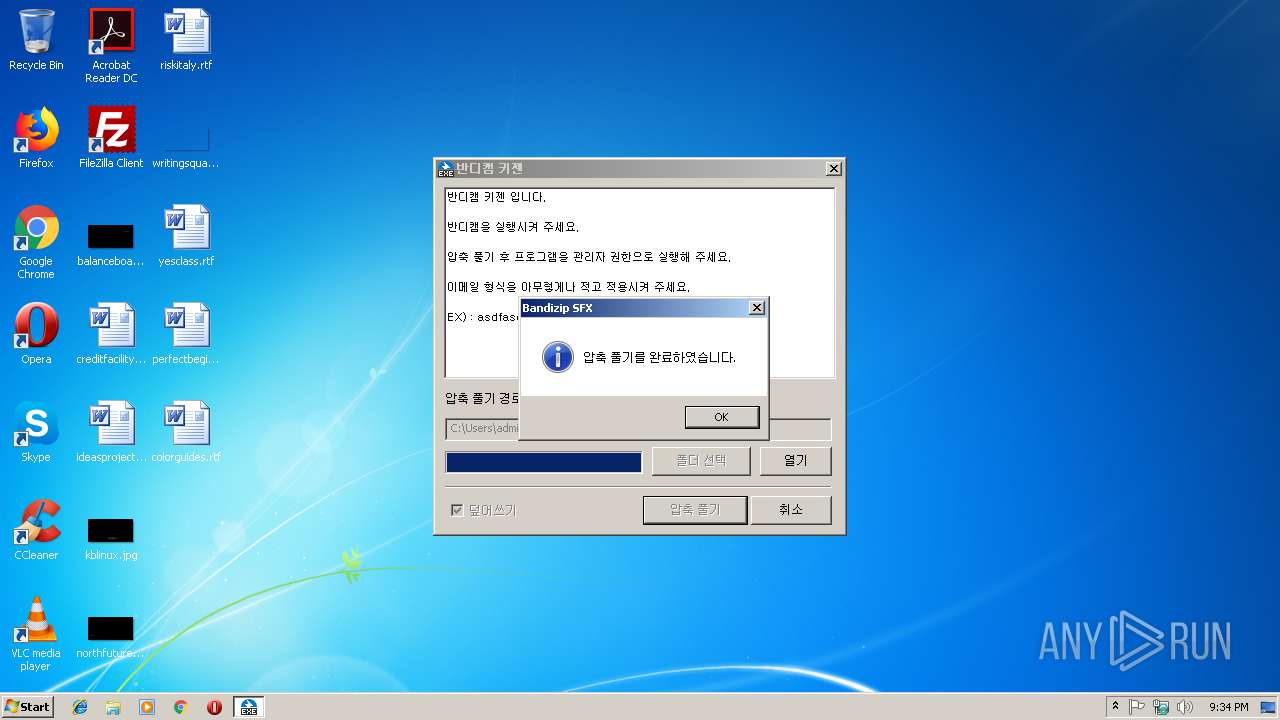
MALICIOUS
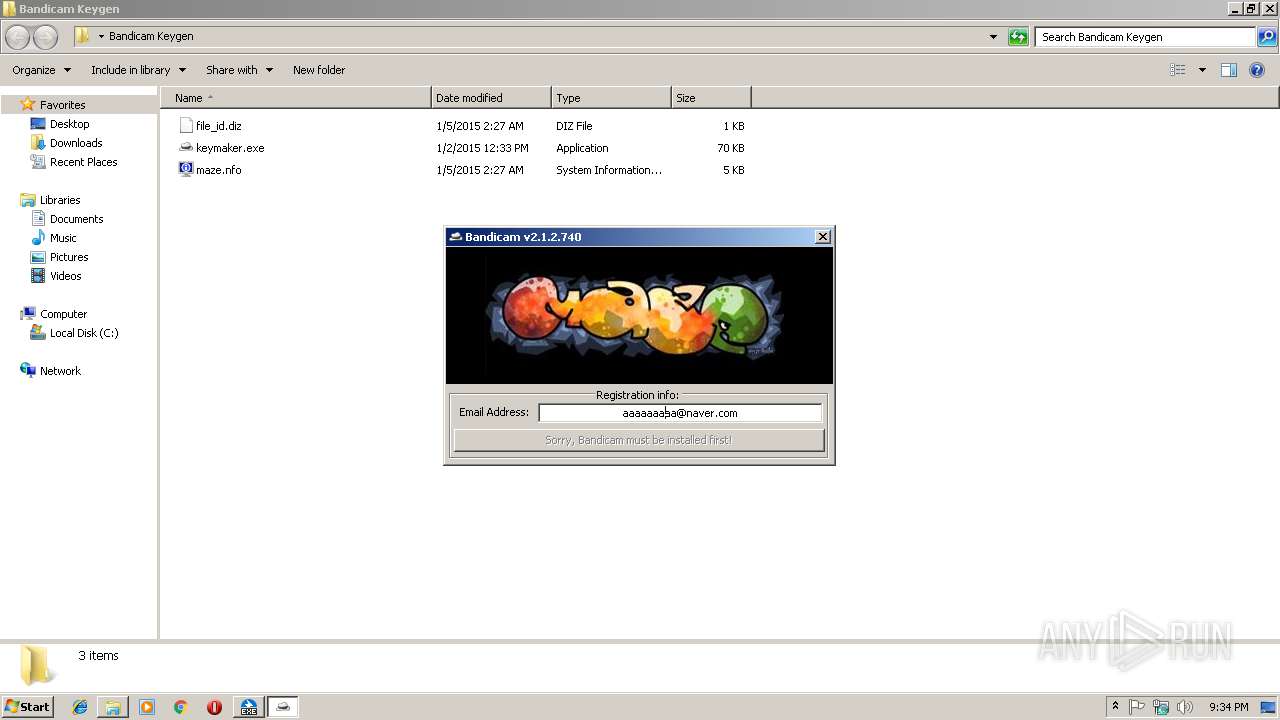
Application was dropped or rewritten from another process
- keymaker.exe (PID: 3120)
SUSPICIOUS
Executable content was dropped or overwritten
- Bandicam+Keygen.exe (PID: 3640)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:18 11:03:01+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 205312 |
| InitializedDataSize: | 116736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x22203 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Oct-2018 09:03:01 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Oct-2018 09:03:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000320C9 | 0x00032200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.72614 |
.rdata | 0x00034000 | 0x0000C446 | 0x0000C600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.75484 |
.data | 0x00041000 | 0x0000FDFC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04516 |
.rsrc | 0x00051000 | 0x00009464 | 0x00009600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.65972 |
.reloc | 0x0005B000 | 0x00004BBE | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.81545 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.37872 | 1358 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.29784 | 1128 | Latin 1 / Western European | Korean - Korea | RT_ICON |
3 | 3.74585 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.34586 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.37439 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 7.89047 | 9675 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 1.7274 | 56 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.31752 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.29784 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
107 | 2.70819 | 104 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
32
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
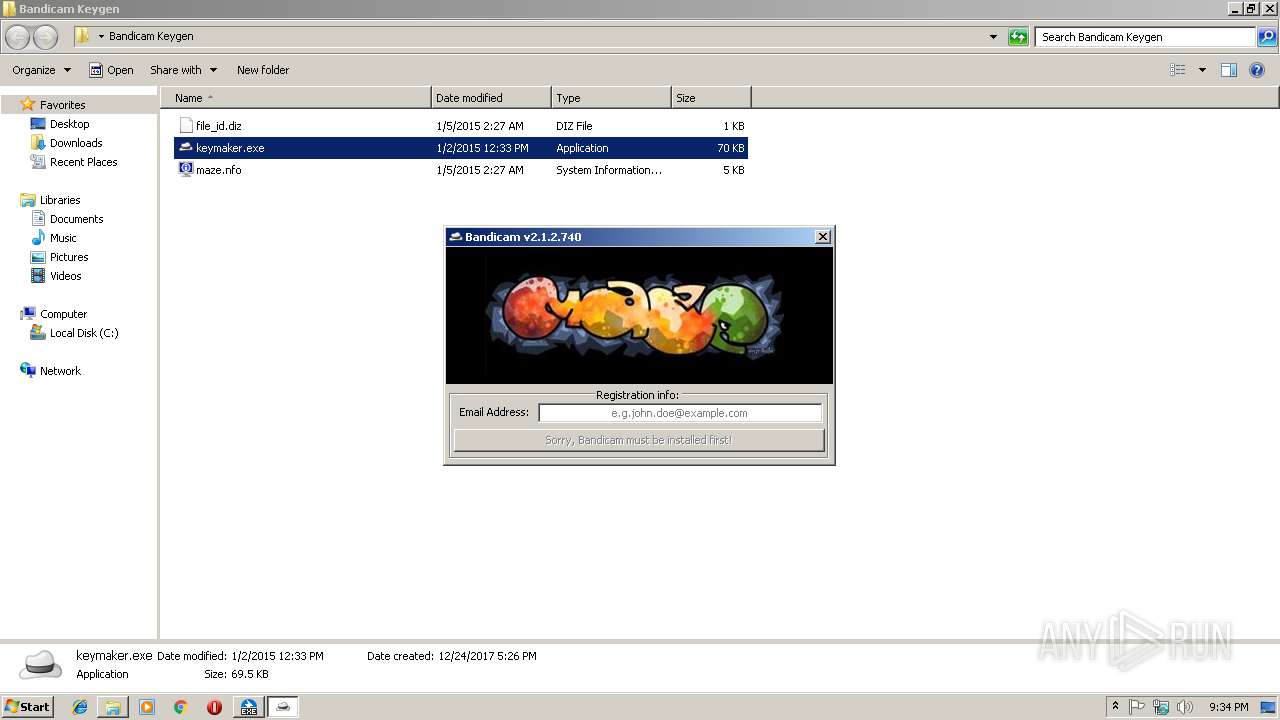
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
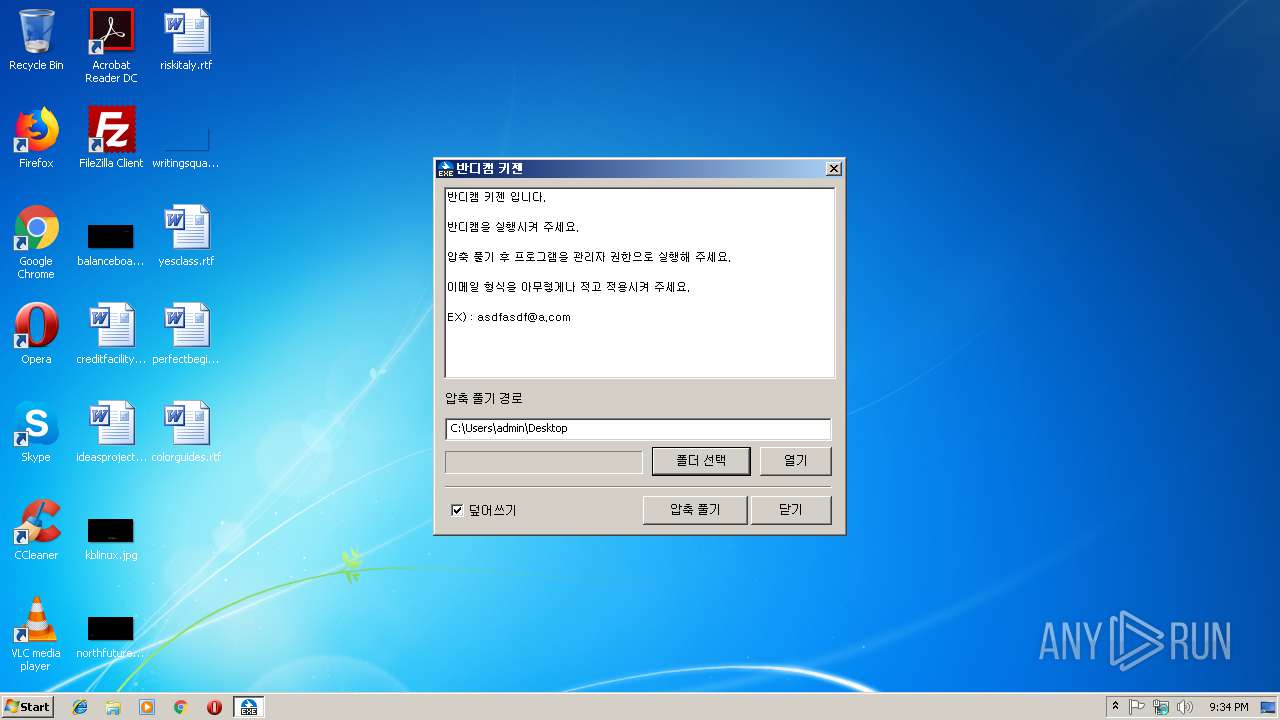
| 3120 | "C:\Users\admin\Desktop\Bandicam Keygen\keymaker.exe" | C:\Users\admin\Desktop\Bandicam Keygen\keymaker.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3640 | "C:\Users\admin\AppData\Local\Temp\Bandicam+Keygen.exe" | C:\Users\admin\AppData\Local\Temp\Bandicam+Keygen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
451
Read events
440
Write events
11
Delete events
0
Modification events
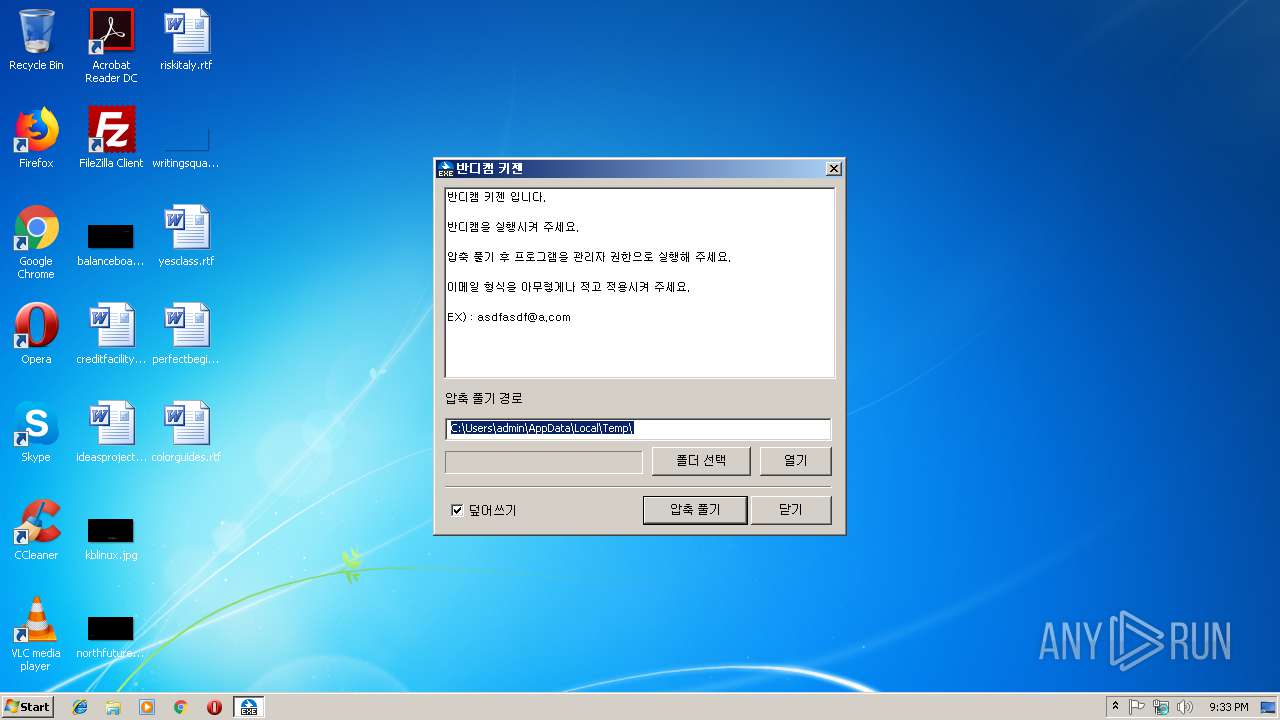
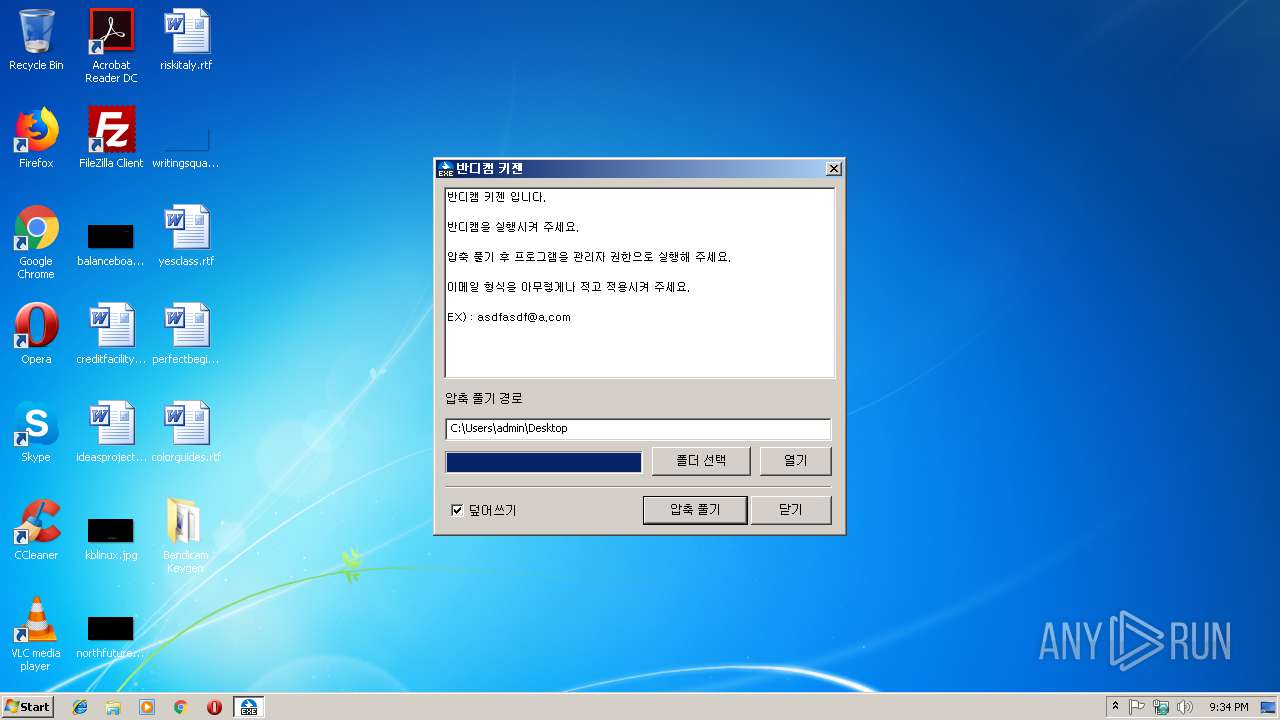
| (PID) Process: | (3640) Bandicam+Keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
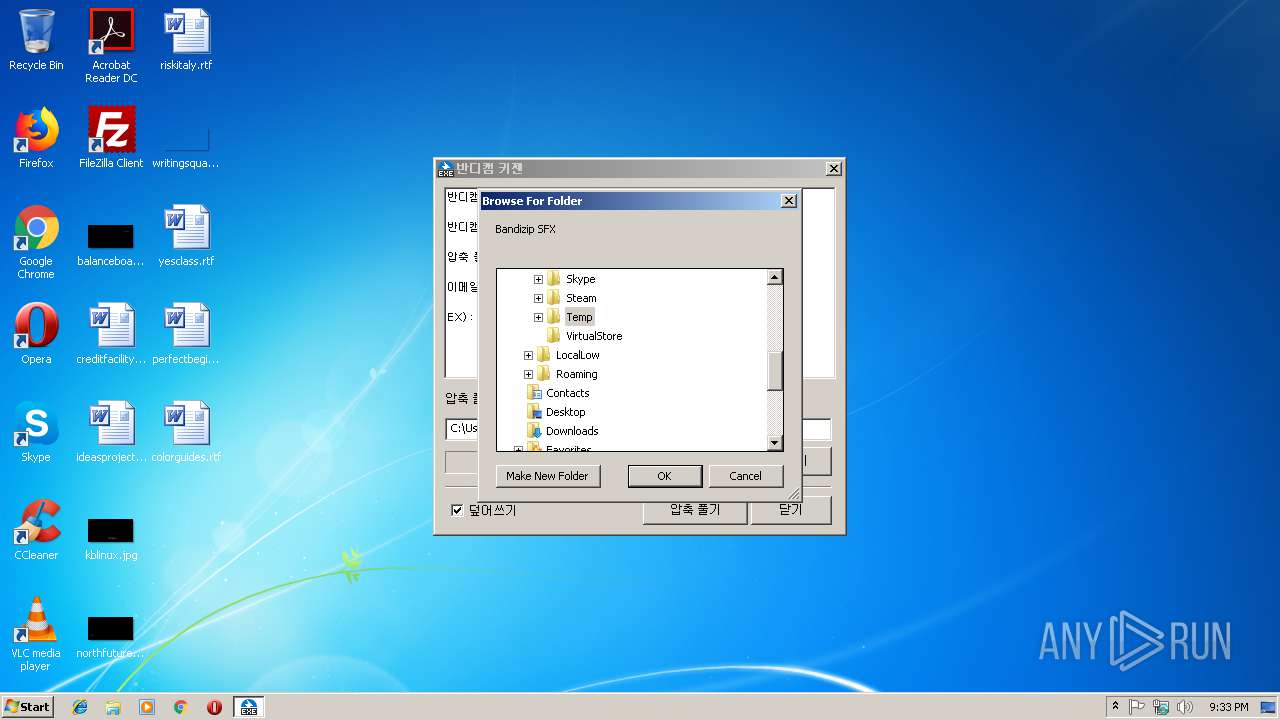
| (PID) Process: | (3640) Bandicam+Keygen.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (3640) Bandicam+Keygen.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
0
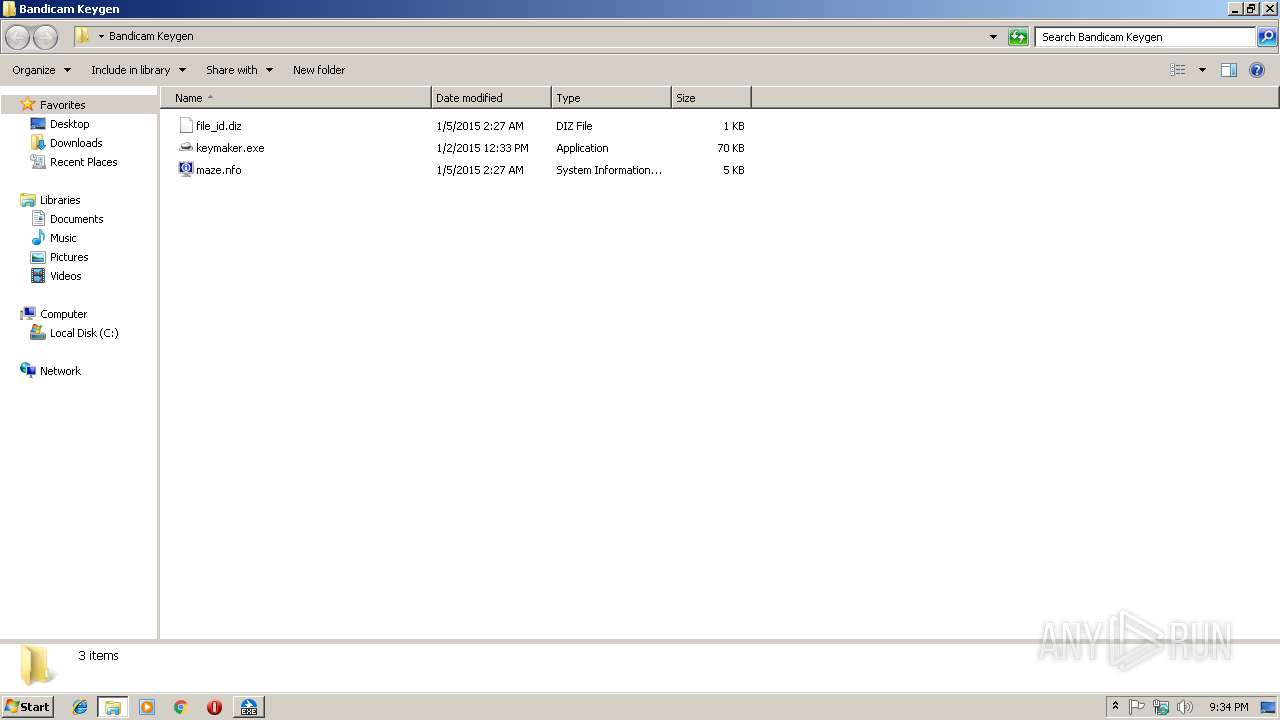
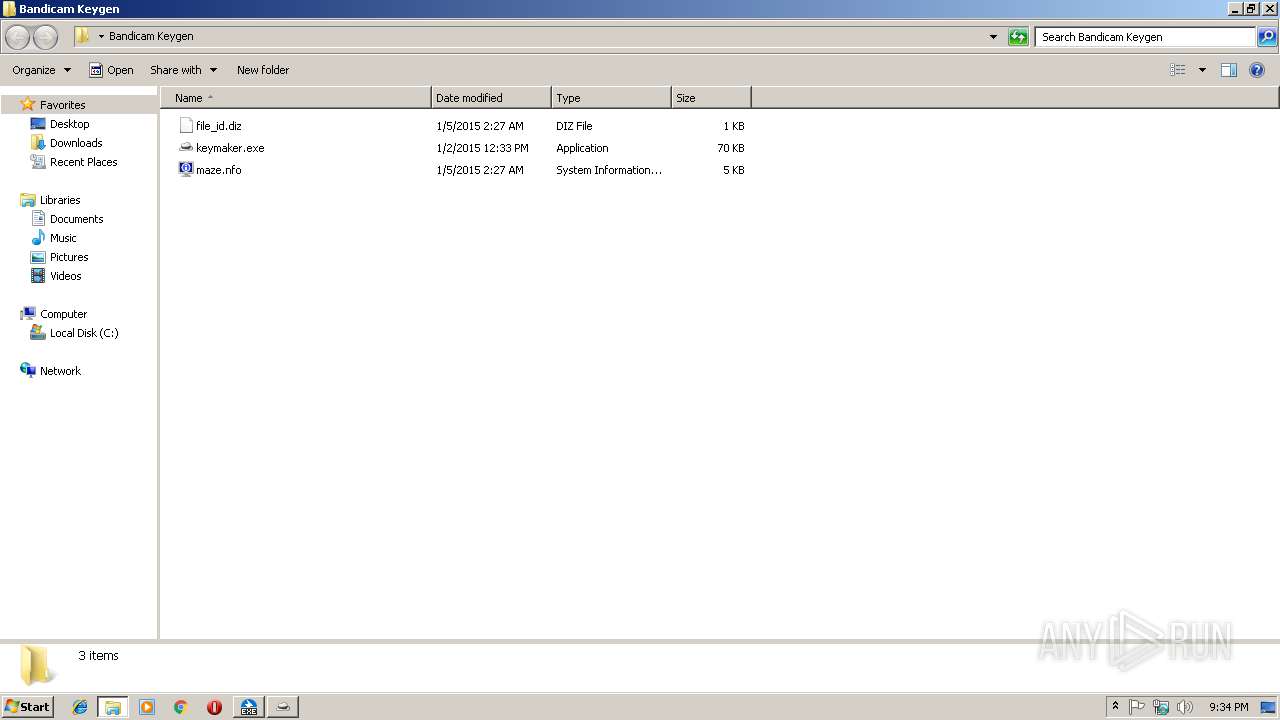
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3640 | Bandicam+Keygen.exe | C:\Users\admin\Desktop\Bandicam Keygen\maze.nfo | text | |
MD5:43509A7A37DF409116DF6CD4828F72EE | SHA256:B71ADCE58D3491720E8F23A9C48F8993D3FC62481FB677EB0A10096B68D46AE2 | |||
| 3640 | Bandicam+Keygen.exe | C:\Users\admin\Desktop\Bandicam Keygen\keymaker.exe | executable | |
MD5:E2B75C862BB136D9A9168929A6C9A00A | SHA256:E1D78799D1CD43DC5A9C3C7306439B04D6C5AC99FA9ADC3FD1FD5032676E1077 | |||
| 3640 | Bandicam+Keygen.exe | C:\Users\admin\Desktop\Bandicam Keygen\file_id.diz | text | |
MD5:0809986FC2B6CFC056C05213F4A7C5B2 | SHA256:FCD905693932C2F2833C0F2757CC8CBE09DB159F9B62FC1AB5E9D3CB32AAB245 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report