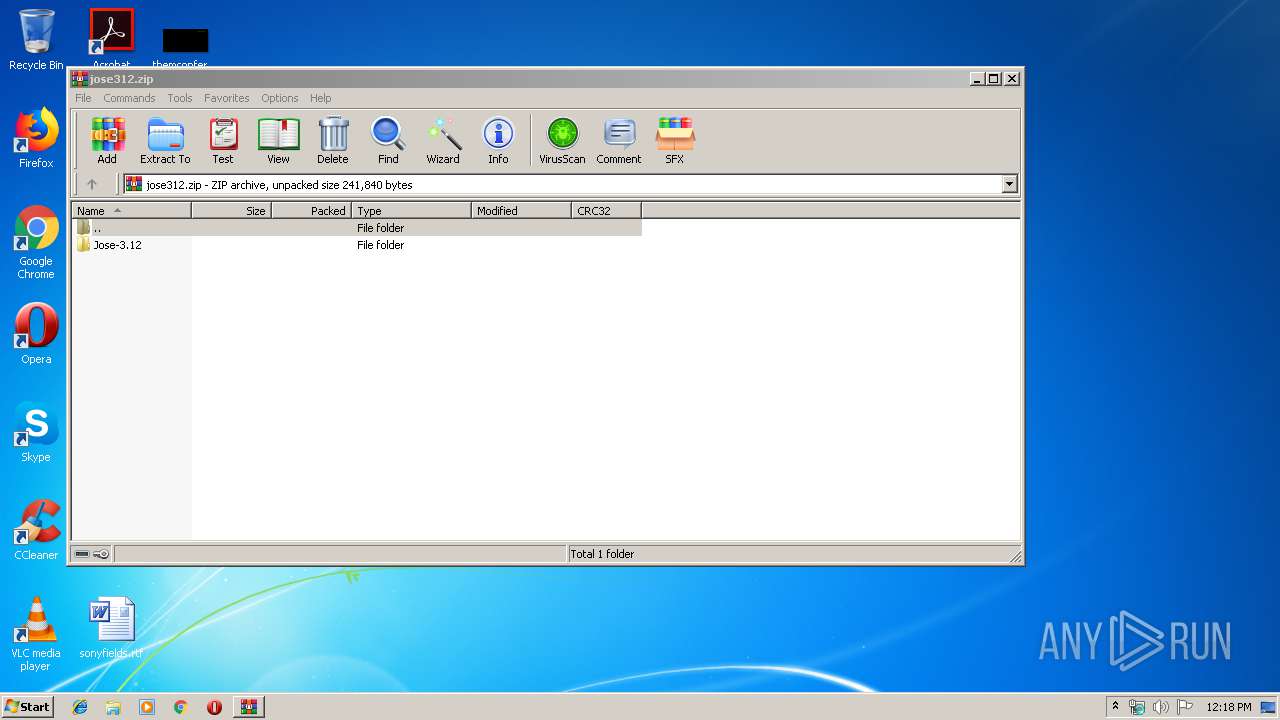
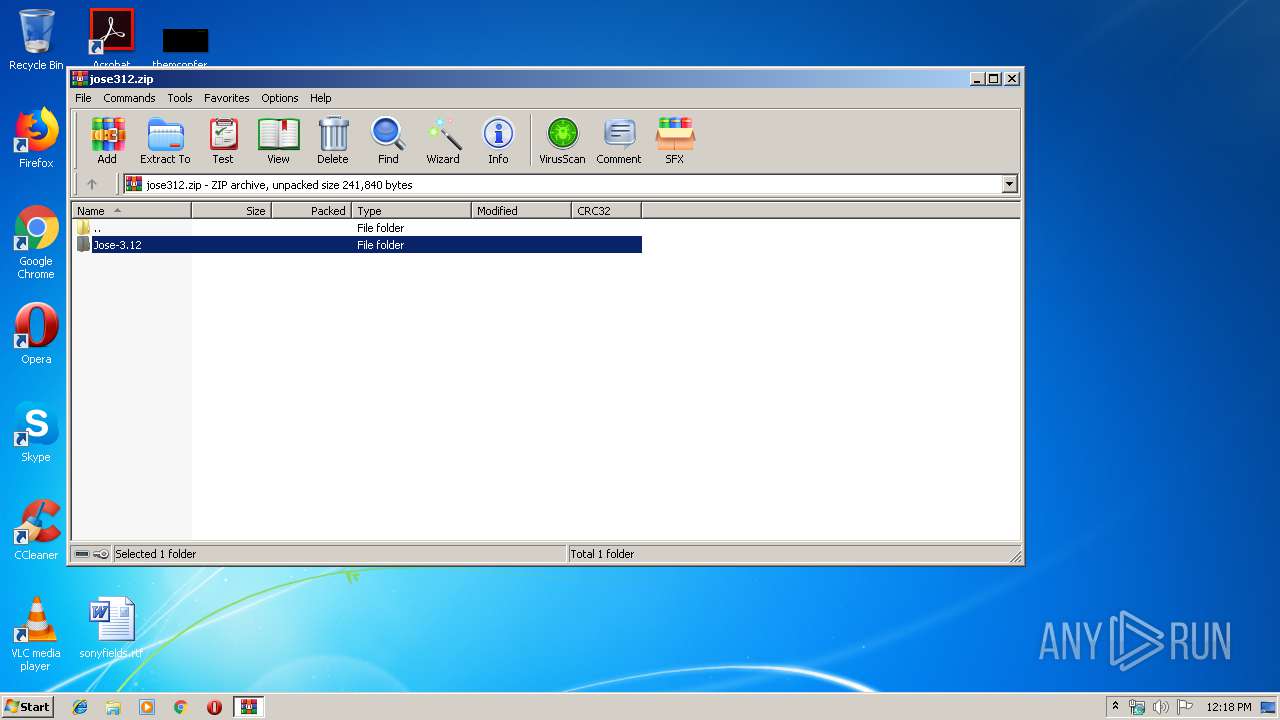
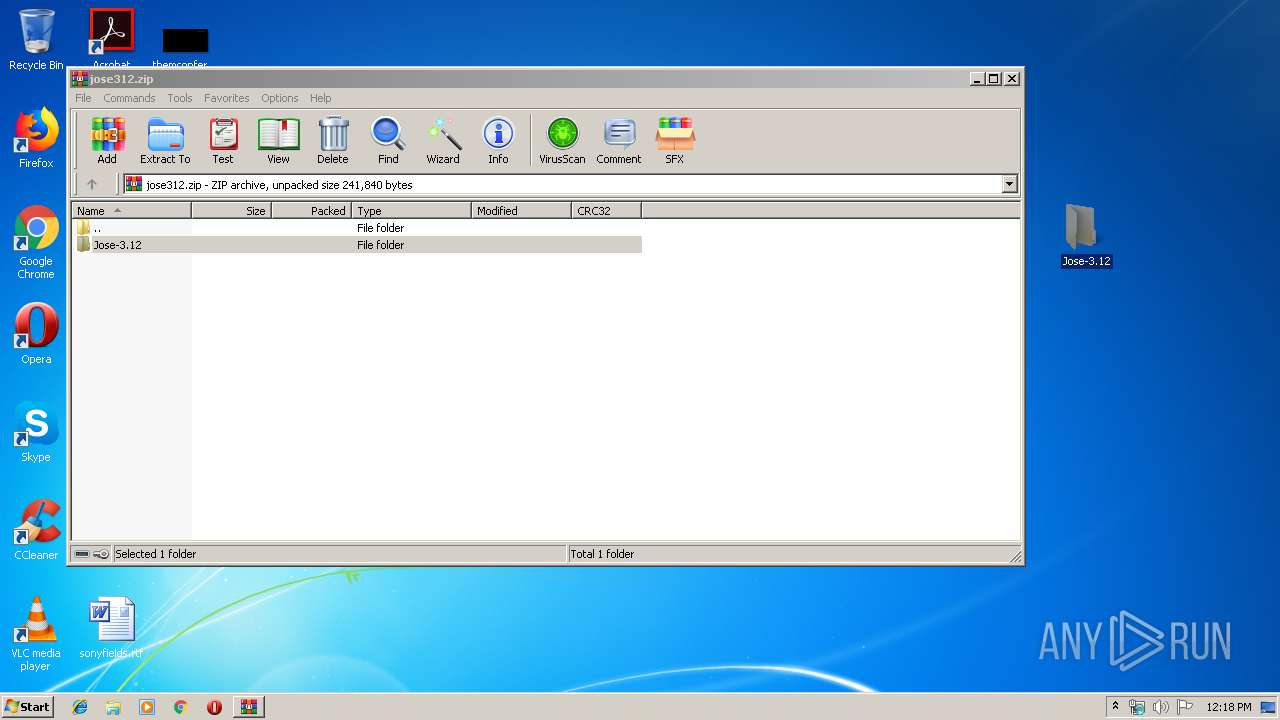
| File name: | jose312.zip |
| Full analysis: | https://app.any.run/tasks/d935b0ae-f5c2-42a5-81f7-92f5c3227046 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 11:17:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B04038CD43879E90A589CD8109964EEA |
| SHA1: | DC051F85F8C82614A0DA443B398778489233E654 |
| SHA256: | 35EDDFDBE72F2FFDC15AEAE4E7CA44F677141AD47E97156D42C4734351D878C3 |
| SSDEEP: | 1536:kdal8vhSckFbP4A6W2C05lA/S4nWAvyHQ+5gg5Y2IiNNZa/FkgB:k4l8V8J275y/hnWEywEK2IcZa/FFB |
MALICIOUS
No malicious indicators.SUSPICIOUS
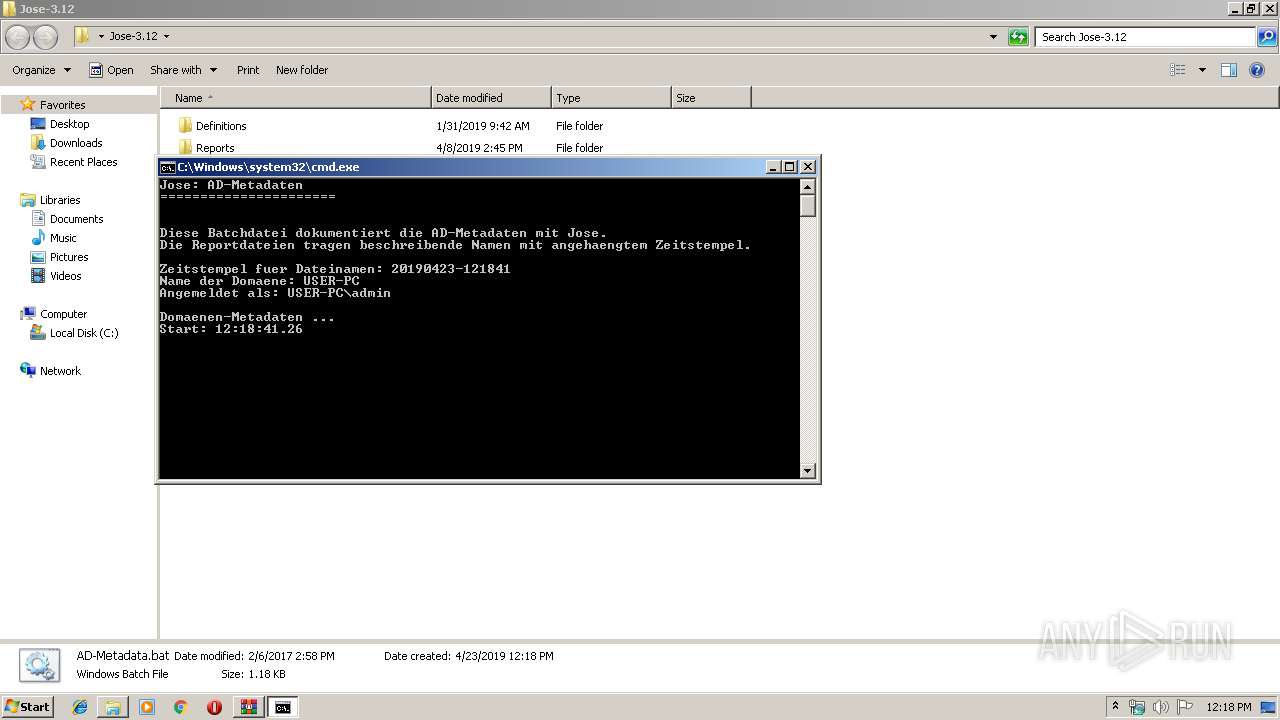
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2720)
- WinRAR.exe (PID: 2852)
- cmd.exe (PID: 3608)
Executes scripts
- cmd.exe (PID: 3608)
- cmd.exe (PID: 2272)
- cmd.exe (PID: 3472)
- cmd.exe (PID: 2720)
Application launched itself
- cmd.exe (PID: 2720)
Uses WHOAMI.EXE to obtaining logged on user information
- cmd.exe (PID: 2780)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2017:02:06 14:58:27 |
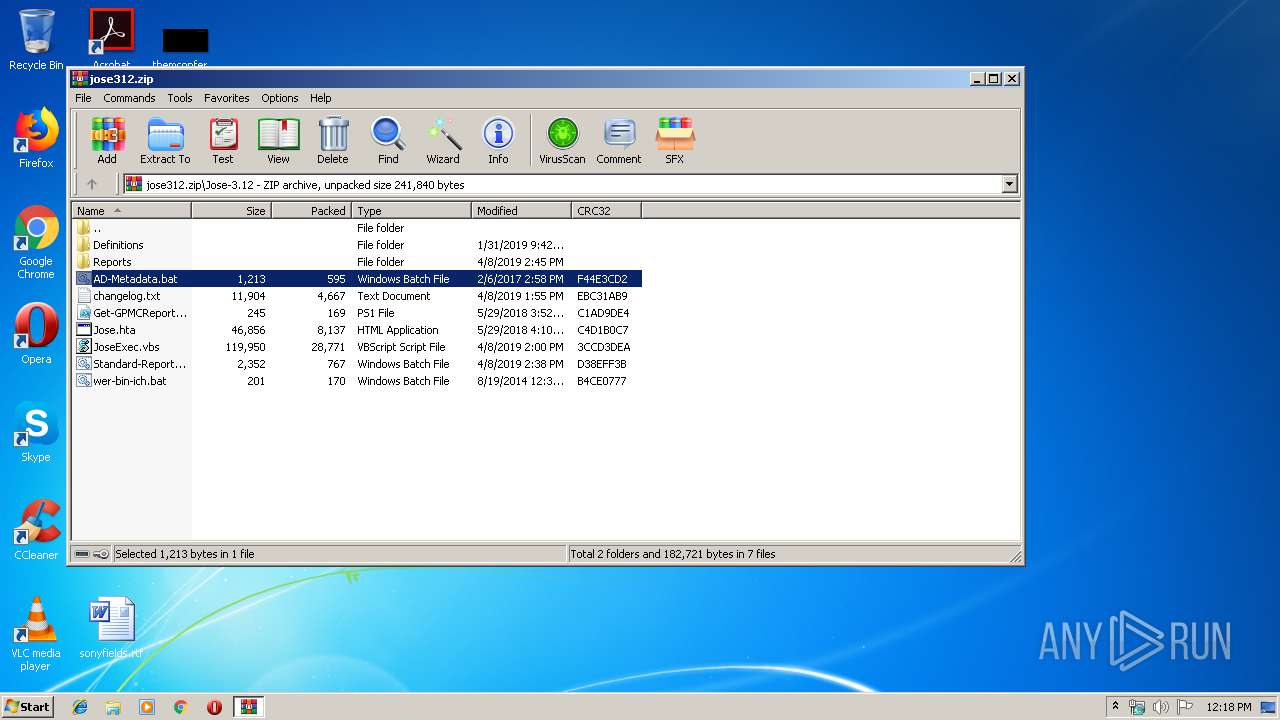
| ZipCRC: | 0xf44e3cd2 |
| ZipCompressedSize: | 595 |
| ZipUncompressedSize: | 1213 |
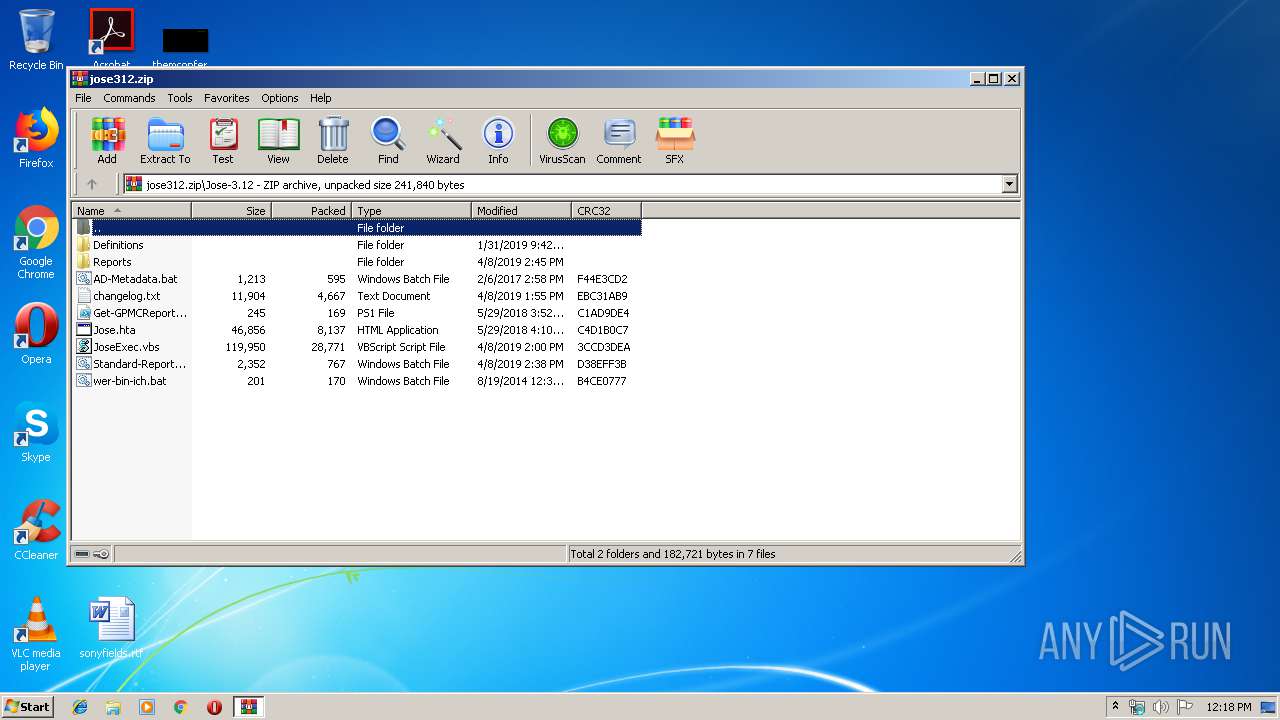
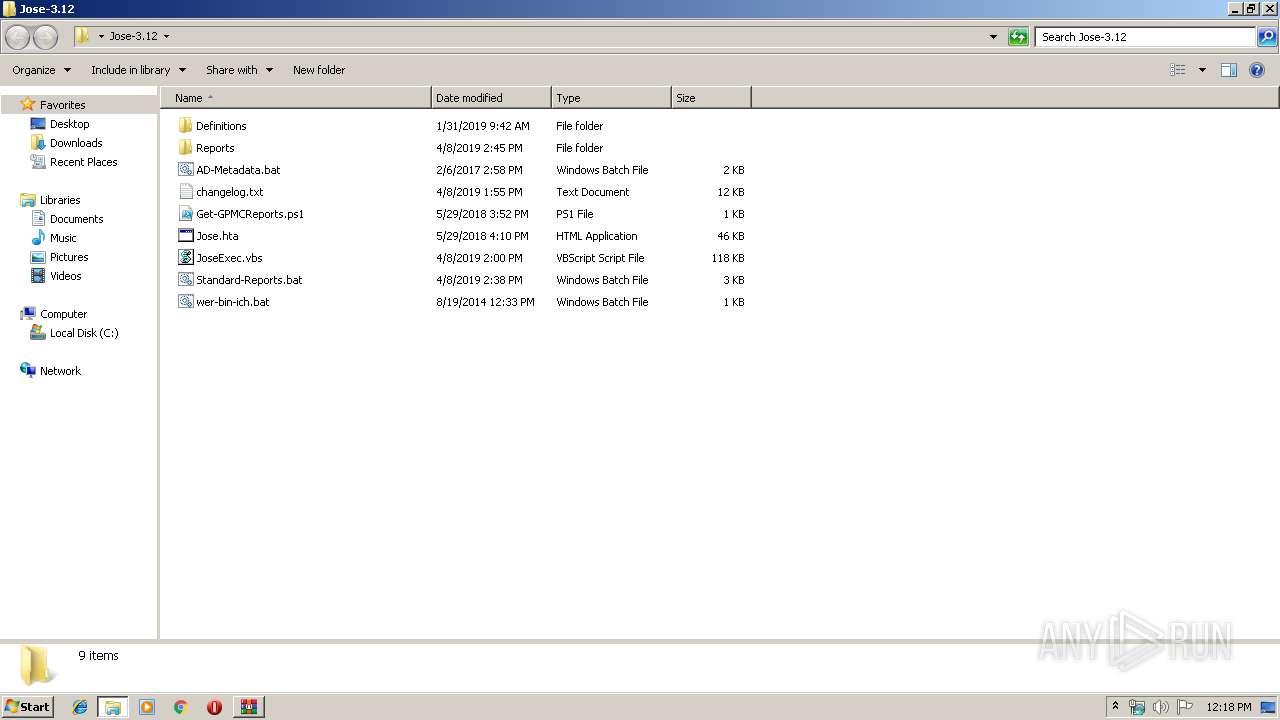
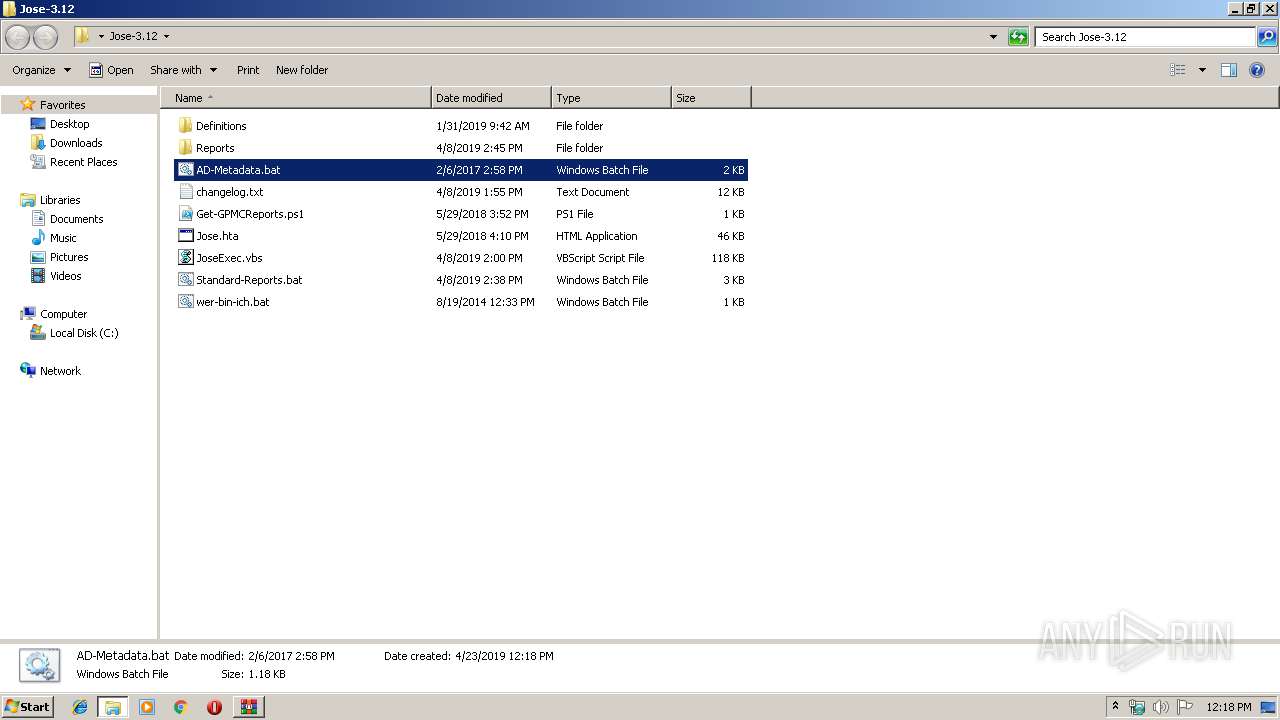
| ZipFileName: | Jose-3.12/AD-Metadata.bat |
Total processes
44
Monitored processes
11
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1868 | WHOAMI /GROUPS /FO CSV /NH | C:\Windows\system32\whoami.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | C:\Windows\system32\cmd.exe /c @CSCRIPT //NOLOGO 85Temp.vbs | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2488 | CSCRIPT //NOLOGO 85Temp.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2720 | cmd /c ""C:\Users\admin\Desktop\Jose-3.12\AD-Metadata.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2780 | C:\Windows\system32\cmd.exe /c WHOAMI /GROUPS /FO CSV /NH | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2852 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\jose312.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2864 | cscript //nologo //u JoseExec.vbs /d:!Domaene-Metadaten.txt /r:Domaene-Metadaten_USER-PC_20190423-121841.htm | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3472 | C:\Windows\system32\cmd.exe /c @CSCRIPT //NOLOGO 144Temp.vbs | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3496 | cscript //nologo //u JoseExec.vbs /d:!Domaene-Metadaten.txt /r:Domaene-Metadaten_USER-PC_20190423-121822.htm | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3608 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa2852.30387\AD-Metadata.bat" " | C:\Windows\system32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
508
Read events
488
Write events
20
Delete events
0
Modification events
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\jose312.zip | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (2852) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
0
Suspicious files
0
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2852.31791\Jose-3.12\Definitions\!User-Computer-Gruppen-Zusatzfelder.txt | — | |
MD5:— | SHA256:— | |||
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2852.31791\Jose-3.12\Definitions\Create-DynamicReportsBuiltinUsers.bat | — | |
MD5:— | SHA256:— | |||
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2852.31791\Jose-3.12\Get-GPMCReports.ps1 | — | |
MD5:— | SHA256:— | |||
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2852.31791\Jose-3.12\Jose.hta | — | |
MD5:— | SHA256:— | |||
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2852.31791\Jose-3.12\JoseExec.vbs | — | |
MD5:— | SHA256:— | |||
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2852.31791\Jose-3.12\Reports\Dateien\anzahl.gif | — | |
MD5:— | SHA256:— | |||
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2852.31791\Jose-3.12\Reports\Dateien\blocked.gif | — | |
MD5:— | SHA256:— | |||
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2852.31791\Jose-3.12\Reports\Dateien\computer.gif | — | |
MD5:— | SHA256:— | |||
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2852.31791\Jose-3.12\Reports\Dateien\contact.gif | — | |
MD5:— | SHA256:— | |||
| 2852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2852.31791\Jose-3.12\Reports\Dateien\datum.gif | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report