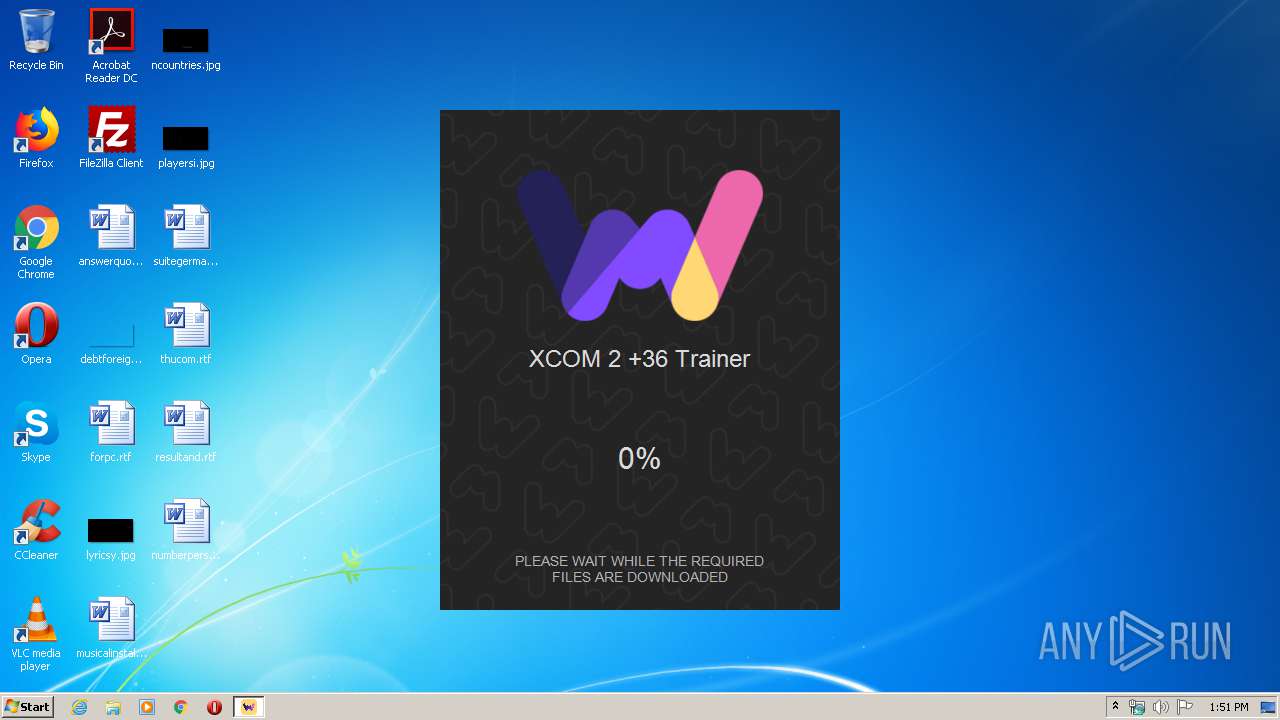
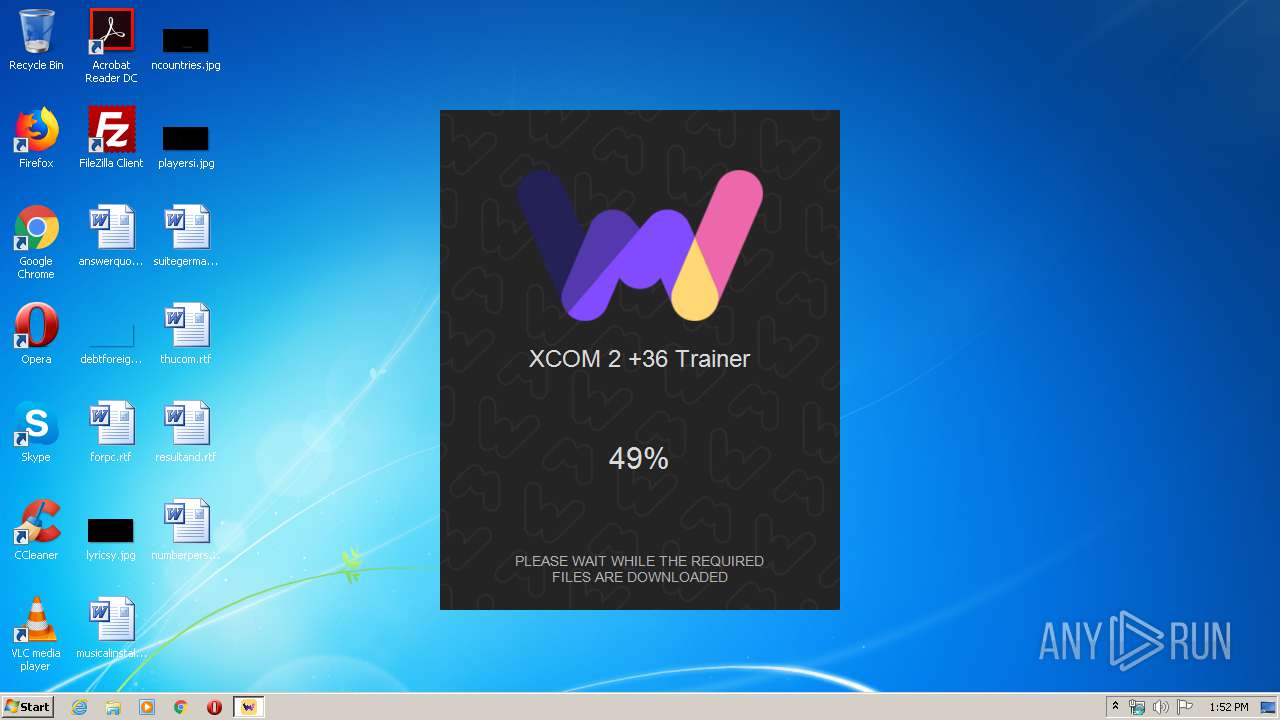
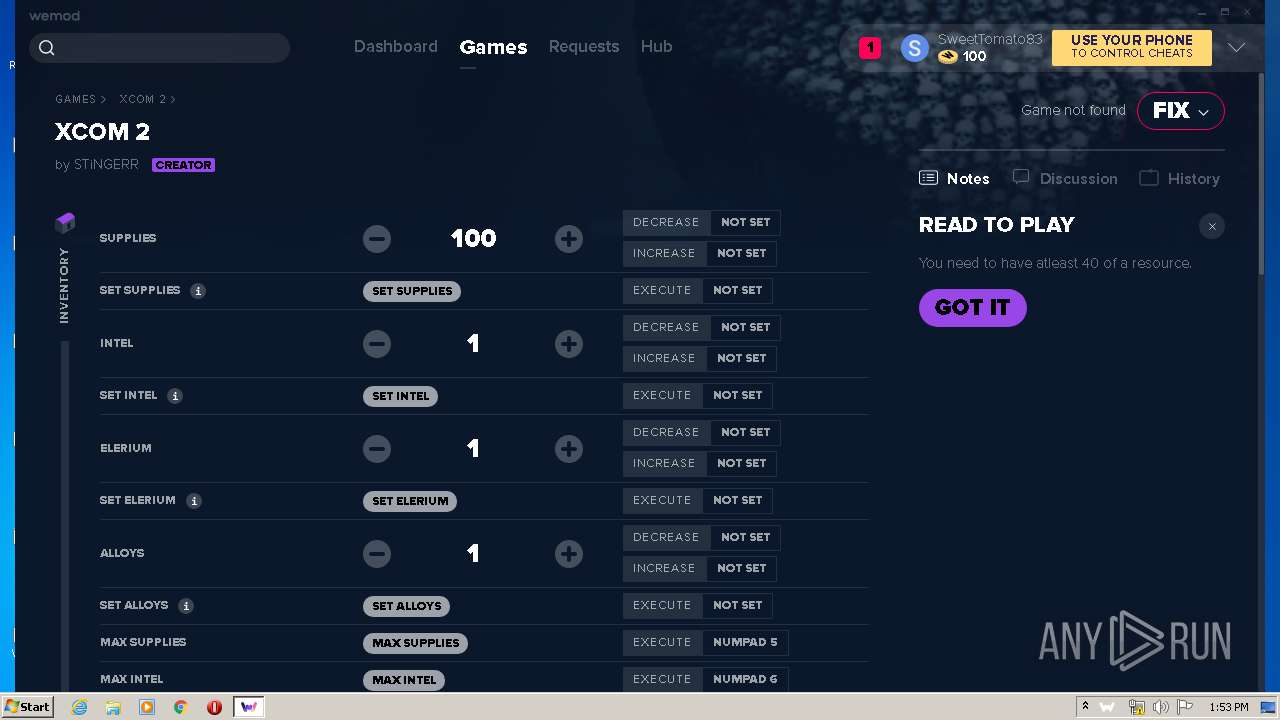
| File name: | XCOM 2 Trainer.exe |
| Full analysis: | https://app.any.run/tasks/1e05c912-4f1c-4dea-bddd-88e00570de40 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 13:51:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 20033F9900C8440AB486F5A144491CB9 |
| SHA1: | FA164CCBD5DD611011BD9489D2D76A4AFF6D6129 |
| SHA256: | 35DB327FBE2DA48745D1F2C0B2A4671C9E70DDF61BCFC797FA0BFA37DC506075 |
| SSDEEP: | 1536:uP3C75n6UGB8M/kLu9qtz5IsH6aEu4afE91rkc3/oclgRV905bPy+9G:8Sx6UG+Fu9qwIXfE/kc3/ov2e+9 |
MALICIOUS
Application was dropped or rewritten from another process
- Update.exe (PID: 2296)
- Squirrel.exe (PID: 3164)
- Update.exe (PID: 3188)
- Update.exe (PID: 2068)
- Update.exe (PID: 2412)
- WeModAuxiliaryService.exe (PID: 3316)
Loads dropped or rewritten executable
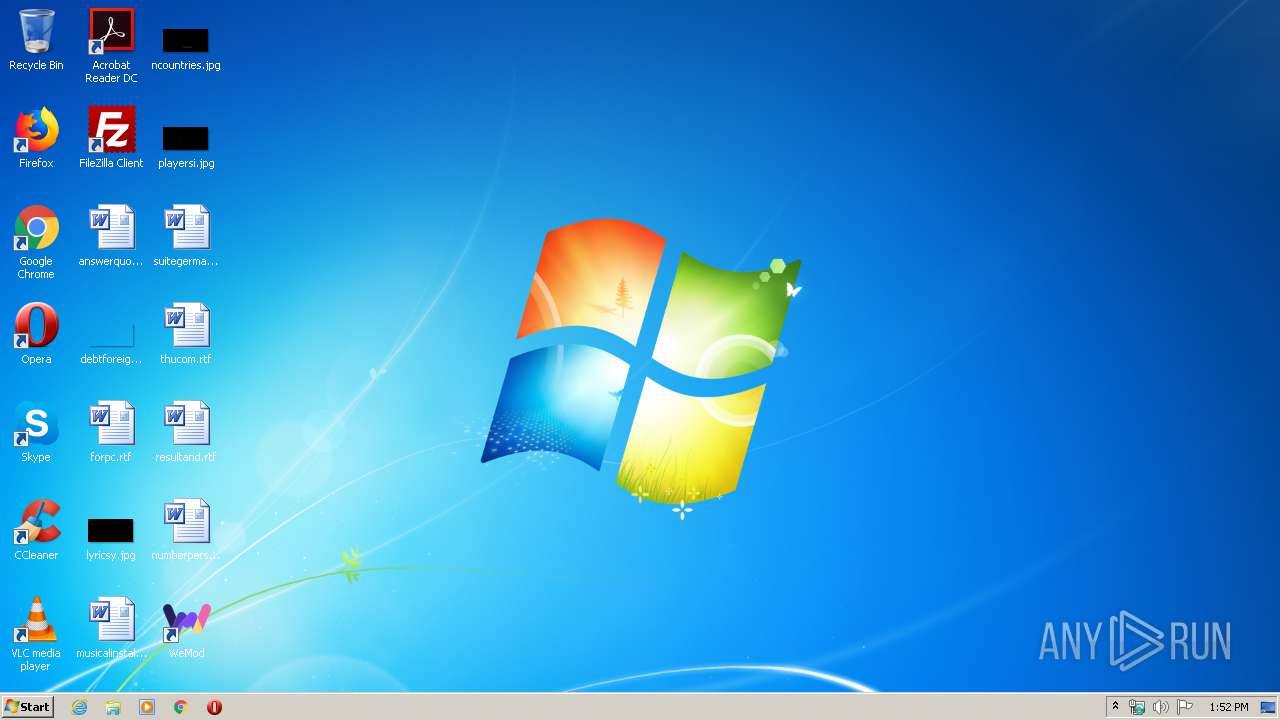
- WeMod.exe (PID: 2092)
- WeMod.exe (PID: 3228)
- WeMod.exe (PID: 2744)
- WeMod.exe (PID: 912)
- WeMod.exe (PID: 1872)
- WeMod.exe (PID: 3620)
- WeMod.exe (PID: 3732)
SUSPICIOUS
Reads Internet Cache Settings
- XCOM 2 Trainer.exe (PID: 3352)
Creates files in the user directory
- XCOM 2 Trainer.exe (PID: 3352)
- Update.exe (PID: 3188)
- WeMod.exe (PID: 2744)
- WeMod.exe (PID: 3732)
Executable content was dropped or overwritten
- Update.exe (PID: 2296)
- WeMod-6.2.17[1].exe (PID: 3868)
- Squirrel.exe (PID: 3164)
Reads Environment values
- Update.exe (PID: 2296)
- Update.exe (PID: 2412)
Application launched itself
- WeMod.exe (PID: 3228)
- WeMod.exe (PID: 2744)
Creates a software uninstall entry
- Update.exe (PID: 2296)
Uses WMIC.EXE to obtain a list of AntiViruses
- cmd.exe (PID: 3472)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 3472)
Modifies the open verb of a shell class
- WeMod.exe (PID: 2744)
Starts CMD.EXE for commands execution
- WeMod.exe (PID: 912)
INFO
Reads the hosts file
- WeMod.exe (PID: 3228)
- WeMod.exe (PID: 2744)
- WeMod.exe (PID: 3732)
Reads settings of System Certificates
- Update.exe (PID: 2412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:27 04:43:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.15 |
| CodeSize: | 53248 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | 77824 |
| EntryPoint: | 0x20950 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.0.0 |
| ProductVersionNumber: | 5.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Daring Development Inc. |
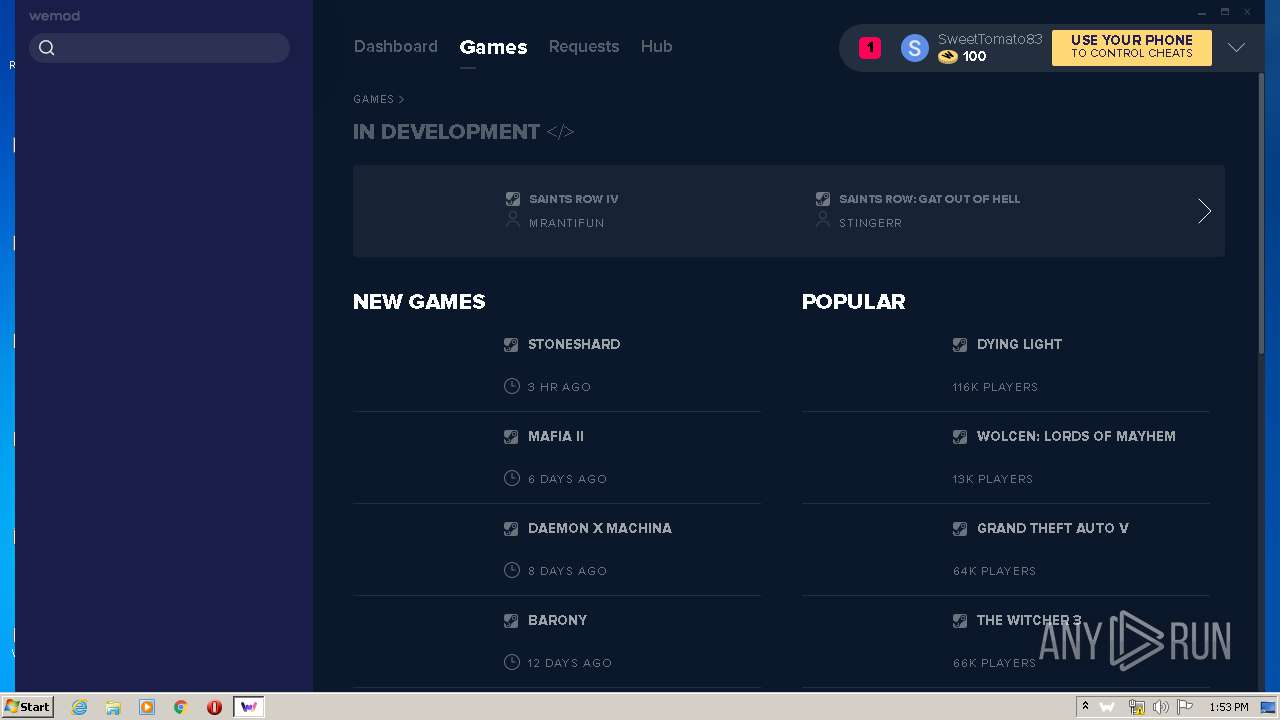
| FileDescription: | WeMod Setup |
| FileVersion: | 5.0.0.0 |
| LegalCopyright: | Copyright (C) 2018 |
| ProductName: | WeMod |
| ProductVersion: | 5.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Sep-2018 02:43:27 |
| Detected languages: |
|
| CompanyName: | Daring Development Inc. |
| FileDescription: | WeMod Setup |
| FileVersion: | 5.0.0.0 |
| LegalCopyright: | Copyright (C) 2018 |
| ProductName: | WeMod |
| ProductVersion: | 5.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 27-Sep-2018 02:43:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00013000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00014000 | 0x0000D000 | 0x0000CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.91245 |
.rsrc | 0x00021000 | 0x00004000 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.67704 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.14523 | 1556 | UNKNOWN | English - United States | RT_MANIFEST |
102 | 1.51664 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
GDI32.dll |
KERNEL32.DLL |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WININET.dll |
gdiplus.dll |
urlmon.dll |
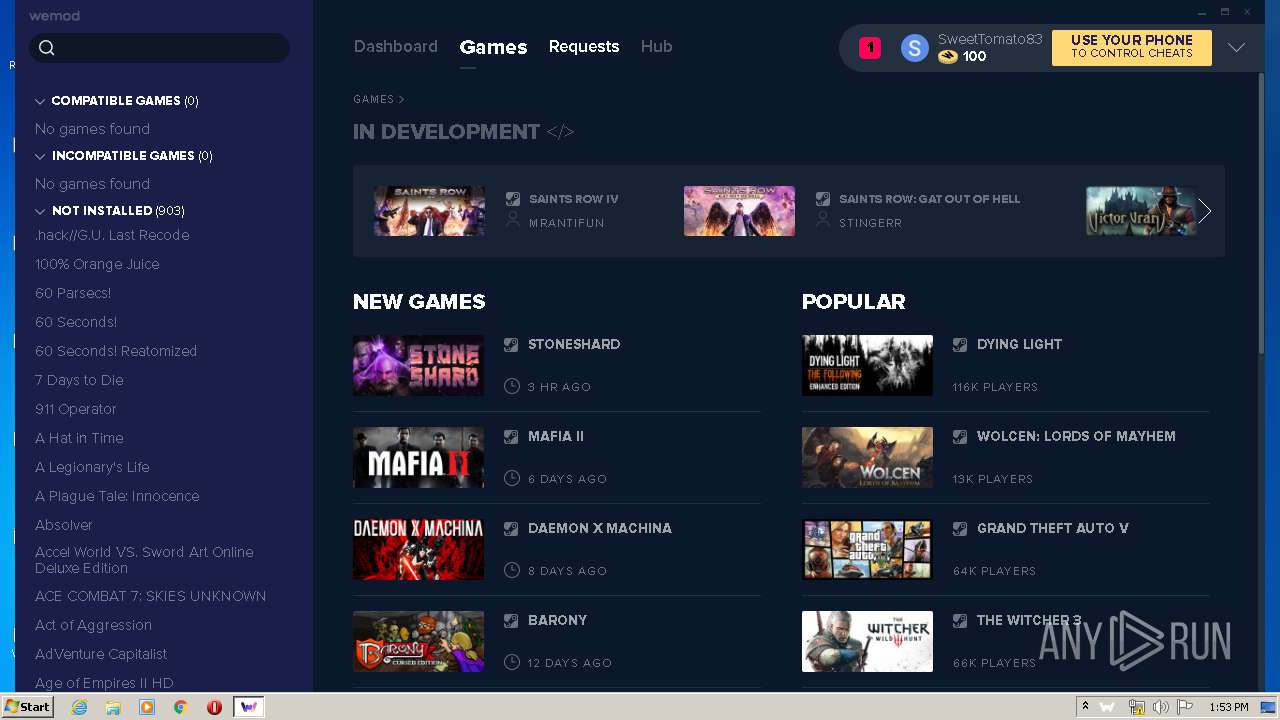
Total processes
52
Monitored processes
17
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 912 | "C:\Users\admin\AppData\Local\WeMod\app-6.2.17\WeMod.exe" --type=renderer --field-trial-handle=1056,7787853926999432601,9429570300976954671,131072 --disable-features=SpareRendererForSitePerProcess --lang=en-US --app-user-model-id=com.squirrel.WeMod.WeMod --app-path="C:\Users\admin\AppData\Local\WeMod\app-6.2.17\resources\app.asar" --node-integration --no-sandbox --no-zygote --background-color=#111111 --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4474848617652417253 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1508 /prefetch:1 | C:\Users\admin\AppData\Local\WeMod\app-6.2.17\WeMod.exe | — | WeMod.exe | |||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - Cheats and Mods Exit code: 0 Version: 6.2.17 Modules
| |||||||||||||||
| 1872 | "C:\Users\admin\AppData\Local\WeMod\app-6.2.17\WeMod.exe" --type=gpu-process --field-trial-handle=1056,7787853926999432601,9429570300976954671,131072 --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAADgAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --service-request-channel-token=11556751788607750666 --mojo-platform-channel-handle=1072 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\WeMod\app-6.2.17\WeMod.exe | — | WeMod.exe | |||||||||||
User: admin Company: WeMod Integrity Level: LOW Description: WeMod - Cheats and Mods Exit code: 4 Version: 6.2.17 Modules
| |||||||||||||||
| 2068 | "C:\Users\admin\AppData\Local\WeMod\Update.exe" --processStart "WeMod.exe" --process-start-args "wemod://projects/167?_inst=FKzR6sOaH48dbTy2" | C:\Users\admin\AppData\Local\WeMod\Update.exe | — | XCOM 2 Trainer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2092 | "C:\Users\admin\AppData\Local\WeMod\app-6.2.17\WeMod.exe" --type=gpu-process --field-trial-handle=1068,15709455450890493026,16122287598936082956,131072 --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAADgAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6322105952003962140 --mojo-platform-channel-handle=1104 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\WeMod\app-6.2.17\WeMod.exe | — | WeMod.exe | |||||||||||
User: admin Company: WeMod Integrity Level: LOW Description: WeMod - Cheats and Mods Exit code: 0 Version: 6.2.17 Modules
| |||||||||||||||
| 2296 | "C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe" --install . --silent | C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | WeMod-6.2.17[1].exe | ||||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 0 Version: 1.9.1.0 Modules
| |||||||||||||||
| 2412 | C:\Users\admin\AppData\Local\WeMod\Update.exe --checkForUpdate https://api.wemod.com/client/channels/stable | C:\Users\admin\AppData\Local\WeMod\Update.exe | WeMod.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2744 | "C:\Users\admin\AppData\Local\WeMod\app-6.2.17\WeMod.exe" wemod://projects/167?_inst=FKzR6sOaH48dbTy2 | C:\Users\admin\AppData\Local\WeMod\app-6.2.17\WeMod.exe | — | Update.exe | |||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - Cheats and Mods Exit code: 0 Version: 6.2.17 Modules
| |||||||||||||||
| 3092 | wmic /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntiVirusProduct Get displayName /Format:List | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Local\WeMod\app-6.2.17\Squirrel.exe" --updateSelf=C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | C:\Users\admin\AppData\Local\WeMod\app-6.2.17\Squirrel.exe | Update.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3188 | C:\Users\admin\AppData\Local\WeMod\Update.exe --createShortcut WeMod.exe | C:\Users\admin\AppData\Local\WeMod\Update.exe | — | WeMod.exe | |||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 0 Version: 1.9.1.0 Modules
| |||||||||||||||
Total events
1 757
Read events
1 663
Write events
94
Delete events
0
Modification events
| (PID) Process: | (3352) XCOM 2 Trainer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3352) XCOM 2 Trainer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3352) XCOM 2 Trainer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3352) XCOM 2 Trainer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3352) XCOM 2 Trainer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3352) XCOM 2 Trainer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3352) XCOM 2 Trainer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3352) XCOM 2 Trainer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2296) Update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2296) Update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
14
Suspicious files
13
Text files
28
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3352 | XCOM 2 Trainer.exe | C:\Users\admin\AppData\Local\Temp\Cab6E14.tmp | — | |
MD5:— | SHA256:— | |||
| 3352 | XCOM 2 Trainer.exe | C:\Users\admin\AppData\Local\Temp\Tar6E15.tmp | — | |
MD5:— | SHA256:— | |||
| 3352 | XCOM 2 Trainer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\WeMod-6.2.17[1].exe | — | |
MD5:— | SHA256:— | |||
| 3868 | WeMod-6.2.17[1].exe | C:\Users\admin\AppData\Local\SquirrelTemp\WeMod-6.2.17-full.nupkg | — | |
MD5:— | SHA256:— | |||
| 2296 | Update.exe | C:\Users\admin\AppData\Local\WeMod\packages\WeMod-6.2.17-full.nupkg | — | |
MD5:— | SHA256:— | |||
| 2296 | Update.exe | C:\Users\admin\AppData\Local\WeMod\app-6.2.17\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 2296 | Update.exe | C:\Users\admin\AppData\Local\WeMod\Update.exe | executable | |
MD5:— | SHA256:— | |||
| 3352 | XCOM 2 Trainer.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | der | |
MD5:— | SHA256:— | |||
| 2296 | Update.exe | C:\Users\admin\AppData\Local\WeMod\app-6.2.17\Infinity.exe | executable | |
MD5:— | SHA256:— | |||
| 2296 | Update.exe | C:\Users\admin\AppData\Local\WeMod\Infinity.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
11
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3352 | XCOM 2 Trainer.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAwx4ruF5Fxu4ljLnivRF80%3D | US | der | 278 b | whitelisted |
3352 | XCOM 2 Trainer.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2296 | Update.exe | 104.26.14.156:443 | api.wemod.com | Cloudflare Inc | US | unknown |
3352 | XCOM 2 Trainer.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2412 | Update.exe | 104.26.14.156:443 | api.wemod.com | Cloudflare Inc | US | unknown |
3732 | WeMod.exe | 172.217.22.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3732 | WeMod.exe | 185.172.148.128:443 | api-cdn.wemod.com | proinity GmbH | DE | malicious |
3732 | WeMod.exe | 104.26.15.156:443 | api.wemod.com | Cloudflare Inc | US | unknown |
3352 | XCOM 2 Trainer.exe | 104.26.14.156:443 | api.wemod.com | Cloudflare Inc | US | unknown |
3732 | WeMod.exe | 172.217.18.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3732 | WeMod.exe | 54.85.229.255:443 | ws.pusherapp.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.wemod.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
storage-cdn.wemod.com |
| suspicious |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
ws.pusherapp.com |
| whitelisted |
api-cdn.wemod.com |
| malicious |
community.wemod.com |
| unknown |