| File name: | l.rar.zip |
| Full analysis: | https://app.any.run/tasks/27867308-dbc1-4ad0-9d78-a243cecafcb0 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 17:08:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
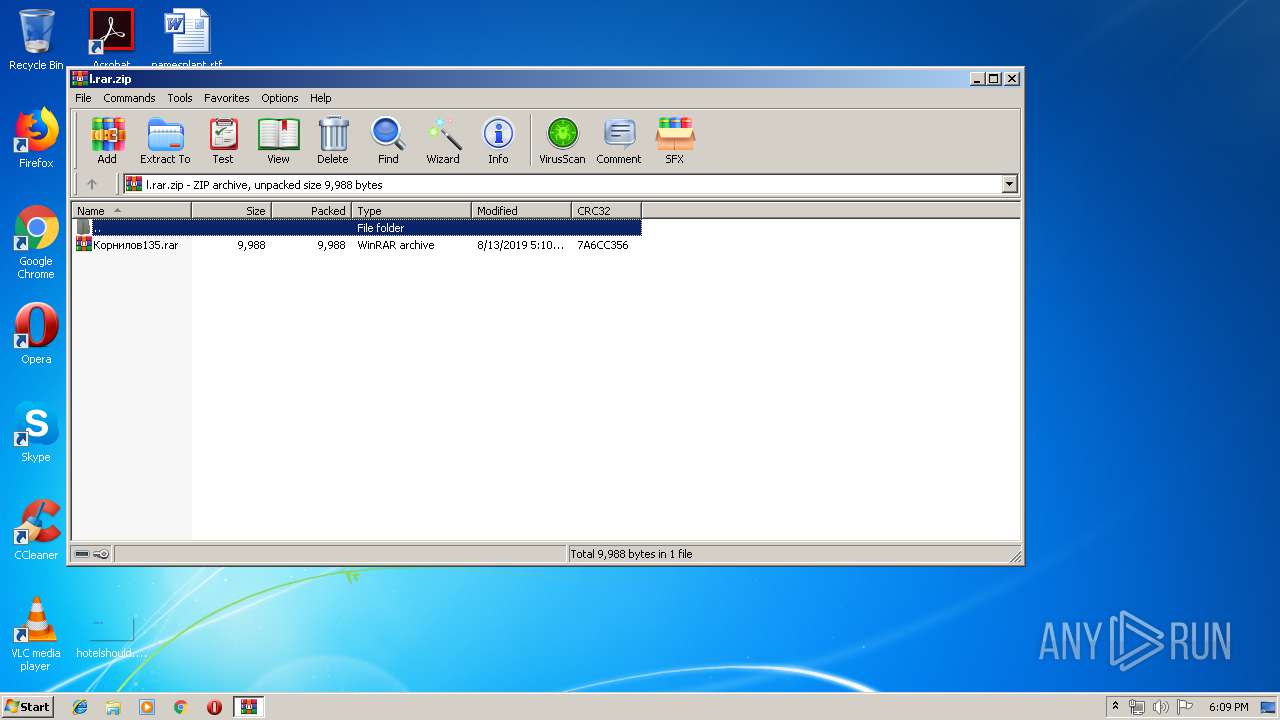
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 1CCE46312ACCEEAF9BAAF81F42C660FE |
| SHA1: | 4AC7DE6F5818A5C1E60E9CBF69DBB94E899E9AA4 |
| SHA256: | 35BB0603E378B5046356477BF75DB1E7B2E4C385D1A5D9A7184636726E391698 |
| SSDEEP: | 192:jDCjGwSNlh7GkD6OkbXyuU/qe/OGW5uVDoZrYWZb+1o7mTFBgS:HGwlh7vxkbXA/qeG9sBoZUDJBz |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes scripts
- WinRAR.exe (PID: 4088)
Application launched itself
- WinRAR.exe (PID: 1404)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1404 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\l.rar.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
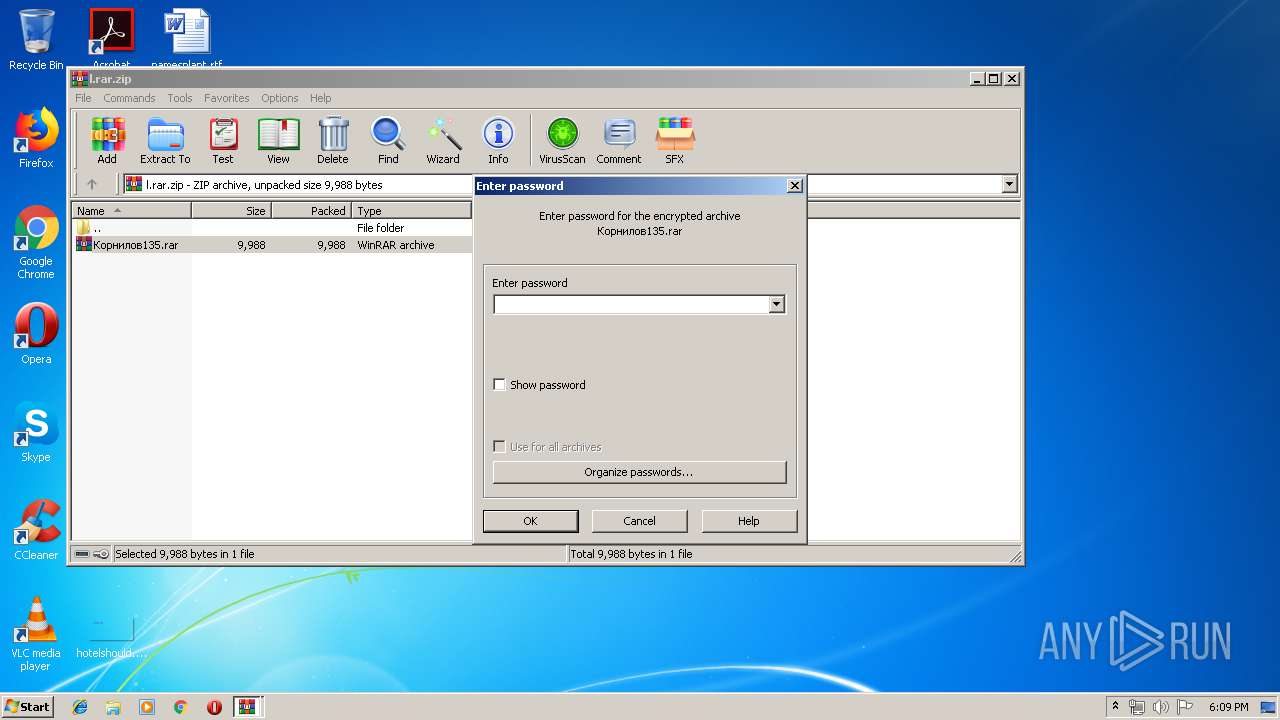
| 2716 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb4088.16365\Информация о заказе.2019-0812.docx.js" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
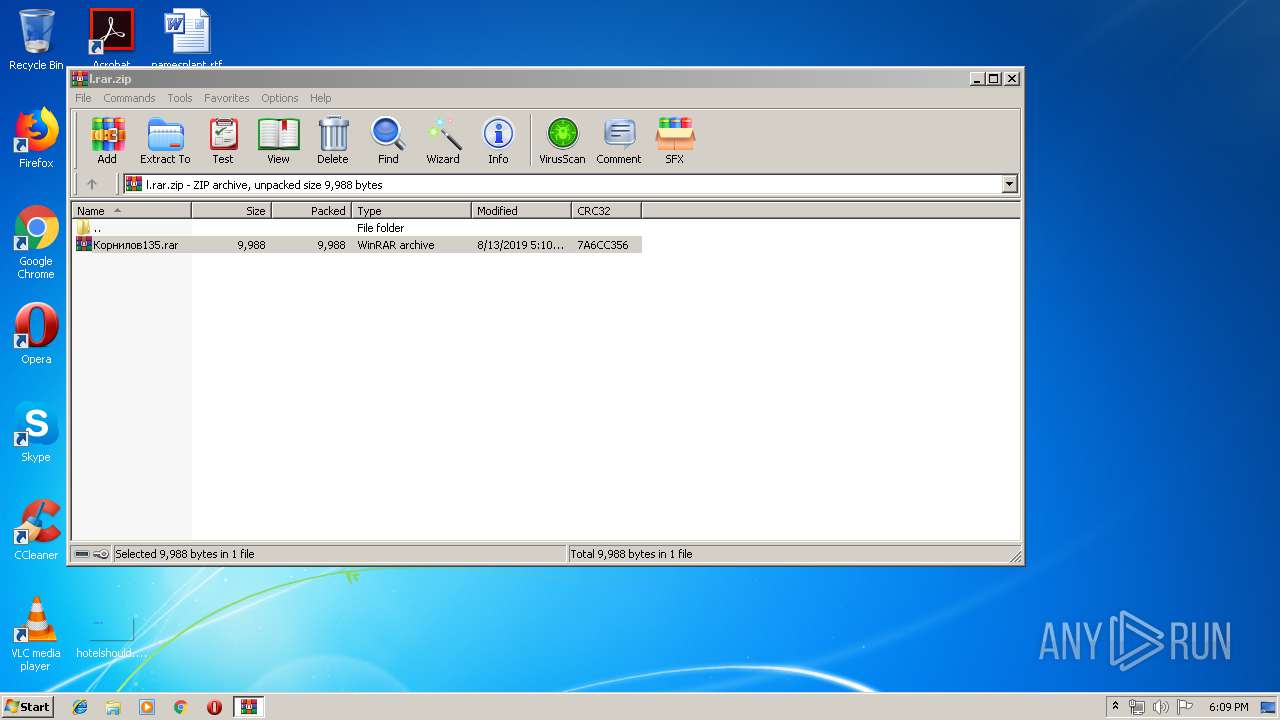
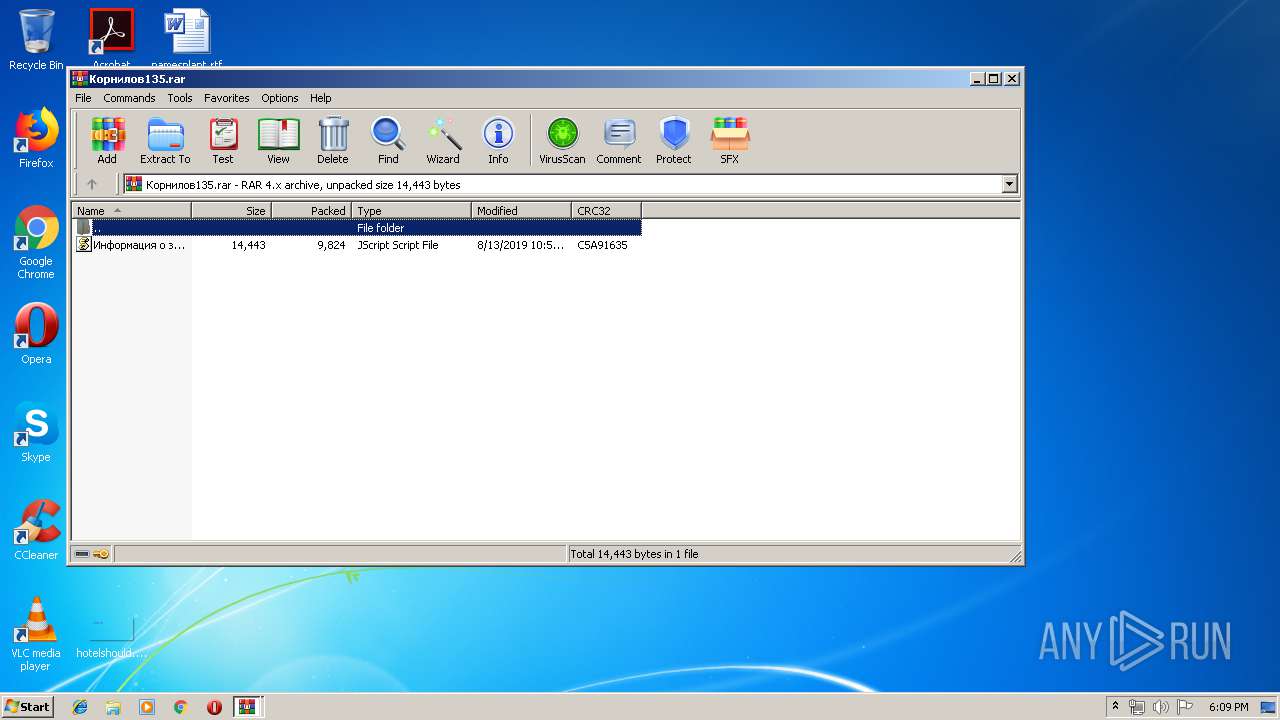
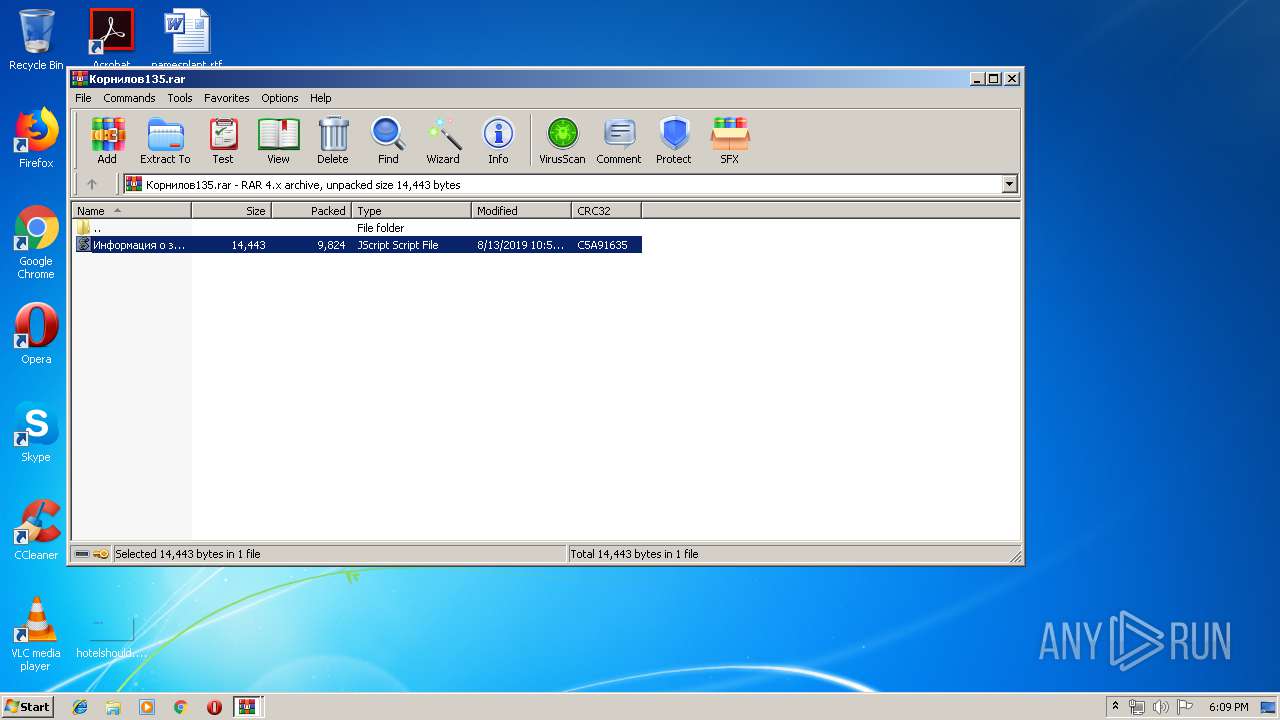
| 4088 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa1404.15687\Корнилов135.rar | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
924
Read events
878
Write events
46
Delete events
0
Modification events
| (PID) Process: | (1404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1404) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\l.rar.zip | |||
| (PID) Process: | (1404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
0
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4088 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb4088.16365\Информация о заказе.2019-0812.docx.js | text | |
MD5:— | SHA256:— | |||
| 1404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa1404.15687\Корнилов135.rar | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2716 | WScript.exe | GET | 404 | 192.227.118.7:80 | http://www.eletrotecsolucoes.com/wp-content/languages/plugins/1c.jpg | US | xml | 345 b | malicious |
2716 | WScript.exe | GET | 404 | 64.13.232.105:80 | http://s42679.gridserver.com/1c.jpg | US | xml | 345 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2716 | WScript.exe | 192.227.118.7:80 | www.eletrotecsolucoes.com | Cloud South | US | malicious |
— | — | 64.13.232.105:80 | s42679.gridserver.com | Media Temple, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.eletrotecsolucoes.com |
| malicious |
s42679.gridserver.com |
| unknown |