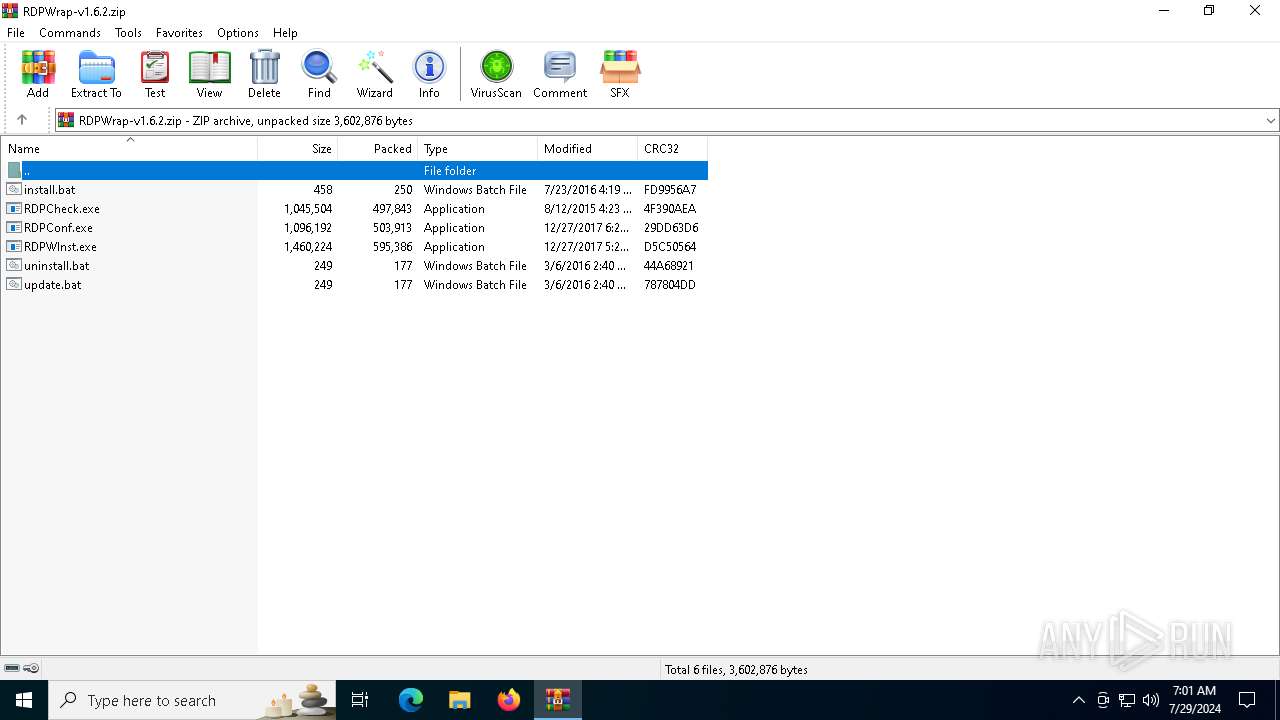
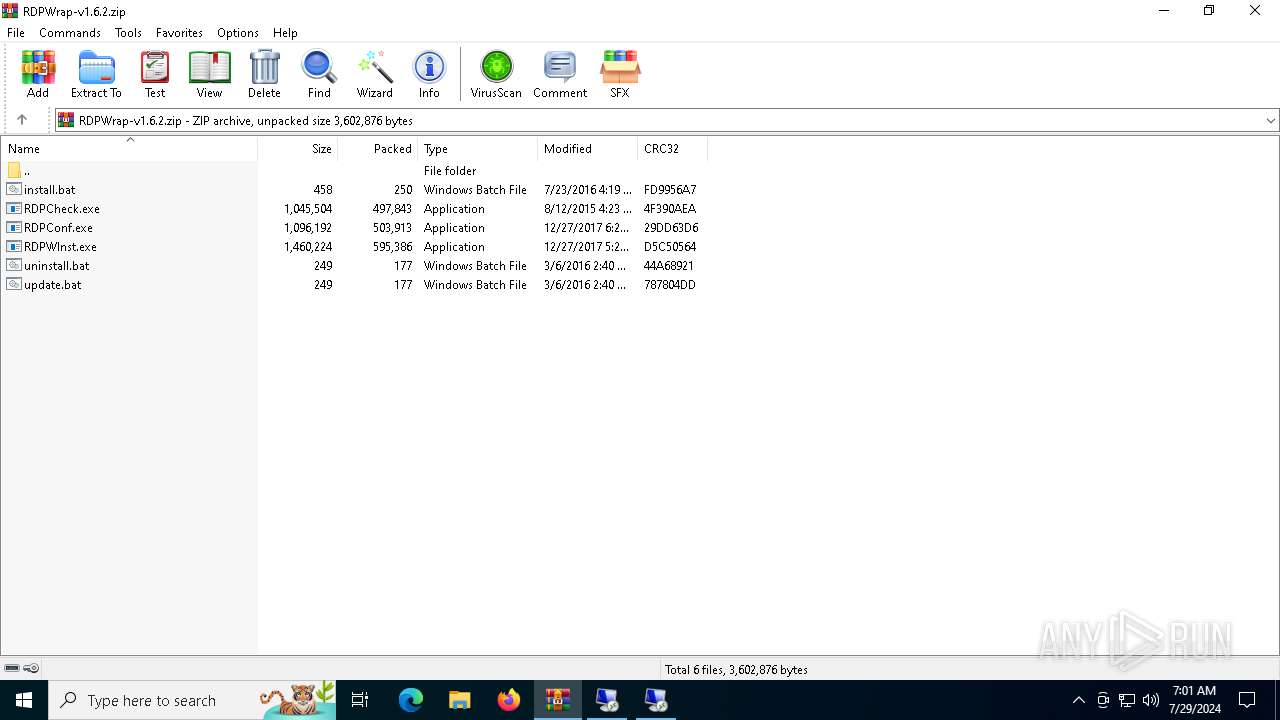
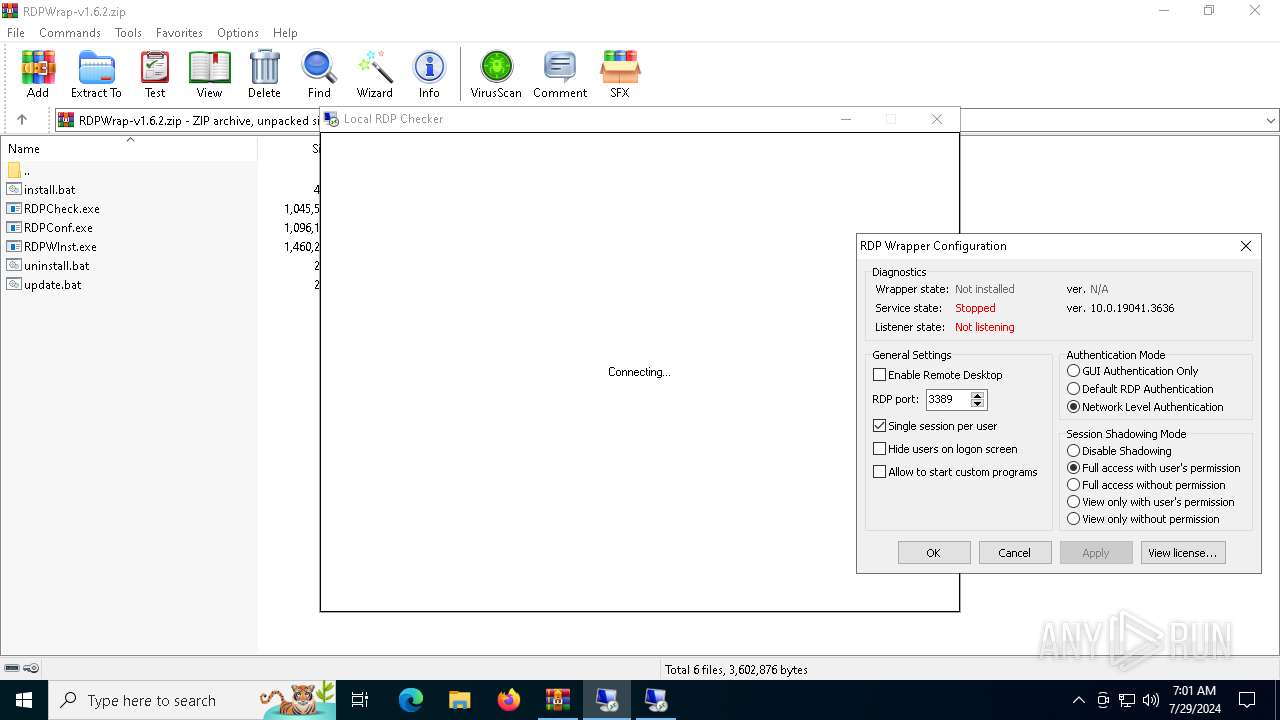
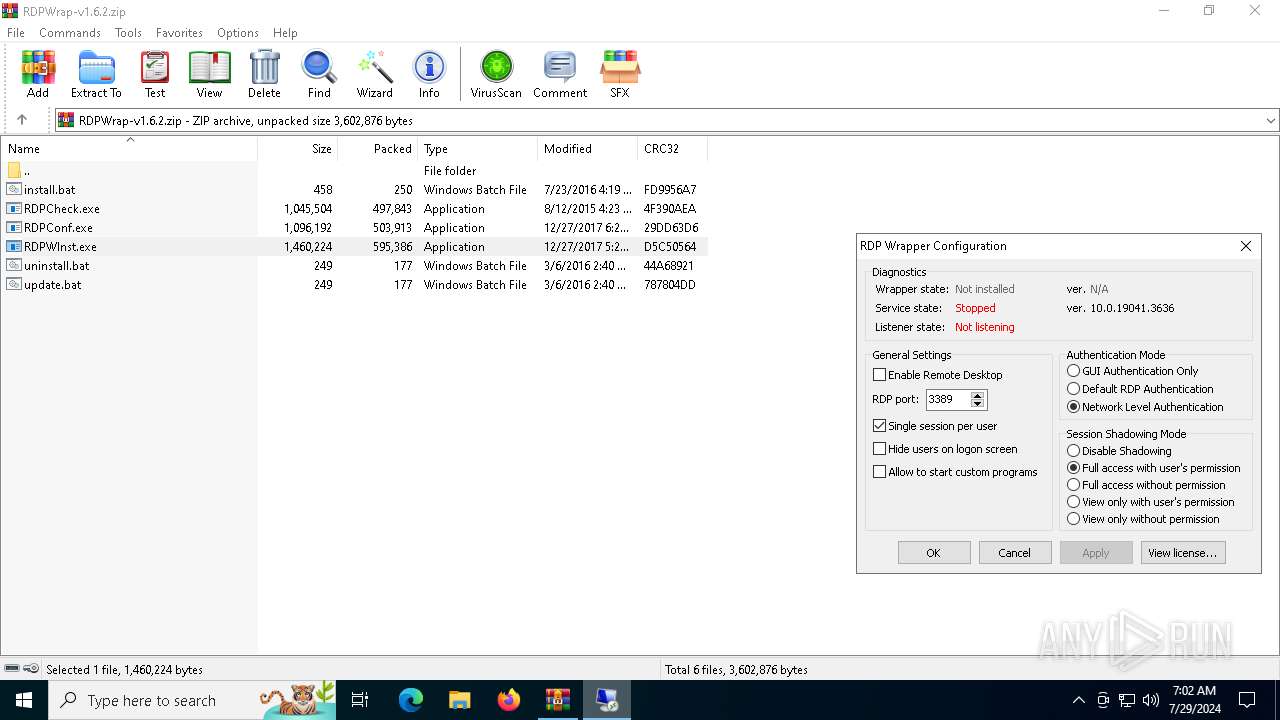
| File name: | RDPWrap-v1.6.2.zip |
| Full analysis: | https://app.any.run/tasks/bc1552c0-6f49-4be0-99bd-3e22ddcb30f3 |
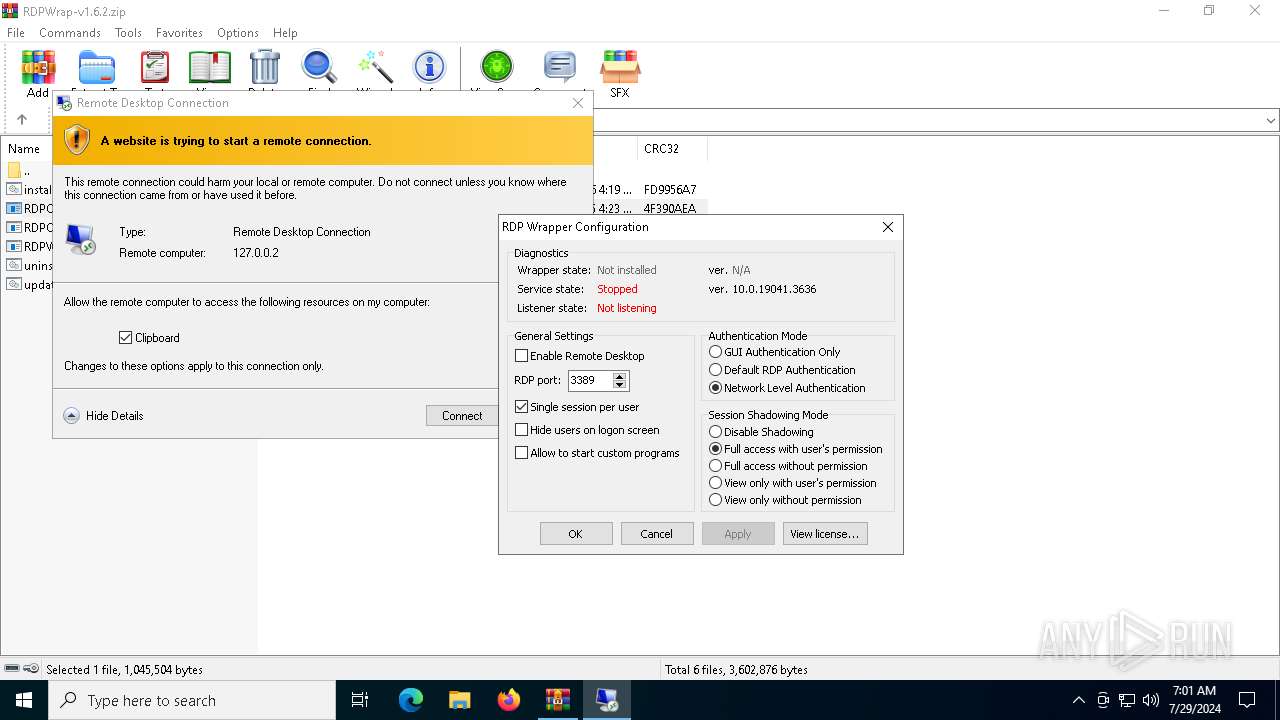
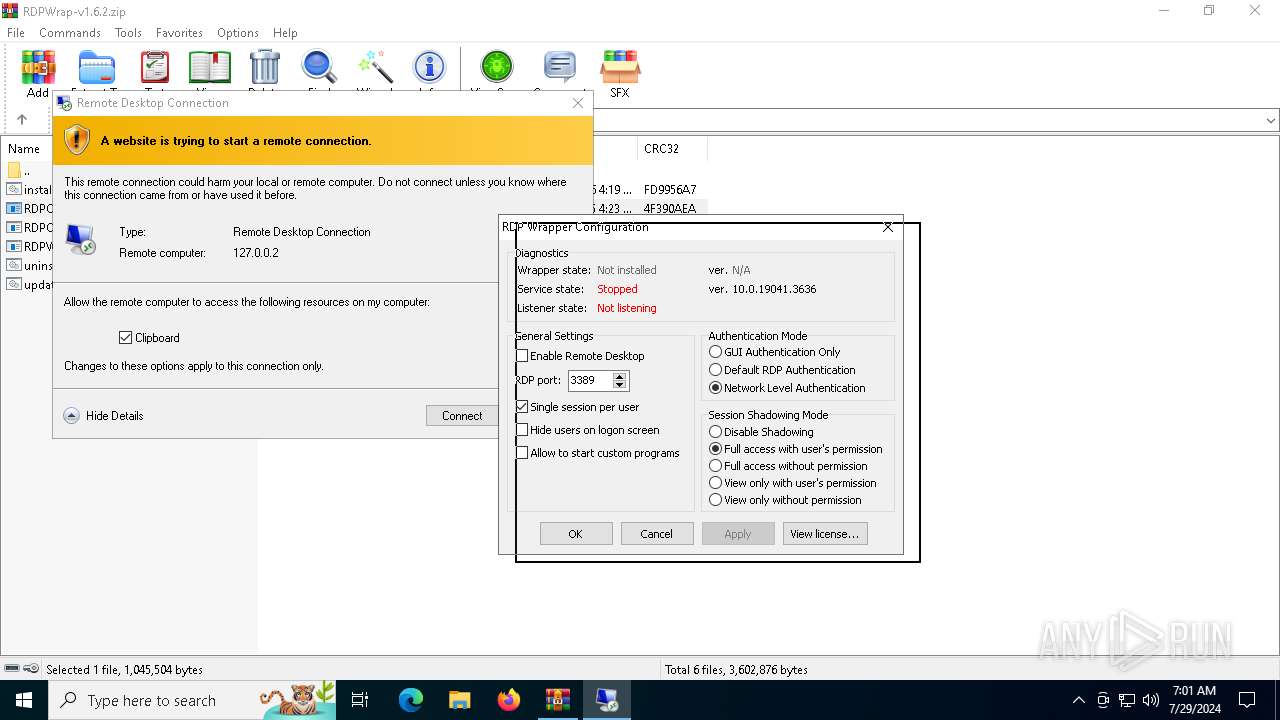
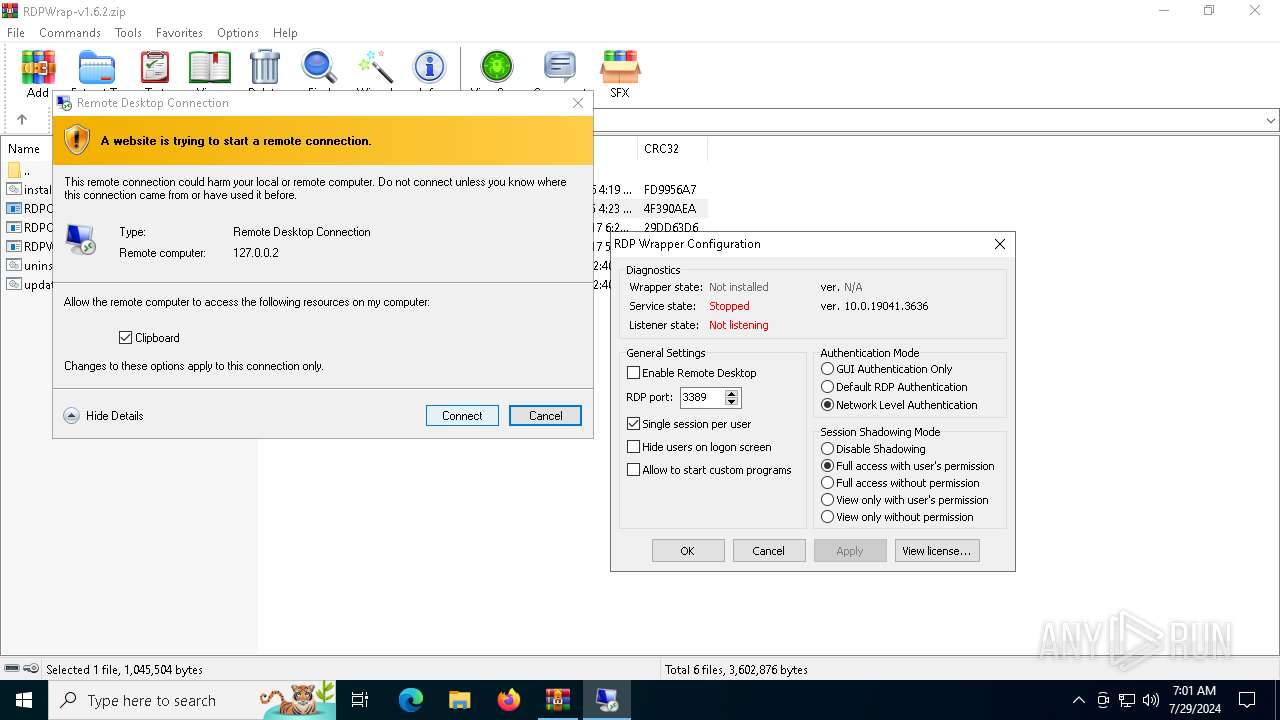
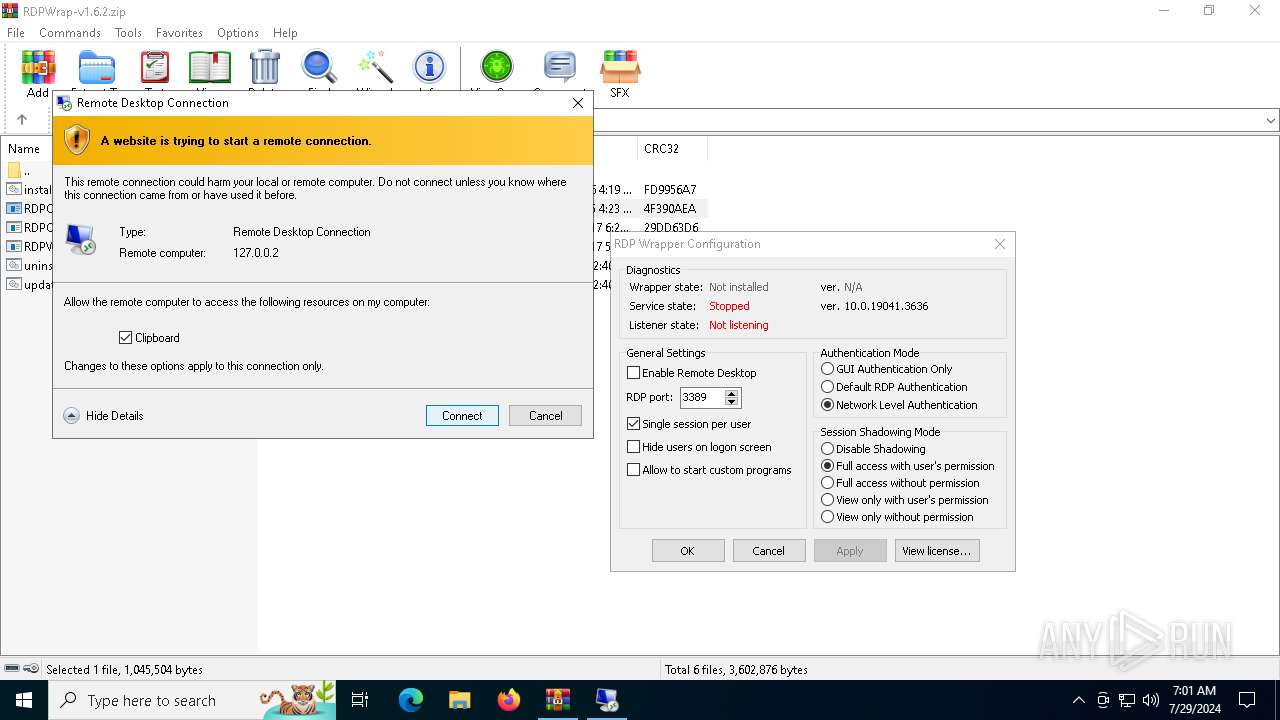
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2024, 07:01:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | C26A2C5F6154225E8D83C4000306F162 |
| SHA1: | 67C586CEDBF0852AA52268311841CBAC5C96FDF8 |
| SHA256: | 35A9481DDBED5177431A9EA4BD09468FE987797D7B1231D64942D17EB54EC269 |
| SSDEEP: | 49152:cPEbpqUPr0OMPjmNgyV24OXxr2/NV0CA7QUmu4LnB:cPEbpPPrC4gWFOBr4Wfg |
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3168)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3168)
- RDPCheck.exe (PID: 5124)
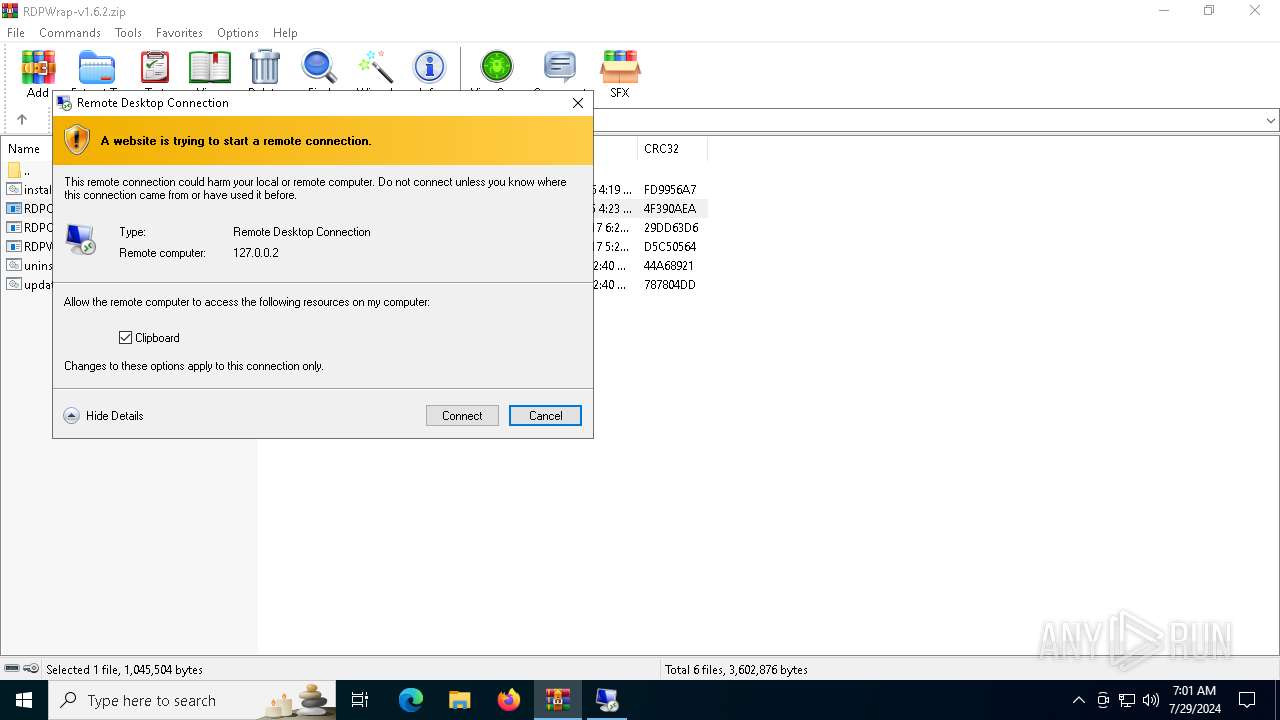
Reads the history of recent RDP connections
- RDPCheck.exe (PID: 5124)
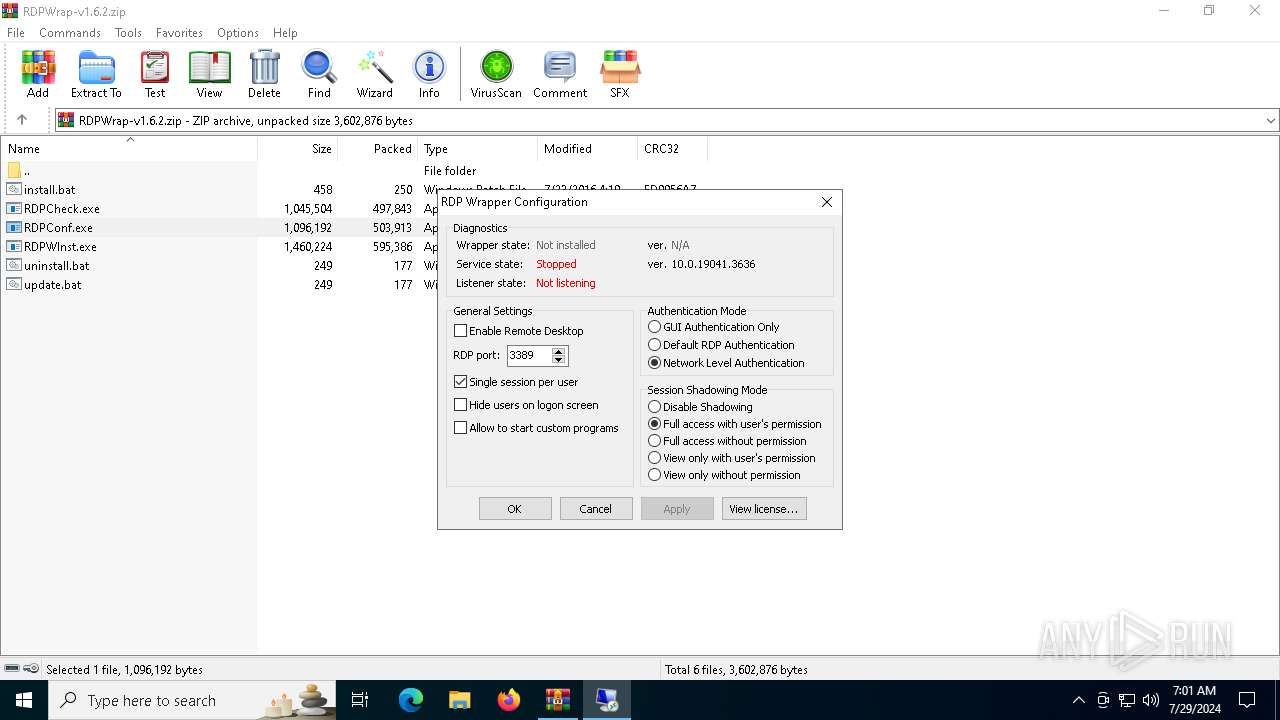
The process checks if it is being run in the virtual environment
- RDPCheck.exe (PID: 5124)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3168)
Checks supported languages
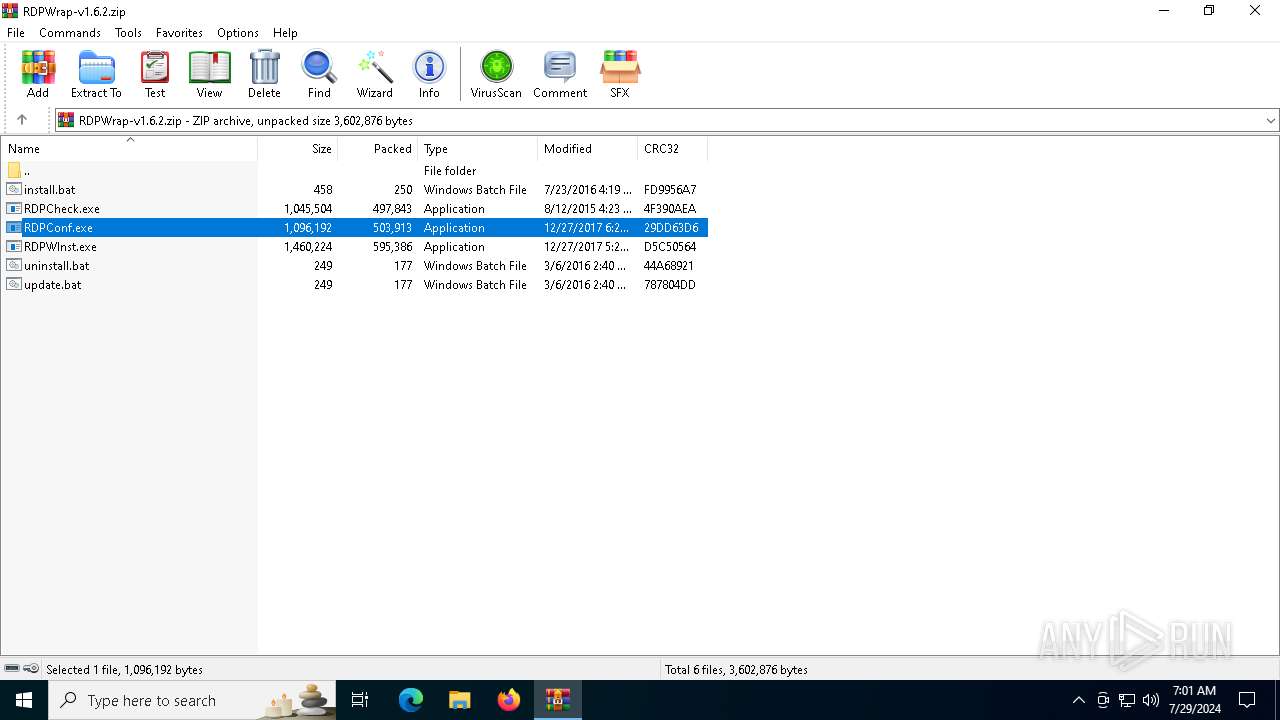
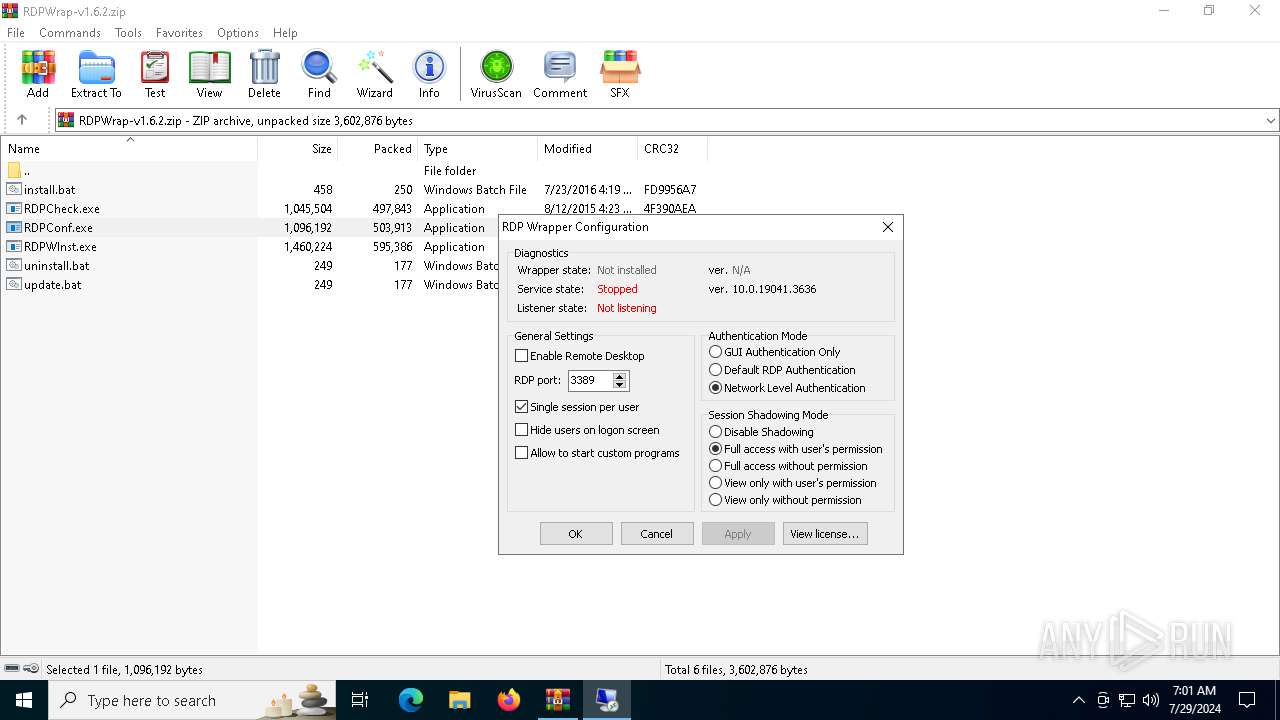
- RDPConf.exe (PID: 4152)
- RDPCheck.exe (PID: 5124)
- RDPWInst.exe (PID: 1112)
Reads the computer name
- RDPConf.exe (PID: 4152)
- RDPCheck.exe (PID: 5124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2016:07:23 19:19:08 |
| ZipCRC: | 0xfd9956a7 |
| ZipCompressedSize: | 250 |
| ZipUncompressedSize: | 458 |
| ZipFileName: | install.bat |
Total processes
153
Monitored processes
9
Malicious processes
2
Suspicious processes
0
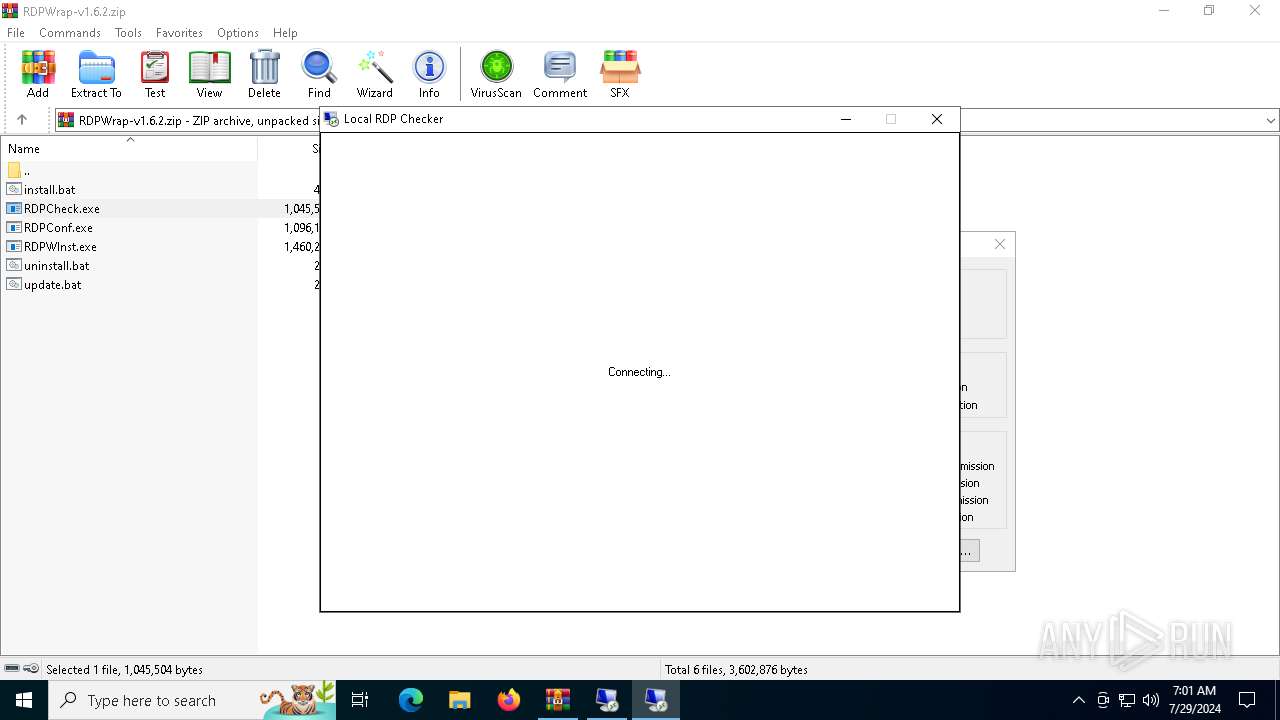
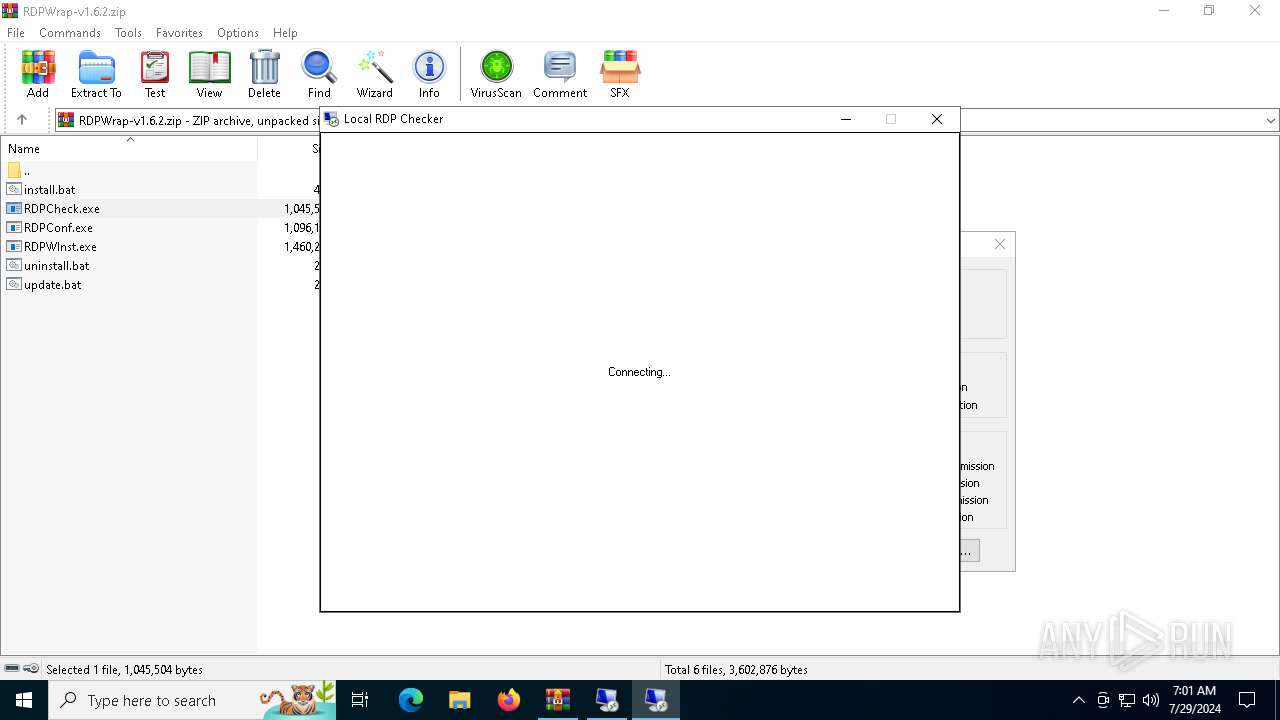
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
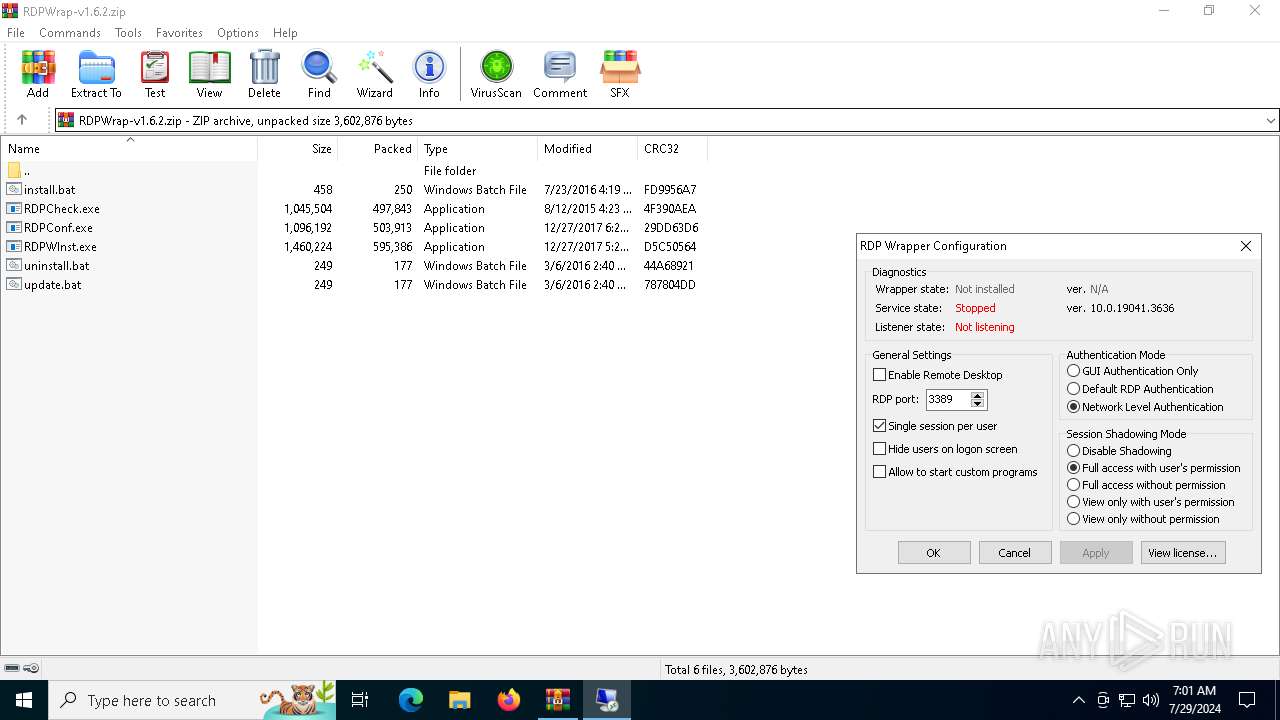
| 1112 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.33231\RDPWInst.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.33231\RDPWInst.exe | WinRAR.exe | ||||||||||||
User: admin Company: Stas'M Corp. Integrity Level: HIGH Description: RDP Wrapper Library Installer Exit code: 0 Version: 2.5.0.0 Modules
| |||||||||||||||
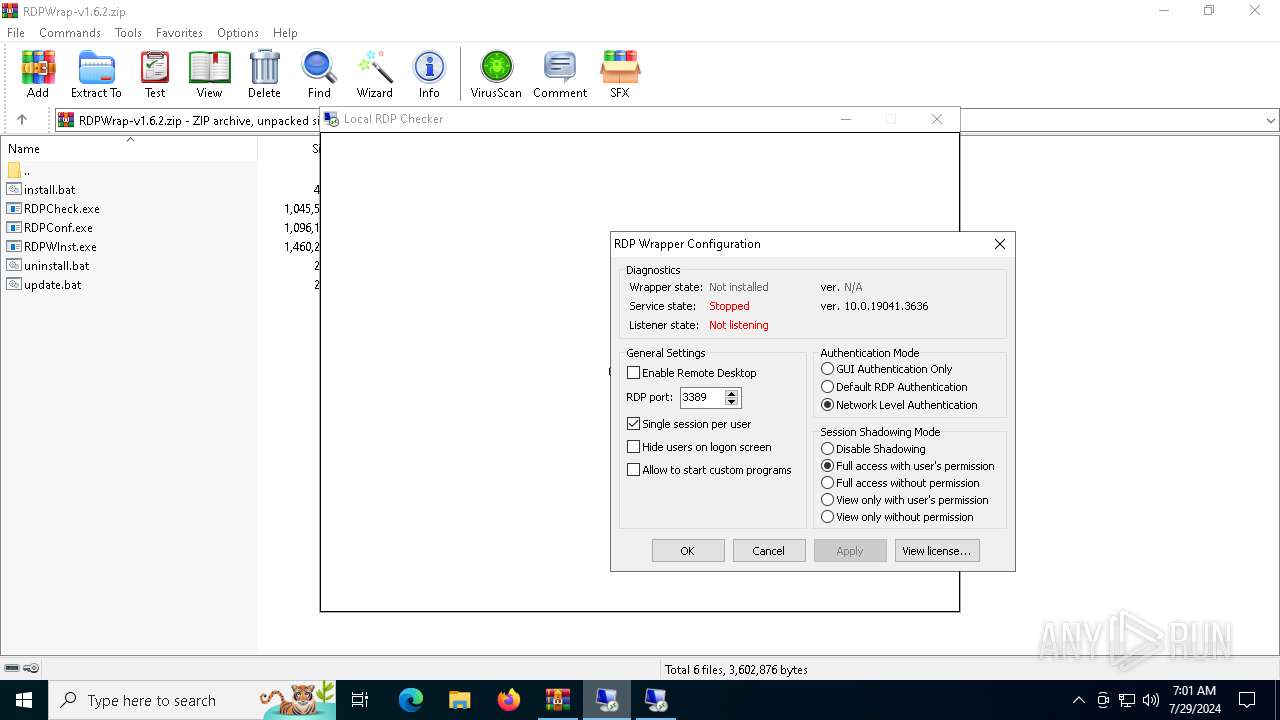
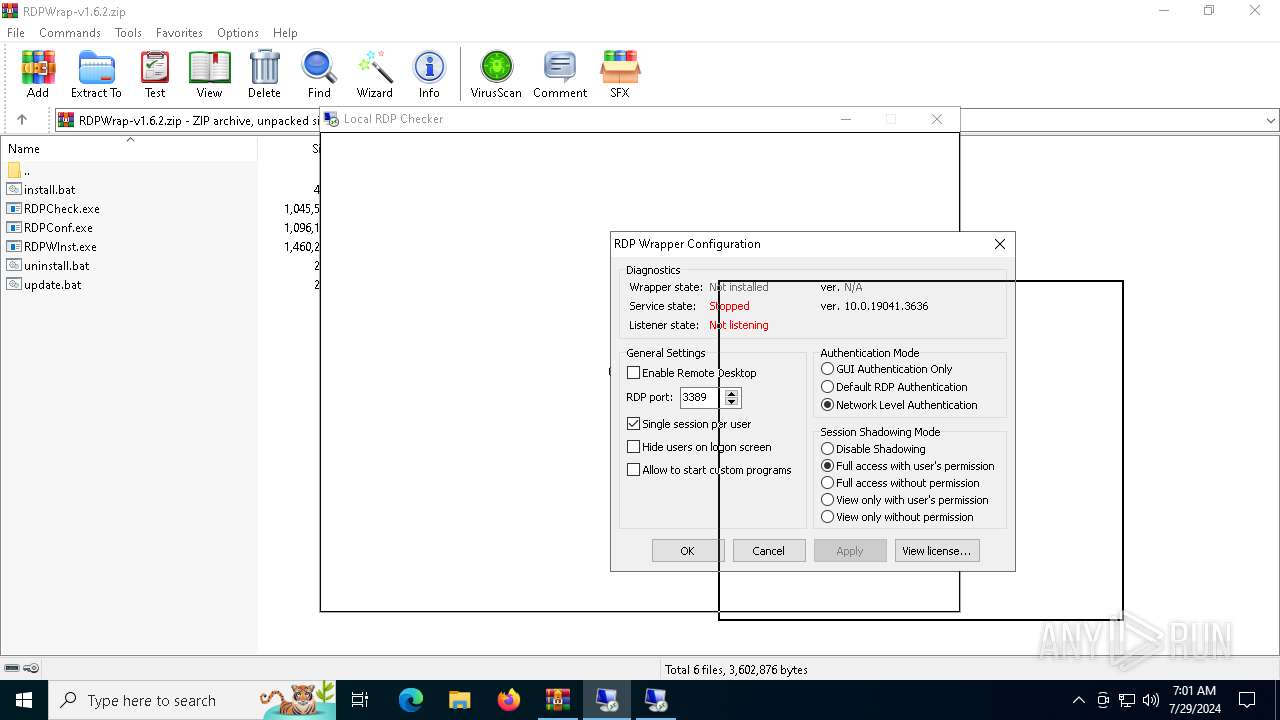
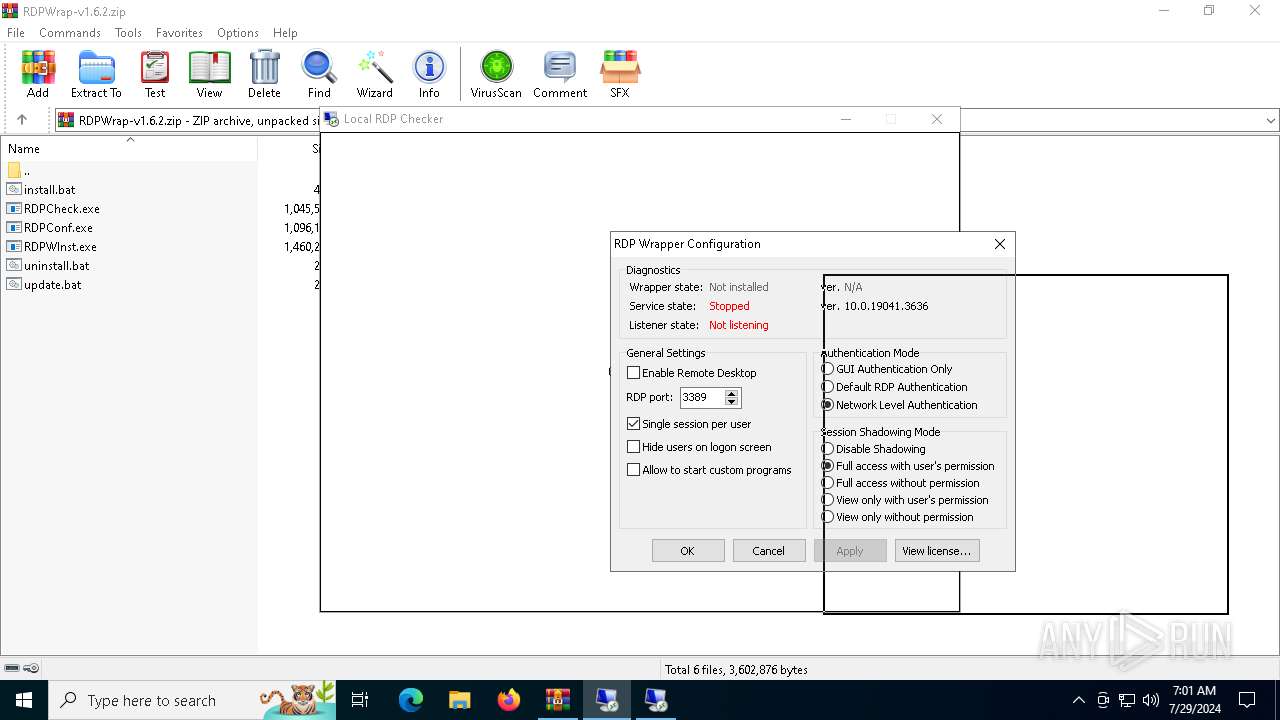
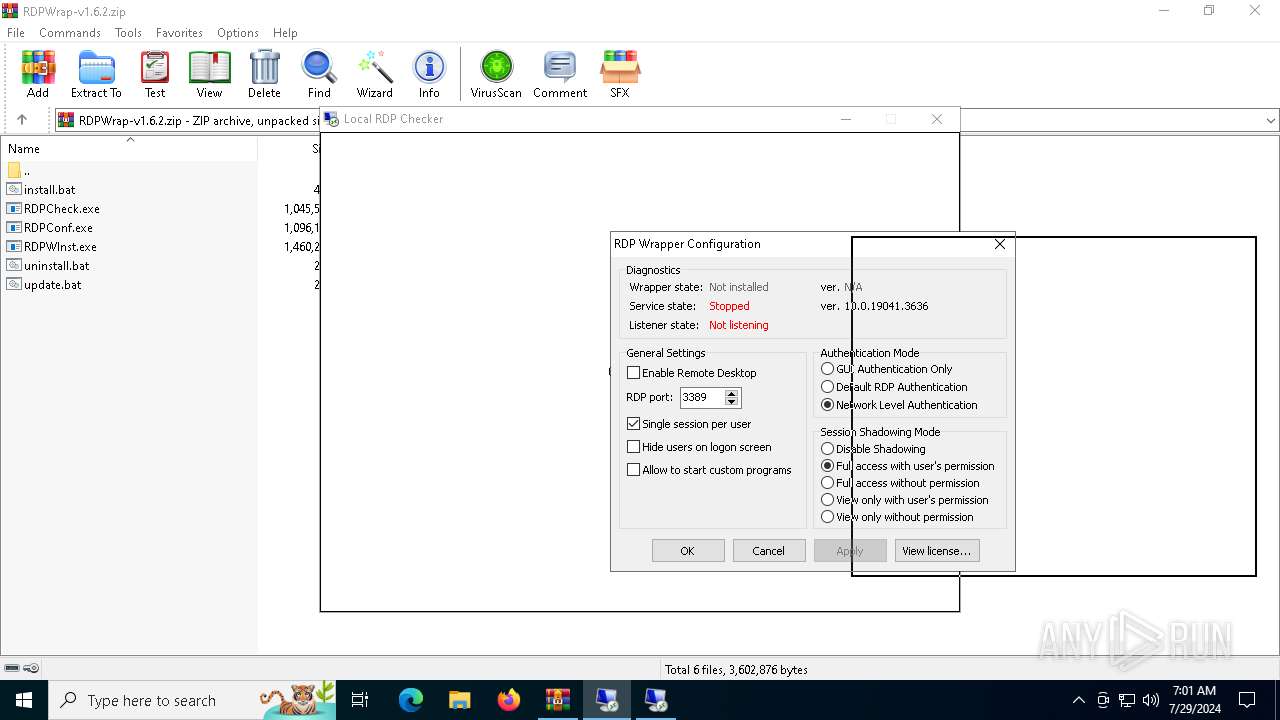
| 1764 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.28799\RDPConf.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.28799\RDPConf.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Stas'M Corp. Integrity Level: MEDIUM Description: RDP Configuration Program Exit code: 3221226540 Version: 1.4.0.0 Modules
| |||||||||||||||
| 3168 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\RDPWrap-v1.6.2.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4152 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.28799\RDPConf.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.28799\RDPConf.exe | WinRAR.exe | ||||||||||||
User: admin Company: Stas'M Corp. Integrity Level: HIGH Description: RDP Configuration Program Version: 1.4.0.0 Modules
| |||||||||||||||
| 4608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | RDPWInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
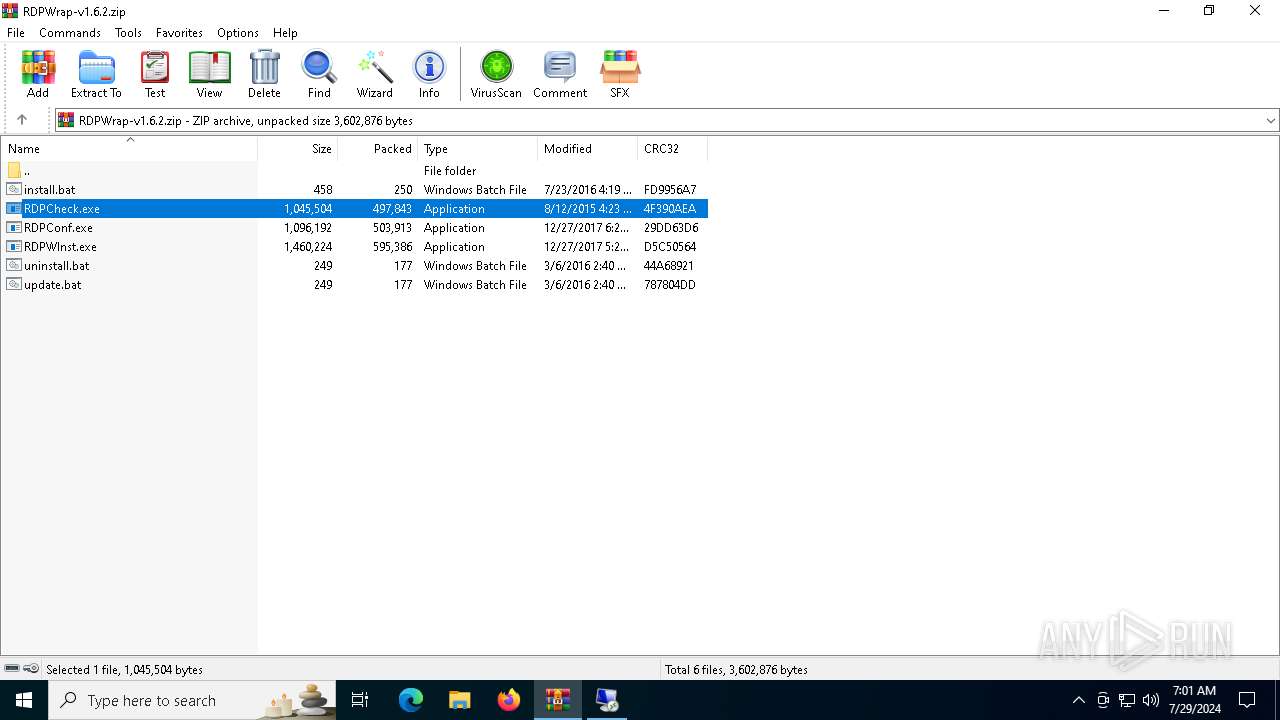
| 5124 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.29499\RDPCheck.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.29499\RDPCheck.exe | WinRAR.exe | ||||||||||||
User: admin Company: Stas'M Corp. Integrity Level: HIGH Description: Local RDP Checker Exit code: 0 Version: 2.2.0.0 Modules
| |||||||||||||||
| 6504 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6636 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.33231\RDPWInst.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.33231\RDPWInst.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Stas'M Corp. Integrity Level: MEDIUM Description: RDP Wrapper Library Installer Exit code: 3221226540 Version: 2.5.0.0 Modules
| |||||||||||||||
| 6640 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.29499\RDPCheck.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.29499\RDPCheck.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Stas'M Corp. Integrity Level: MEDIUM Description: Local RDP Checker Exit code: 3221226540 Version: 2.2.0.0 Modules
| |||||||||||||||
Total events
9 290
Read events
9 271
Write events
19
Delete events
0
Modification events
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\RDPWrap-v1.6.2.zip | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
9
Suspicious files
0
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
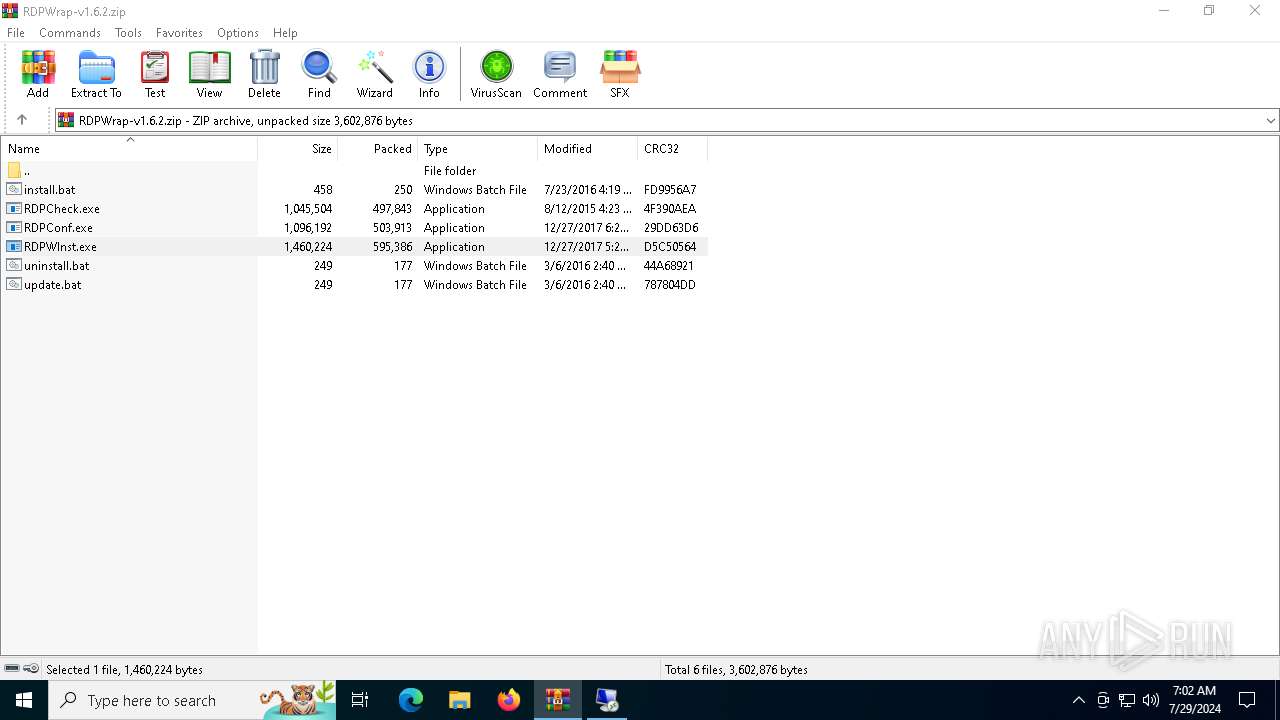
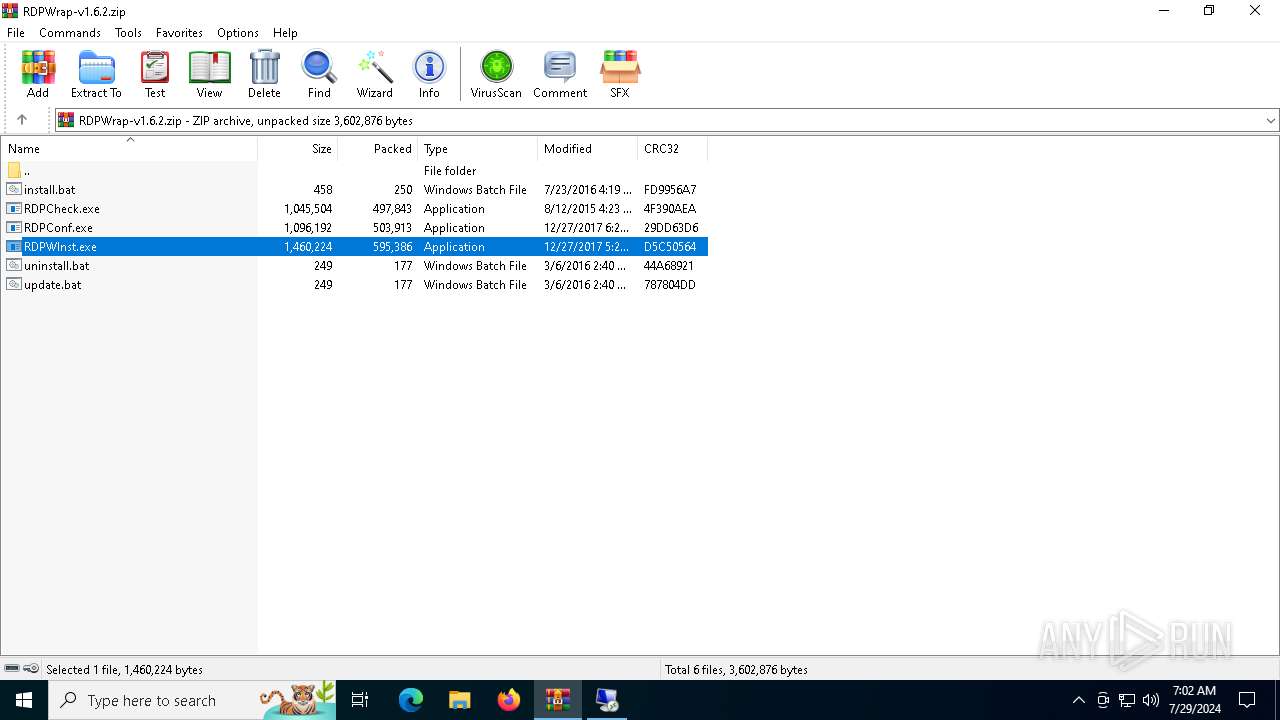
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.29499\RDPCheck.exe | executable | |
MD5:8F82226B2F24D470C02F6664F67F23F7 | SHA256:5603338A1F8DBB46EFB8E0869DB3491D5DB92F362711D6680F91ECC5D18BFADF | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.28799\uninstall.bat | text | |
MD5:ECCB8A01D0427EF29C2380D7DDA399F3 | SHA256:083CD340C800CC021D4A59388680CE0E7AB0F8B998E67DEF6A507070E7FA01B7 | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.29499\RDPWInst.exe | executable | |
MD5:3288C284561055044C489567FD630AC2 | SHA256:AC92D4C6397EB4451095949AC485EF4EC38501D7BB6F475419529AE67E297753 | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.29499\install.bat | text | |
MD5:CBAD5B2CA73917006791882274F769E8 | SHA256:022364EE1FCE61C8A867216C79F223BF47692CD648E3FD6B244FC615B86E4C58 | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.29499\update.bat | text | |
MD5:29CA1C35075247B035AF75C11CAB78F1 | SHA256:353F2DC17A4E80564CAA175F7170DBEDC1B40F704444520AE671F78A5D1F2B6D | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.33231\install.bat | text | |
MD5:CBAD5B2CA73917006791882274F769E8 | SHA256:022364EE1FCE61C8A867216C79F223BF47692CD648E3FD6B244FC615B86E4C58 | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.29499\uninstall.bat | text | |
MD5:ECCB8A01D0427EF29C2380D7DDA399F3 | SHA256:083CD340C800CC021D4A59388680CE0E7AB0F8B998E67DEF6A507070E7FA01B7 | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.33231\RDPCheck.exe | executable | |
MD5:8F82226B2F24D470C02F6664F67F23F7 | SHA256:5603338A1F8DBB46EFB8E0869DB3491D5DB92F362711D6680F91ECC5D18BFADF | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.33231\RDPWInst.exe | executable | |
MD5:3288C284561055044C489567FD630AC2 | SHA256:AC92D4C6397EB4451095949AC485EF4EC38501D7BB6F475419529AE67E297753 | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3168.33231\update.bat | text | |
MD5:29CA1C35075247B035AF75C11CAB78F1 | SHA256:353F2DC17A4E80564CAA175F7170DBEDC1B40F704444520AE671F78A5D1F2B6D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
38
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1296 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1028 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5368 | SearchApp.exe | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
5368 | SearchApp.exe | 2.23.209.169:443 | www.bing.com | Akamai International B.V. | GB | unknown |
4028 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6012 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6572 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
204 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
a-ring-fallback.msedge.net |
| unknown |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |