| URL: | https://connectfansus.lt.acemlna.com/Prod/link-tracker?redirectUrl=aHR0cHMlM0ElMkYlMkZwYWdhbWVudG8ub2dydXBvaW1wdWxzZS5jb20lMkZMR2tO&sig=HEz1yAE3AnqPuE1E5x2B85npNv9apJBriEfD1oZFcDeu&iat=1709127434&a=%7C%7C801579481%7C%7C&account=connectfansus.activehosted.com&email=RWpwN3ZZGJSMM3y4VAS9azF01WqVKzNpZVcpdrf6UFhM8Ew%3D%3AQ7K7ypPXKwbvTegOw5FKpT%2BzdPVOoq5N&s=be6ec883b9846ec07ebc65a9eb80278b&i=3875A4218A1A15249 |
| Full analysis: | https://app.any.run/tasks/9198a973-6d7a-4e02-bf62-feb70b947127 |
| Verdict: | Malicious activity |
| Analysis date: | February 29, 2024, 06:20:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6B8899BF1F12BAF0A84AAF64AD972255 |
| SHA1: | AA23C97AABF8E82B762492BE1E29F7866DED1C2B |
| SHA256: | 35A46AD9C1FD11AA3766432F293BC4769D24F2B2CCF935CE2638E877AD10B1DA |
| SSDEEP: | 12:2d3WUglSm0mMPCenvF9CDJrZh21hT0k/RF6:2dTgY/CenbSJrZh+iEF6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- msdt.exe (PID: 956)
Reads settings of System Certificates
- msdt.exe (PID: 956)
Reads the Internet Settings
- sdiagnhost.exe (PID: 3164)
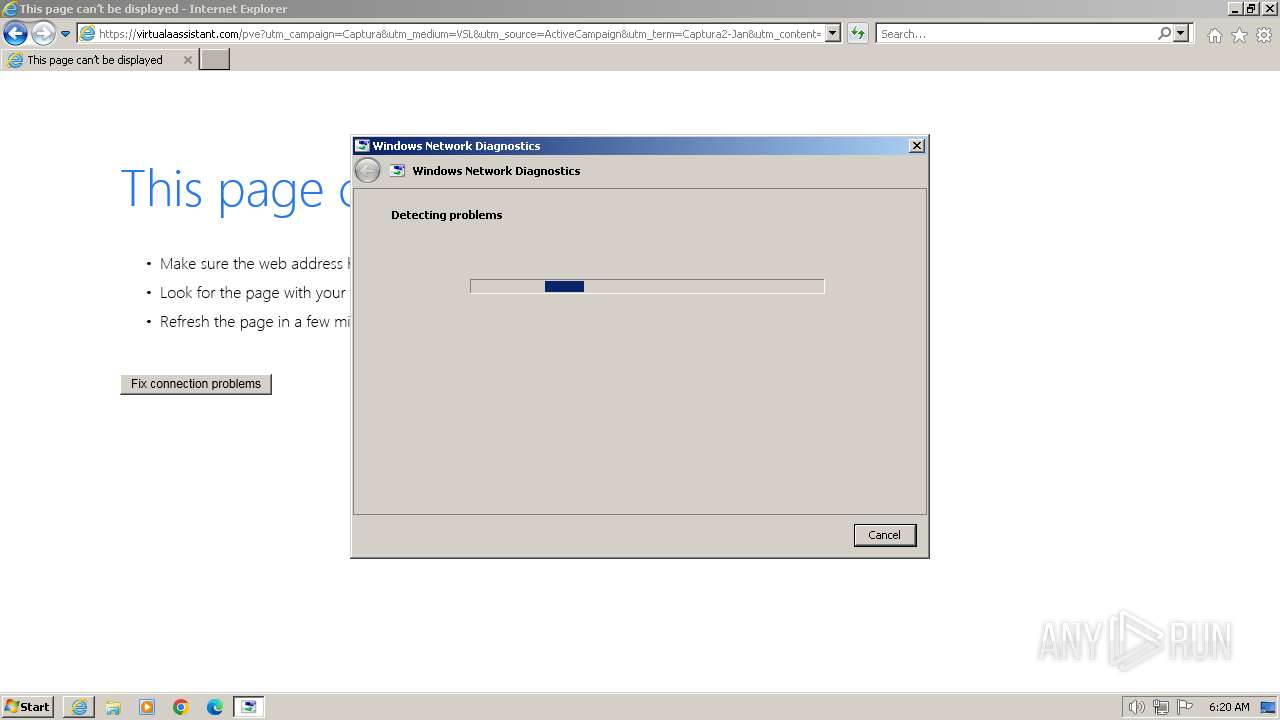
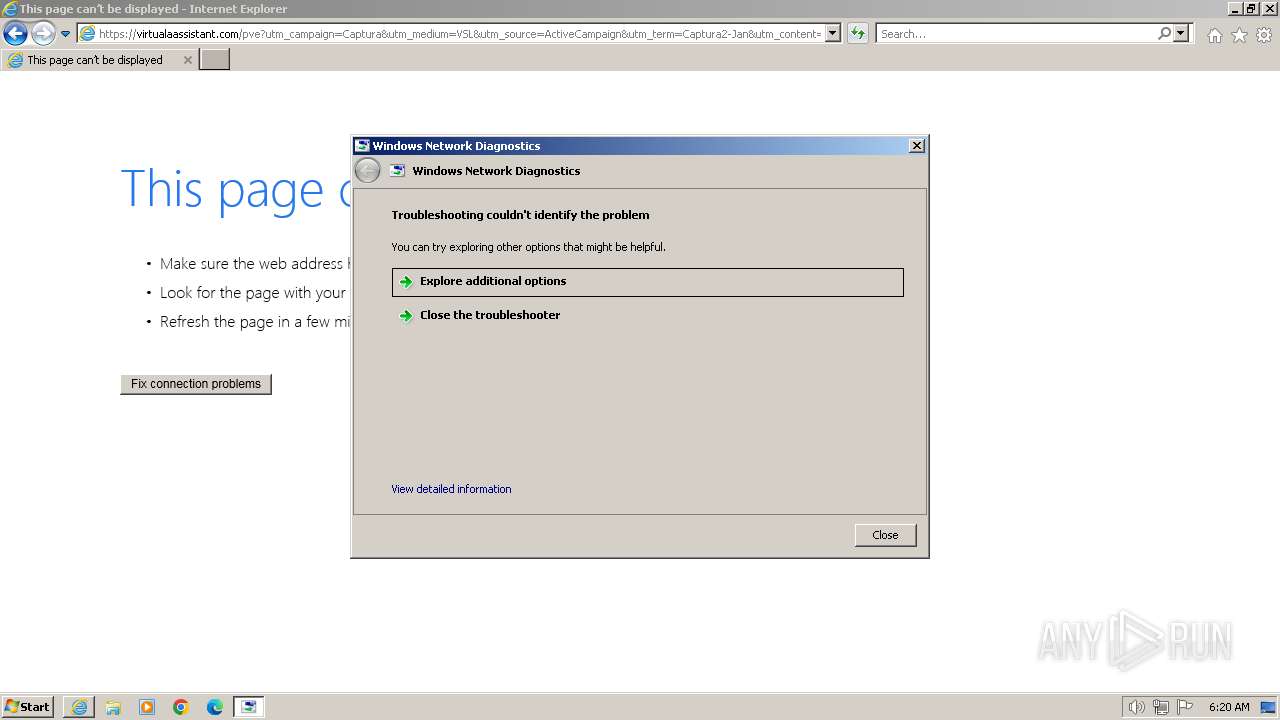
Process uses IPCONFIG to discover network configuration
- sdiagnhost.exe (PID: 3164)
Uses ROUTE.EXE to obtain the routing table information
- sdiagnhost.exe (PID: 3164)
INFO
Application launched itself
- iexplore.exe (PID: 3240)
Reads security settings of Internet Explorer
- msdt.exe (PID: 956)
- sdiagnhost.exe (PID: 3164)
Create files in a temporary directory
- msdt.exe (PID: 956)
- sdiagnhost.exe (PID: 3164)
- makecab.exe (PID: 2724)
Drops the executable file immediately after the start
- msdt.exe (PID: 956)
Reads the software policy settings
- msdt.exe (PID: 956)
Creates files or folders in the user directory
- msdt.exe (PID: 956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | -modal 1114548 -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDF2C6A.tmp -ep NetworkDiagnosticsWeb | C:\Windows\System32\msdt.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1768 | "C:\Windows\system32\ROUTE.EXE" print | C:\Windows\System32\ROUTE.EXE | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2724 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\System32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2832 | "C:\Windows\system32\ipconfig.exe" /all | C:\Windows\System32\ipconfig.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3164 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
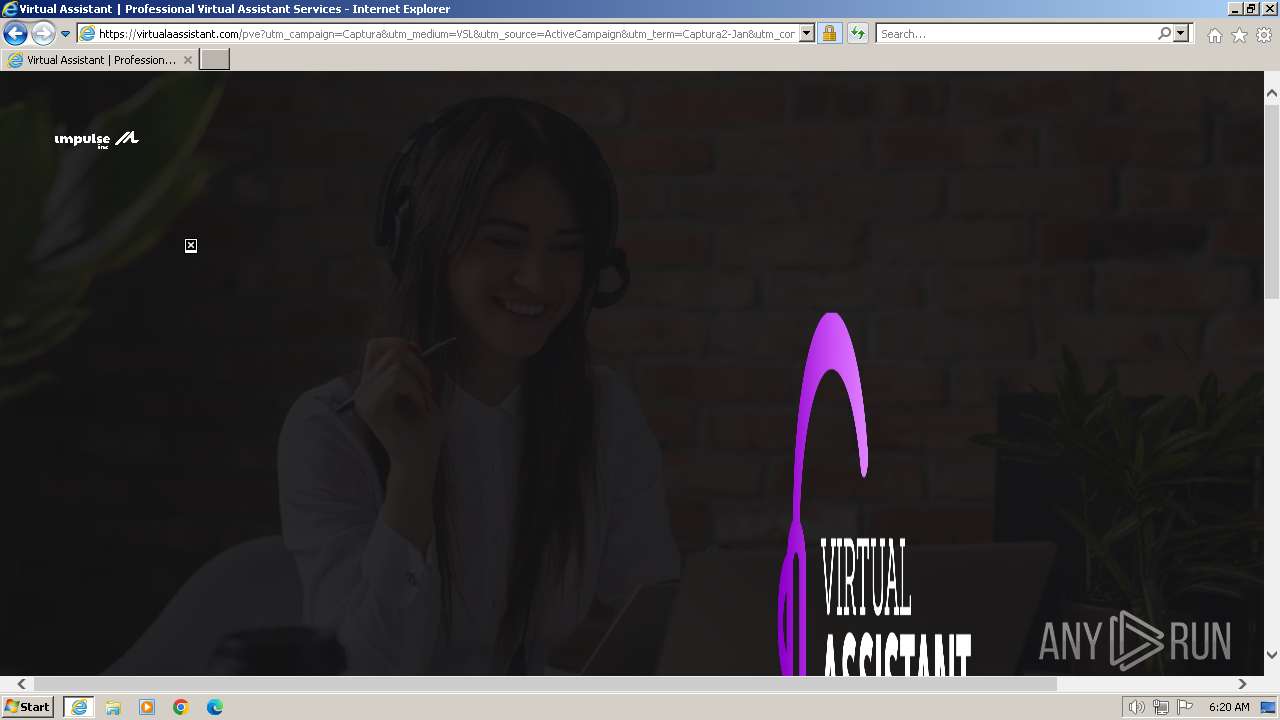
| 3240 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://connectfansus.lt.acemlna.com/Prod/link-tracker?redirectUrl=aHR0cHMlM0ElMkYlMkZwYWdhbWVudG8ub2dydXBvaW1wdWxzZS5jb20lMkZMR2tO&sig=HEz1yAE3AnqPuE1E5x2B85npNv9apJBriEfD1oZFcDeu&iat=1709127434&a=%7C%7C801579481%7C%7C&account=connectfansus.activehosted.com&email=RWpwN3ZZGJSMM3y4VAS9azF01WqVKzNpZVcpdrf6UFhM8Ew%3D%3AQ7K7ypPXKwbvTegOw5FKpT%2BzdPVOoq5N&s=be6ec883b9846ec07ebc65a9eb80278b&i=3875A4218A1A15249" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3916 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3240 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
28 753
Read events
28 589
Write events
120
Delete events
44
Modification events
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31091415 | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31091415 | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
58
Text files
56
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\83D863F495E7D991917B3ABB3E1EB382_1CF3CD648CFFE038A8327ADAF3322CD2 | der | |
MD5:12FE0A5E1A0F680A5DC722B9345EDEE0 | SHA256:79AA45DDAD19DB5544E8F3473244CD85FCC508AD8BDF38B794A458009F5B1000 | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | der | |
MD5:FD66ADDD22F049518BC196F28543DFC3 | SHA256:05ABB5EB90A022BE4B8BAEDC2B3118A19984179CFFEE2B66F27309717A791B70 | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_645BC4A49DCDC40FE5917FA45C6D4517 | binary | |
MD5:41AEA8163E6956B66E783889F2353318 | SHA256:699BE7BFEB9B64F78A3293DC2383C903D5ADBC8CF20B3E6452820CA93205F20E | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:B40C4FD2DD24A9A07FF85824E7CD5D4F | SHA256:FE5838C562EDD5E79D5D56D607B6DE565D7FCC96F3FADAD0D745B5406094EAFB | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\83D863F495E7D991917B3ABB3E1EB382_1CF3CD648CFFE038A8327ADAF3322CD2 | binary | |
MD5:3F53DF4ABB759A712DA258BE46F6ACCF | SHA256:03F374B0B6661F2B5EADFB4537185A8E2398EFBAF29B0F8420479364E8DC9FD9 | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\LGkN[1].htm | html | |
MD5:7DBA135789BC0E8E39E484E9548D895A | SHA256:57899AE9BDEA491FAC76BDE7A81614BDA37AFD49D119E418C58ABF1E4E19F7B9 | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_645BC4A49DCDC40FE5917FA45C6D4517 | der | |
MD5:109B095F52A39759254DFF4B002DFA03 | SHA256:7D84582B78964DF7820F831B550D69AD60E906CBA15166F0DC2B09F058B78004 | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFADC.tmp | compressed | |
MD5:753DF6889FD7410A2E9FE333DA83A429 | SHA256:B42DC237E44CBC9A43400E7D3F9CBD406DBDEFD62BFE87328F8663897D69DF78 | |||
| 3916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:45D25CDF11FF2D31AFA92052883A6B28 | SHA256:CBD3AF4EDA1BB97E5791B3EB7F3FD250EC2970CB6A6054F7276787B9A59D6949 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
50
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3916 | iexplore.exe | GET | 304 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f78d505714a595e3 | unknown | — | — | unknown |
3916 | iexplore.exe | GET | 304 | 23.32.238.226:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?545e1839169dd0e6 | unknown | — | — | unknown |
3916 | iexplore.exe | GET | 200 | 18.239.15.14:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | binary | 2.02 Kb | unknown |
3916 | iexplore.exe | GET | 200 | 18.65.41.80:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | binary | 1.49 Kb | unknown |
3916 | iexplore.exe | GET | 200 | 18.65.41.80:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkzUBtJnwJkc3SmanzgxeYU%3D | unknown | binary | 1.37 Kb | unknown |
3916 | iexplore.exe | GET | 200 | 18.239.62.218:80 | http://ocsp.r2m03.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQqHI%2BsdmapawQncL1rpCEZZ8gTSAQUVdkYX9IczAHhWLS%2Bq9lVQgHXLgICEARXBmF0edQaVZNxqATVgMU%3D | unknown | binary | 471 b | unknown |
3916 | iexplore.exe | GET | 200 | 23.32.238.226:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a08f35fbea17b647 | unknown | compressed | 67.5 Kb | unknown |
3916 | iexplore.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?fa310b6d6a2541a6 | unknown | compressed | 67.5 Kb | unknown |
3916 | iexplore.exe | GET | 200 | 23.32.238.226:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?86b4b67e50f1d6bf | unknown | compressed | 67.5 Kb | unknown |
3916 | iexplore.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3916 | iexplore.exe | 54.80.179.254:443 | connectfansus.lt.acemlna.com | AMAZON-AES | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3916 | iexplore.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3916 | iexplore.exe | 23.32.238.226:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3916 | iexplore.exe | 18.239.15.14:80 | o.ss2.us | — | US | unknown |
3916 | iexplore.exe | 18.65.41.80:80 | ocsp.rootg2.amazontrust.com | AMAZON-02 | US | unknown |
3916 | iexplore.exe | 18.239.62.218:80 | ocsp.r2m03.amazontrust.com | — | US | unknown |
3916 | iexplore.exe | 34.76.180.229:443 | pagamento.ogrupoimpulse.com | GOOGLE-CLOUD-PLATFORM | BE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectfansus.lt.acemlna.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.r2m03.amazontrust.com |
| unknown |
pagamento.ogrupoimpulse.com |
| unknown |
x1.c.lencr.org |
| whitelisted |
virtualaassistant.com |
| unknown |
api.bing.com |
| whitelisted |