| File name: | 795ee57d.7z |
| Full analysis: | https://app.any.run/tasks/64ddd268-7798-4bd7-bdbb-b898159db74c |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 04:30:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.3 |
| MD5: | 6BBD9796986921E54324AB2ACC621567 |
| SHA1: | 5843DB4801A83B170CF23277DFC03F0D877296E0 |
| SHA256: | 359B171EB488E4E403AC43DC59A08F2CD9BE549904B6A3560368879B8F03C76B |
| SSDEEP: | 1536:bc/BTt66hbmSRqmjVEPF2jbCj+h/hYScMvzJE:aBTPb1q6XCCFhBe |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 2692)
- Explorer.EXE (PID: 764)
- svchost.exe (PID: 2060)
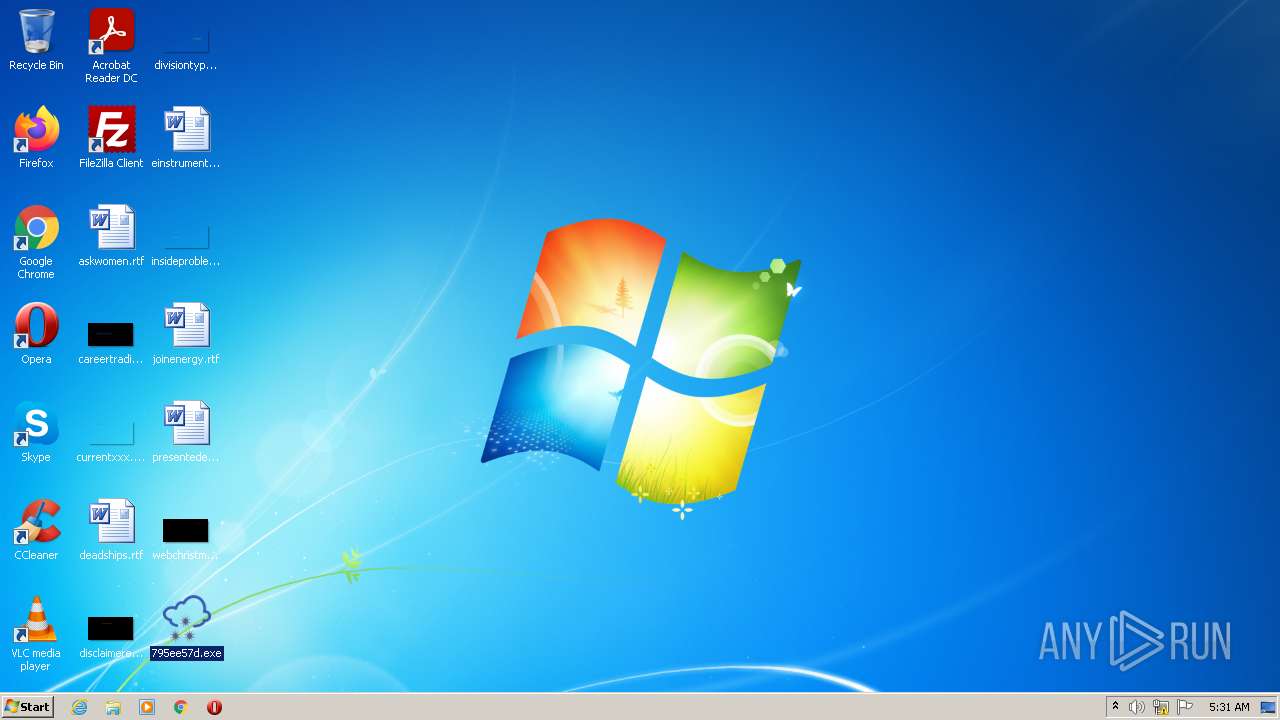
Application was dropped or rewritten from another process
- 795ee57d.exe (PID: 1616)
- 795ee57d.exe (PID: 520)
Runs injected code in another process
- explorer.exe (PID: 3096)
Application was injected by another process
- Explorer.EXE (PID: 764)
Uses SVCHOST.EXE for hidden code execution
- Explorer.EXE (PID: 764)
Changes the login/logoff helper path in the registry
- svchost.exe (PID: 2060)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 2692)
Checks supported languages
- WinRAR.exe (PID: 2692)
- 795ee57d.exe (PID: 1616)
- 795ee57d.exe (PID: 520)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2692)
- svchost.exe (PID: 2060)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2692)
- Explorer.EXE (PID: 764)
- svchost.exe (PID: 2060)
Application launched itself
- 795ee57d.exe (PID: 1616)
Creates files in the user directory
- svchost.exe (PID: 2060)
INFO
Manual execution by user
- 795ee57d.exe (PID: 1616)
- svchost.exe (PID: 2060)
Checks supported languages
- explorer.exe (PID: 3096)
- svchost.exe (PID: 2060)
Reads the computer name
- svchost.exe (PID: 2060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (gen) (100) |
|---|
Total processes
39
Monitored processes
6
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | "c:\users\admin\desktop\795ee57d.exe" | c:\users\admin\desktop\795ee57d.exe | — | 795ee57d.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 764 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1616 | "C:\Users\admin\Desktop\795ee57d.exe" | C:\Users\admin\Desktop\795ee57d.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2060 | "C:\Windows\system32\svchost.exe" | C:\Windows\system32\svchost.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
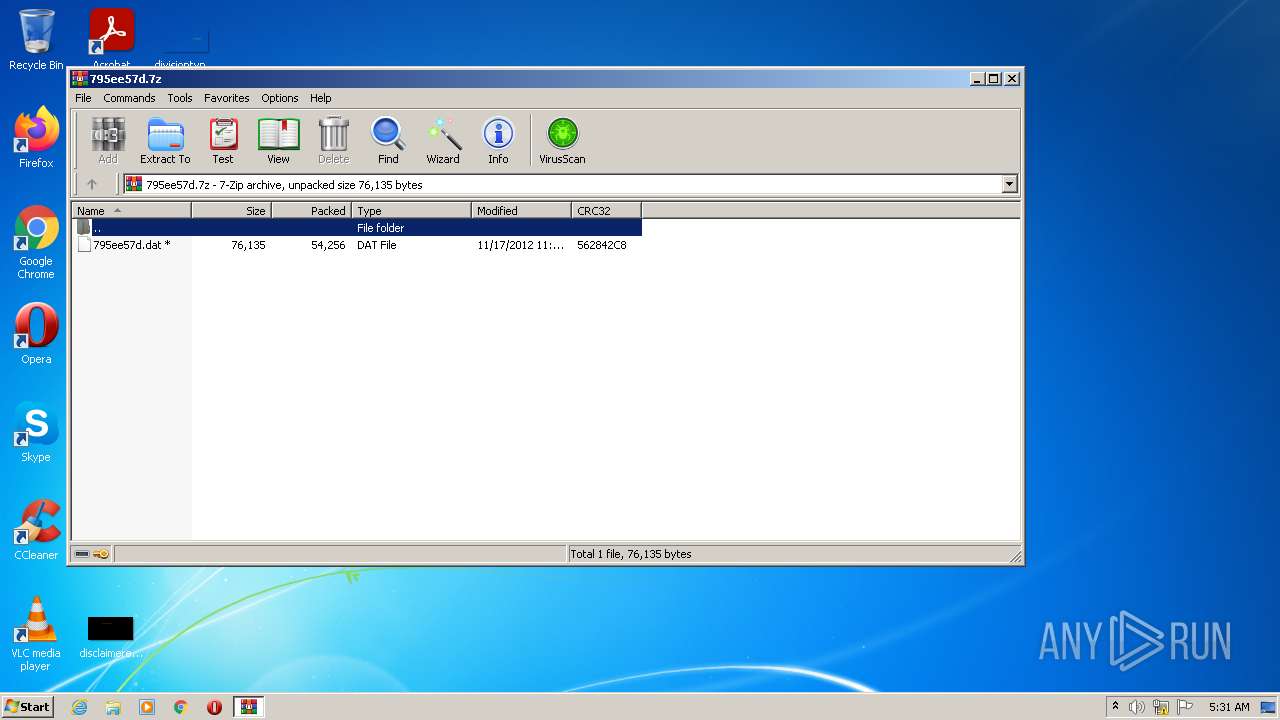
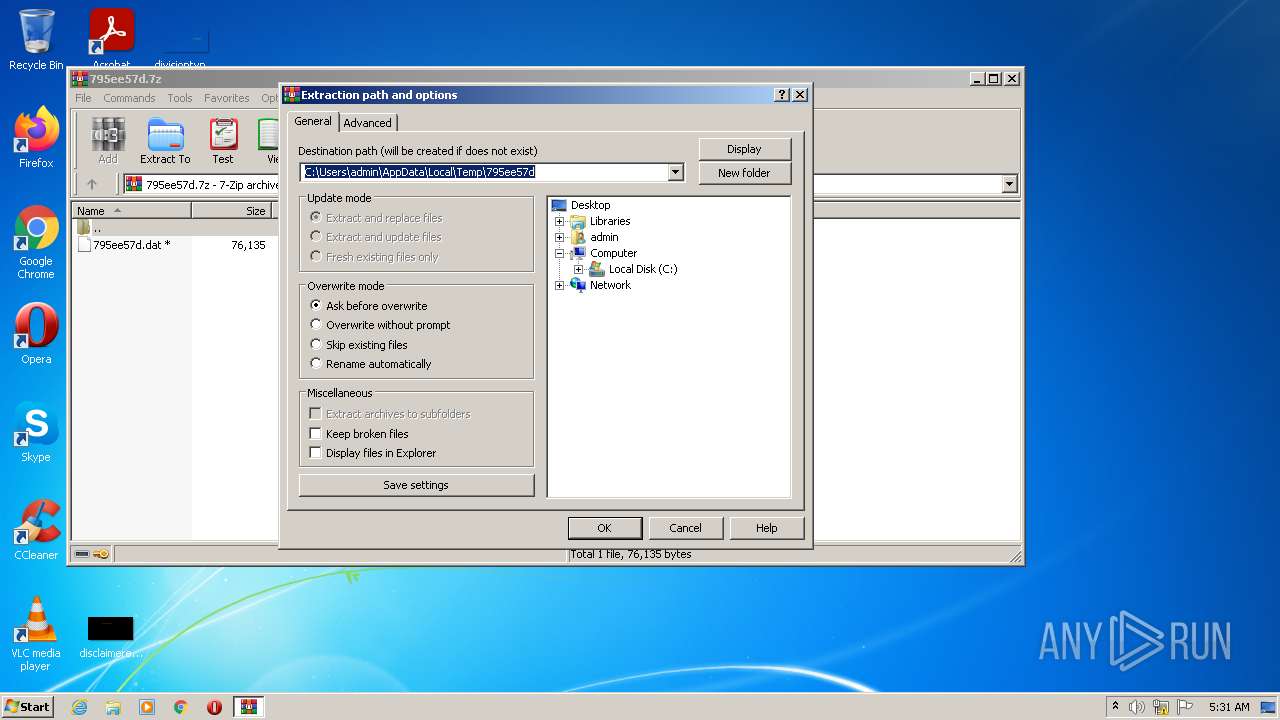
| 2692 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\795ee57d.7z" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3096 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | 795ee57d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 337
Read events
3 275
Write events
62
Delete events
0
Modification events
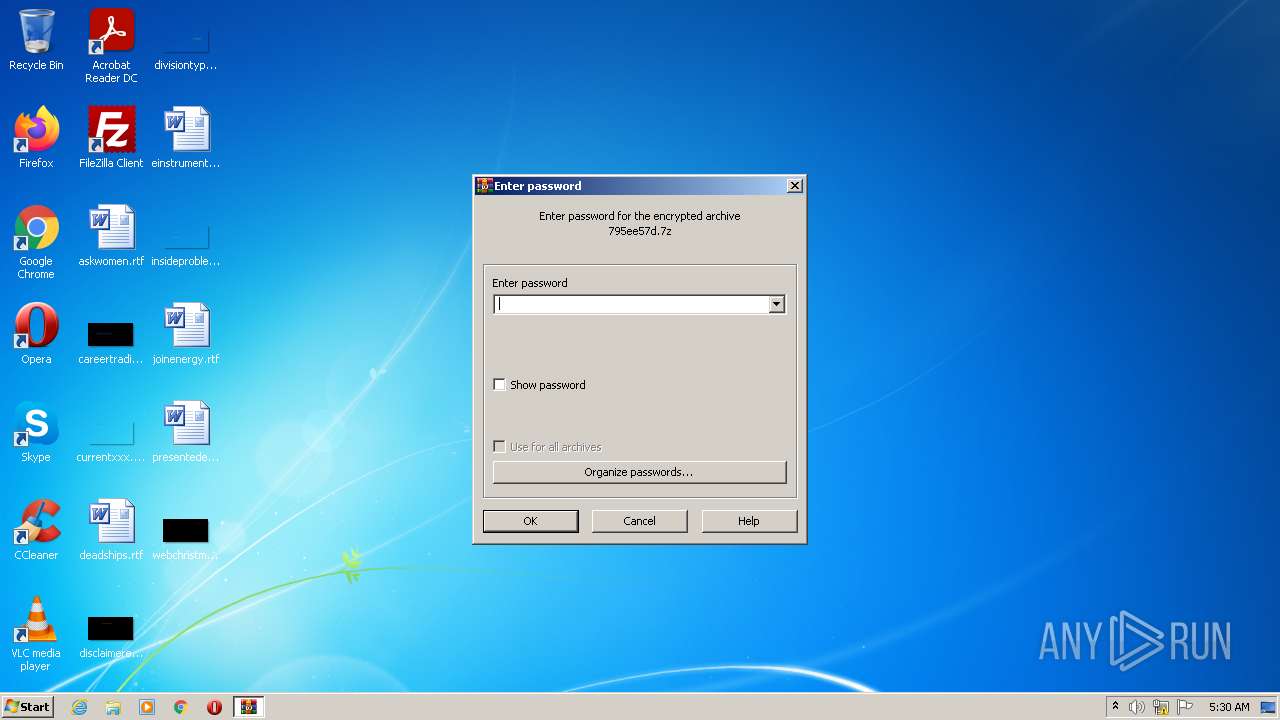
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (764) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\795ee57d.7z | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
0
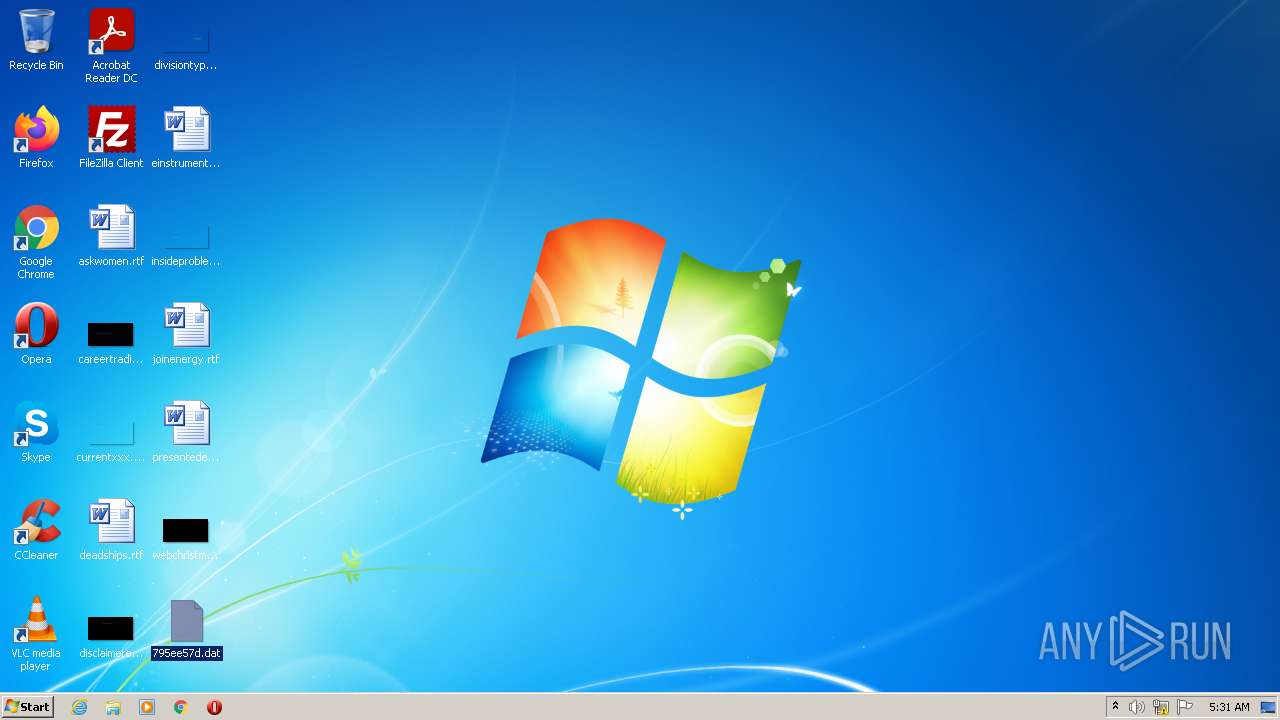
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2692 | WinRAR.exe | C:\Users\admin\Desktop\795ee57d.dat | executable | |
MD5:— | SHA256:— | |||
| 764 | Explorer.EXE | C:\Users\admin\Desktop\795ee57d.exe | executable | |
MD5:— | SHA256:— | |||
| 2060 | svchost.exe | C:\Users\admin\AppData\Roaming\msconfig.dat | executable | |
MD5:— | SHA256:— | |||
| 2060 | svchost.exe | C:\Users\admin\AppData\Roaming\msconfig.ini | binary | |
MD5:9D8D888BB7B09FA4A054AD6DF5C6A6F9 | SHA256:CA5D4975E6FC36BD0B1B978AA09E380CE847009C071BB1B42FDBD1900AD1297C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
2
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
hhrbn.ru |
| malicious |
rnmbe.su |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |