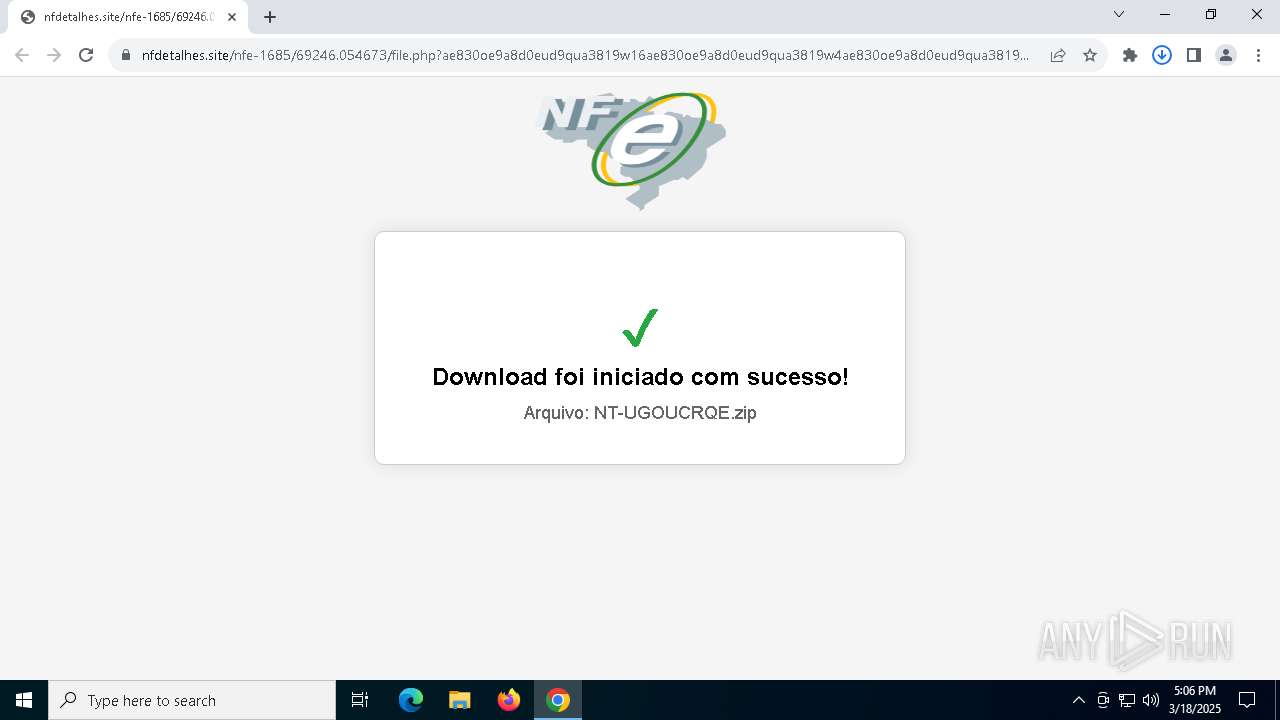
| URL: | https://nf-374416423576.us-central1.run.app/ |
| Full analysis: | https://app.any.run/tasks/544d05fe-54c0-45e4-8edf-a2b4cb0802cf |
| Verdict: | Malicious activity |
| Analysis date: | March 18, 2025, 17:05:18 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 03E632BE375E1E7BDF8342F137E6F7B3 |
| SHA1: | E6D919C5C90EA645B196E98E1A7844A9E6A927B7 |
| SHA256: | 3599108E14D0DF1303D952238BB4A0D1C6CEC8C3EFAFFA685515C88841649F5B |
| SSDEEP: | 3:N8IAQQSwN1d/Kn:2uQ/VK |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 3268)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 3268)
SUSPICIOUS
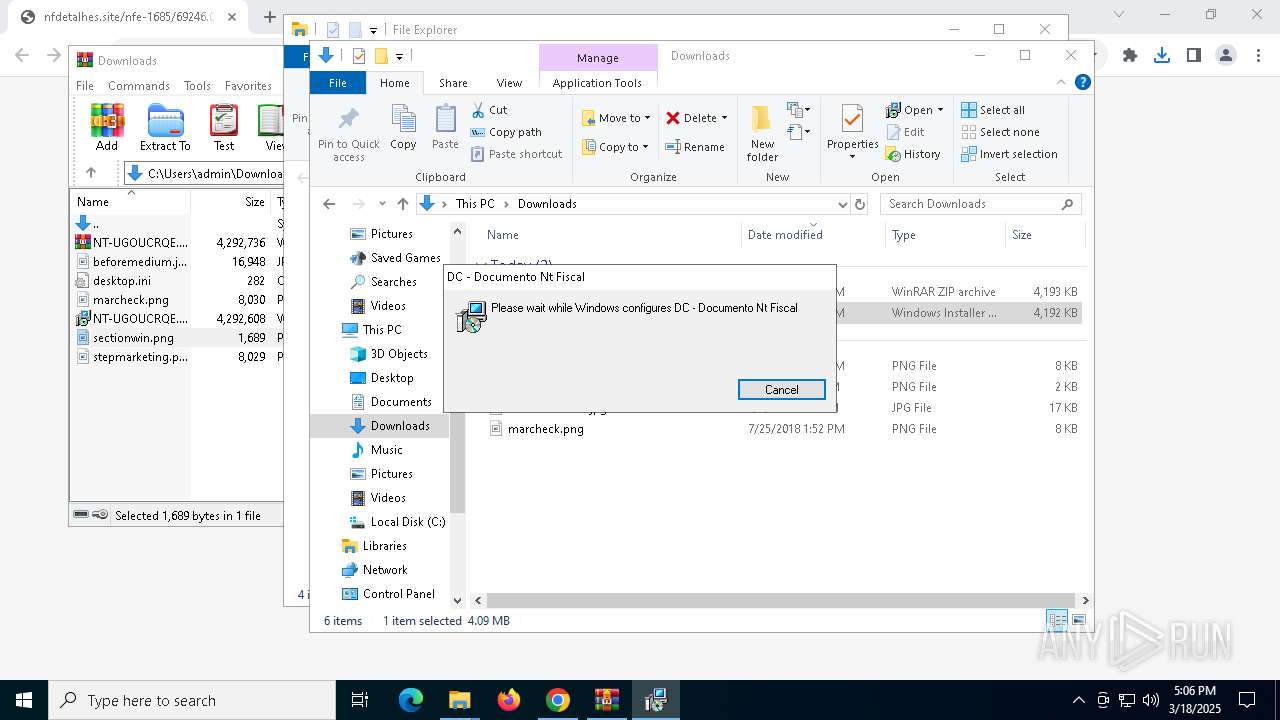
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1452)
Reads security settings of Internet Explorer
- MSIE499.tmp (PID: 4220)
Starts CMD.EXE for commands execution
- MSIE499.tmp (PID: 4220)
- cmd.exe (PID: 872)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3140)
Application launched itself
- cmd.exe (PID: 872)
Likely accesses (executes) a file from the Public directory
- powershell.exe (PID: 3268)
- powershell.exe (PID: 8184)
Downloads file from URI via Powershell
- powershell.exe (PID: 3268)
Found IP address in command line
- powershell.exe (PID: 3268)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 8184)
Connects to the server without a host name
- powershell.exe (PID: 3268)
Executable content was dropped or overwritten
- powershell.exe (PID: 8184)
Executing commands from a ".bat" file
- cmd.exe (PID: 872)
- MSIE499.tmp (PID: 4220)
Process drops python dynamic module
- powershell.exe (PID: 8184)
INFO
Reads the computer name
- msiexec.exe (PID: 1452)
- msiexec.exe (PID: 7656)
- MSIE499.tmp (PID: 4220)
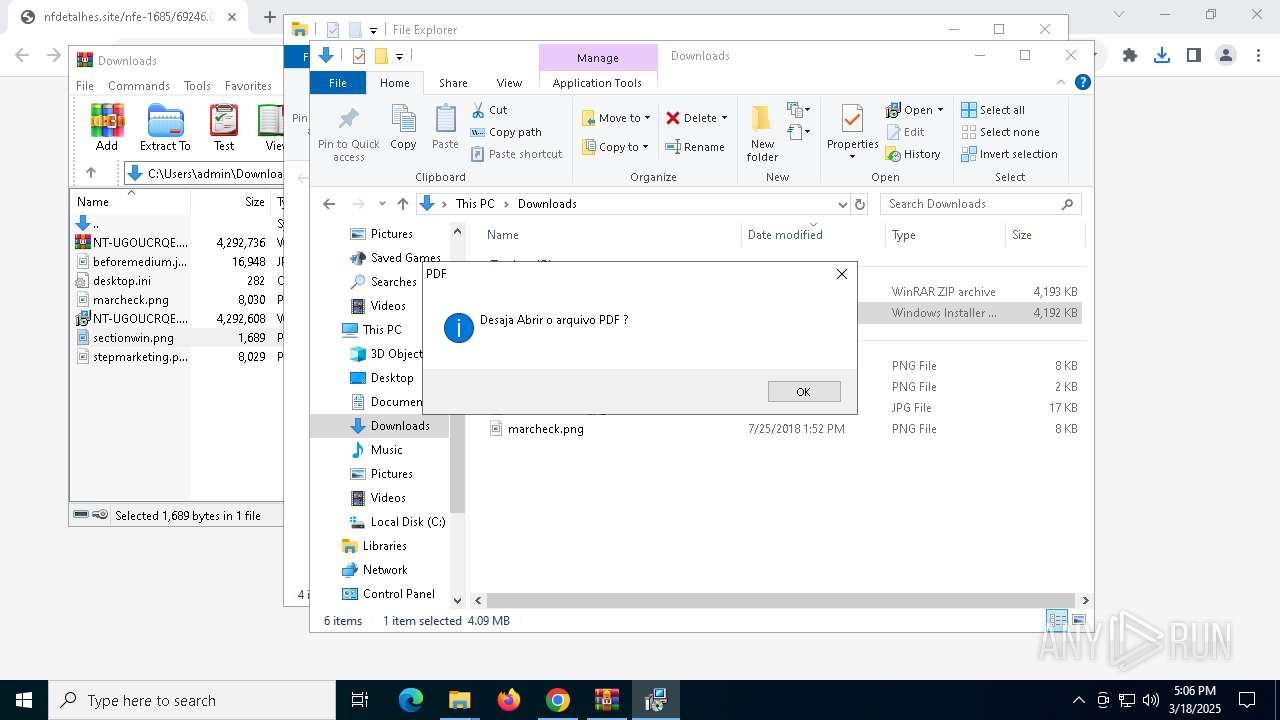
Application launched itself
- chrome.exe (PID: 7188)
- Acrobat.exe (PID: 1324)
- AcroCEF.exe (PID: 8100)
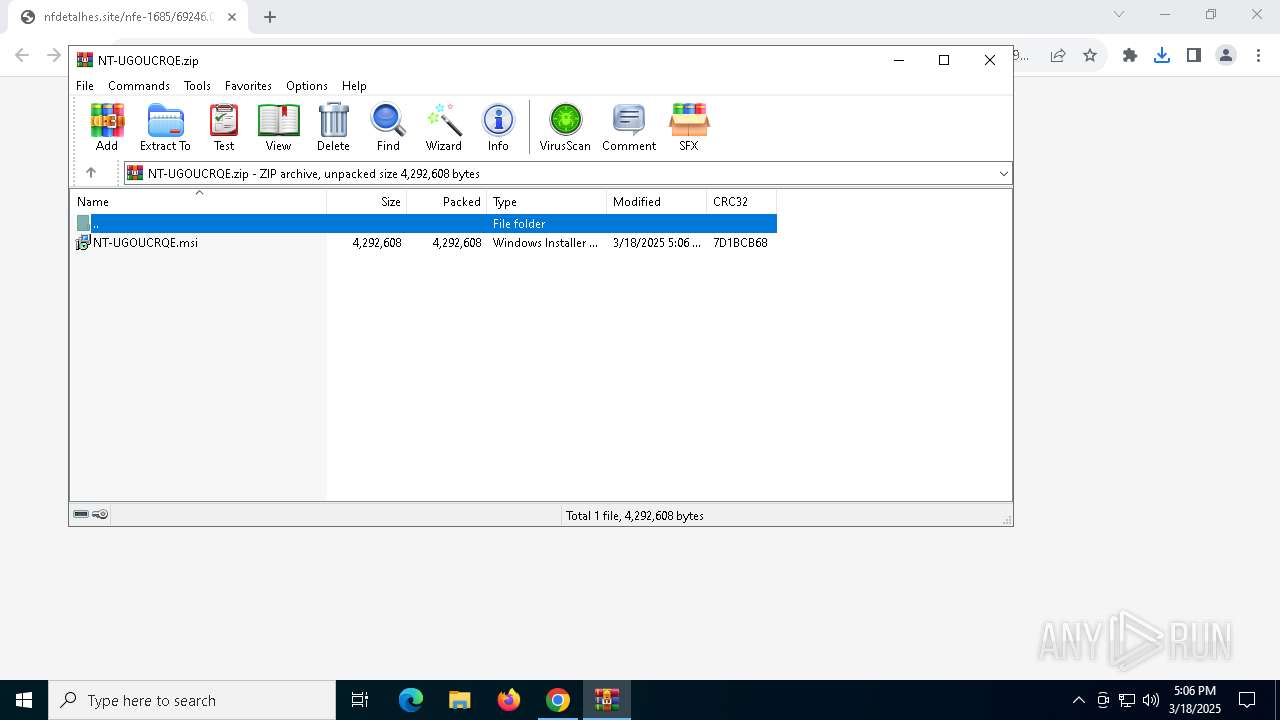
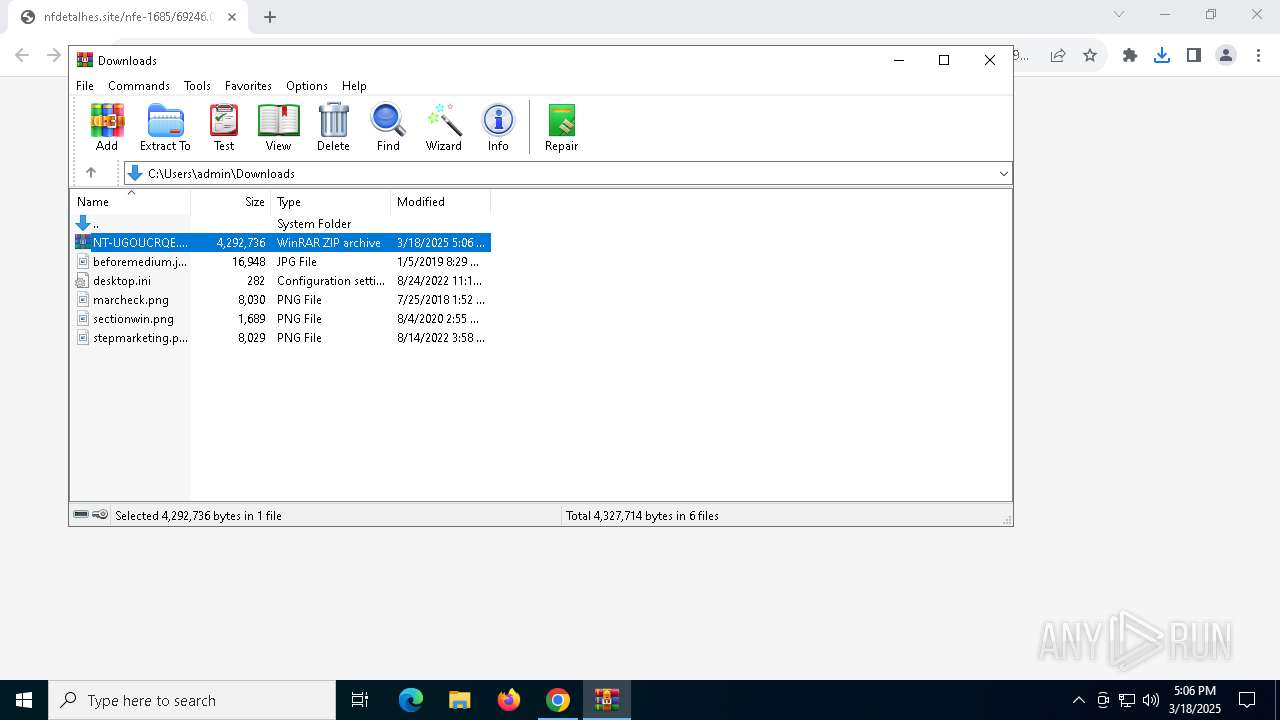
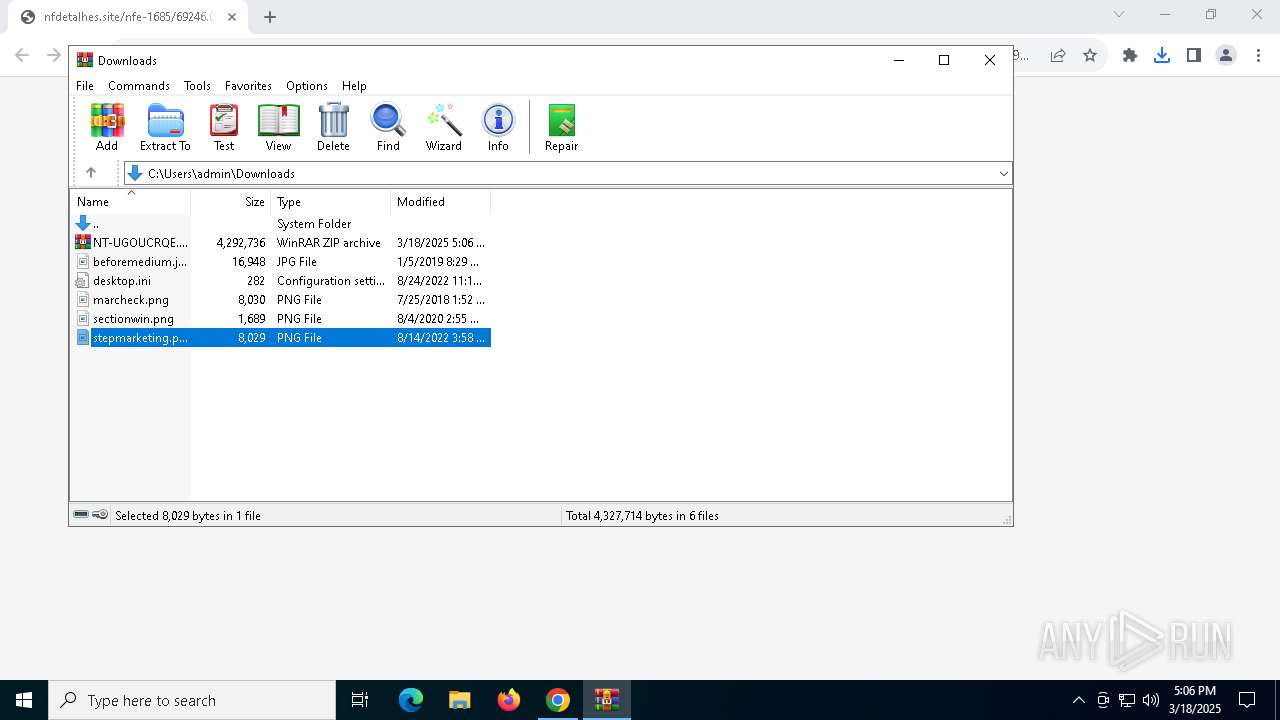
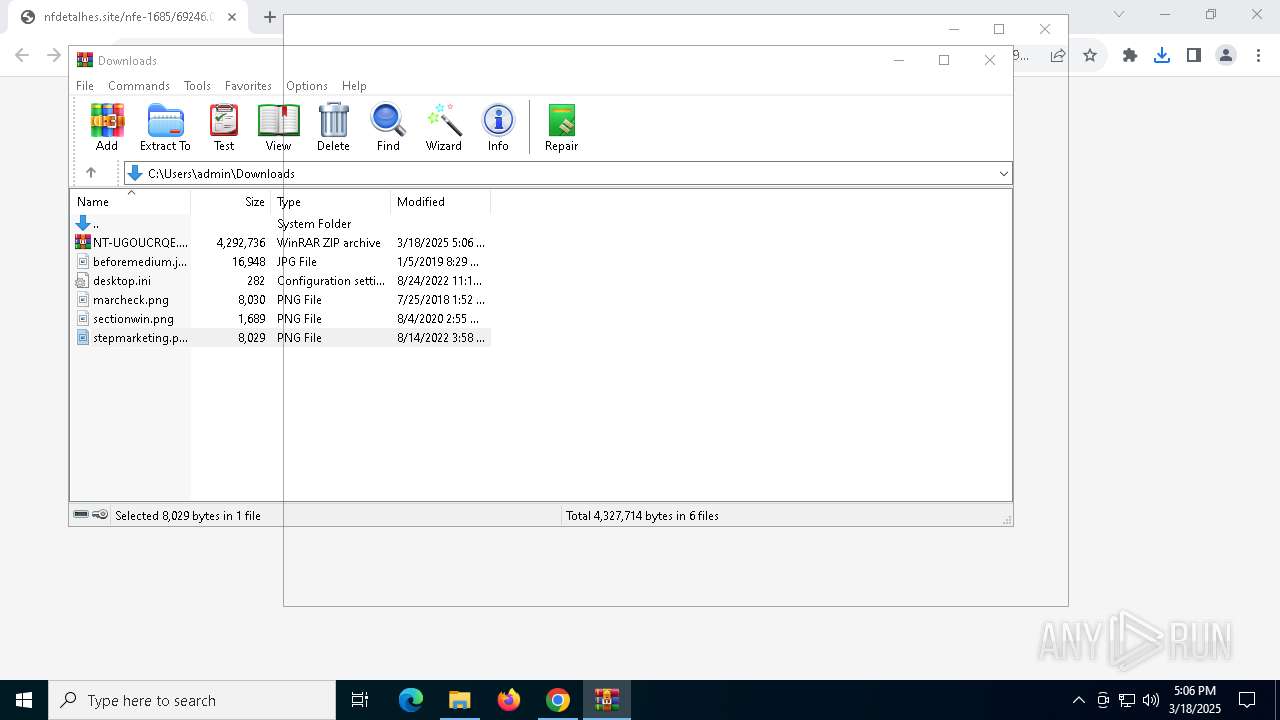
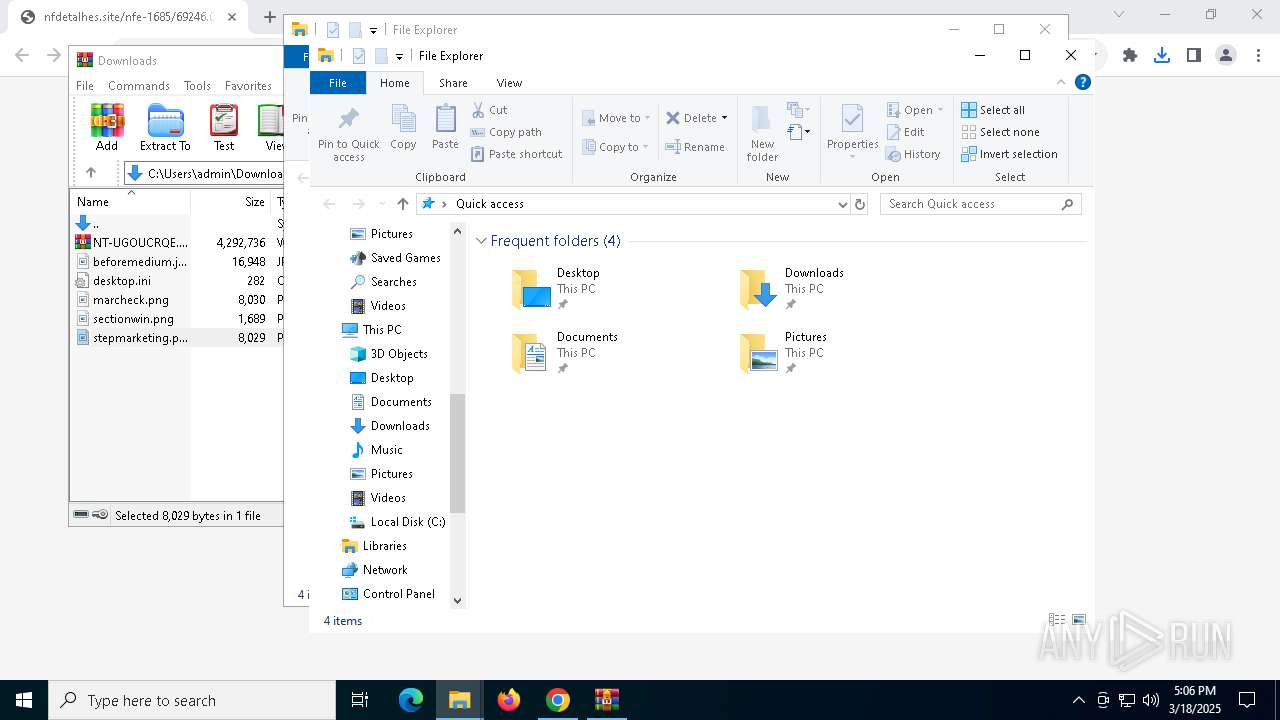
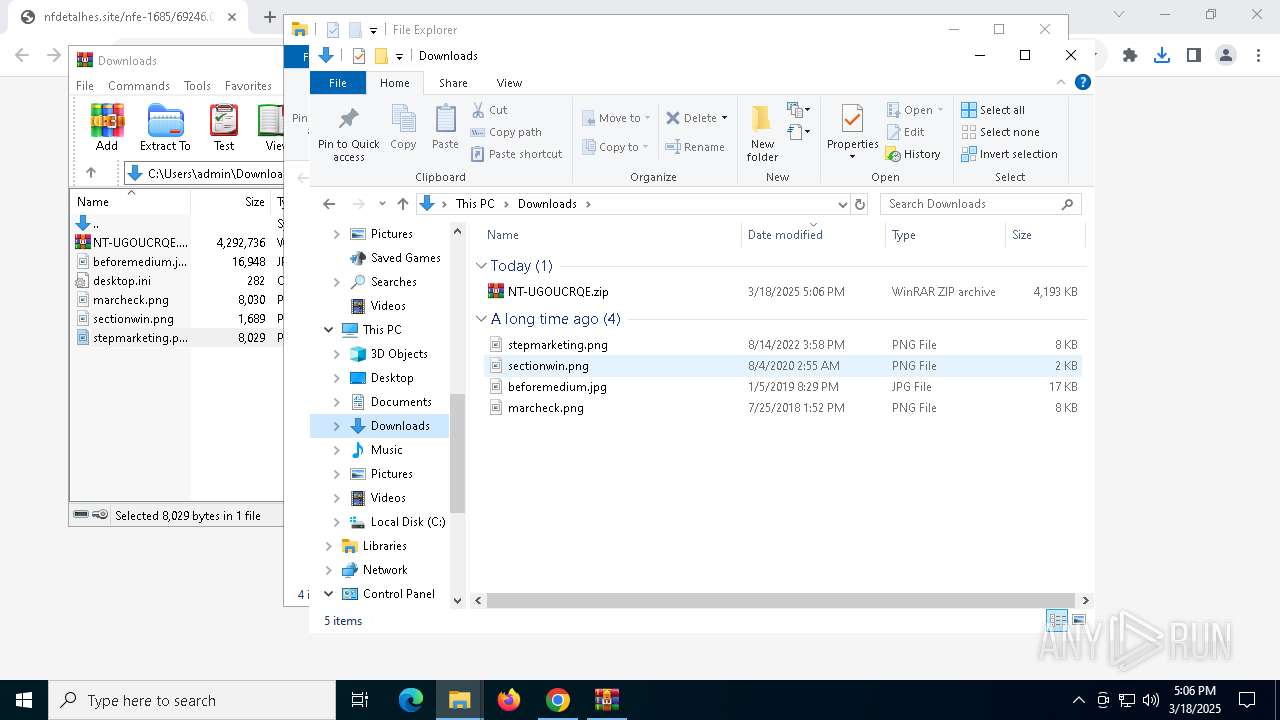
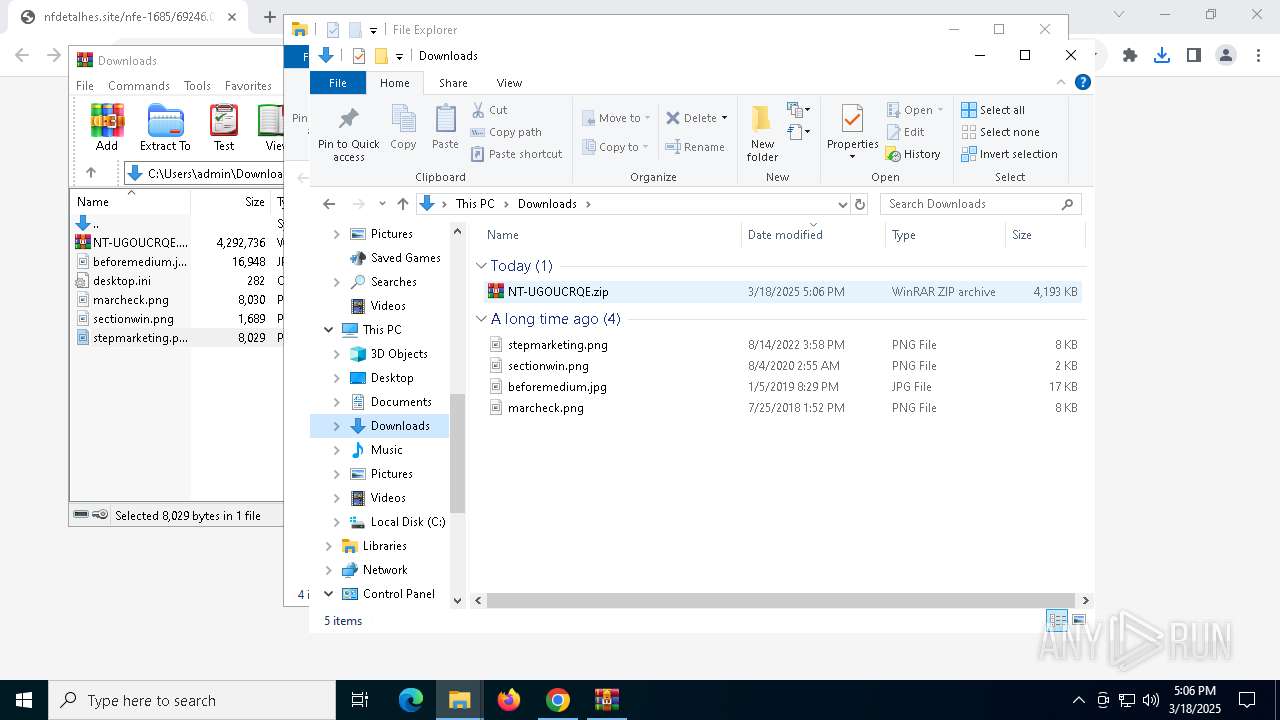
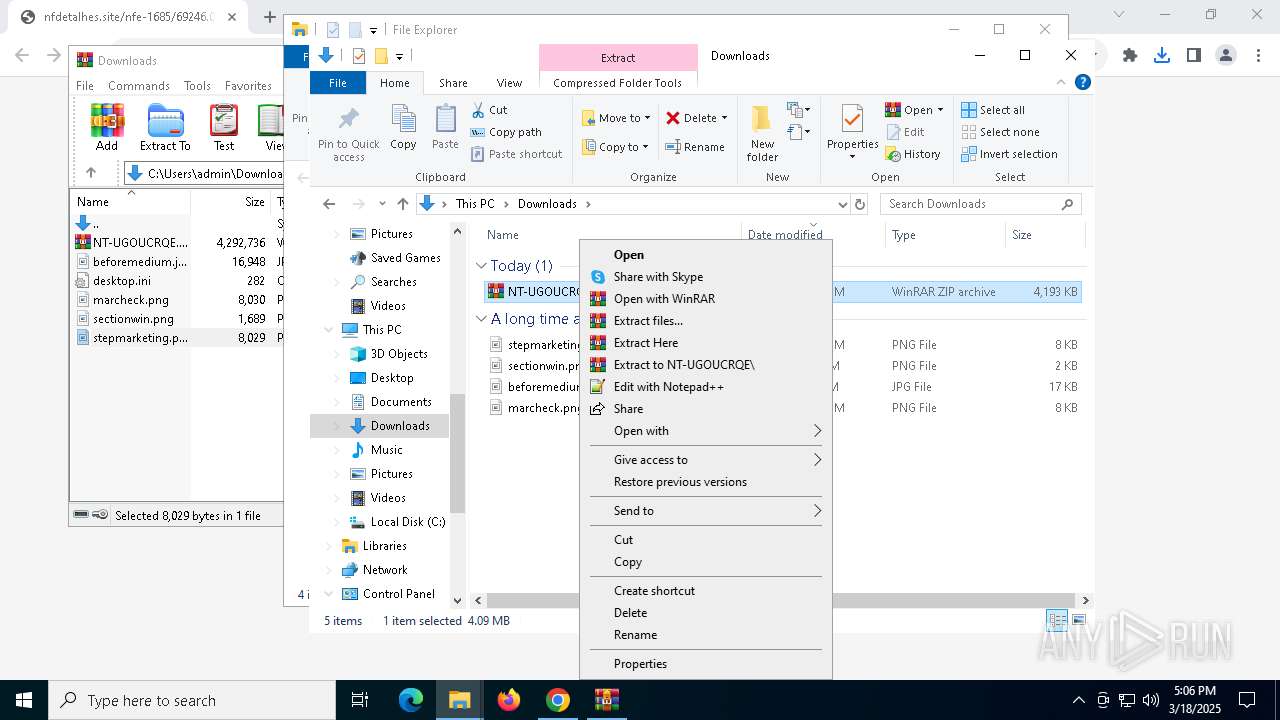
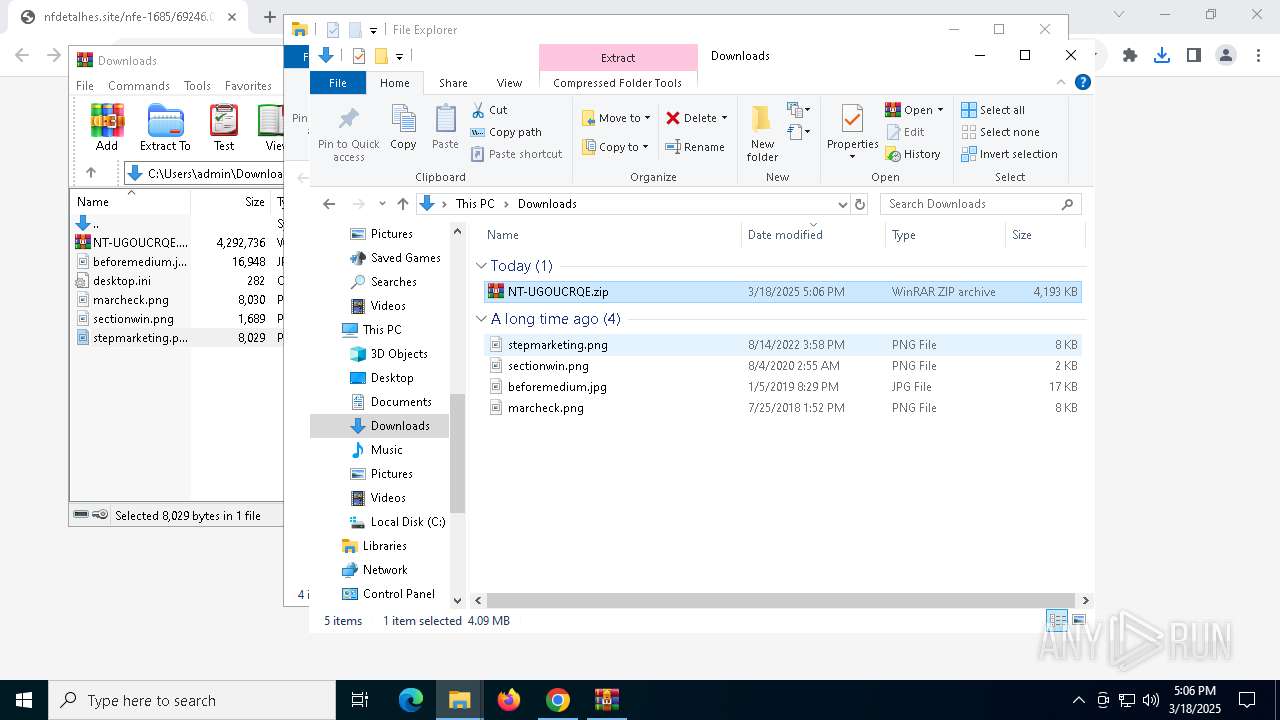
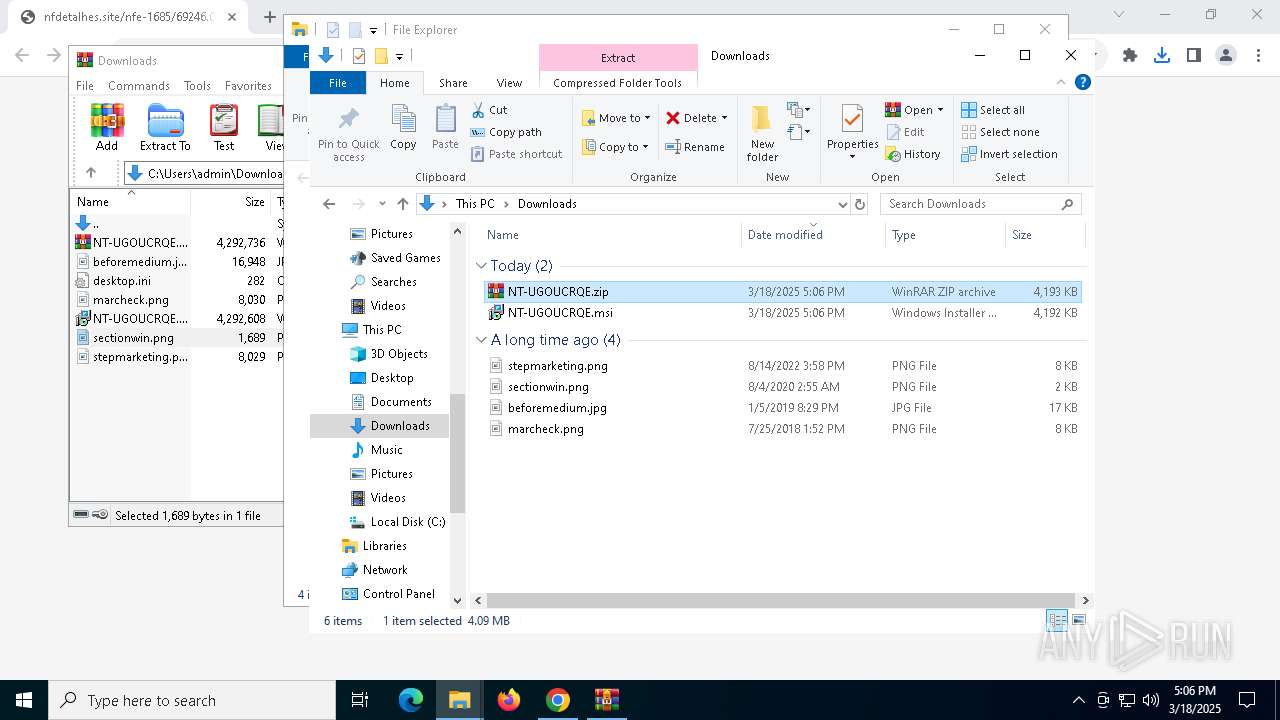
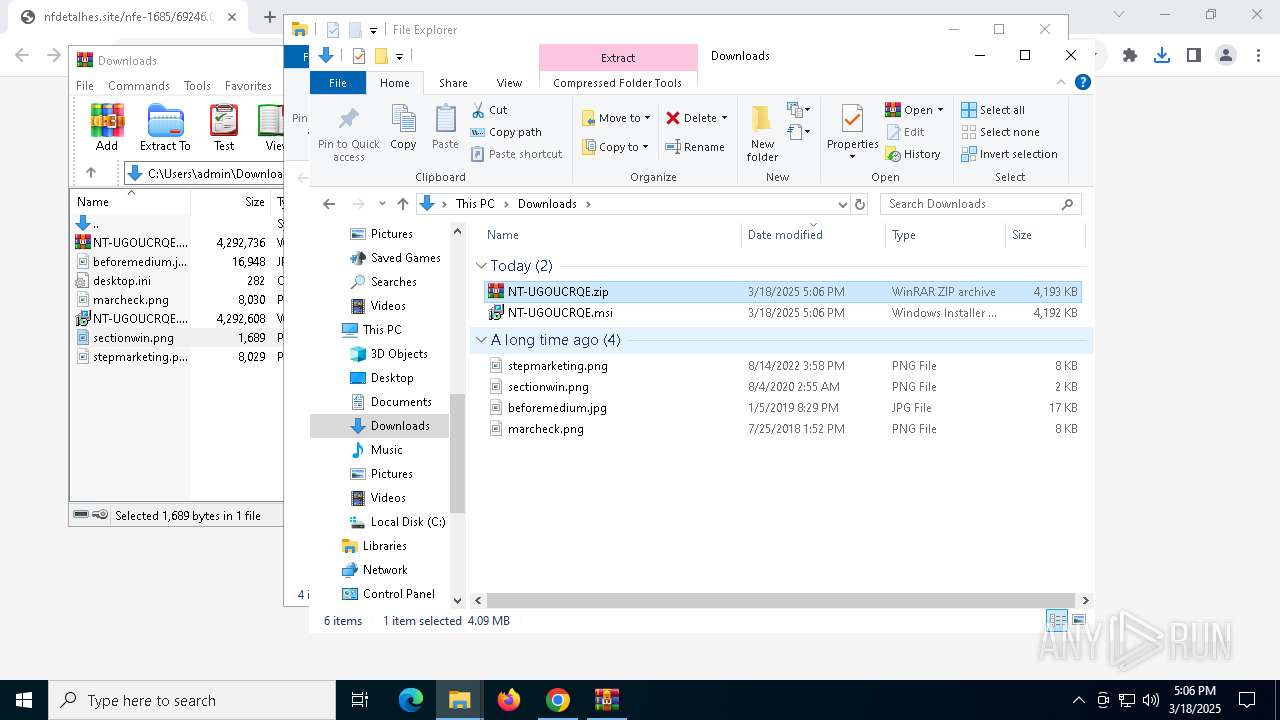
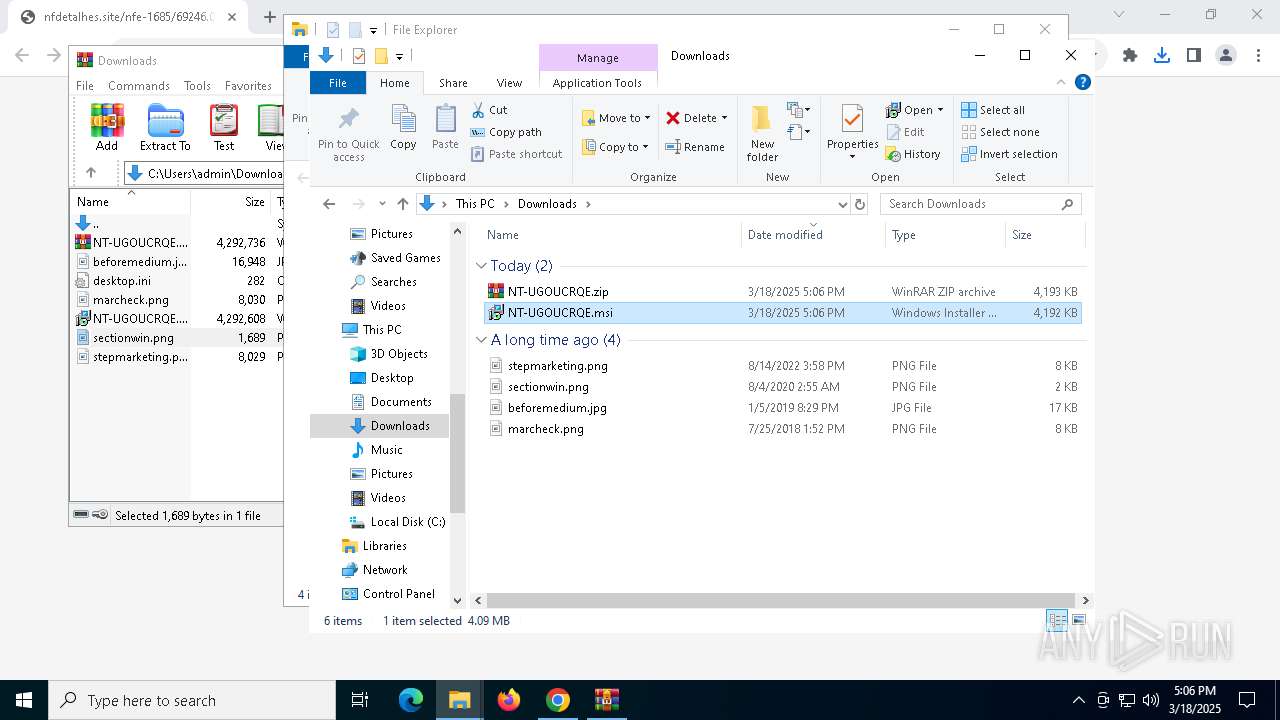
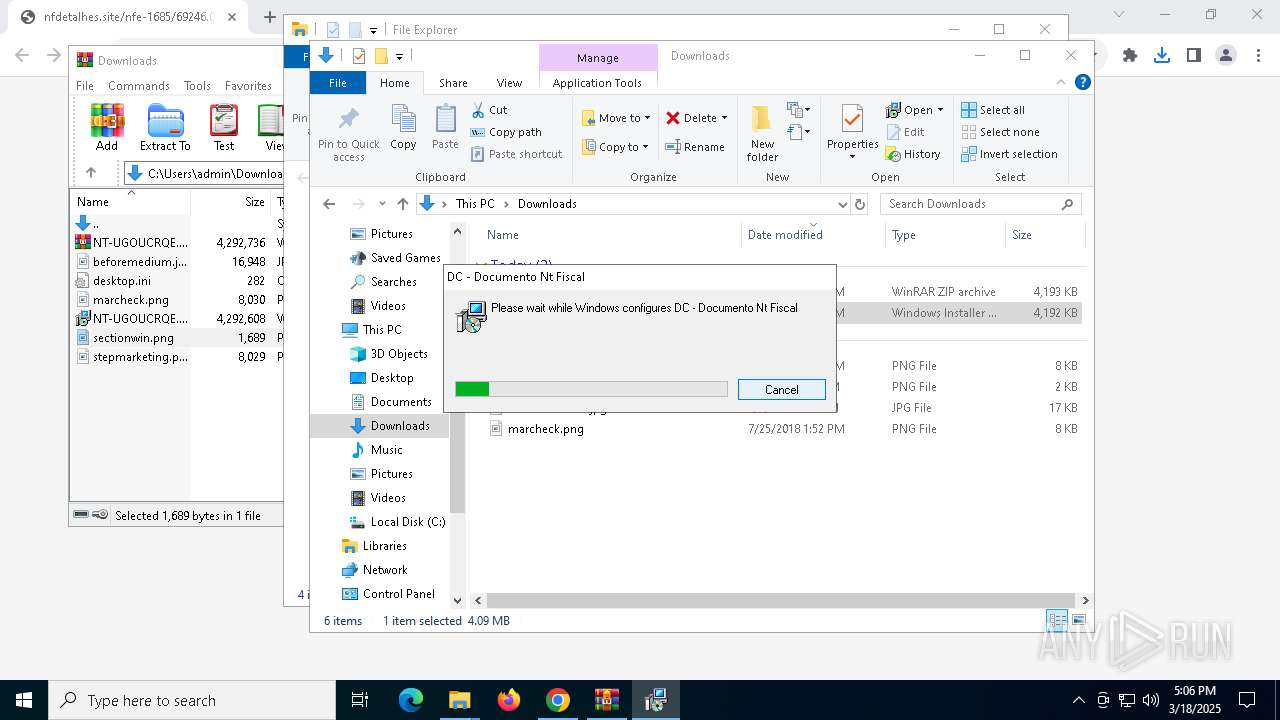
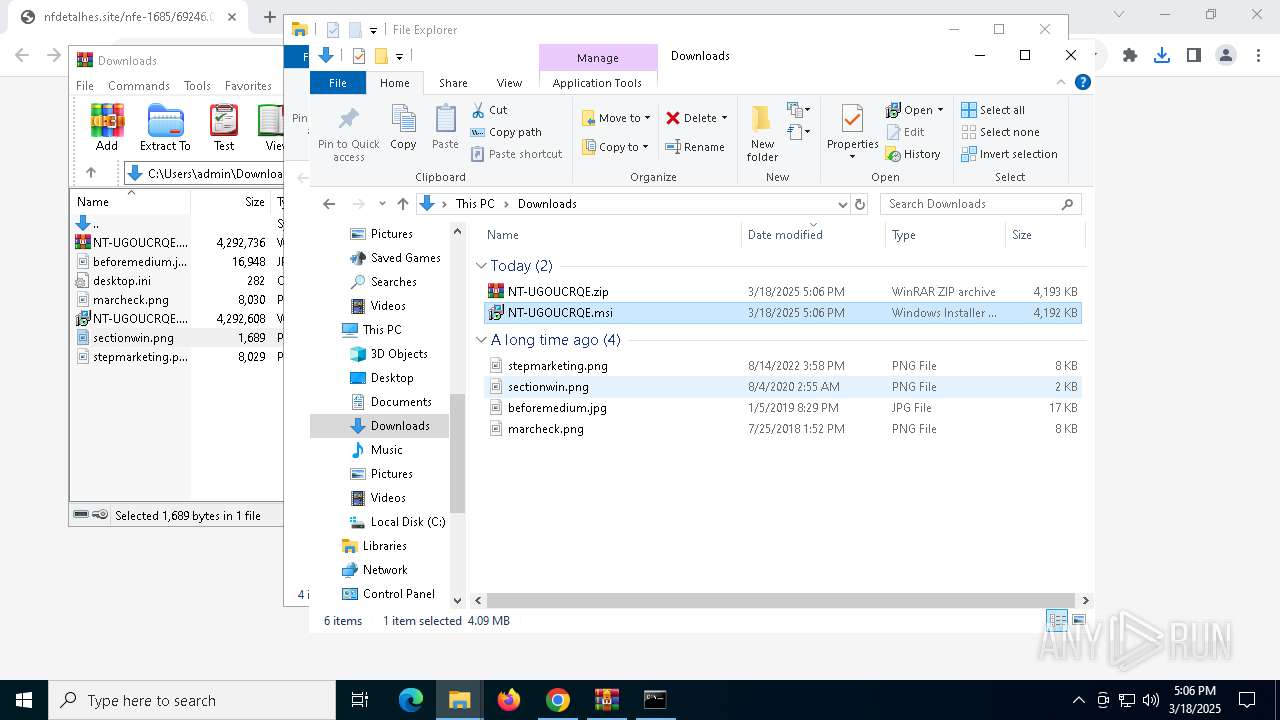
Manual execution by a user
- WinRAR.exe (PID: 1600)
- msiexec.exe (PID: 7908)
Checks supported languages
- msiexec.exe (PID: 1452)
- msiexec.exe (PID: 7656)
- UnRar.exe (PID: 1196)
- MSIE499.tmp (PID: 4220)
Reads the software policy settings
- slui.exe (PID: 7968)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1452)
Reads Environment values
- msiexec.exe (PID: 7656)
Creates files or folders in the user directory
- msiexec.exe (PID: 1452)
- UnRar.exe (PID: 1196)
The sample compiled with english language support
- msiexec.exe (PID: 1452)
- powershell.exe (PID: 8184)
Creates a software uninstall entry
- msiexec.exe (PID: 1452)
Starts application with an unusual extension
- msiexec.exe (PID: 1452)
Process checks computer location settings
- MSIE499.tmp (PID: 4220)
Disables trace logs
- powershell.exe (PID: 3268)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8184)
Checks proxy server information
- powershell.exe (PID: 3268)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
189
Monitored processes
45
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5192 --field-trial-handle=1892,i,12990523102418271474,2039870284484148701,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UnRar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\Dirtech\DC - Documento Nt Fiscal\gestune.bat" " | C:\Windows\SysWOW64\cmd.exe | — | MSIE499.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 9009 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3772 --field-trial-handle=1892,i,12990523102418271474,2039870284484148701,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1196 | "C:\Users\admin\AppData\Roaming\Dirtech\DC - Documento Nt Fiscal\UnRar.exe" x -p"df3164" -o+ "C:\Users\admin\AppData\Roaming\Dirtech\DC - Documento Nt Fiscal\gestune.rar" "C:\Users\admin\AppData\Roaming\Dirtech\DC - Documento Nt Fiscal\" | C:\Users\admin\AppData\Roaming\Dirtech\DC - Documento Nt Fiscal\UnRar.exe | — | msiexec.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: Command line RAR Exit code: 0 Version: 7.1.0 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5224 --field-trial-handle=1892,i,12990523102418271474,2039870284484148701,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
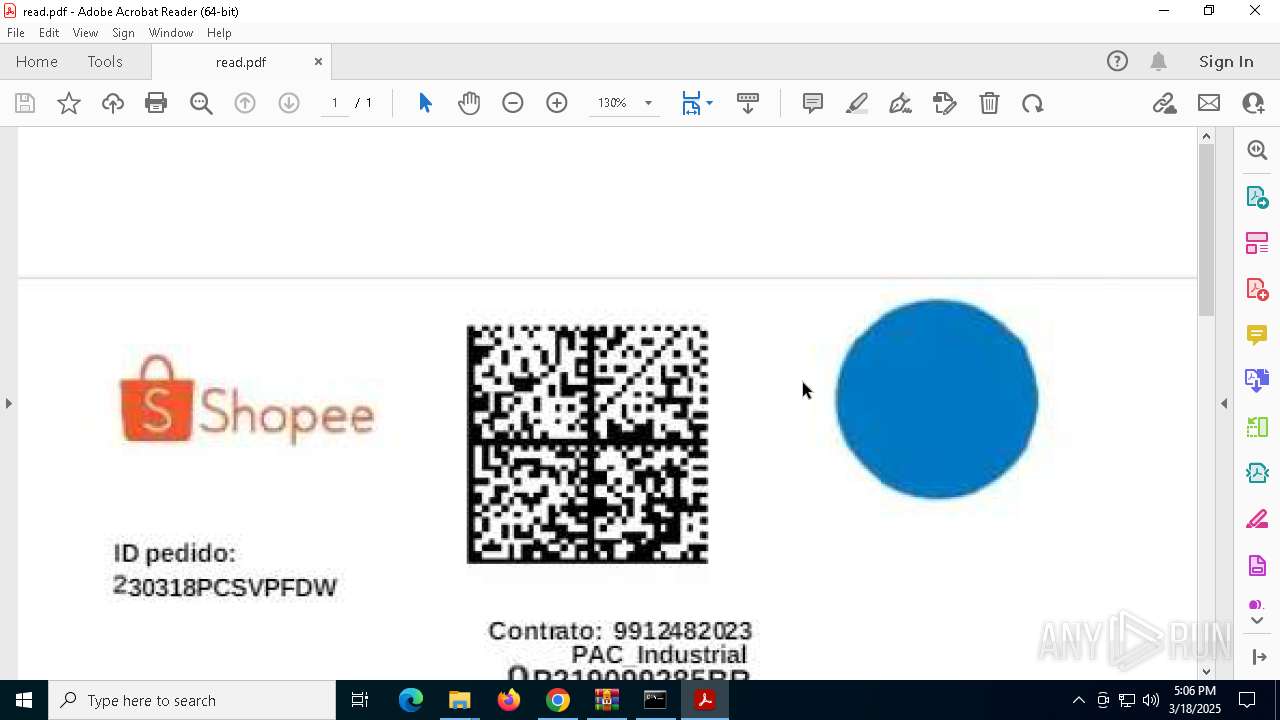
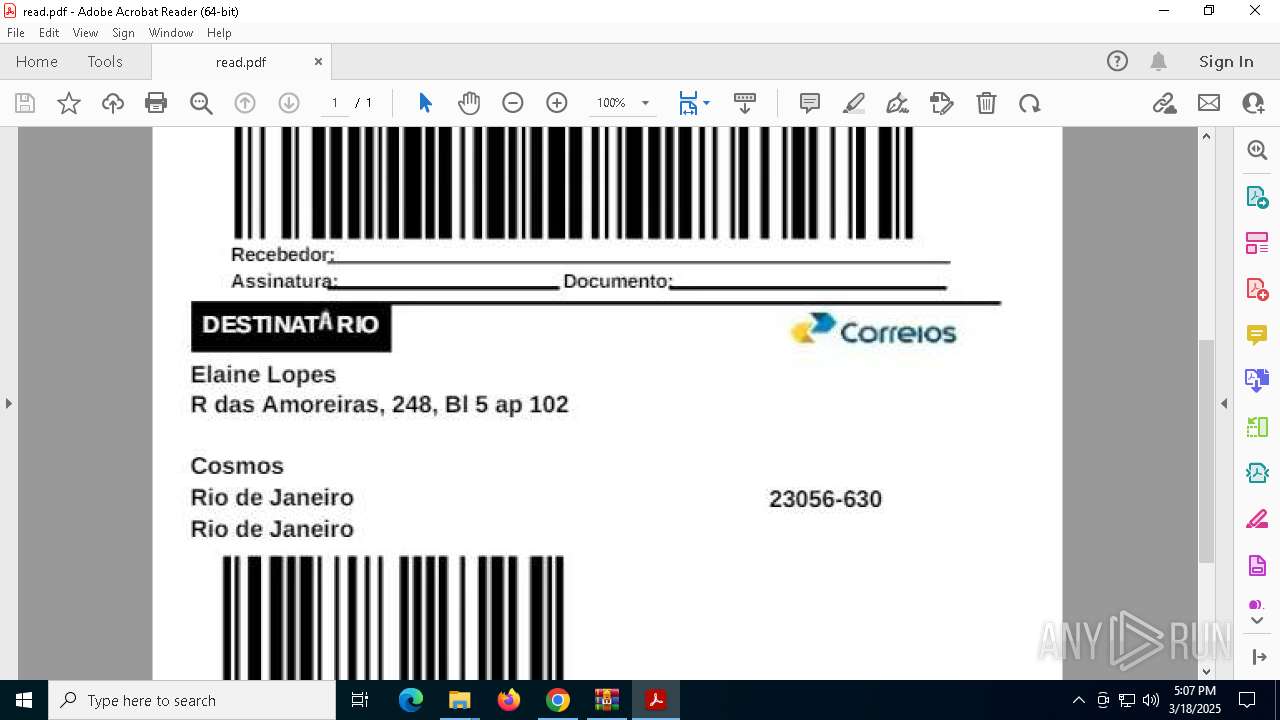
| 1324 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" "C:\Users\admin\AppData\Roaming\Dirtech\DC - Documento Nt Fiscal\read.pdf" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | cmd.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Version: 23.1.20093.0 Modules
| |||||||||||||||
| 1452 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2136 --field-trial-handle=1620,i,5374438436958326184,8087348915263271465,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:8 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | AcroCEF.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Version: 23.1.20093.0 Modules
| |||||||||||||||
Total events
34 090
Read events
33 834
Write events
239
Delete events
17
Modification events
| (PID) Process: | (7188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7188) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5608) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000F678DA0A2898DB01 | |||
| (PID) Process: | (7188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (5008) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5008) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5008) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
47
Suspicious files
325
Text files
409
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c2f4.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c304.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c304.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c304.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c304.TMP | — | |
MD5:— | SHA256:— | |||
| 7188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c304.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
49
DNS requests
38
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
516 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
3268 | powershell.exe | GET | 200 | 192.210.226.143:80 | http://192.210.226.143/Python312-32.zip | unknown | — | — | unknown |
516 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adp7lmscefogeldj4te6xerqth3a_9.55.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.55.0_all_ocm7dvbavb37zglvqhfr5kszse.crx3 | unknown | — | — | whitelisted |
516 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/fry5e54ngknffszxh4ipkqah54_2025.3.17.1/jflhchccmppkfebkiaminageehmchikm_2025.03.17.01_all_adygv2ryqk6vdlseborkn66aocfq.crx3 | unknown | — | — | whitelisted |
516 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
1324 | Acrobat.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | unknown | — | — | whitelisted |
516 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/fry5e54ngknffszxh4ipkqah54_2025.3.17.1/jflhchccmppkfebkiaminageehmchikm_2025.03.17.01_all_adygv2ryqk6vdlseborkn66aocfq.crx3 | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7760 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4268 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.48.23.141:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.141:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7188 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7416 | chrome.exe | 108.177.96.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7416 | chrome.exe | 216.239.36.53:443 | nf-374416423576.us-central1.run.app | GOOGLE | US | unknown |
7416 | chrome.exe | 104.21.64.1:443 | nfdetalhes.site | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
nf-374416423576.us-central1.run.app |
| unknown |
accounts.google.com |
| whitelisted |
nfdetalhes.site |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7416 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7416 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
3268 | powershell.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
3268 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |