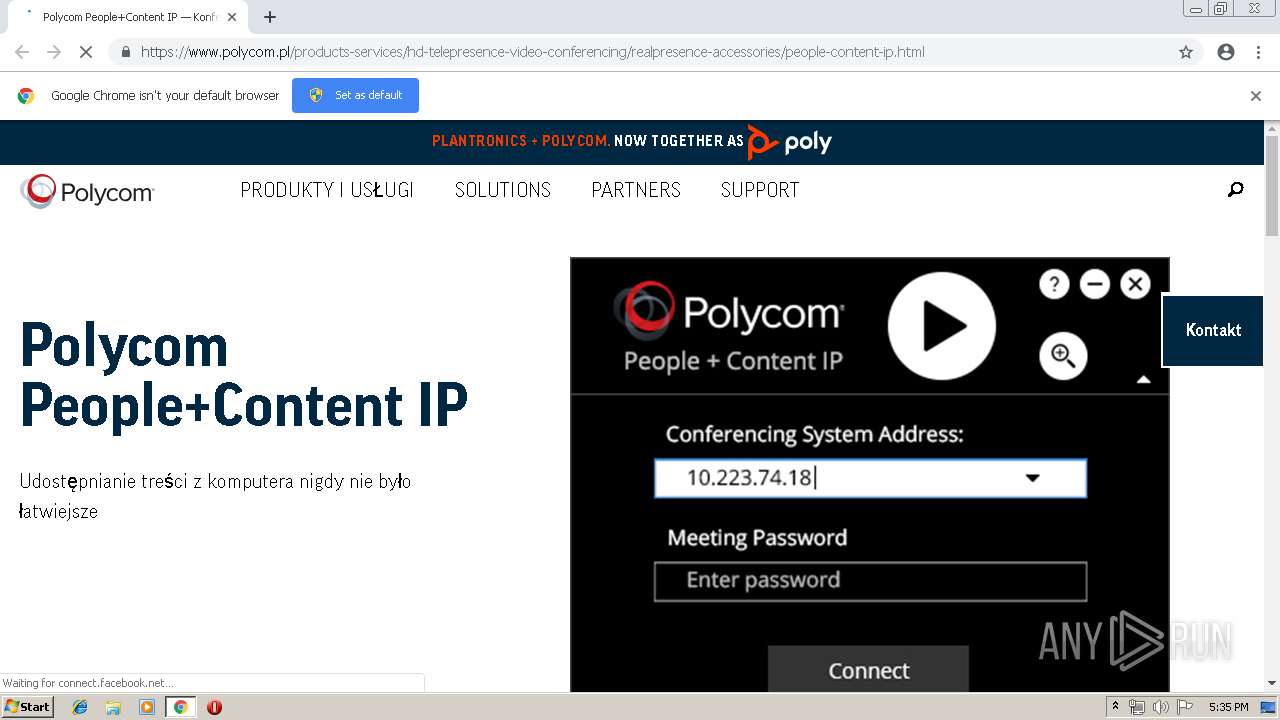
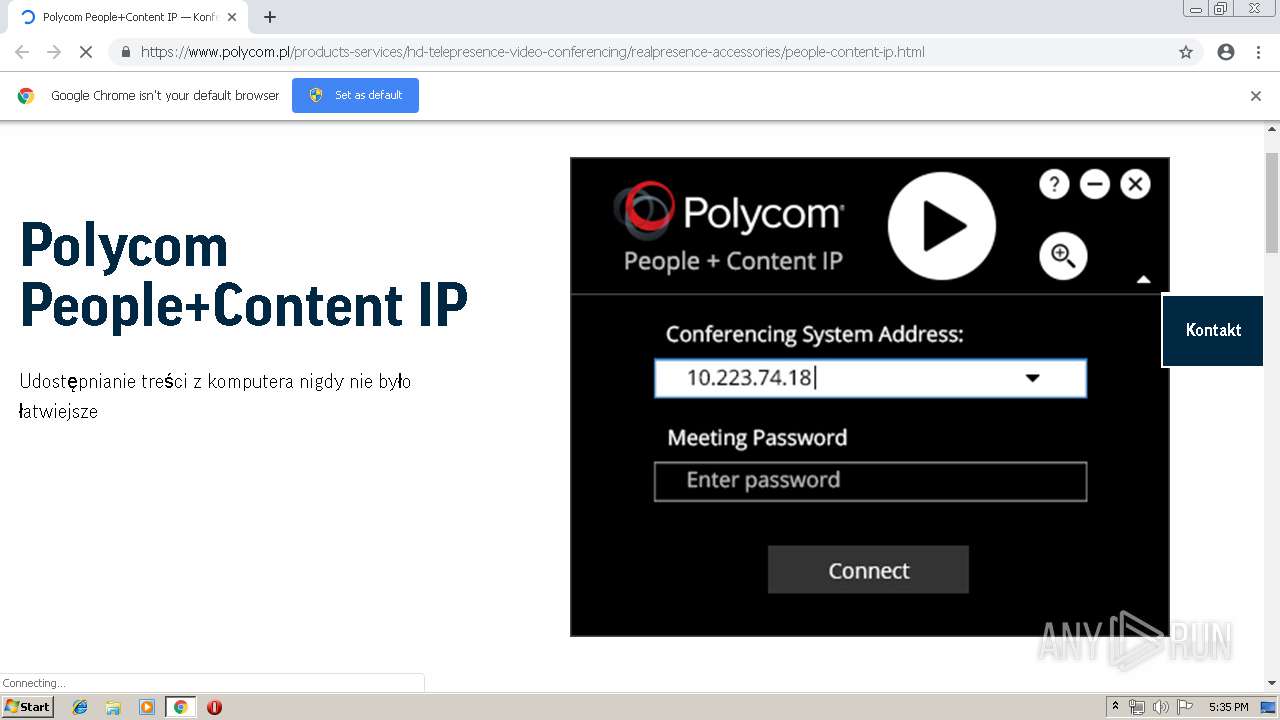
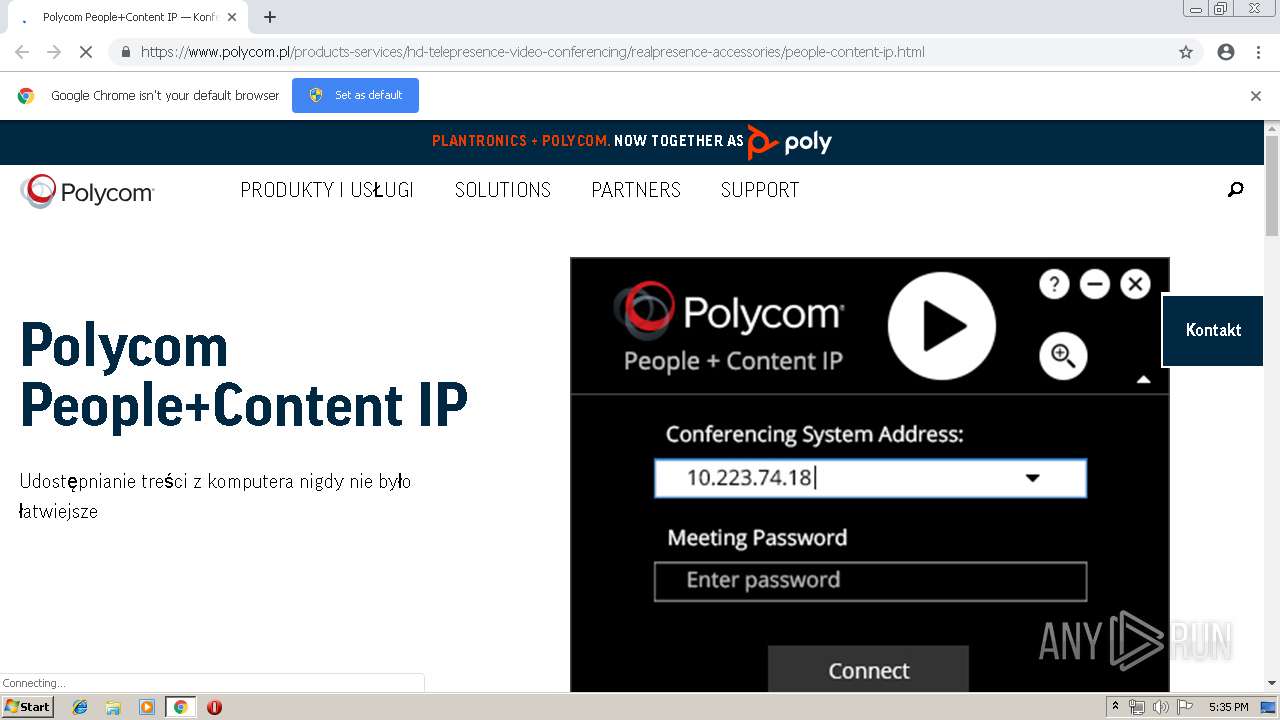
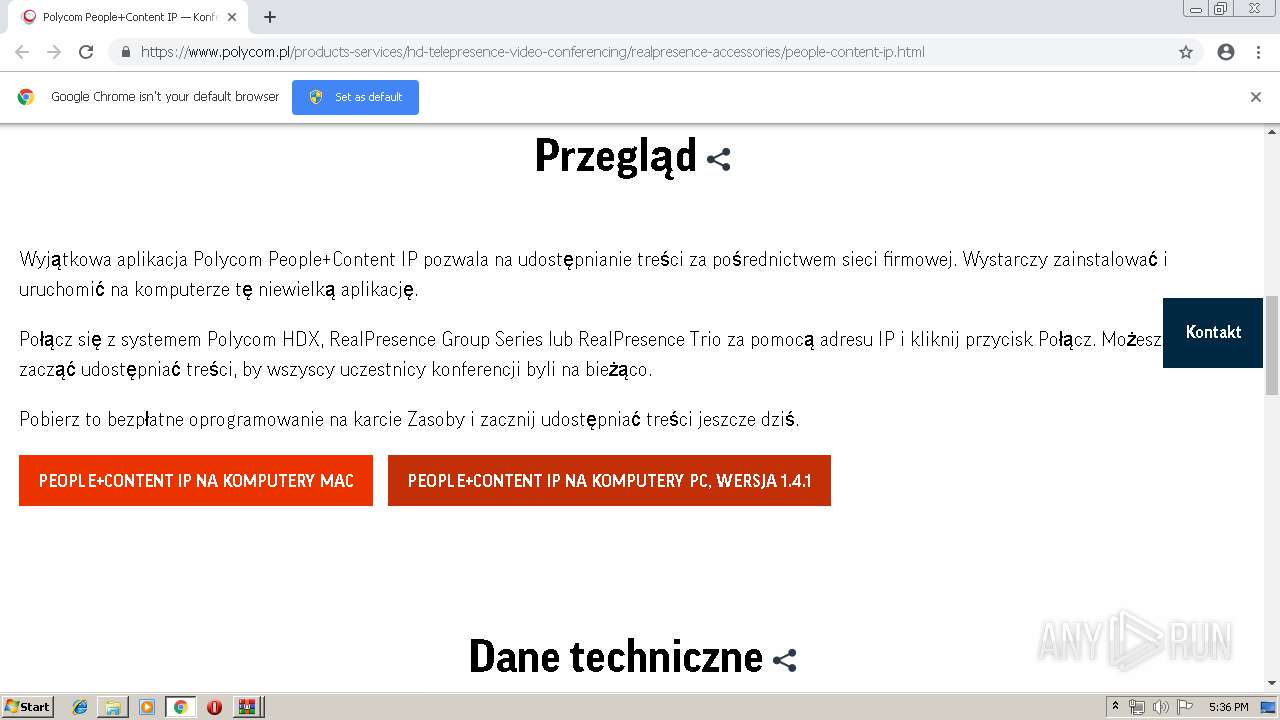
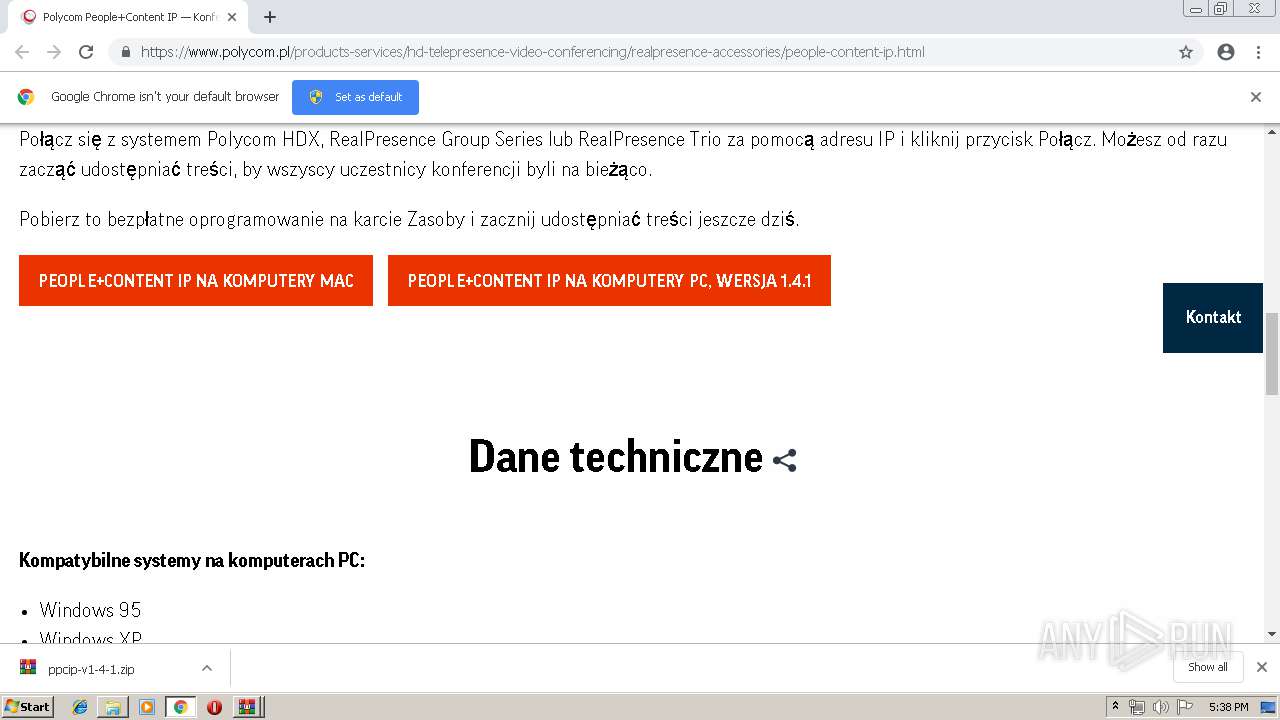
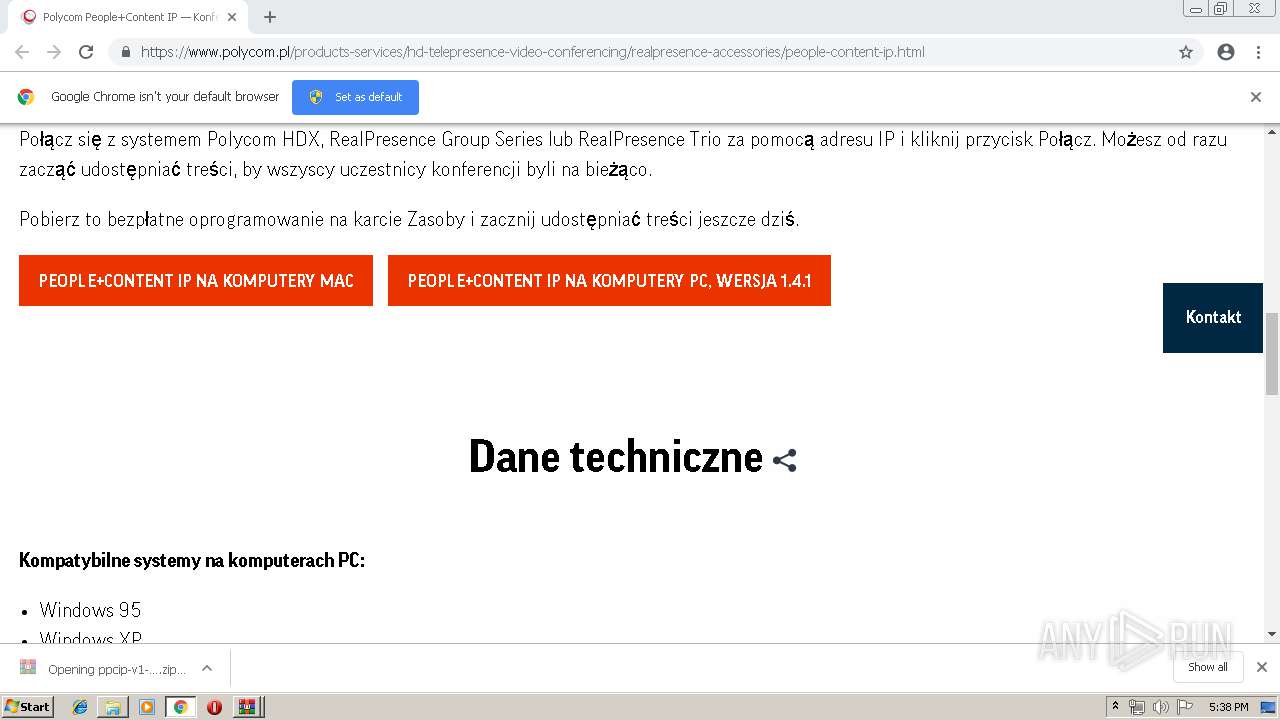
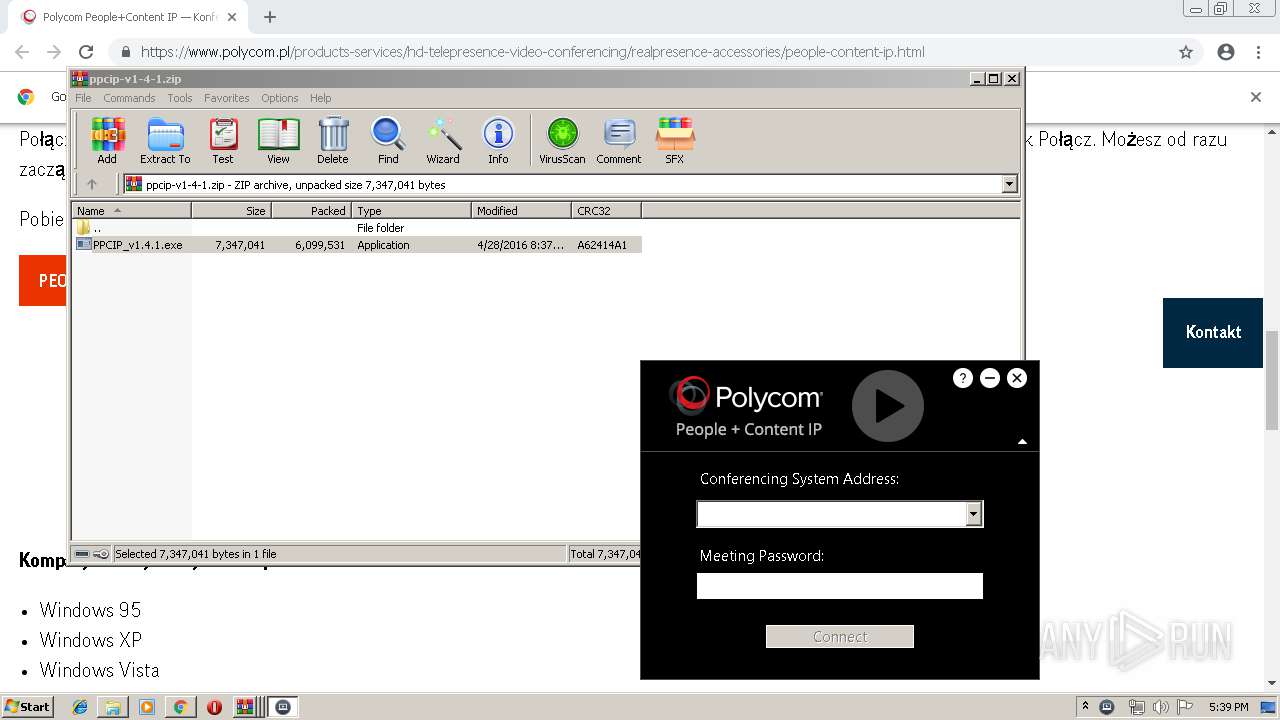
| URL: | https://www.polycom.pl/products-services/hd-telepresence-video-conferencing/realpresence-accessories/people-content-ip.html |
| Full analysis: | https://app.any.run/tasks/e21e1c32-f8c4-424c-9b08-37fa8575bec3 |
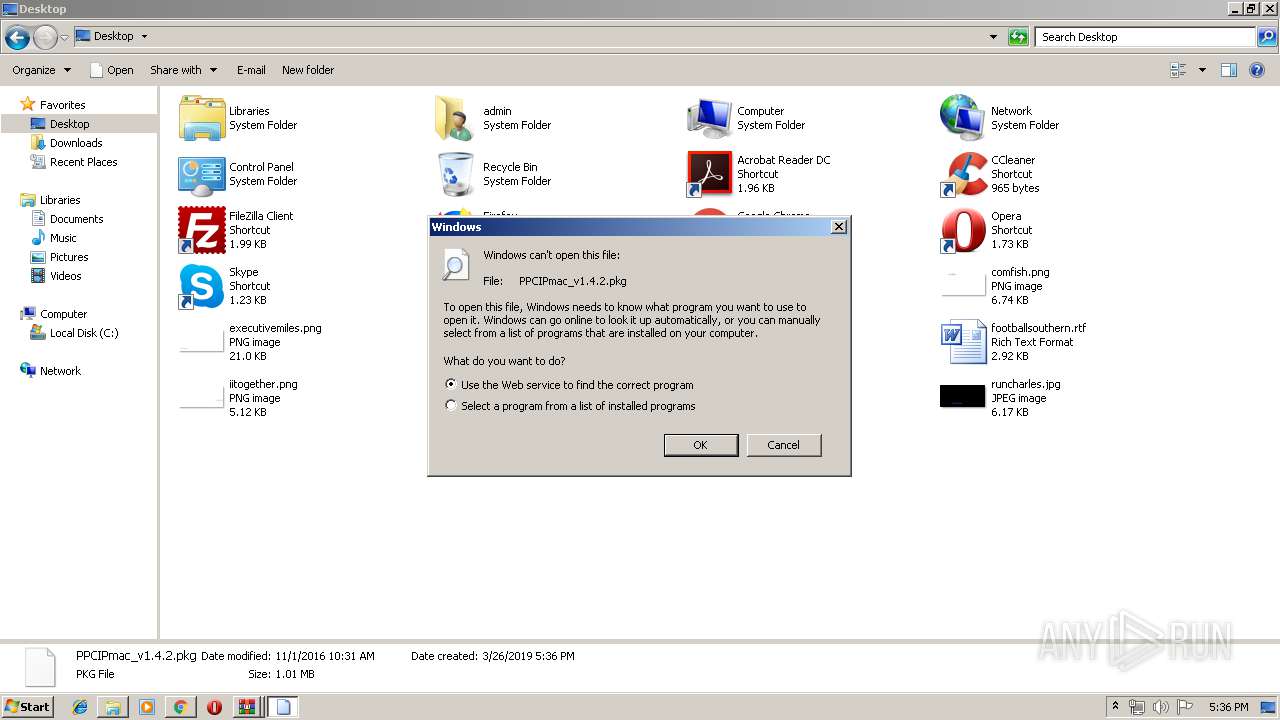
| Verdict: | Malicious activity |
| Analysis date: | March 26, 2019, 17:35:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 39F87319FD46570BDCE3D2E9B945DAEB |
| SHA1: | 9EAA942797BA6A8E68522F4A3B7FAC60927B695D |
| SHA256: | 35920147EA8CF6AB980A7E4BFD7CBCE9D53709AC59CECCB76E4178666867A4F1 |
| SSDEEP: | 3:N8DSL0LEiRW8MPCXqXDBv7QcQfLZAvXrrWKVBfX+R0n:2OLqRWdPCQccY+GA2R0n |
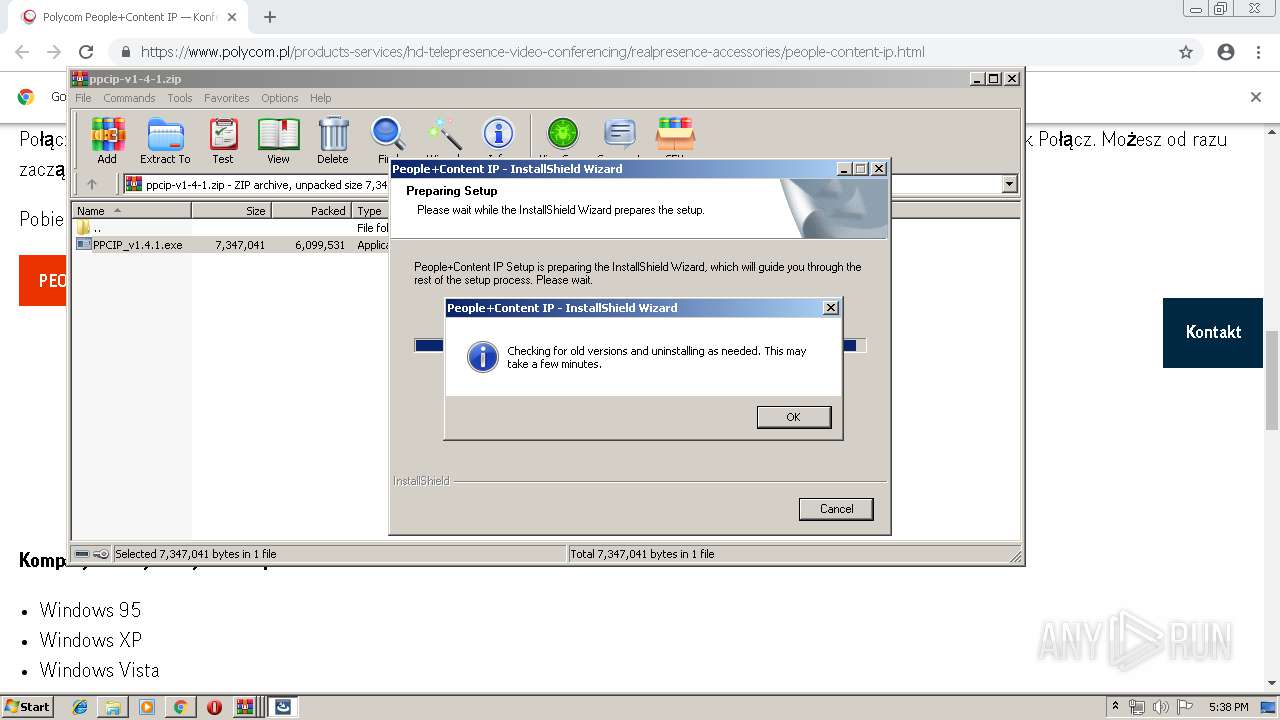
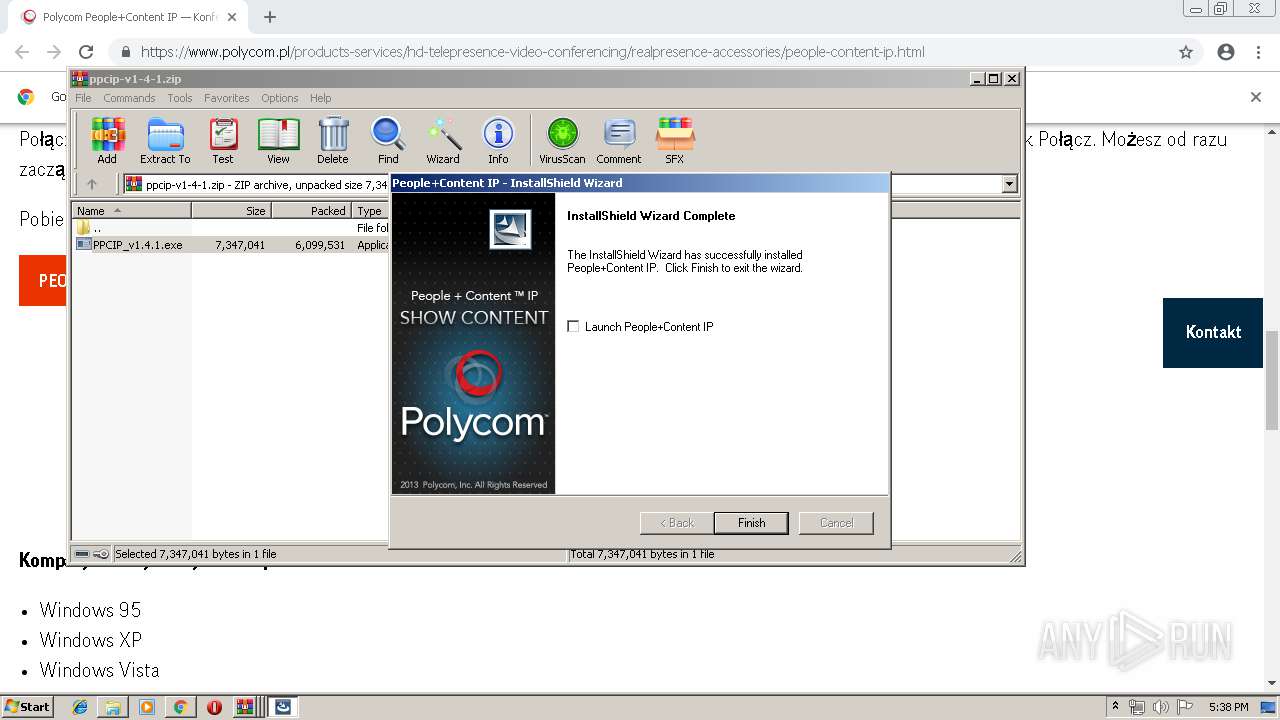
MALICIOUS
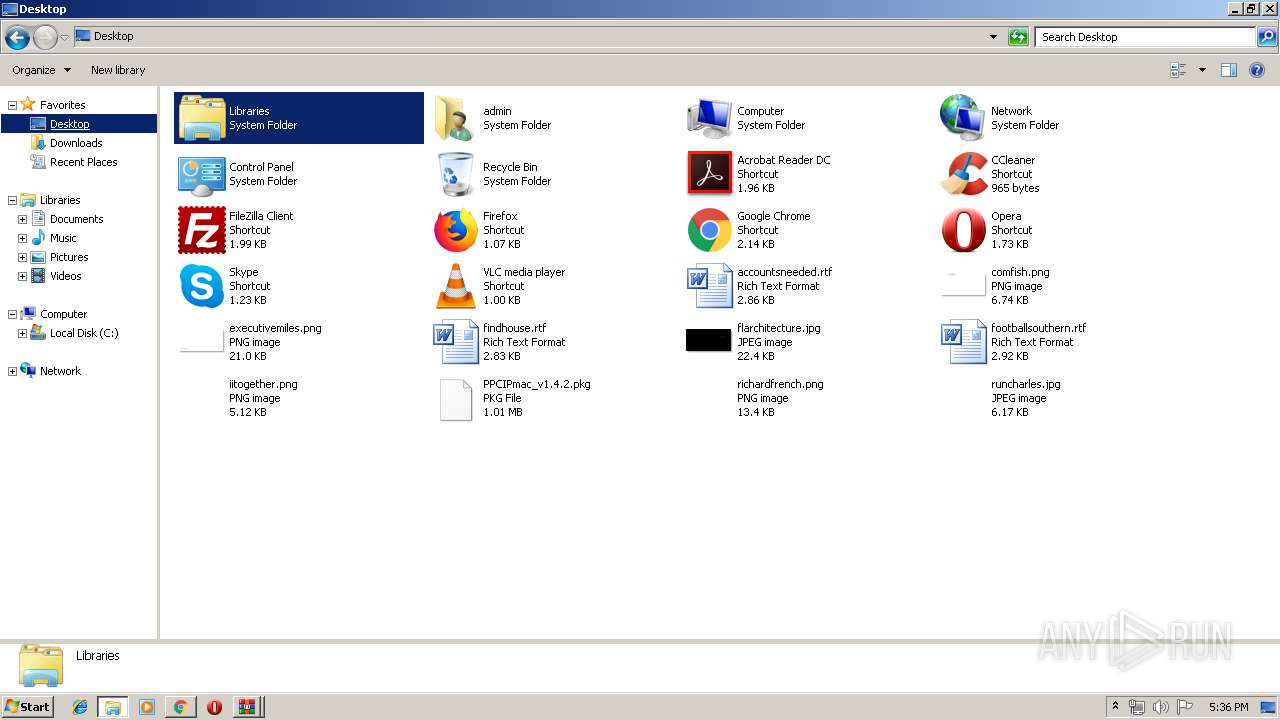
Application was dropped or rewritten from another process
- PPCIP_v1.4.1.exe (PID: 3368)
- PPCIP_v1.4.1.exe (PID: 760)
- PPCIP.exe (PID: 1592)
Loads dropped or rewritten executable
- PPCIP_v1.4.1.exe (PID: 3368)
- PPCIP.exe (PID: 1592)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2760)
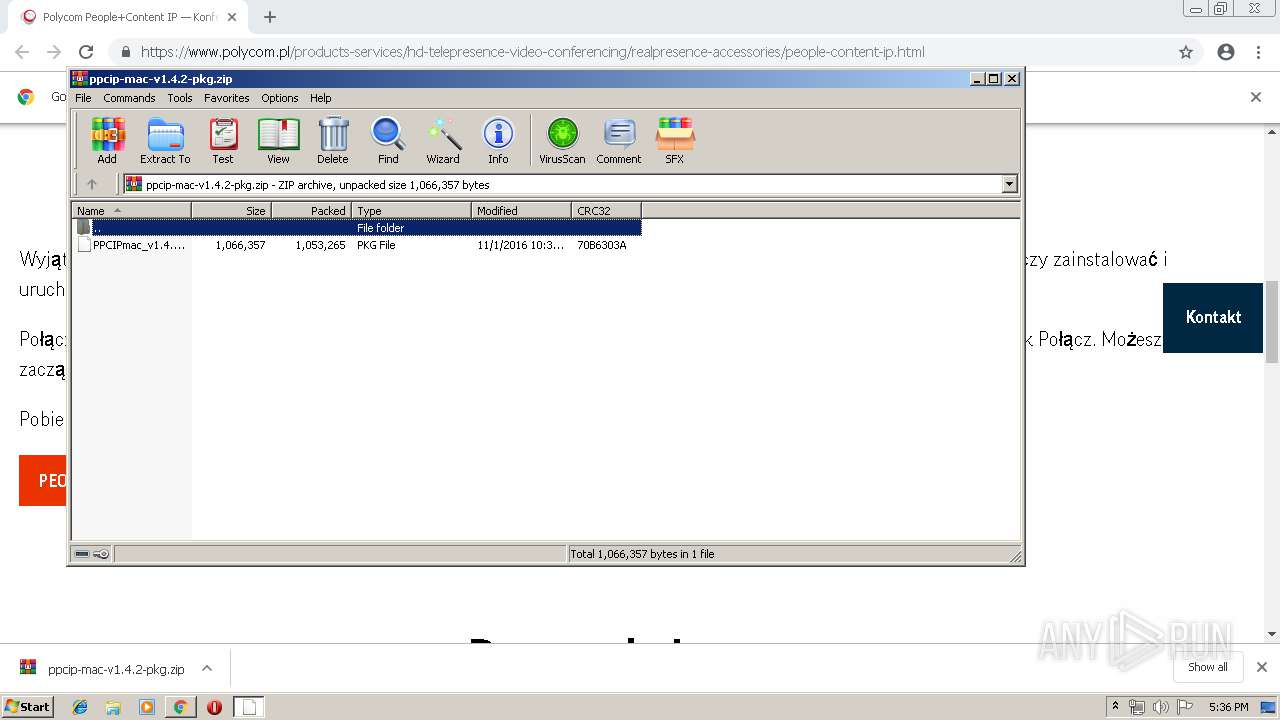
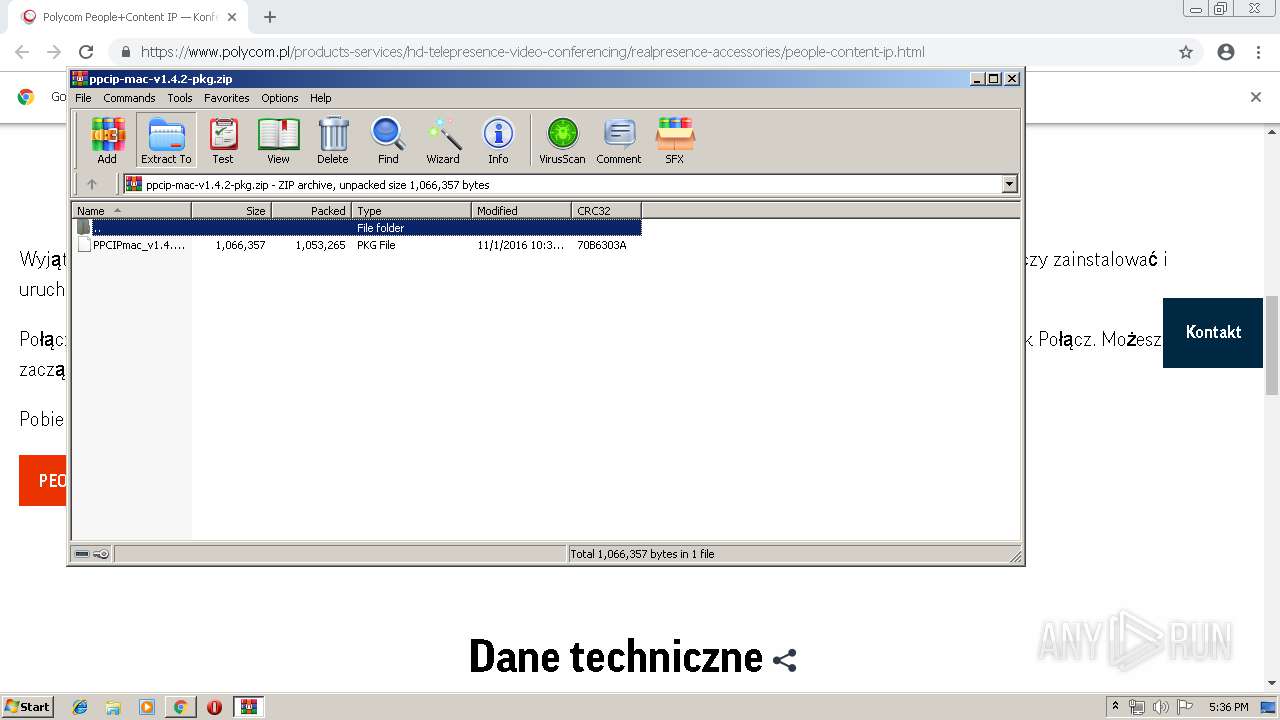
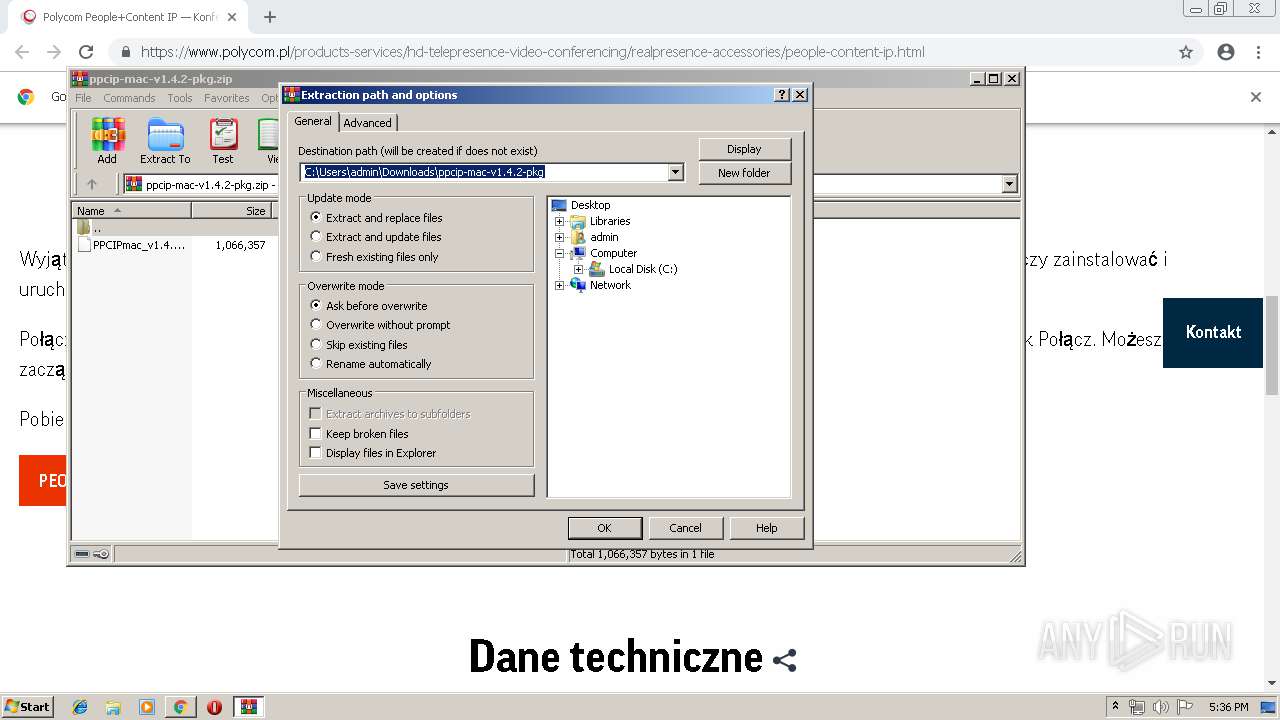
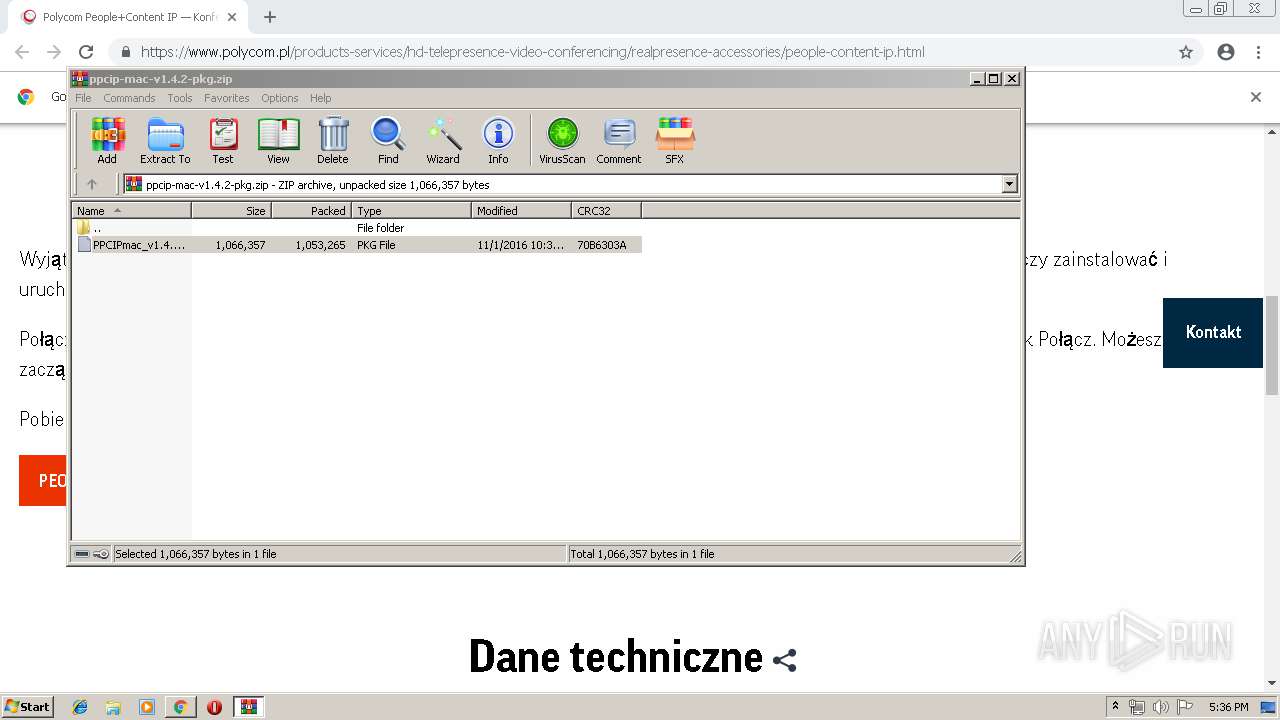
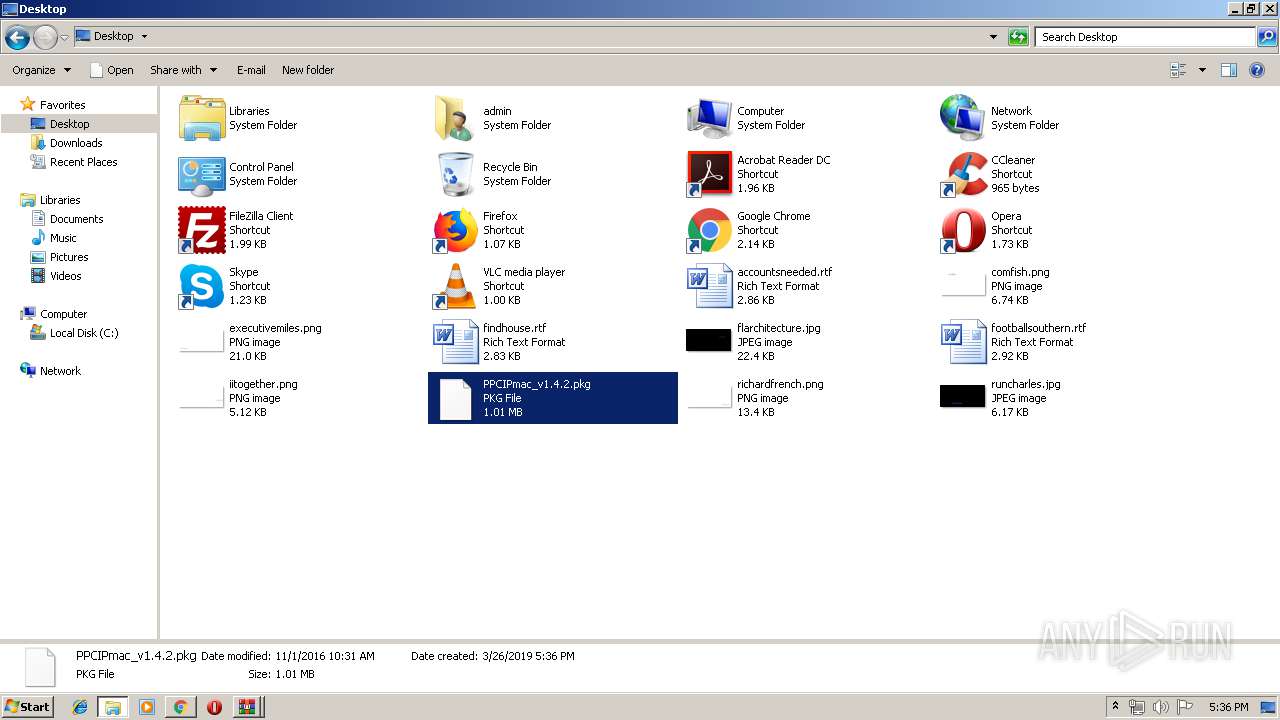
Executable content was dropped or overwritten
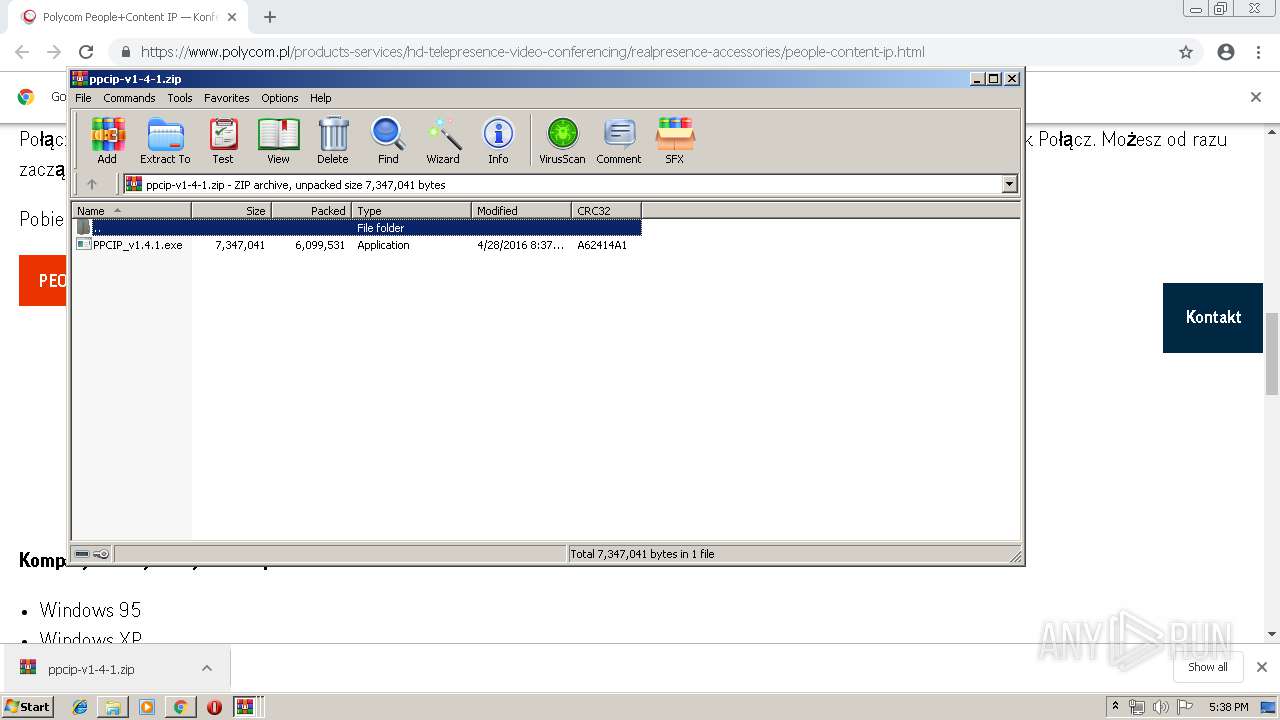
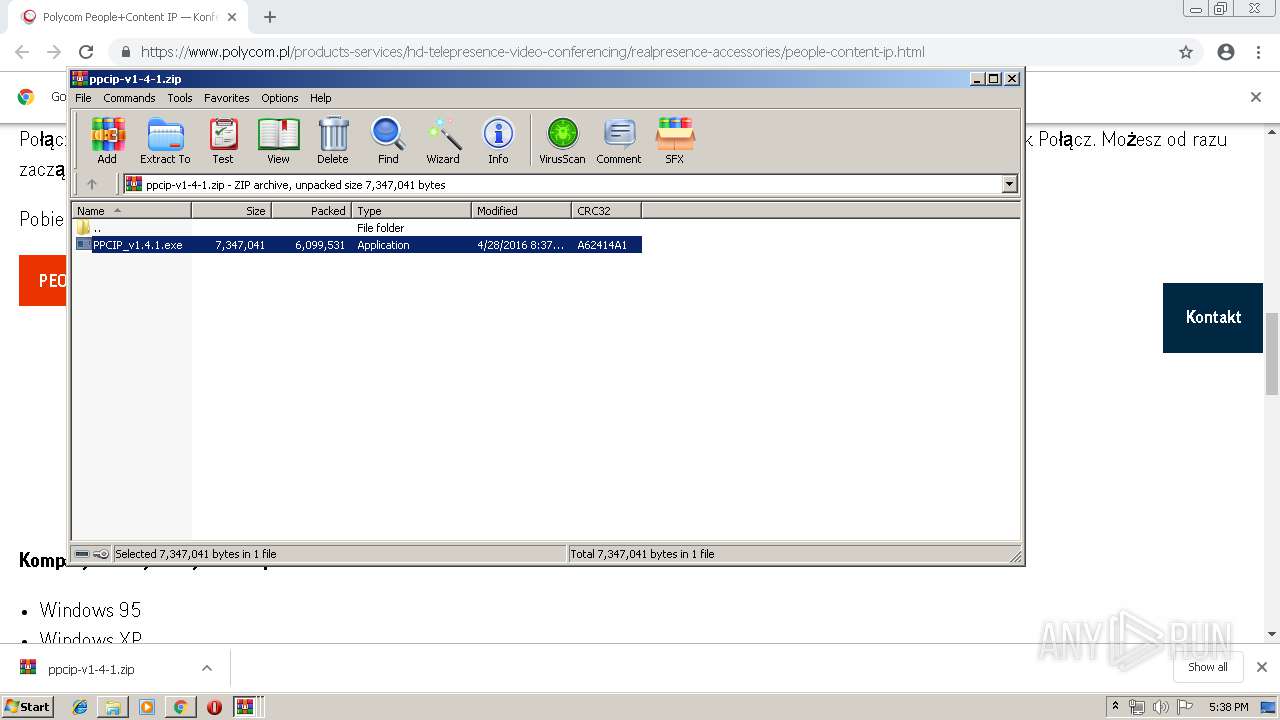
- WinRAR.exe (PID: 4068)
- PPCIP_v1.4.1.exe (PID: 3368)
Creates files in the user directory
- PPCIP_v1.4.1.exe (PID: 3368)
Application launched itself
- WinRAR.exe (PID: 3932)
Searches for installed software
- DllHost.exe (PID: 3544)
- PPCIP_v1.4.1.exe (PID: 3368)
Creates files in the program directory
- PPCIP_v1.4.1.exe (PID: 3368)
- PPCIP.exe (PID: 1592)
Creates a software uninstall entry
- PPCIP_v1.4.1.exe (PID: 3368)
INFO
Application launched itself
- chrome.exe (PID: 2760)
Reads settings of System Certificates
- chrome.exe (PID: 2164)
Creates files in the user directory
- chrome.exe (PID: 2760)
Reads Internet Cache Settings
- chrome.exe (PID: 2760)
Low-level read access rights to disk partition
- vssvc.exe (PID: 292)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3084)
Changes settings of System certificates
- DrvInst.exe (PID: 3084)
Dropped object may contain Bitcoin addresses
- PPCIP_v1.4.1.exe (PID: 3368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
37
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,16757165573614761929,13464838209277135556,131072 --enable-features=PasswordImport --service-pipe-token=12133985021958363888 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12133985021958363888 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
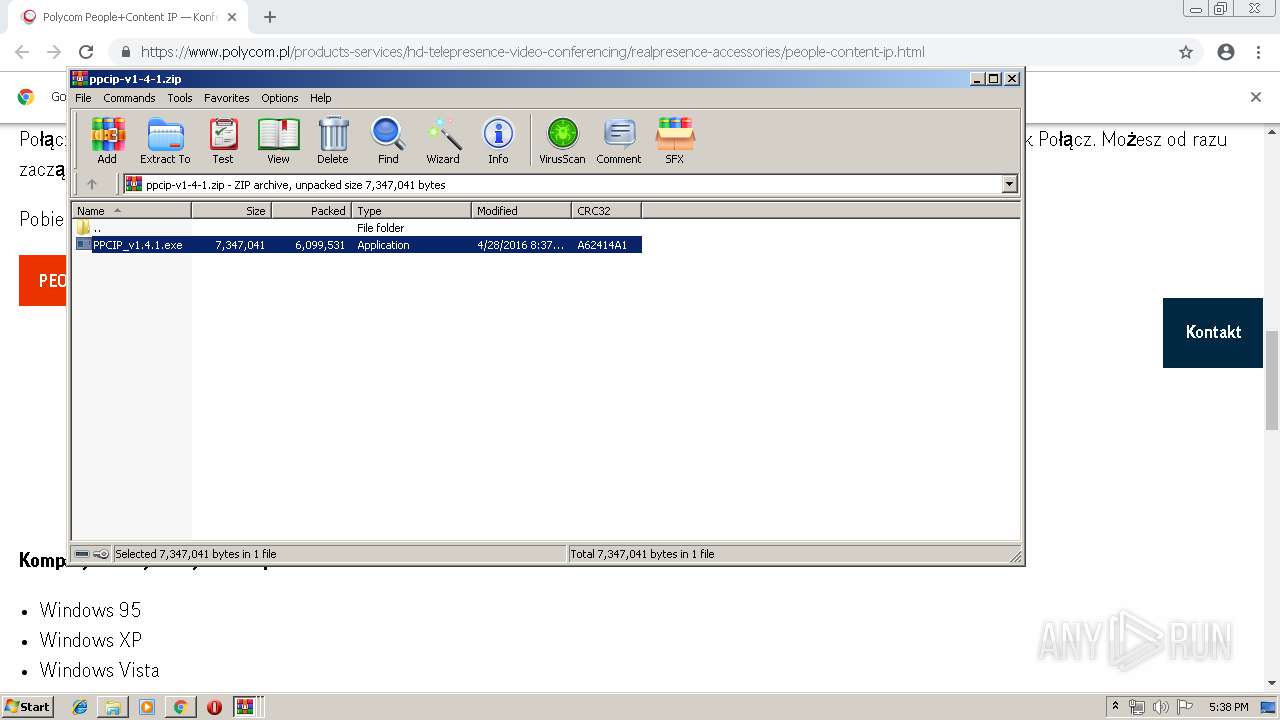
| 760 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4068.39242\PPCIP_v1.4.1.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4068.39242\PPCIP_v1.4.1.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Macrovision Corporation Integrity Level: MEDIUM Description: Setup.exe Exit code: 3221226540 Version: 12.0.58849 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,16757165573614761929,13464838209277135556,131072 --enable-features=PasswordImport --service-pipe-token=18302979589496425780 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18302979589496425780 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,16757165573614761929,13464838209277135556,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10913014888552575637 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10913014888552575637 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4396 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Polycom\People+Content IP\PPCIP.exe" | C:\Program Files\Polycom\People+Content IP\PPCIP.exe | PPCIP_v1.4.1.exe | ||||||||||||
User: admin Company: Polycom, Inc Integrity Level: HIGH Description: People+Content(TM) IP Exit code: 0 Version: 1.4.1.522 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=972,16757165573614761929,13464838209277135556,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=972765324590673106 --mojo-platform-channel-handle=2804 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,16757165573614761929,13464838209277135556,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13333574489058329730 --mojo-platform-channel-handle=1512 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,16757165573614761929,13464838209277135556,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6567674661704806231 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6567674661704806231 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa60f18,0x6fa60f28,0x6fa60f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 843
Read events
2 485
Write events
354
Delete events
4
Modification events
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2760-13198095345031750 |
Value: 259 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2760-13198095345031750 |
Value: 259 | |||
Executable files
27
Suspicious files
192
Text files
340
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fae3b2f6-b8b8-4b02-a1ca-65063de3ccf6.tmp | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
97
DNS requests
60
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
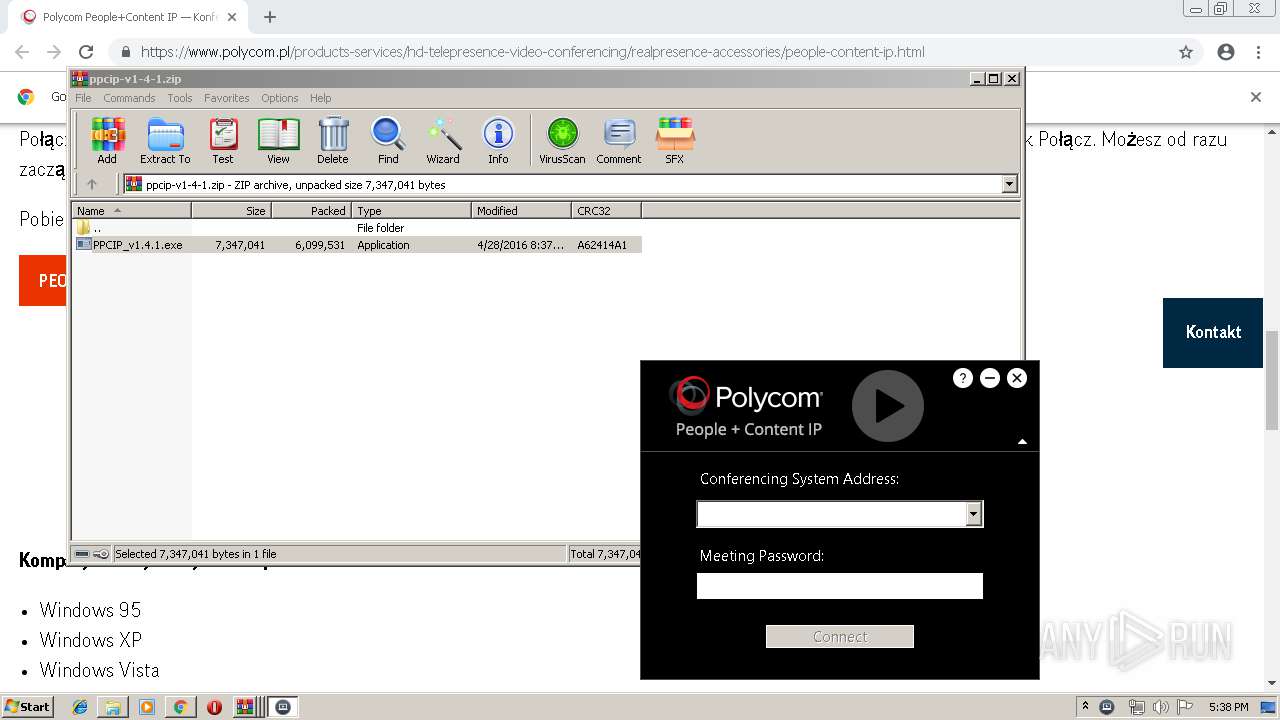
1592 | PPCIP.exe | GET | 301 | 104.123.105.136:80 | http://www.polycom.com/ppcipversion | NL | — | — | whitelisted |
2164 | chrome.exe | GET | 200 | 173.194.19.183:80 | http://r1---sn-5go7yn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.102.22.104&mm=28&mn=sn-5go7yn7z&ms=nvh&mt=1553621611&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2164 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
1592 | PPCIP.exe | GET | 200 | 140.242.65.96:80 | http://downloads.polycom.com/video/ppcip/ppcip_version.txt | US | text | 14 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2164 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 23.45.106.43:443 | www.polycom.pl | Akamai International B.V. | NL | whitelisted |
2164 | chrome.exe | 172.217.22.109:443 | — | Google Inc. | US | whitelisted |
2164 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 104.19.196.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
2164 | chrome.exe | 23.37.56.177:443 | sadmin.brightcove.com | Akamai Technologies, Inc. | NL | whitelisted |
2164 | chrome.exe | 95.100.198.111:443 | players.brightcove.net | Akamai Technologies, Inc. | — | whitelisted |
2164 | chrome.exe | 95.100.196.33:443 | assets.adobedtm.com | Akamai Technologies, Inc. | — | whitelisted |
2164 | chrome.exe | 95.100.67.47:443 | use.typekit.net | Akamai Technologies, Inc. | — | whitelisted |
2164 | chrome.exe | 52.17.182.129:443 | dpm.demdex.net | Amazon.com, Inc. | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.polycom.pl |
| unknown |
accounts.google.com |
| shared |
assets.adobedtm.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
use.typekit.net |
| whitelisted |
sadmin.brightcove.com |
| unknown |
players.brightcove.net |
| whitelisted |
dpm.demdex.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2164 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2164 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2164 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2164 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2164 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2164 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2164 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2164 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
PPCIP.exe | 2019-03-26 17:38:43.624 Found PPCIP at C:\Program Files\Polycom\People+Content IP\PPCIP.exe
|
PPCIP.exe | 2019-03-26 17:38:43.627 TestForVenus: data0 stat [ret: -1] [GLE: 2]
|
PPCIP.exe | enable_os_print: Log file opened [fOSprintFile: 0x1544c58]
|
PPCIP.exe | 2019-03-26 17:38:43.649 main thread id: 0xb48
|
PPCIP.exe | 2019-03-26 17:38:43.649 main thread id: 0xb48
|
PPCIP.exe | 2019-03-26 17:38:43.649 CPPCIPApp::LoadResources: Loading PPCIPENU.dll
|
PPCIP.exe | 2019-03-26 17:38:43.689 CContentSourceImpl::SetNotificationSink: enter
|
PPCIP.exe | 2019-03-26 17:38:43.801 CSplashDlg::OnInitDialog: checking for new version
|
PPCIP.exe | 2019-03-26 17:38:45.137 CheckForUpdate: [web string: version=1.2.3]
|