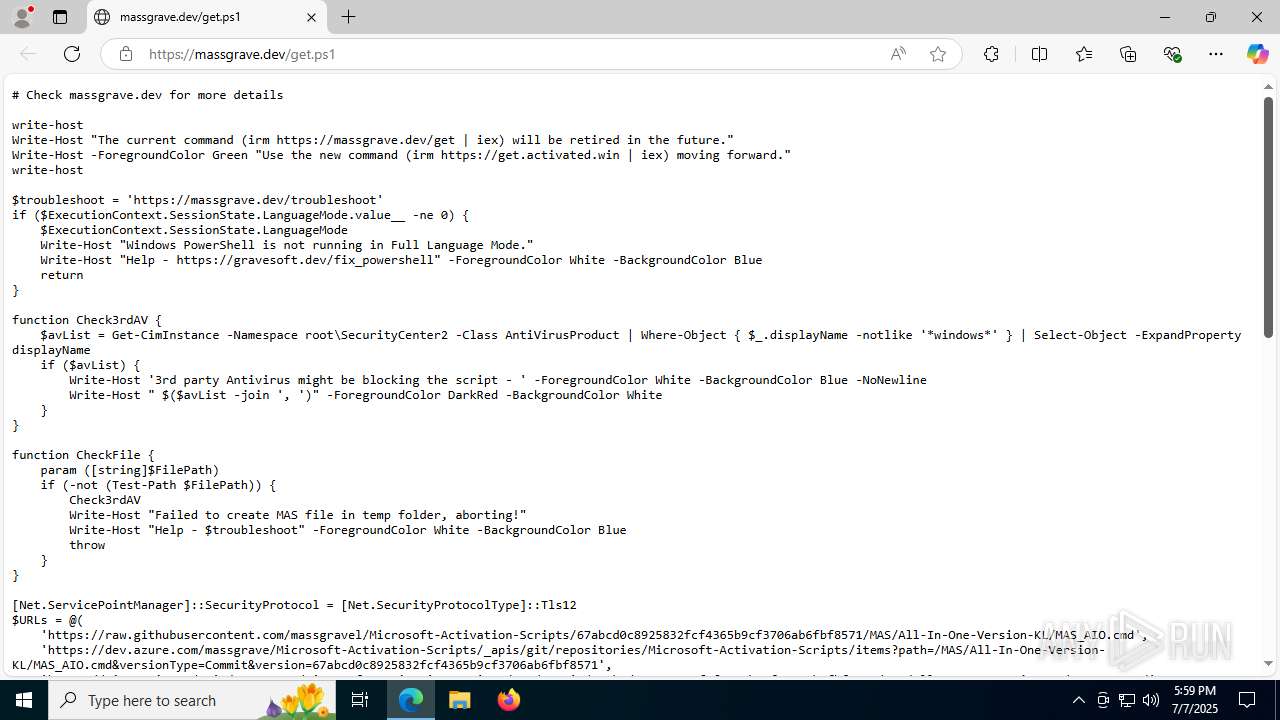
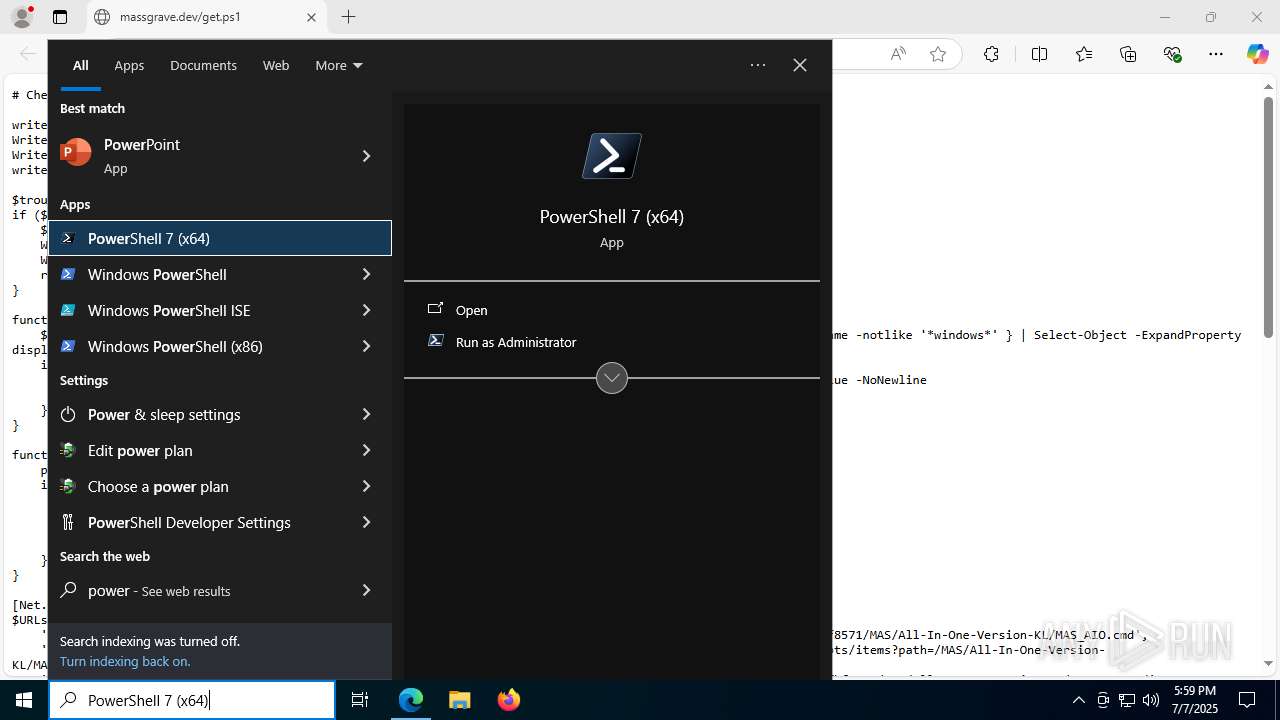
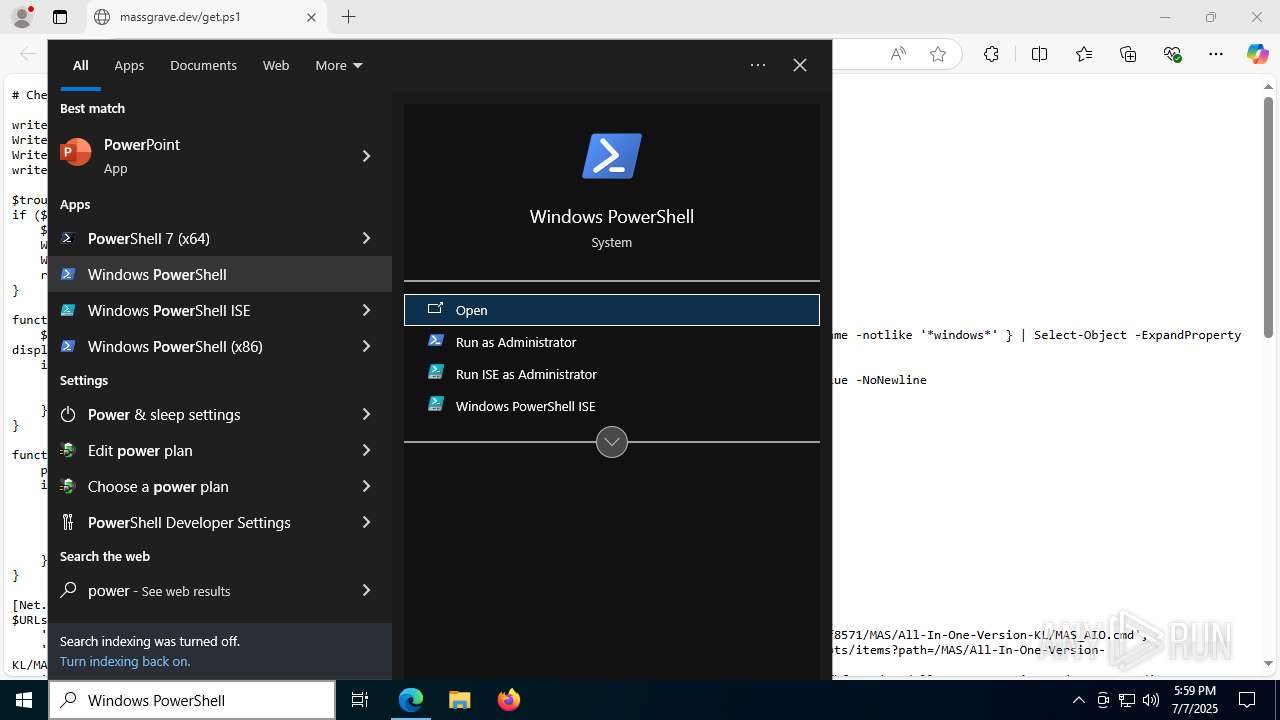
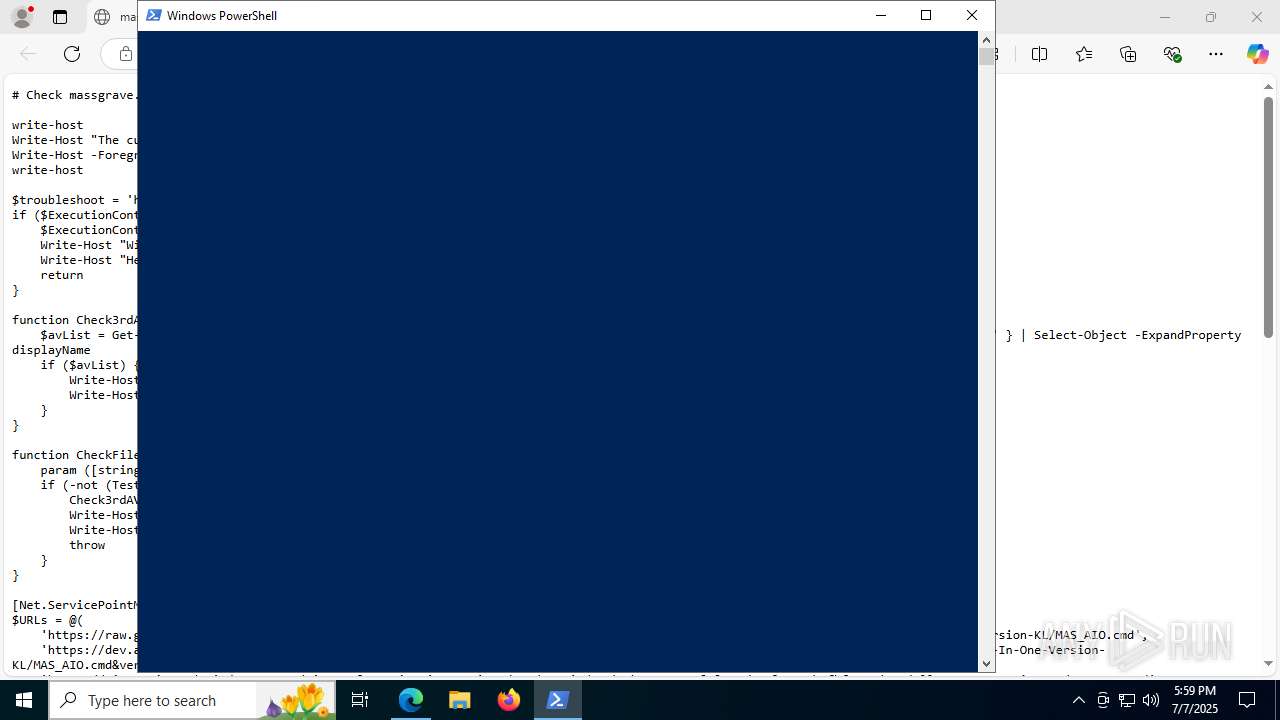
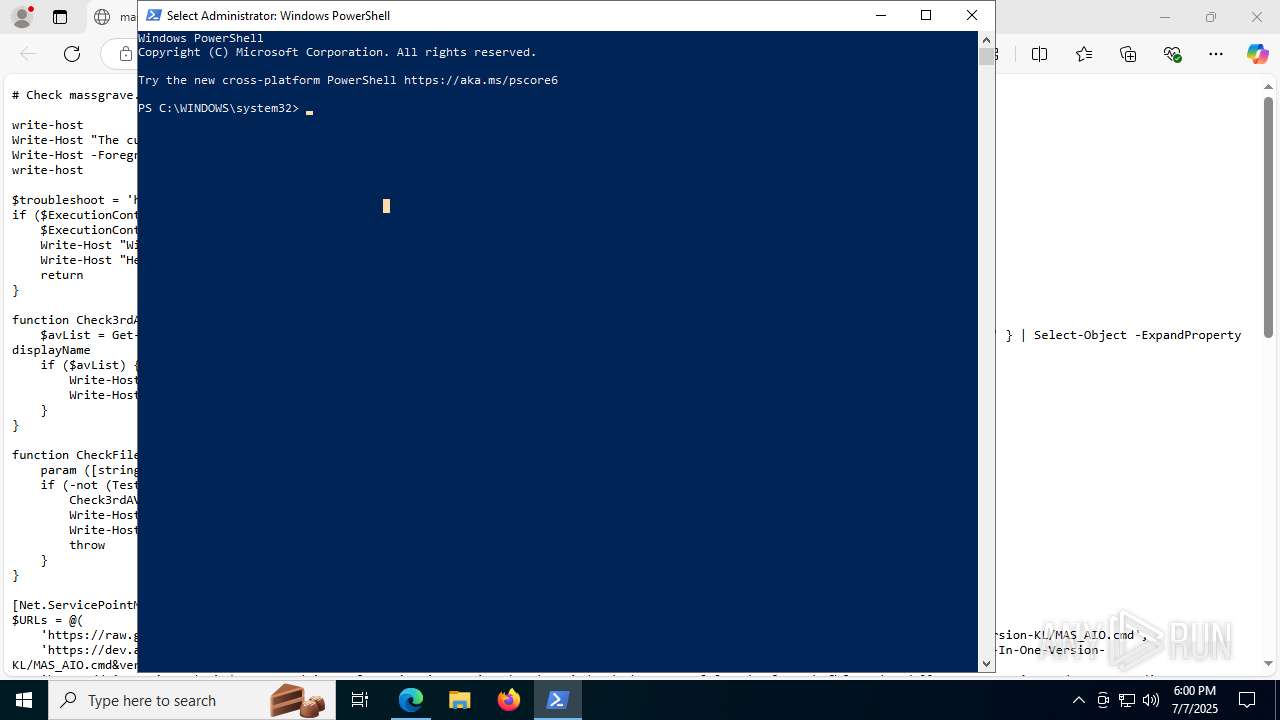
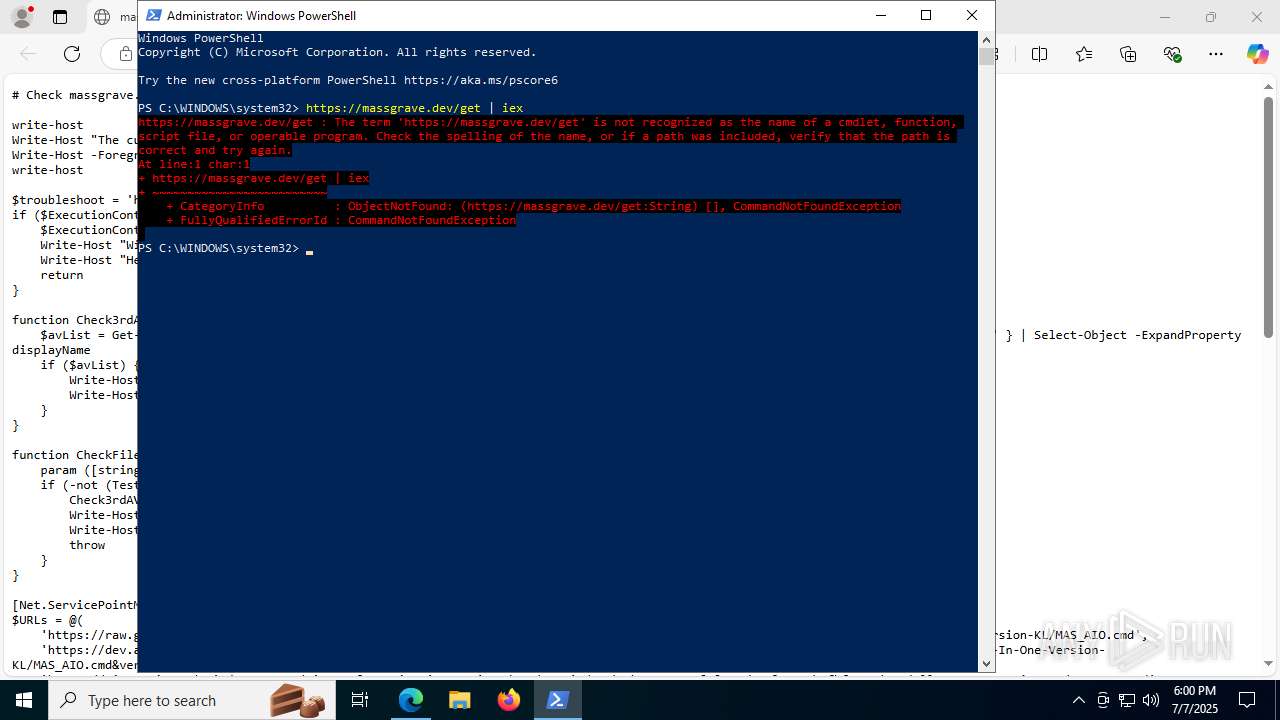
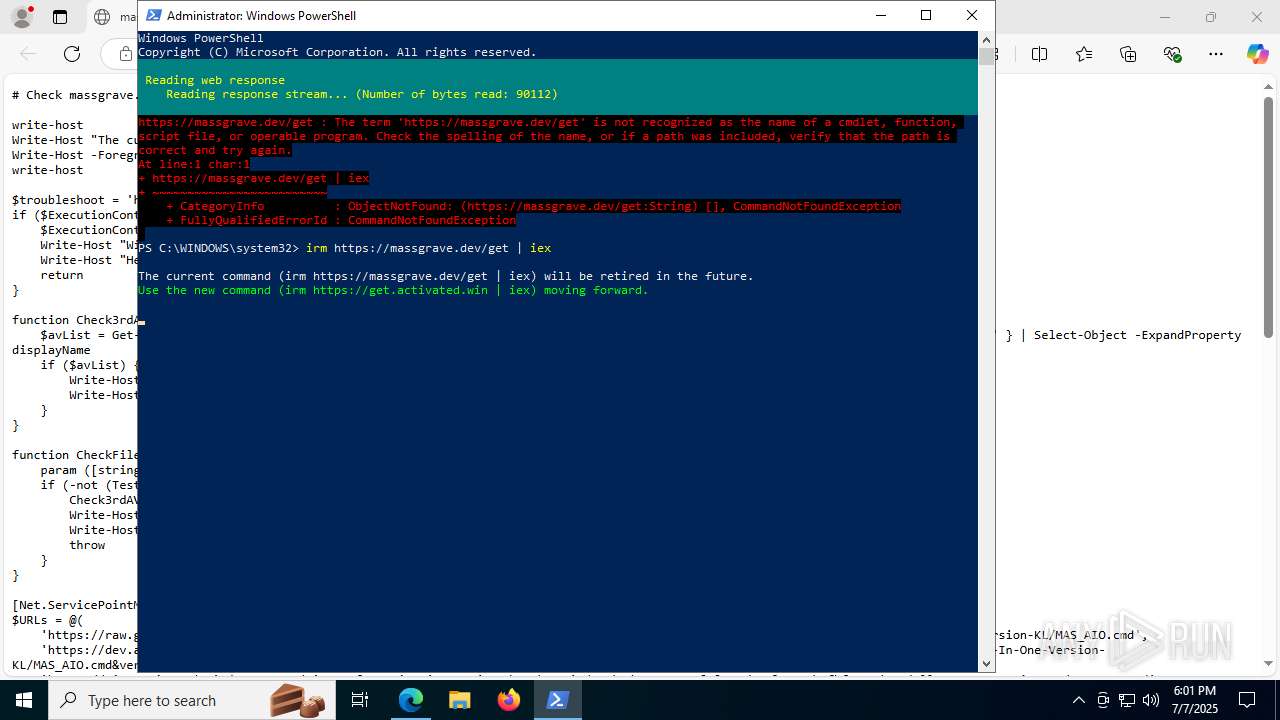
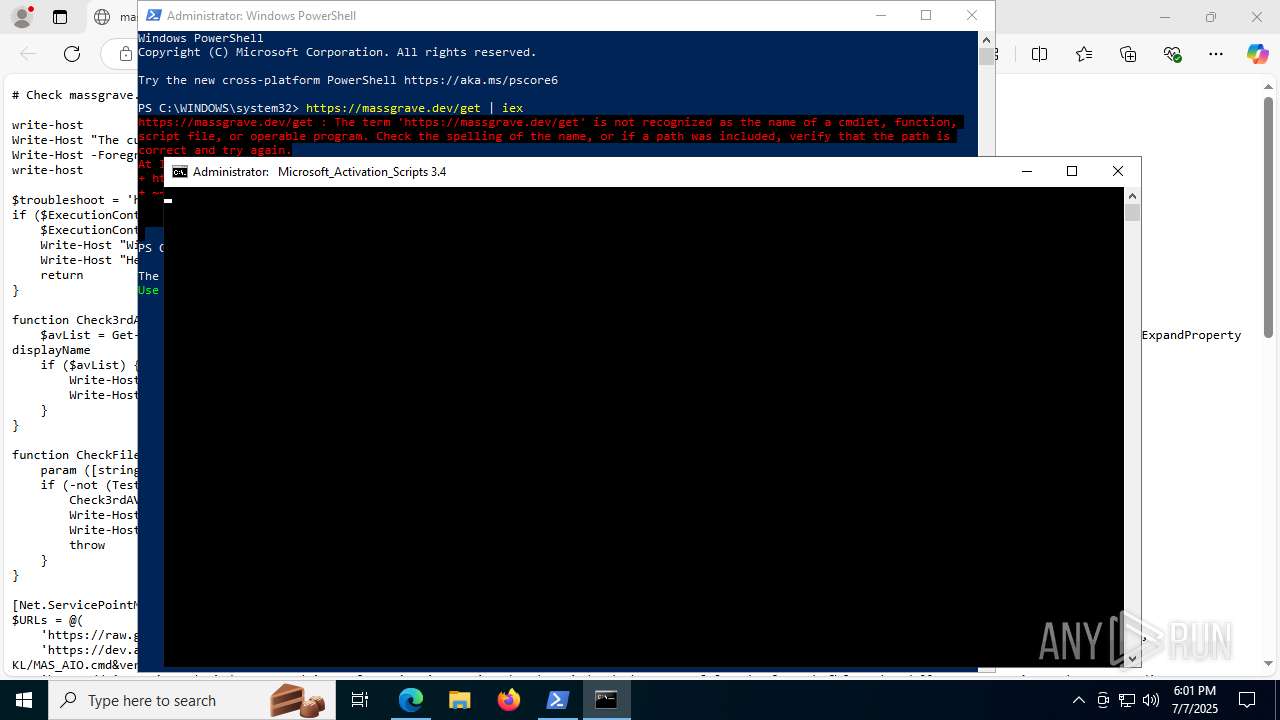
| URL: | https://massgrave.dev/get |
| Full analysis: | https://app.any.run/tasks/7f366492-ace3-413a-bede-5bbb09f5ccf0 |
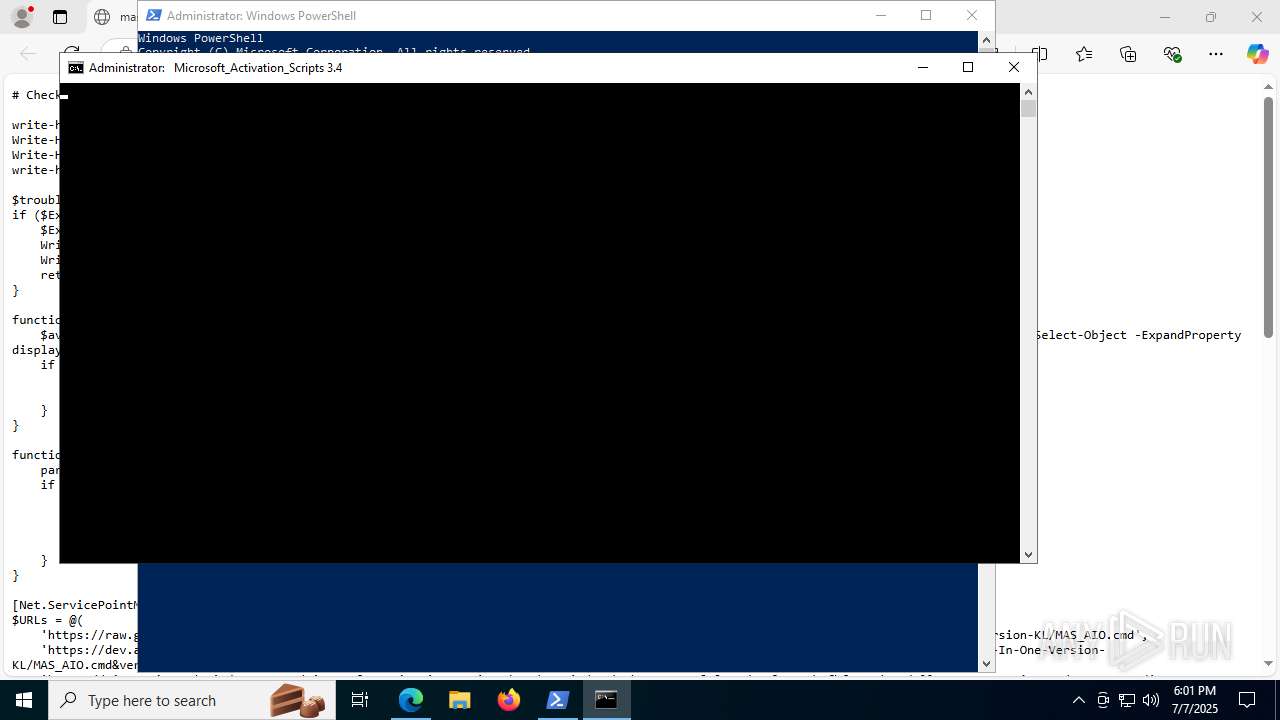
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2025, 17:59:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 924432E6484C1BB79492FD11F0CC882B |
| SHA1: | 7E7AEBA9BA87DAA5EC6C8E33D659DF32EAB1D4BA |
| SHA256: | 35893316F780CDFAD204FEAFE919AB8513B4DD6F6FE4A290DA30AA7A8F358E75 |
| SSDEEP: | 3:N8a0KN:2a0u |
MALICIOUS
No malicious indicators.SUSPICIOUS
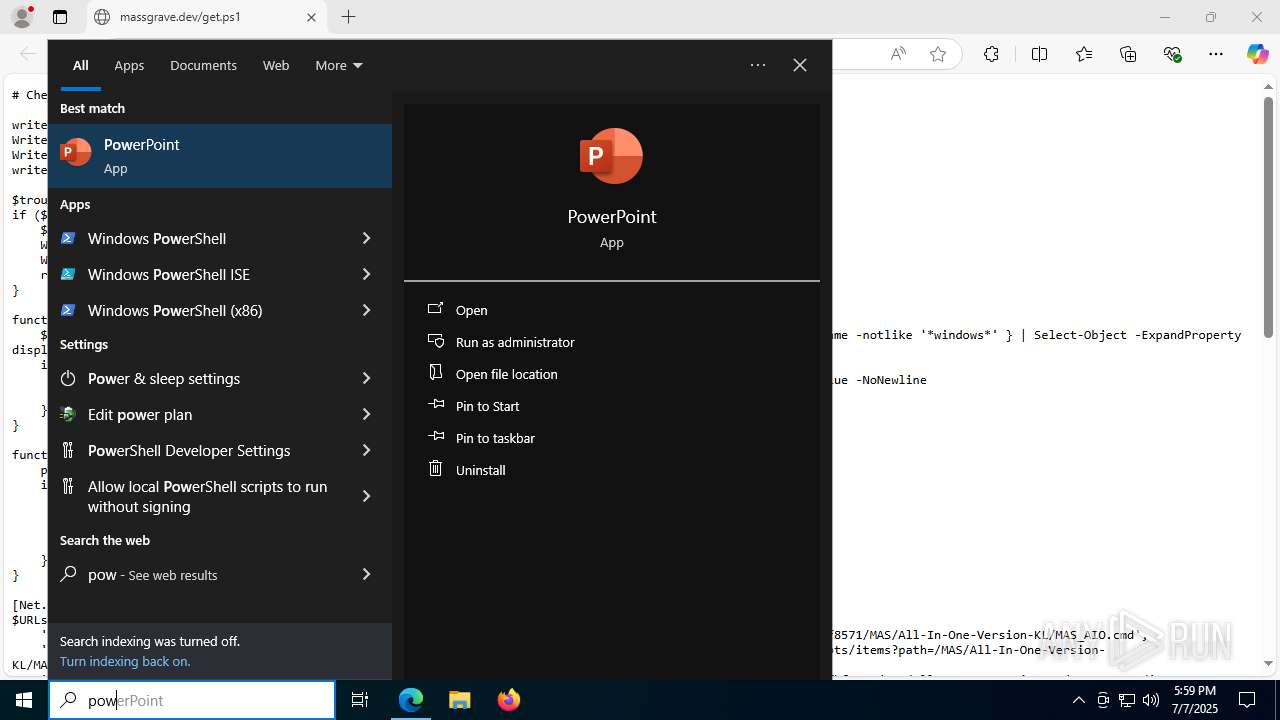
The process executes via Task Scheduler
- powershell.exe (PID: 5896)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5896)
- powershell.exe (PID: 5900)
- powershell.exe (PID: 8056)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 7272)
- powershell.exe (PID: 4828)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 5896)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 5896)
- powershell.exe (PID: 5900)
- powershell.exe (PID: 8056)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 7272)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 5896)
- powershell.exe (PID: 5900)
- powershell.exe (PID: 8056)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 7272)
Executing commands from ".cmd" file
- powershell.exe (PID: 5896)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 8016)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 5896)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 8016)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 5896)
Starts SC.EXE for service management
- cmd.exe (PID: 7764)
- cmd.exe (PID: 8016)
Windows service management via SC.EXE
- sc.exe (PID: 4652)
- sc.exe (PID: 7640)
- sc.exe (PID: 7616)
- sc.exe (PID: 1388)
- sc.exe (PID: 4192)
- sc.exe (PID: 7324)
- sc.exe (PID: 7932)
- sc.exe (PID: 7352)
- sc.exe (PID: 3960)
- sc.exe (PID: 8052)
- sc.exe (PID: 236)
- sc.exe (PID: 1300)
- sc.exe (PID: 7588)
- sc.exe (PID: 6896)
- sc.exe (PID: 6704)
- sc.exe (PID: 6284)
- sc.exe (PID: 8104)
- sc.exe (PID: 2072)
- sc.exe (PID: 4120)
- sc.exe (PID: 6364)
- sc.exe (PID: 5080)
- sc.exe (PID: 6836)
- sc.exe (PID: 5288)
- sc.exe (PID: 2952)
- sc.exe (PID: 7960)
- sc.exe (PID: 7324)
- sc.exe (PID: 8152)
- sc.exe (PID: 1056)
- sc.exe (PID: 6516)
- sc.exe (PID: 7888)
- sc.exe (PID: 7460)
- sc.exe (PID: 2512)
- sc.exe (PID: 7924)
- sc.exe (PID: 7344)
- sc.exe (PID: 7856)
- sc.exe (PID: 7612)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7764)
- cmd.exe (PID: 8016)
Application launched itself
- cmd.exe (PID: 7764)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 8016)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 2216)
- ClipUp.exe (PID: 4072)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7368)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 2216)
- cmd.exe (PID: 1720)
- cmd.exe (PID: 7480)
Executes script without checking the security policy
- powershell.exe (PID: 5900)
- powershell.exe (PID: 8056)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 7800)
- powershell.exe (PID: 2220)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 7272)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 7276)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 7852)
- powershell.exe (PID: 6516)
- powershell.exe (PID: 7932)
- powershell.exe (PID: 4828)
- powershell.exe (PID: 2216)
- powershell.exe (PID: 8148)
- powershell.exe (PID: 6384)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7368)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 2216)
- powershell.exe (PID: 7244)
- cmd.exe (PID: 1720)
- cmd.exe (PID: 8104)
- cmd.exe (PID: 7236)
- powershell.exe (PID: 2216)
- cmd.exe (PID: 7480)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 7368)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 1720)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7368)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 2216)
- powershell.exe (PID: 7244)
- cmd.exe (PID: 1720)
- cmd.exe (PID: 8104)
- powershell.exe (PID: 2216)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 7236)
Hides command output
- cmd.exe (PID: 7368)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 1356)
- cmd.exe (PID: 6764)
- cmd.exe (PID: 1720)
- cmd.exe (PID: 7664)
- cmd.exe (PID: 4764)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 8104)
- cmd.exe (PID: 2632)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 7416)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7764)
- cmd.exe (PID: 8016)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7560)
- cmd.exe (PID: 8016)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 6764)
Probably file/command deobfuscation
- cmd.exe (PID: 2216)
- cmd.exe (PID: 7480)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 7244)
- powershell.exe (PID: 2216)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 8016)
- cmd.exe (PID: 7664)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 2632)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 8016)
INFO
Reads the computer name
- identity_helper.exe (PID: 7404)
Application launched itself
- msedge.exe (PID: 5480)
Checks supported languages
- identity_helper.exe (PID: 7404)
- mode.com (PID: 7476)
- mode.com (PID: 2428)
- mode.com (PID: 7976)
- mode.com (PID: 7896)
Reads Environment values
- identity_helper.exe (PID: 7404)
Disables trace logs
- powershell.exe (PID: 5896)
Checks current location (POWERSHELL)
- powershell.exe (PID: 5896)
Checks proxy server information
- powershell.exe (PID: 5896)
- slui.exe (PID: 640)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5896)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 5896)
- powershell.exe (PID: 5900)
- powershell.exe (PID: 8056)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 7272)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 5896)
- powershell.exe (PID: 5900)
- powershell.exe (PID: 8056)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 7272)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5896)
- powershell.exe (PID: 5900)
- powershell.exe (PID: 8056)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 7272)
Checks operating system version
- cmd.exe (PID: 7764)
- cmd.exe (PID: 8016)
Starts MODE.COM to configure console settings
- mode.com (PID: 7476)
- mode.com (PID: 2428)
- mode.com (PID: 7896)
- mode.com (PID: 7976)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7224)
- WMIC.exe (PID: 6748)
- WMIC.exe (PID: 7804)
- WMIC.exe (PID: 6384)
- WMIC.exe (PID: 4520)
- WMIC.exe (PID: 8136)
- WMIC.exe (PID: 6796)
- WMIC.exe (PID: 7528)
- WMIC.exe (PID: 5540)
- WMIC.exe (PID: 7776)
- WMIC.exe (PID: 8168)
Reads the software policy settings
- slui.exe (PID: 640)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7244)
Creates files in the program directory
- cmd.exe (PID: 8016)
- ClipUp.exe (PID: 1700)
Create files in a temporary directory
- ClipUp.exe (PID: 1700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
434
Monitored processes
289
Malicious processes
10
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | sc start sppsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 316 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "TwBTAE0AYQBqAG8AcgBWAGUAcgBzAGkAbwBuAD0ANQA7AE8AUwBNAGkAbgBvAHIAVgBlAHIAcwBpAG8AbgA9ADEAOwBPAFMAUABsAGEAdABmAG8AcgBtAEkAZAA9ADIAOwBQAFAAPQAwADsAUABmAG4APQBNAGkAYwByAG8AcwBvAGYAdAAuAFcAaQBuAGQAbwB3AHMALgA0ADgALgBYADEAOQAtADkAOAA4ADQAMQBfADgAdwBlAGsAeQBiADMAZAA4AGIAYgB3AGUAOwBQAEsAZQB5AEkASQBEAD0ANAA2ADUAMQA0ADUAMgAxADcAMQAzADEAMwAxADQAMwAwADQAMgA2ADQAMwAzADkANAA4ADEAMQAxADcAOAA2ADIAMgA2ADYAMgA0ADIAMAAzADMANAA1ADcAMgA2ADAAMwAxADEAOAAxADkANgA2ADQANwAzADUAMgA4ADAAOwAAAA==" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 432 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 592 | reg query "HKCU\Console" /v ForceV2 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 788 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 868 | reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /v "SkipRearm" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 888 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v Type | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | sc start LicenseManager | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
107 280
Read events
107 265
Write events
15
Delete events
0
Modification events
| (PID) Process: | (5480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5480) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AC66EBE3F0972F00 | |||
| (PID) Process: | (5480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263054 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EEBA84F3-F0E3-44C2-ADDA-220C26C5B7FB} | |||
| (PID) Process: | (5480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263054 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B7397E63-7DC6-4027-A4E1-DC1E6B060FBA} | |||
| (PID) Process: | (5480) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3D6D12E4F0972F00 | |||
| (PID) Process: | (5480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263054 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {190A4814-078A-41D6-8D7A-269BF71DD74C} | |||
| (PID) Process: | (5480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
0
Suspicious files
234
Text files
112
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF176234.TMP | — | |
MD5:— | SHA256:— | |||
| 5480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176234.TMP | — | |
MD5:— | SHA256:— | |||
| 5480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176234.TMP | — | |
MD5:— | SHA256:— | |||
| 5480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF176244.TMP | — | |
MD5:— | SHA256:— | |||
| 5480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176254.TMP | — | |
MD5:— | SHA256:— | |||
| 5480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176273.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
71
DNS requests
68
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1200 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:OcuYnwZa9XDaNaGtHSd7x-Wl-_ueE2rcjtTZdFzS-0U&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5284 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7592 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7592 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7684 | svchost.exe | HEAD | 200 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752451688&P2=404&P3=2&P4=l84LsWZ52cKXL3eioujKOT7vL4dYi%2fBJqMz5wf0FiOqQ0iqaxeWec530hv5Jk5U%2fsijRcUuT0O79Te9FUv5u3g%3d%3d | unknown | — | — | whitelisted |
7684 | svchost.exe | GET | 206 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752451688&P2=404&P3=2&P4=l84LsWZ52cKXL3eioujKOT7vL4dYi%2fBJqMz5wf0FiOqQ0iqaxeWec530hv5Jk5U%2fsijRcUuT0O79Te9FUv5u3g%3d%3d | unknown | — | — | whitelisted |
7684 | svchost.exe | GET | 206 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752451688&P2=404&P3=2&P4=l84LsWZ52cKXL3eioujKOT7vL4dYi%2fBJqMz5wf0FiOqQ0iqaxeWec530hv5Jk5U%2fsijRcUuT0O79Te9FUv5u3g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2648 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1200 | msedge.exe | 104.21.22.3:443 | massgrave.dev | CLOUDFLARENET | — | unknown |
1200 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1200 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1200 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1200 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
massgrave.dev |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1200 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1200 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
— | — | Misc activity | SUSPICIOUS [ANY.RUN] The Principal.WindowsIdentity in PS.Script has been detected |
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Get-CimInstance Cmdlet has been detected |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |