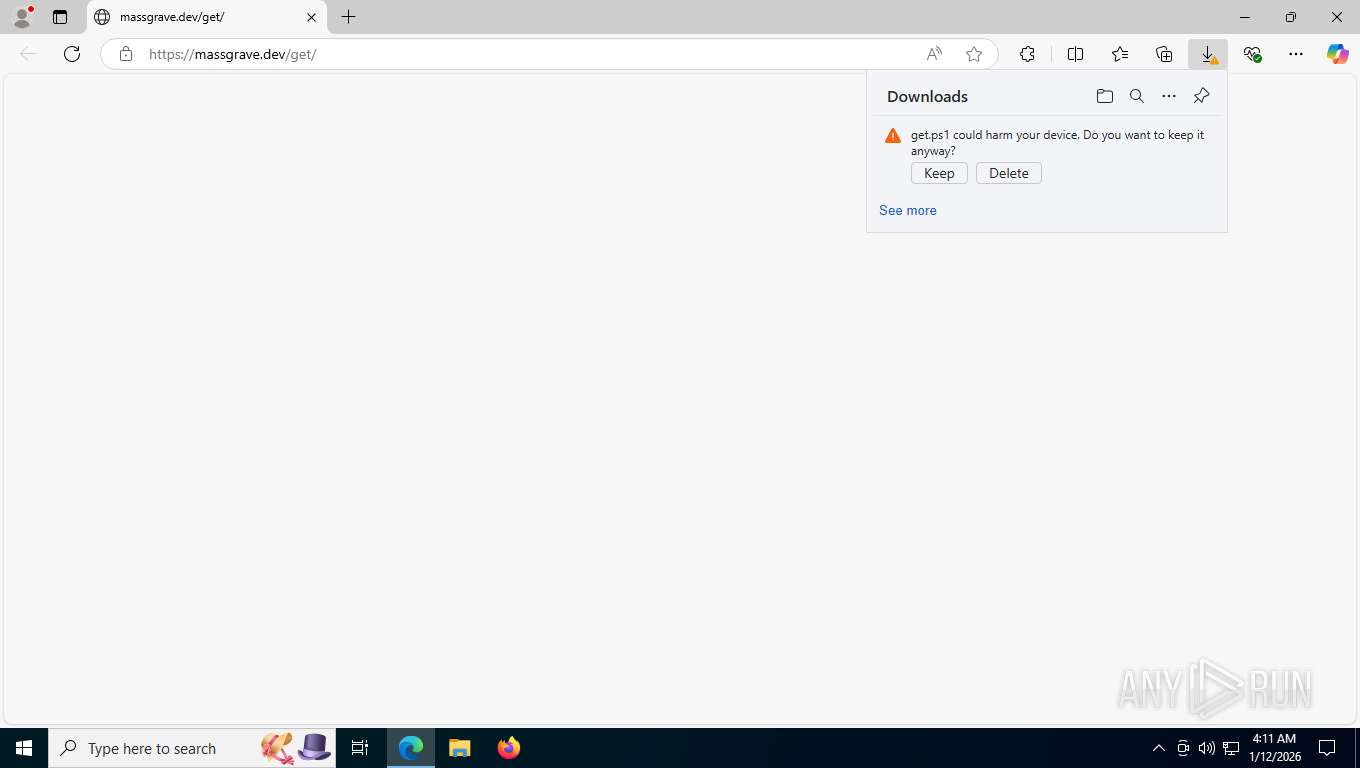
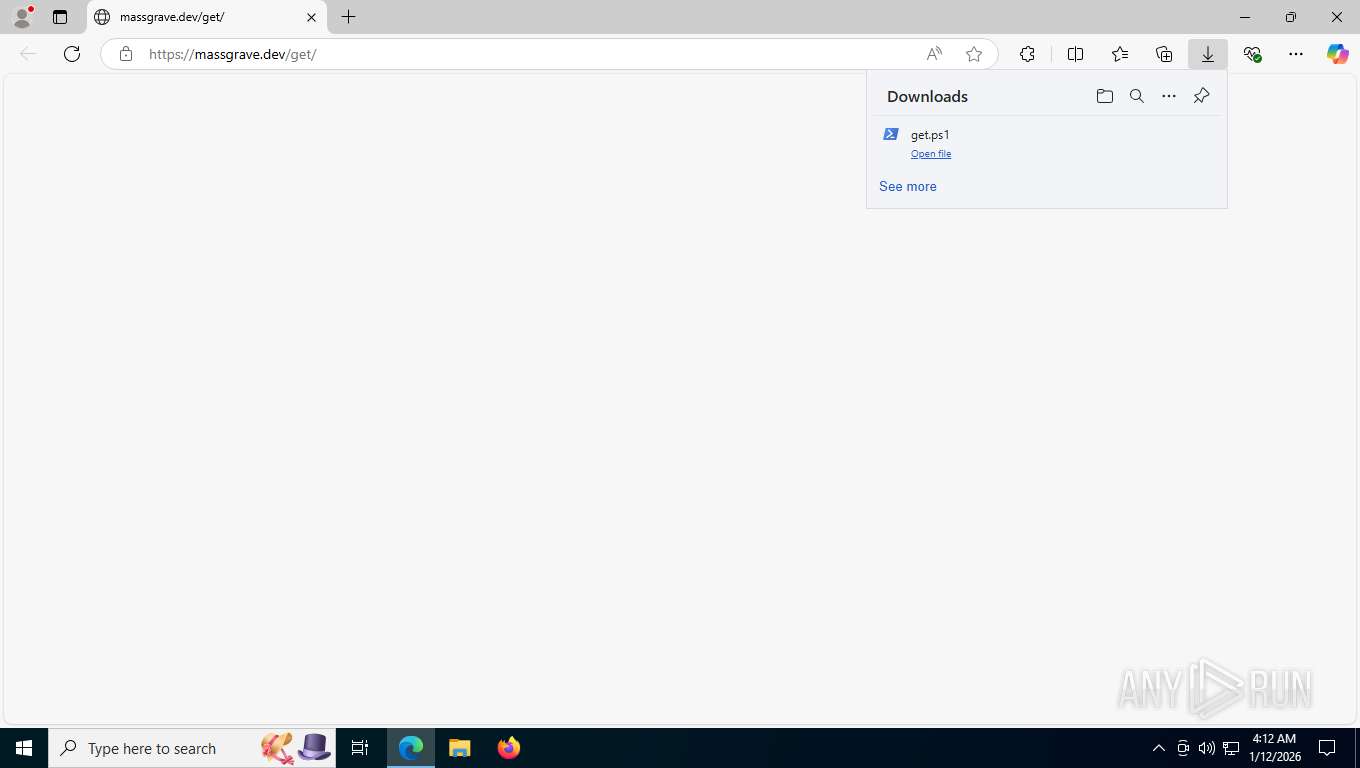
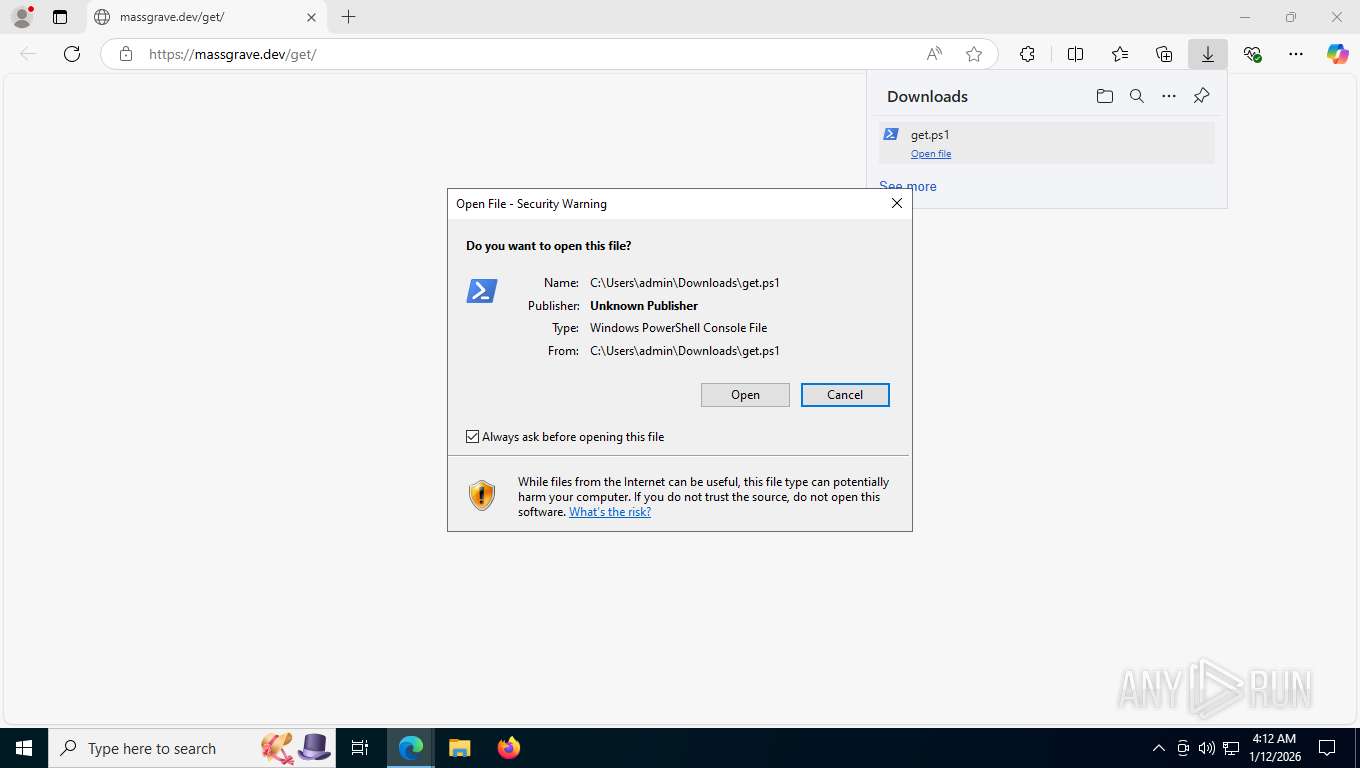
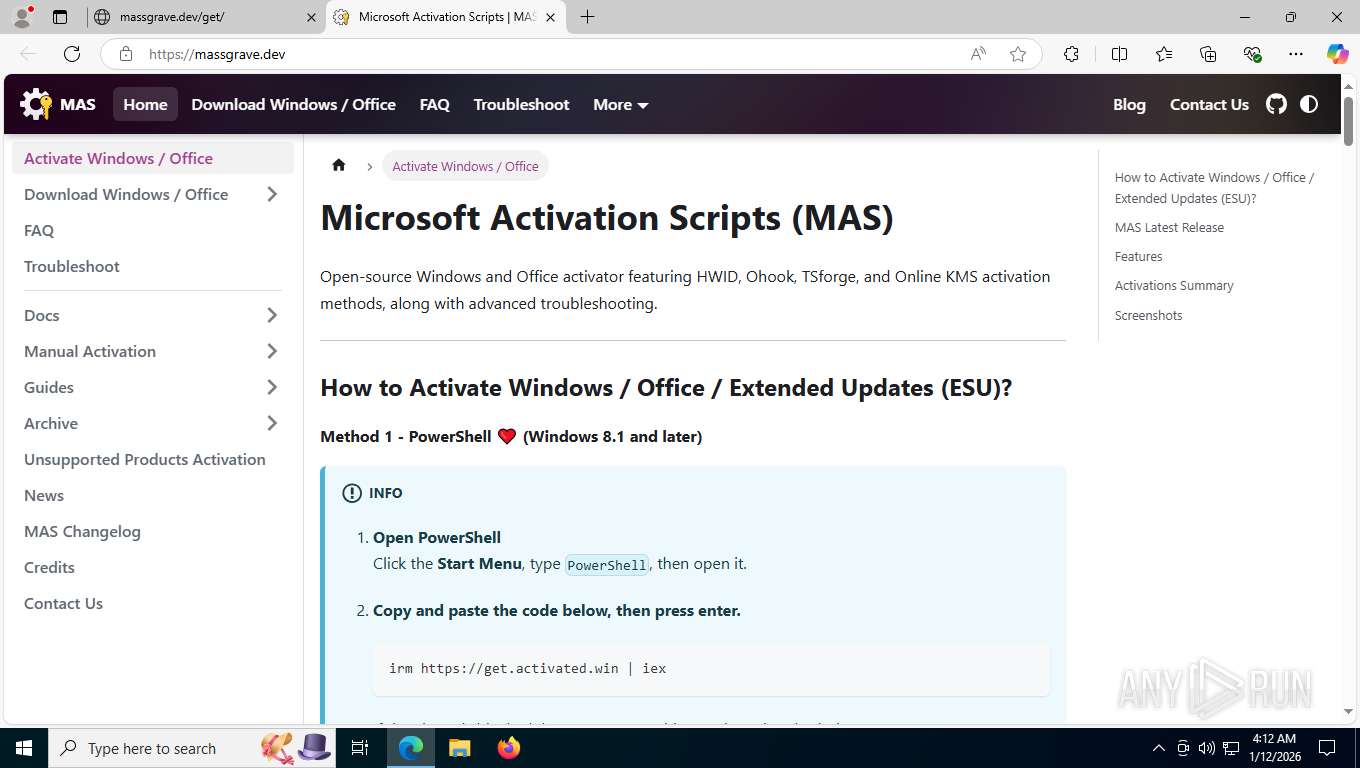
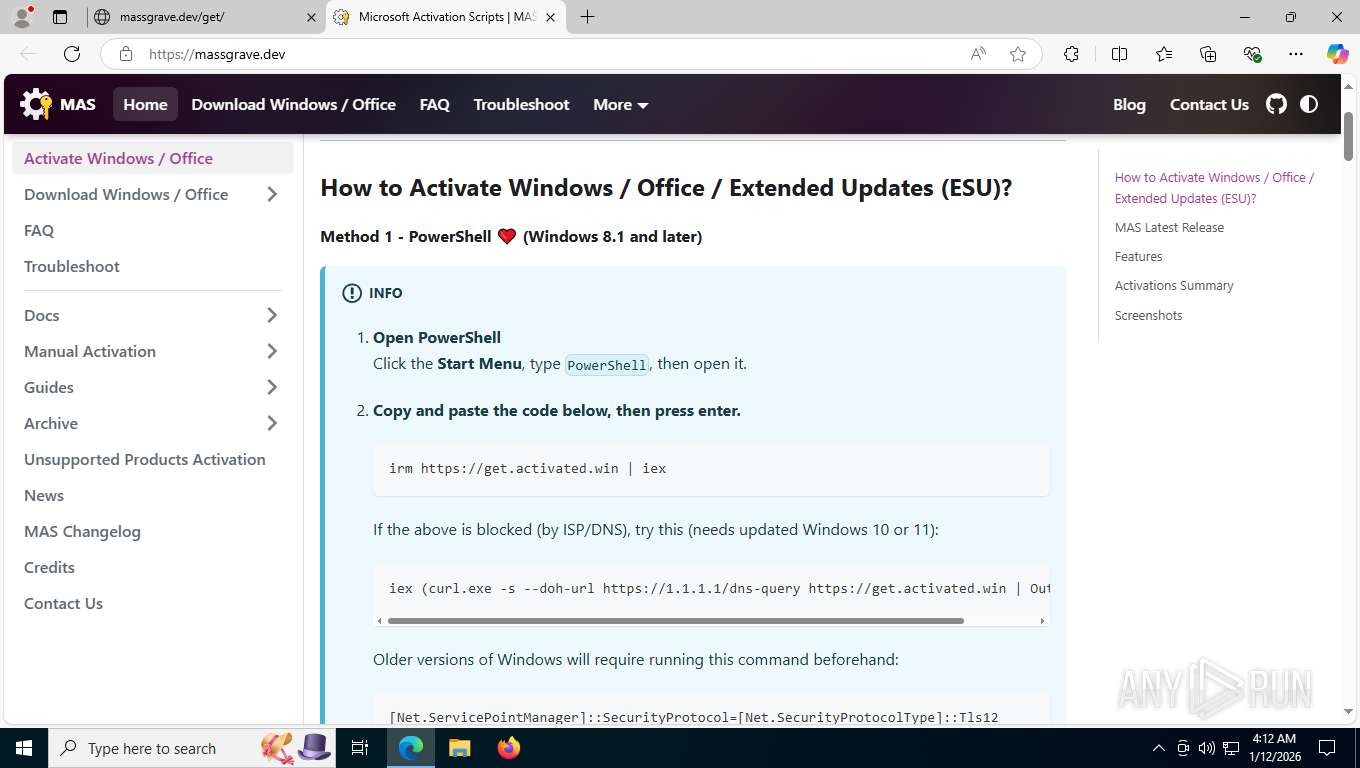
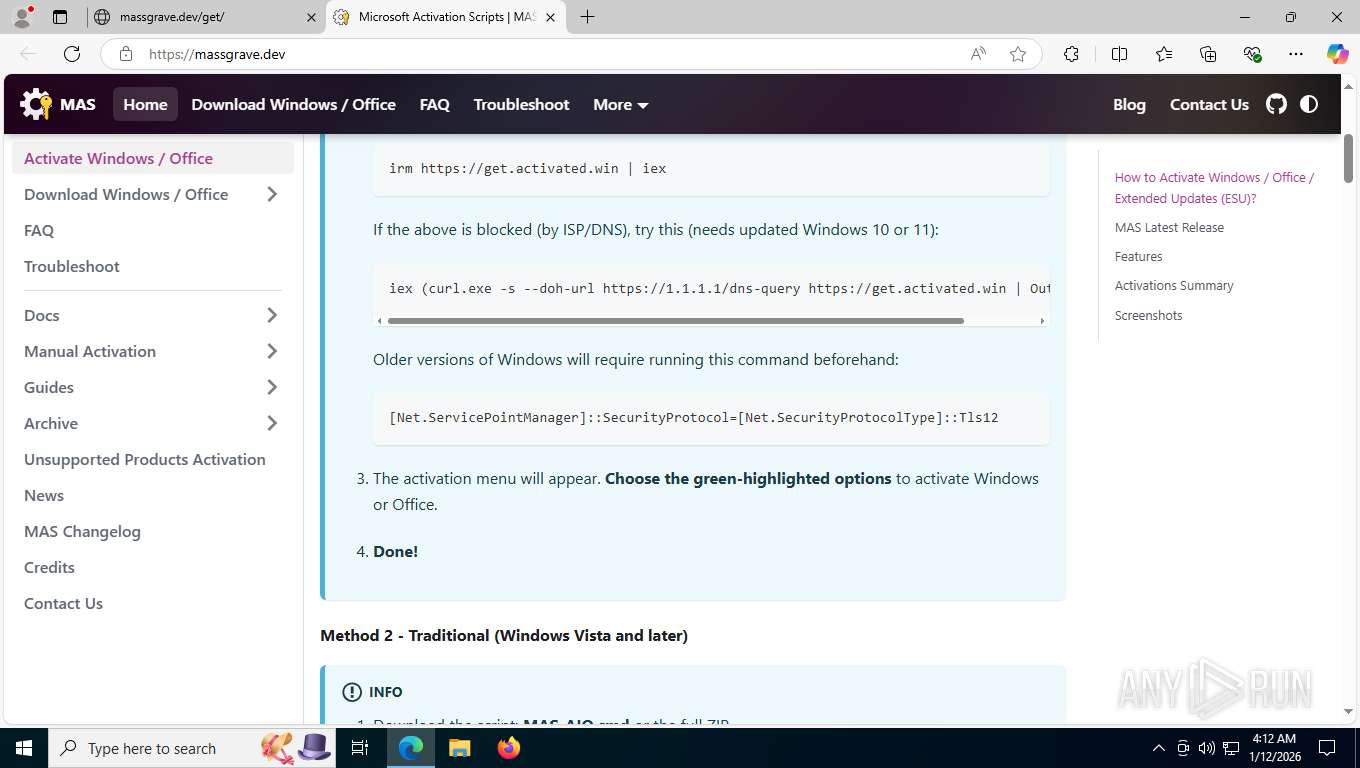
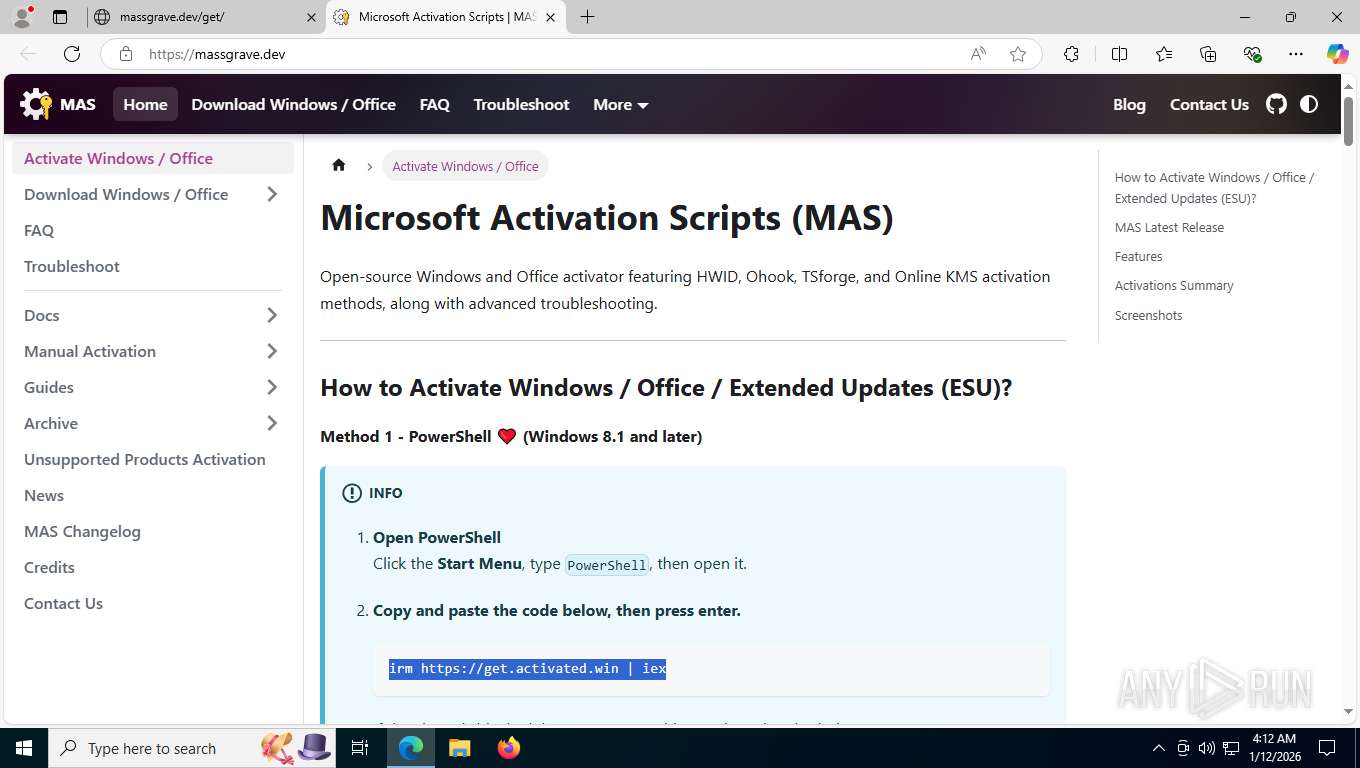
| URL: | https://massgrave.dev/get |
| Full analysis: | https://app.any.run/tasks/43e5b072-0c2f-4082-b790-04dc37b3feb4 |
| Verdict: | Malicious activity |
| Analysis date: | January 12, 2026, 09:11:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 924432E6484C1BB79492FD11F0CC882B |
| SHA1: | 7E7AEBA9BA87DAA5EC6C8E33D659DF32EAB1D4BA |
| SHA256: | 35893316F780CDFAD204FEAFE919AB8513B4DD6F6FE4A290DA30AA7A8F358E75 |
| SSDEEP: | 3:N8a0KN:2a0u |
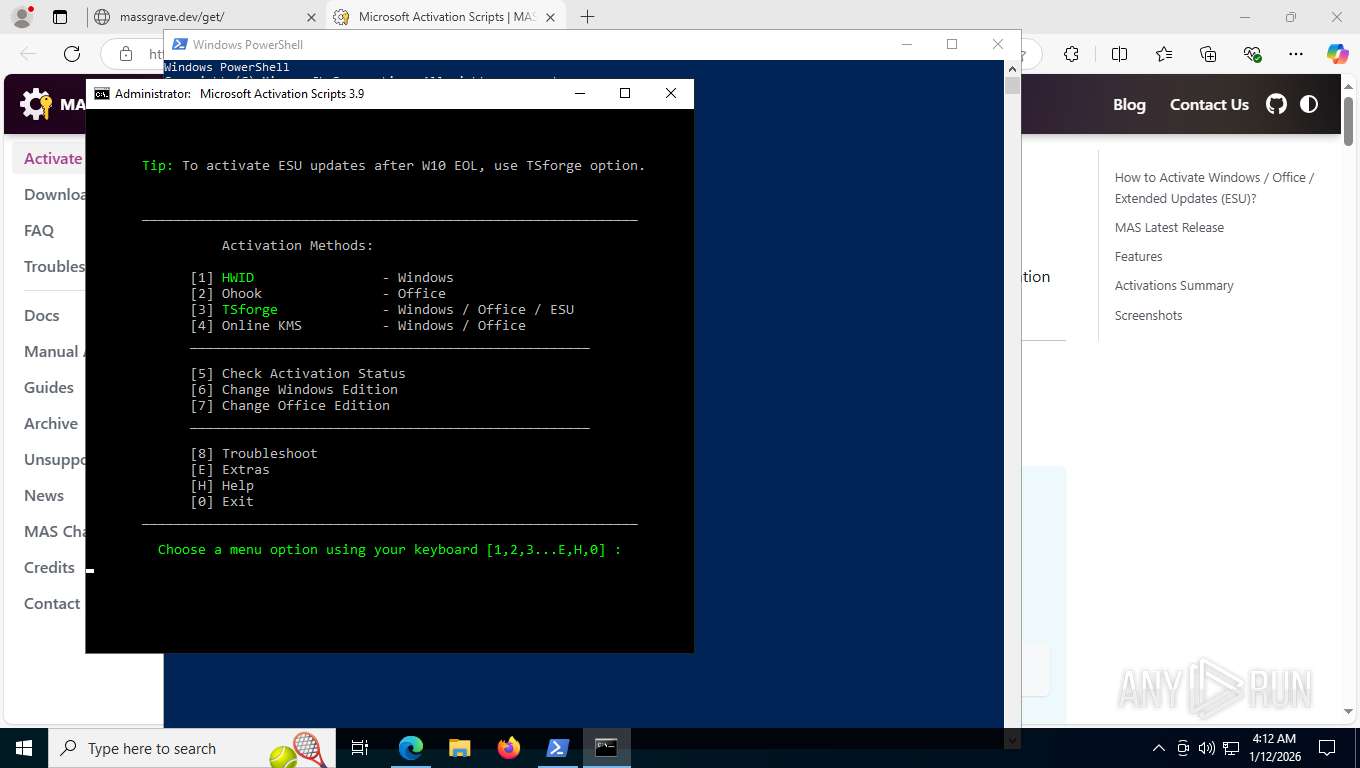
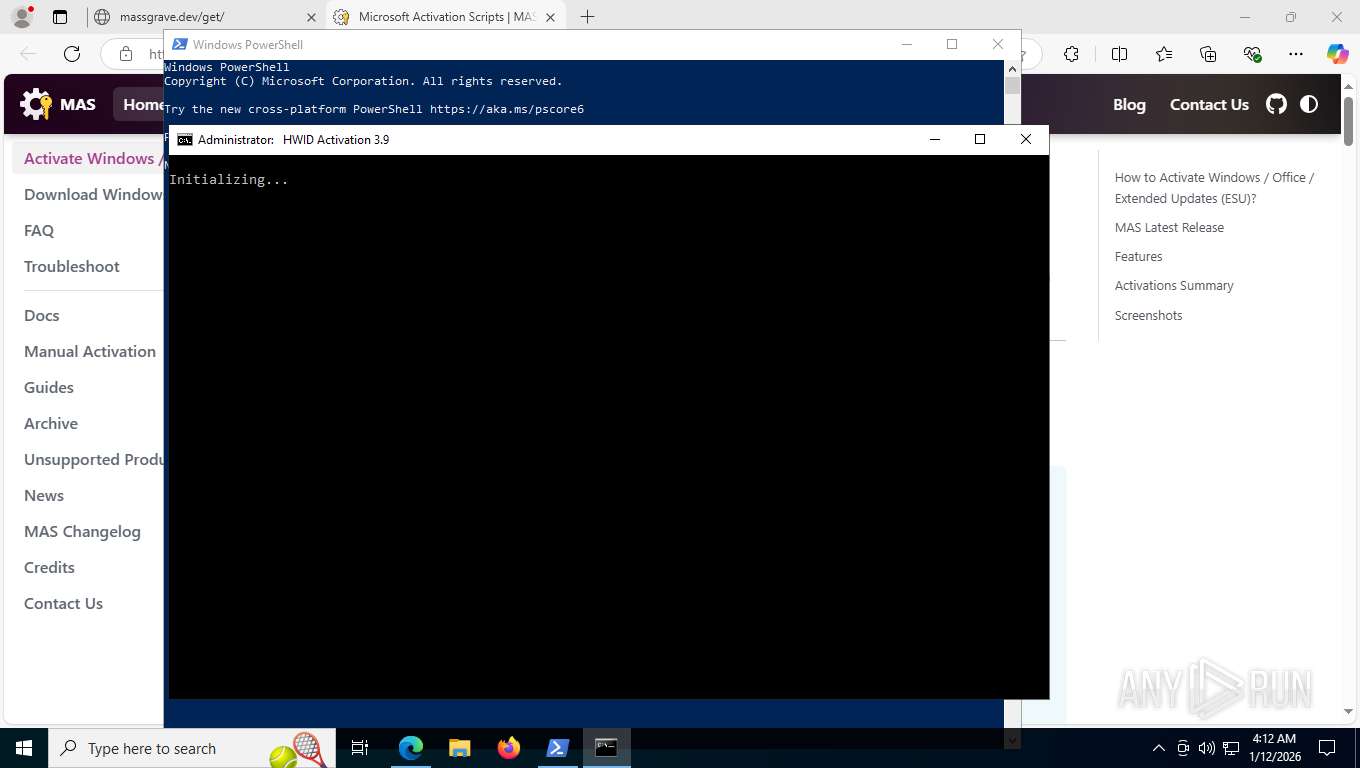
MALICIOUS
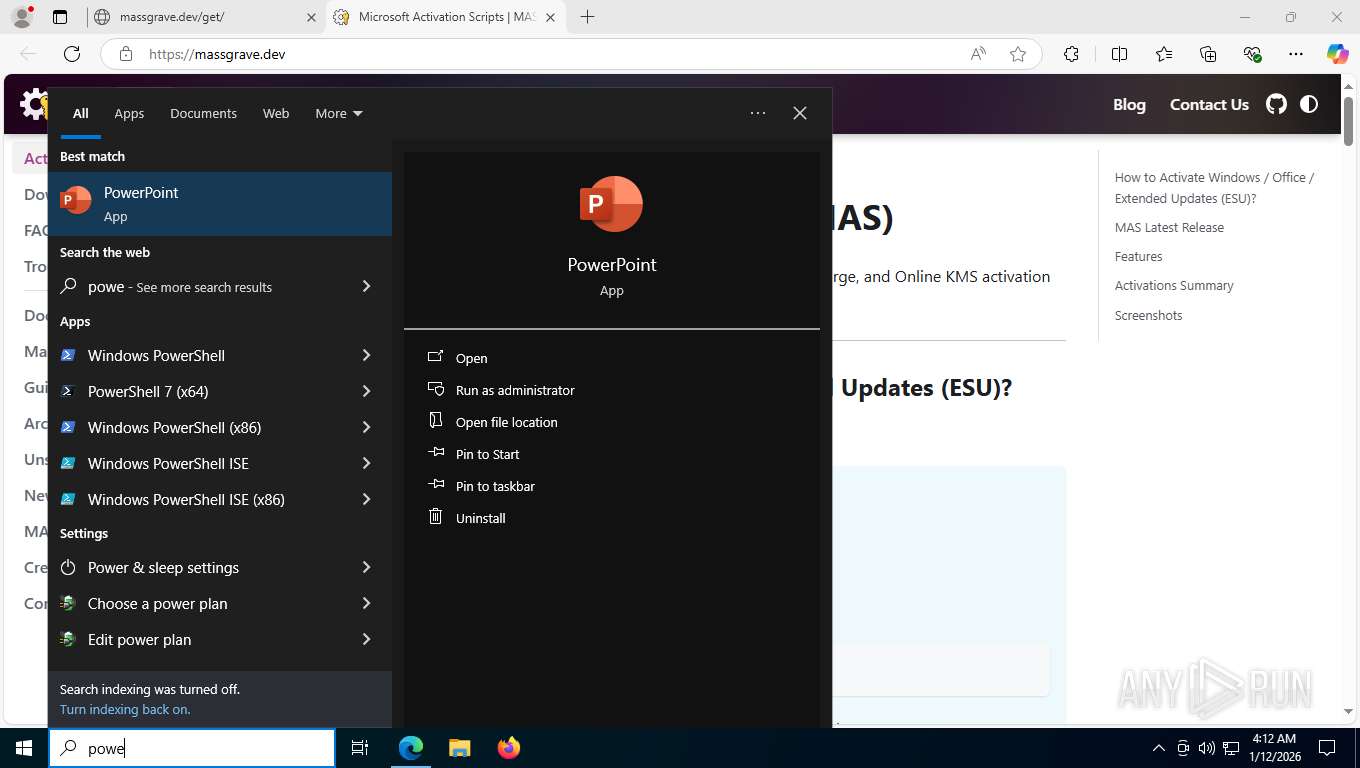
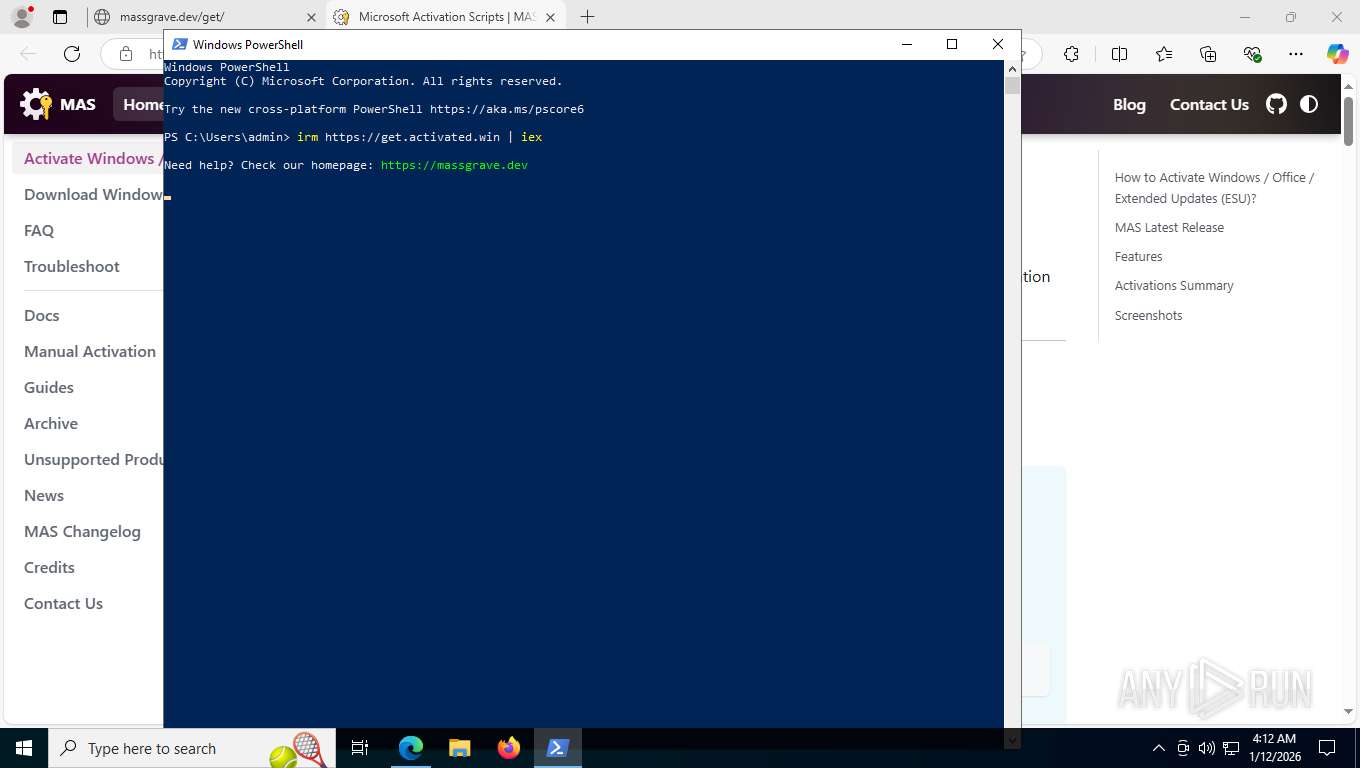
Starts POWERSHELL.EXE for commands execution
- msedge.exe (PID: 7704)
Changes powershell execution policy (Bypass)
- msedge.exe (PID: 7704)
Bypass execution policy to execute commands
- powershell.exe (PID: 8572)
SUSPICIOUS
The process executes Powershell scripts
- msedge.exe (PID: 7704)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 8544)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 8544)
- powershell.exe (PID: 8392)
- powershell.exe (PID: 1772)
- powershell.exe (PID: 2400)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8544)
- powershell.exe (PID: 8392)
- powershell.exe (PID: 1772)
- powershell.exe (PID: 2400)
Queries Computer System Information (Win32_ComputerSystem) (SCRIPT)
- powershell.exe (PID: 8544)
- powershell.exe (PID: 8392)
- powershell.exe (PID: 1772)
- powershell.exe (PID: 2400)
Starts SC.EXE for service management
- cmd.exe (PID: 6244)
- cmd.exe (PID: 752)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 8544)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6244)
- cmd.exe (PID: 752)
Executing commands from ".cmd" file
- powershell.exe (PID: 8544)
- cmd.exe (PID: 6244)
- cmd.exe (PID: 752)
Application launched itself
- cmd.exe (PID: 7200)
- cmd.exe (PID: 6244)
- cmd.exe (PID: 752)
- cmd.exe (PID: 4724)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 8544)
- cmd.exe (PID: 6244)
- cmd.exe (PID: 752)
- cmd.exe (PID: 4724)
- cmd.exe (PID: 7200)
Windows service management via SC.EXE
- sc.exe (PID: 5152)
- sc.exe (PID: 4372)
- sc.exe (PID: 3104)
Hides command output
- cmd.exe (PID: 2668)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 8332)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2668)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 1868)
- cmd.exe (PID: 752)
- cmd.exe (PID: 7692)
Converts TXT file into a string
- powershell.exe (PID: 8392)
- powershell.exe (PID: 1772)
- powershell.exe (PID: 2400)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2668)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 1868)
- cmd.exe (PID: 752)
- cmd.exe (PID: 7692)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2668)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 752)
- cmd.exe (PID: 7692)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 8544)
- powershell.exe (PID: 8392)
- powershell.exe (PID: 1772)
- powershell.exe (PID: 2400)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6244)
- cmd.exe (PID: 752)
Executes script without checking the security policy
- powershell.exe (PID: 1772)
- powershell.exe (PID: 8204)
- powershell.exe (PID: 8392)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 2400)
Obfuscation pattern (POWERSHELL)
- powershell.exe (PID: 8204)
- powershell.exe (PID: 7480)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 9144)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 8332)
Probably file/command deobfuscation
- cmd.exe (PID: 7692)
INFO
Application launched itself
- msedge.exe (PID: 7704)
Reads the computer name
- identity_helper.exe (PID: 7212)
- TextInputHost.exe (PID: 7712)
Checks supported languages
- identity_helper.exe (PID: 7212)
- TextInputHost.exe (PID: 7712)
- mode.com (PID: 8860)
- mode.com (PID: 6408)
- mode.com (PID: 8568)
- mode.com (PID: 8724)
Reads Environment values
- identity_helper.exe (PID: 7212)
Launching a file from the Downloads directory
- msedge.exe (PID: 7704)
Checks proxy server information
- powershell.exe (PID: 8544)
Disables trace logs
- powershell.exe (PID: 8544)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 8544)
- powershell.exe (PID: 8392)
- powershell.exe (PID: 1772)
- powershell.exe (PID: 2400)
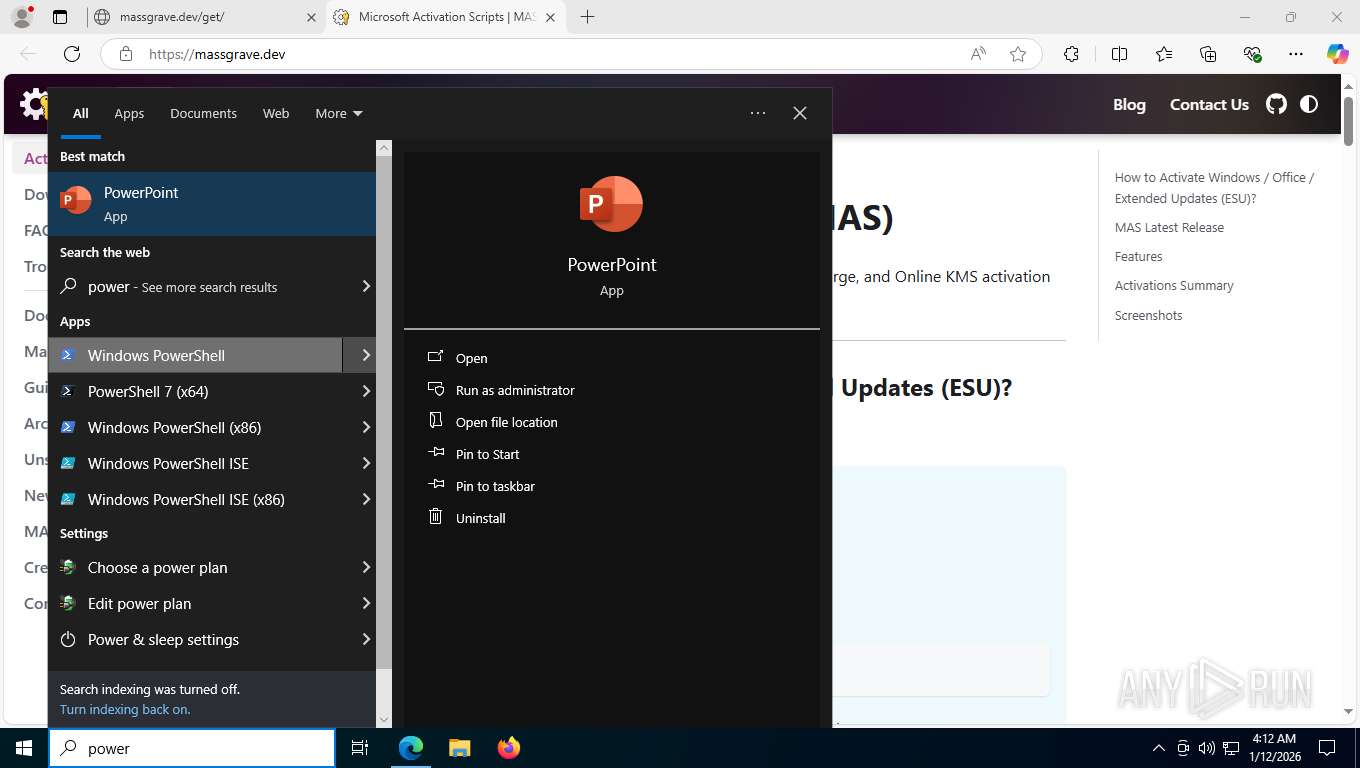
Manual execution by a user
- powershell.exe (PID: 8544)
Checks current location (POWERSHELL)
- powershell.exe (PID: 8544)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8544)
- powershell.exe (PID: 8392)
- powershell.exe (PID: 1772)
- powershell.exe (PID: 2400)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 8544)
- powershell.exe (PID: 8392)
- powershell.exe (PID: 1772)
- powershell.exe (PID: 2400)
Search a value from a registry key
- reg.exe (PID: 6080)
- reg.exe (PID: 8568)
- reg.exe (PID: 6904)
- cmd.exe (PID: 8700)
- reg.exe (PID: 8668)
- reg.exe (PID: 508)
- reg.exe (PID: 7108)
- reg.exe (PID: 4864)
- cmd.exe (PID: 6236)
Checks operating system version
- cmd.exe (PID: 6244)
- cmd.exe (PID: 752)
Starts MODE.COM to configure console settings
- mode.com (PID: 8860)
- mode.com (PID: 6408)
- mode.com (PID: 8724)
- mode.com (PID: 8568)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 9172)
- WMIC.exe (PID: 8368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
272
Monitored processes
122
Malicious processes
10
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 412 | find /i "/" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 508 | reg query HKLM\SOFTWARE\Wow6432Node\Microsoft\Office\ClickToRun\Configuration /v ProductReleaseIds | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
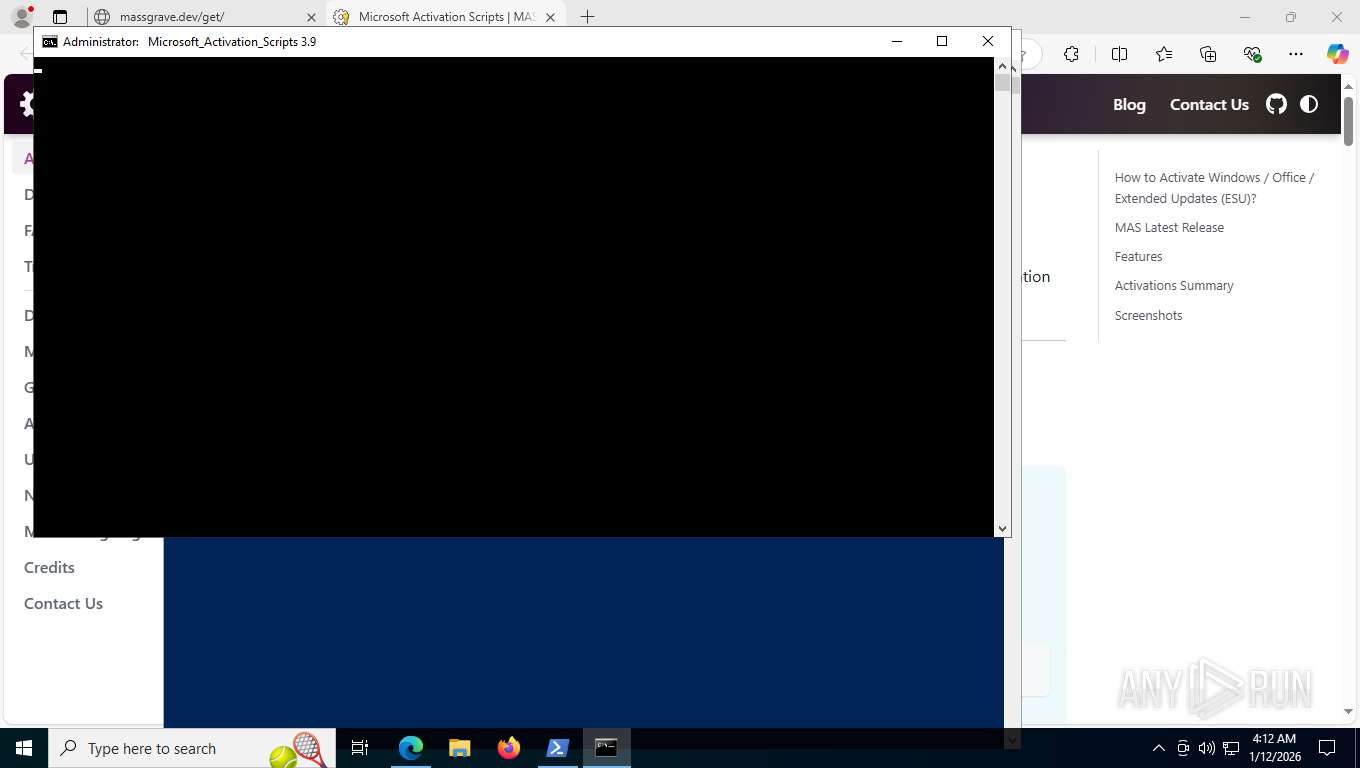
| 752 | cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\MAS_24f58cdd-af2b-435f-a1c5-f806ebe47aee.cmd" -el -qedit" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | find /i "O365" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1772 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1772 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c "if ($PSVersionTable.PSEdition -ne 'Core') {$f=[System.IO.File]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_24f58cdd-af2b-435f-a1c5-f806ebe47aee.cmd') -split ':pstst';. ([scriptblock]::Create($f[1]))}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1792 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "-el -qedit" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1868 | C:\WINDOWS\System32\cmd.exe /c "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe -nop -c $AssemblyBuilder = [AppDomain]::CurrentDomain.DefineDynamicAssembly(4, 1); $ModuleBuilder = $AssemblyBuilder.DefineDynamicModule(2, $False); $TypeBuilder = $ModuleBuilder.DefineType(0); [void]$TypeBuilder.DefinePInvokeMethod('SLGetWindowsInformationDWORD', 'slc.dll', 'Public, Static', 1, [int], @([String], [int].MakeByRefType()), 1, 3); $Sku = 0; [void]$TypeBuilder.CreateType()::SLGetWindowsInformationDWORD('Kernel-BrandingInfo', [ref]$Sku); $Sku" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2216 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
39 818
Read events
39 815
Write events
3
Delete events
0
Modification events
| (PID) Process: | (8572) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8572) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8572) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
39
Text files
236
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfdc0f.TMP | — | |
MD5:— | SHA256:— | |||
| 7704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfdc1e.TMP | — | |
MD5:— | SHA256:— | |||
| 7704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfdc1e.TMP | — | |
MD5:— | SHA256:— | |||
| 7704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfdc1e.TMP | — | |
MD5:— | SHA256:— | |||
| 7704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfdc1e.TMP | — | |
MD5:— | SHA256:— | |||
| 7704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfdc1e.TMP | — | |
MD5:— | SHA256:— | |||
| 7704 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
182
TCP/UDP connections
72
DNS requests
56
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7936 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
7936 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:UgJO5MOs9ba47WSMGNbPn-BSDesnXvObuyvqD4NJ9Qo&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 93 b | whitelisted |
7936 | msedge.exe | GET | 200 | 185.199.109.153:443 | https://massgrave.dev/get.ps1 | US | text | 485 b | unknown |
7936 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | US | text | 768 b | whitelisted |
7936 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
7936 | msedge.exe | GET | 200 | 2.16.204.141:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | NL | text | 128 Kb | whitelisted |
7936 | msedge.exe | POST | 200 | 142.250.184.227:443 | https://update.googleapis.com/service/update2/json?cup2key=14:qin2bkWSikt5D263QXLDq6W_sRa0-Kfwz-d7KpzpIis&cup2hreq=7e5b21e5db97af8b1881229f9432b76292a1c229d591902133582351fe7b12a9 | US | text | 888 b | whitelisted |
7936 | msedge.exe | GET | 200 | 2.16.204.141:443 | https://www.bing.com/api/shopping/v1/user/shoppingsettings?EnabledServiceFeaturesv2=edgeServerUX.shopping.cashbackEUMarkets,edgeServerUX.shopping.msEdgeShoppingCashbackDismissTimeout2s | NL | binary | 1.02 Kb | whitelisted |
7936 | msedge.exe | GET | 301 | 185.199.109.153:443 | https://massgrave.dev/get | US | html | 162 b | unknown |
7936 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1768209118&lafgdate=0 | US | text | 4.71 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5868 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6640 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7936 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7936 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7936 | msedge.exe | 185.199.109.153:443 | massgrave.dev | FASTLY | US | whitelisted |
7936 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7936 | msedge.exe | 104.18.23.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
massgrave.dev |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET HUNTING Powershell ScheduledTasks cmdlet Get-ScheduledTask command in HTTP Body Response |
— | — | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell NoProfile Command Received In Powershell Stagers |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Get-WmiObject Cmdlet has been detected |
— | — | A Network Trojan was detected | ET ATTACK_RESPONSE PowerShell Internet Connectivity Check via Network GUID Inbound |
— | — | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell NoProfile Command Received In Powershell Stagers |