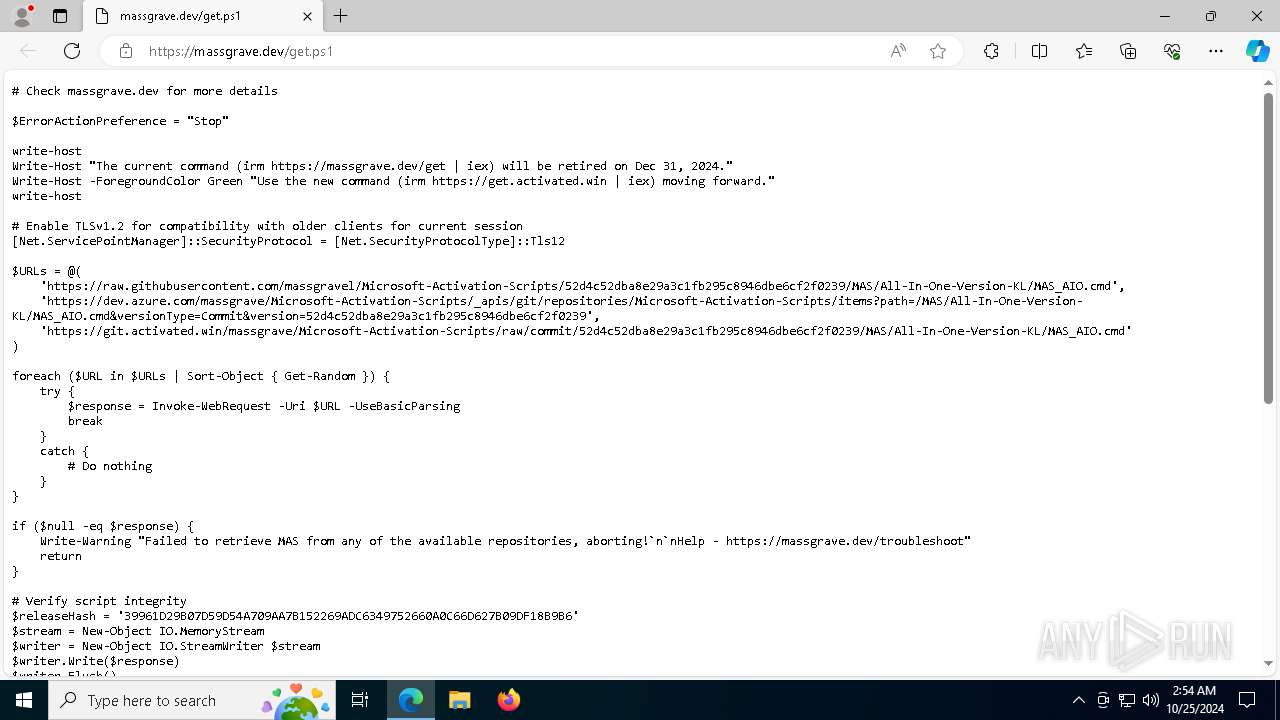
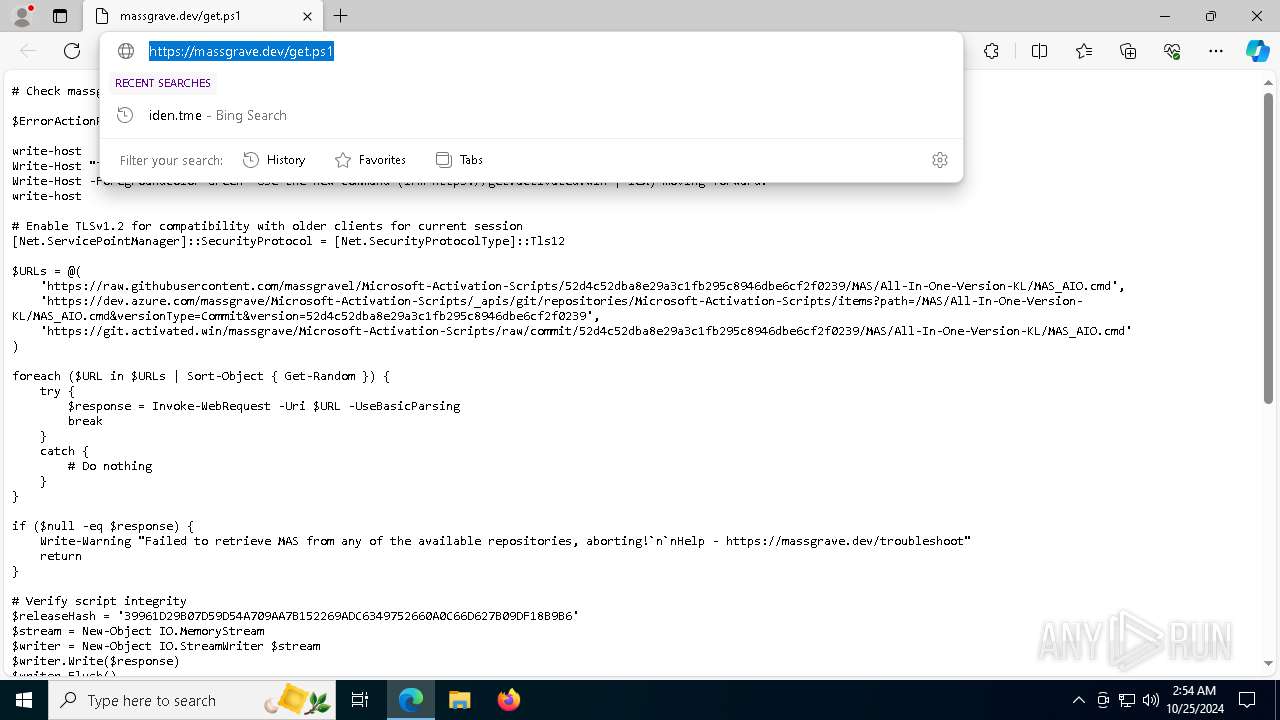
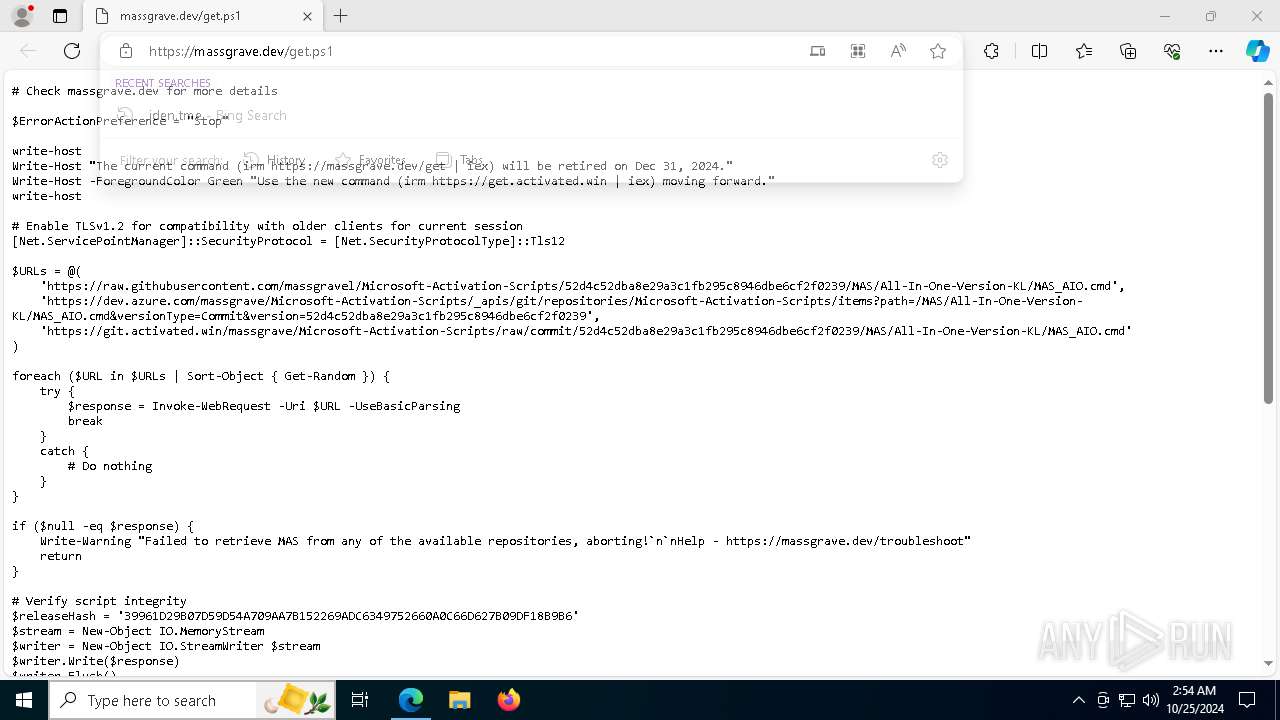
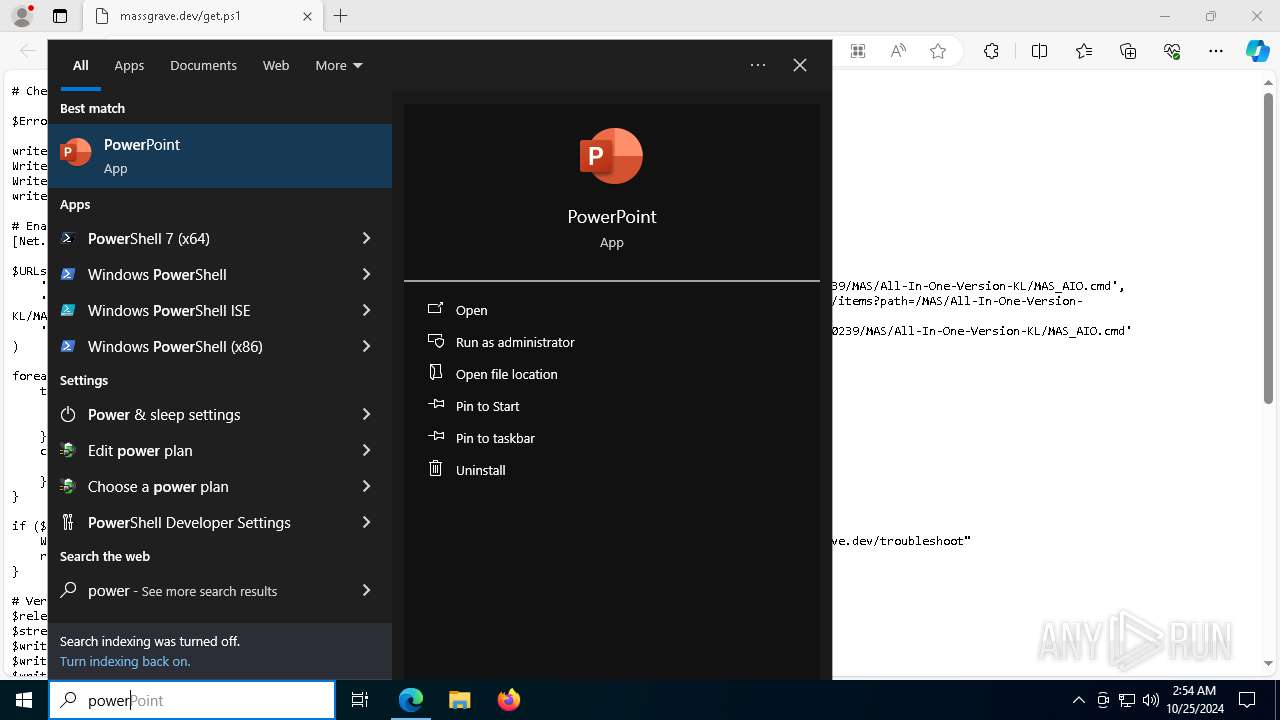
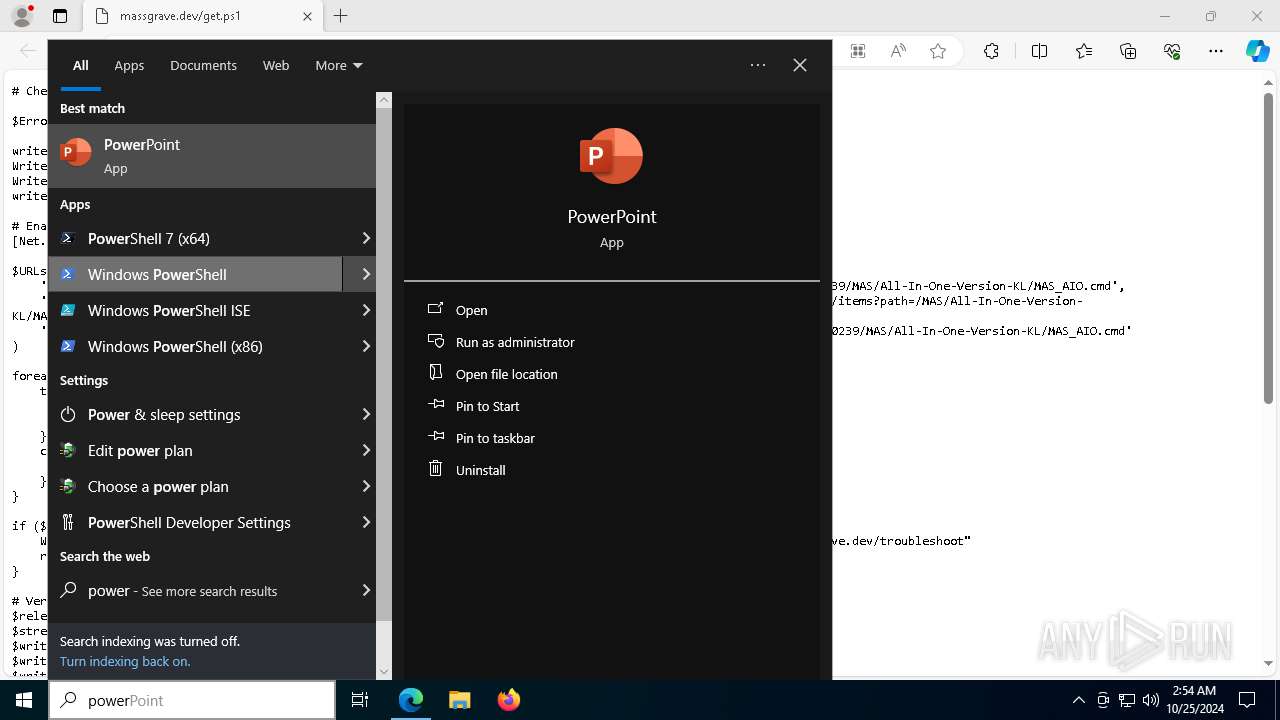
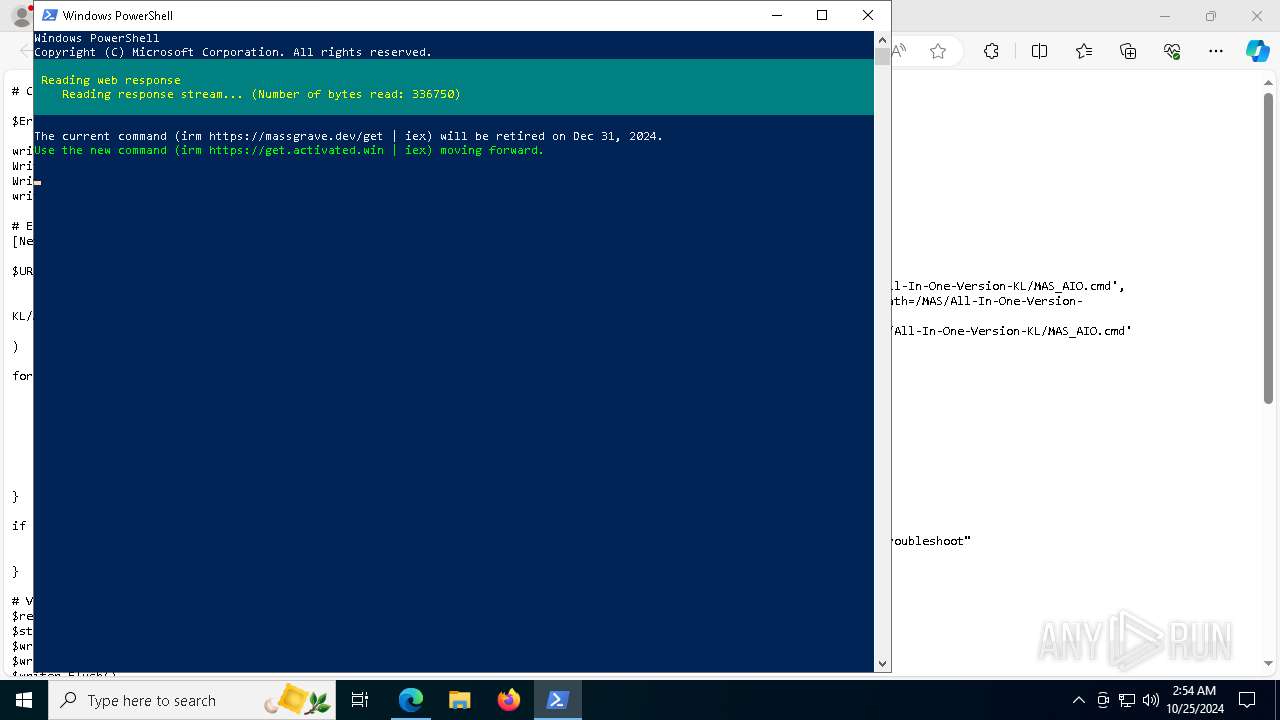
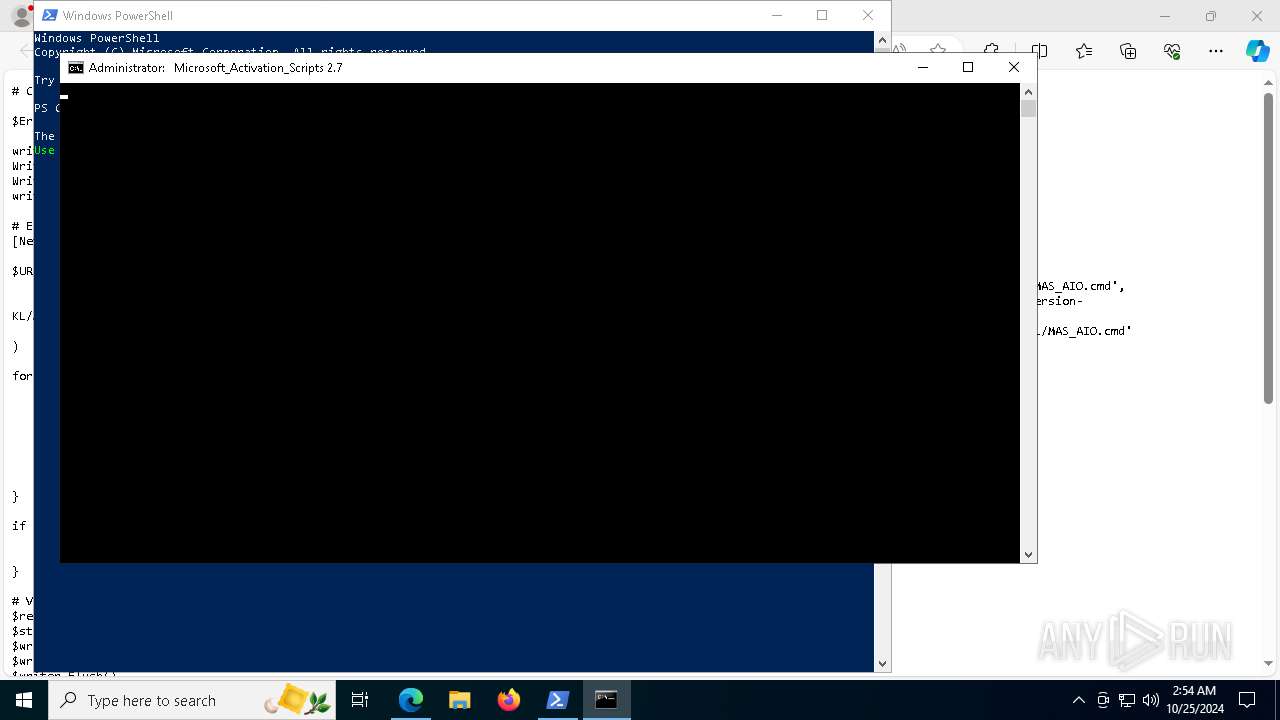
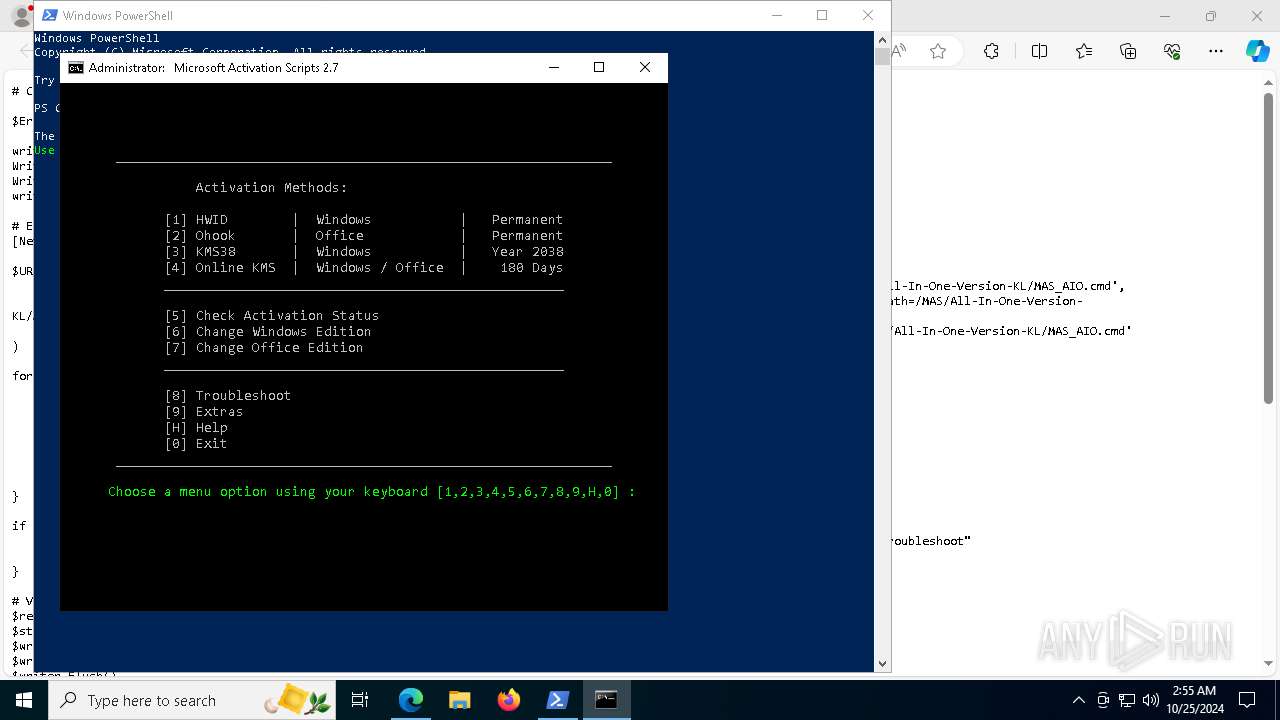
| URL: | https://massgrave.dev/get |
| Full analysis: | https://app.any.run/tasks/2b14d1ee-04d1-4f86-bb80-9dbacf604302 |
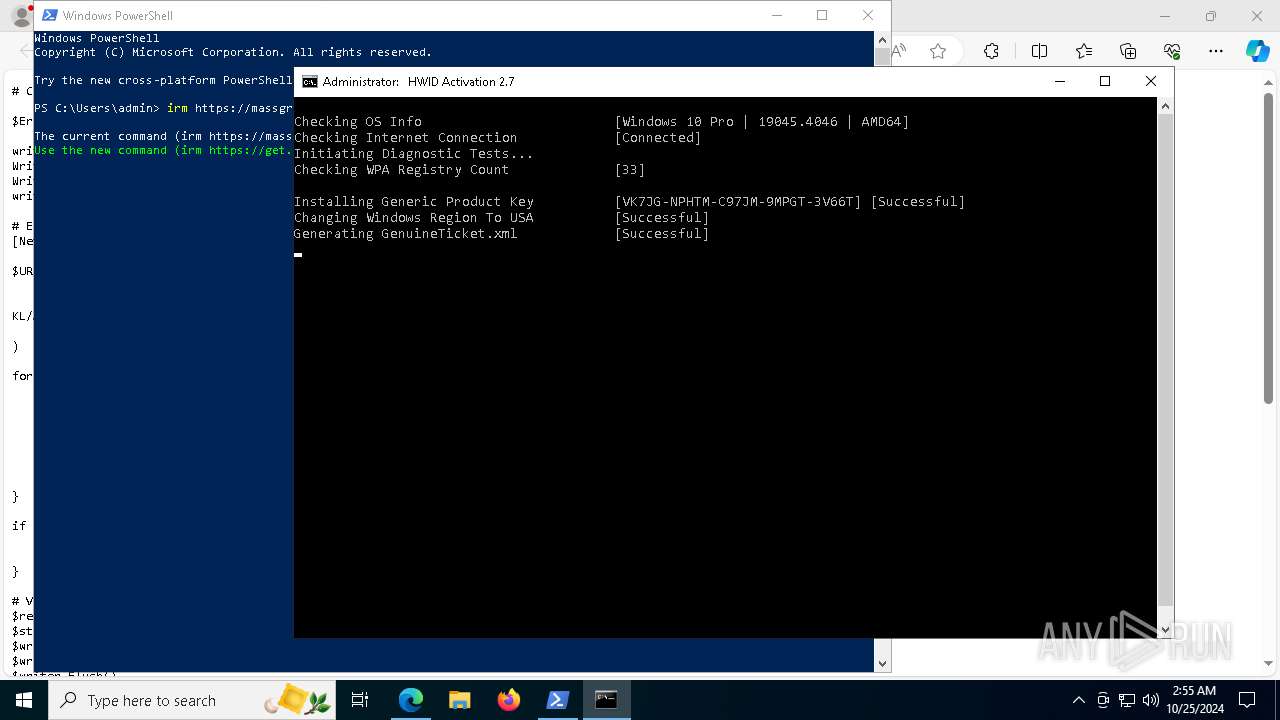
| Verdict: | Malicious activity |
| Analysis date: | October 25, 2024, 02:54:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 924432E6484C1BB79492FD11F0CC882B |
| SHA1: | 7E7AEBA9BA87DAA5EC6C8E33D659DF32EAB1D4BA |
| SHA256: | 35893316F780CDFAD204FEAFE919AB8513B4DD6F6FE4A290DA30AA7A8F358E75 |
| SSDEEP: | 3:N8a0KN:2a0u |
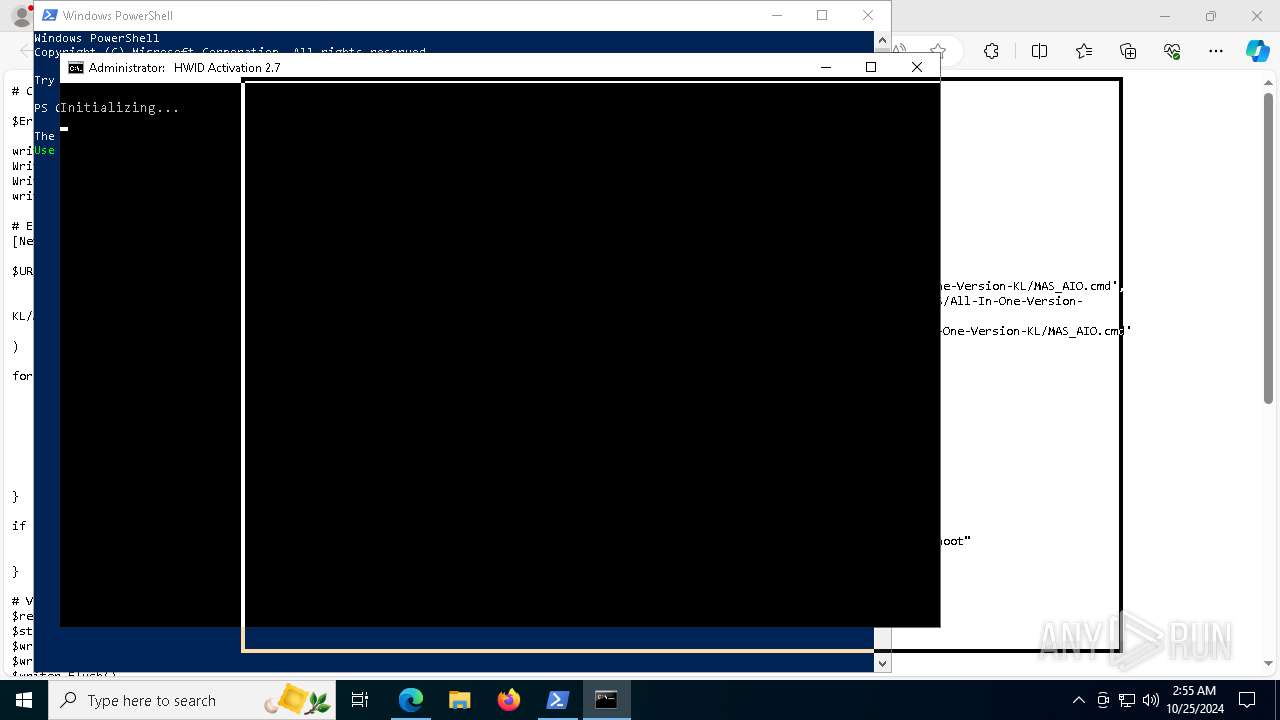
MALICIOUS
No malicious indicators.SUSPICIOUS
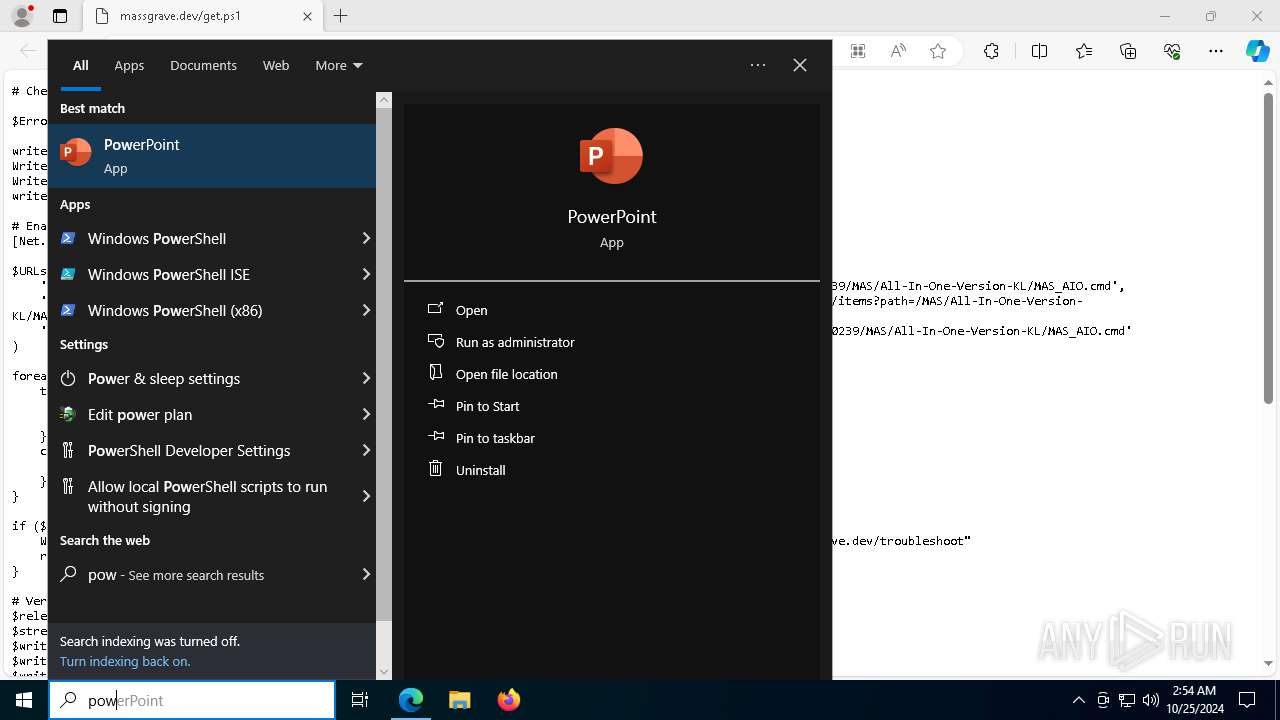
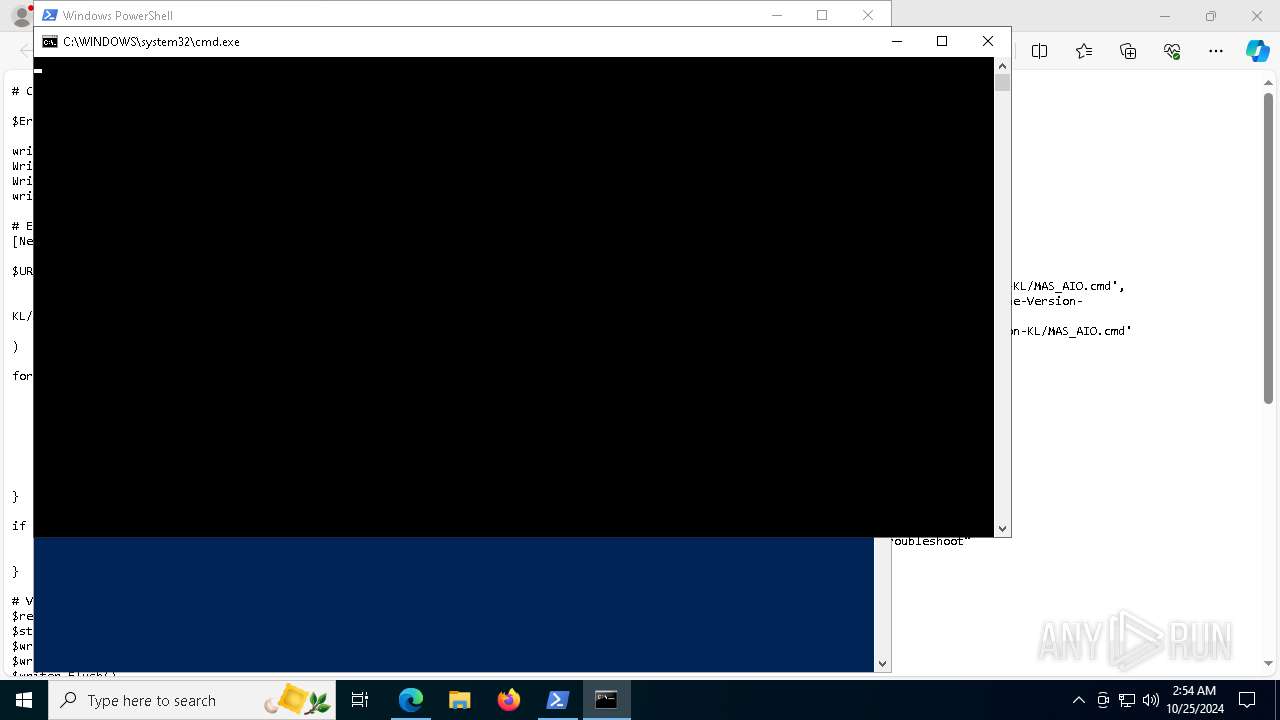
Starts CMD.EXE for commands execution
- powershell.exe (PID: 4232)
- cmd.exe (PID: 8124)
- powershell.exe (PID: 8064)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 3620)
- powershell.exe (PID: 616)
- cmd.exe (PID: 2420)
- cmd.exe (PID: 6232)
- cmd.exe (PID: 7760)
Executing commands from ".cmd" file
- powershell.exe (PID: 4232)
- cmd.exe (PID: 8124)
- powershell.exe (PID: 8064)
- cmd.exe (PID: 7892)
- powershell.exe (PID: 616)
- cmd.exe (PID: 2420)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8124)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 2420)
Starts SC.EXE for service management
- cmd.exe (PID: 8124)
- cmd.exe (PID: 2420)
- cmd.exe (PID: 7892)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6304)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 7516)
- cmd.exe (PID: 2420)
- cmd.exe (PID: 1180)
- cmd.exe (PID: 7688)
- powershell.exe (PID: 6176)
- cmd.exe (PID: 2196)
- cmd.exe (PID: 7056)
- cmd.exe (PID: 6940)
- powershell.exe (PID: 2184)
- powershell.exe (PID: 3904)
- cmd.exe (PID: 7704)
- powershell.exe (PID: 8144)
- cmd.exe (PID: 4996)
- powershell.exe (PID: 7756)
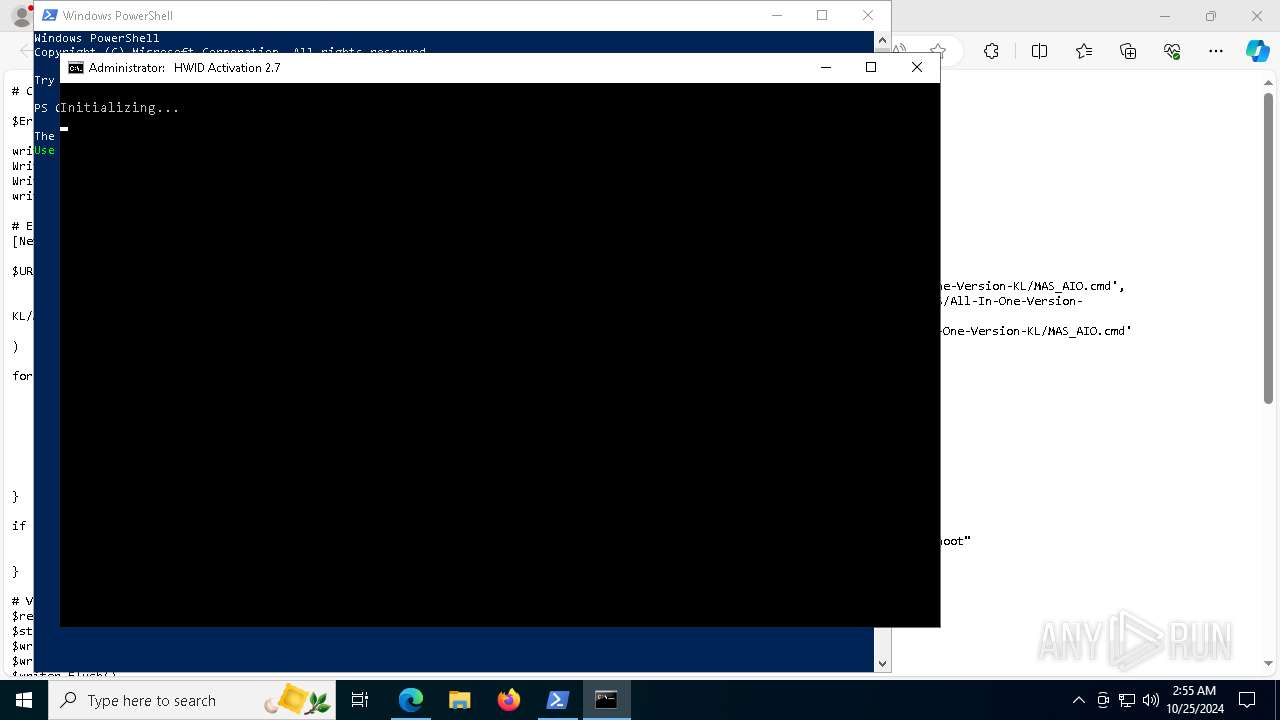
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 6304)
- cmd.exe (PID: 7704)
- cmd.exe (PID: 7516)
- cmd.exe (PID: 2420)
- cmd.exe (PID: 2196)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 6304)
- cmd.exe (PID: 7704)
- cmd.exe (PID: 7516)
- cmd.exe (PID: 2420)
- cmd.exe (PID: 2196)
Application launched itself
- cmd.exe (PID: 7760)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 2420)
- cmd.exe (PID: 6232)
- powershell.exe (PID: 6176)
- powershell.exe (PID: 7756)
- ClipUp.exe (PID: 5512)
- powershell.exe (PID: 2184)
- powershell.exe (PID: 3904)
- powershell.exe (PID: 8144)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2420)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7552)
- cmd.exe (PID: 2420)
Hides command output
- cmd.exe (PID: 1432)
- cmd.exe (PID: 4292)
- cmd.exe (PID: 2196)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 6444)
- cmd.exe (PID: 7900)
- cmd.exe (PID: 7208)
- cmd.exe (PID: 7056)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 1048)
- cmd.exe (PID: 7900)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 4292)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 6176)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 2184)
- powershell.exe (PID: 3904)
- powershell.exe (PID: 8144)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 6176)
- powershell.exe (PID: 2184)
- powershell.exe (PID: 3904)
- powershell.exe (PID: 8144)
- powershell.exe (PID: 7756)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2420)
- cmd.exe (PID: 7900)
- cmd.exe (PID: 7188)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 2420)
INFO
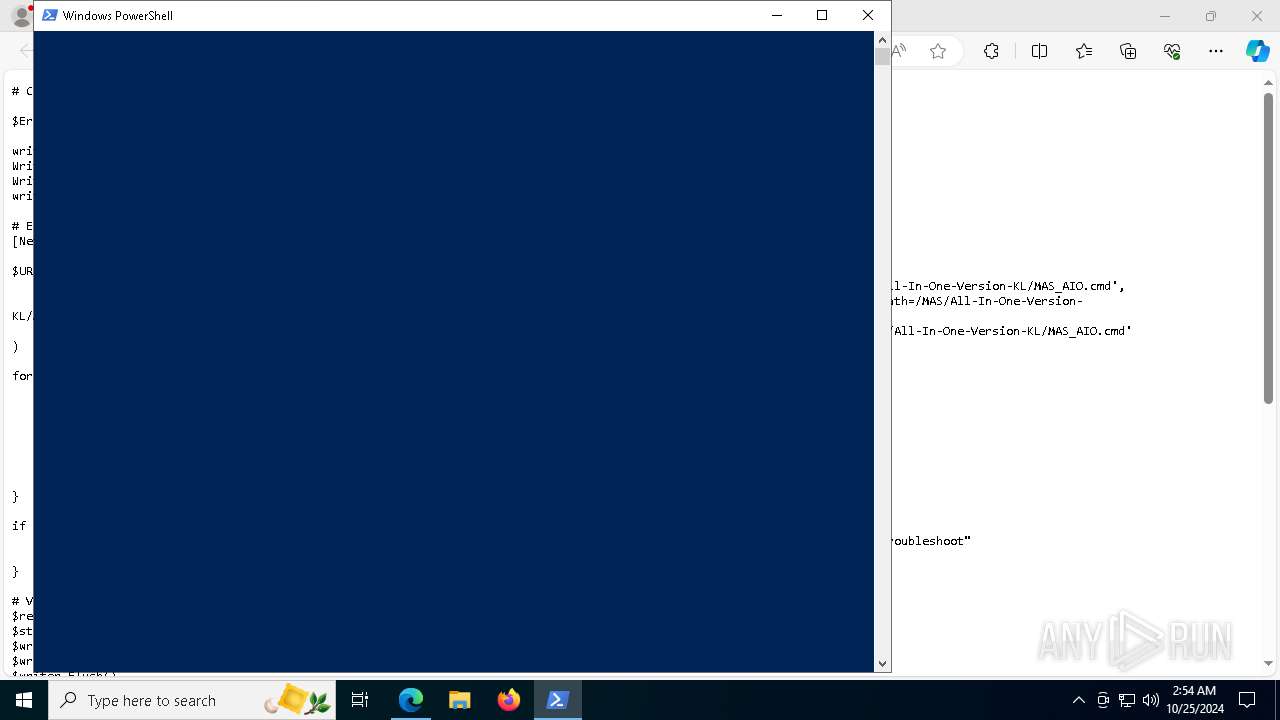
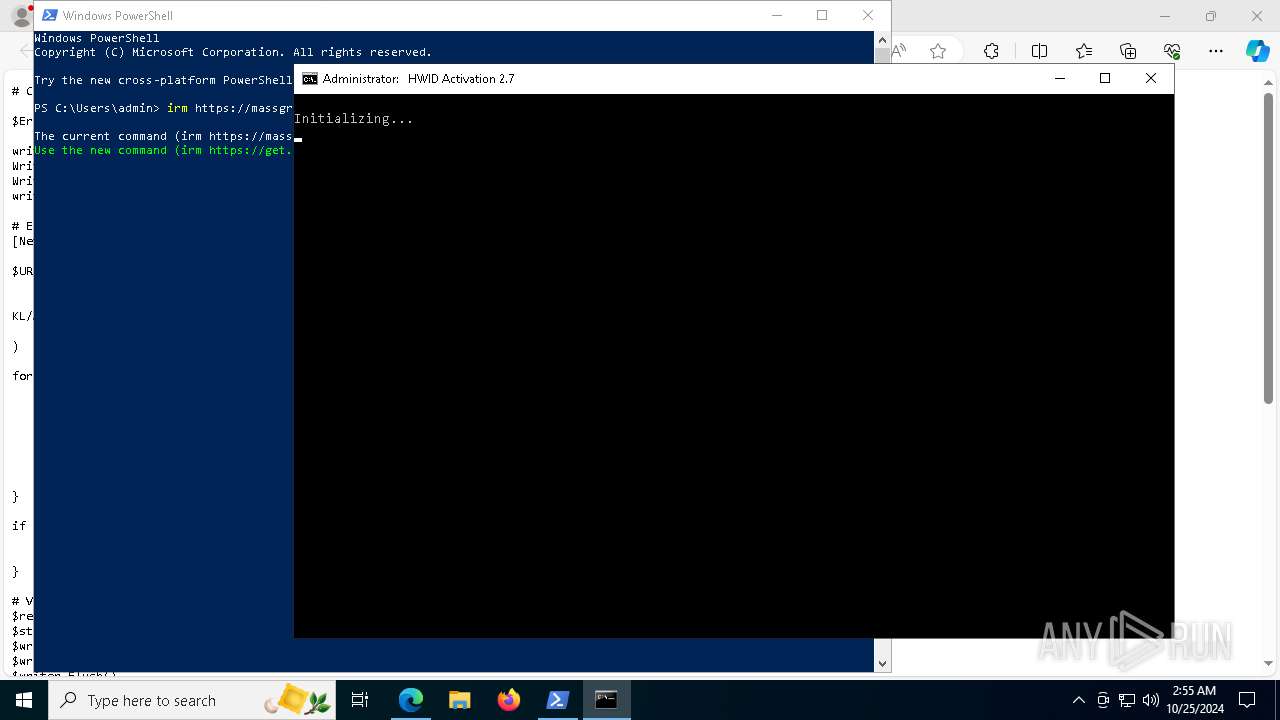
Manual execution by a user
- powershell.exe (PID: 4232)
The process uses the downloaded file
- iexplore.exe (PID: 6284)
Checks operating system version
- cmd.exe (PID: 8124)
- cmd.exe (PID: 2420)
- cmd.exe (PID: 7892)
Application launched itself
- msedge.exe (PID: 6568)
Starts MODE.COM to configure console settings
- mode.com (PID: 1112)
- mode.com (PID: 7572)
Executable content was dropped or overwritten
- msedge.exe (PID: 4004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
501
Monitored processes
354
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | reg query "HKCU\Console" /v ForceV2 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 528 | find /i "AutoPico" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | powershell.exe "$t=[AppDomain]::CurrentDomain.DefineDynamicAssembly(4, 1).DefineDynamicModule(2, $False).DefineType(0); $t.DefinePInvokeMethod('GetStdHandle', 'kernel32.dll', 22, 1, [IntPtr], @([Int32]), 1, 3).SetImplementationFlags(128); $t.DefinePInvokeMethod('SetConsoleMode', 'kernel32.dll', 22, 1, [Boolean], @([IntPtr], [Int32]), 1, 3).SetImplementationFlags(128); $k=$t.CreateType(); $b=$k::SetConsoleMode($k::GetStdHandle(-10), 0x0080); & cmd.exe '/c' '"""C:\Users\admin\AppData\Local\Temp\MAS_539f87bd-1e79-49f0-8021-e2e622509762.cmd""" -el -el -qedit'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | find /i "R@1n" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 624 | reg query HKLM\SYSTEM\CurrentControlSet\Services\sppsvc /v DependOnService | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 692 | reg query HKLM\SYSTEM\CurrentControlSet\Services\wuauserv /v DisplayName | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | reg query HKLM\SYSTEM\CurrentControlSet\Services\LicenseManager /v Start | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 696 | reg query HKLM\SYSTEM\CurrentControlSet\Services\wuauserv /v ErrorControl | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 696 | sc start Winmgmt | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 780 | reg query HKLM\SYSTEM\CurrentControlSet\Services\ClipSVC /v ObjectName | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
57 393
Read events
57 374
Write events
19
Delete events
0
Modification events
| (PID) Process: | (6284) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6284) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6284) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6284) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (6284) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (6284) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
1
Suspicious files
300
Text files
158
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF8b9a4.TMP | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF8b9b4.TMP | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF8b9c3.TMP | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF8b9b4.TMP | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF8b9d3.TMP | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
111
DNS requests
70
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 206 | 23.32.238.121:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ac8d4a99-4067-46d7-b9be-0967a17f0d8d?P1=1730362105&P2=404&P3=2&P4=EzH5a2%2bPdzVTc8dYPw4z4OfDa%2frO4ikfw31WWQm8RzT9lUnTxb4SABuJ1i410wsPtVfWCzv7qPCx5EGNqMXT%2bw%3d%3d | unknown | — | — | whitelisted |
6384 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4076 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 23.32.238.121:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ac8d4a99-4067-46d7-b9be-0967a17f0d8d?P1=1730362105&P2=404&P3=2&P4=EzH5a2%2bPdzVTc8dYPw4z4OfDa%2frO4ikfw31WWQm8RzT9lUnTxb4SABuJ1i410wsPtVfWCzv7qPCx5EGNqMXT%2bw%3d%3d | unknown | — | — | whitelisted |
5580 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 206 | 23.32.238.121:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a081ba6e-045a-42ea-b073-95dd0653279b?P1=1730343496&P2=404&P3=2&P4=TfvxuS%2bkATjQU5zsp0Ln9wpy6G6AZxHVq0pDJhr1sQPfqRsLRYkBX4M6zhagda7MJudKizkjMn7QqypY66VkQA%3d%3d | unknown | — | — | whitelisted |
— | — | GET | 206 | 23.32.238.121:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a081ba6e-045a-42ea-b073-95dd0653279b?P1=1730343496&P2=404&P3=2&P4=TfvxuS%2bkATjQU5zsp0Ln9wpy6G6AZxHVq0pDJhr1sQPfqRsLRYkBX4M6zhagda7MJudKizkjMn7QqypY66VkQA%3d%3d | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 23.32.238.121:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a081ba6e-045a-42ea-b073-95dd0653279b?P1=1730343496&P2=404&P3=2&P4=TfvxuS%2bkATjQU5zsp0Ln9wpy6G6AZxHVq0pDJhr1sQPfqRsLRYkBX4M6zhagda7MJudKizkjMn7QqypY66VkQA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6568 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5068 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5068 | msedge.exe | 104.21.22.3:443 | massgrave.dev | CLOUDFLARENET | — | unknown |
5068 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5068 | msedge.exe | 13.107.246.64:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
massgrave.dev |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |