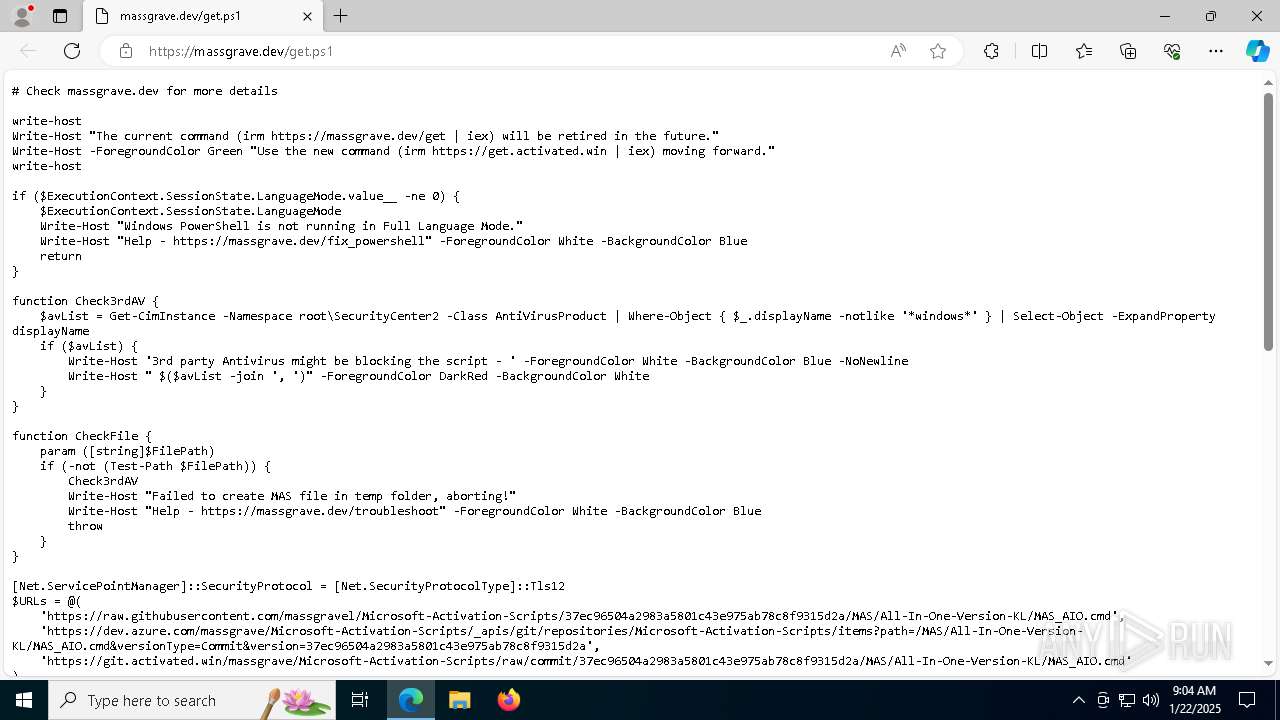
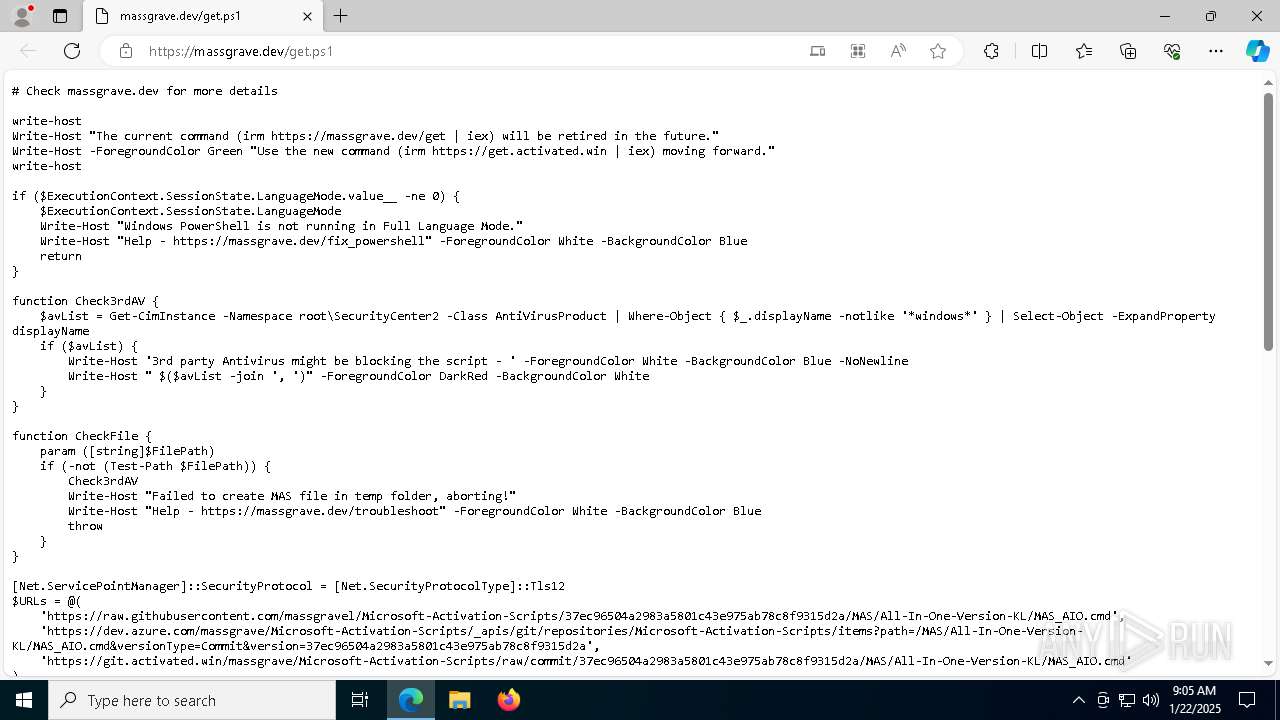
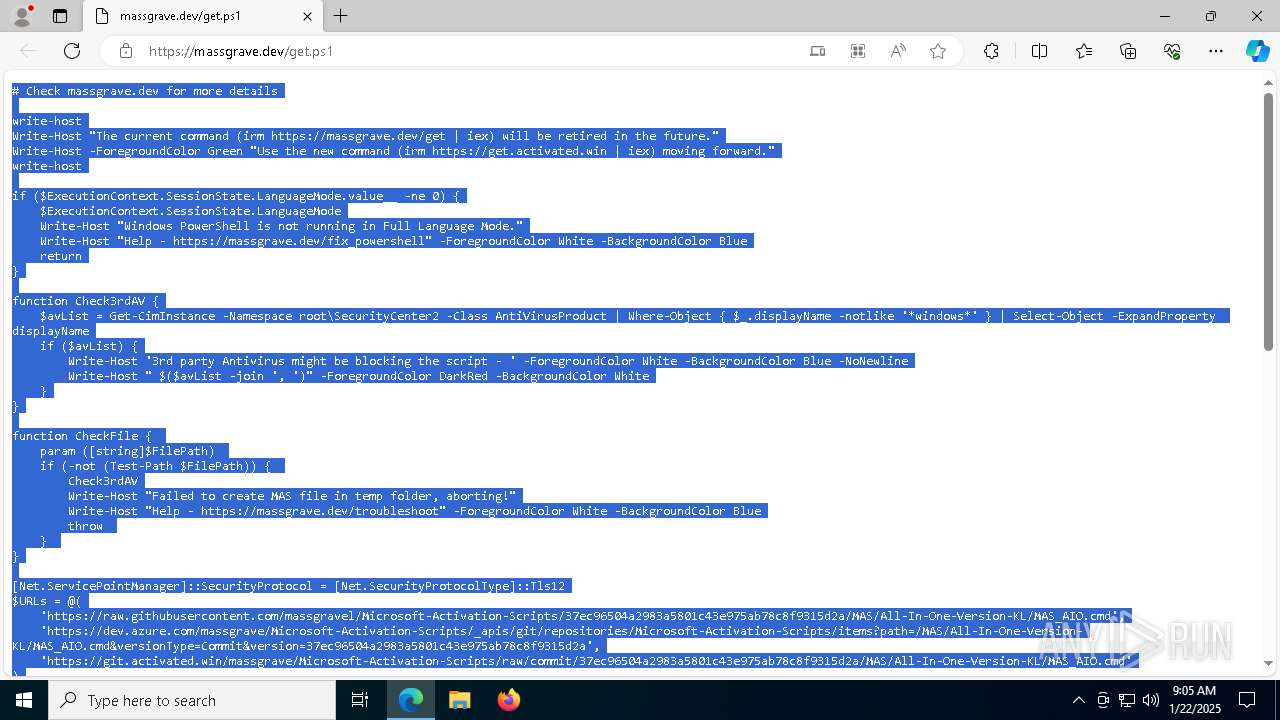
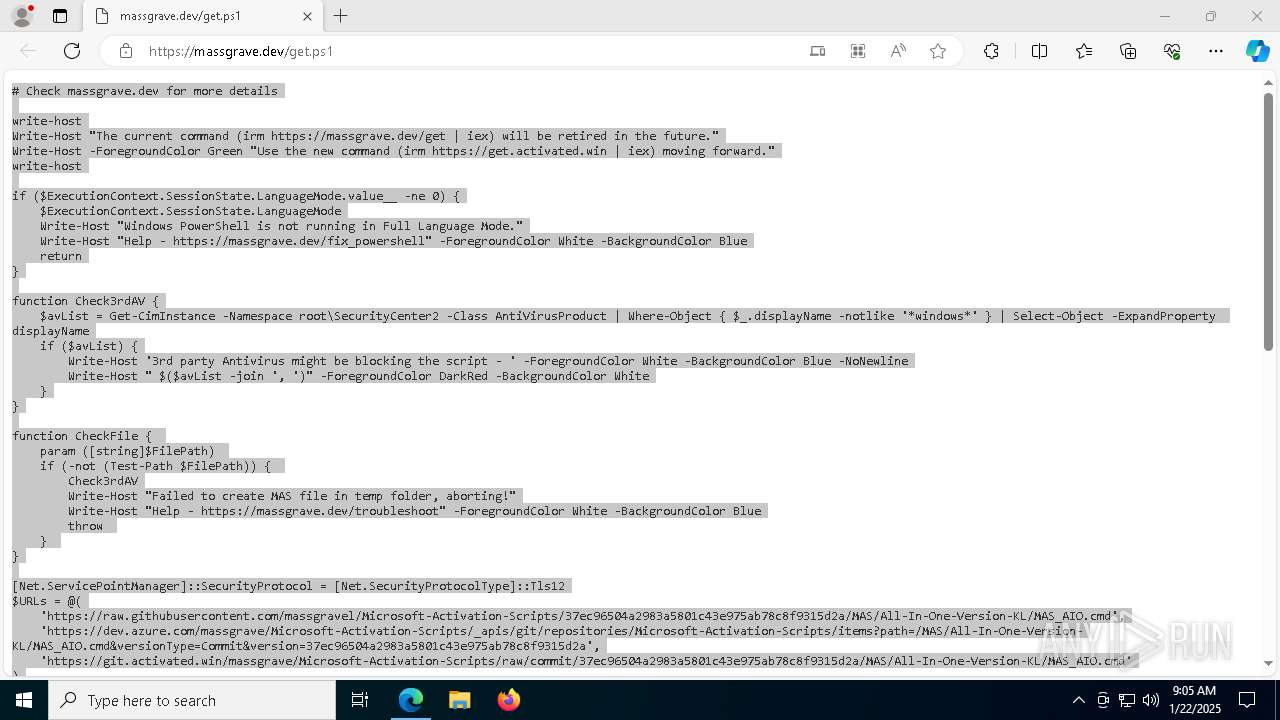
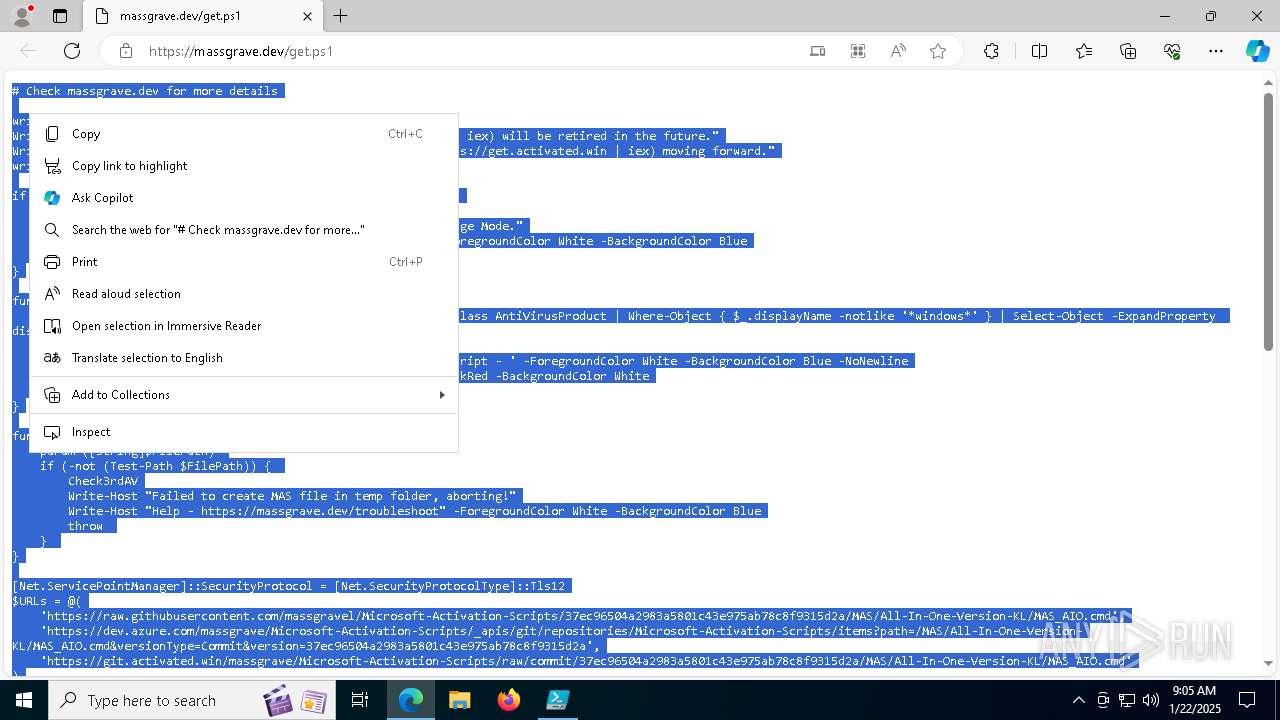
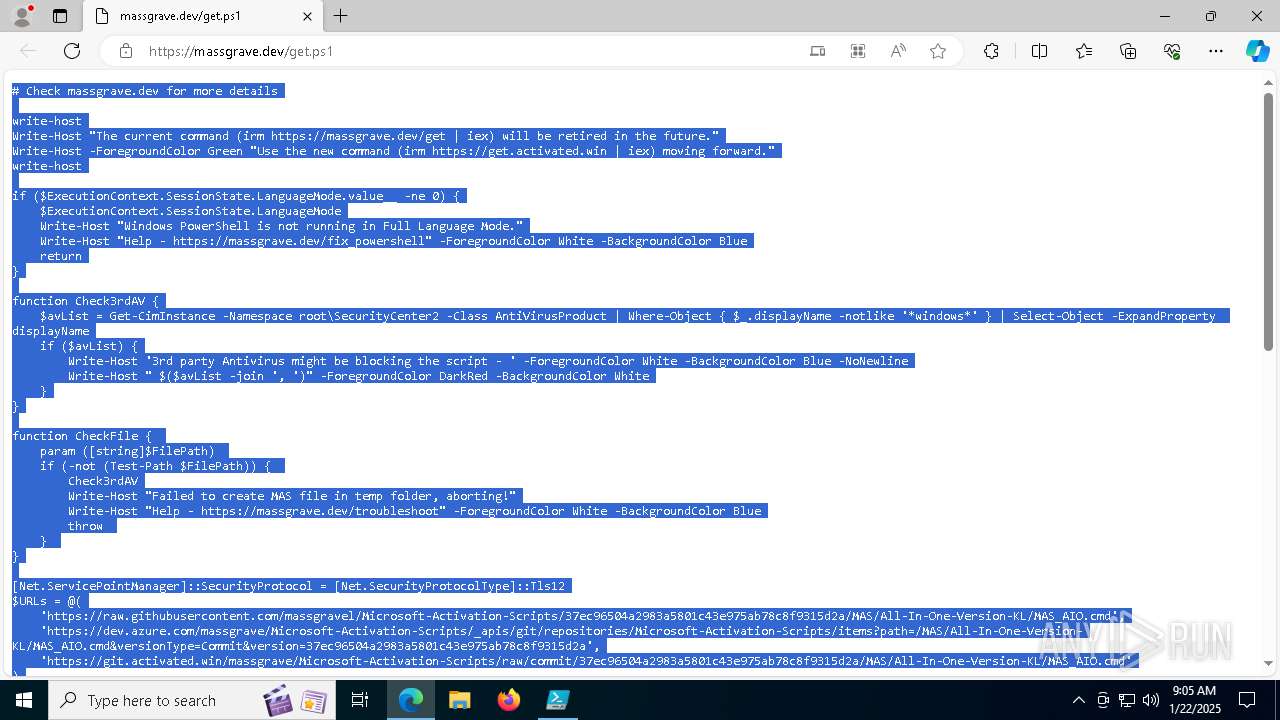
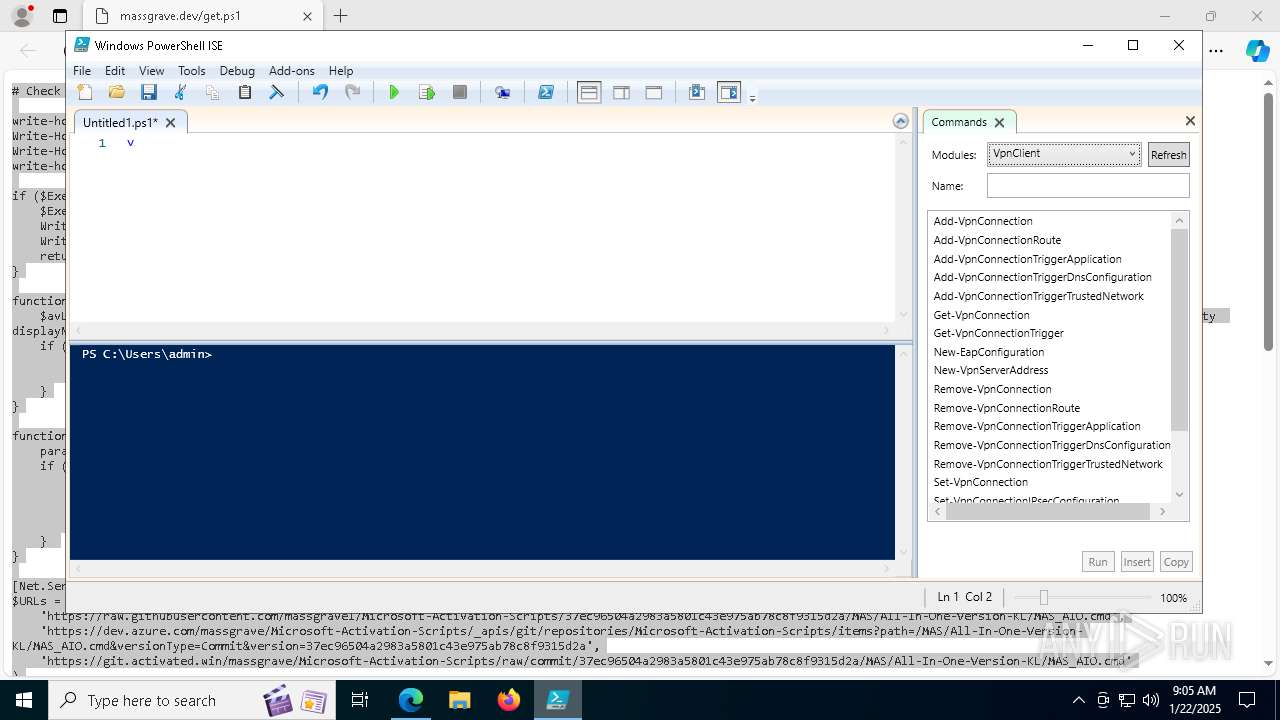
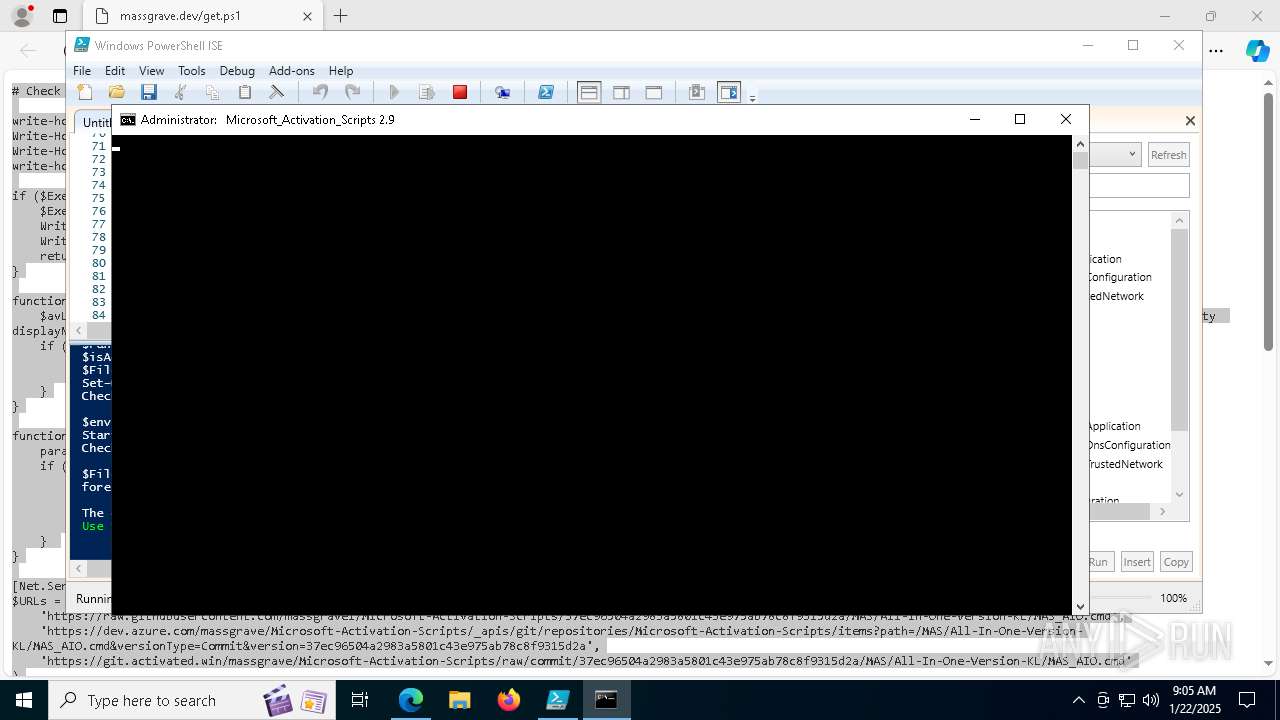
| URL: | https://massgrave.dev/get |
| Full analysis: | https://app.any.run/tasks/03ad0a92-4518-42ab-a030-5c5087ed36f4 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2025, 09:04:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 924432E6484C1BB79492FD11F0CC882B |
| SHA1: | 7E7AEBA9BA87DAA5EC6C8E33D659DF32EAB1D4BA |
| SHA256: | 35893316F780CDFAD204FEAFE919AB8513B4DD6F6FE4A290DA30AA7A8F358E75 |
| SSDEEP: | 3:N8a0KN:2a0u |
MALICIOUS
No malicious indicators.SUSPICIOUS
Gets or sets the security protocol (POWERSHELL)
- powershell_ise.exe (PID: 6004)
Uses base64 encoding (POWERSHELL)
- powershell_ise.exe (PID: 6004)
- powershell.exe (PID: 2136)
- powershell.exe (PID: 6972)
Gets content of a file (POWERSHELL)
- powershell_ise.exe (PID: 6004)
- powershell.exe (PID: 2136)
- powershell.exe (PID: 6972)
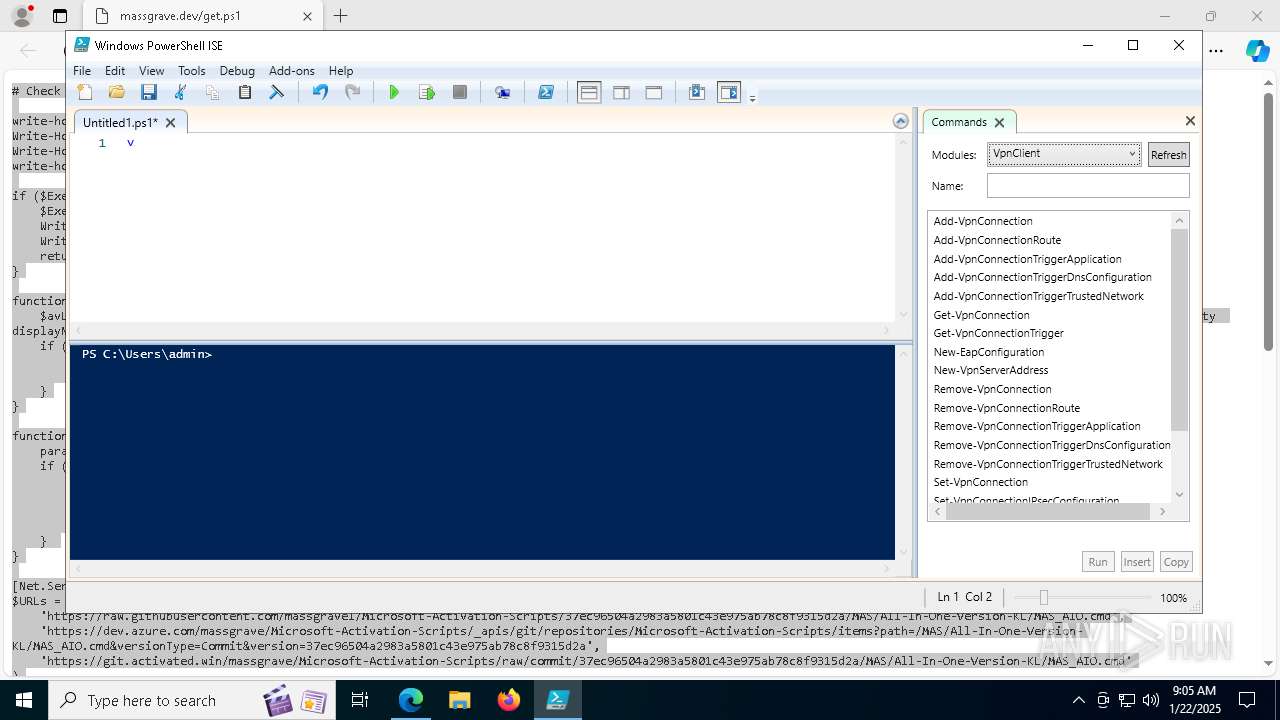
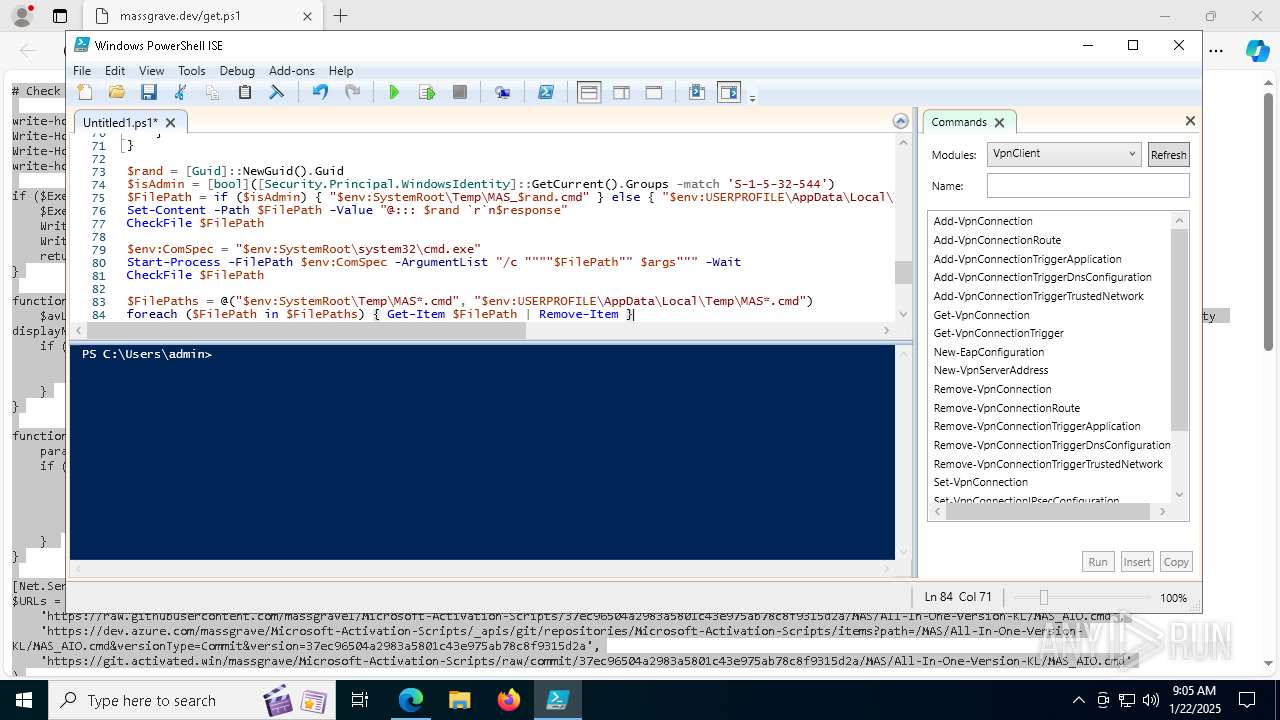
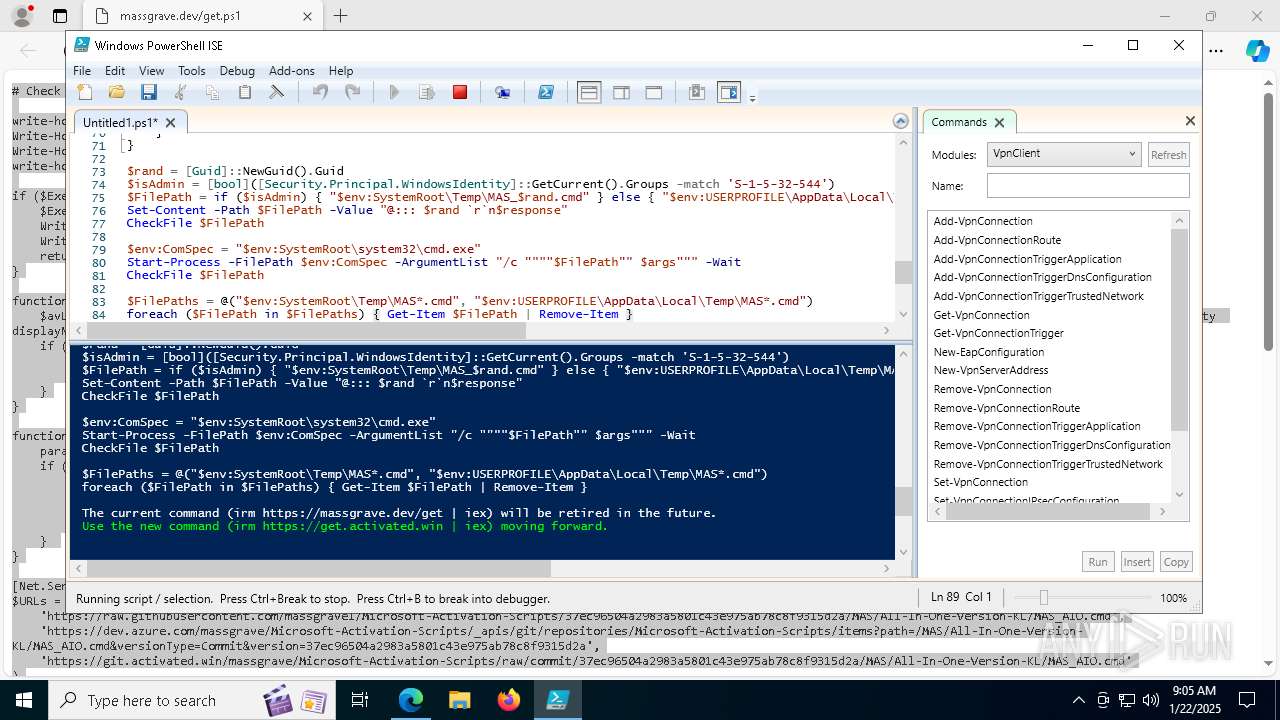
Creates new GUID (POWERSHELL)
- powershell_ise.exe (PID: 6004)
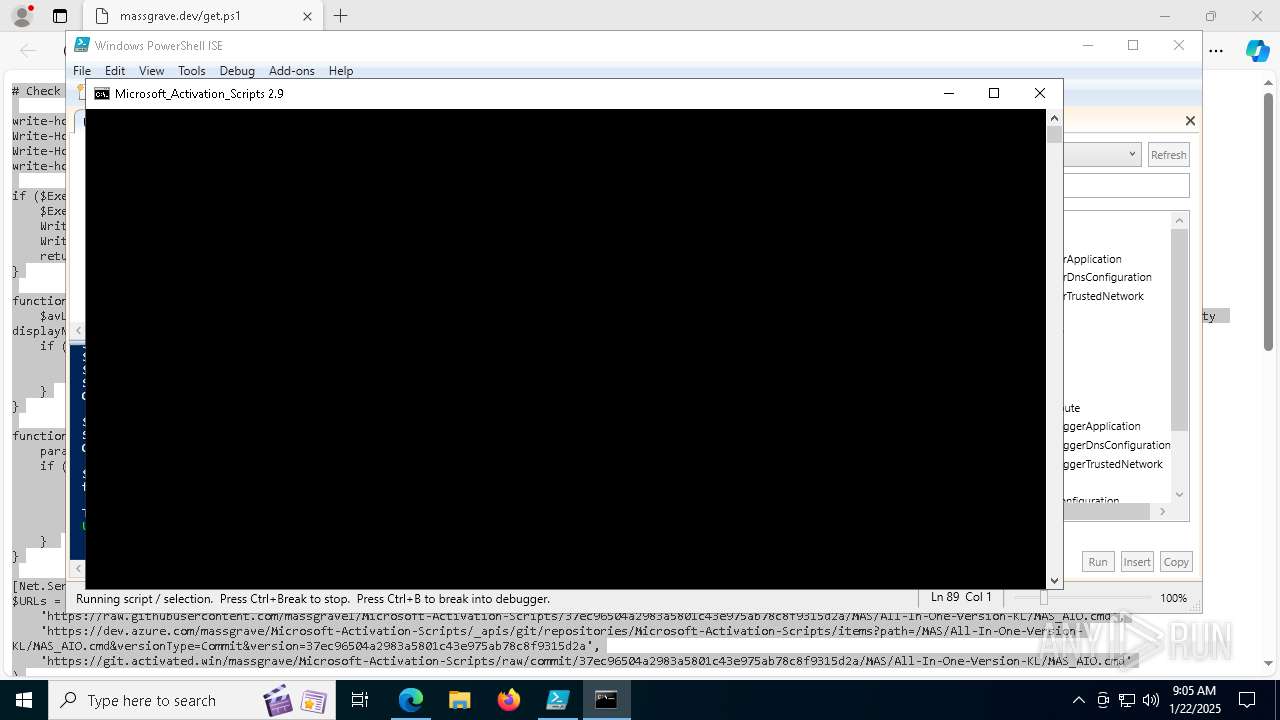
Starts CMD.EXE for commands execution
- powershell_ise.exe (PID: 6004)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 7532)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 1916)
- powershell.exe (PID: 7180)
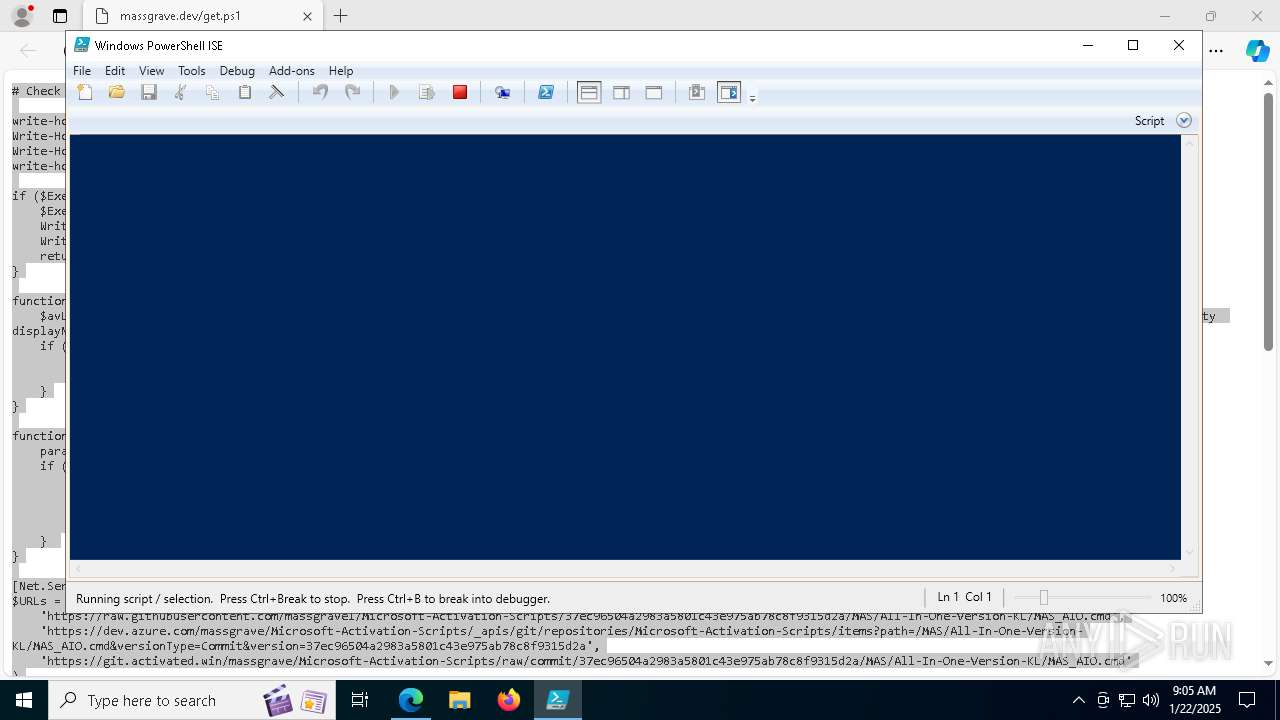
Executing commands from ".cmd" file
- powershell_ise.exe (PID: 6004)
- cmd.exe (PID: 1804)
- powershell.exe (PID: 7180)
- cmd.exe (PID: 7880)
Application launched itself
- cmd.exe (PID: 7532)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 1916)
- cmd.exe (PID: 7880)
Windows service management via SC.EXE
- sc.exe (PID: 4980)
- sc.exe (PID: 7928)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1804)
- cmd.exe (PID: 7880)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 5256)
- cmd.exe (PID: 6940)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5256)
- cmd.exe (PID: 6940)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 7880)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 5256)
- cmd.exe (PID: 6940)
Starts SC.EXE for service management
- cmd.exe (PID: 1804)
- cmd.exe (PID: 7880)
INFO
Creates files or folders in the user directory
- powershell_ise.exe (PID: 6004)
Application launched itself
- msedge.exe (PID: 5856)
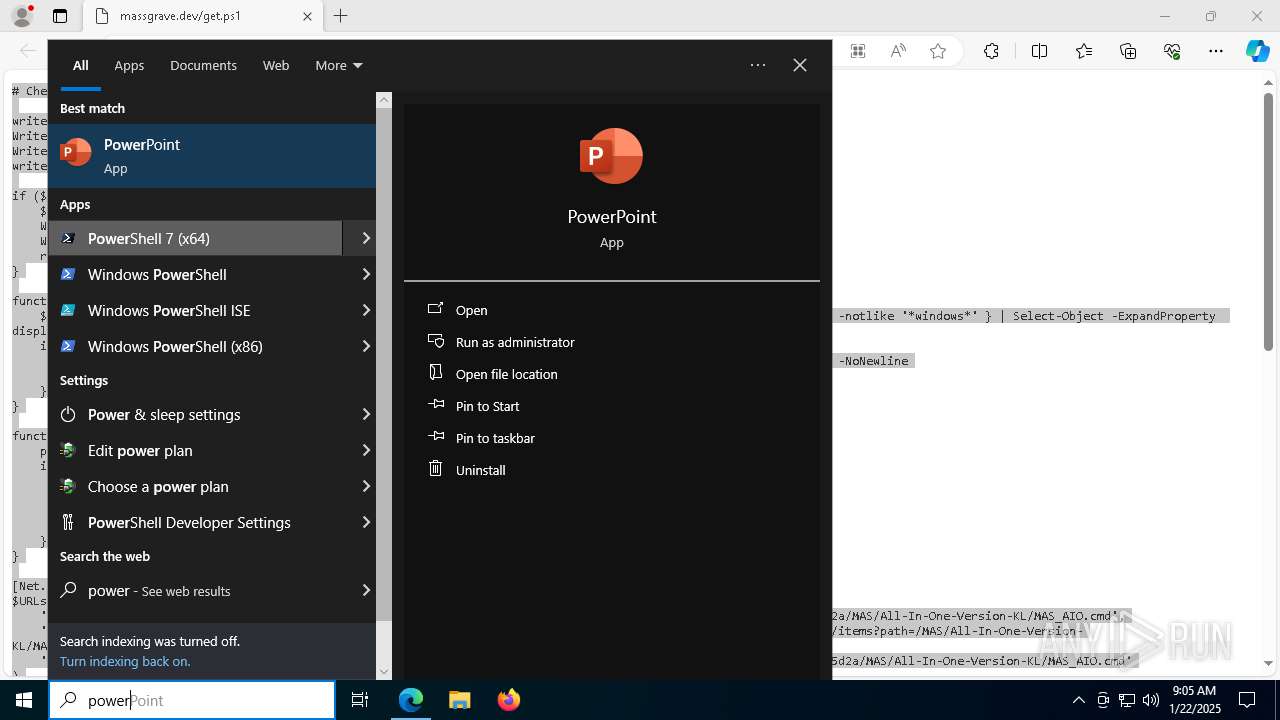
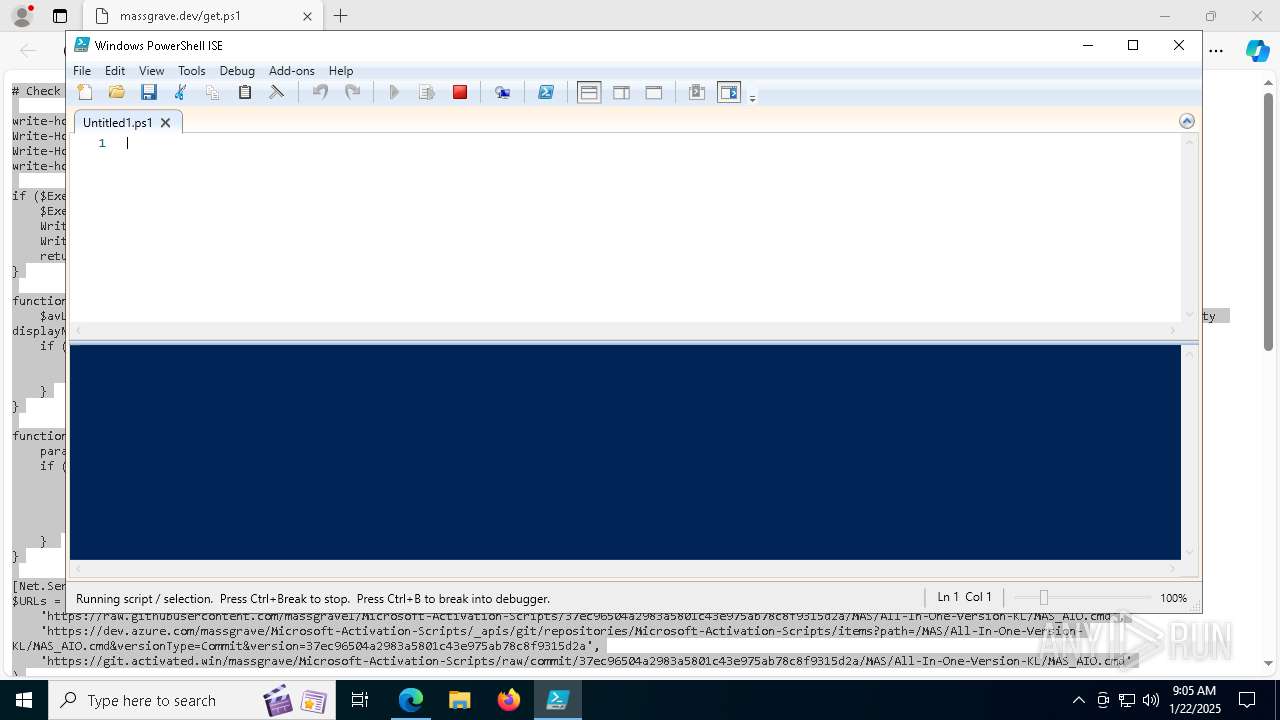
Manual execution by a user
- powershell_ise.exe (PID: 6004)
Reads Environment values
- identity_helper.exe (PID: 7588)
Reads the computer name
- identity_helper.exe (PID: 7588)
Checks supported languages
- identity_helper.exe (PID: 7588)
Reads security settings of Internet Explorer
- powershell_ise.exe (PID: 6004)
Checks current location (POWERSHELL)
- powershell_ise.exe (PID: 6004)
Create files in a temporary directory
- powershell_ise.exe (PID: 6004)
Checks proxy server information
- powershell_ise.exe (PID: 6004)
Reads the software policy settings
- powershell_ise.exe (PID: 6004)
The process uses the downloaded file
- powershell_ise.exe (PID: 6004)
Disables trace logs
- powershell_ise.exe (PID: 6004)
Checks whether the specified file exists (POWERSHELL)
- powershell_ise.exe (PID: 6004)
- powershell.exe (PID: 2136)
- powershell.exe (PID: 6972)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell_ise.exe (PID: 6004)
- powershell.exe (PID: 2136)
- powershell.exe (PID: 6972)
Converts byte array into ASCII string (POWERSHELL)
- powershell_ise.exe (PID: 6004)
- powershell.exe (PID: 2136)
- powershell.exe (PID: 6972)
Checks operating system version
- cmd.exe (PID: 1804)
- cmd.exe (PID: 7880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
202
Monitored processes
71
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1140 | powershell.exe "$TB = [AppDomain]::CurrentDomain.DefineDynamicAssembly(4, 1).DefineDynamicModule(2, $False).DefineType(0); [void]$TB.DefinePInvokeMethod('GetConsoleWindow', 'kernel32.dll', 22, 1, [IntPtr], @(), 1, 3).SetImplementationFlags(128); [void]$TB.DefinePInvokeMethod('SendMessageW', 'user32.dll', 22, 1, [IntPtr], @([IntPtr], [UInt32], [IntPtr], [IntPtr]), 1, 3).SetImplementationFlags(128); $hIcon = $TB.CreateType(); $hWnd = $hIcon::GetConsoleWindow(); echo $($hIcon::SendMessageW($hWnd, 127, 0, 0) -ne [IntPtr]::Zero);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1400 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | "C:\WINDOWS\system32\cmd.exe" /c ""C:\Users\admin\AppData\Local\Temp\MAS_7d406b2a-df2e-44c5-b2ac-8e0c231fa3af.cmd" " | C:\Windows\System32\cmd.exe | — | powershell_ise.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1916 | C:\WINDOWS\System32\cmd.exe /c echo prompt $E | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_7d406b2a-df2e-44c5-b2ac-8e0c231fa3af.cmd') -split ':PStest:\s*';iex ($f[1])" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2164 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3224 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3488 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo prompt $E " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3560 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6636 --field-trial-handle=2876,i,10097400911887815828,4183307363665380161,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
25 703
Read events
25 676
Write events
27
Delete events
0
Modification events
| (PID) Process: | (5856) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 14ABE911DE8A2F00 | |||
| (PID) Process: | (5856) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328378 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2DC4E71D-75AD-4D20-B7A7-BA05ADE9E39C} | |||
| (PID) Process: | (5856) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328378 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BB1E0479-9485-4D75-AE38-63BED7EE2282} | |||
| (PID) Process: | (5856) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5856) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5856) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5856) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5856) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2EC3B811DE8A2F00 | |||
| (PID) Process: | (5856) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BD696812DE8A2F00 | |||
| (PID) Process: | (5856) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
7
Suspicious files
214
Text files
47
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5856 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF137b1f.TMP | — | |
MD5:— | SHA256:— | |||
| 5856 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5856 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF137b1f.TMP | — | |
MD5:— | SHA256:— | |||
| 5856 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5856 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF137b1f.TMP | — | |
MD5:— | SHA256:— | |||
| 5856 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF137b1f.TMP | — | |
MD5:— | SHA256:— | |||
| 5856 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5856 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5856 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF137b3e.TMP | — | |
MD5:— | SHA256:— | |||
| 5856 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
59
DNS requests
48
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6888 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7436 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7436 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6004 | powershell_ise.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
6004 | powershell_ise.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 104.126.37.137:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6412 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5856 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6412 | msedge.exe | 104.21.22.3:443 | massgrave.dev | — | — | unknown |
6412 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6412 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
massgrave.dev |
| unknown |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |