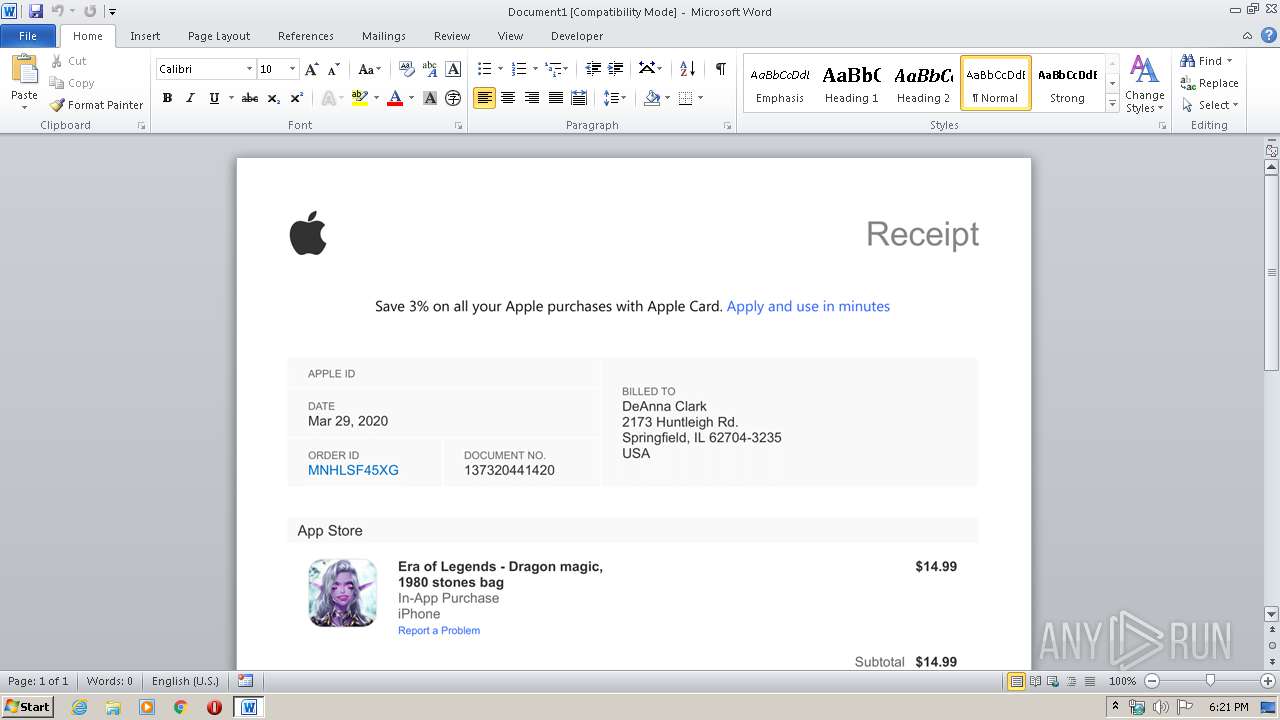
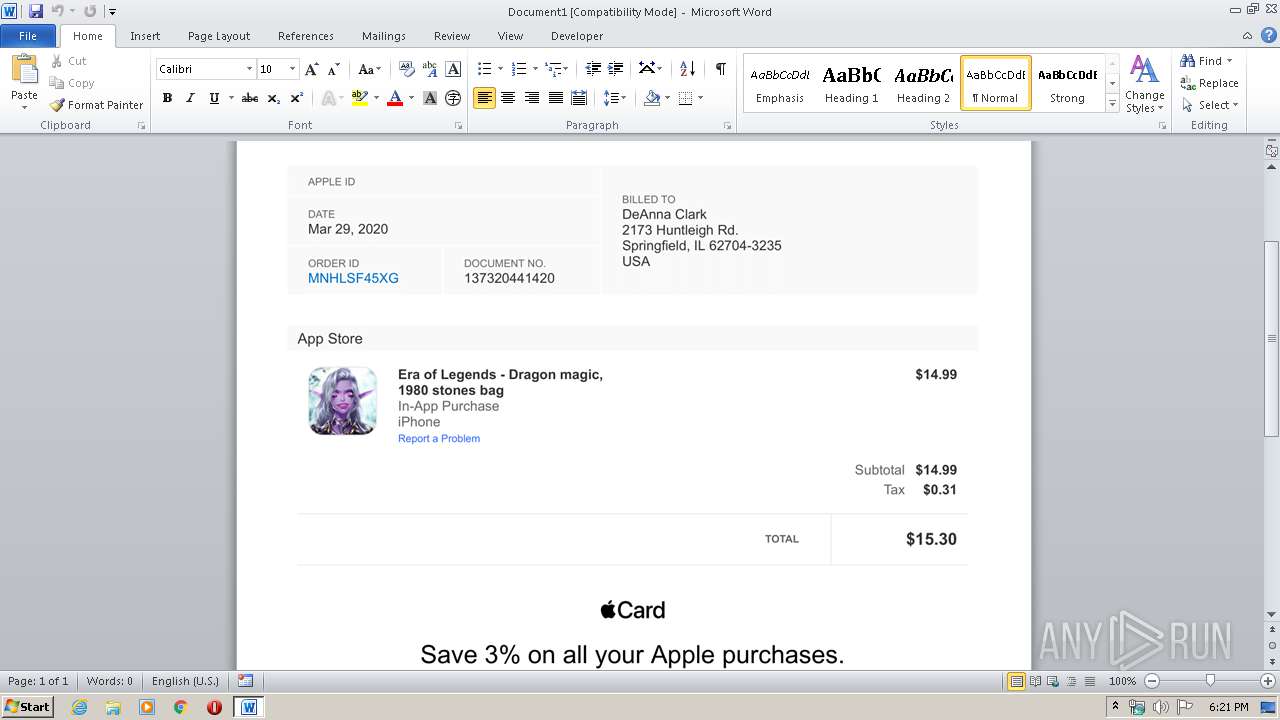
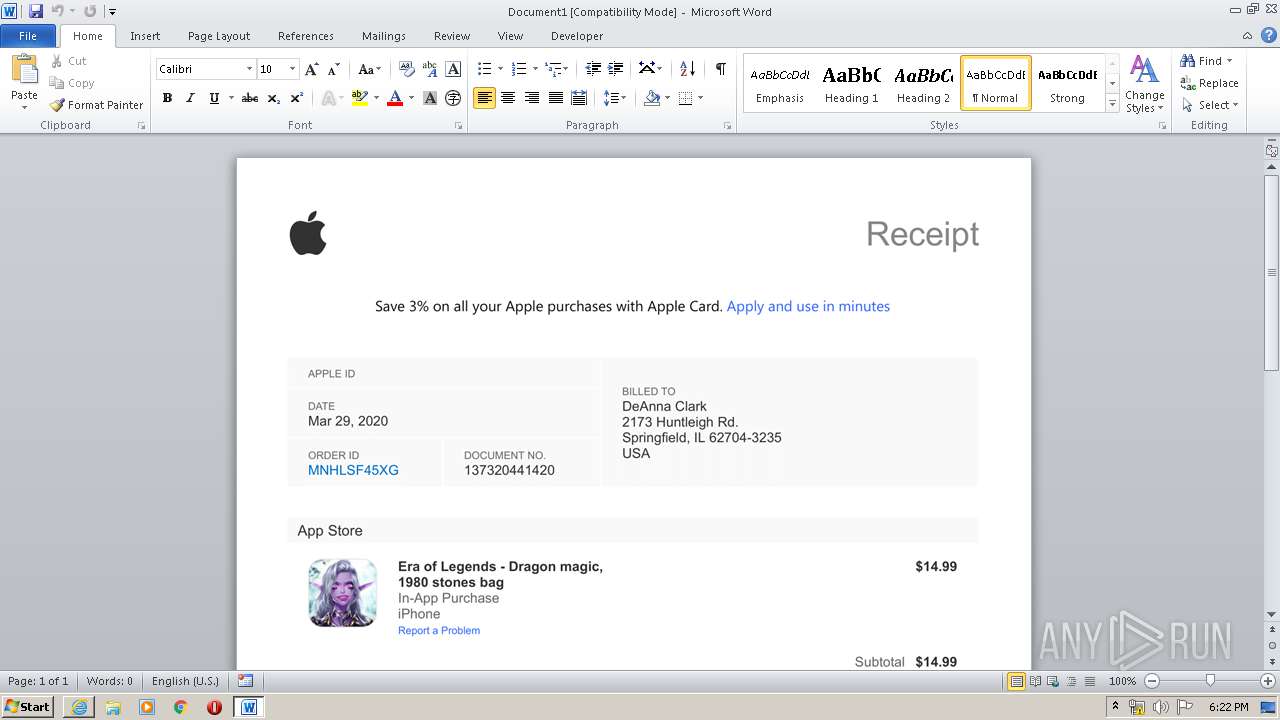
| File name: | Era of Legends - Dragon magic.dot |
| Full analysis: | https://app.any.run/tasks/3ccb4936-6d14-4d86-921a-3fab11027b10 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 17:20:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1200, Locale ID: 1033, Author: FAR, Template: Normal, Last Saved By: FAR, Revision Number: 1, Create Time/Date: Sun Mar 29 21:56:00 2020, Last Saved Time/Date: Sun Mar 29 21:56:53 2020, Number of Pages: 1, Number of Words: 0, Number of Characters: 0, Name of Creating Application: WPS Wr, Security: 0 |
| MD5: | 24DAE1E147DB60792CC8137FA4F3F1F1 |
| SHA1: | 6A3DAD34E4501113EF8B185FF563E9EBD34AB3BA |
| SHA256: | 356980B846E1D72075CC228447DA151E97DE1998B5362D3D81AC3DB2D2408E7F |
| SSDEEP: | 3072:g92lTJxonEr1n5G9PQZUwRulMlCCiuueQS0+qwN7Q7pKPwuYj2scJ5rOF2q1x/1x:g0yEK9oZG8iNtS3O4wuY0X01xb |
MALICIOUS
No malicious indicators.SUSPICIOUS
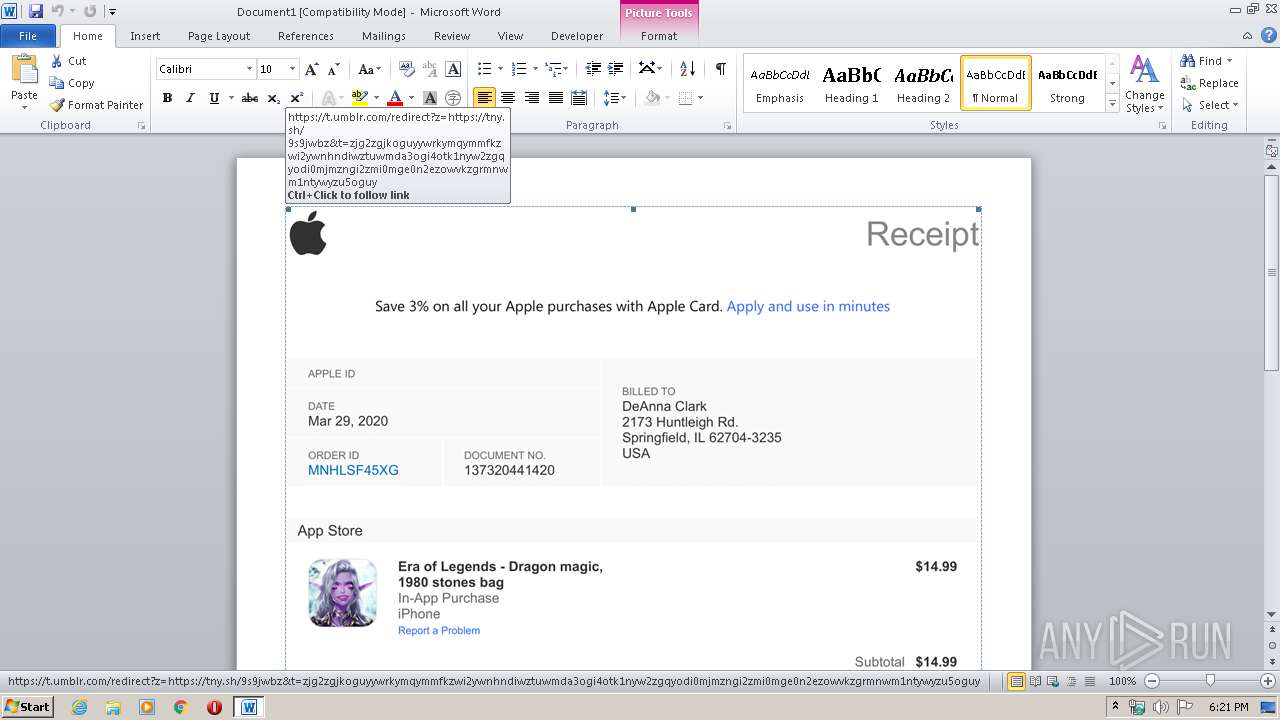
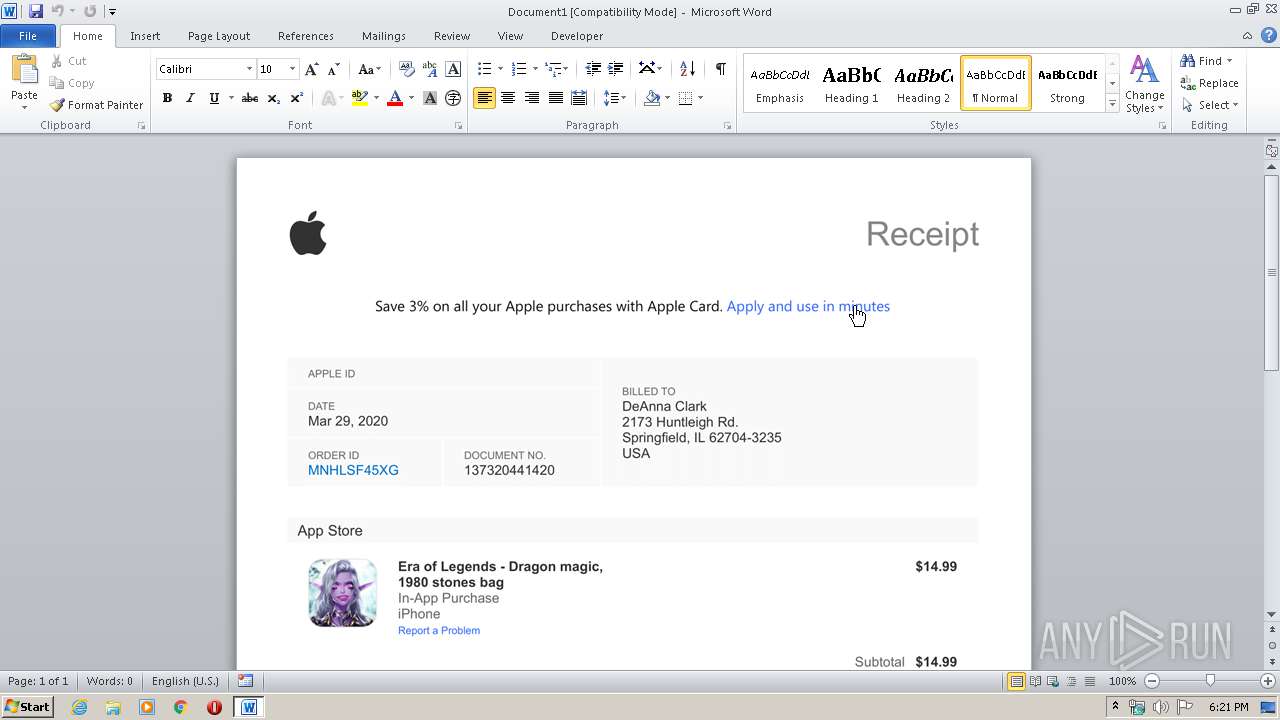
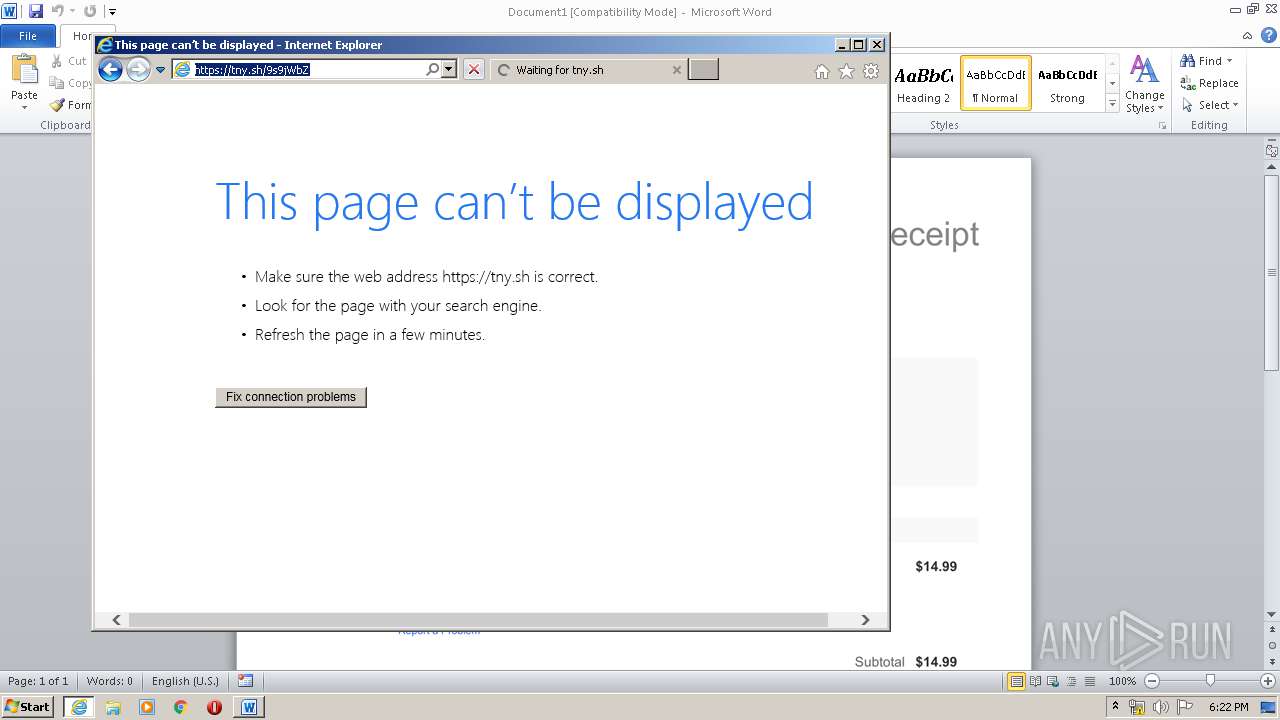
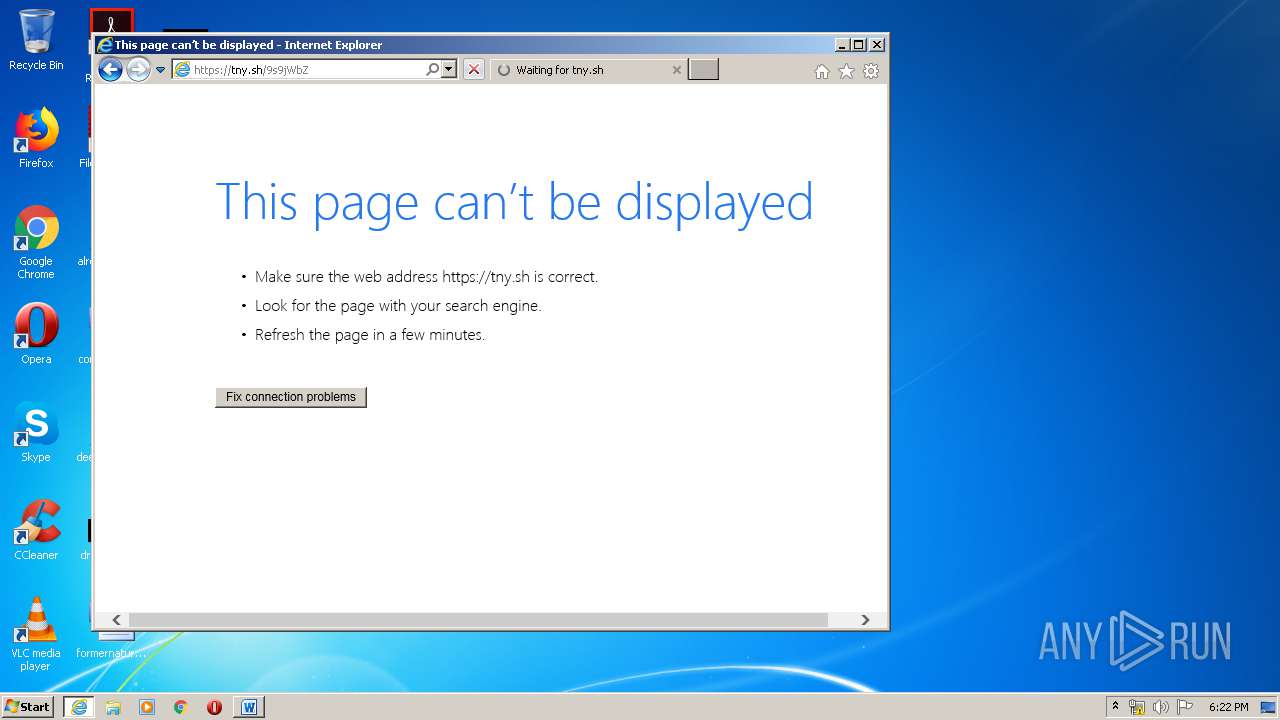
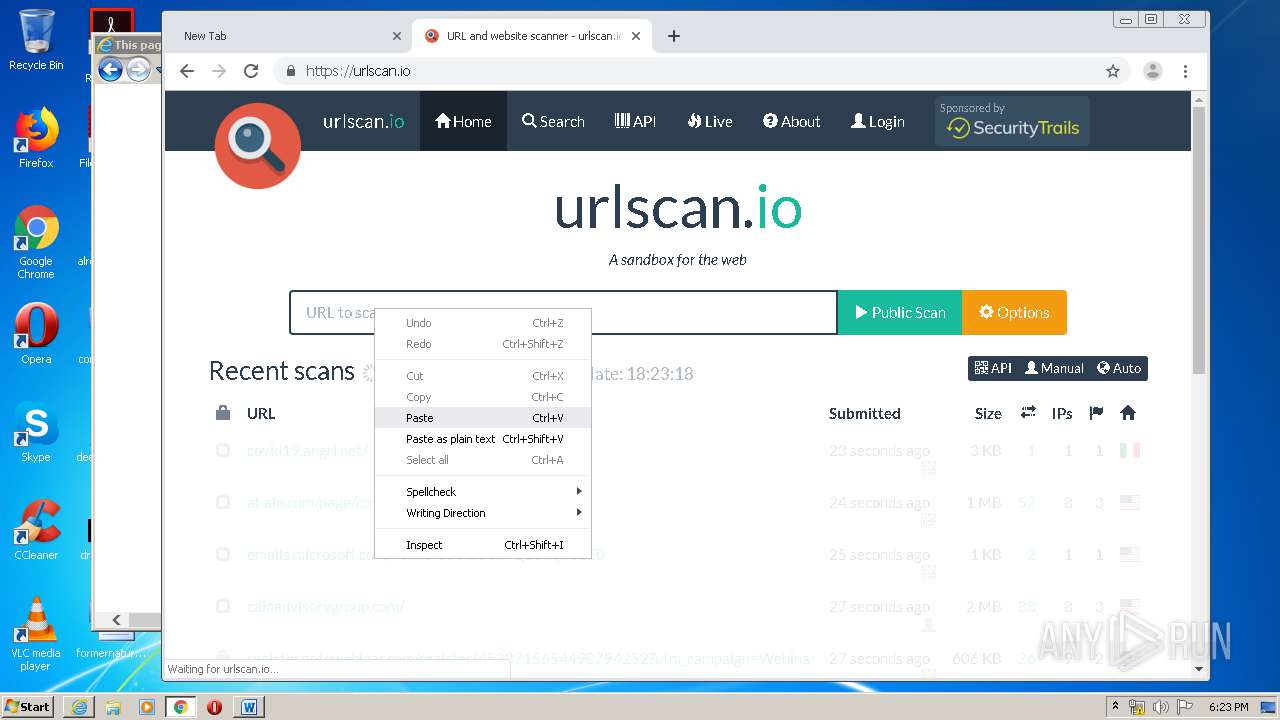
Unusual connect from Microsoft Office
- WINWORD.EXE (PID: 3988)
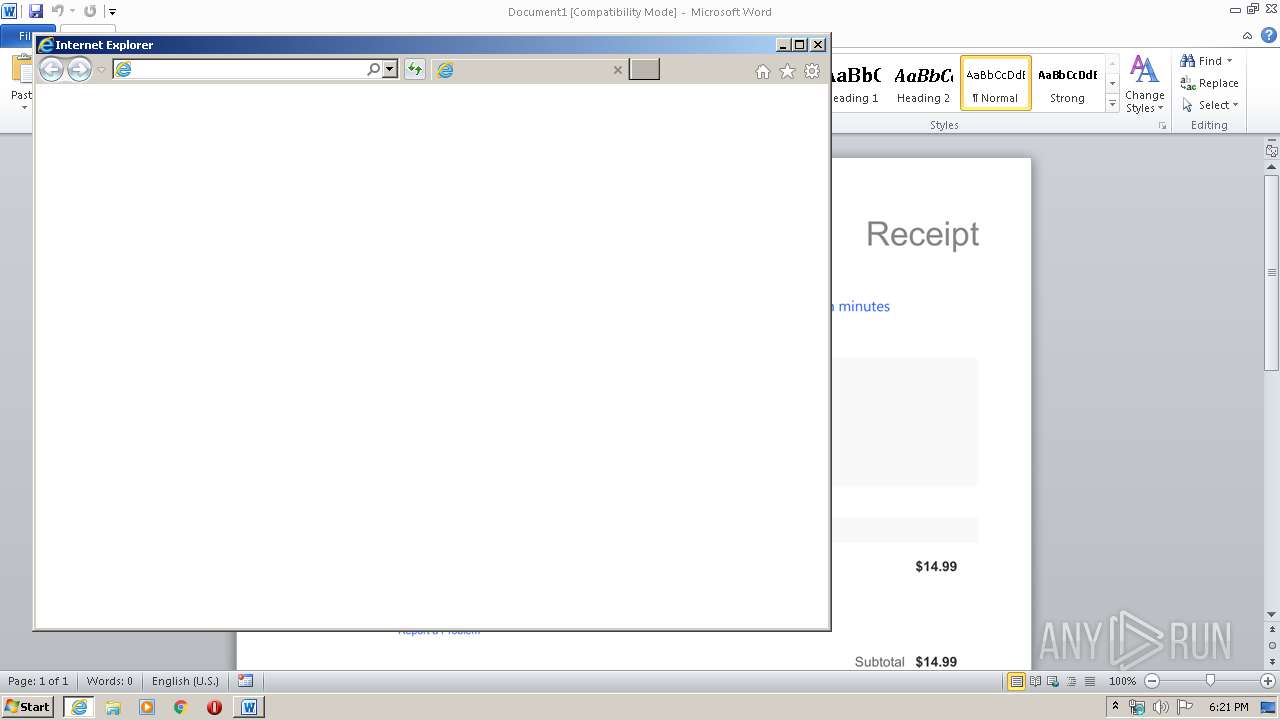
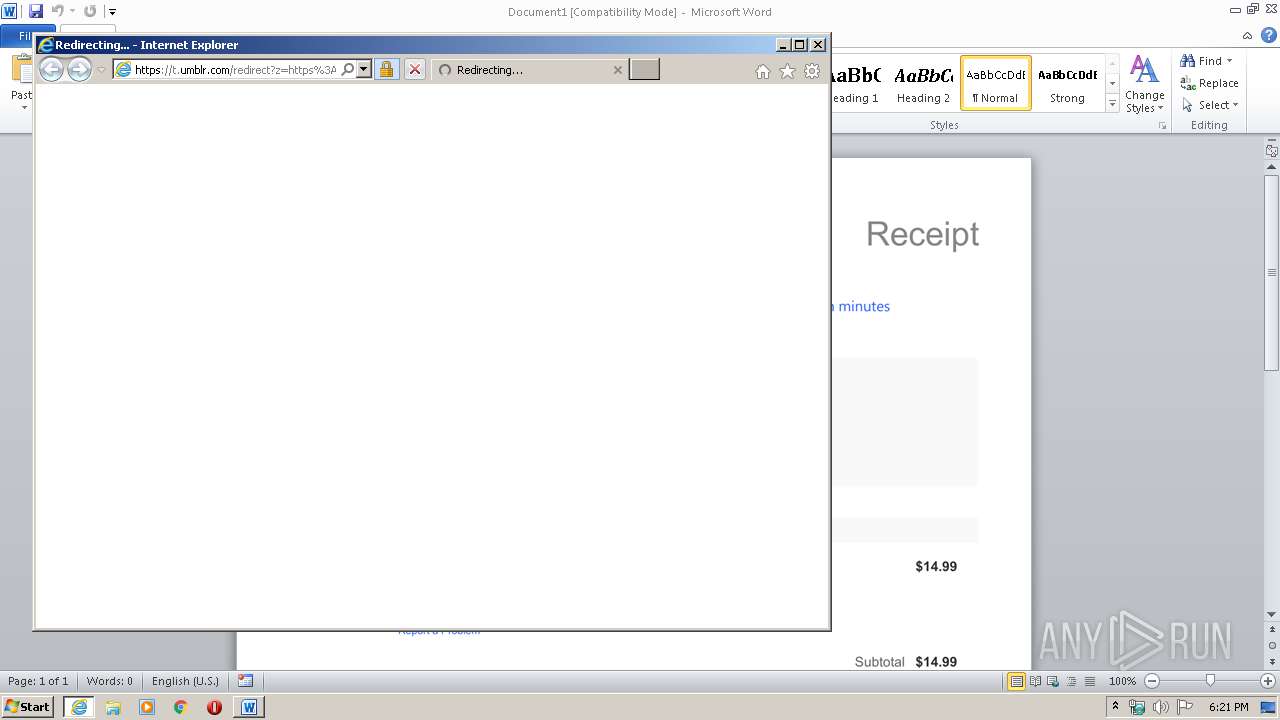
Executed via COM
- sdiagnhost.exe (PID: 3820)
- iexplore.exe (PID: 1784)
Uses IPCONFIG.EXE to discover IP address
- sdiagnhost.exe (PID: 3820)
Executable content was dropped or overwritten
- msdt.exe (PID: 1940)
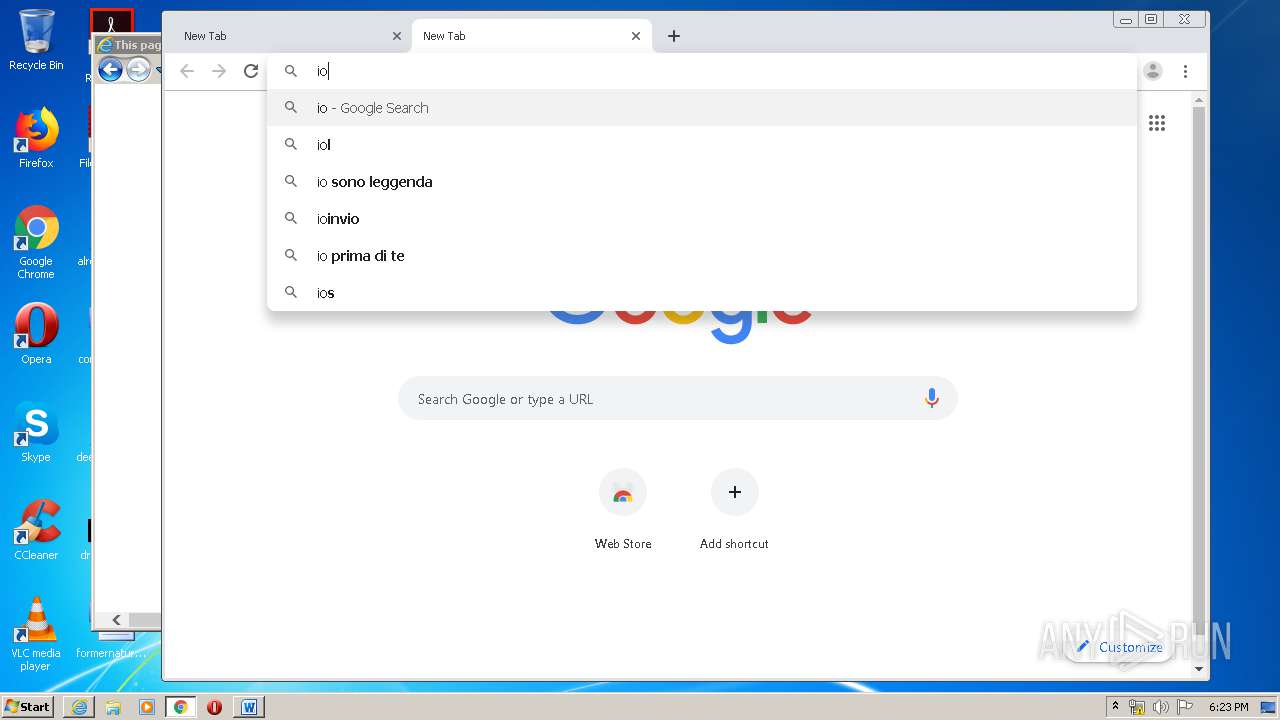
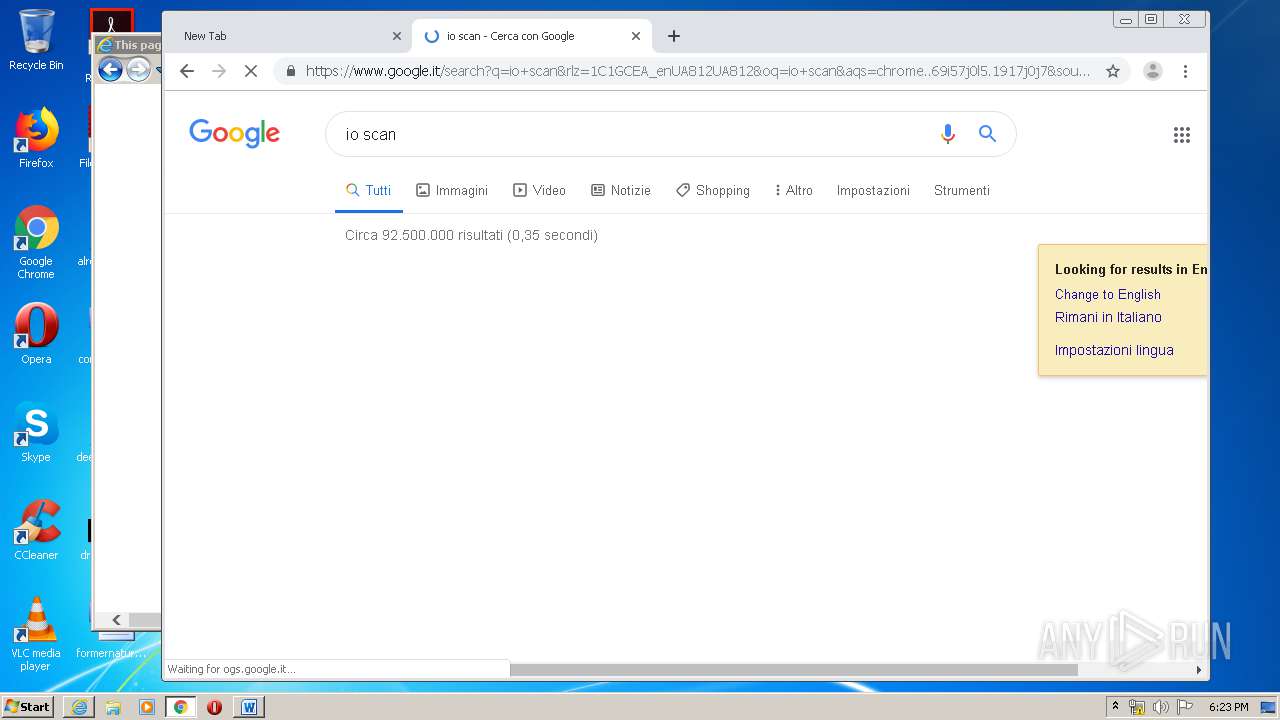
Modifies files in Chrome extension folder
- chrome.exe (PID: 1724)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3988)
Changes internet zones settings
- iexplore.exe (PID: 1784)
Application launched itself
- iexplore.exe (PID: 1784)
- chrome.exe (PID: 1724)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 3988)
- iexplore.exe (PID: 1784)
- iexplore.exe (PID: 3576)
Creates files in the user directory
- WINWORD.EXE (PID: 3988)
- iexplore.exe (PID: 3576)
- iexplore.exe (PID: 1784)
Reads internet explorer settings
- WINWORD.EXE (PID: 3988)
- iexplore.exe (PID: 3576)
- iexplore.exe (PID: 1812)
Reads settings of System Certificates
- WINWORD.EXE (PID: 3988)
- iexplore.exe (PID: 1812)
- iexplore.exe (PID: 3576)
- chrome.exe (PID: 2612)
- iexplore.exe (PID: 1784)
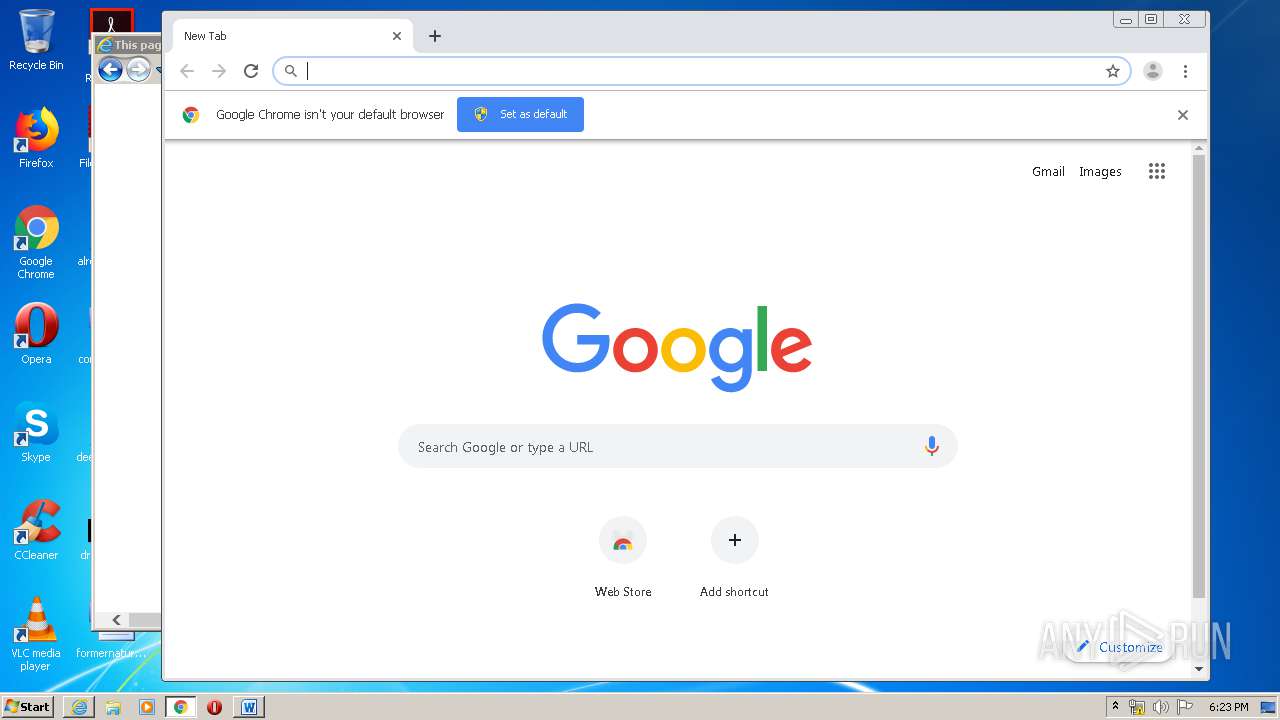
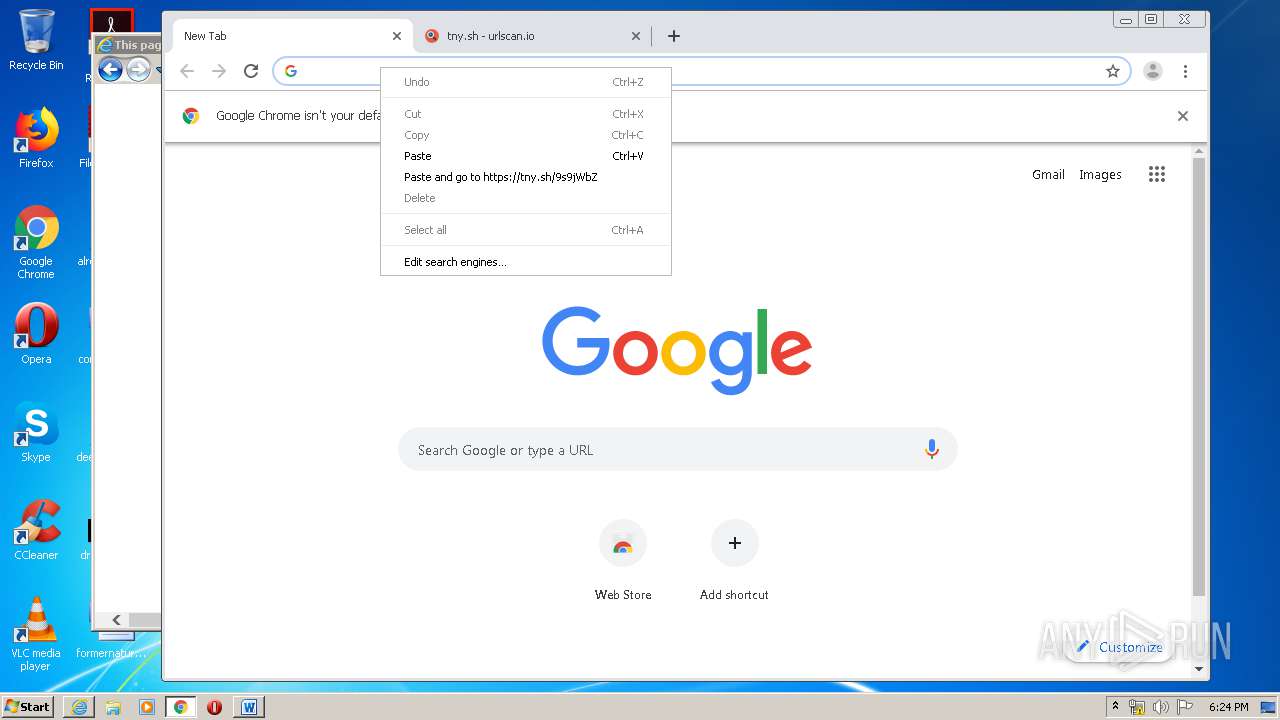
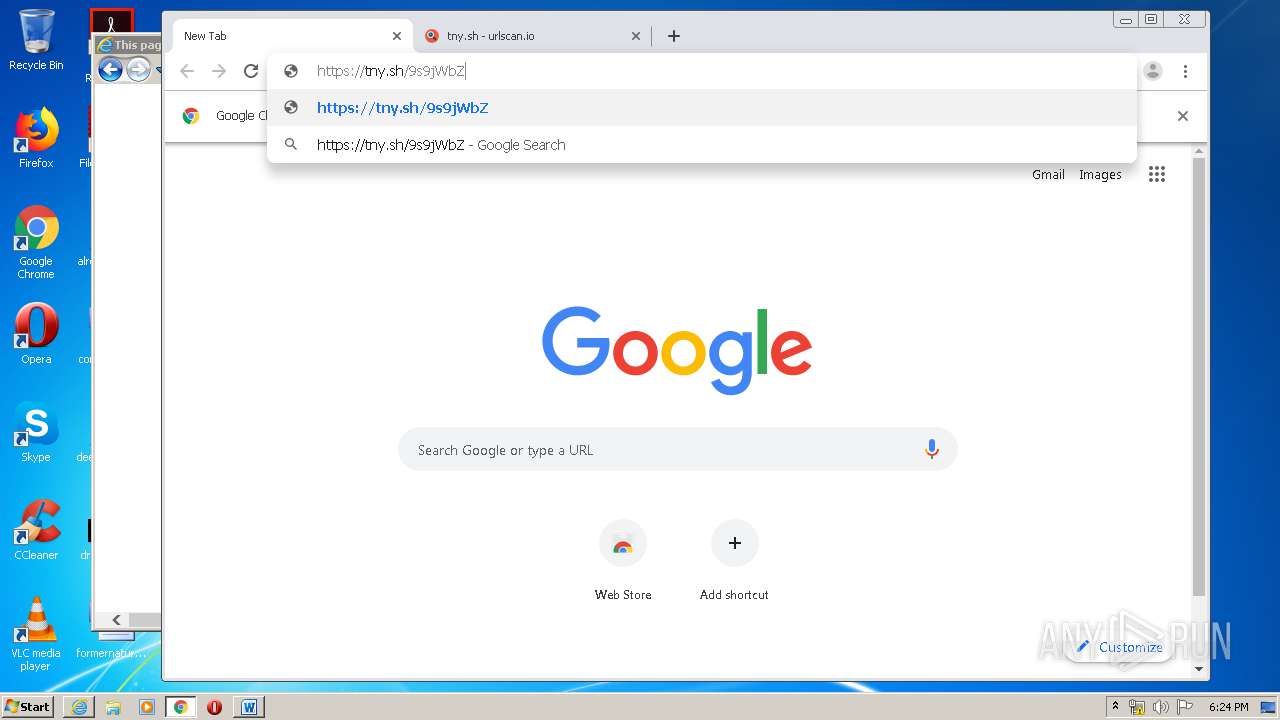
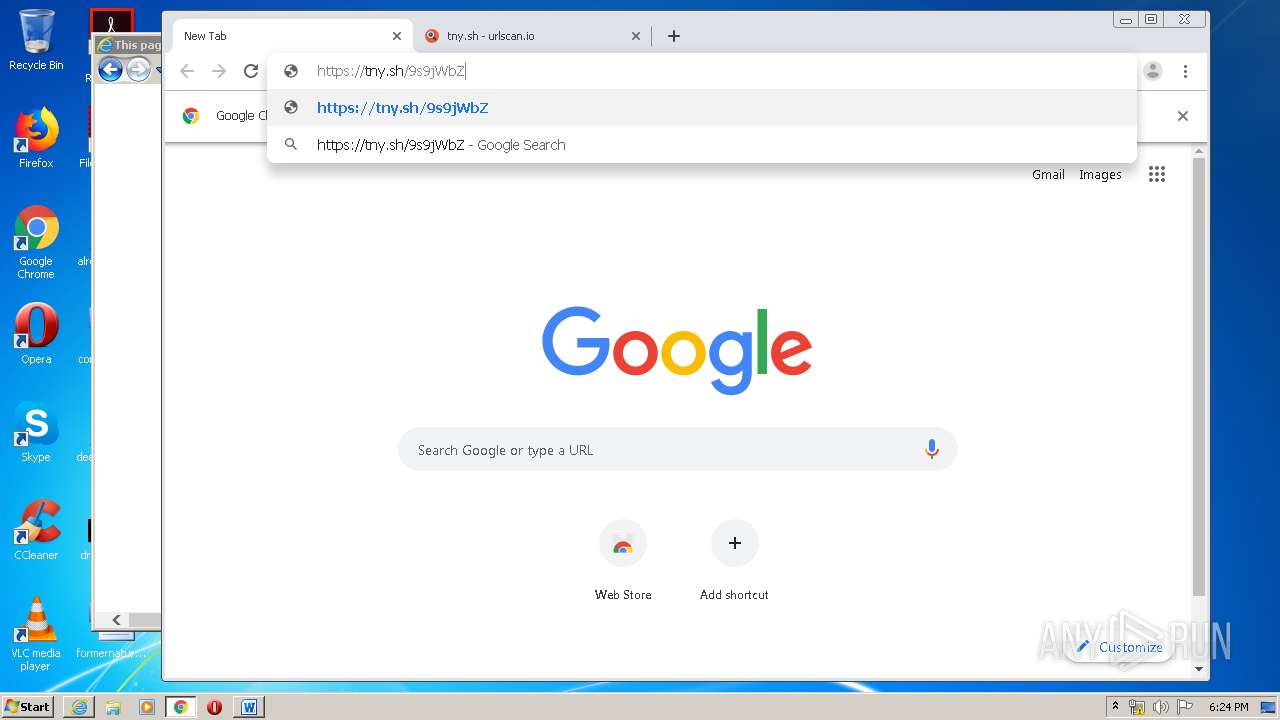
Manual execution by user
- chrome.exe (PID: 1724)
Reads the hosts file
- chrome.exe (PID: 1724)
- chrome.exe (PID: 2612)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1812)
- iexplore.exe (PID: 1784)
Changes settings of System certificates
- iexplore.exe (PID: 1784)
- iexplore.exe (PID: 1812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
FlashPix
| Author: | FARMA |
|---|---|
| Template: | Normal.dotm |
| LastModifiedBy: | FARMA |
| RevisionNumber: | 1 |
| CreateDate: | 2020:03:29 20:56:00 |
| ModifyDate: | 2020:03:29 20:56:53 |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Software: | WPS Writer |
| Security: | None |
| Company: | - |
| Paragraphs: | - |
| Lines: | - |
| CharCountWithSpaces: | - |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| TagK: | 1033-11.2.0.9232 |
Total processes
80
Monitored processes
42
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,7927671765581759988,3024439969180020861,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12067566358896079535 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,7927671765581759988,3024439969180020861,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14568506302696387338 --mojo-platform-channel-handle=3564 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2696 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,7927671765581759988,3024439969180020861,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9990245069701916332 --mojo-platform-channel-handle=2496 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,7927671765581759988,3024439969180020861,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8412042445550891851 --mojo-platform-channel-handle=3468 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,7927671765581759988,3024439969180020861,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11252715493249349097 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,7927671765581759988,3024439969180020861,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14956658439747308822 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Internet Explorer\iexplore.exe" -startmediumtab -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1784 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
14 375
Read events
3 224
Write events
7 538
Delete events
3 613
Modification events
| (PID) Process: | (3988) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | #c5 |
Value: 23633500940F0000010000000000000000000000 | |||
| (PID) Process: | (3988) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3988) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3988) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3988) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3988) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3988) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3988) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3988) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3988) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
95
Text files
244
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B93.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF5BFEDF34BB8E160F.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF5A23793CB368FC60.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Cab68C.tmp | — | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Tar68D.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFE2.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFE3.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFE5.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFE4.tmp | — | |
MD5:— | SHA256:— | |||
| 3576 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\D17Y5JZ0.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
69
DNS requests
40
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2612 | chrome.exe | GET | — | 173.194.7.11:80 | http://r5---sn-p5qlsns6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=85.203.20.11&mm=28&mn=sn-p5qlsns6&ms=nvh&mt=1585588873&mv=m&mvi=4&pl=24&shardbypass=yes | US | — | — | whitelisted |
2612 | chrome.exe | GET | — | 173.194.7.11:80 | http://r5---sn-p5qlsns6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=85.203.20.11&mm=28&mn=sn-p5qlsns6&ms=nvh&mt=1585588993&mv=m&mvi=4&pl=24&shardbypass=yes | US | — | — | whitelisted |
3988 | WINWORD.EXE | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
1052 | svchost.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIGkp0%2Fv9GUvNUu1EP06Tu7%2BChyAQUkZ47RGw9V5xCdyo010%2FRzEqXLNoCEyAAASWxwt68EQiA3cUAAAABJbE%3D | US | der | 1.79 Kb | whitelisted |
2612 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
3576 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3576 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3576 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEArbZW6hjQZxNSVbgRP%2FRIU%3D | US | der | 279 b | whitelisted |
3988 | WINWORD.EXE | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAGCPlqfYbcz%2FqHwhCx6rQ8%3D | US | der | 471 b | whitelisted |
2612 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3988 | WINWORD.EXE | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3576 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1784 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
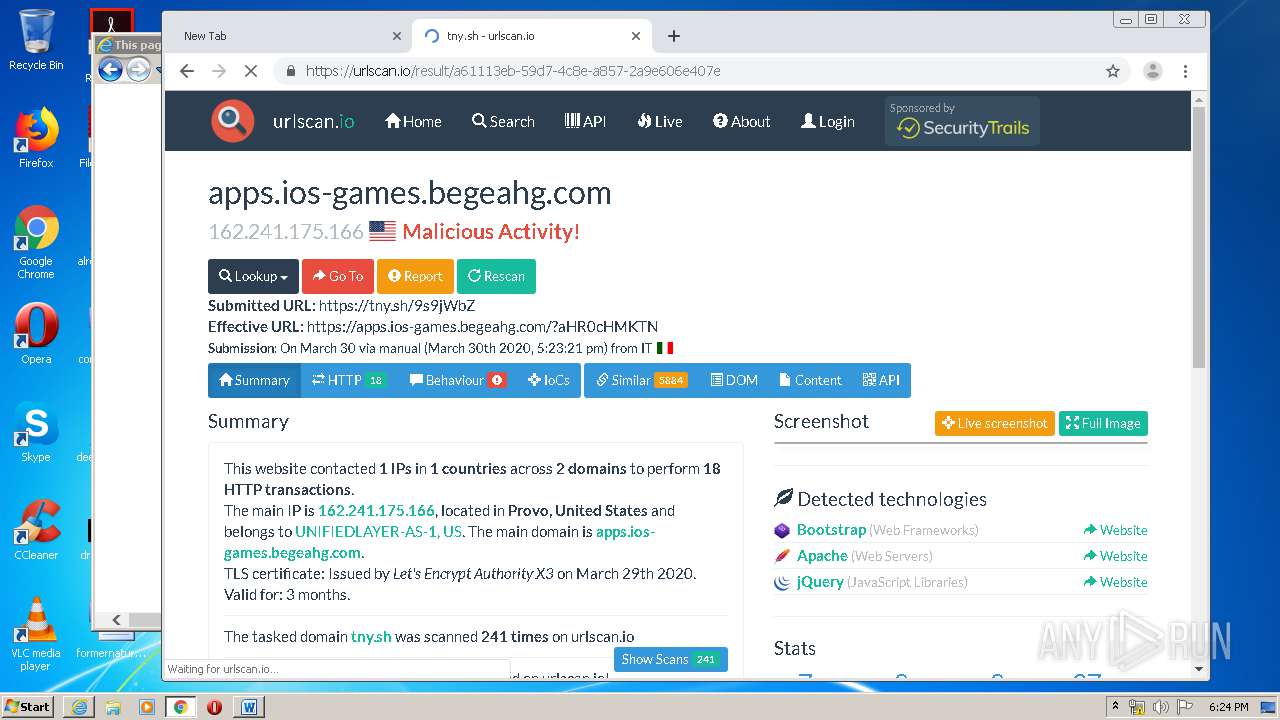
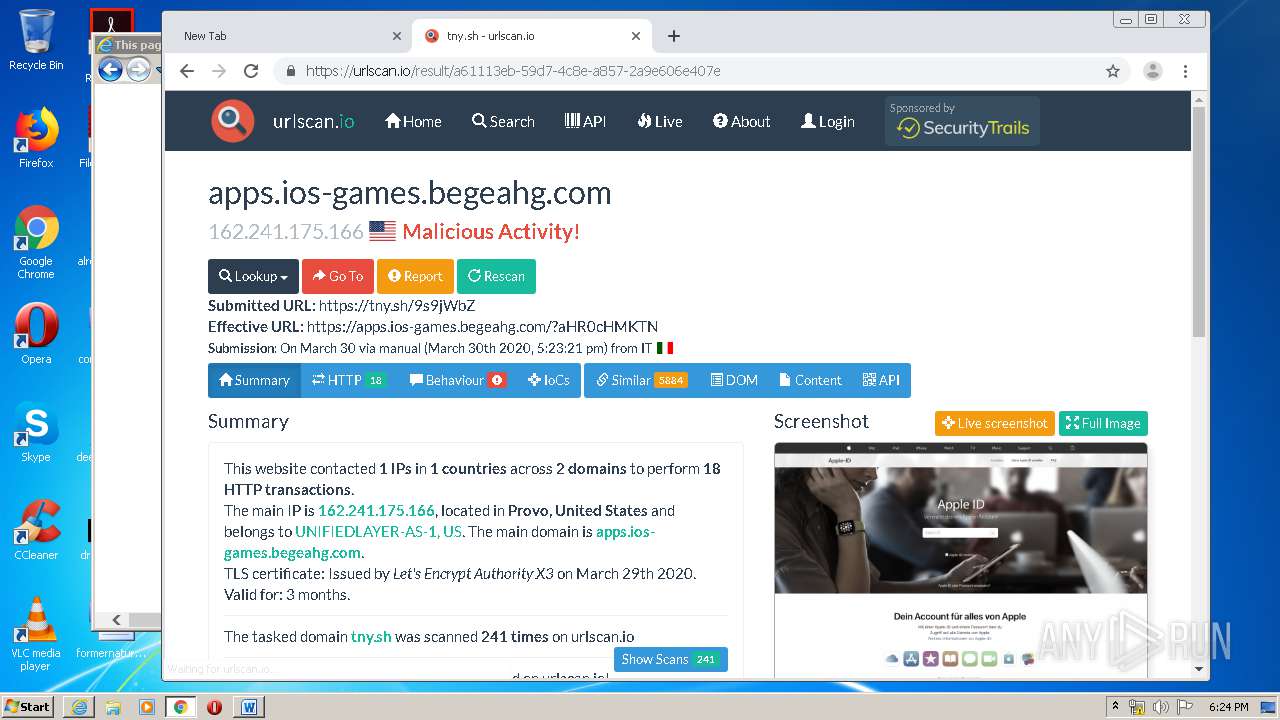
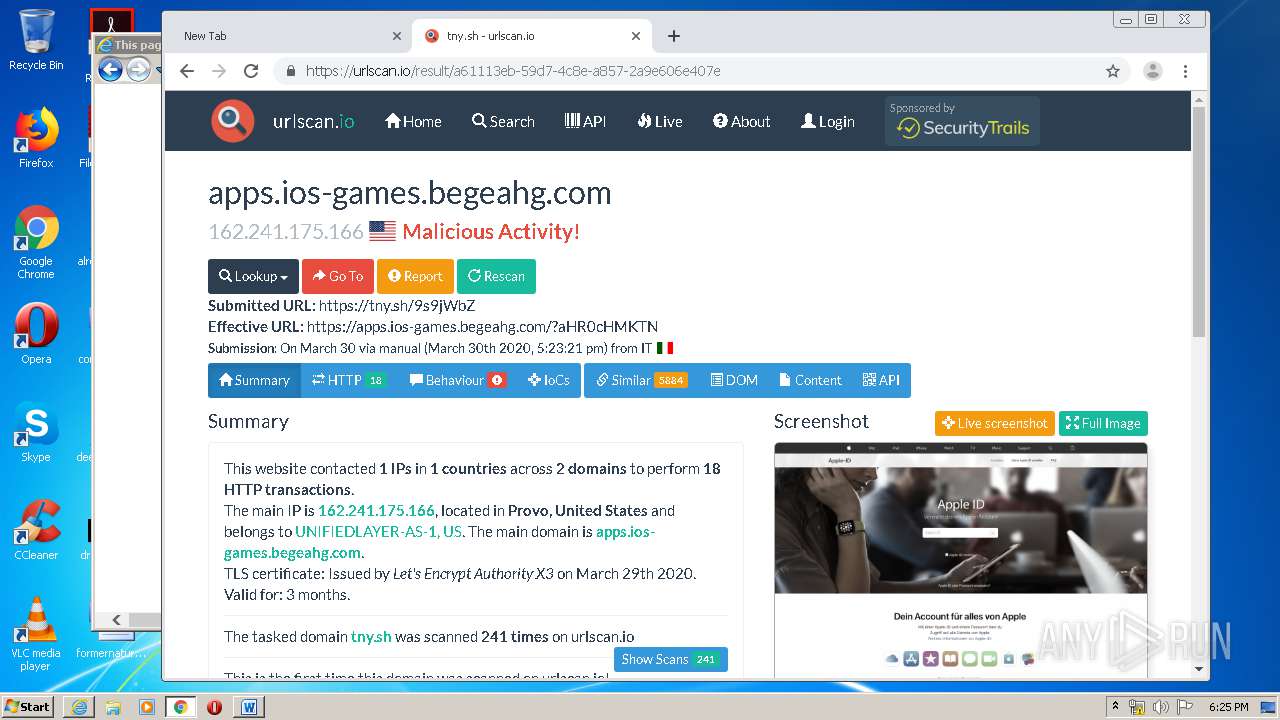
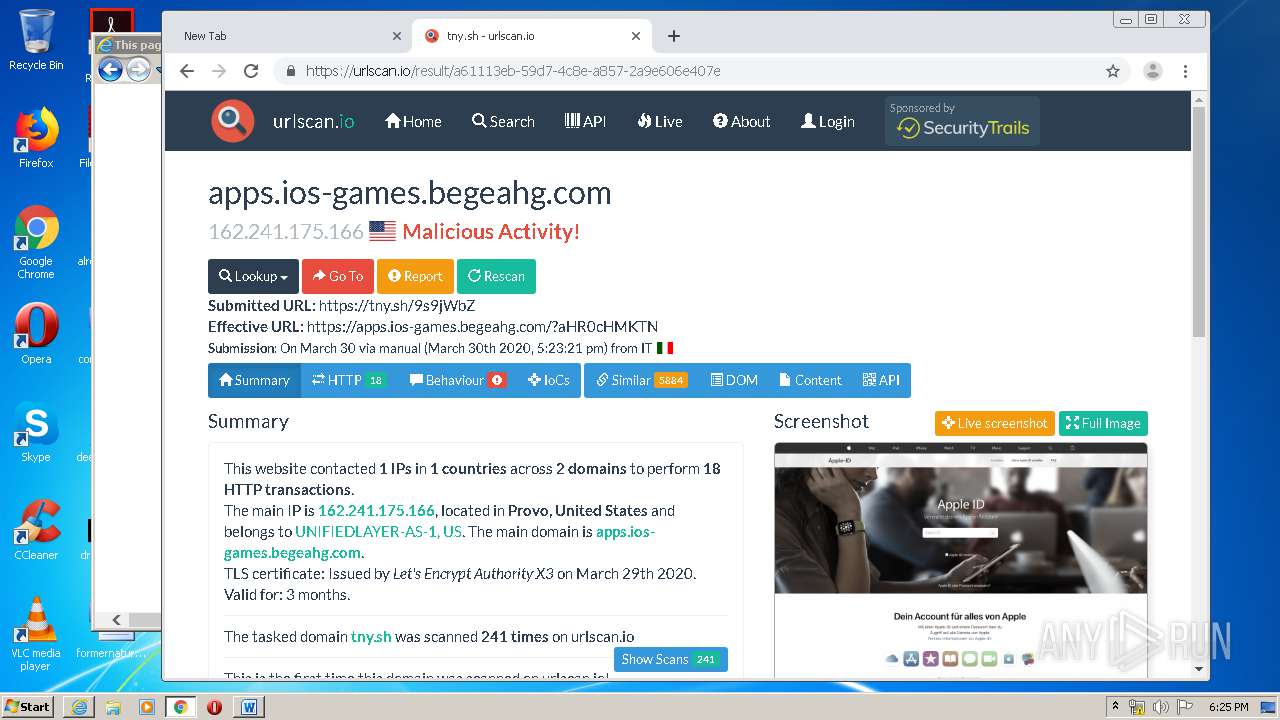
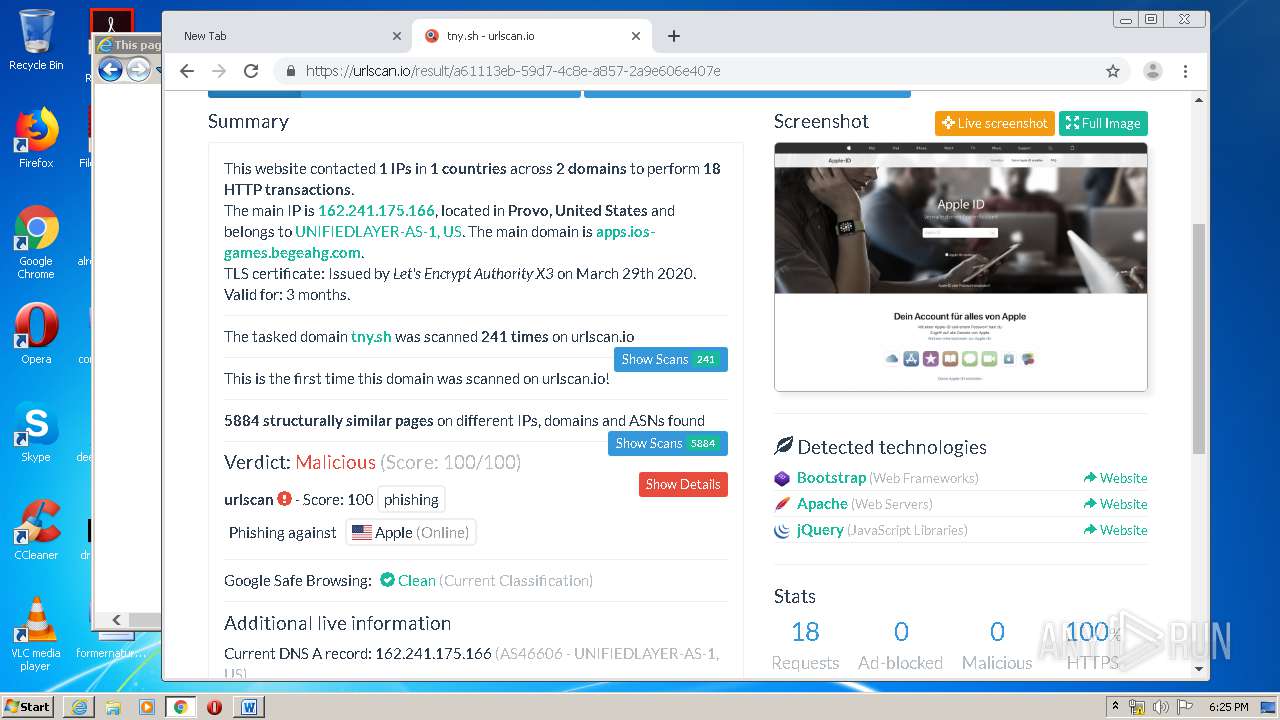
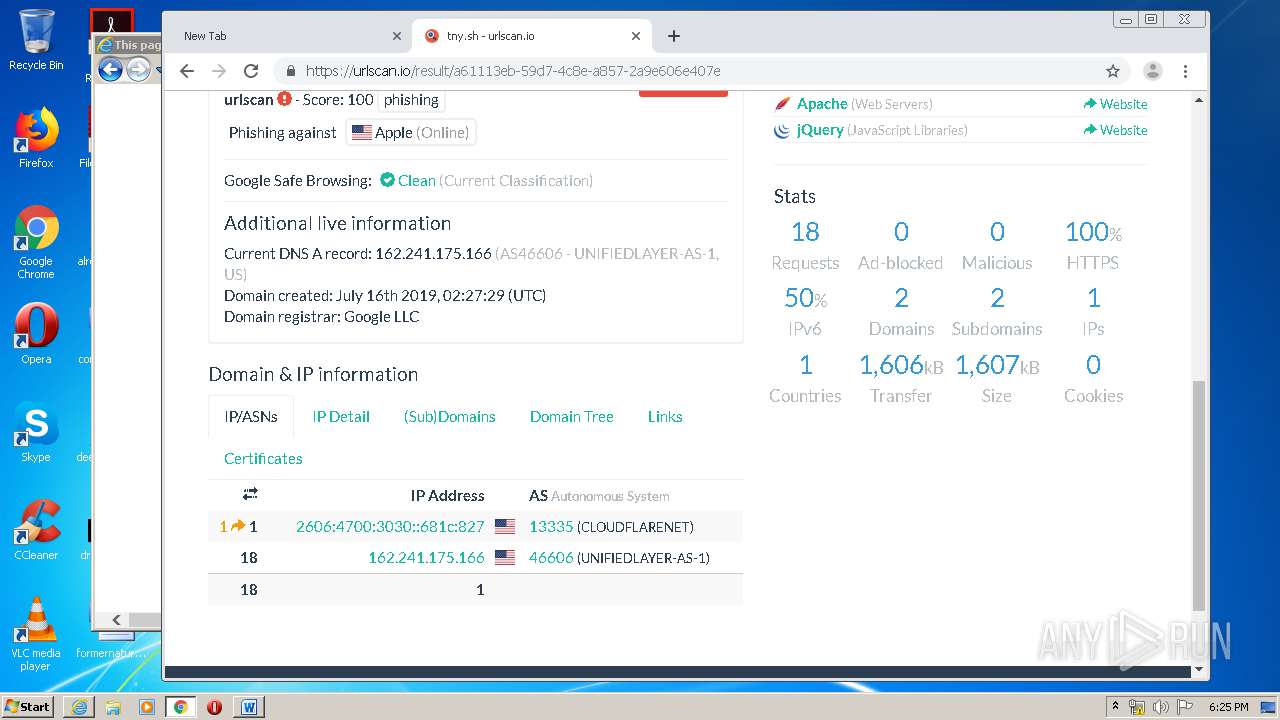
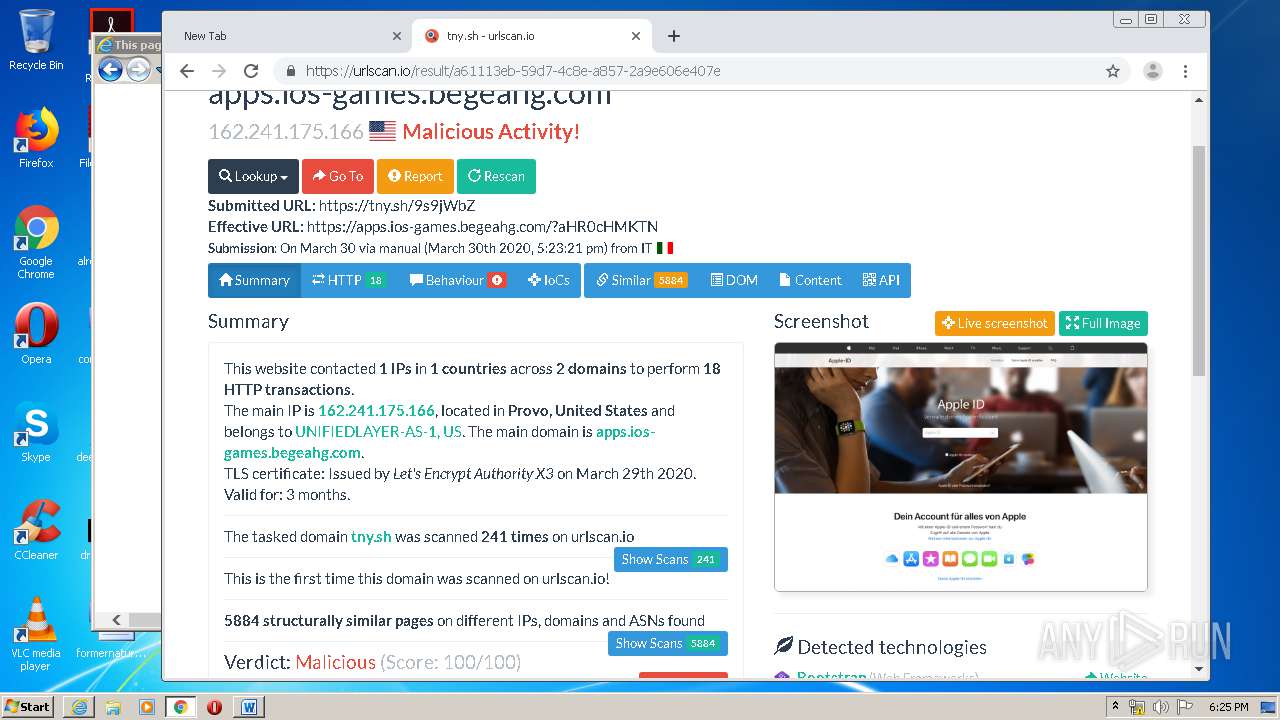
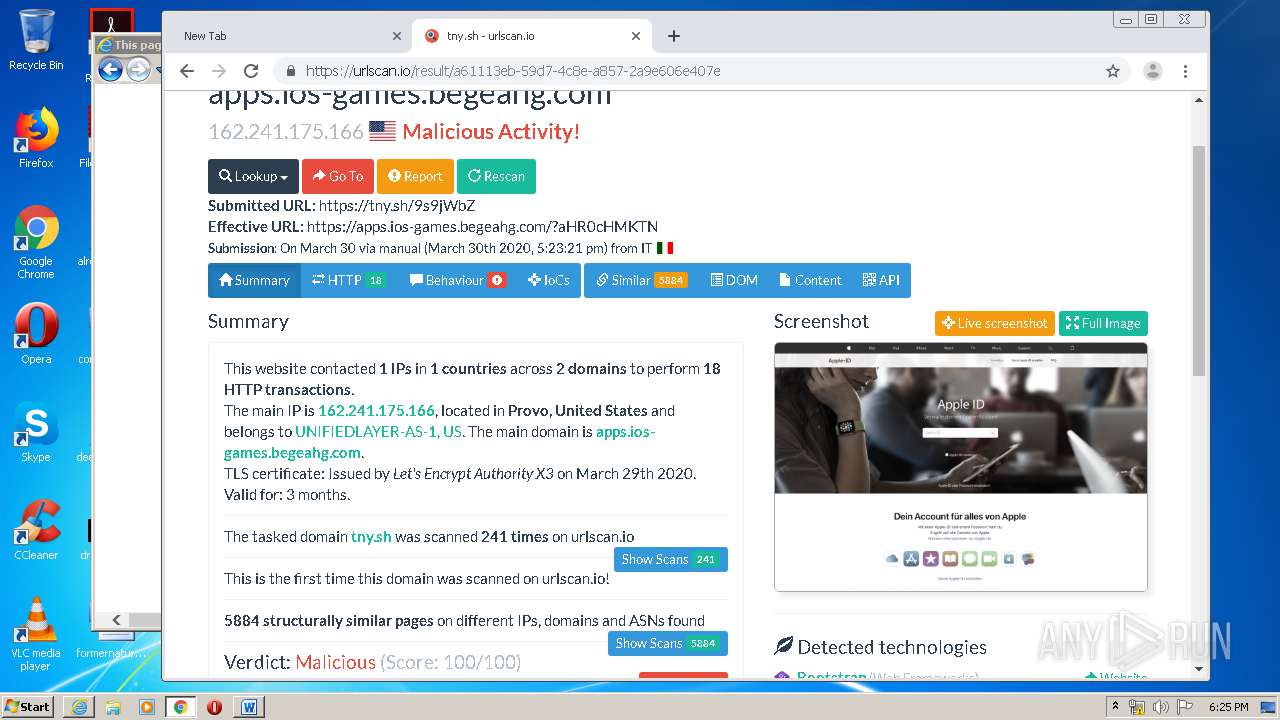
3576 | iexplore.exe | 162.241.175.166:443 | apps.ios-games.begeahg.com | CyrusOne LLC | US | suspicious |
824 | svchost.exe | 104.28.20.28:443 | linksplit.io | Cloudflare Inc | US | shared |
1784 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2612 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2612 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2612 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2612 | chrome.exe | 172.217.16.131:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t.umblr.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
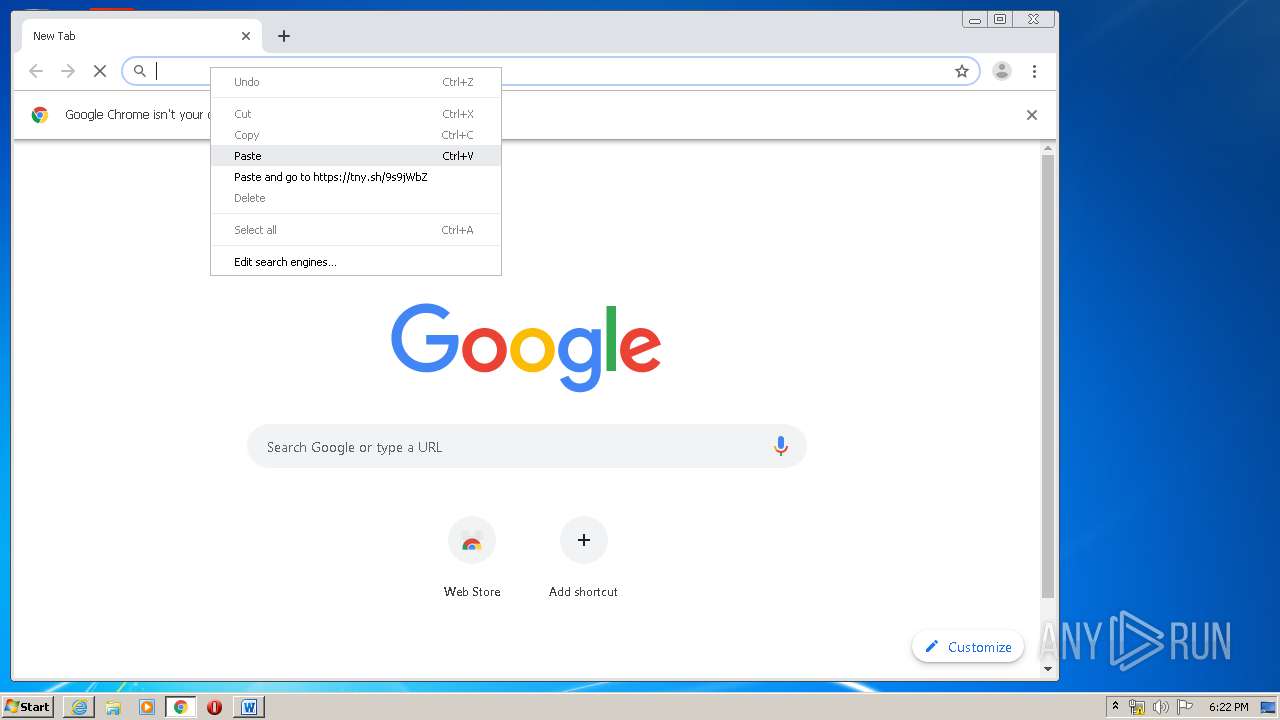
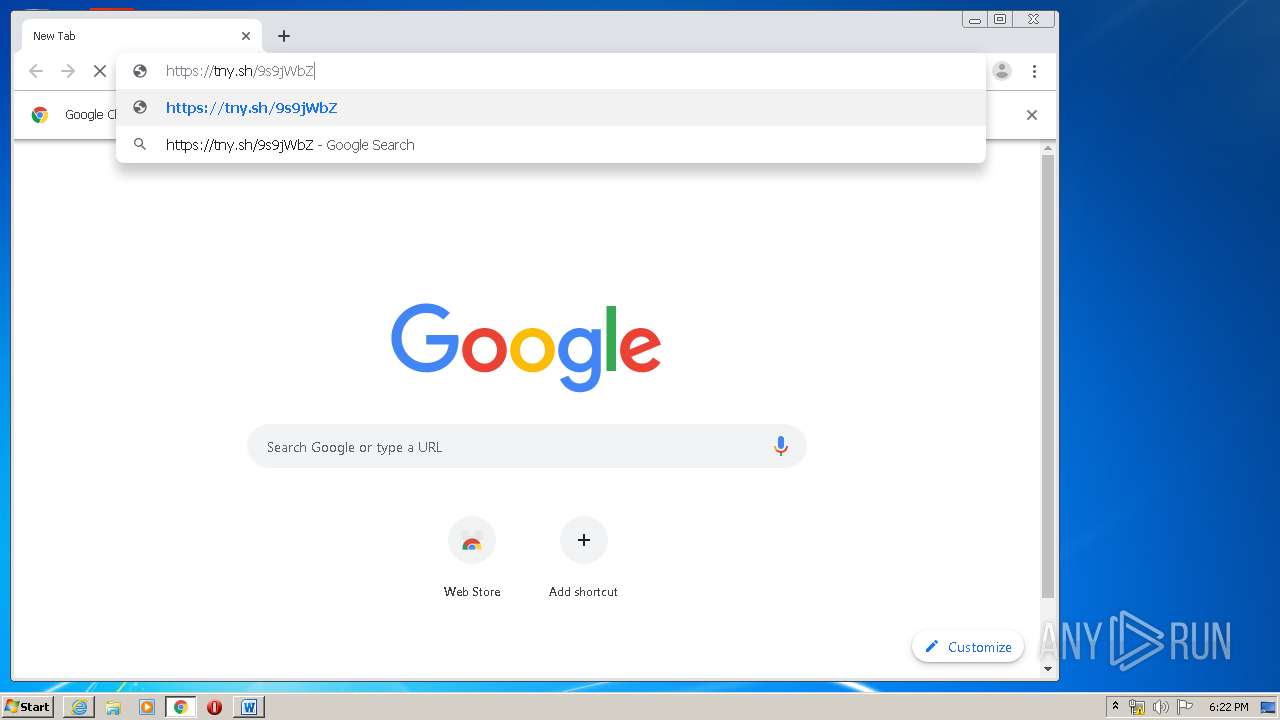
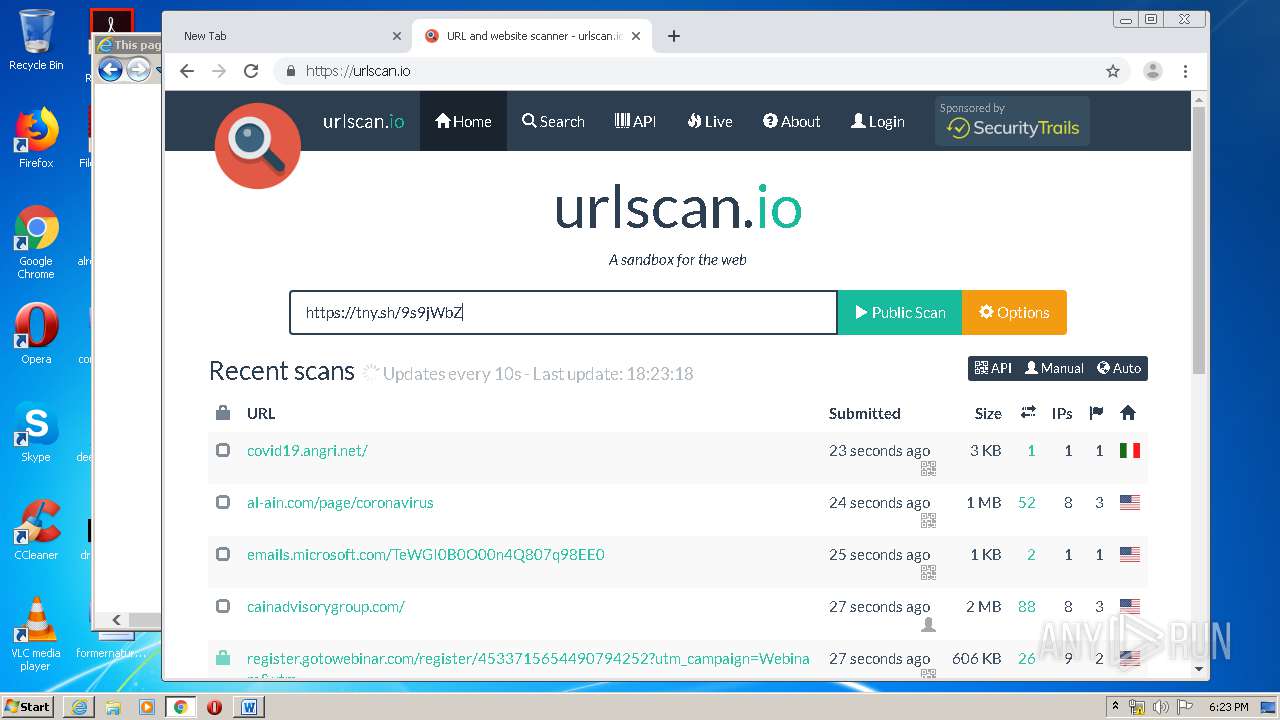
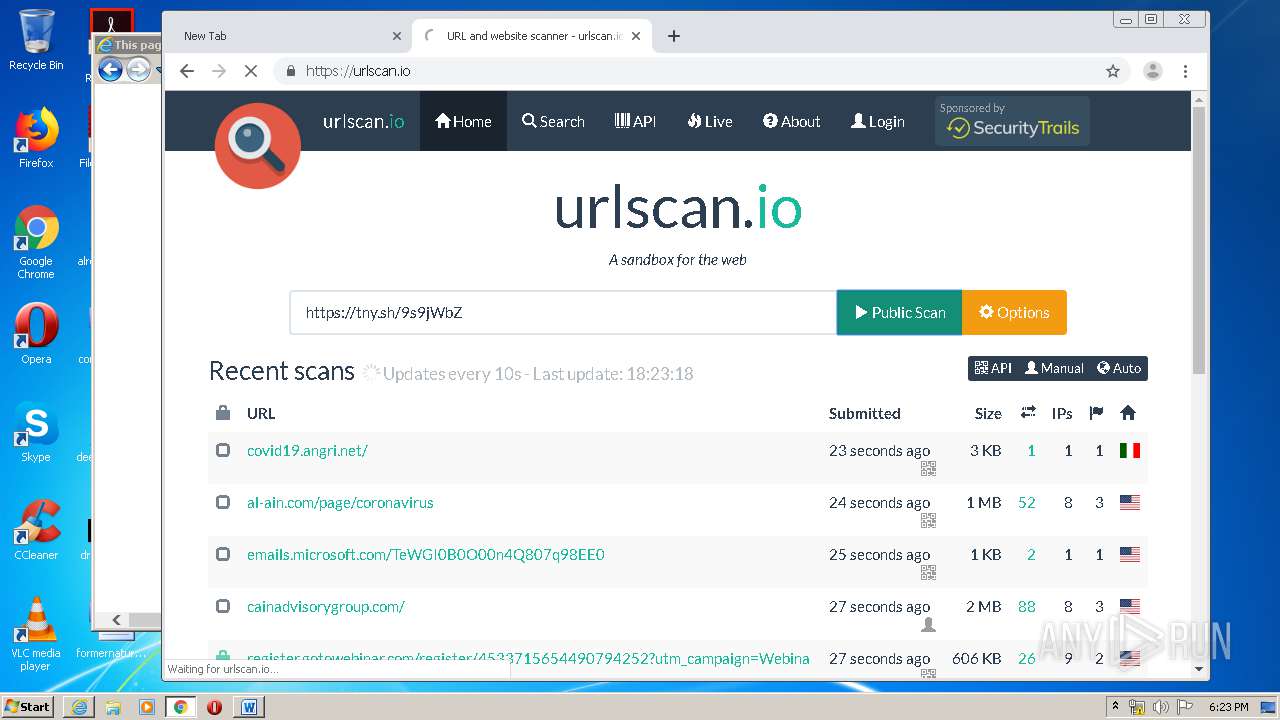
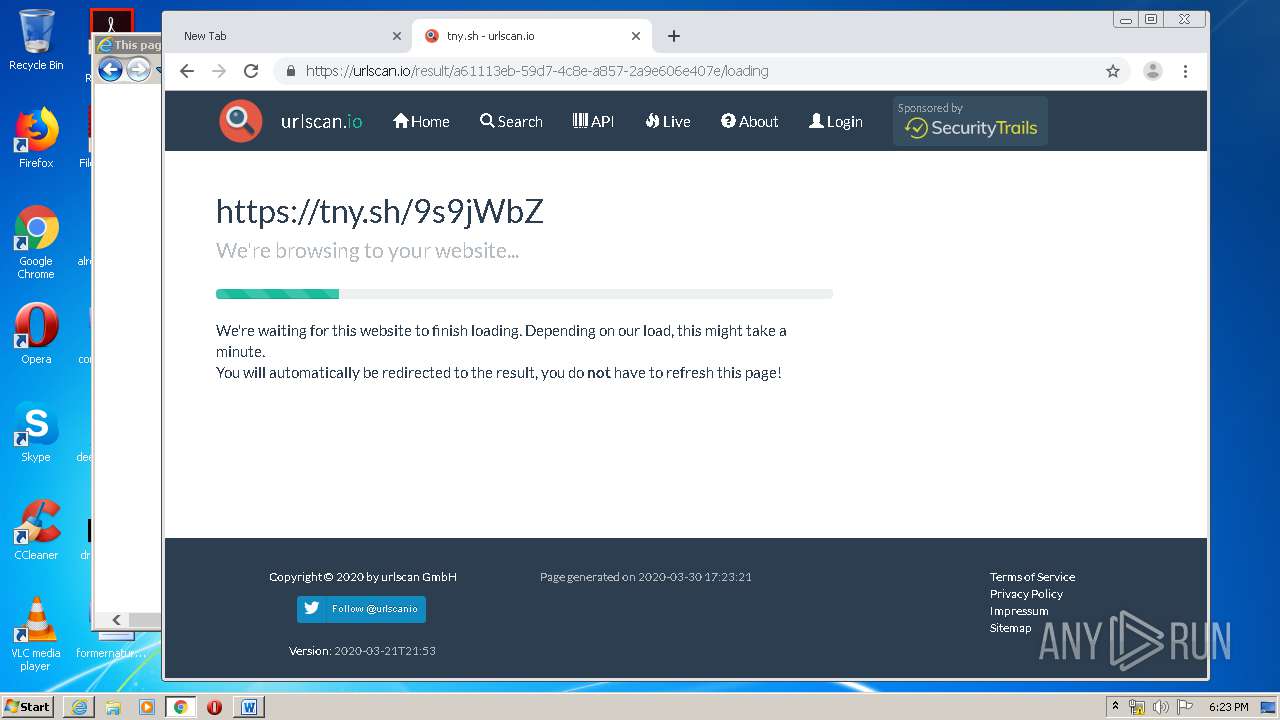
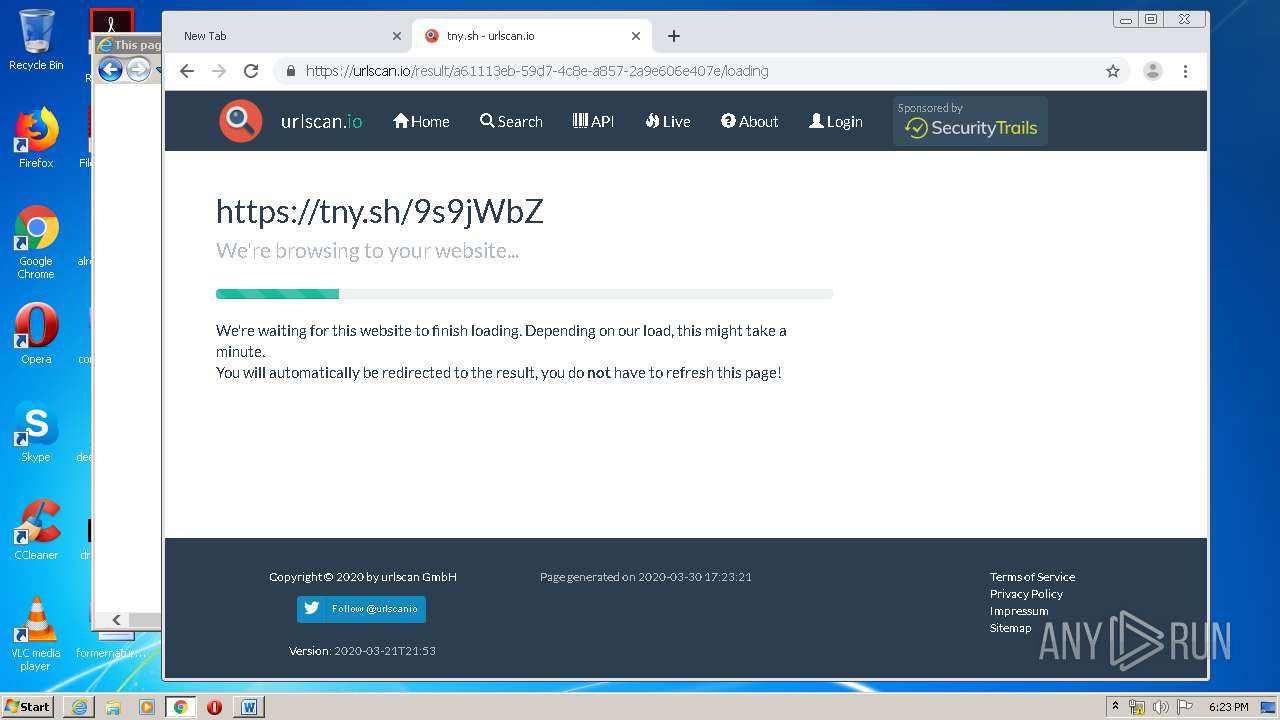
tny.sh |
| whitelisted |
apps.ios-games.begeahg.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
linksplit.io |
| malicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3576 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3576 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3576 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3576 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3576 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3576 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3576 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3576 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3576 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3576 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |