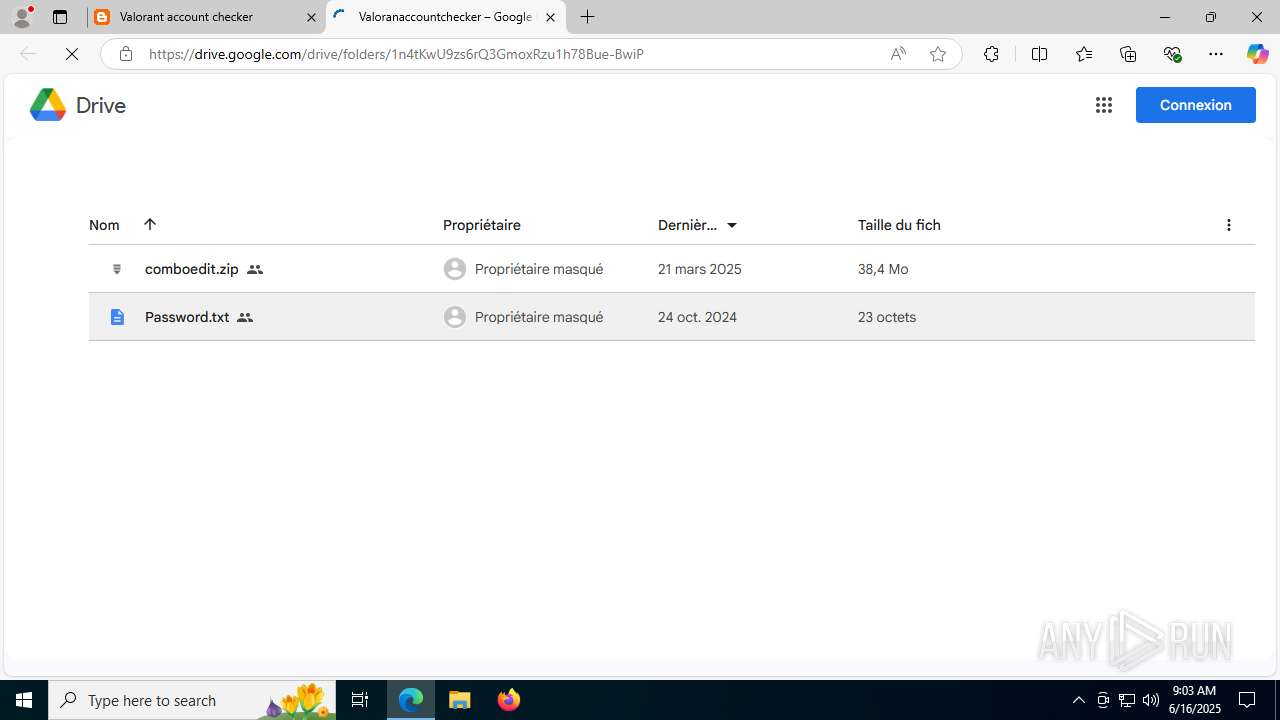
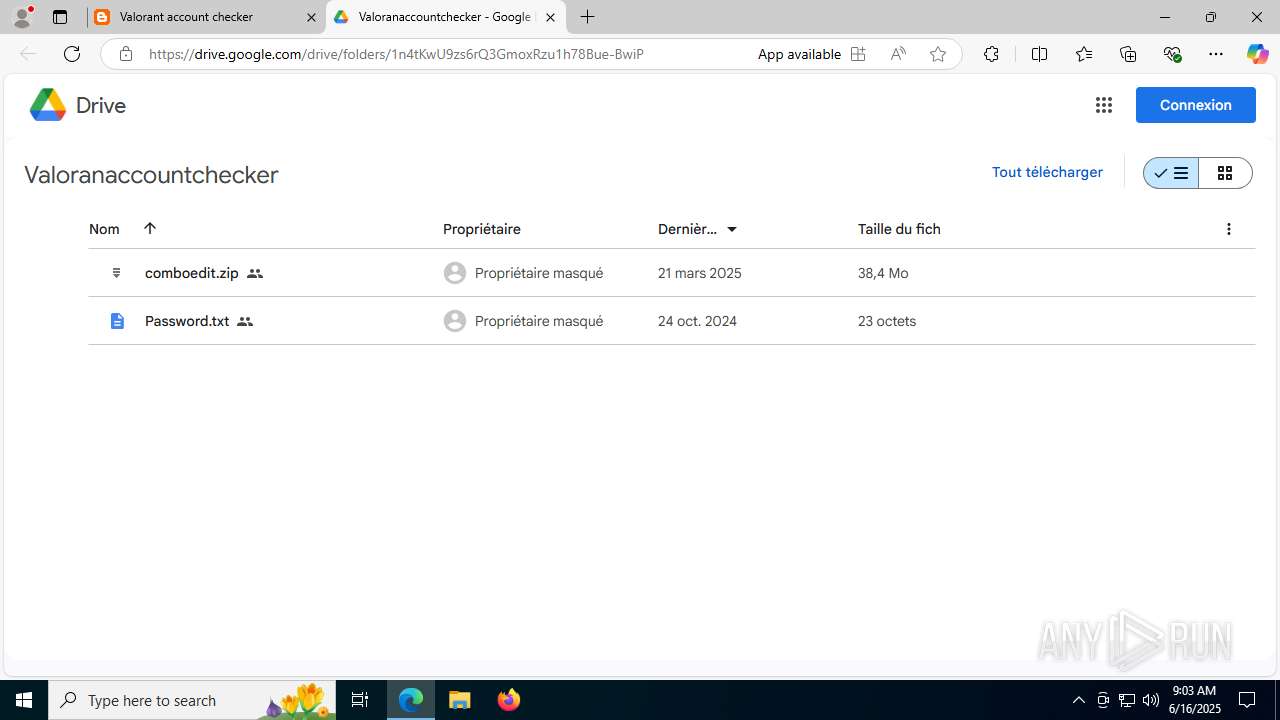
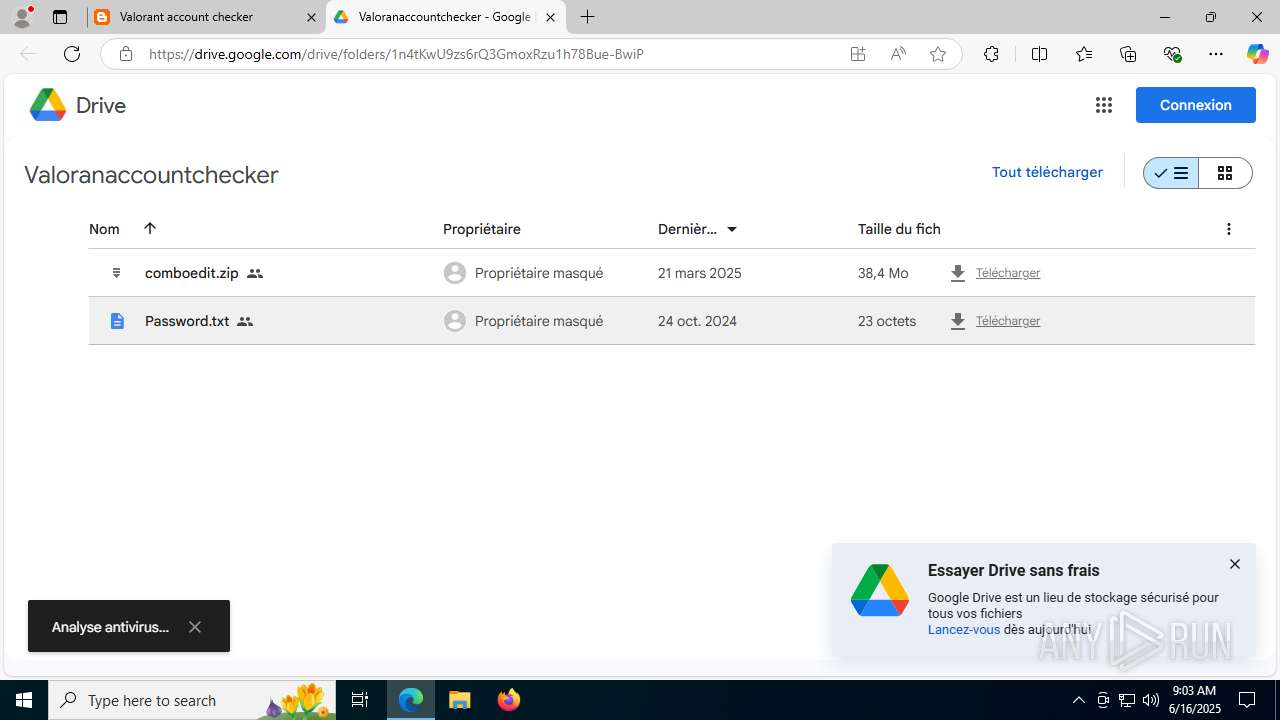
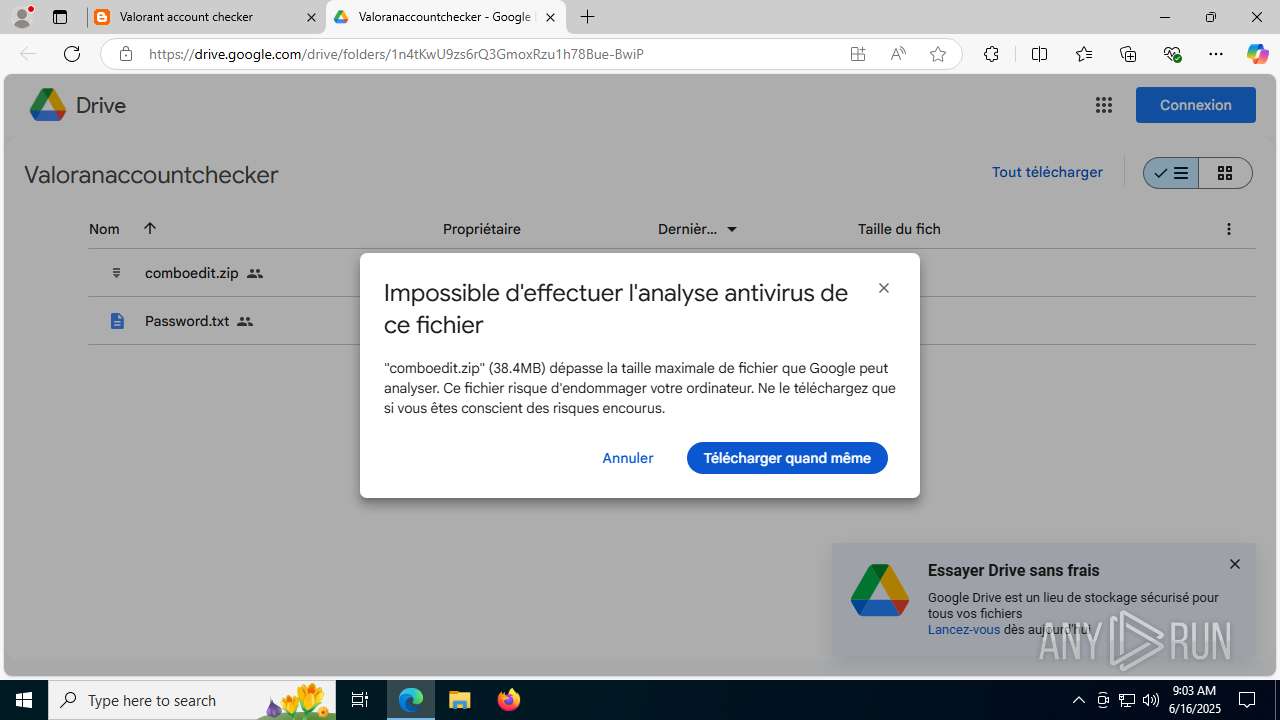
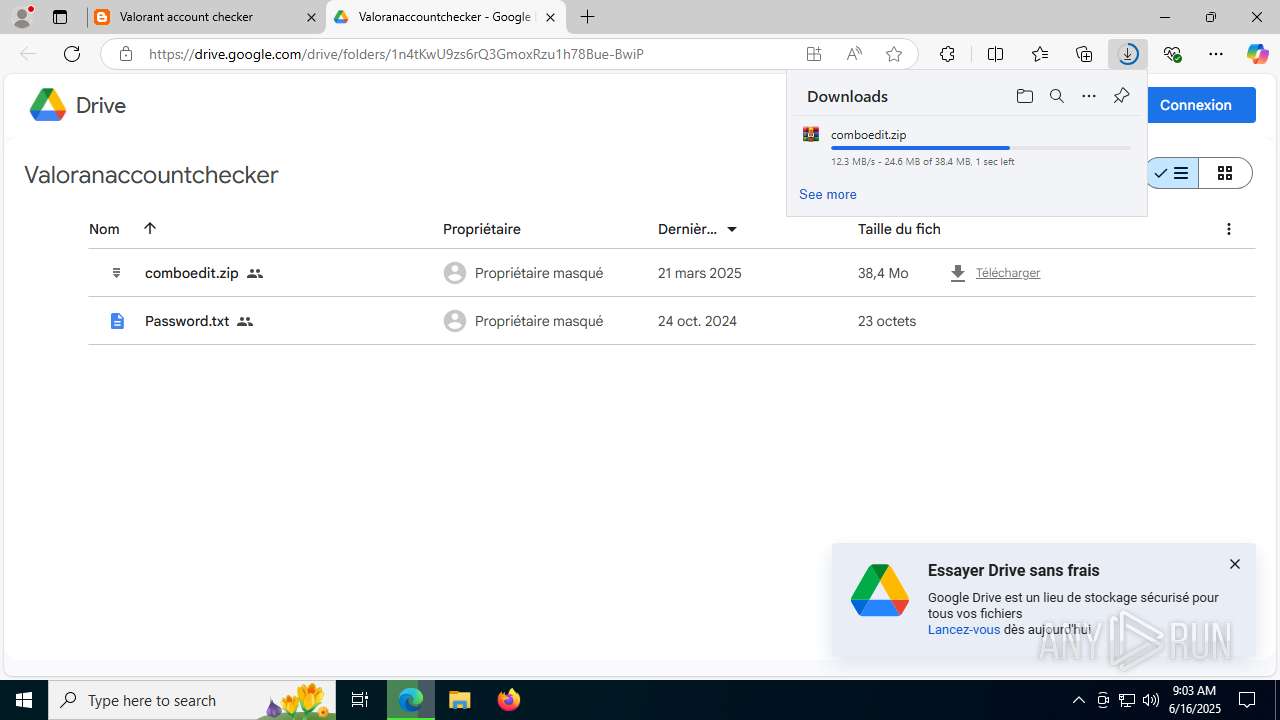
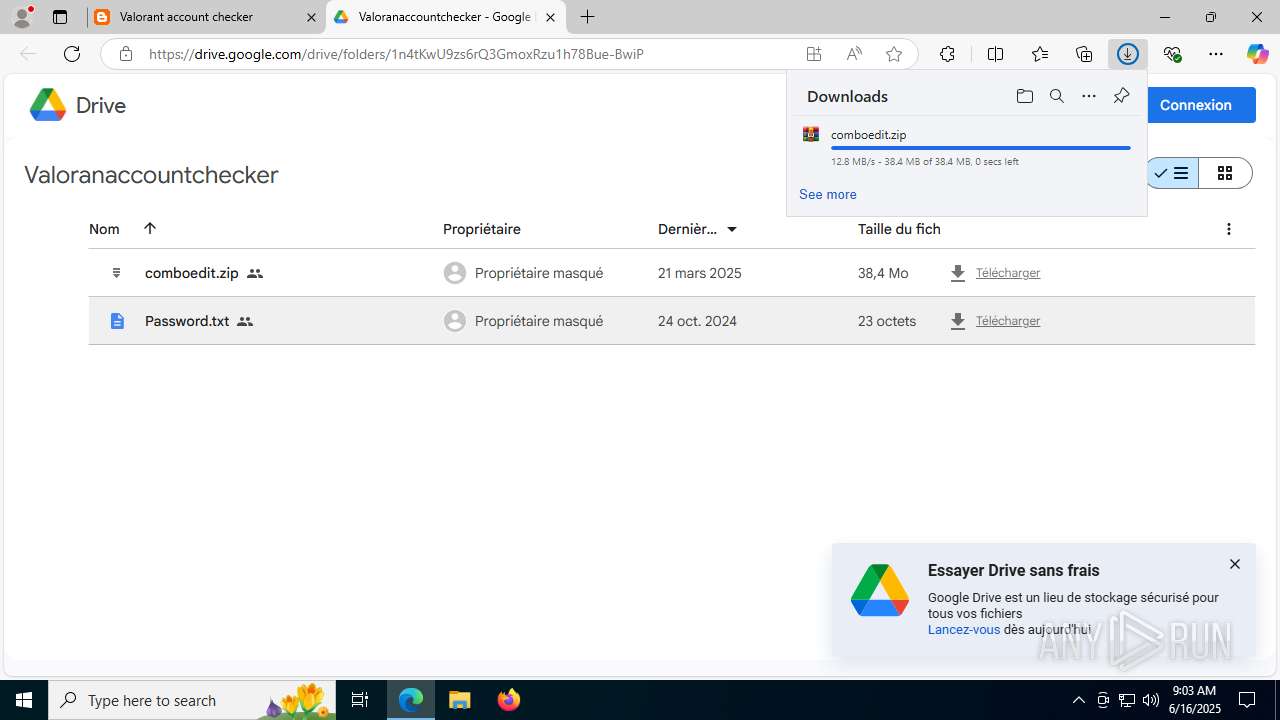
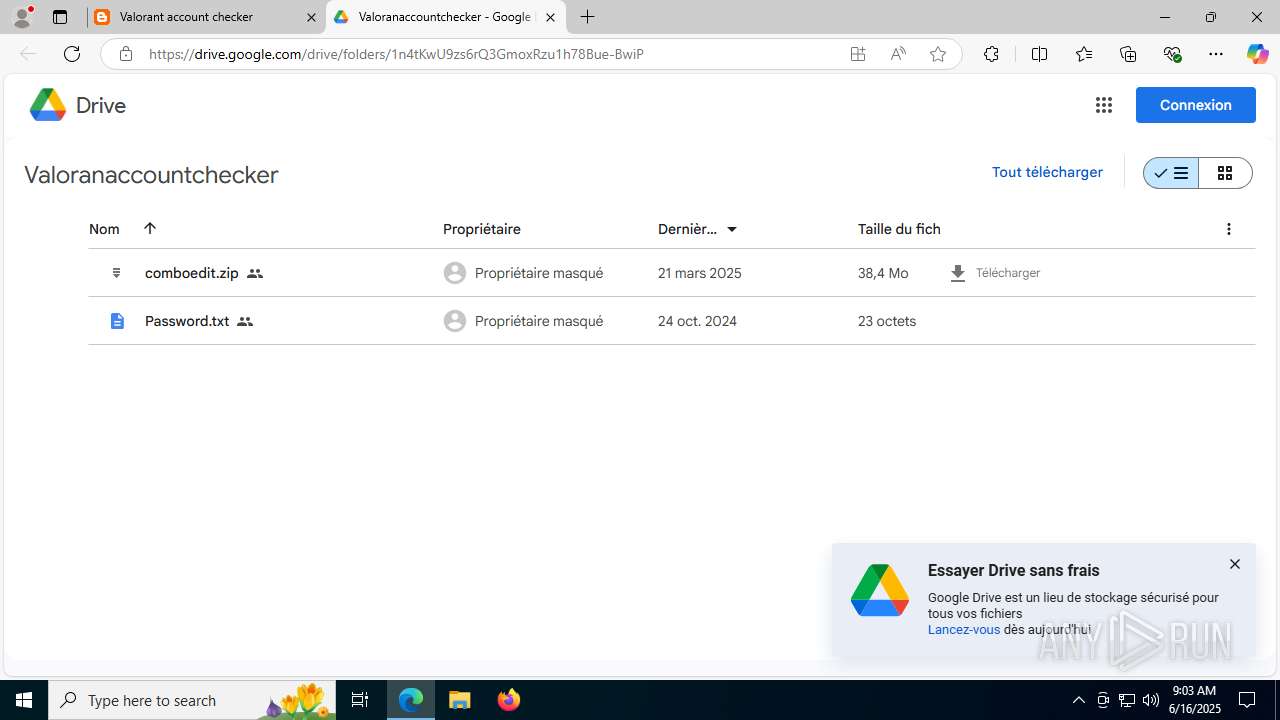
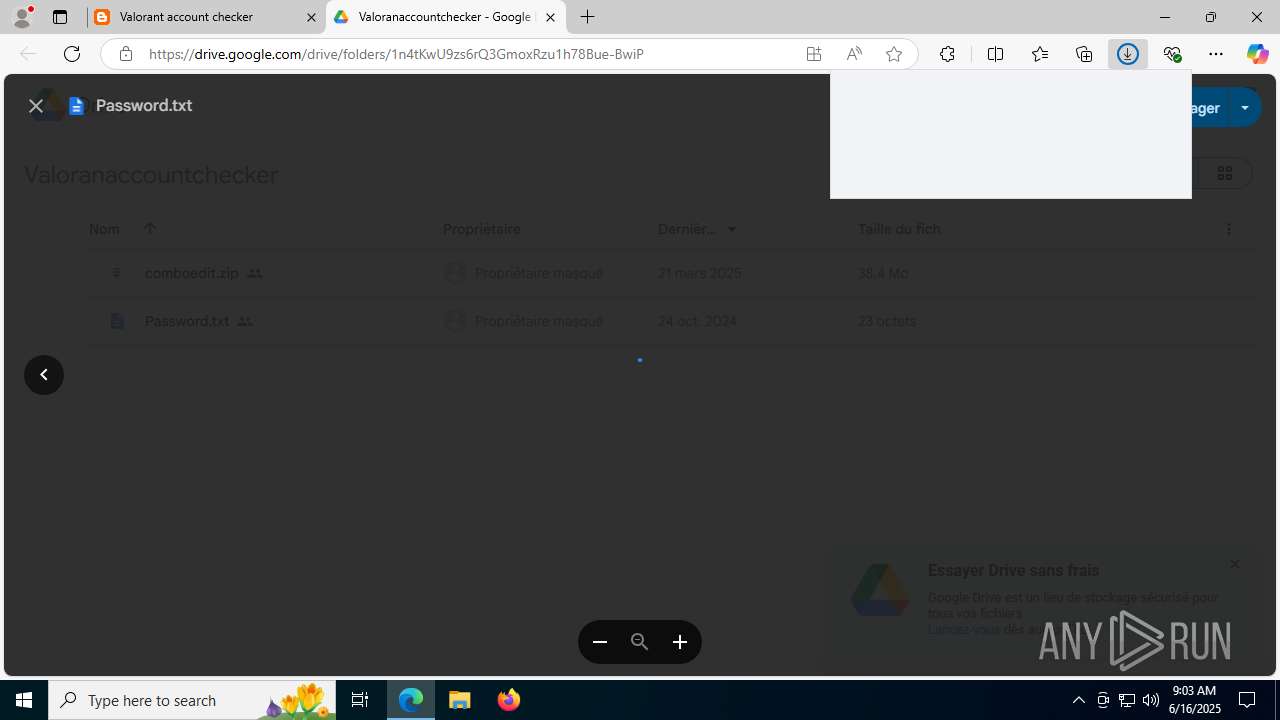
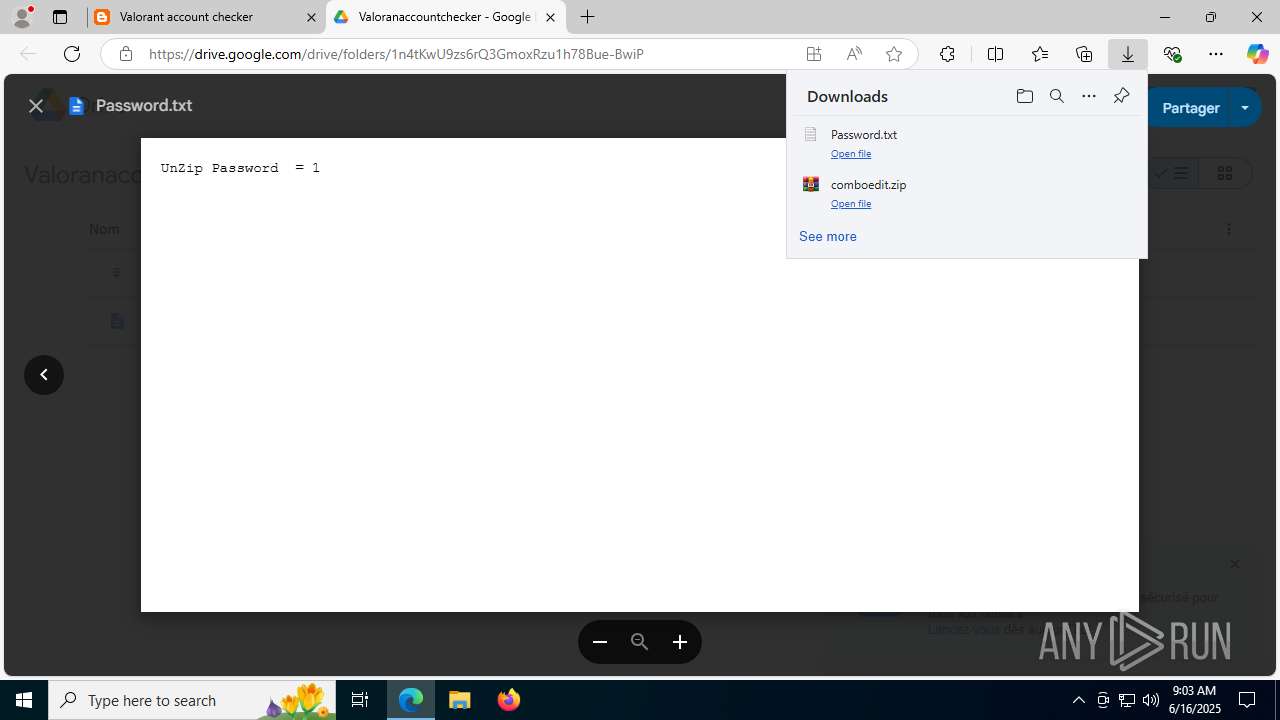
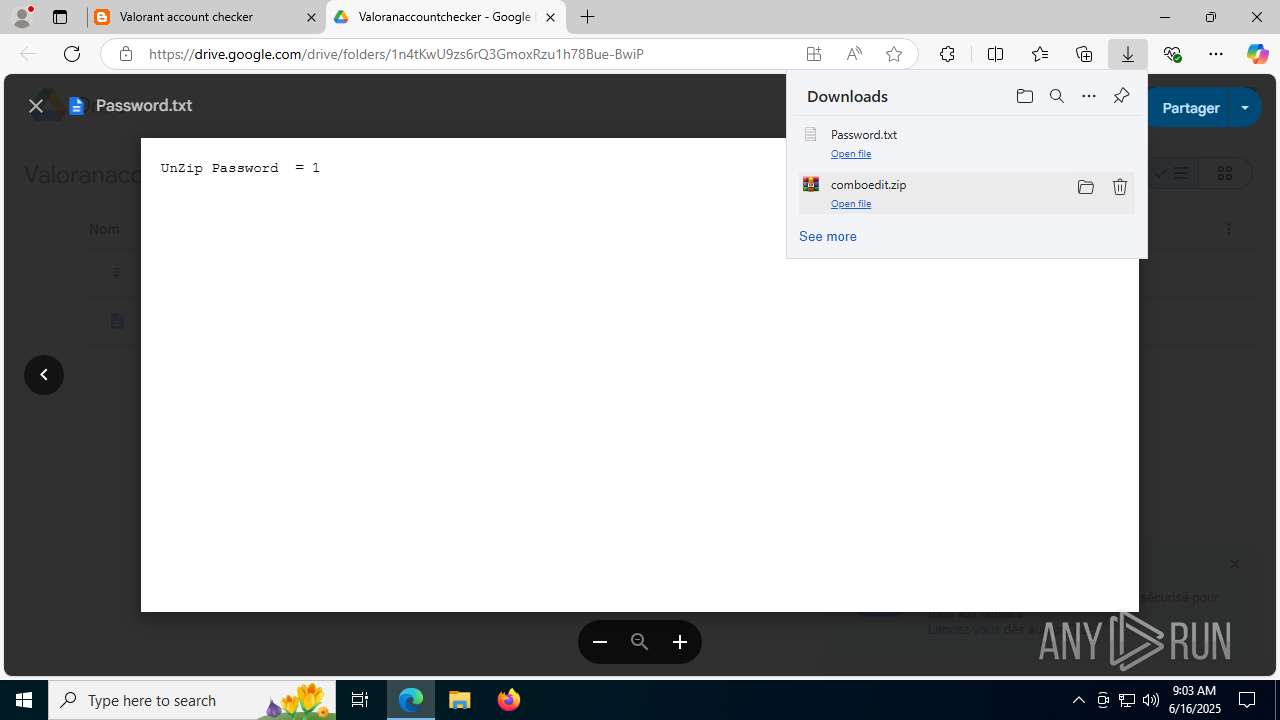
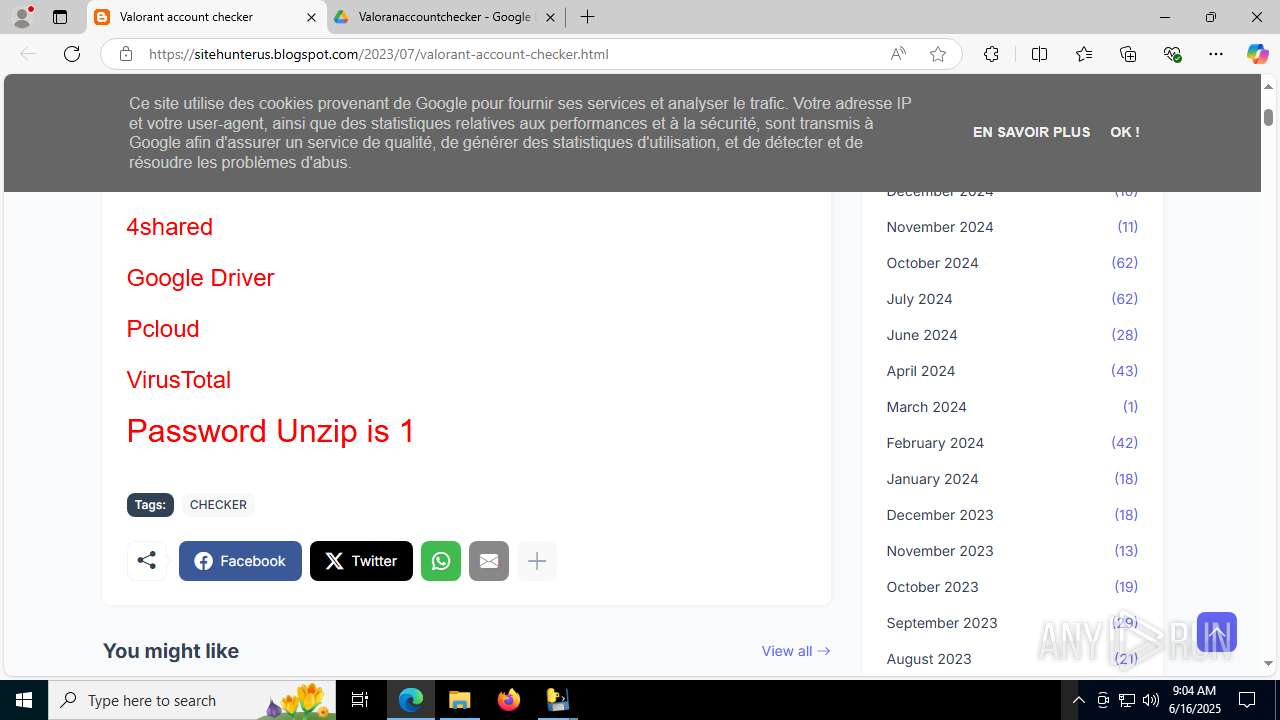
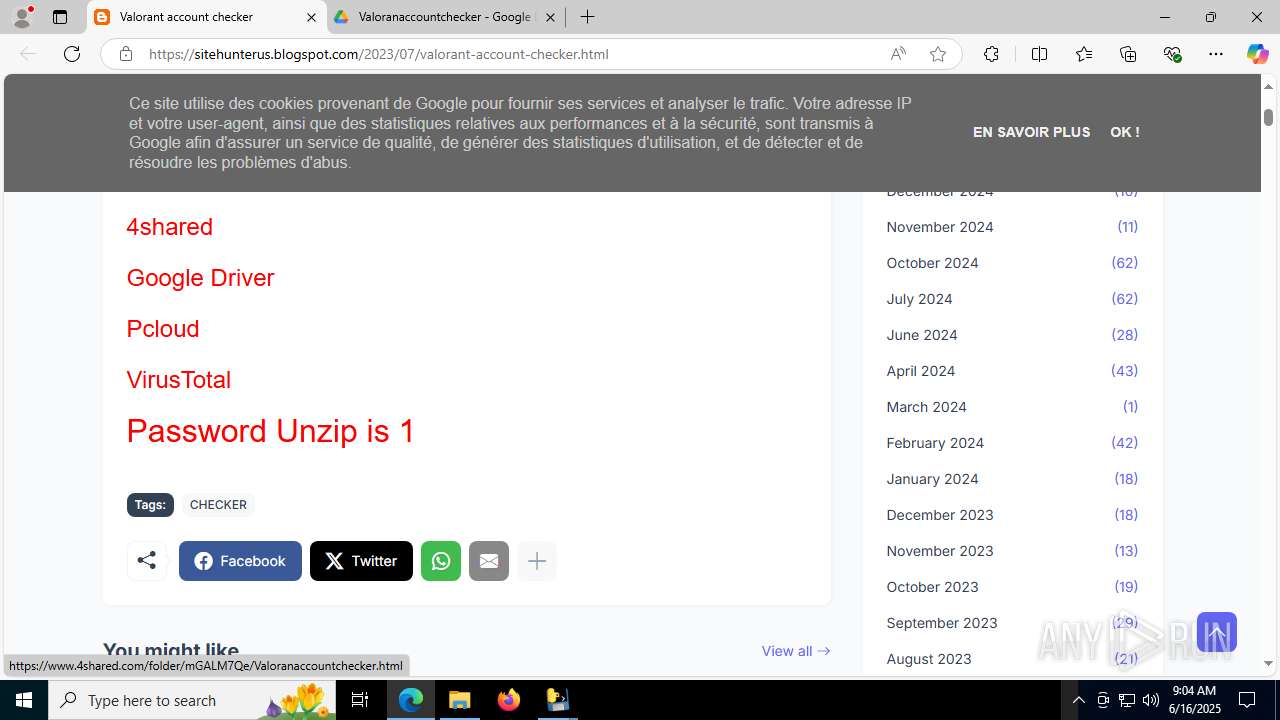
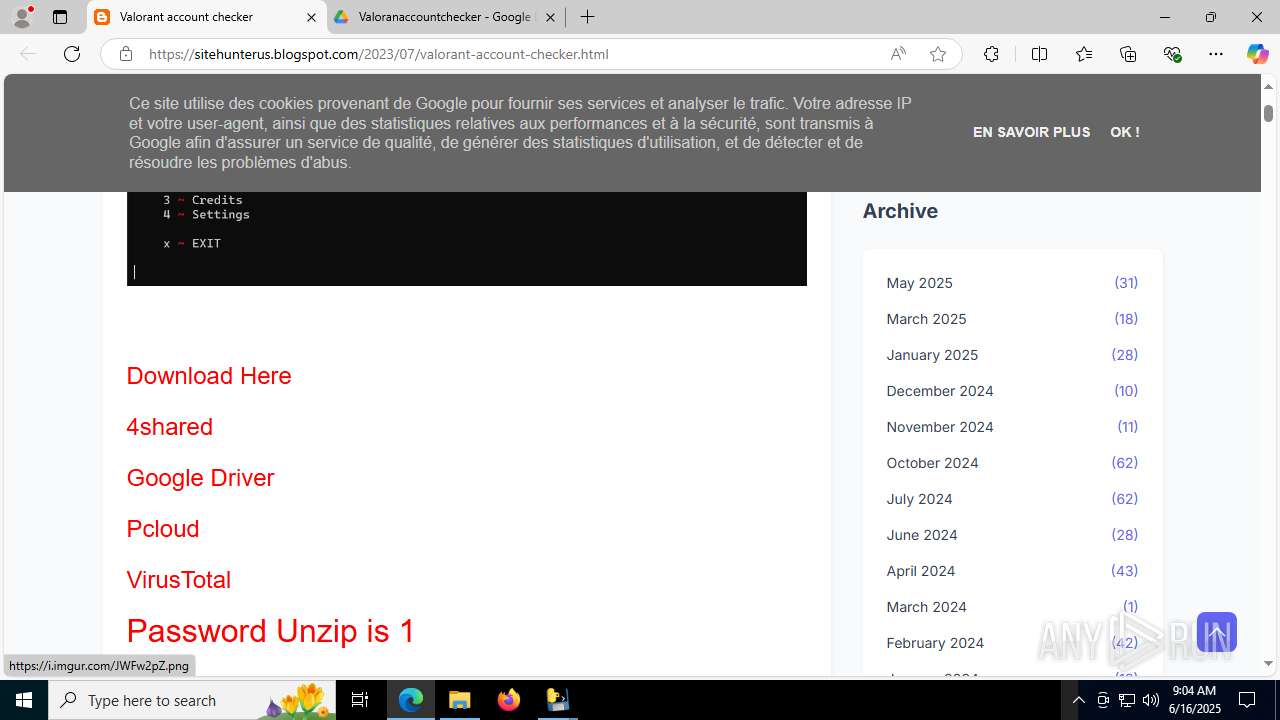
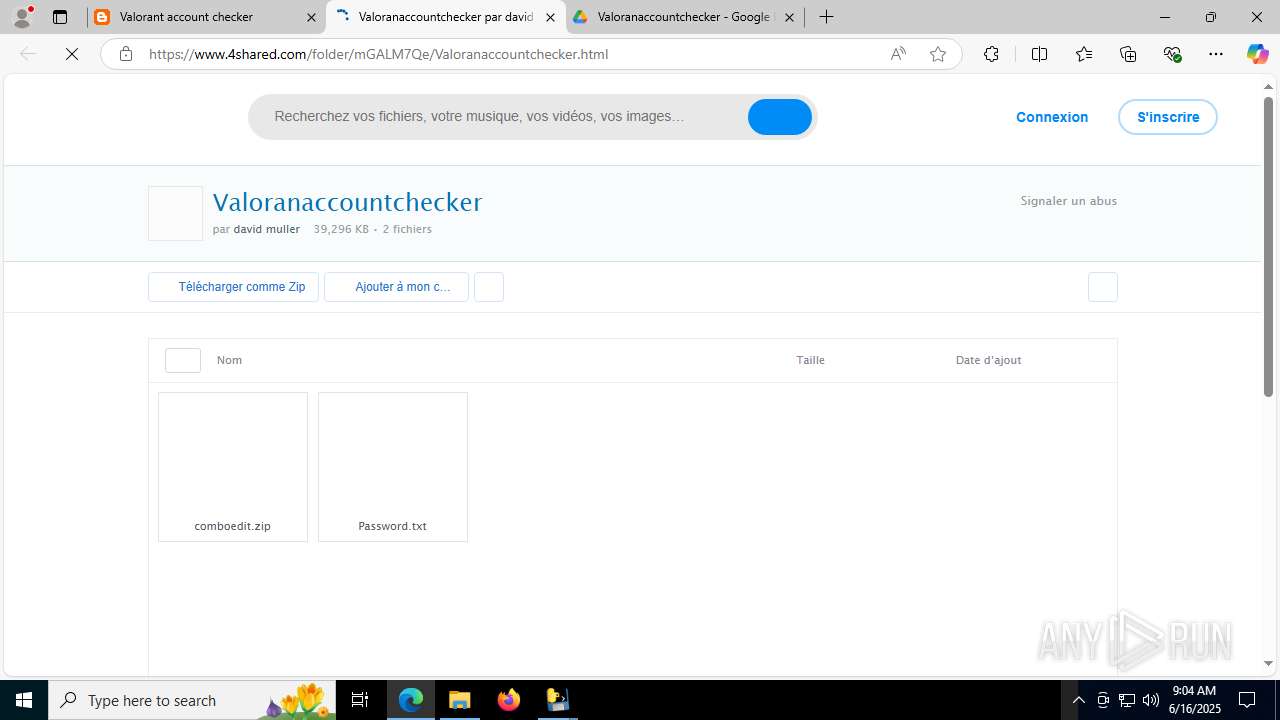
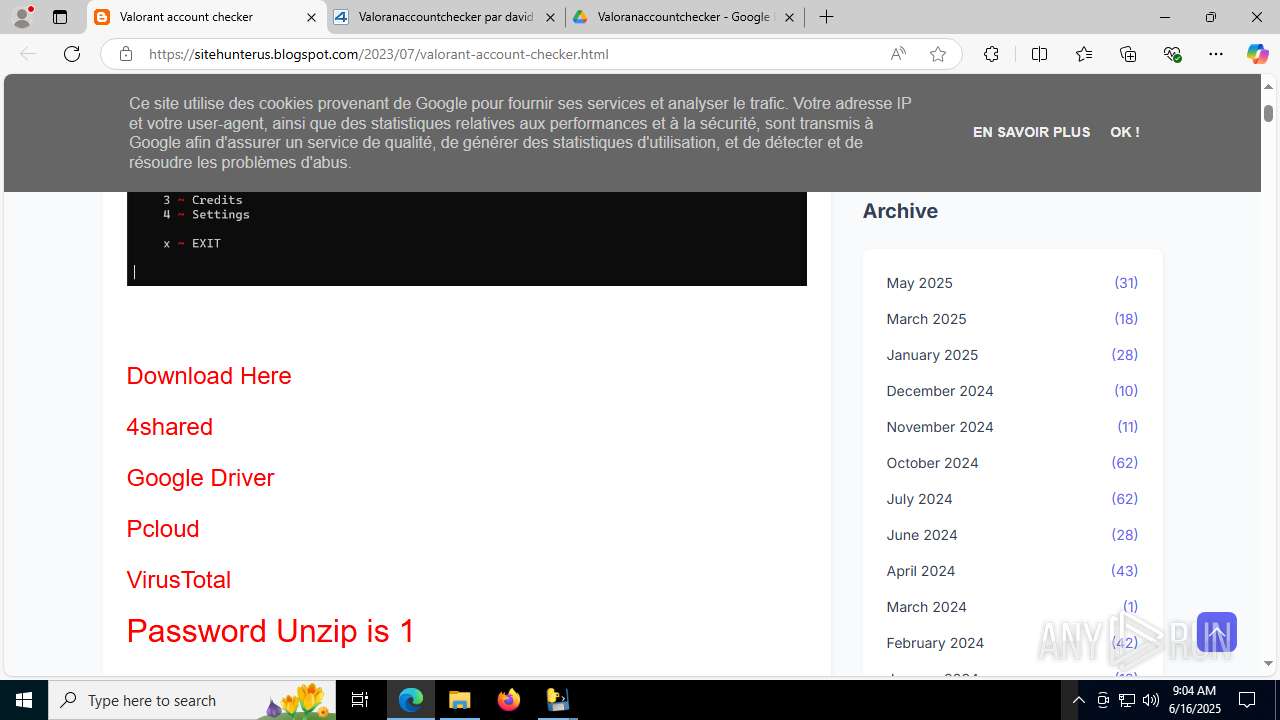
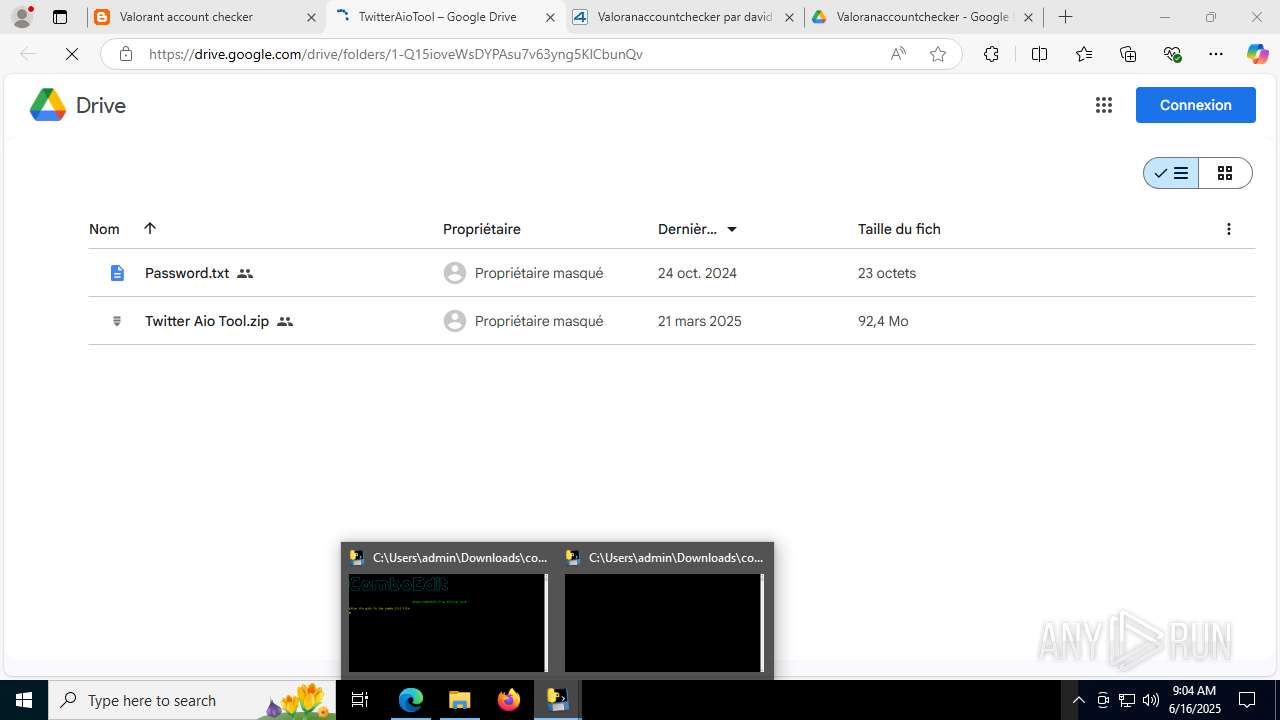
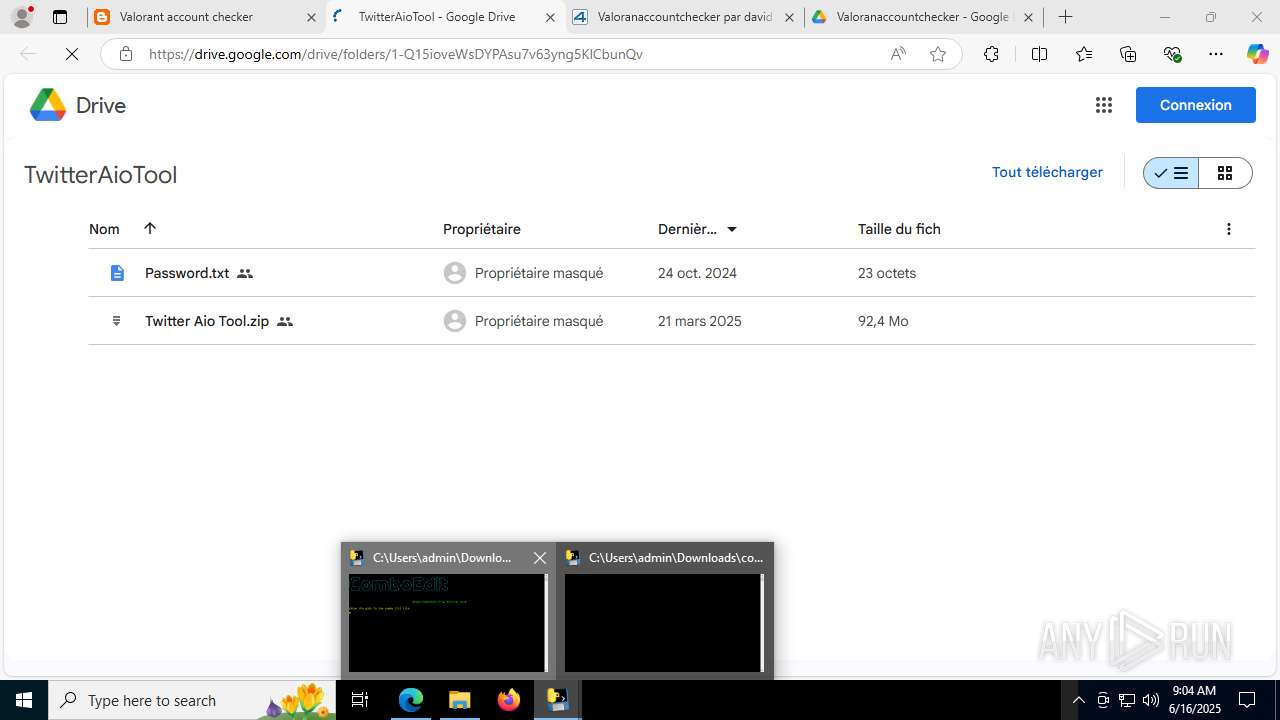
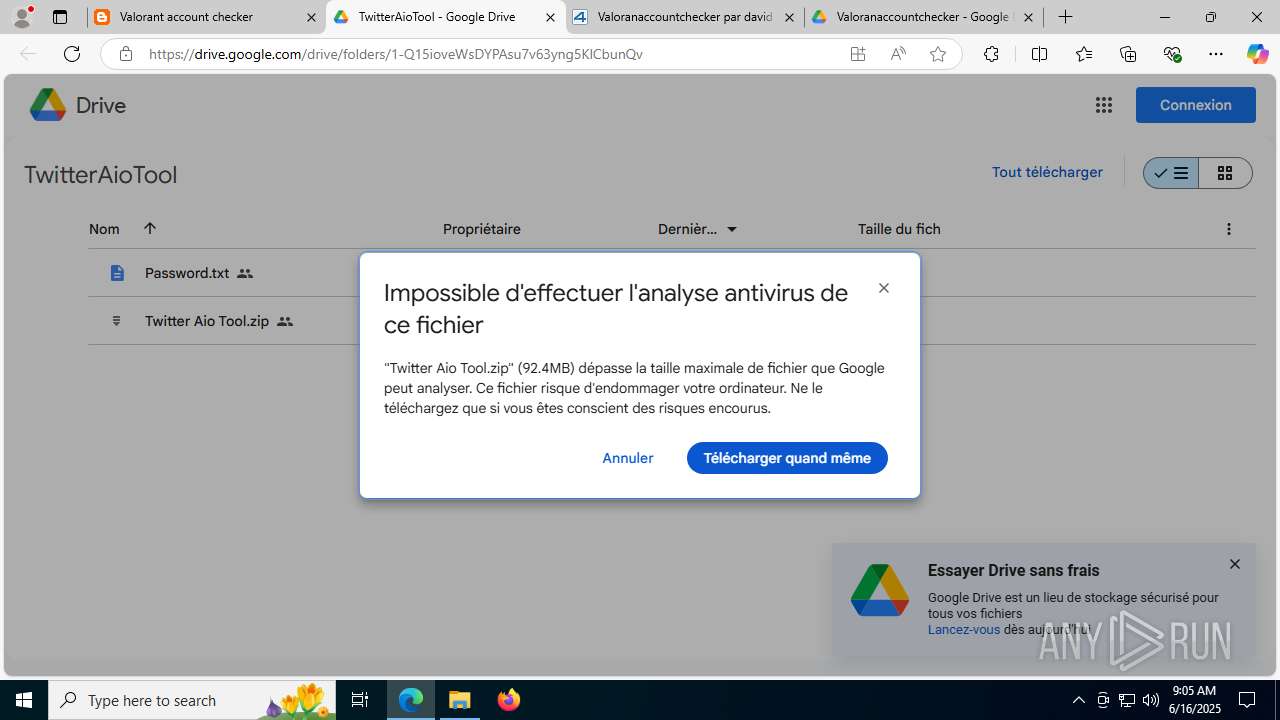
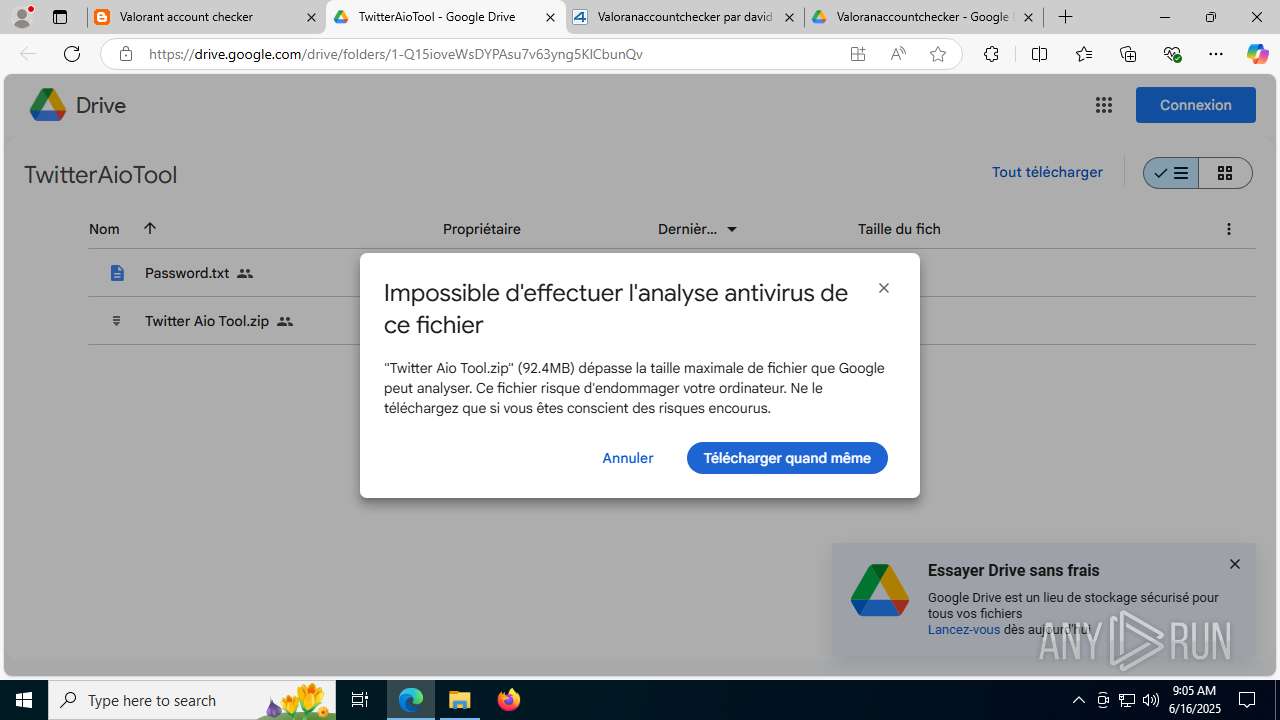
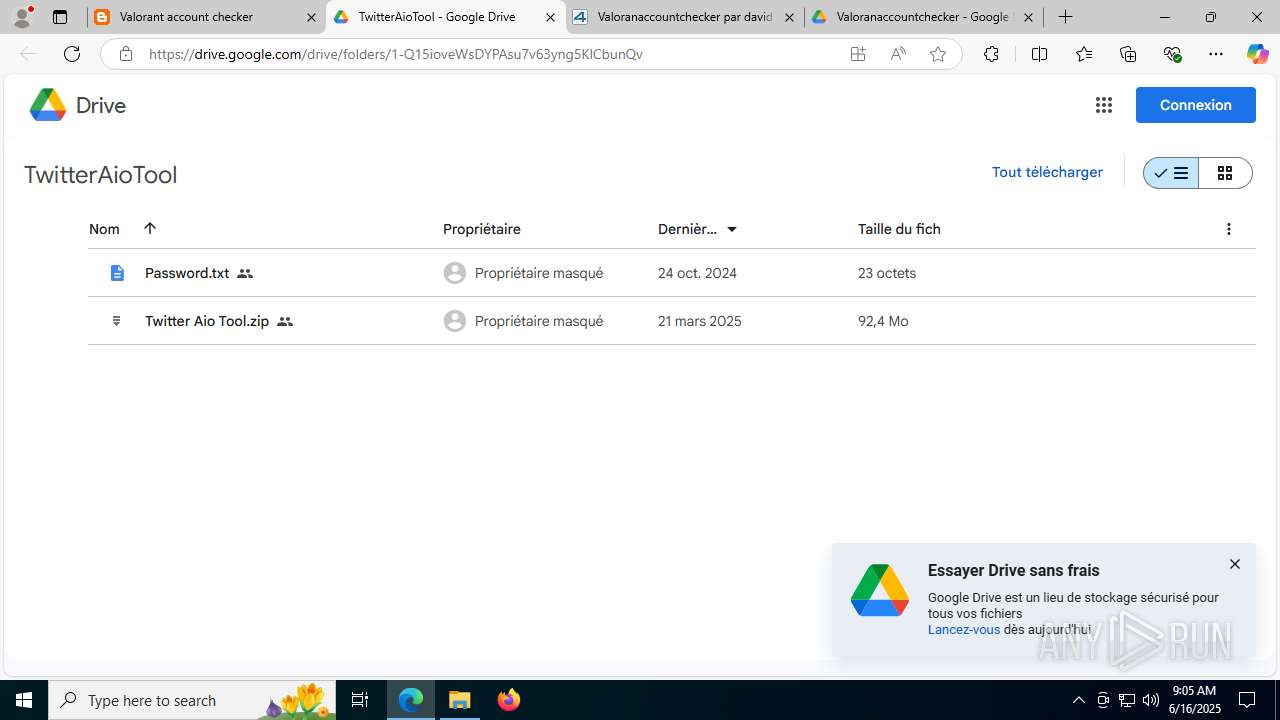
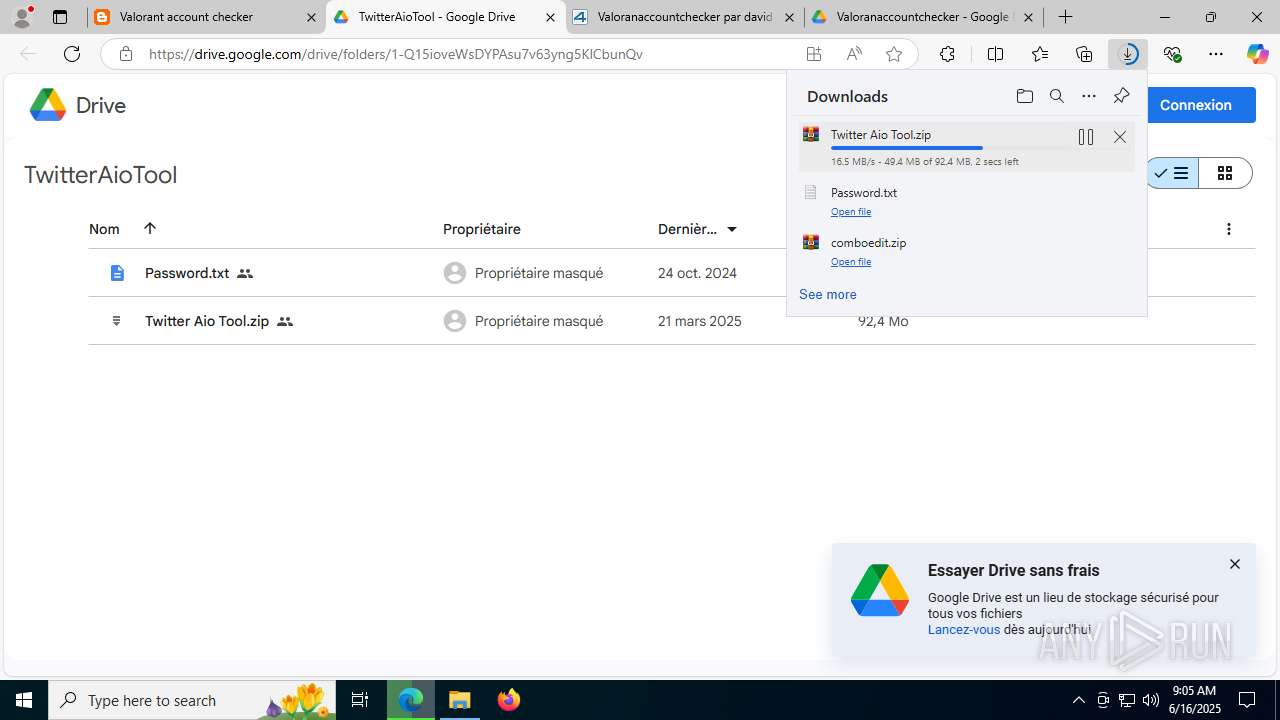
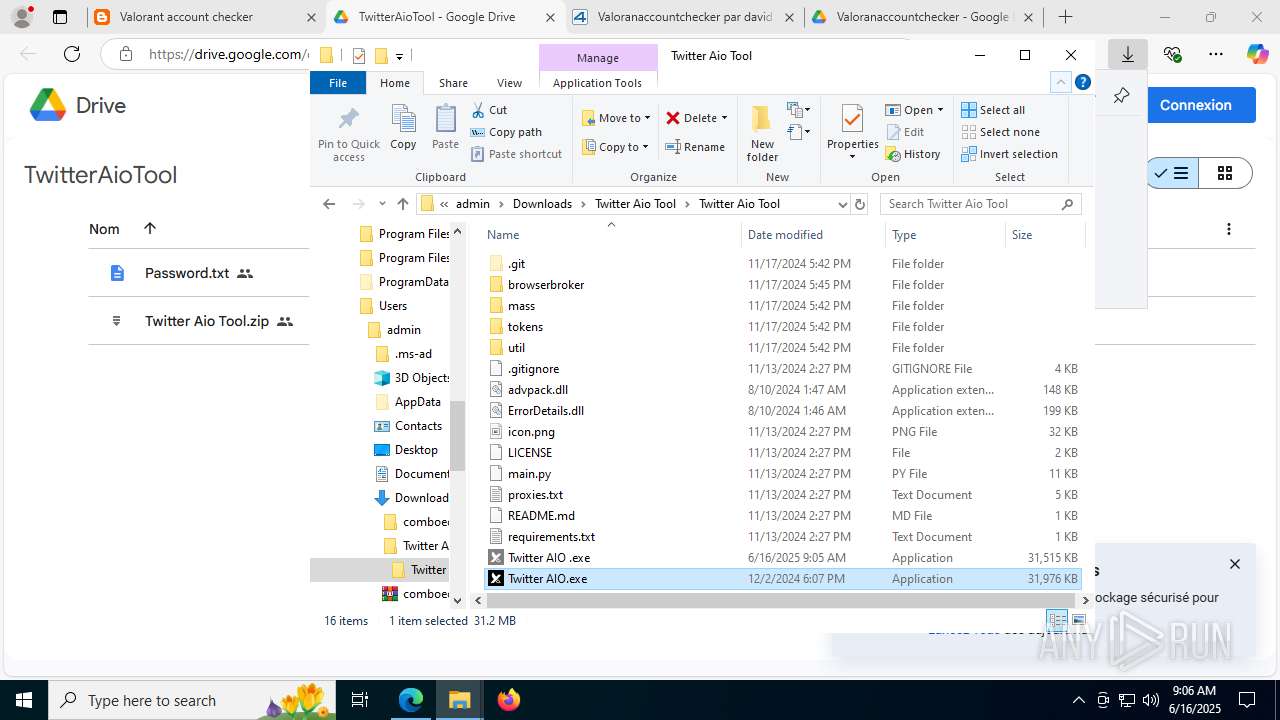
| URL: | https://sitehunterus.blogspot.com/2023/07/valorant-account-checker.html |
| Full analysis: | https://app.any.run/tasks/e92fd9f3-16d2-4588-96e2-79544cafd778 |
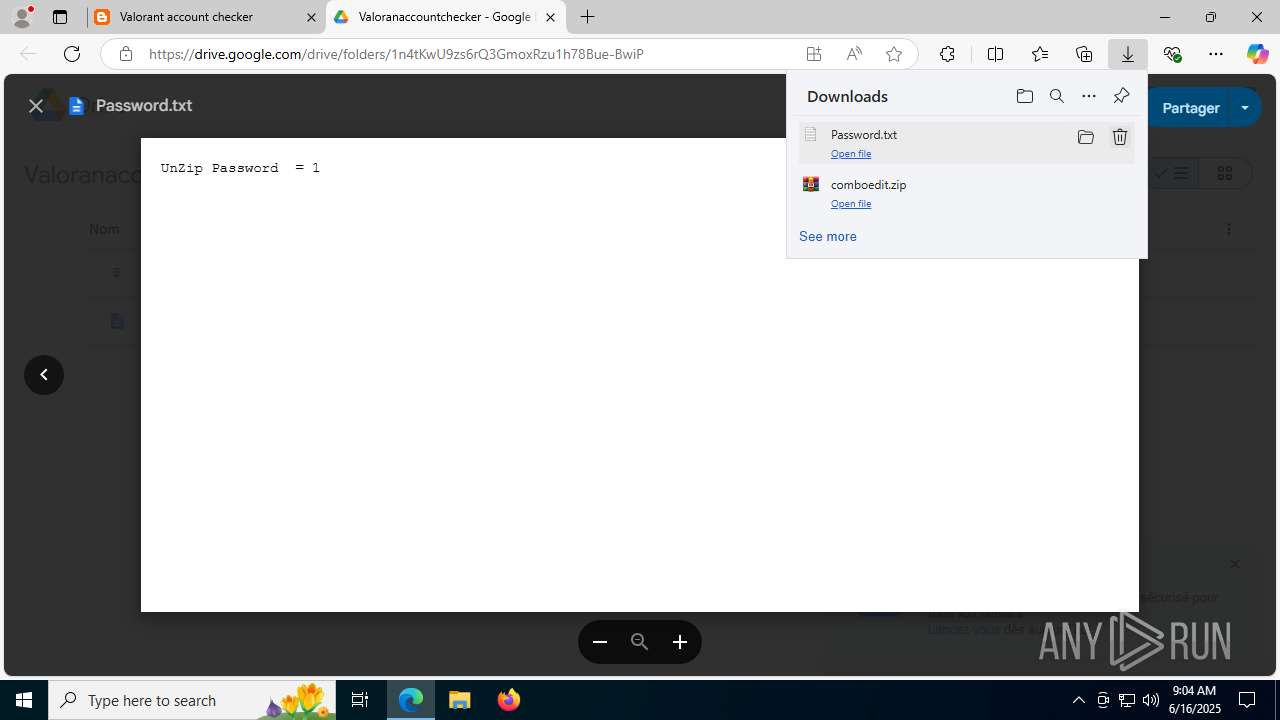
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2025, 09:03:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 99D7DDE4A107FE27F410061AA832C081 |
| SHA1: | 05DD9A648C2F535CF5BBCE5B8D402755CA9BF51A |
| SHA256: | 3561B098843CFB32BFF9ED85E5470634275F58ED34F53B876D56D3A53360DC51 |
| SSDEEP: | 3:N8B6vHXKM0O57ELR5R/JNjORJ:2ov3KM57ELV/J1Ov |
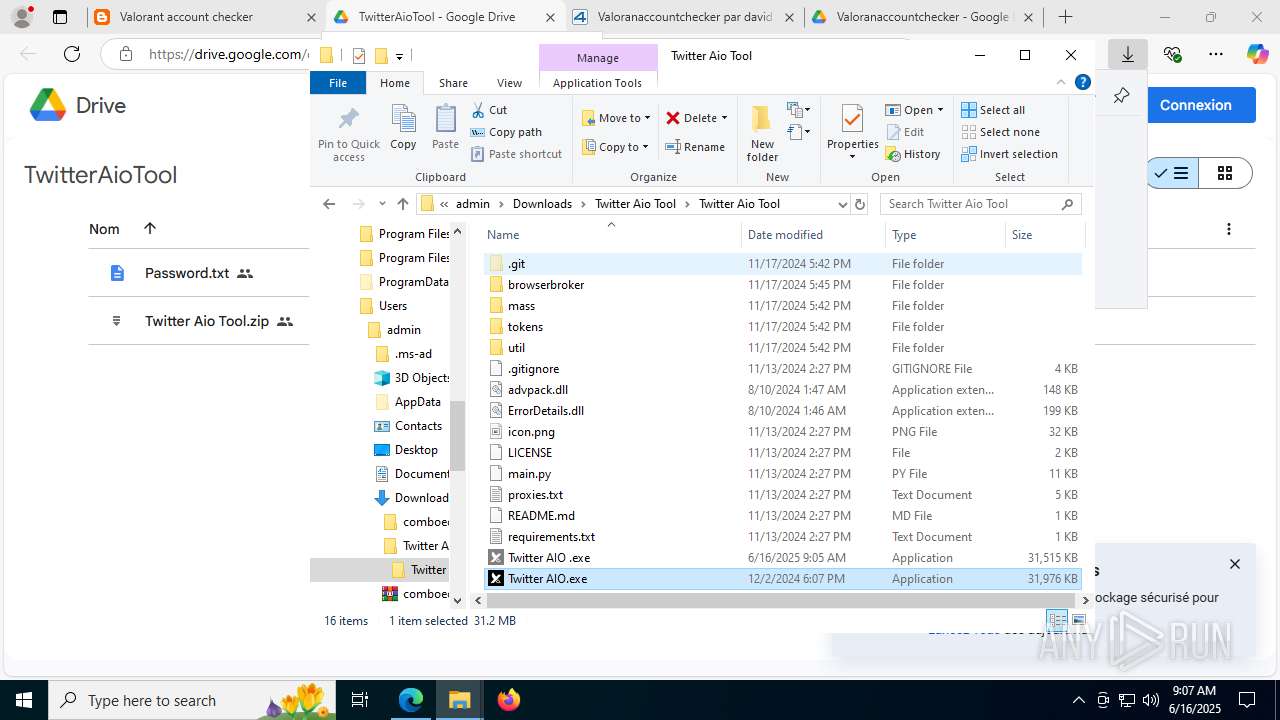
MALICIOUS
Changes the autorun value in the registry
- Setup.exe (PID: 4088)
- Setup.exe (PID: 7920)
Adds path to the Windows Defender exclusion list
- version.exe (PID: 8148)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 7052)
- cmd.exe (PID: 1508)
- cmd.exe (PID: 4836)
- cmd.exe (PID: 5504)
- cmd.exe (PID: 4444)
Changes Windows Defender settings
- cmd.exe (PID: 7904)
- cmd.exe (PID: 7052)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 1508)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 4836)
- cmd.exe (PID: 4444)
- cmd.exe (PID: 5504)
Run PowerShell with an invisible window
- powershell.exe (PID: 2148)
- powershell.exe (PID: 2728)
- powershell.exe (PID: 8216)
- powershell.exe (PID: 7948)
- powershell.exe (PID: 6520)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 8448)
- powershell.exe (PID: 8684)
Known privilege escalation attack
- dllhost.exe (PID: 5612)
SUSPICIOUS
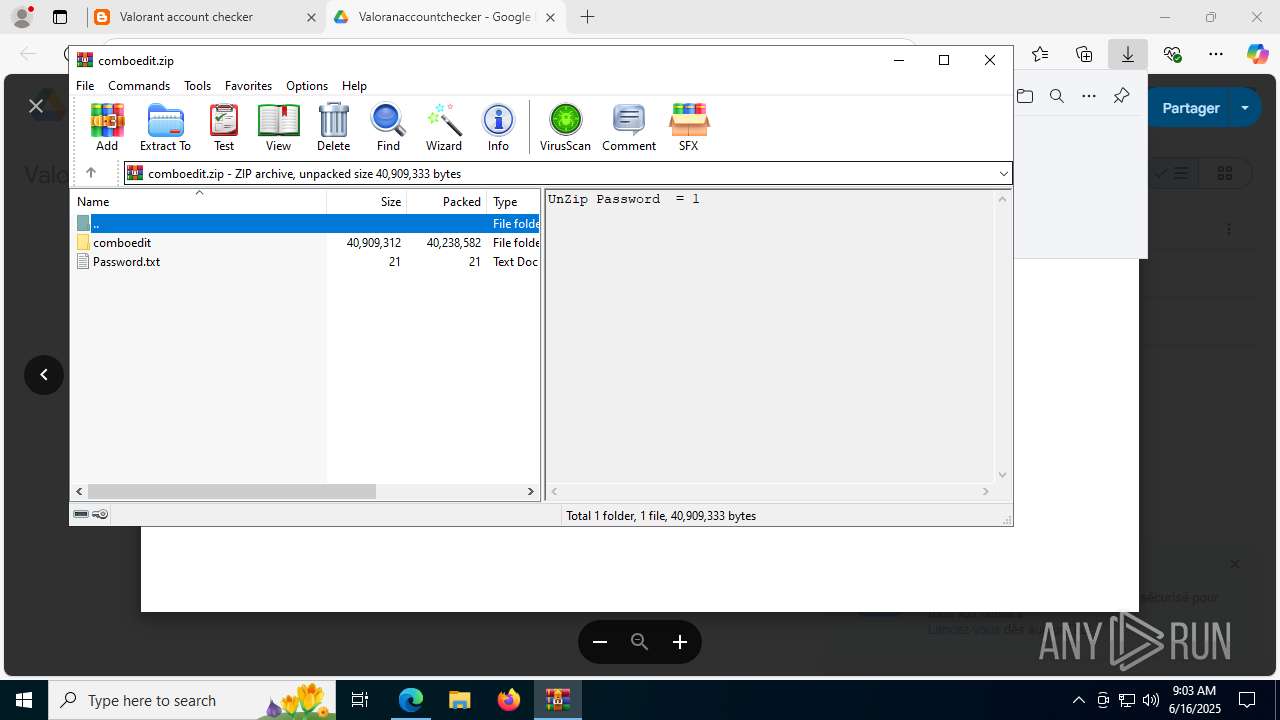
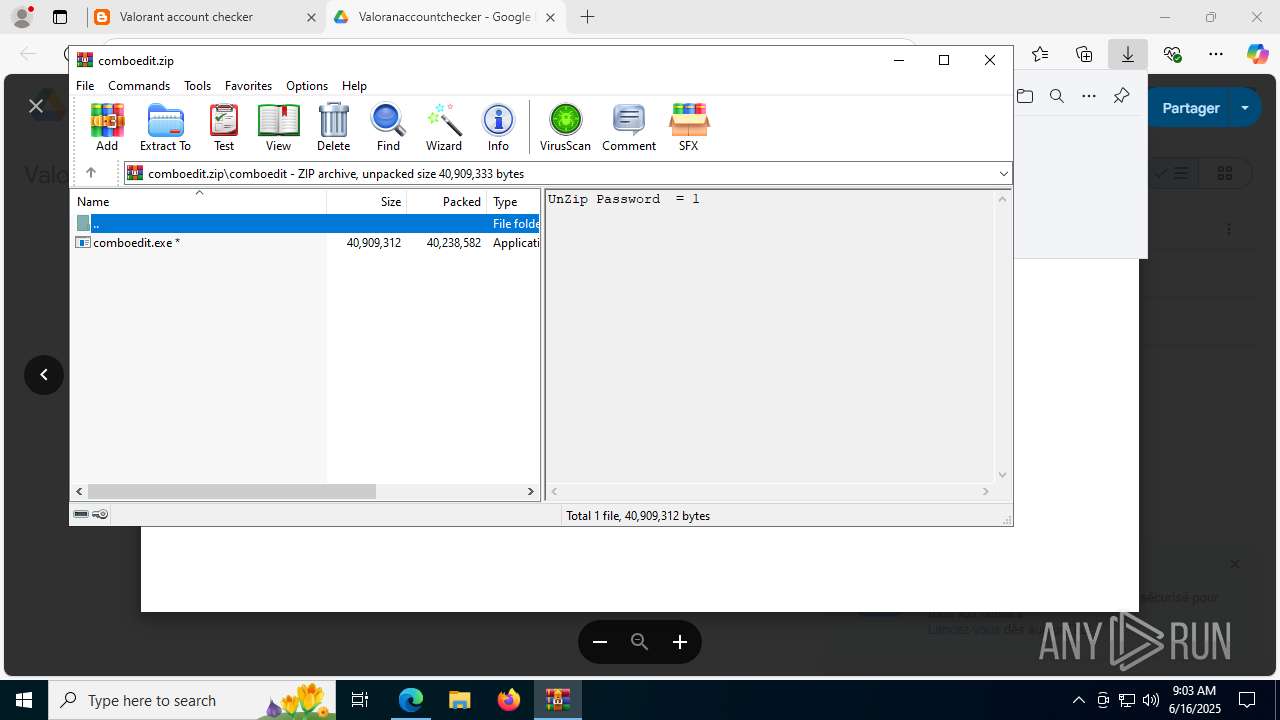
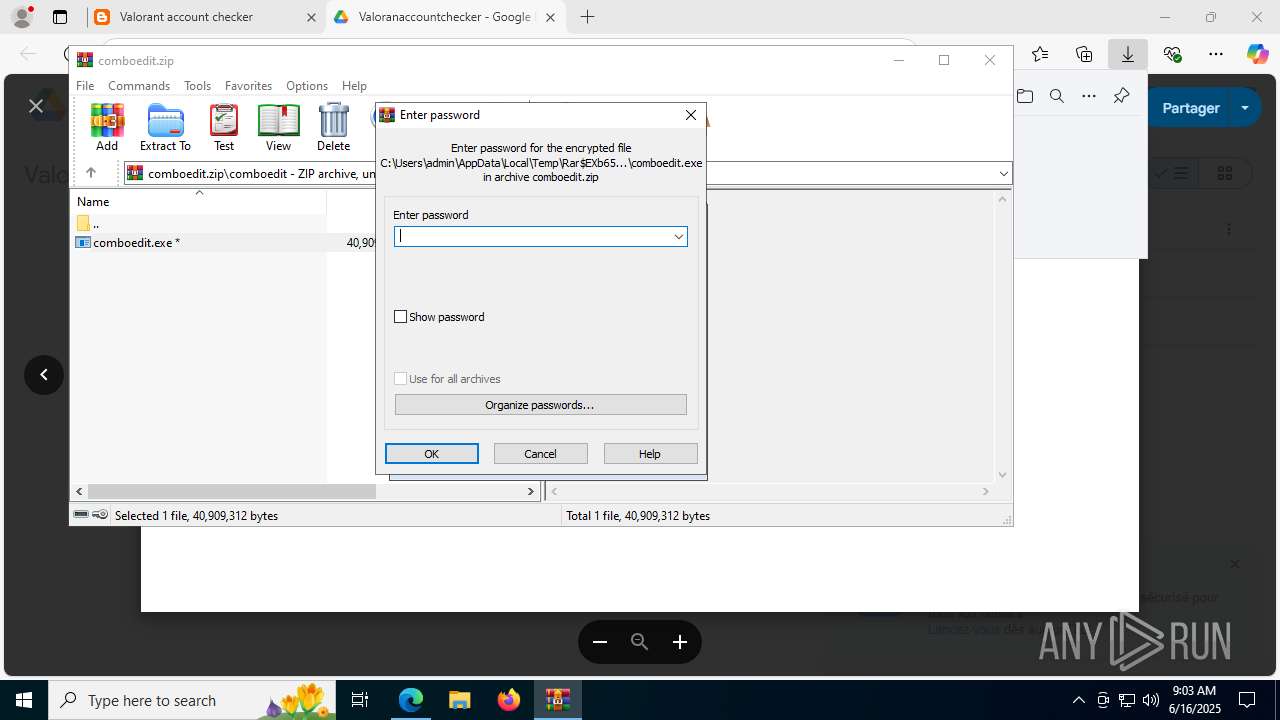
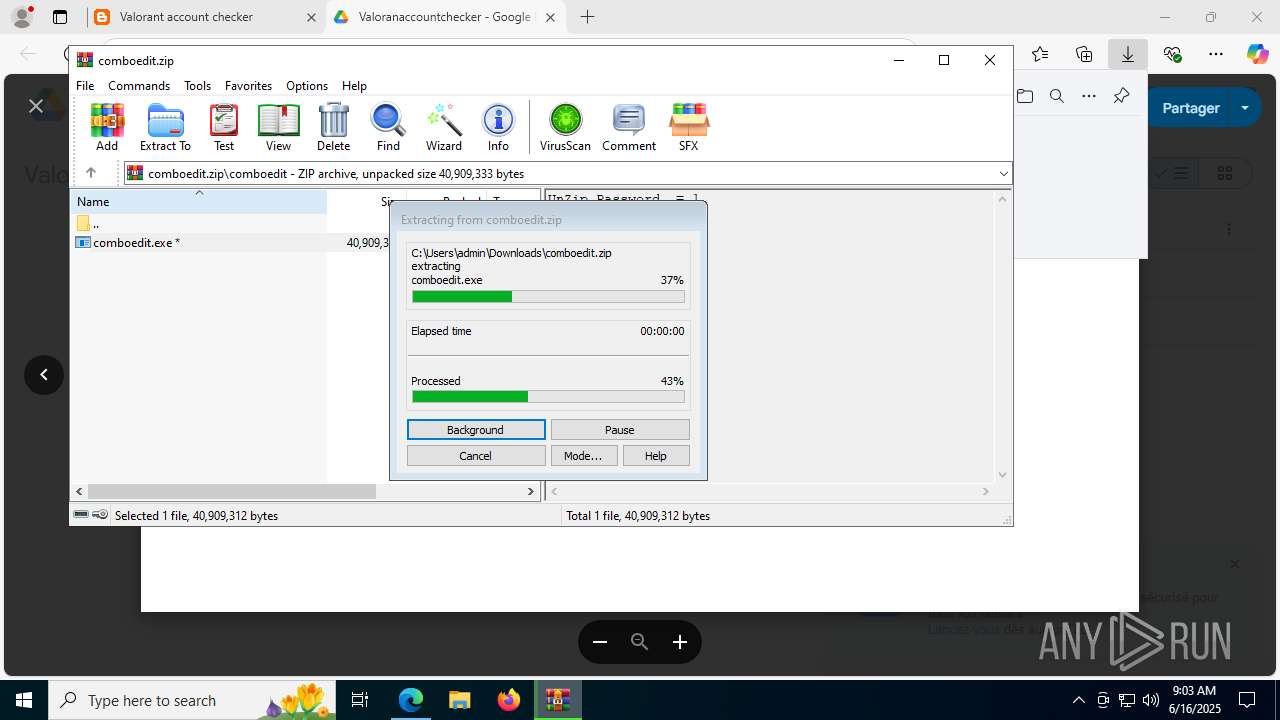
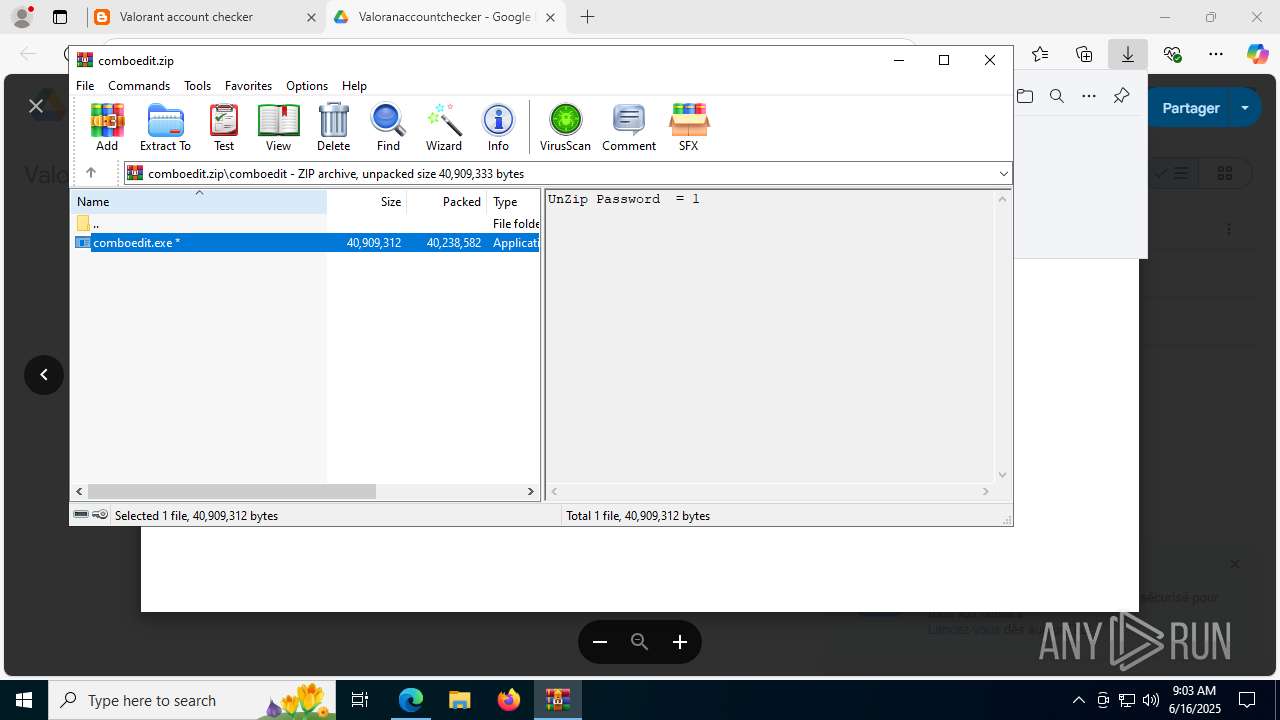
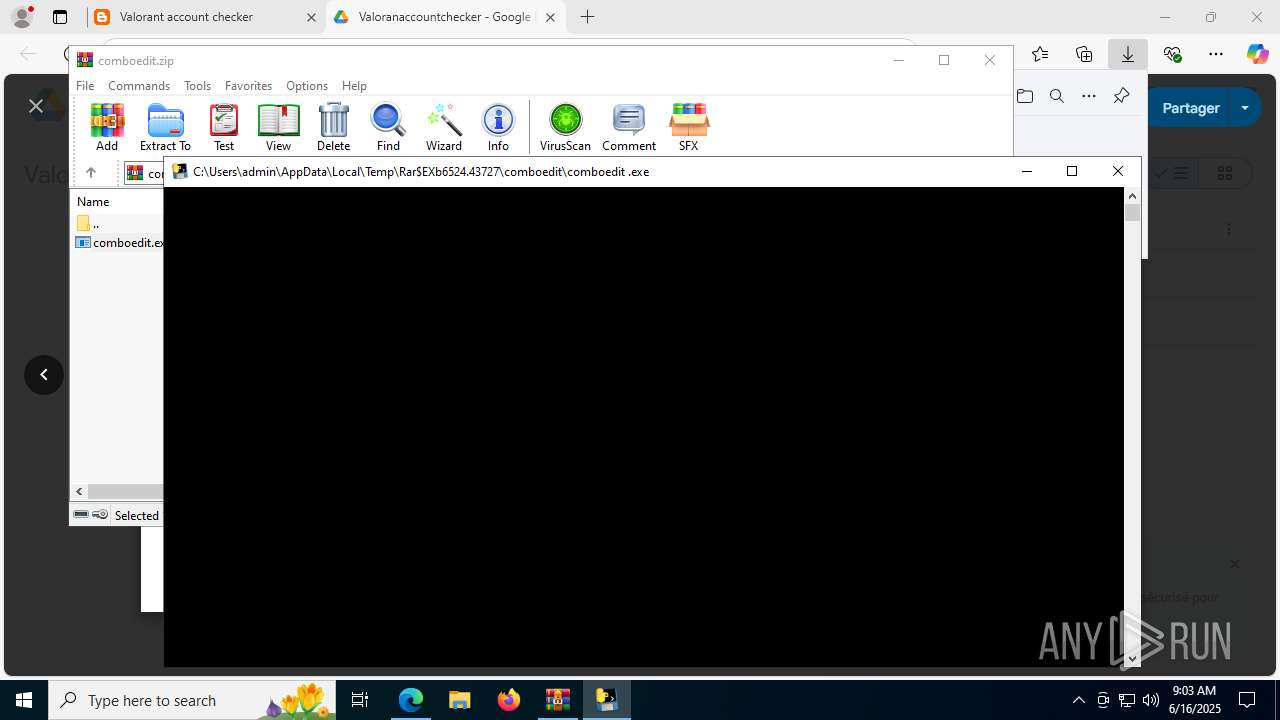
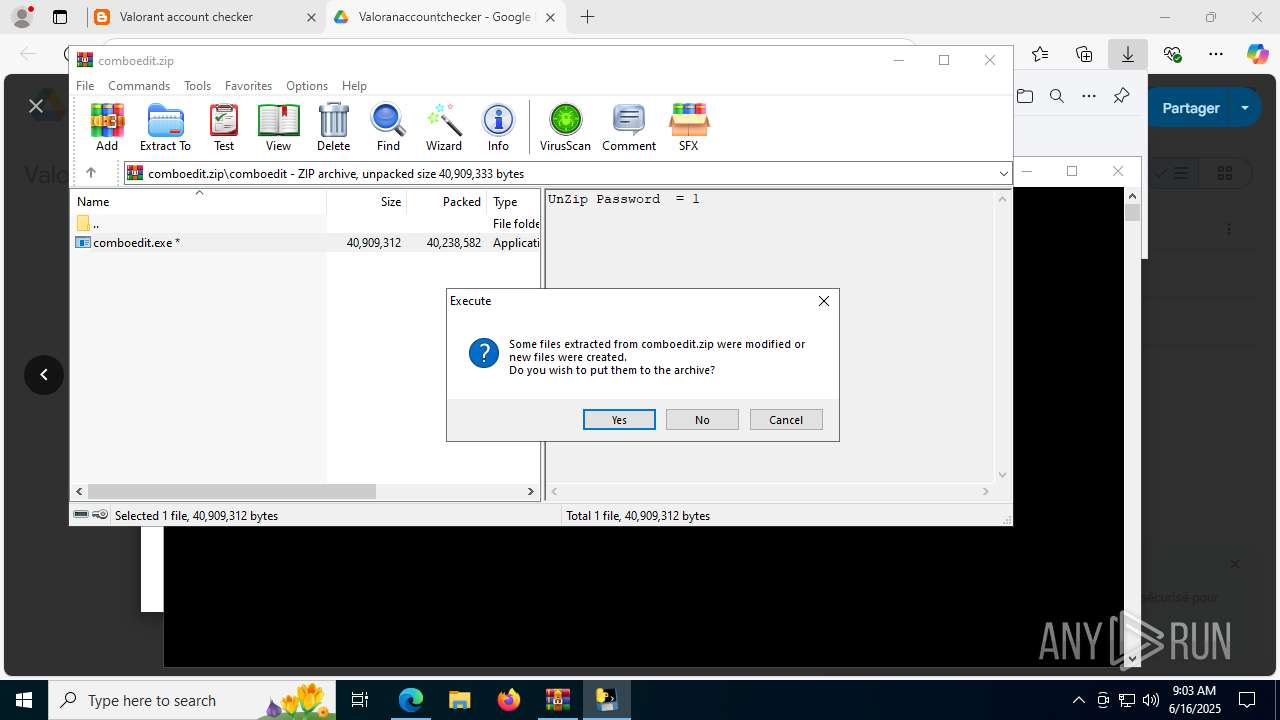
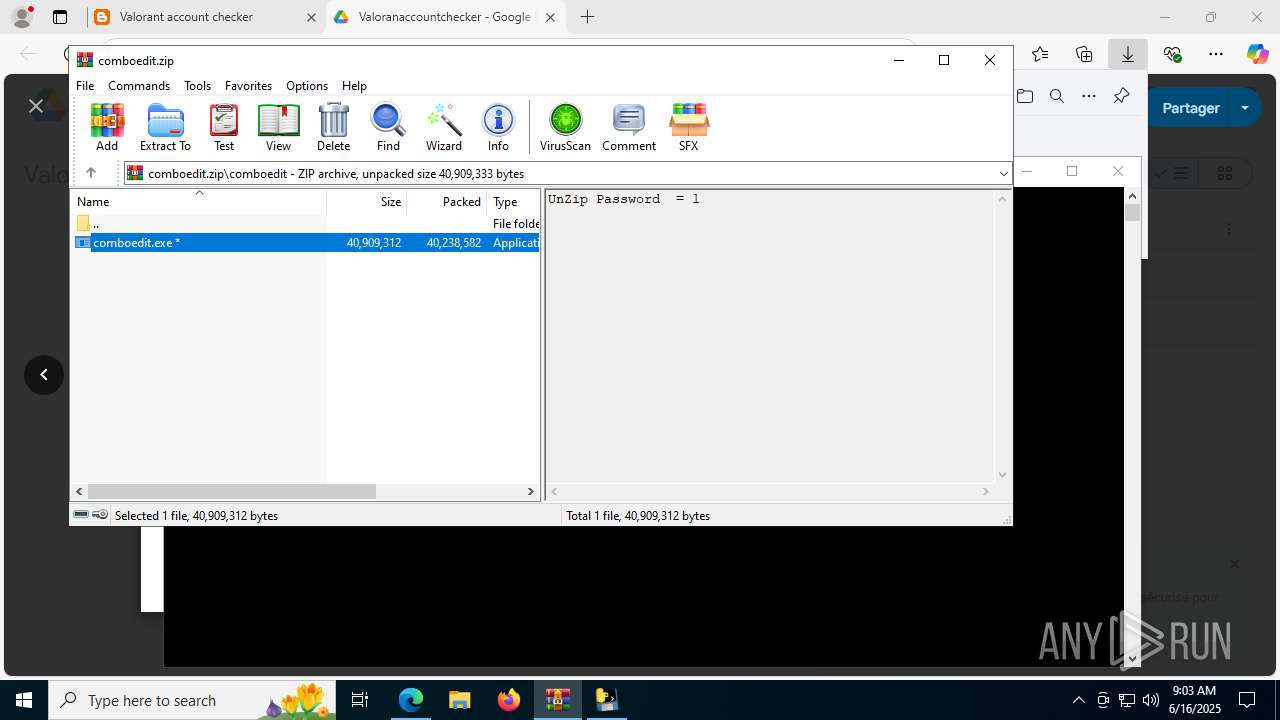
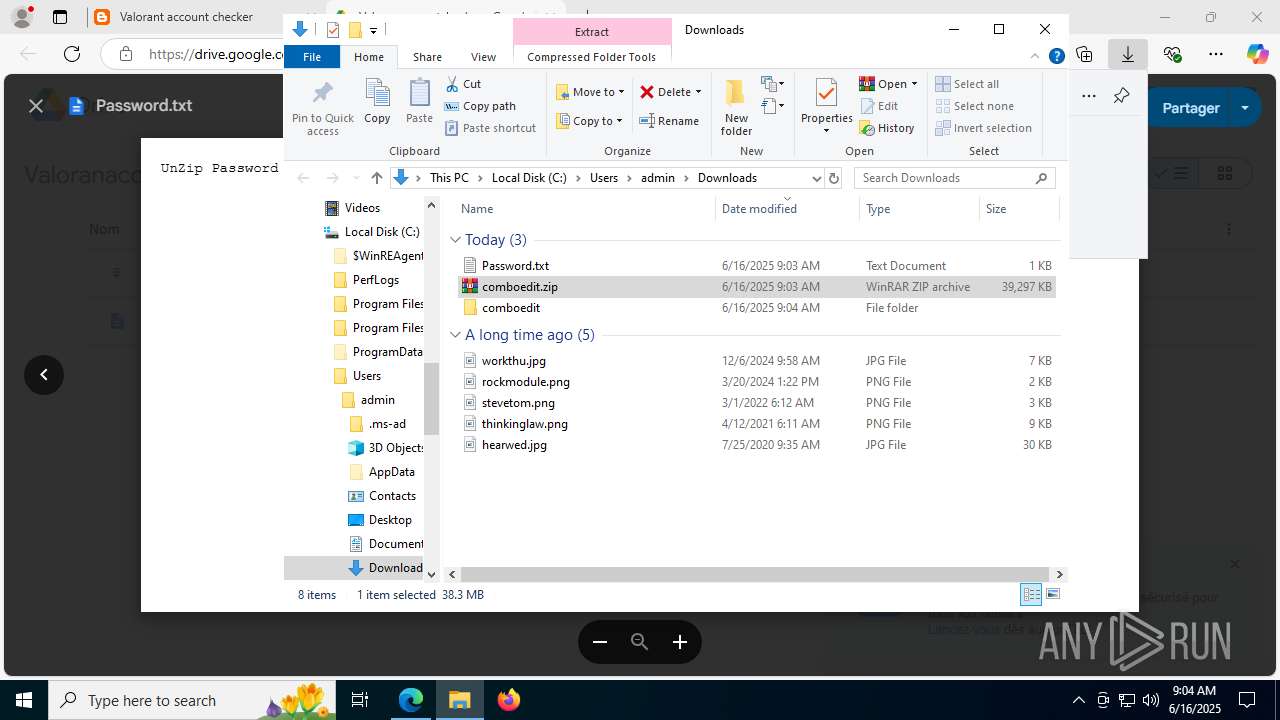
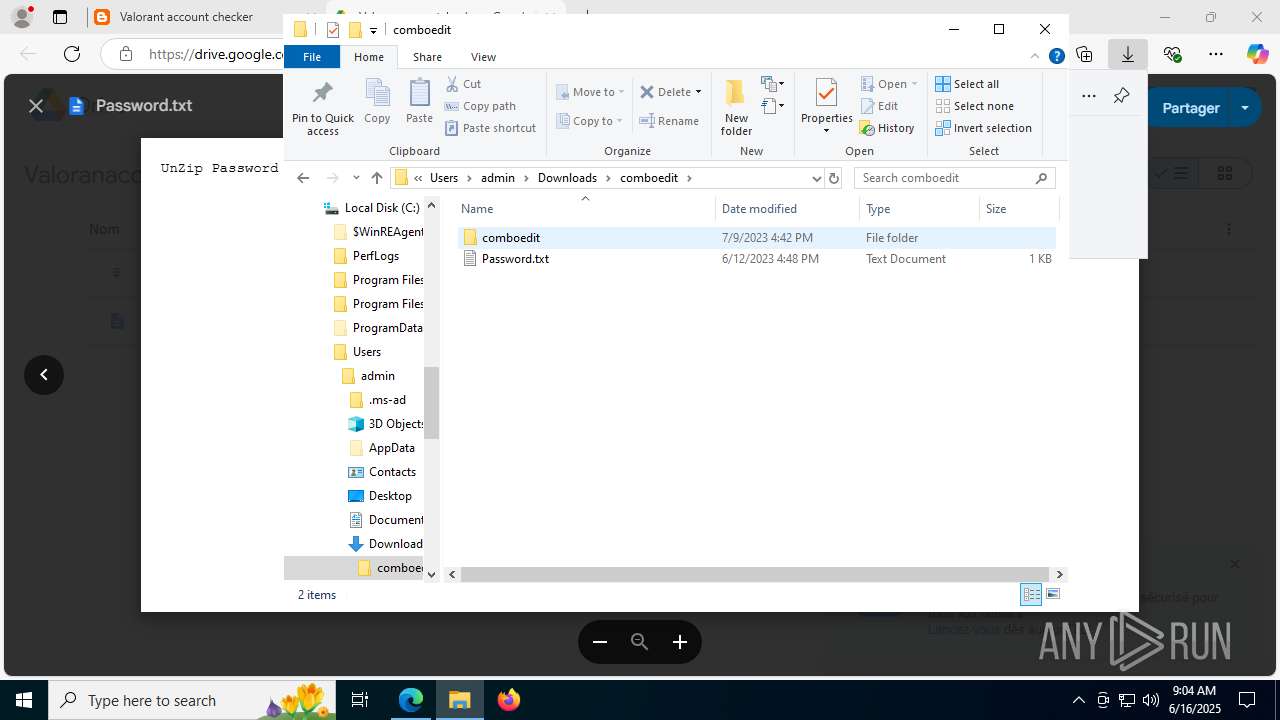
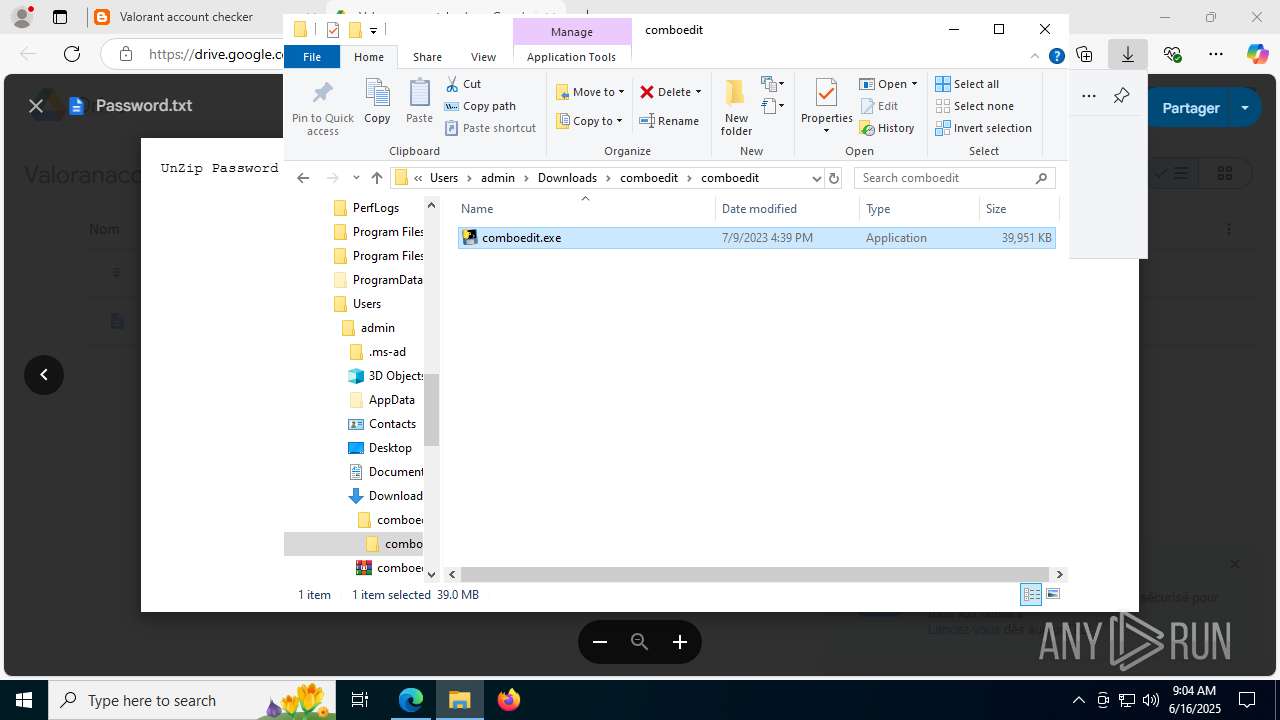
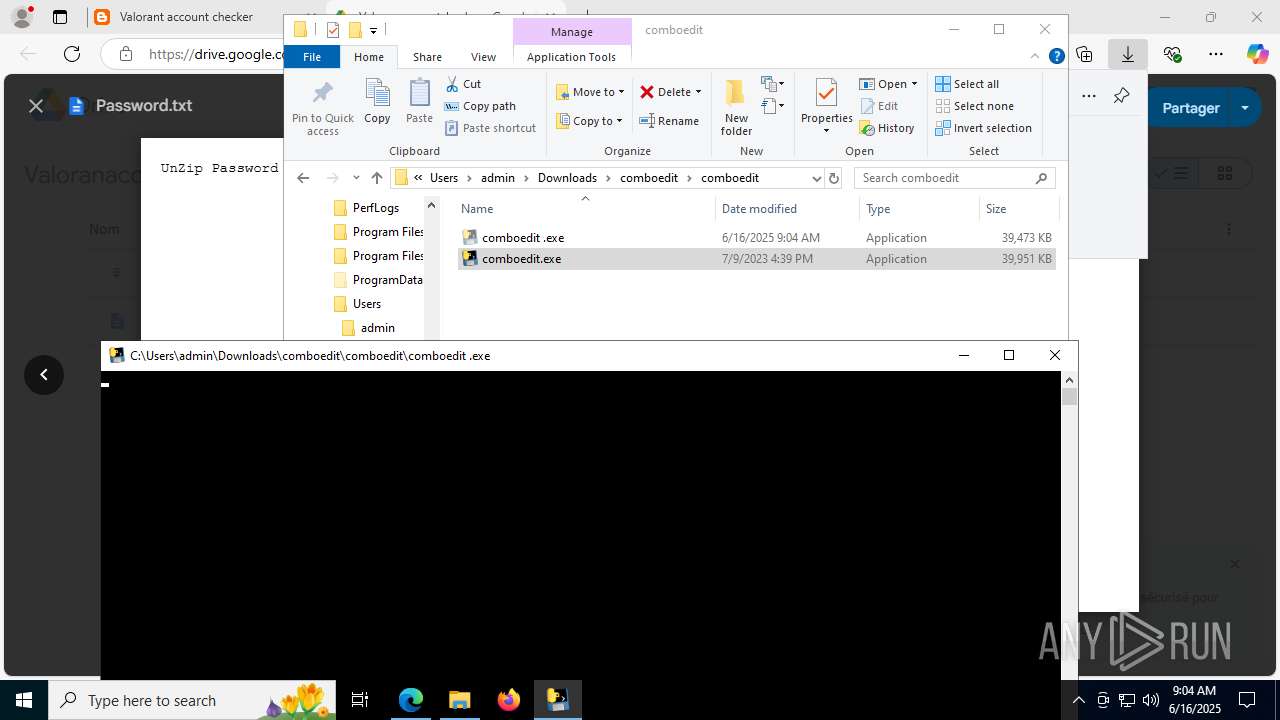
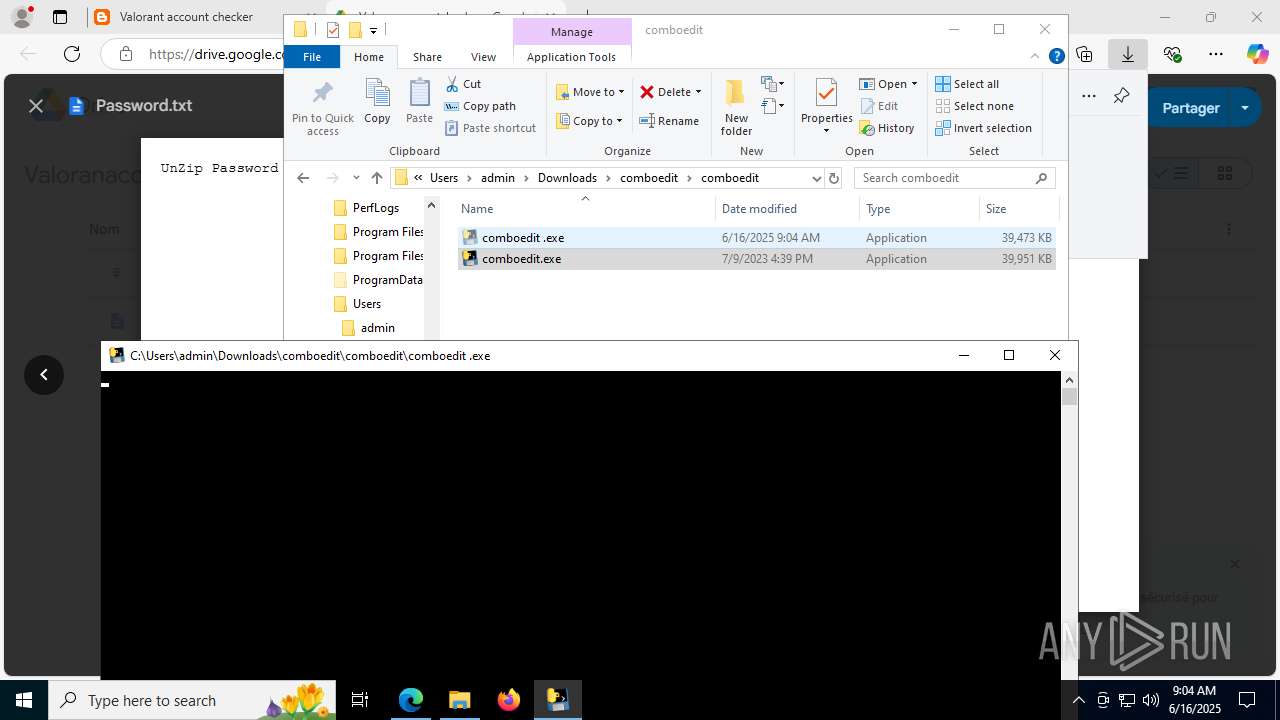
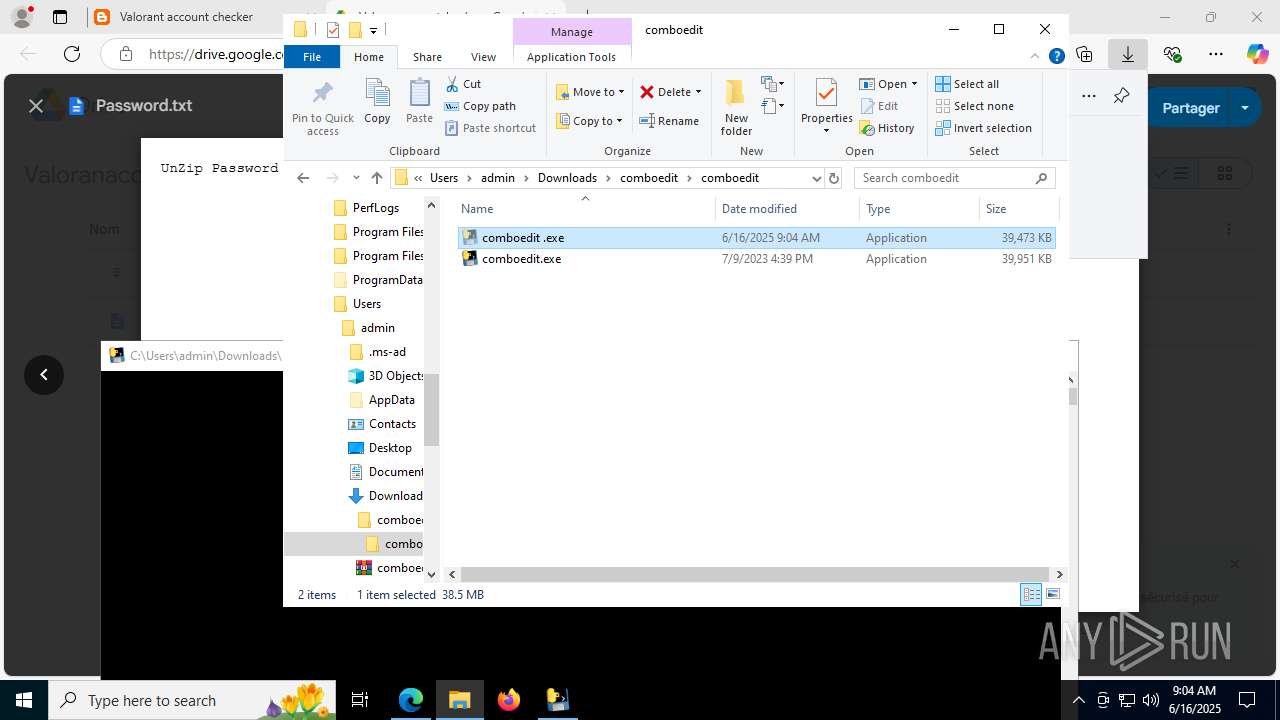
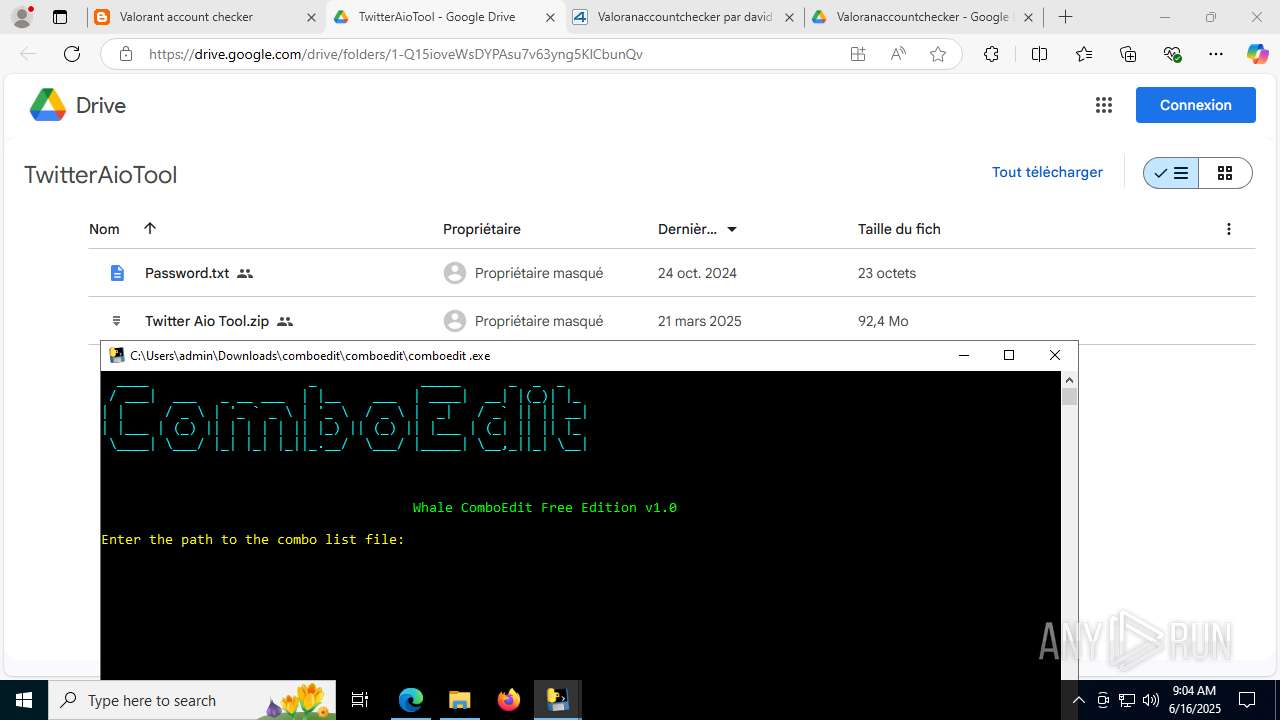
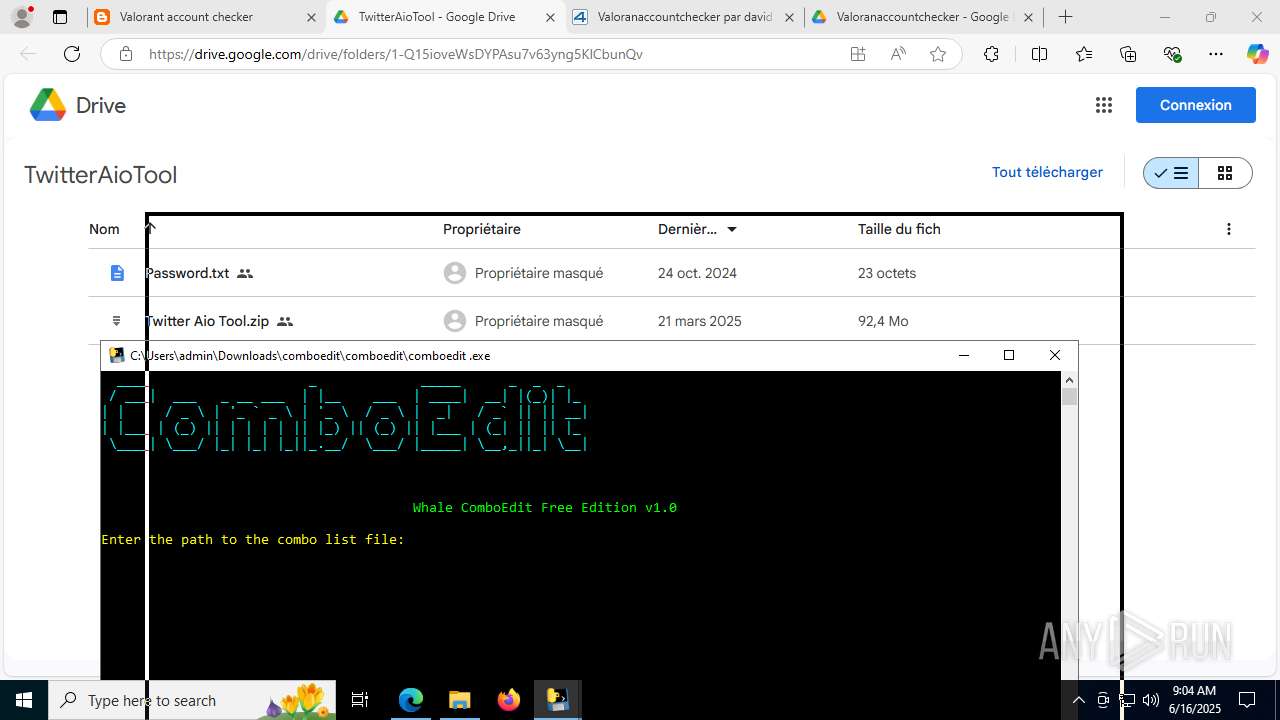
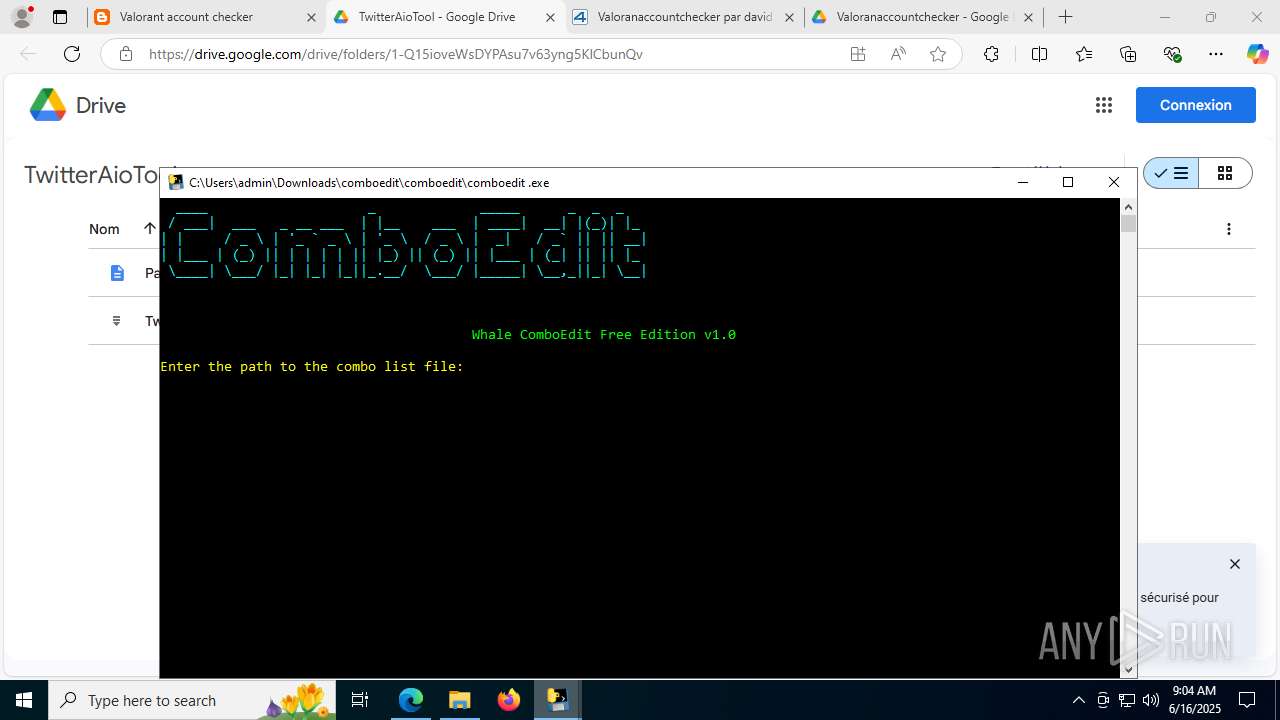
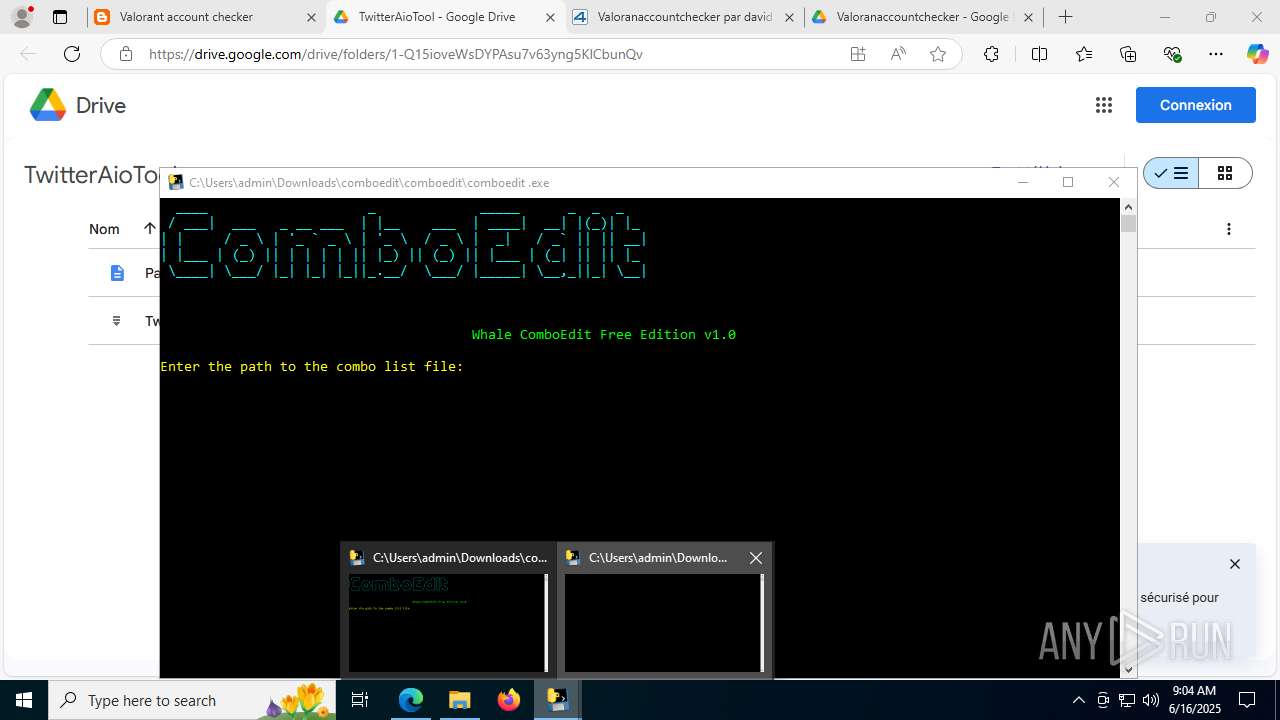
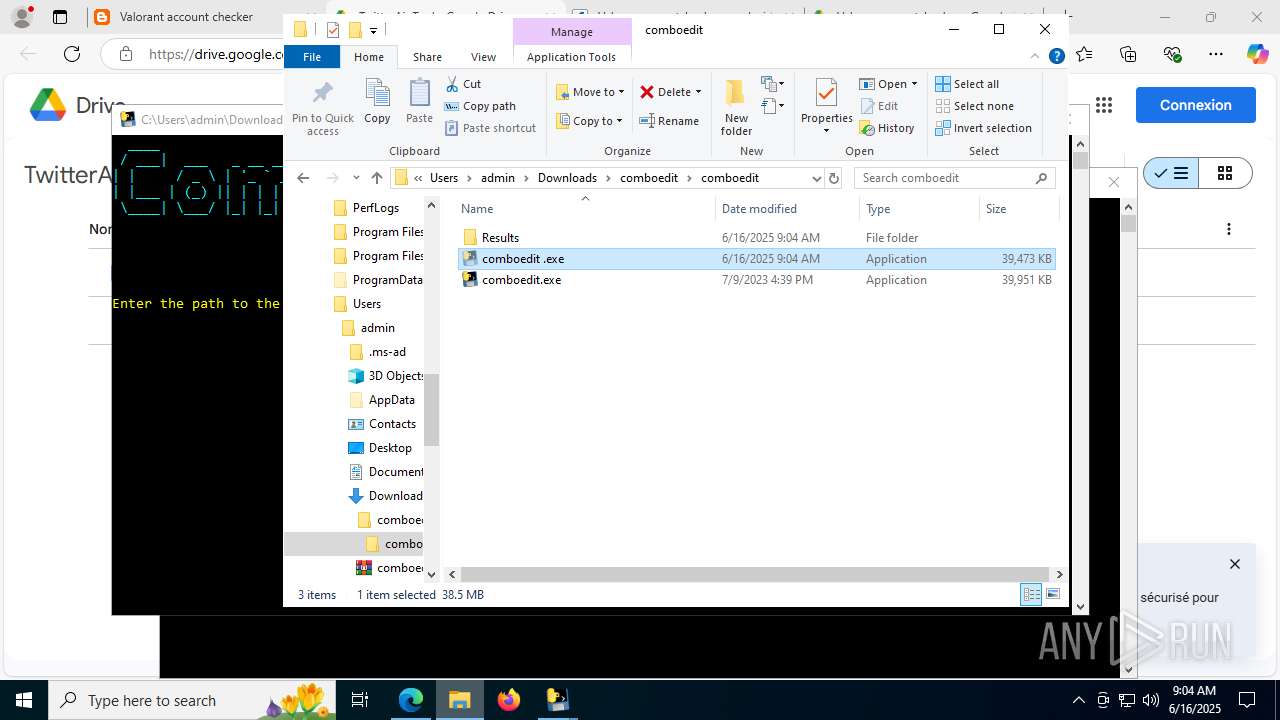
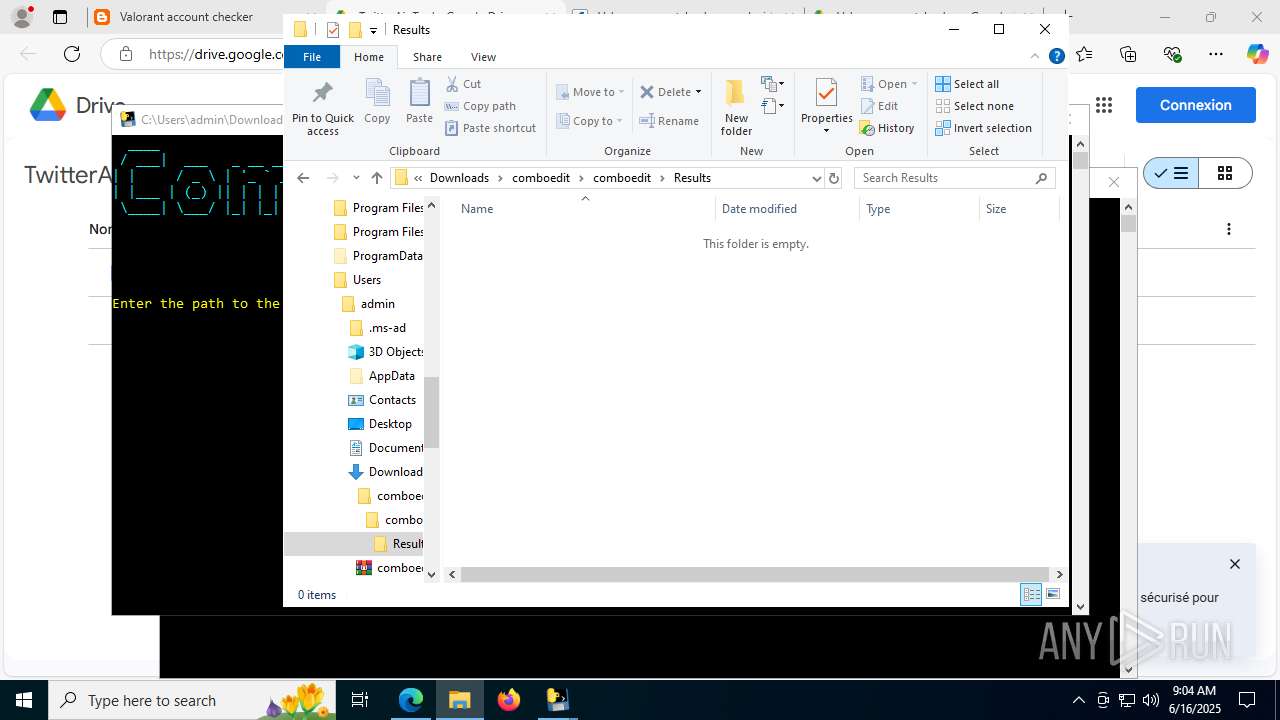
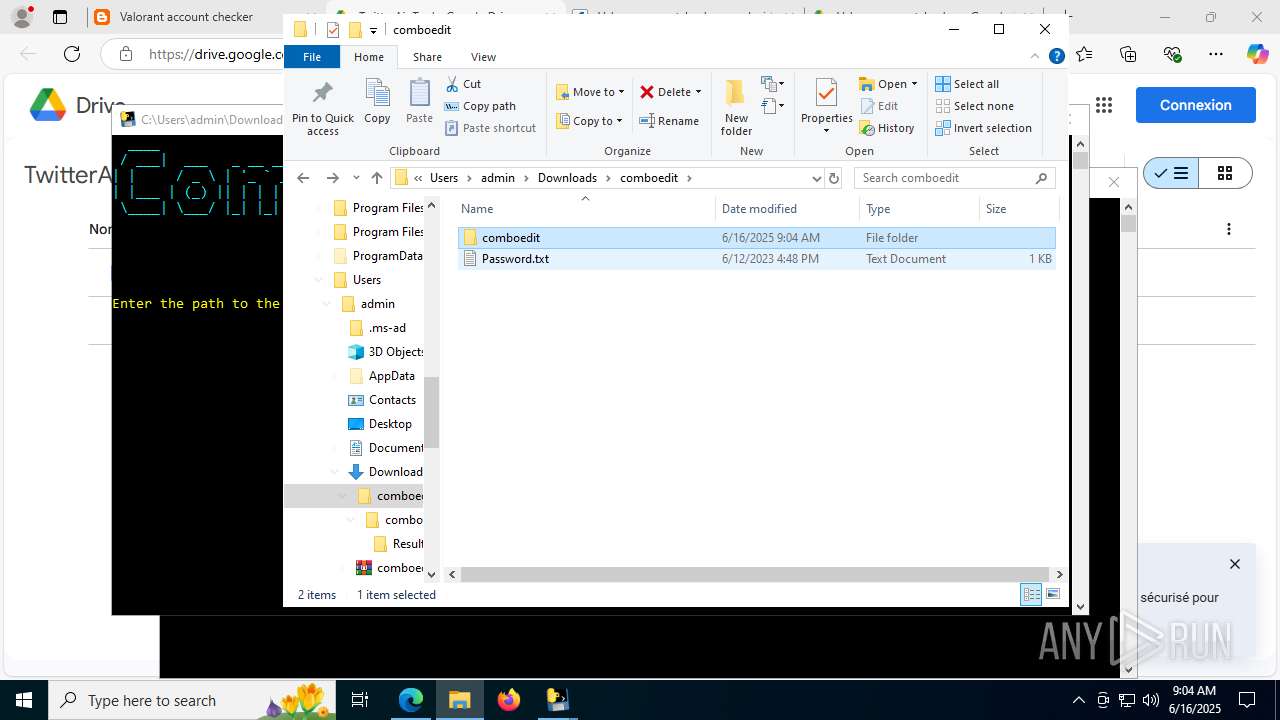
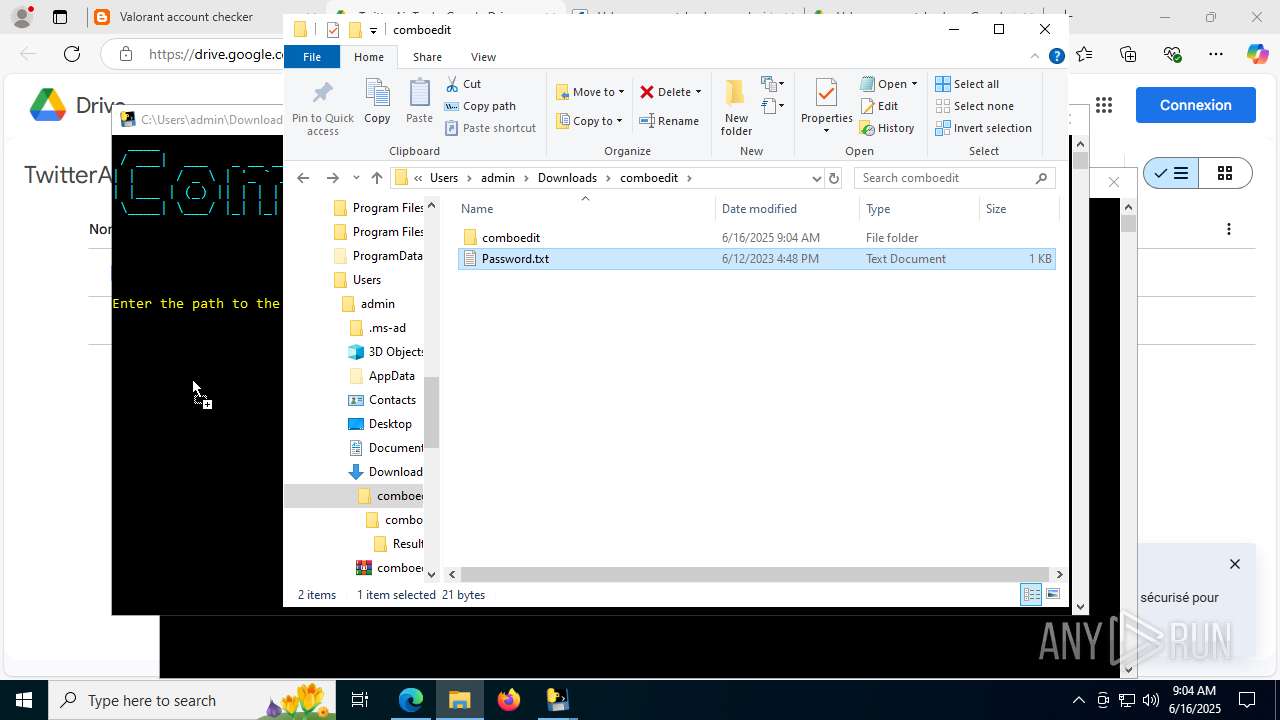
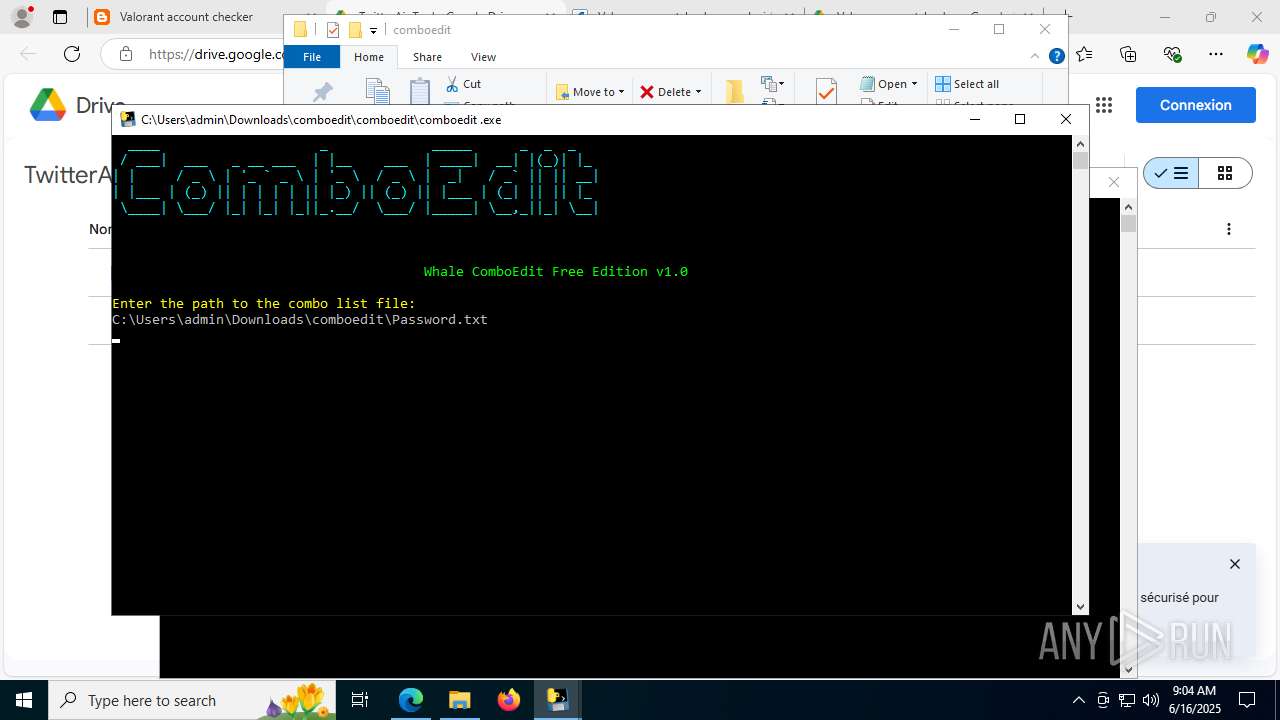
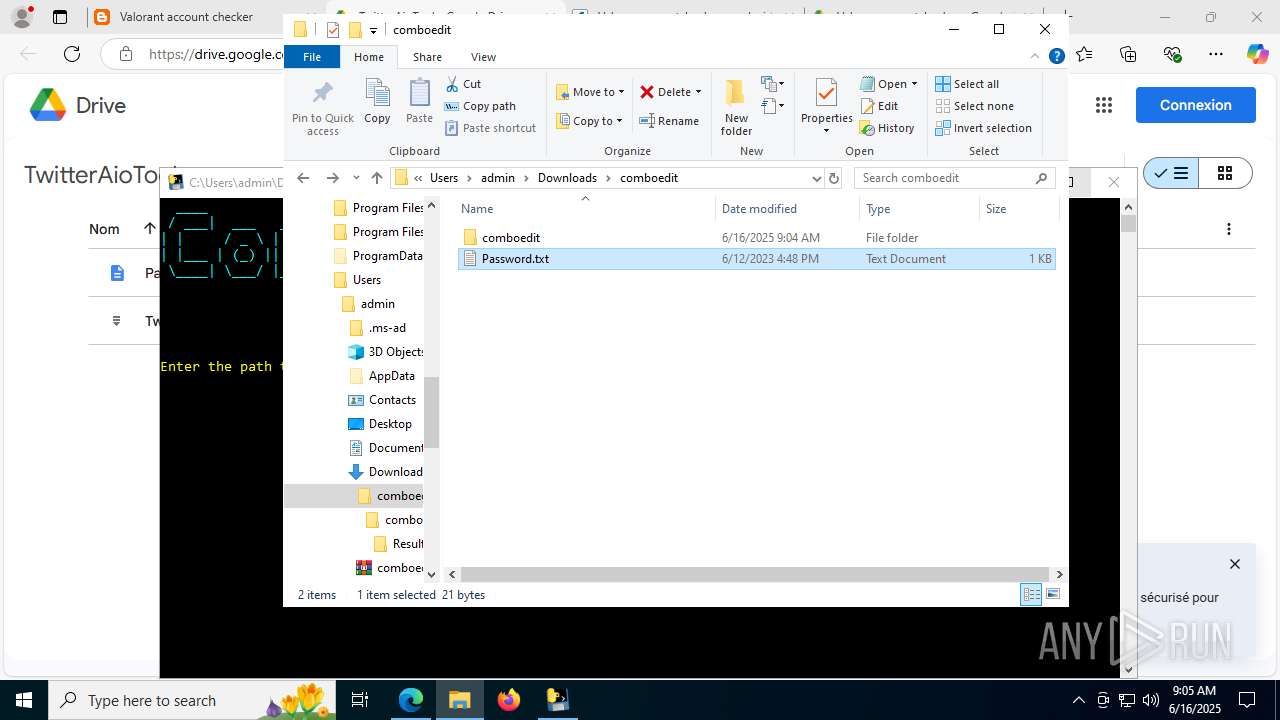
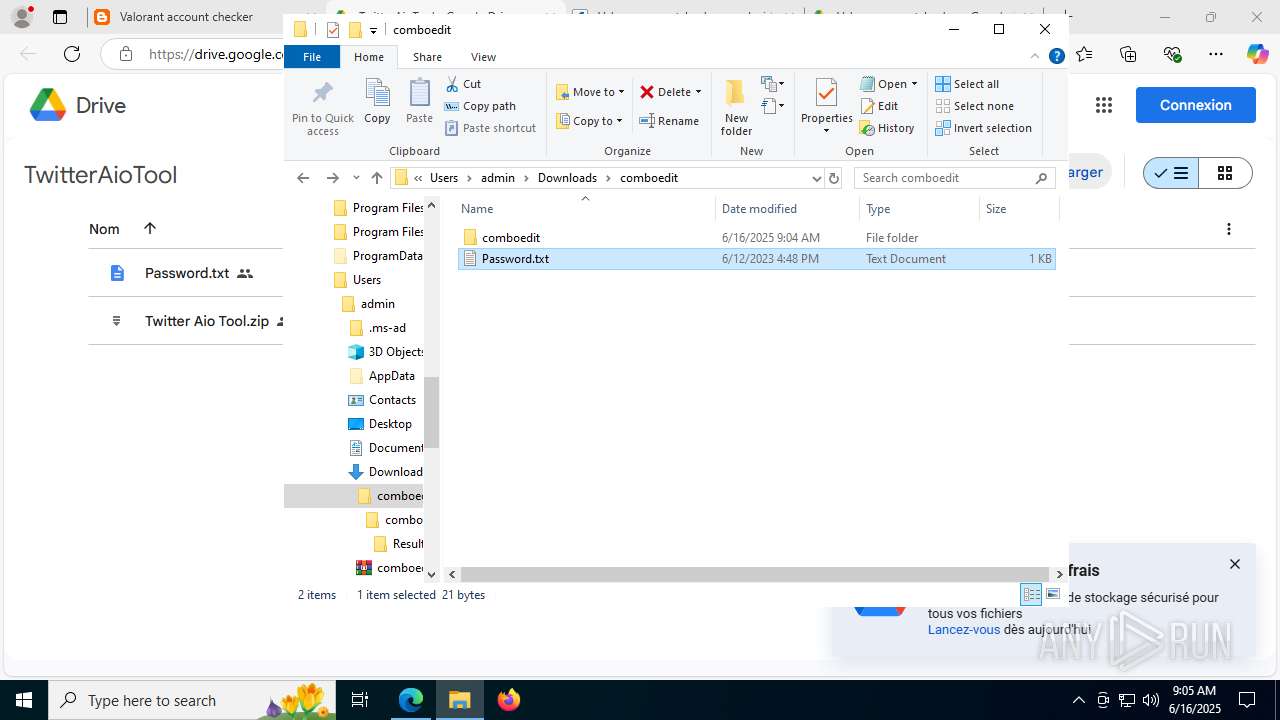
Process drops legitimate windows executable
- comboedit.exe (PID: 7376)
- Setup.exe (PID: 4088)
- comboedit .exe (PID: 2952)
- svchost.exe (PID: 8144)
- comboedit .exe (PID: 472)
- svchost.exe (PID: 7968)
- comboedit .exe (PID: 5968)
- explorer.exe (PID: 1812)
- WinRAR.exe (PID: 7072)
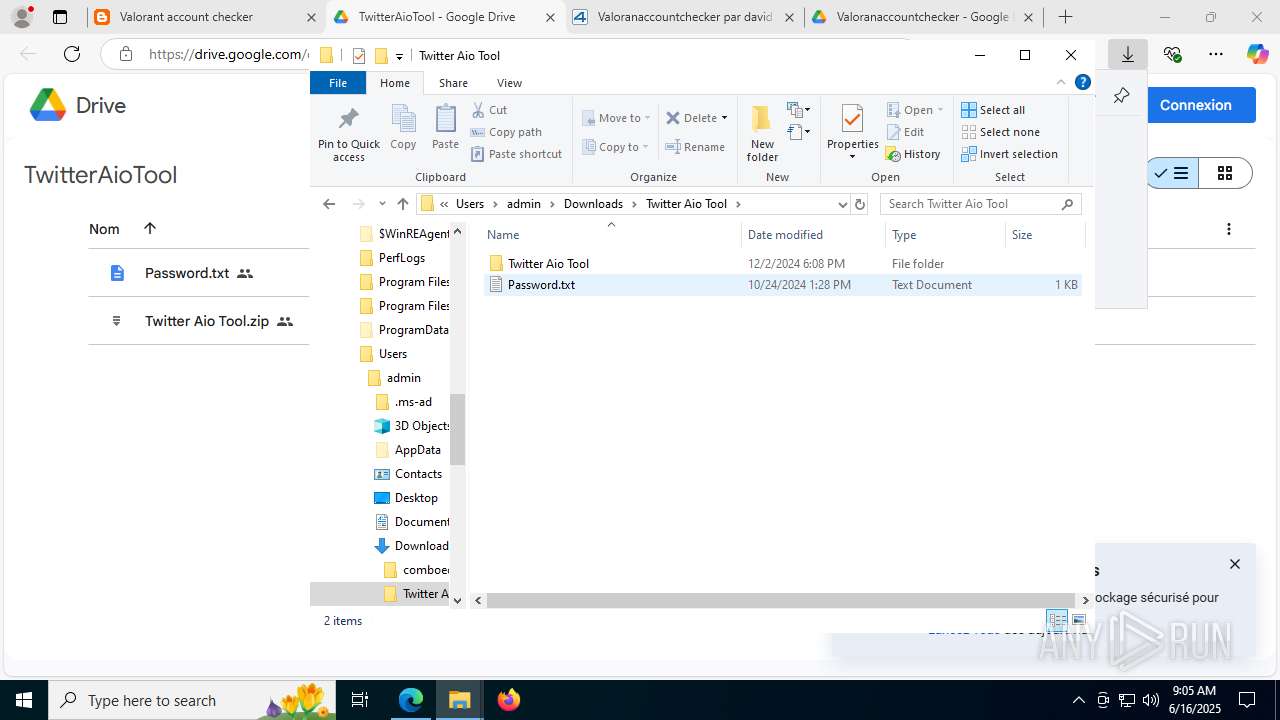
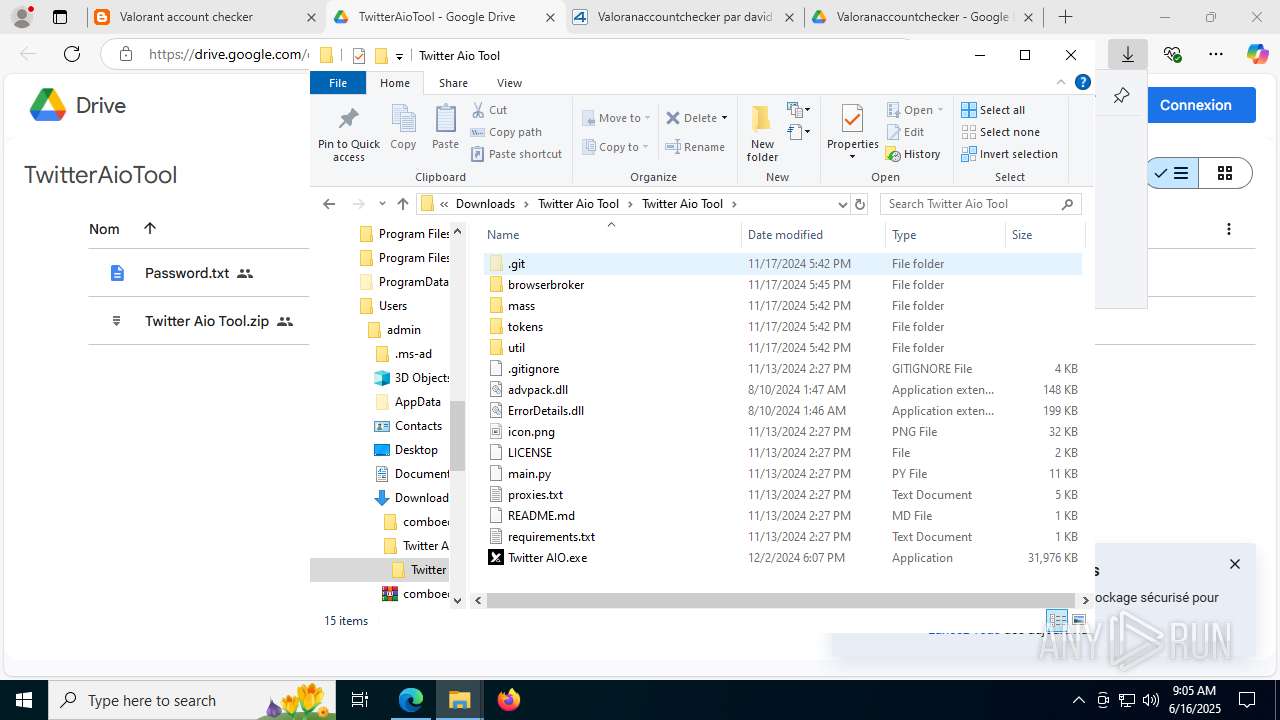
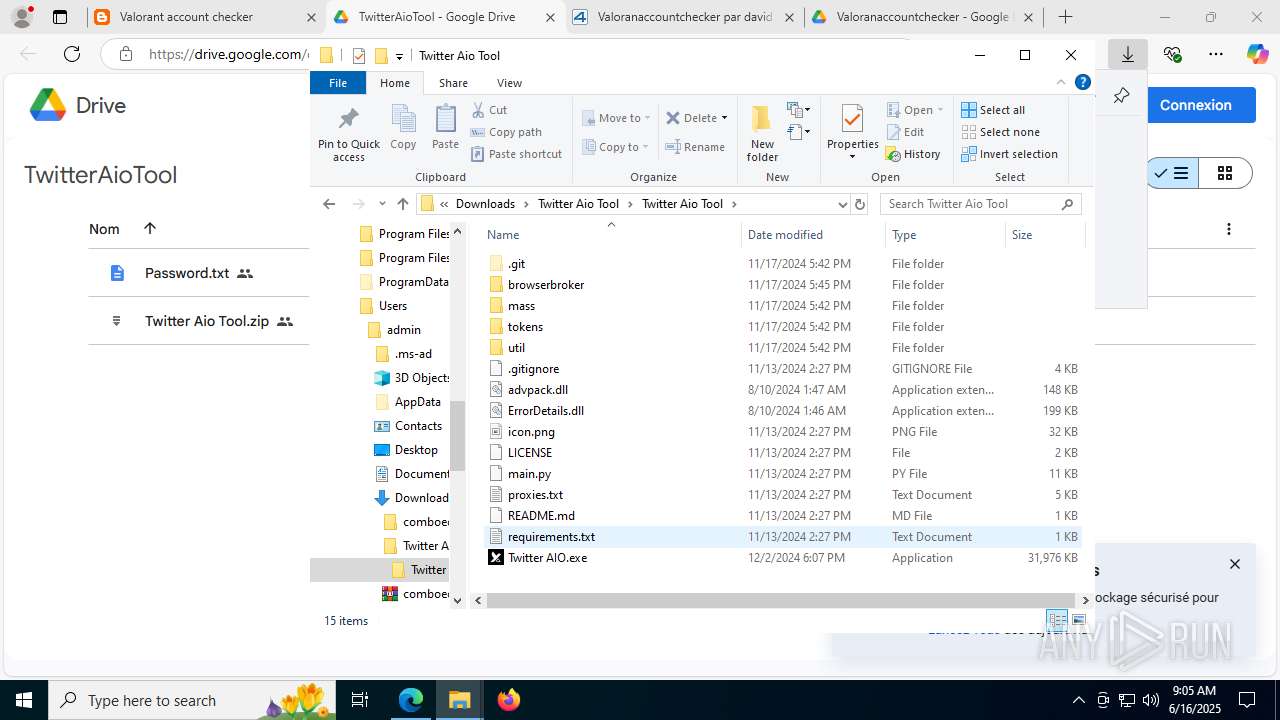
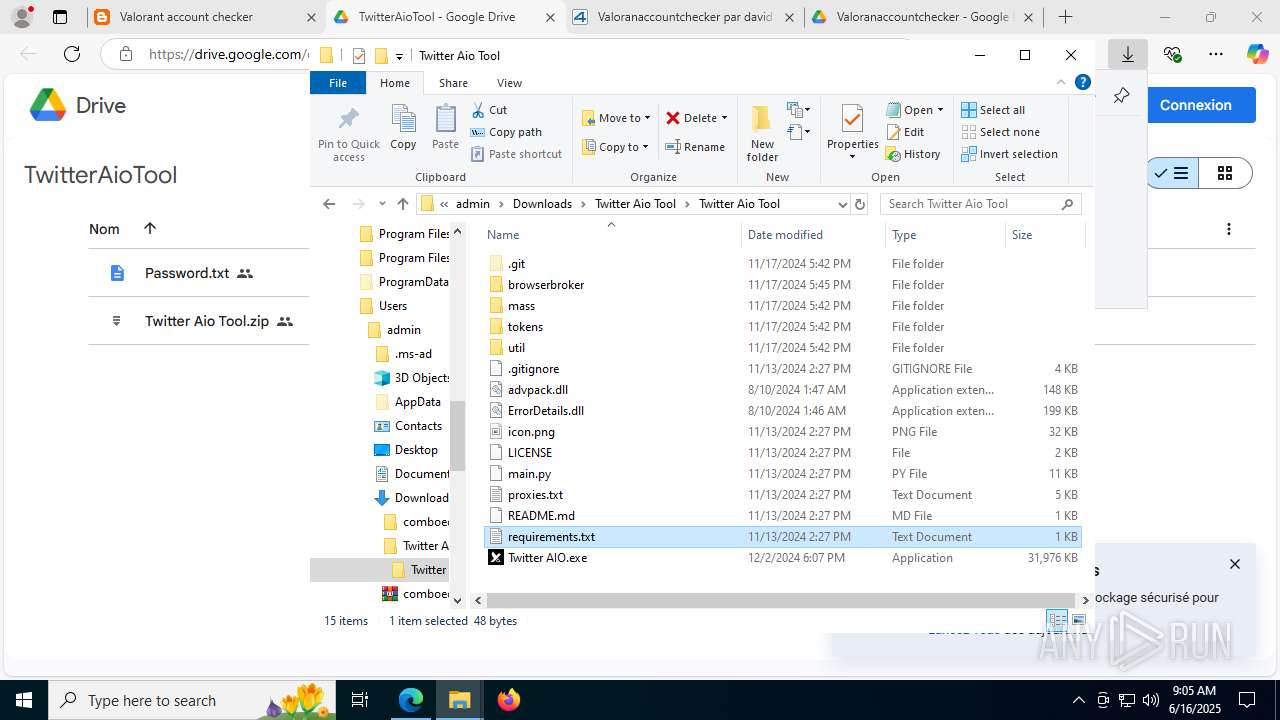
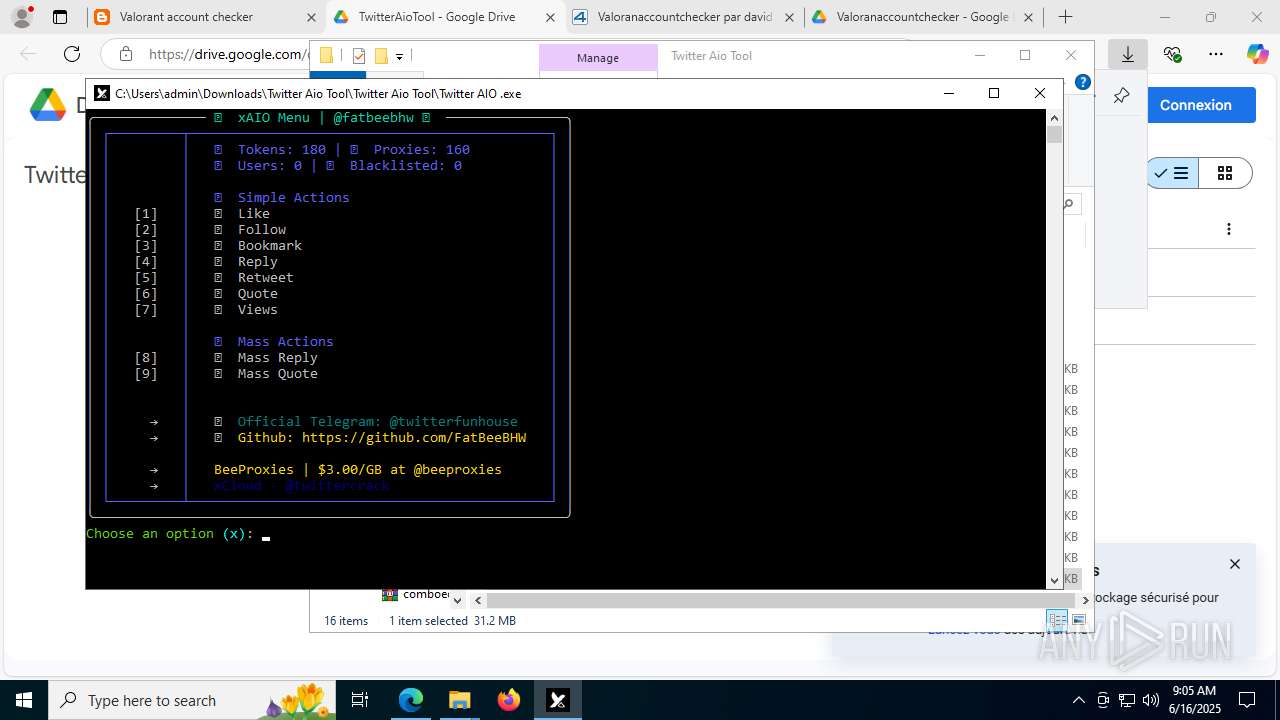
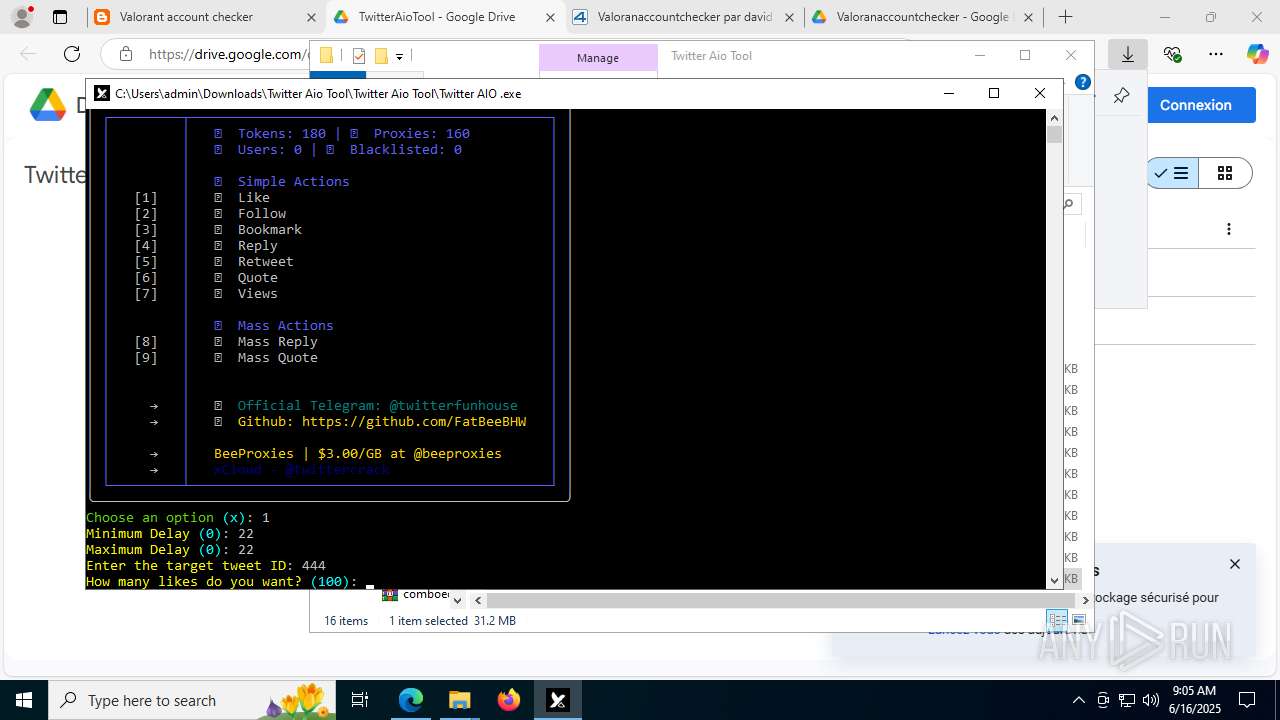
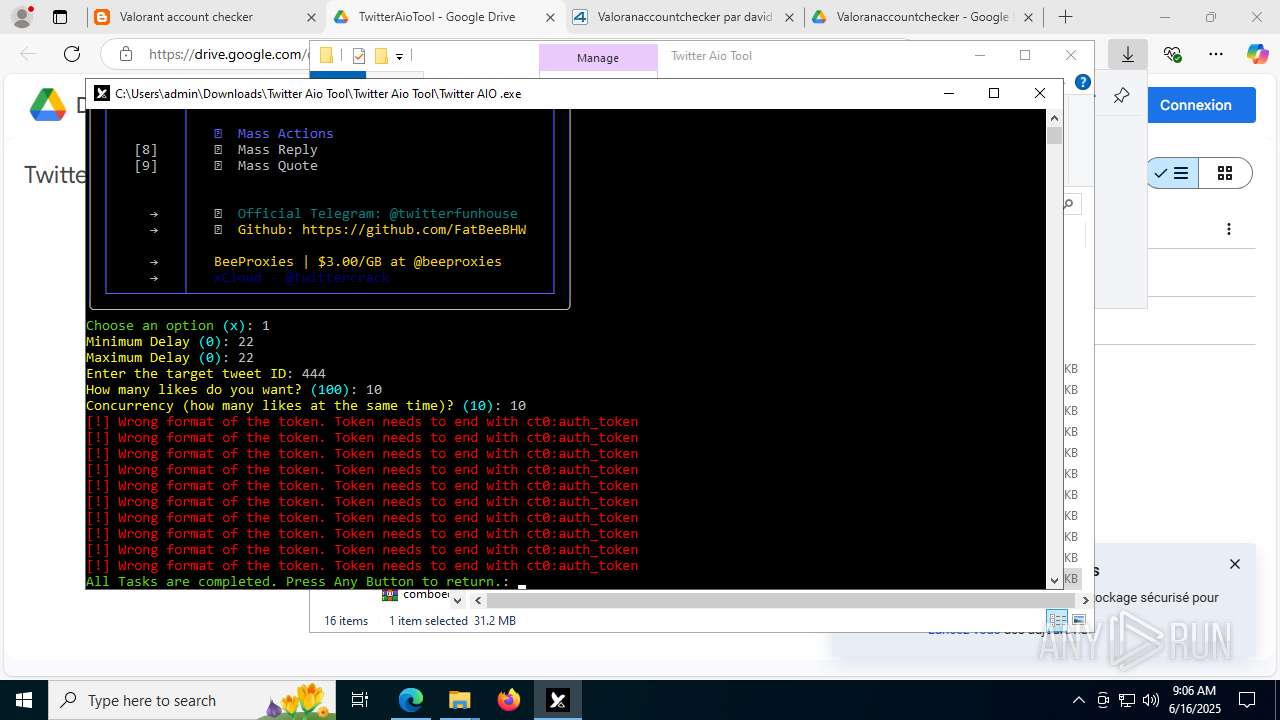
- Twitter AIO .exe (PID: 8388)
Reads security settings of Internet Explorer
- comboedit.exe (PID: 7376)
- WinRAR.exe (PID: 6524)
- Setup.exe (PID: 4088)
- Setup.exe (PID: 7920)
Reads the date of Windows installation
- comboedit.exe (PID: 7376)
- Setup.exe (PID: 4088)
- Setup.exe (PID: 7920)
Executable content was dropped or overwritten
- comboedit.exe (PID: 7376)
- Setup.exe (PID: 4088)
- comboedit .exe (PID: 2952)
- svchost.exe (PID: 8144)
- svchost.exe (PID: 7968)
- comboedit .exe (PID: 5968)
- comboedit .exe (PID: 472)
- explorer.exe (PID: 1812)
- Twitter AIO.exe (PID: 9088)
- Twitter AIO .exe (PID: 8388)
Starts a Microsoft application from unusual location
- Setup.exe (PID: 4088)
- Setup.exe (PID: 7920)
- Setup.exe (PID: 7904)
- Setup.exe (PID: 8640)
The process creates files with name similar to system file names
- Setup.exe (PID: 4088)
- svchost.exe (PID: 8144)
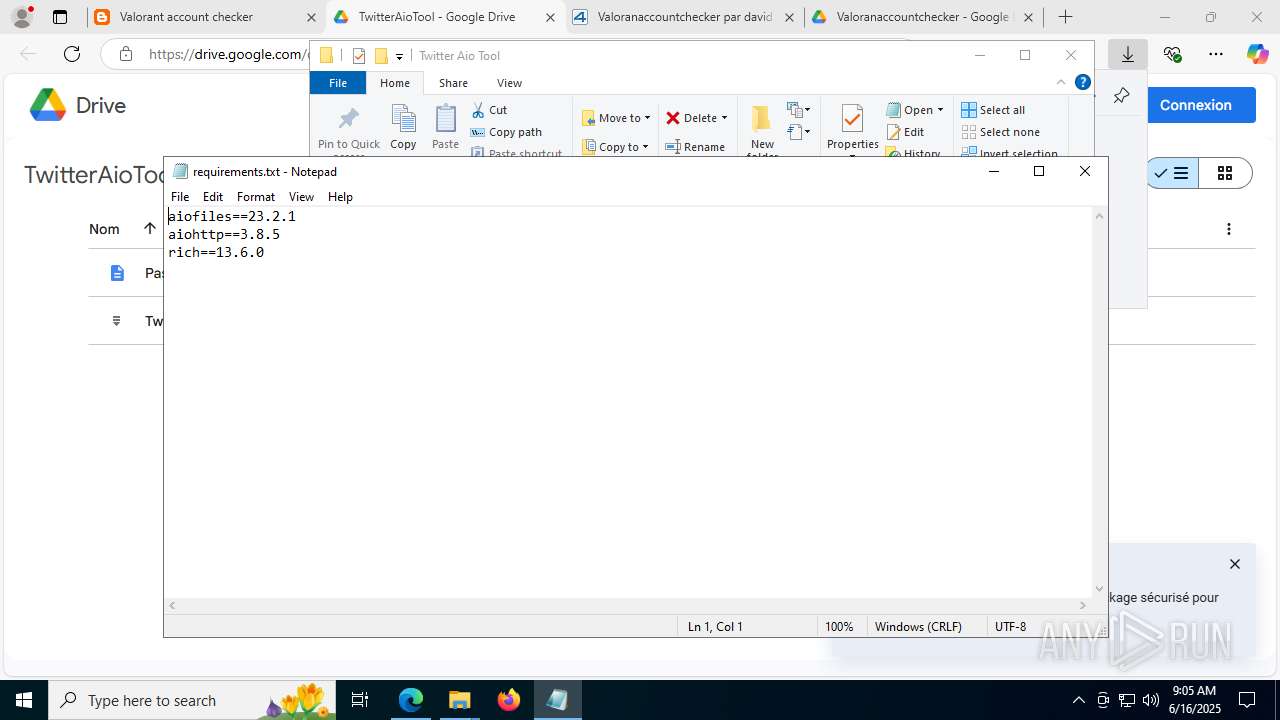
Process drops python dynamic module
- comboedit .exe (PID: 2952)
- comboedit .exe (PID: 472)
- comboedit .exe (PID: 5968)
- Twitter AIO .exe (PID: 8388)
The process drops C-runtime libraries
- comboedit .exe (PID: 2952)
- comboedit .exe (PID: 472)
- comboedit .exe (PID: 5968)
- Twitter AIO .exe (PID: 8388)
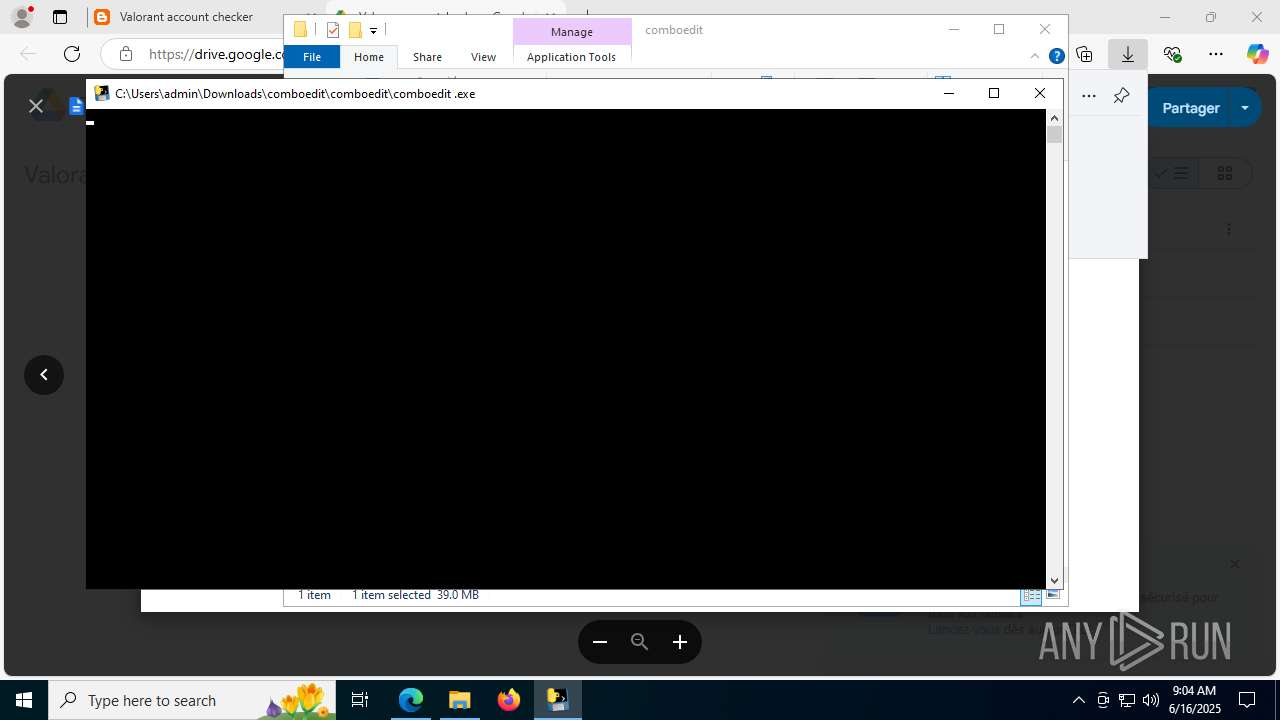
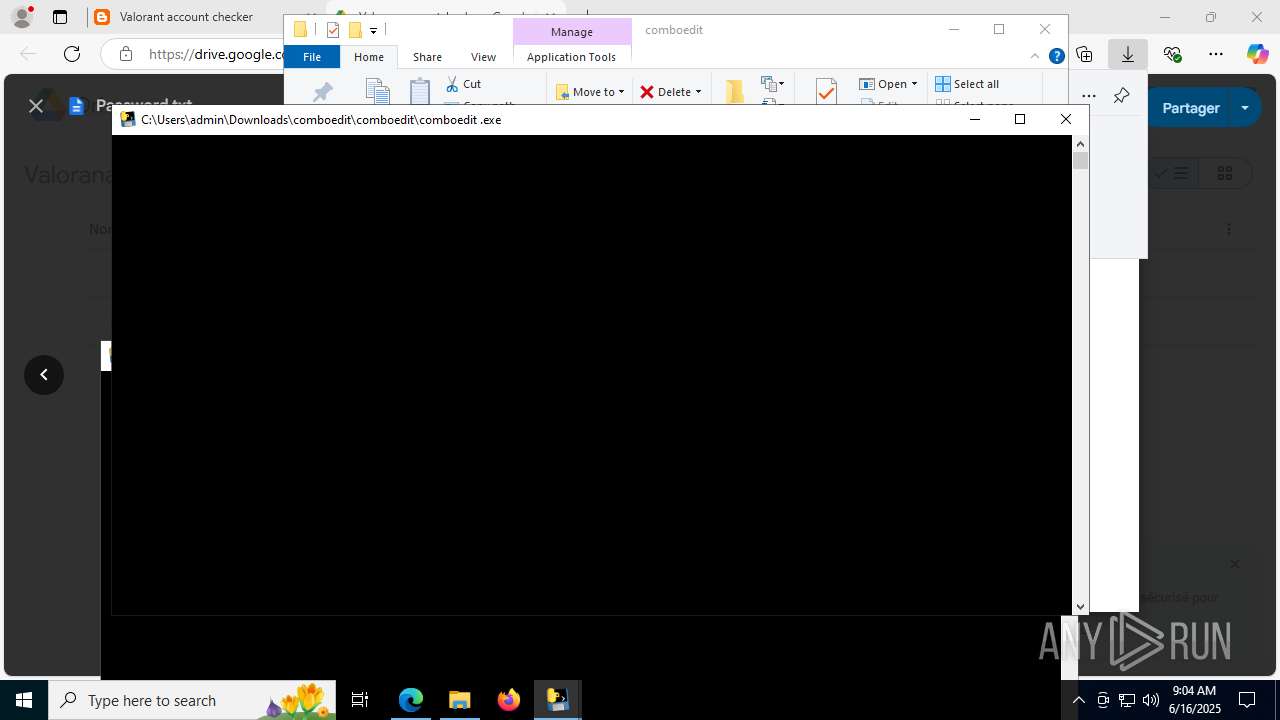
Starts CMD.EXE for commands execution
- comboedit .exe (PID: 7308)
- version.exe (PID: 8148)
- comboedit .exe (PID: 8980)
- Twitter AIO .exe (PID: 8516)
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- explorer.exe (PID: 1812)
Application launched itself
- comboedit .exe (PID: 472)
- comboedit .exe (PID: 5968)
- Twitter AIO .exe (PID: 8388)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7904)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 7052)
- cmd.exe (PID: 1508)
- cmd.exe (PID: 5504)
- cmd.exe (PID: 4836)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 4444)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7904)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 7052)
- cmd.exe (PID: 1508)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 5504)
- cmd.exe (PID: 4444)
- cmd.exe (PID: 4836)
Uses TASKKILL.EXE to kill process
- dllhost.exe (PID: 5612)
Starts itself from another location
- explorer.exe (PID: 1812)
Uses NETSH.EXE to add a firewall rule or allowed programs
- explorer.exe (PID: 9036)
Connects to unusual port
- explorer.exe (PID: 9036)
INFO
Checks supported languages
- identity_helper.exe (PID: 7820)
- Setup.exe (PID: 4088)
- Setup.exe (PID: 7920)
- comboedit.exe (PID: 7376)
- svchost.exe (PID: 8144)
- svchost.exe (PID: 7336)
- comboedit .exe (PID: 2952)
Application launched itself
- msedge.exe (PID: 504)
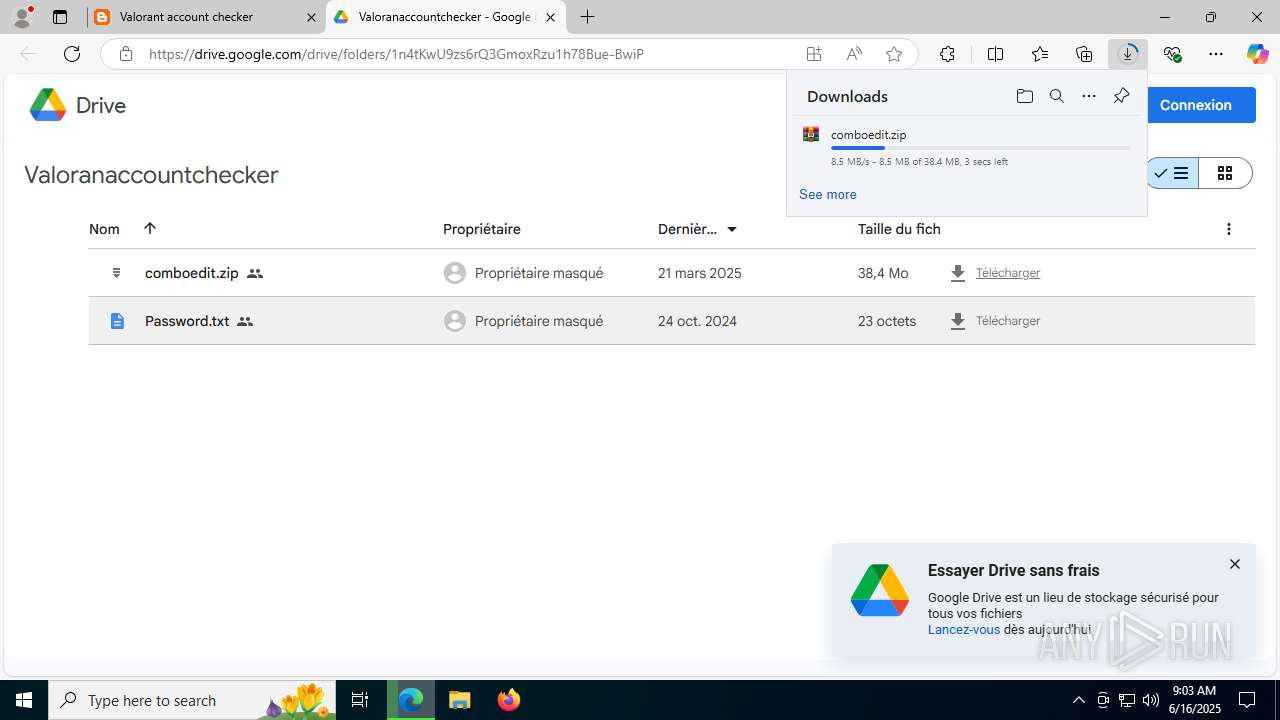
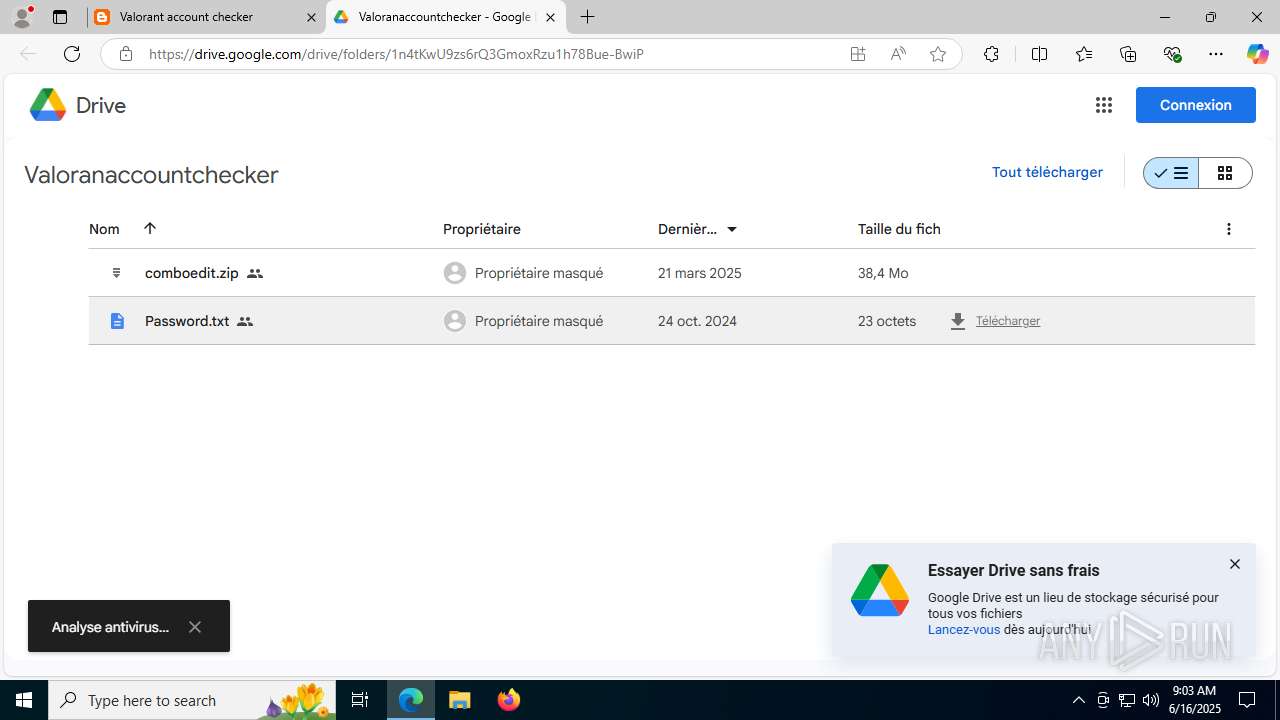
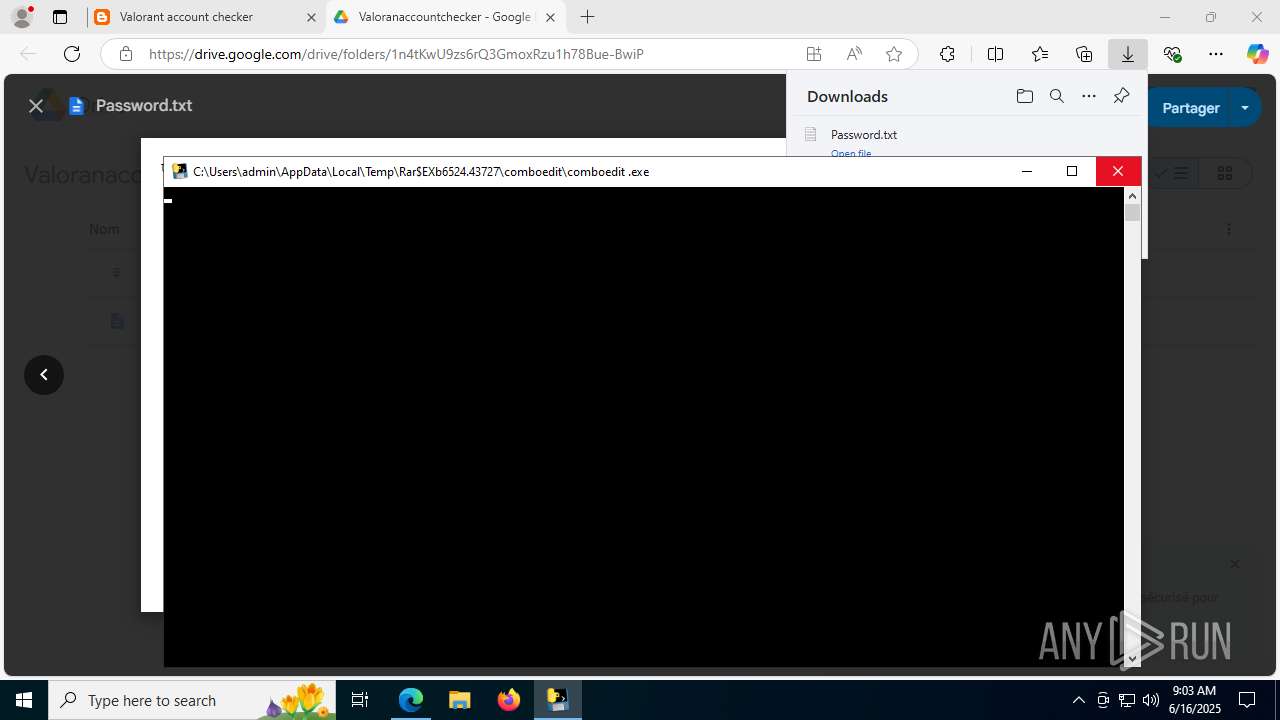
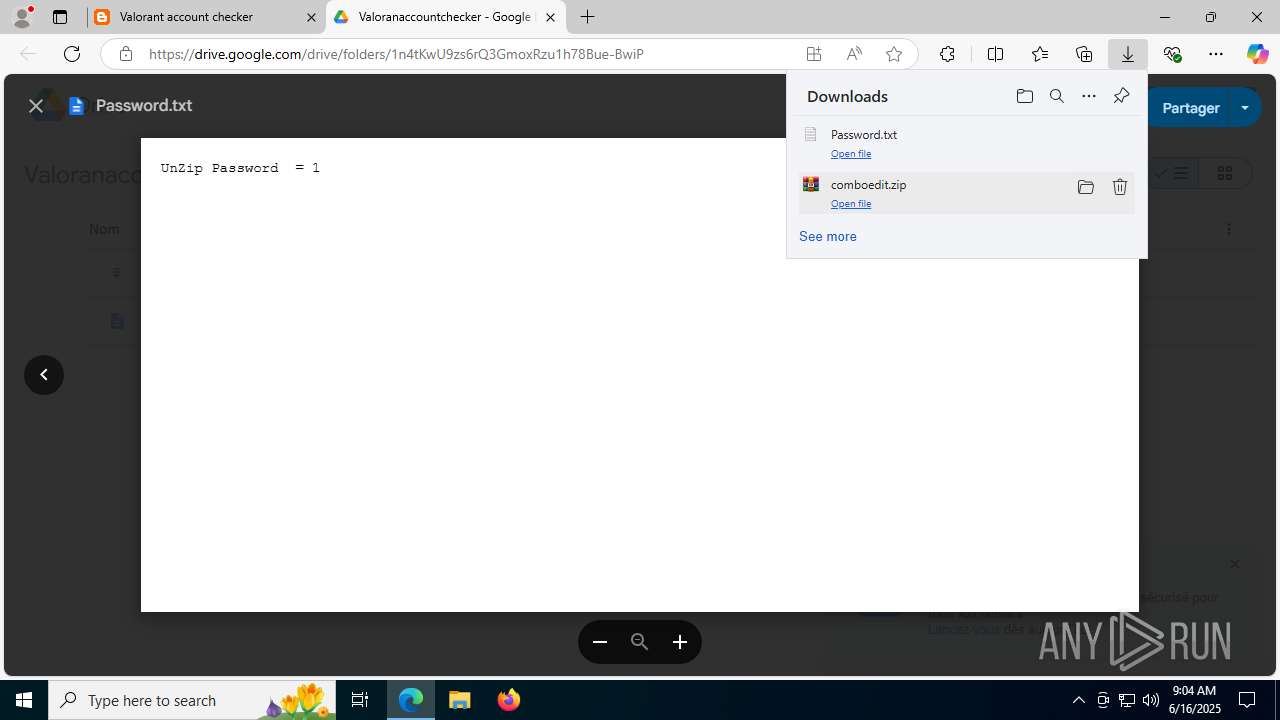
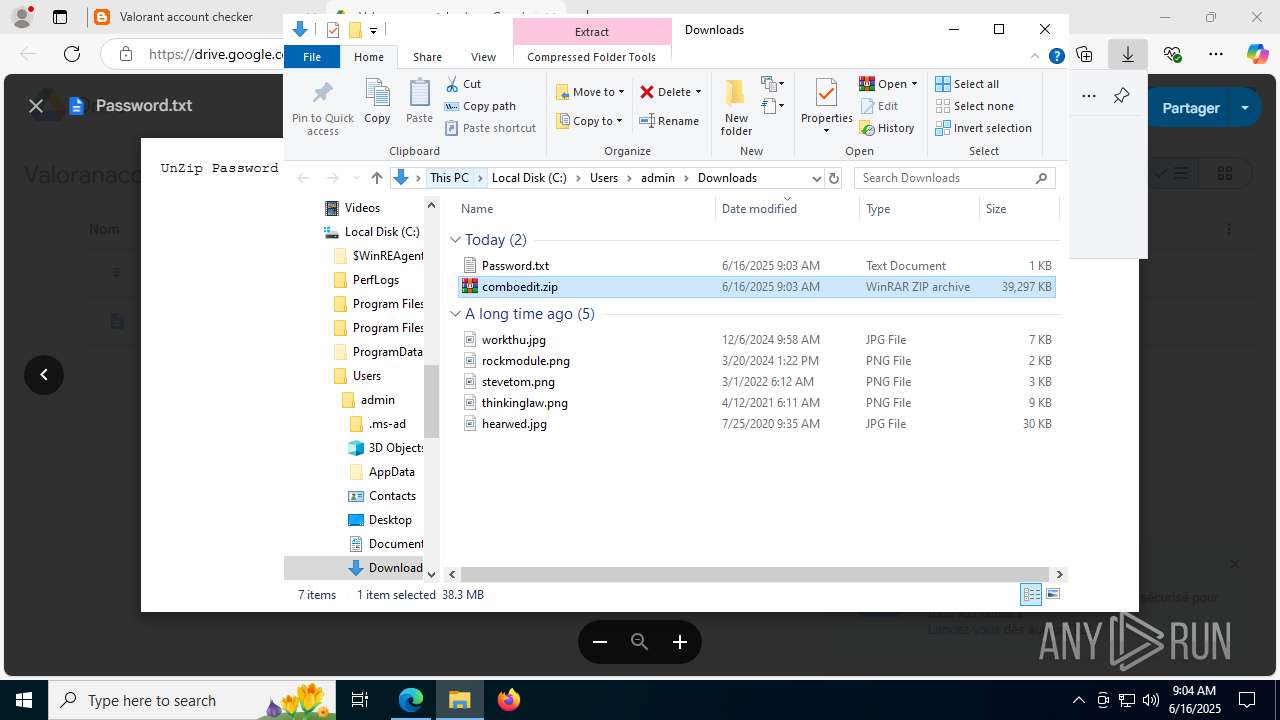
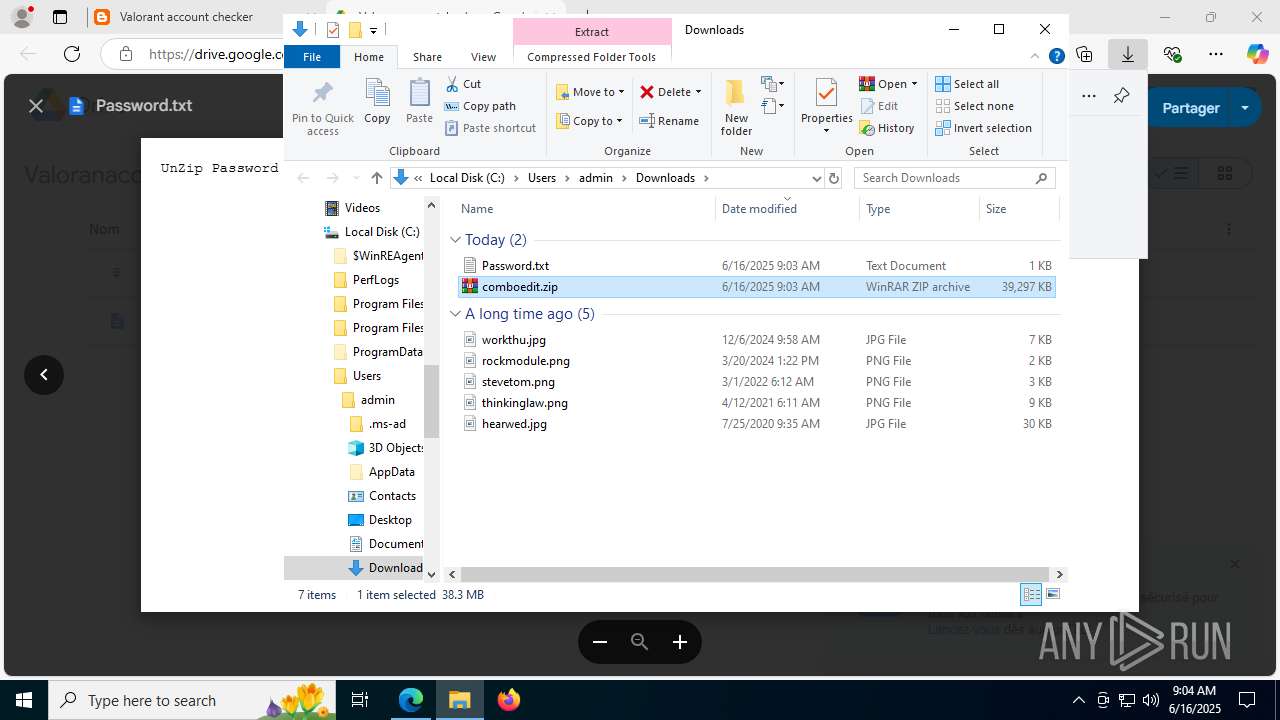
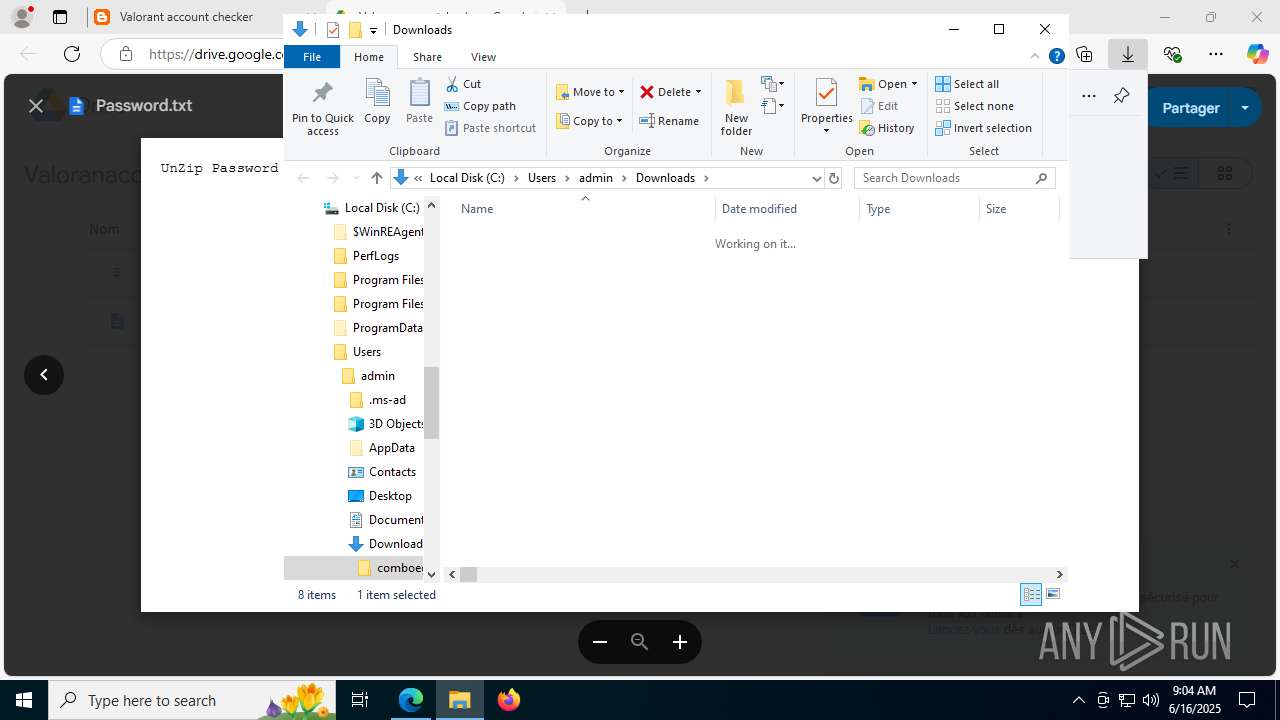
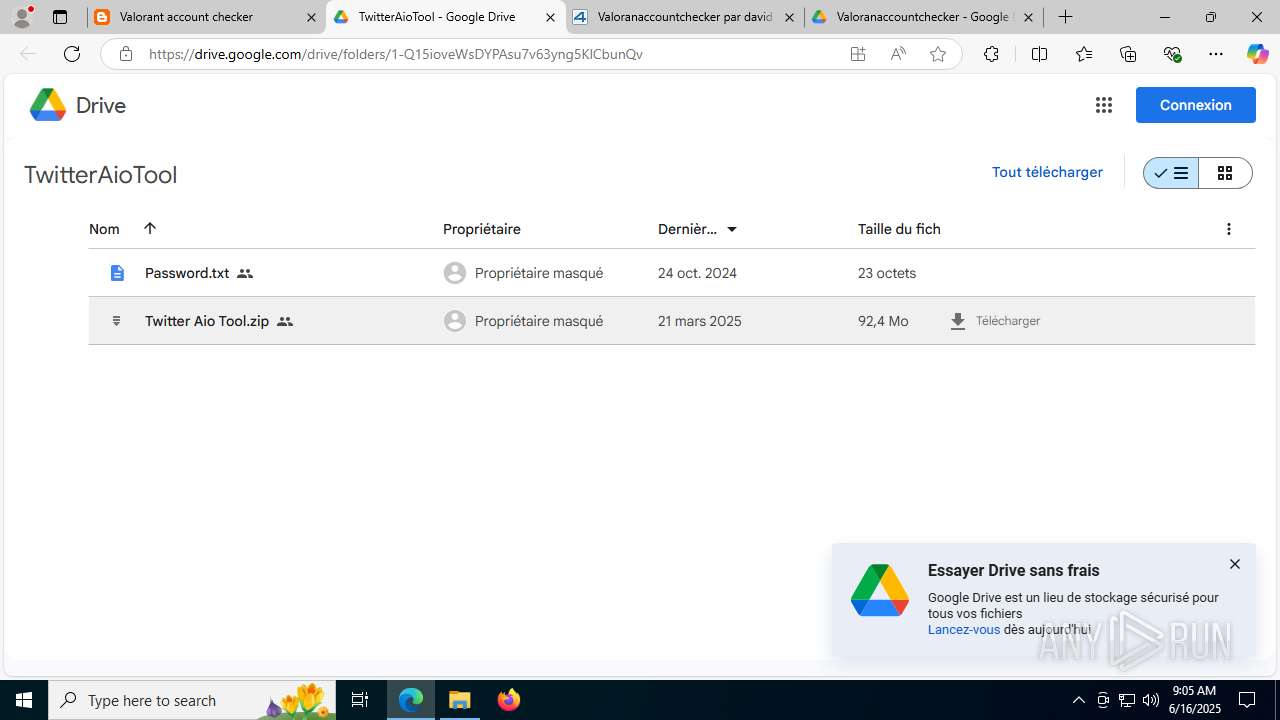
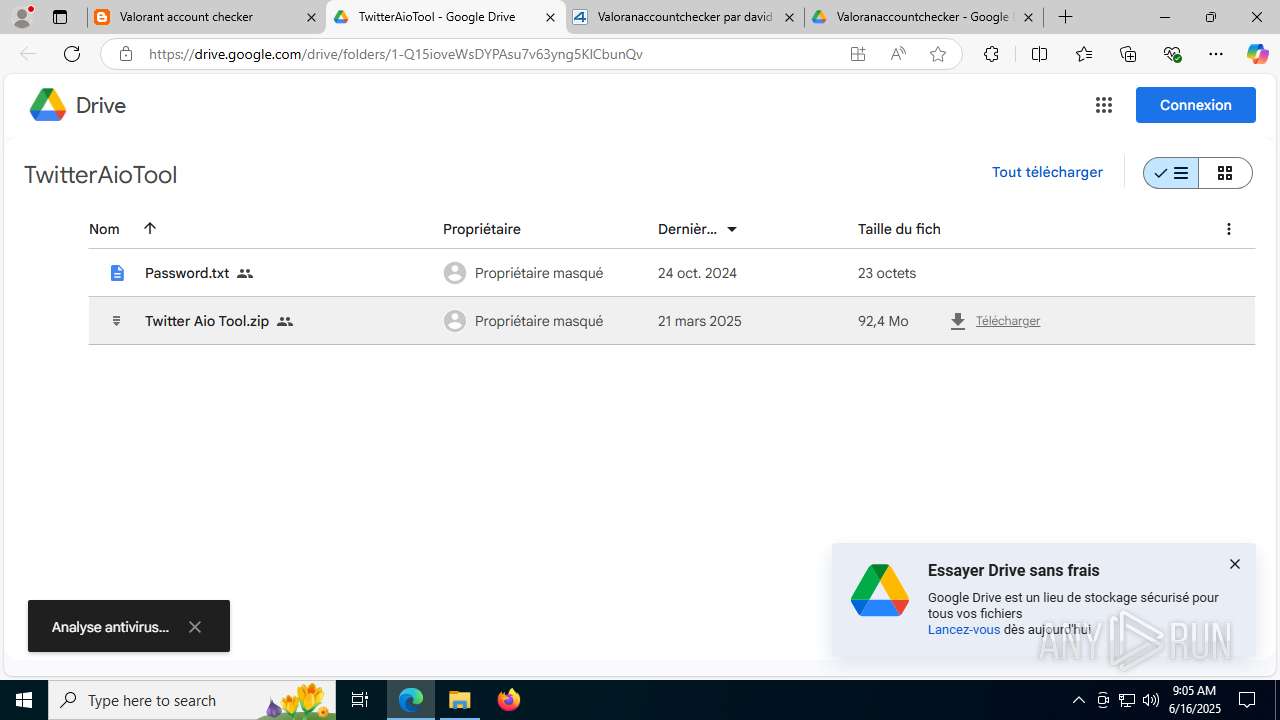
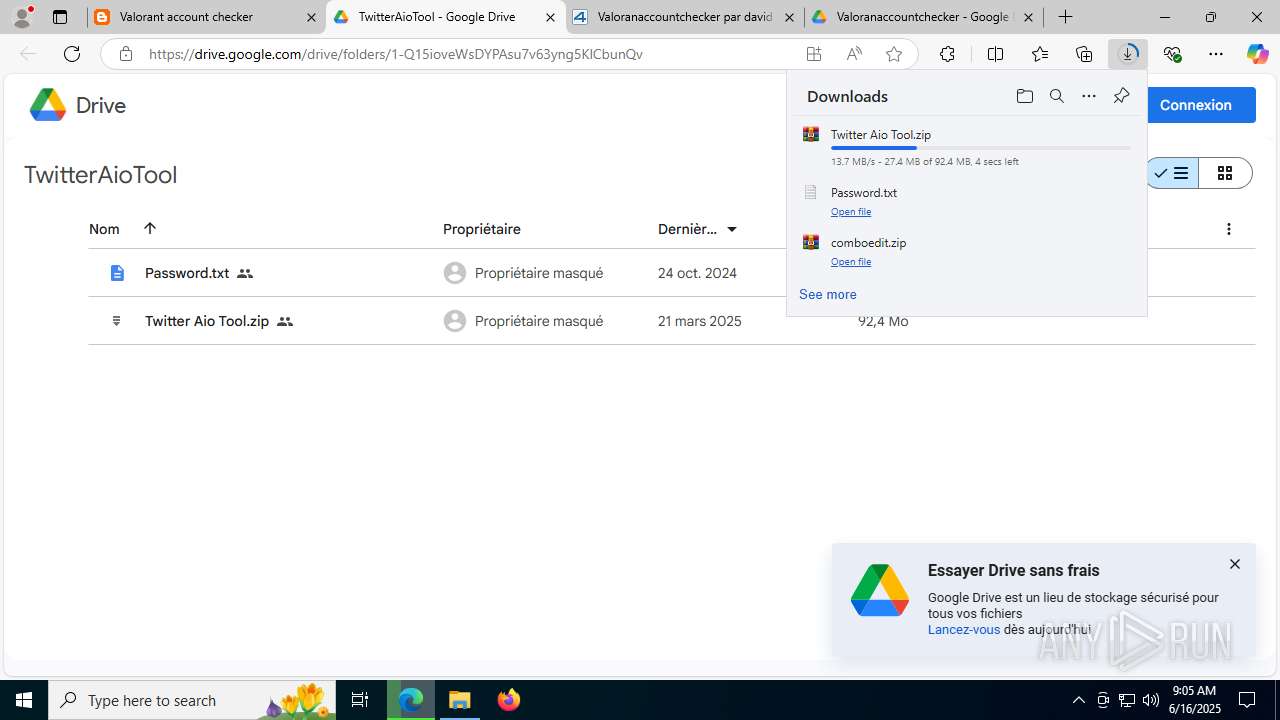
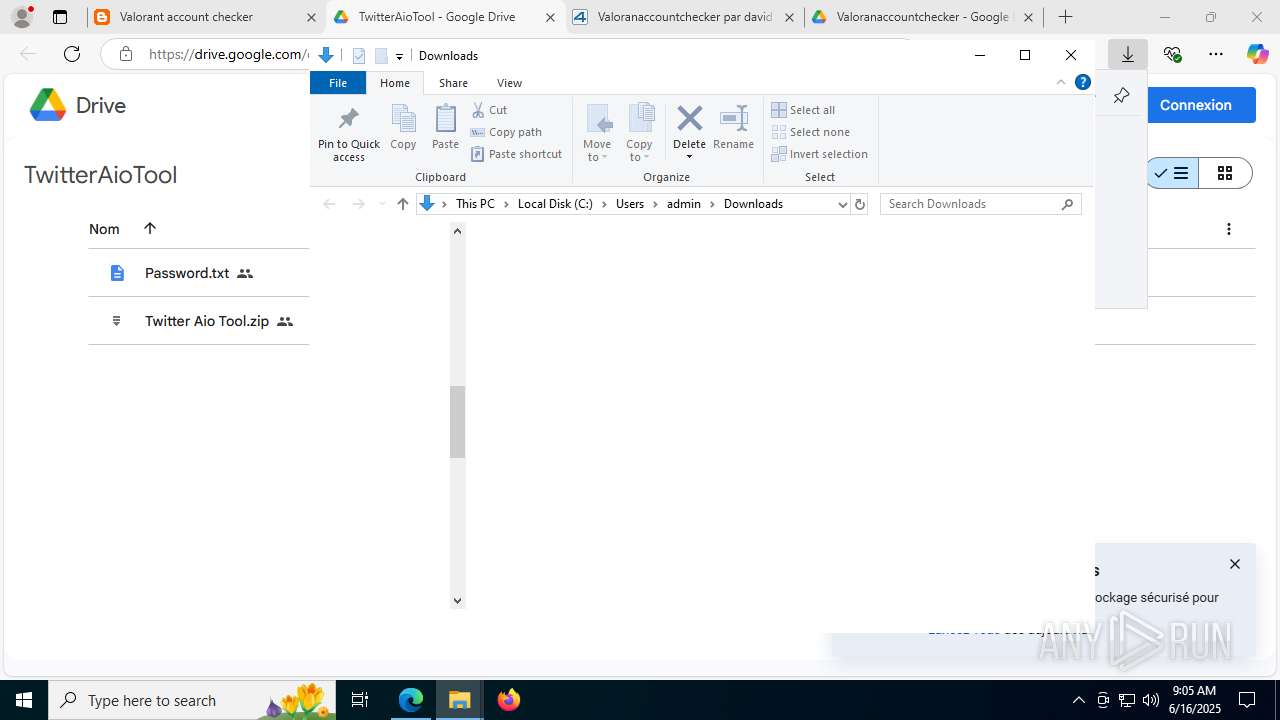
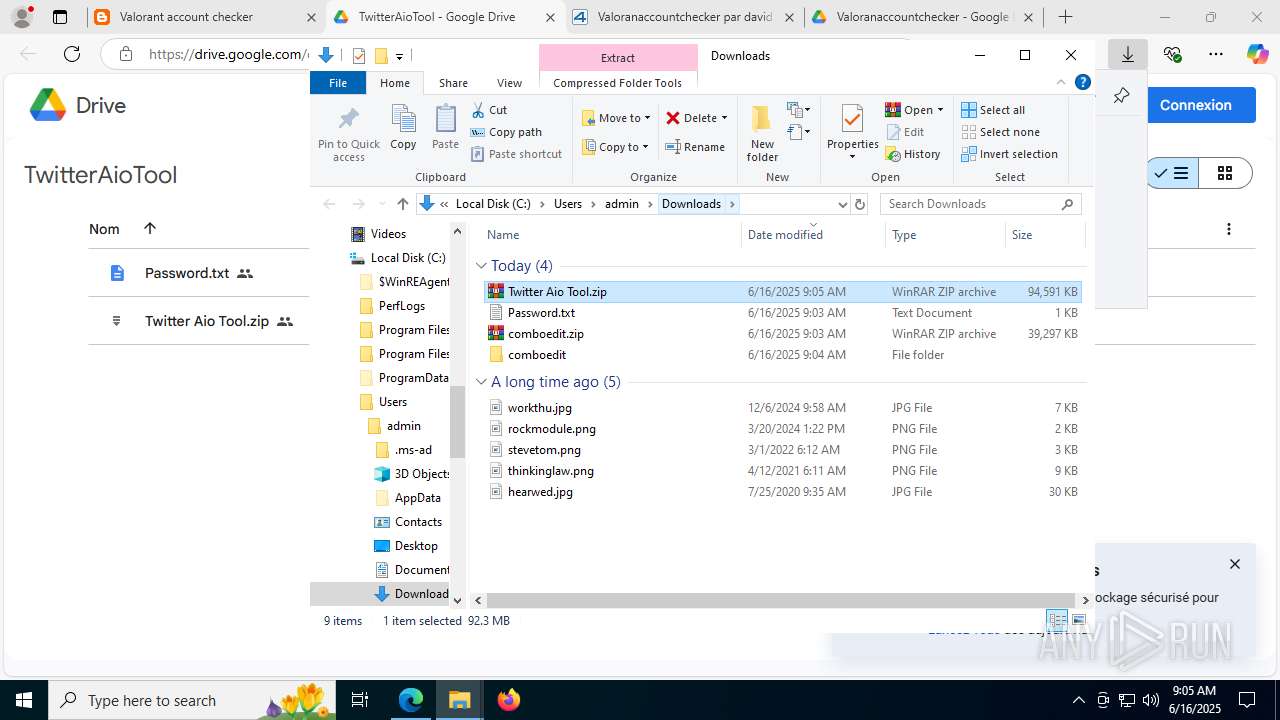
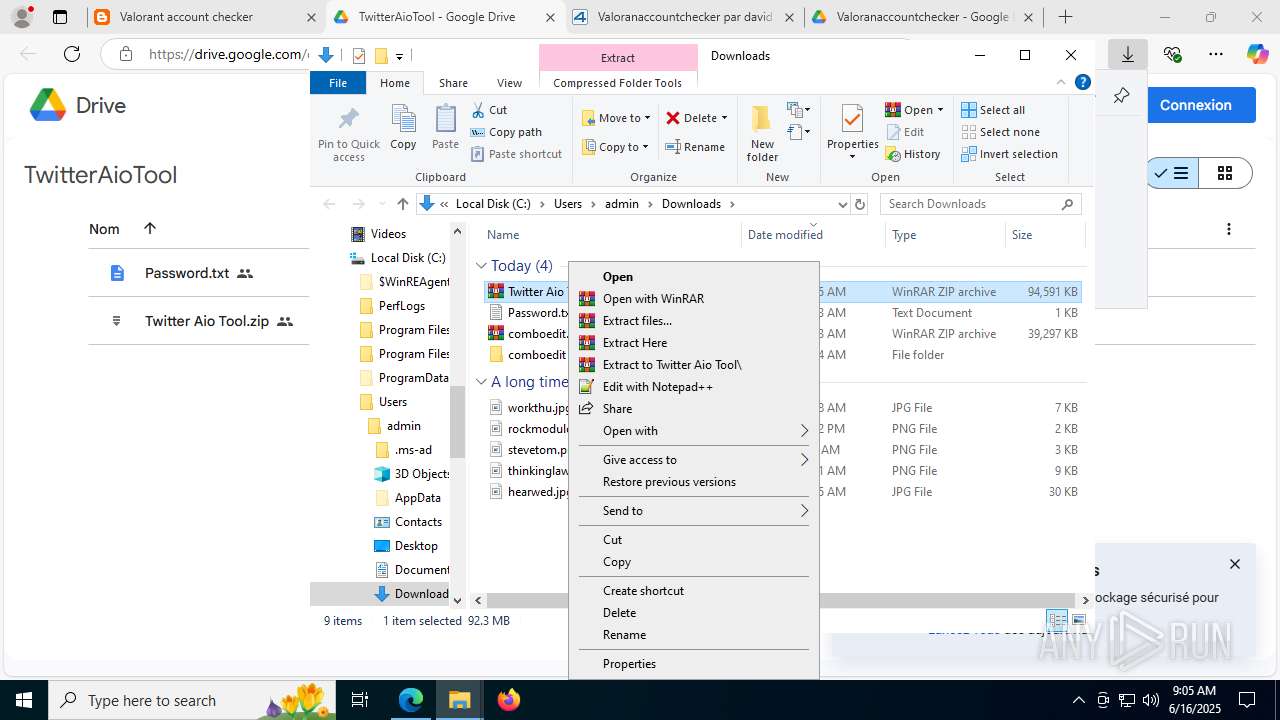
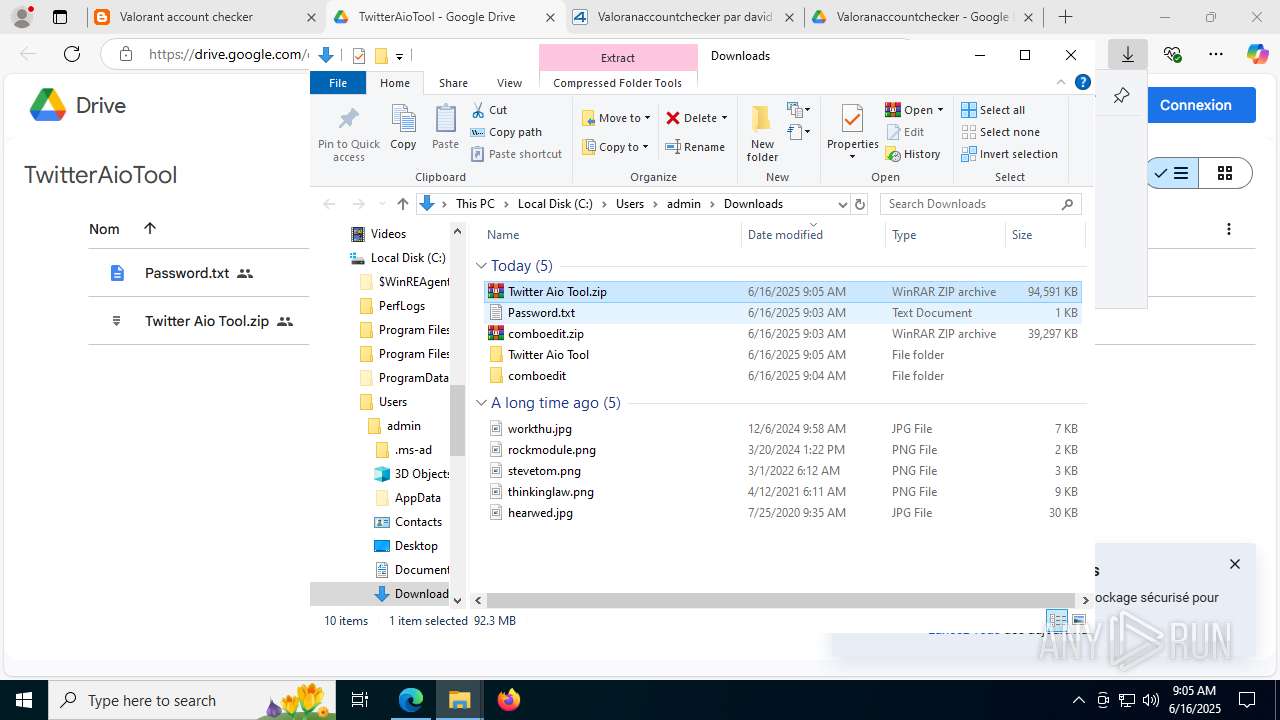
Launching a file from the Downloads directory
- msedge.exe (PID: 504)
Reads the computer name
- Setup.exe (PID: 4088)
- Setup.exe (PID: 7920)
- identity_helper.exe (PID: 7820)
- comboedit .exe (PID: 2952)
- comboedit.exe (PID: 7376)
- svchost.exe (PID: 8144)
- svchost.exe (PID: 7336)
Reads the machine GUID from the registry
- Setup.exe (PID: 4088)
- Setup.exe (PID: 7920)
- svchost.exe (PID: 7336)
- svchost.exe (PID: 8144)
Process checks computer location settings
- comboedit.exe (PID: 7376)
- Setup.exe (PID: 4088)
- Setup.exe (PID: 7920)
Create files in a temporary directory
- comboedit.exe (PID: 7376)
- comboedit .exe (PID: 2952)
Reads Environment values
- identity_helper.exe (PID: 7820)
- svchost.exe (PID: 7336)
- svchost.exe (PID: 8144)
Launching a file from a Registry key
- Setup.exe (PID: 4088)
- Setup.exe (PID: 7920)
Reads Microsoft Office registry keys
- msedge.exe (PID: 504)
The sample compiled with english language support
- comboedit .exe (PID: 2952)
- svchost.exe (PID: 8144)
- comboedit .exe (PID: 472)
- svchost.exe (PID: 7968)
- comboedit .exe (PID: 5968)
- explorer.exe (PID: 1812)
- WinRAR.exe (PID: 7072)
- Twitter AIO .exe (PID: 8388)
Creates files or folders in the user directory
- Setup.exe (PID: 4088)
- svchost.exe (PID: 8144)
Disables trace logs
- svchost.exe (PID: 8144)
- svchost.exe (PID: 7336)
Checks proxy server information
- svchost.exe (PID: 7336)
Reads the software policy settings
- svchost.exe (PID: 7336)
- svchost.exe (PID: 8144)
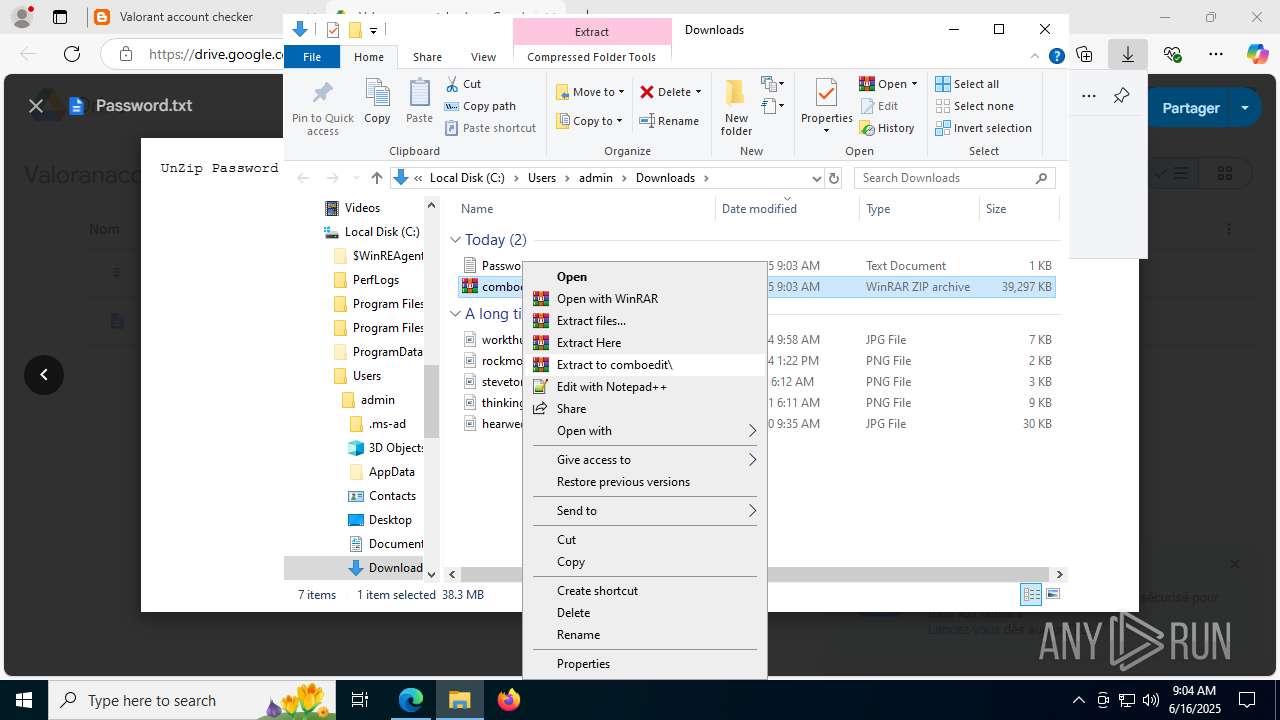
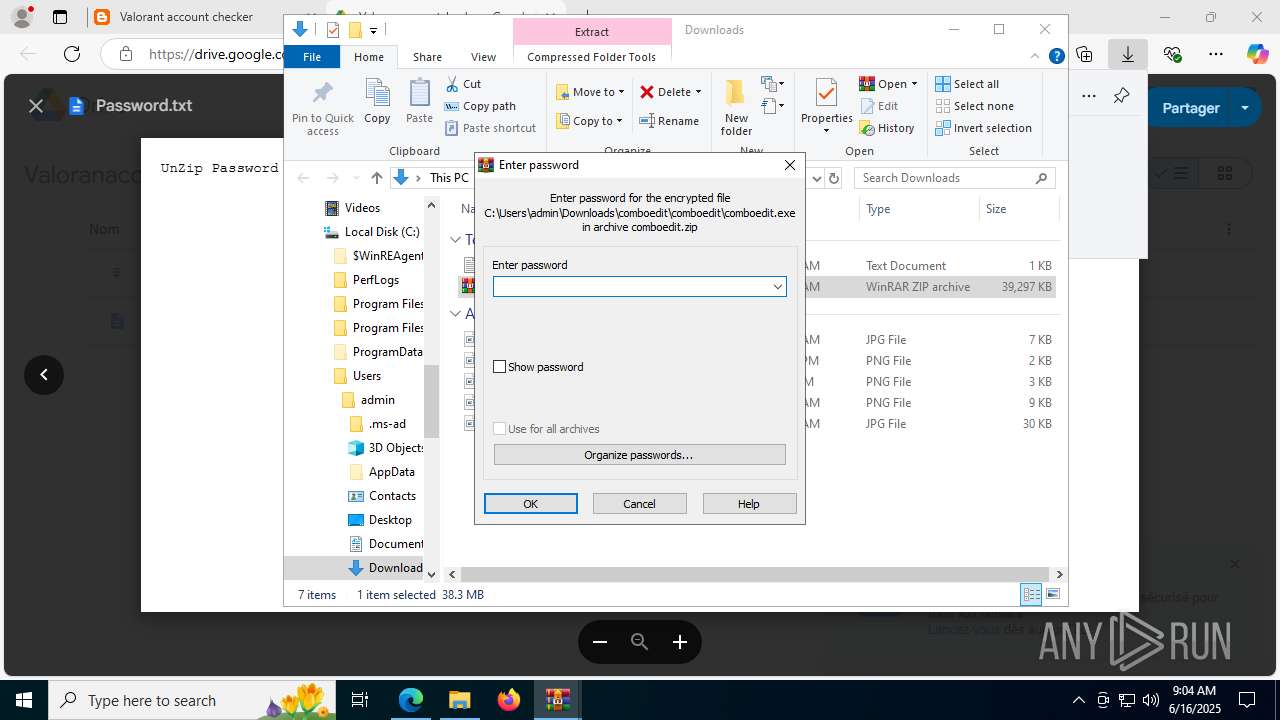
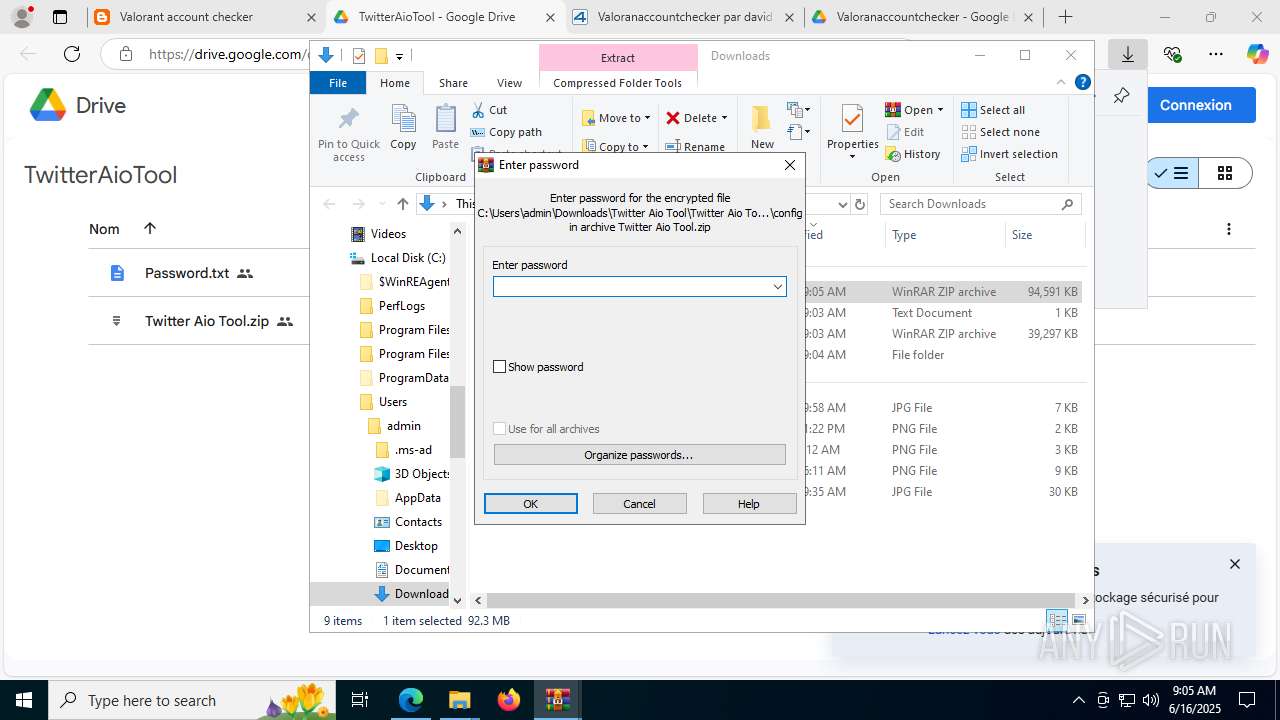
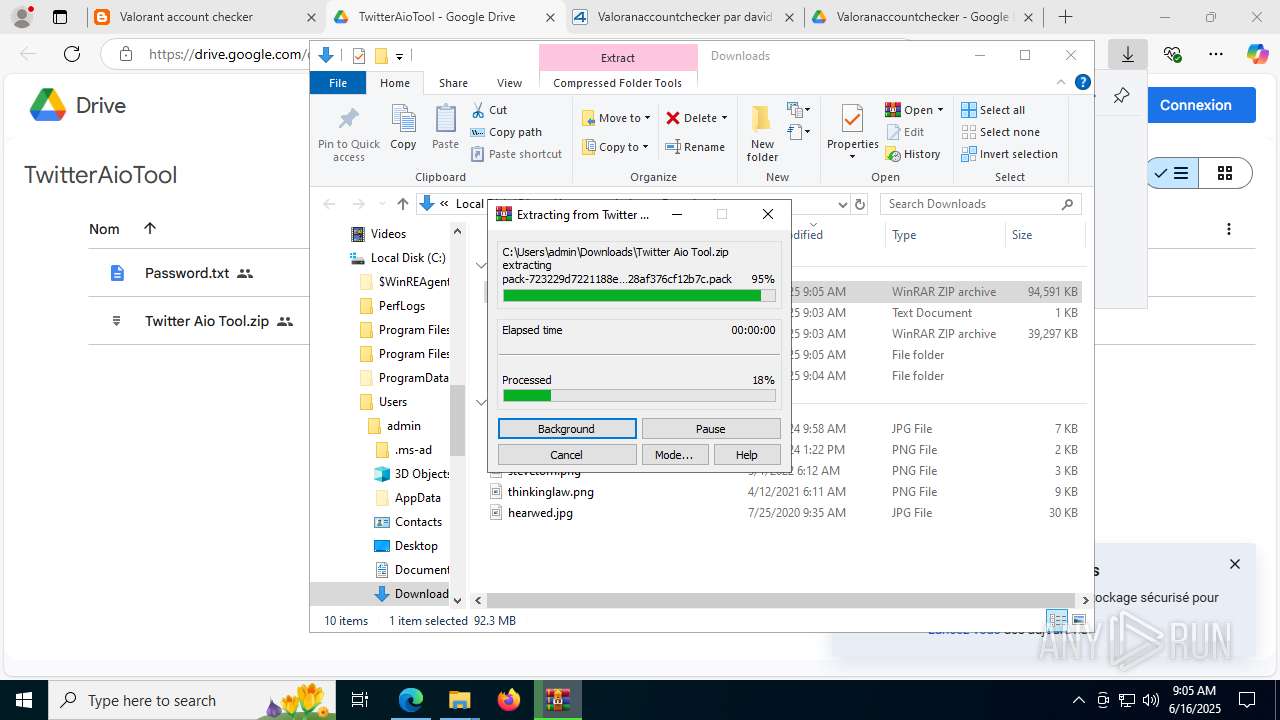
Manual execution by a user
- WinRAR.exe (PID: 6124)
- comboedit.exe (PID: 7924)
- comboedit .exe (PID: 5968)
- WinRAR.exe (PID: 7072)
- notepad.exe (PID: 8852)
- Twitter AIO.exe (PID: 9088)
.NET Reactor protector has been detected
- svchost.exe (PID: 8144)
PyInstaller has been detected (YARA)
- comboedit .exe (PID: 472)
- comboedit .exe (PID: 7308)
- comboedit .exe (PID: 5968)
Checks operating system version
- Twitter AIO .exe (PID: 8516)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
264
Monitored processes
116
Malicious processes
20
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --always-read-main-dll --field-trial-handle=7188,i,8379012479206892300,146765441946323112,262144 --variations-seed-version --mojo-platform-channel-handle=7204 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 472 | "C:\Users\admin\Downloads\comboedit\comboedit\comboedit .exe" | C:\Users\admin\Downloads\comboedit\comboedit\comboedit .exe | comboedit.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 504 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://sitehunterus.blogspot.com/2023/07/valorant-account-checker.html" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7316,i,8379012479206892300,146765441946323112,262144 --variations-seed-version --mojo-platform-channel-handle=7712 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7884,i,8379012479206892300,146765441946323112,262144 --variations-seed-version --mojo-platform-channel-handle=7904 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1508 | "C:\Windows\System32\cmd.exe" /c PowerShell.exe -windowstyle hidden Add-Mppreference -ExclusionPath C:\Users\admin\AppData\Roaming\Microsoft\Windows\Themes\msedge.exe | C:\Windows\System32\cmd.exe | — | version.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1580 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4964,i,8379012479206892300,146765441946323112,262144 --variations-seed-version --mojo-platform-channel-handle=5476 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1688 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2220,i,8379012479206892300,146765441946323112,262144 --variations-seed-version --mojo-platform-channel-handle=2580 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1812 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\explorer.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\explorer.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 10.0.19041.4355 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1868 | PowerShell.exe -windowstyle hidden Add-Mppreference -ExclusionPath C:\Users\admin\AppData\Roaming\Microsoft\Windows\Themes\msedge.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
67 674
Read events
67 363
Write events
311
Delete events
0
Modification events
| (PID) Process: | (504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (504) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5A84B8F242962F00 | |||
| (PID) Process: | (504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459642 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C201F4D7-96DC-4483-99EC-4FDB671F8ADA} | |||
| (PID) Process: | (504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459642 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B2AAC7CF-DFC6-48A8-A321-7C05E9E2B960} | |||
| (PID) Process: | (504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459642 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {20A24350-9CE2-4061-881E-D5E84E55BE0B} | |||
| (PID) Process: | (504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459642 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {559A7AA0-A89A-40D0-9D06-58DEBB07DD6C} | |||
| (PID) Process: | (504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459642 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D4657200-6328-41A7-B536-67DA7C2D5060} | |||
Executable files
537
Suspicious files
560
Text files
267
Unknown types
1 667
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1768bc.TMP | — | |
MD5:— | SHA256:— | |||
| 504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1768eb.TMP | — | |
MD5:— | SHA256:— | |||
| 504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1768eb.TMP | — | |
MD5:— | SHA256:— | |||
| 504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1768eb.TMP | — | |
MD5:— | SHA256:— | |||
| 504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1768fb.TMP | — | |
MD5:— | SHA256:— | |||
| 504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
222
DNS requests
250
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2524 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7336 | svchost.exe | HEAD | 200 | 107.180.41.239:80 | http://amazonhost.thedreamsop.com/2023/explorer.txt | unknown | — | — | unknown |
7328 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1688 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:LY7aKeRvV7OsbGpTC9C-Txlm6uKMwU6P8lE6QvlcEVs&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
8144 | svchost.exe | HEAD | 200 | 107.180.41.239:80 | http://amazonhost.thedreamsop.com/2023/explorer.txt | unknown | — | — | unknown |
7968 | svchost.exe | HEAD | 200 | 107.180.41.239:80 | http://amazonhost.thedreamsop.com/2023/explorer.txt | unknown | — | — | unknown |
4576 | svchost.exe | HEAD | 200 | 23.48.23.53:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750334764&P2=404&P3=2&P4=kxEhz%2br2sbj3myPfeKG%2b599aR4JY6E9ge5ZlC5NzSUfYkixPFv99WGAhtwf1gpa6mG93hDiRxHWSGdTKJ59Avg%3d%3d | unknown | — | — | whitelisted |
7336 | svchost.exe | HEAD | 200 | 107.180.41.239:80 | http://amazonhost.thedreamsop.com/2023/explorer.txt | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6960 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1688 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1688 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1688 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1688 | msedge.exe | 142.250.186.73:443 | www.blogger.com | GOOGLE | US | whitelisted |
1688 | msedge.exe | 142.250.185.138:443 | translate.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
sitehunterus.blogspot.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.blogger.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
1688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
1688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
1688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
1688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
1688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
1688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
1688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2200 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2200 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |