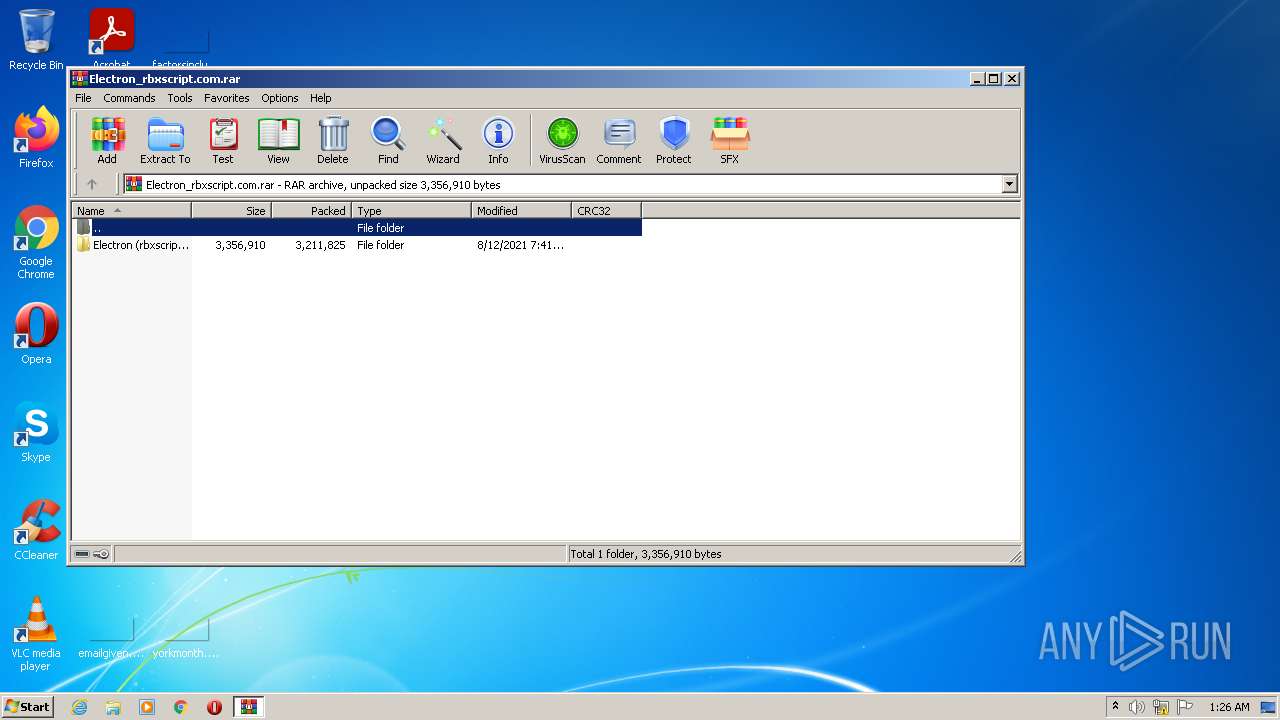
| File name: | Electron_rbxscript.com.rar |
| Full analysis: | https://app.any.run/tasks/a7db57f1-9bb6-45ad-80b9-a0751814954d |
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2022, 01:26:47 |
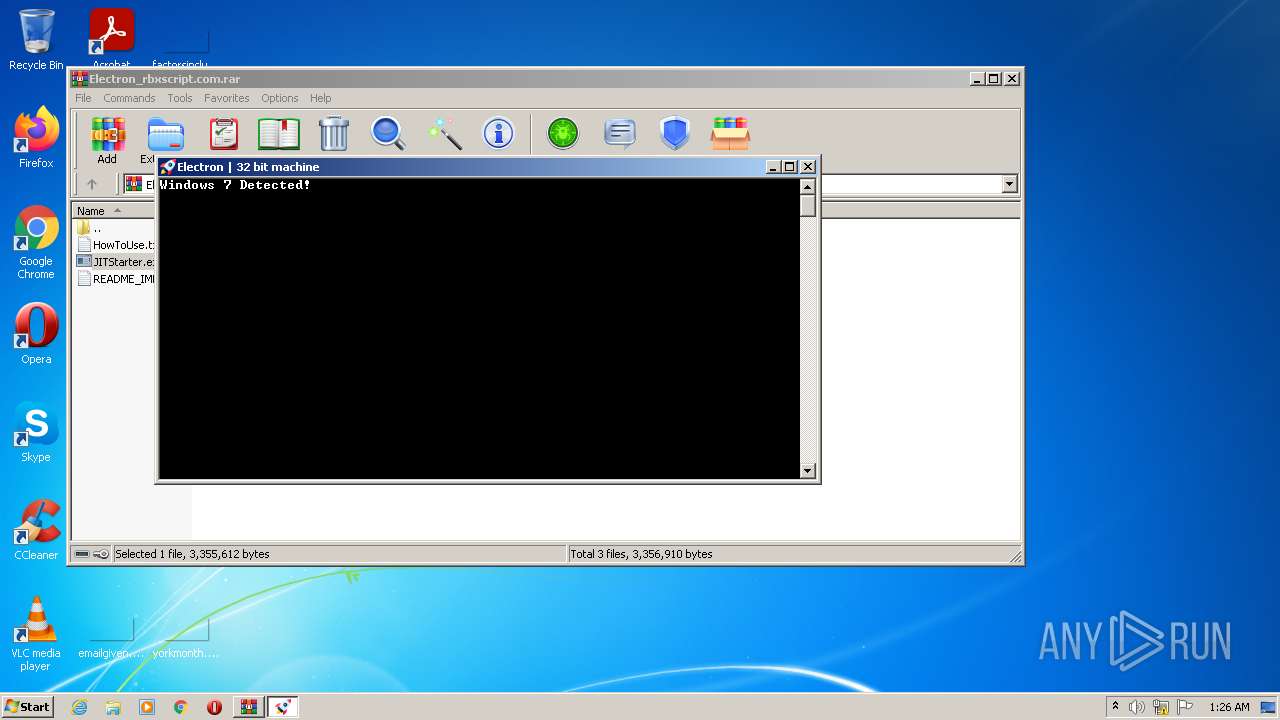
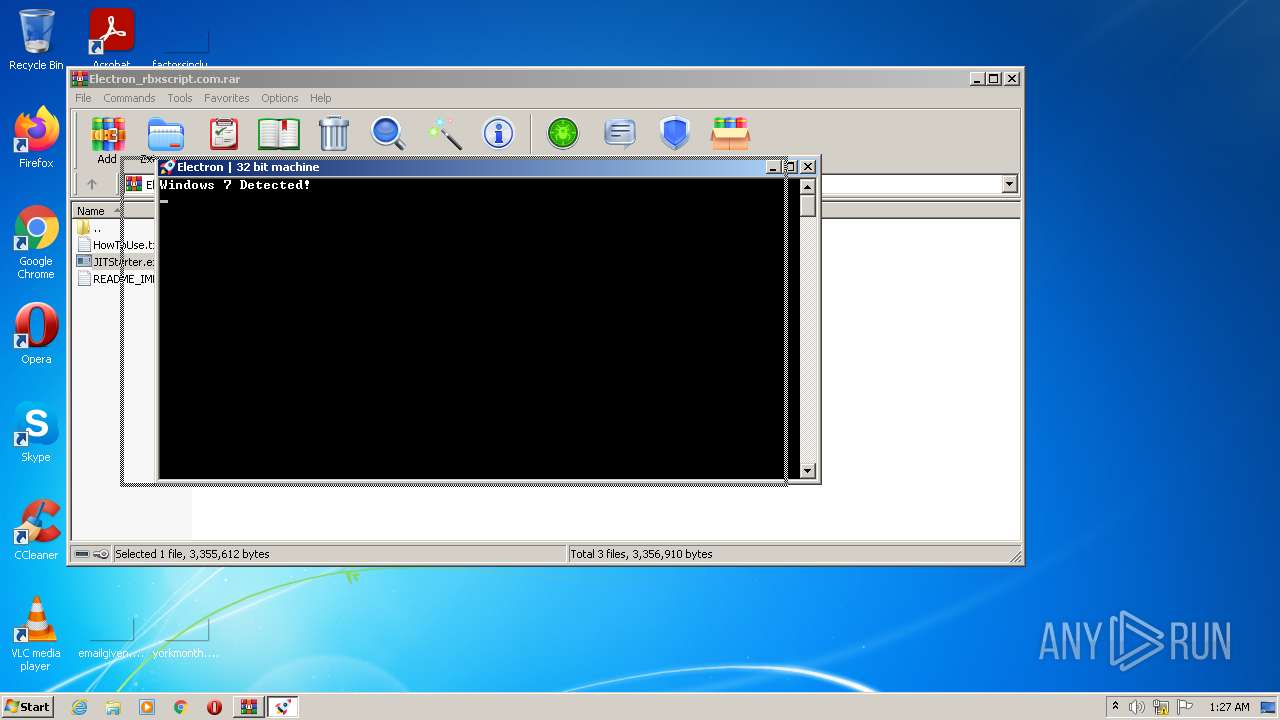
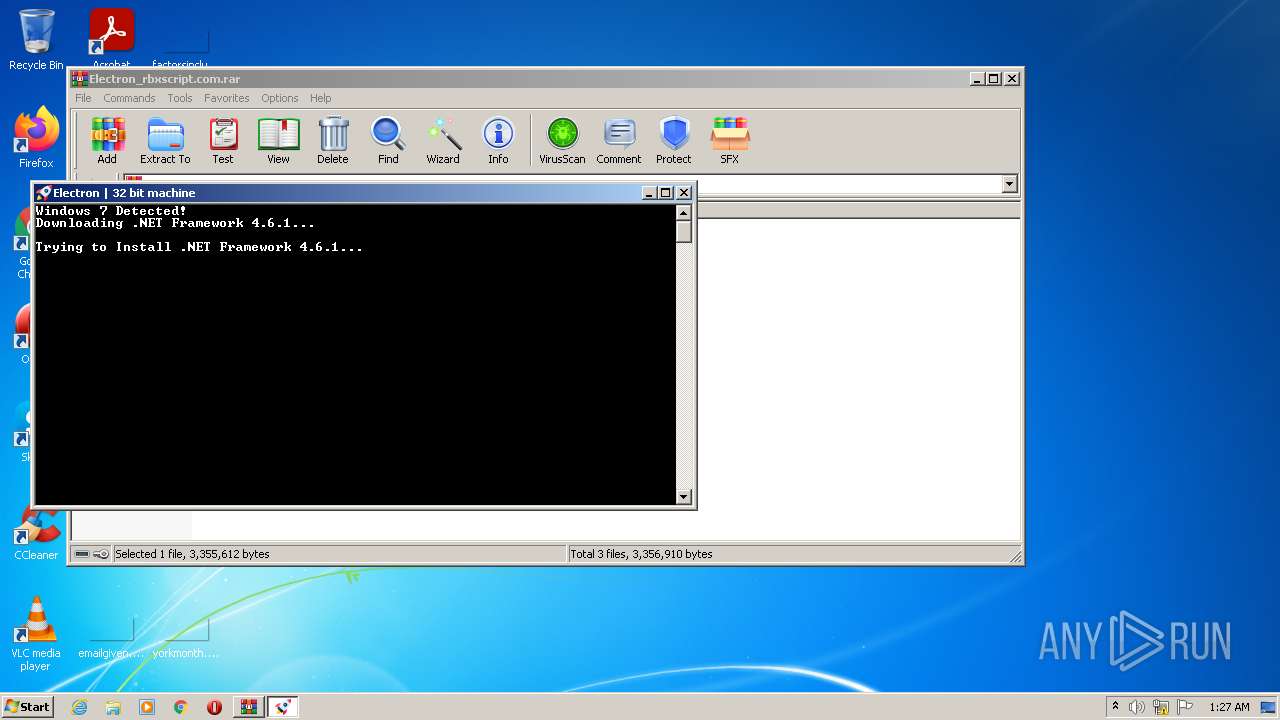
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2ABA670302A8D03D1E48C963B8A70B2E |
| SHA1: | AE6C232DD66D0E84D3C7155ED9543DAE7741F2EF |
| SHA256: | 355D241C0973EC51A4FCD36D5262BF584101AF286FD5723D09DEA45785BECFB3 |
| SSDEEP: | 98304:dkyLTMtVNNlUzu7xpoQkxXVeDQaK8Kge2ERahU:dFnYVFULXtQC |
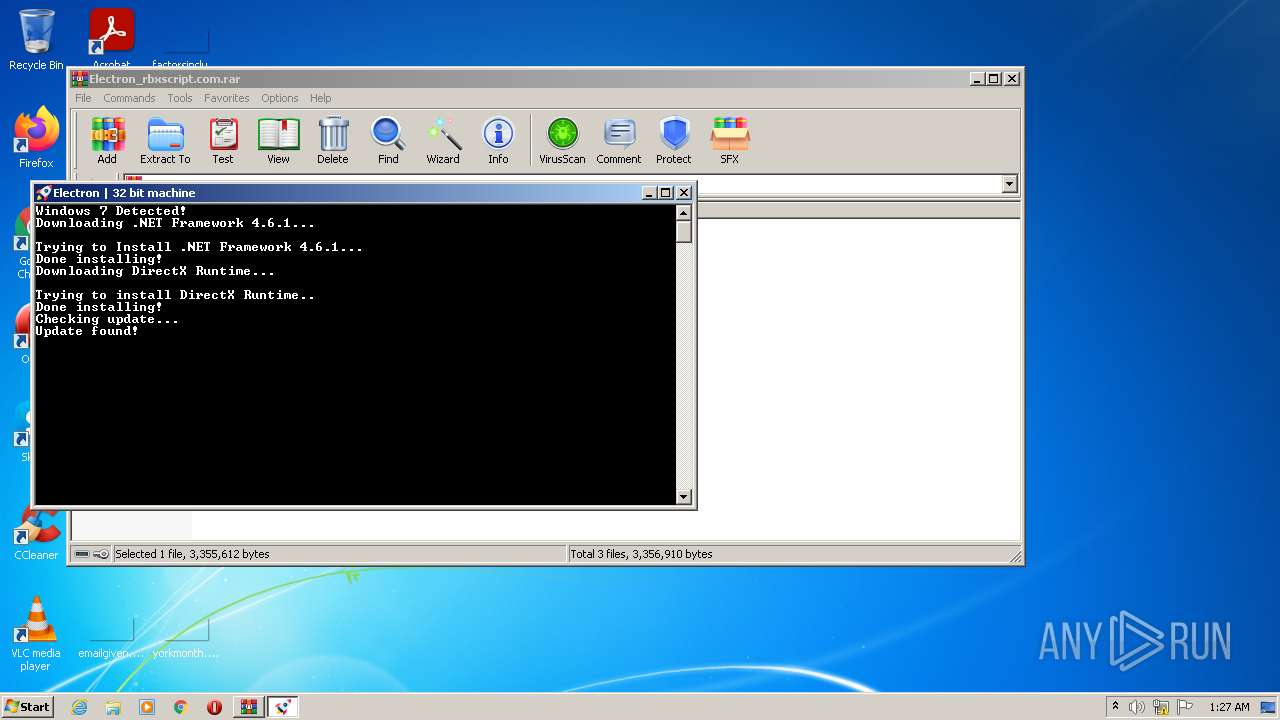
MALICIOUS
Application was dropped or rewritten from another process
- JITStarter.exe (PID: 2260)
- JITStarter.exe (PID: 852)
- Electron.exe (PID: 3624)
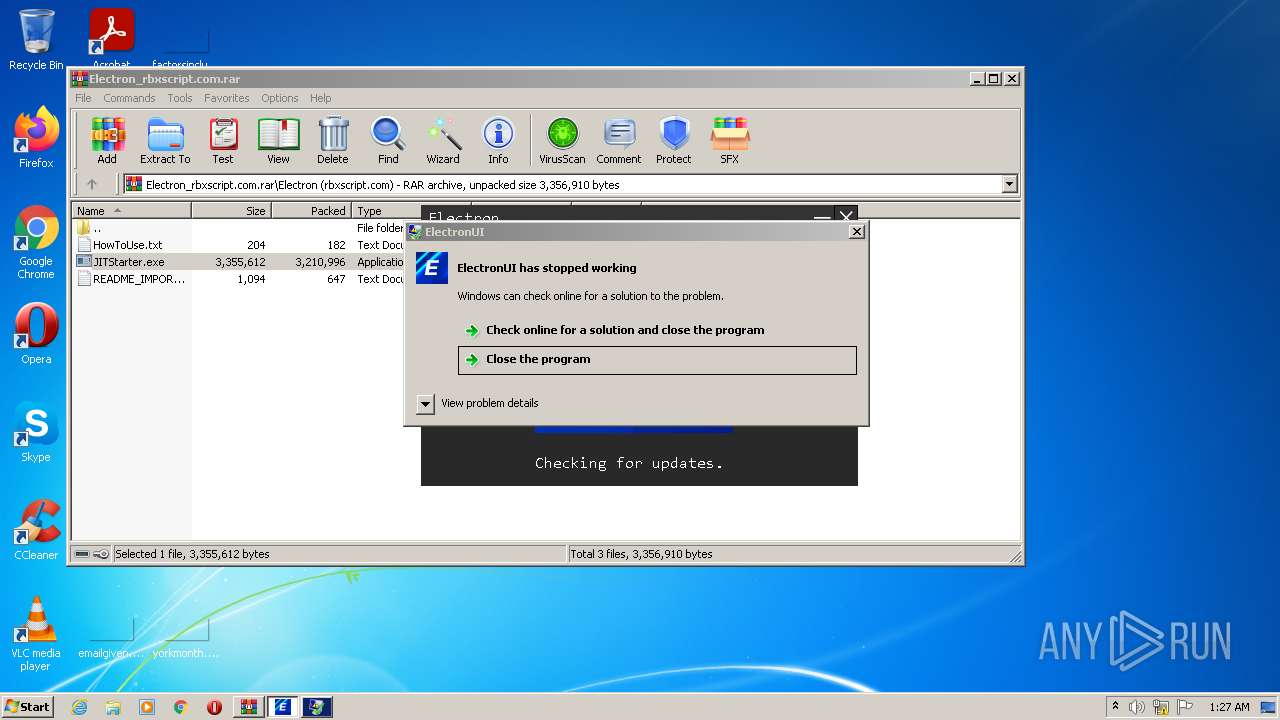
Loads dropped or rewritten executable
- Electron.exe (PID: 3624)
- WerFault.exe (PID: 400)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3444)
- JITStarter.exe (PID: 2260)
- Electron.exe (PID: 3624)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3444)
- JITStarter.exe (PID: 2260)
- Electron.exe (PID: 3624)
Reads the computer name
- WinRAR.exe (PID: 3444)
- JITStarter.exe (PID: 2260)
- Electron.exe (PID: 3624)
Searches for installed software
- JITStarter.exe (PID: 2260)
Starts CMD.EXE for commands execution
- JITStarter.exe (PID: 2260)
Drops a file with a compile date too recent
- JITStarter.exe (PID: 2260)
Drops a file that was compiled in debug mode
- JITStarter.exe (PID: 2260)
- Electron.exe (PID: 3624)
Reads Environment values
- Electron.exe (PID: 3624)
Creates files in the program directory
- WerFault.exe (PID: 400)
INFO
Checks supported languages
- cmd.exe (PID: 1236)
- cmd.exe (PID: 2760)
- WerFault.exe (PID: 400)
Reads the computer name
- cmd.exe (PID: 1236)
- cmd.exe (PID: 2760)
- WerFault.exe (PID: 400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
48
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 400 | C:\Windows\system32\WerFault.exe -u -p 3624 -s 1320 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 852 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3444.17126\Electron (rbxscript.com)\JITStarter.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3444.17126\Electron (rbxscript.com)\JITStarter.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
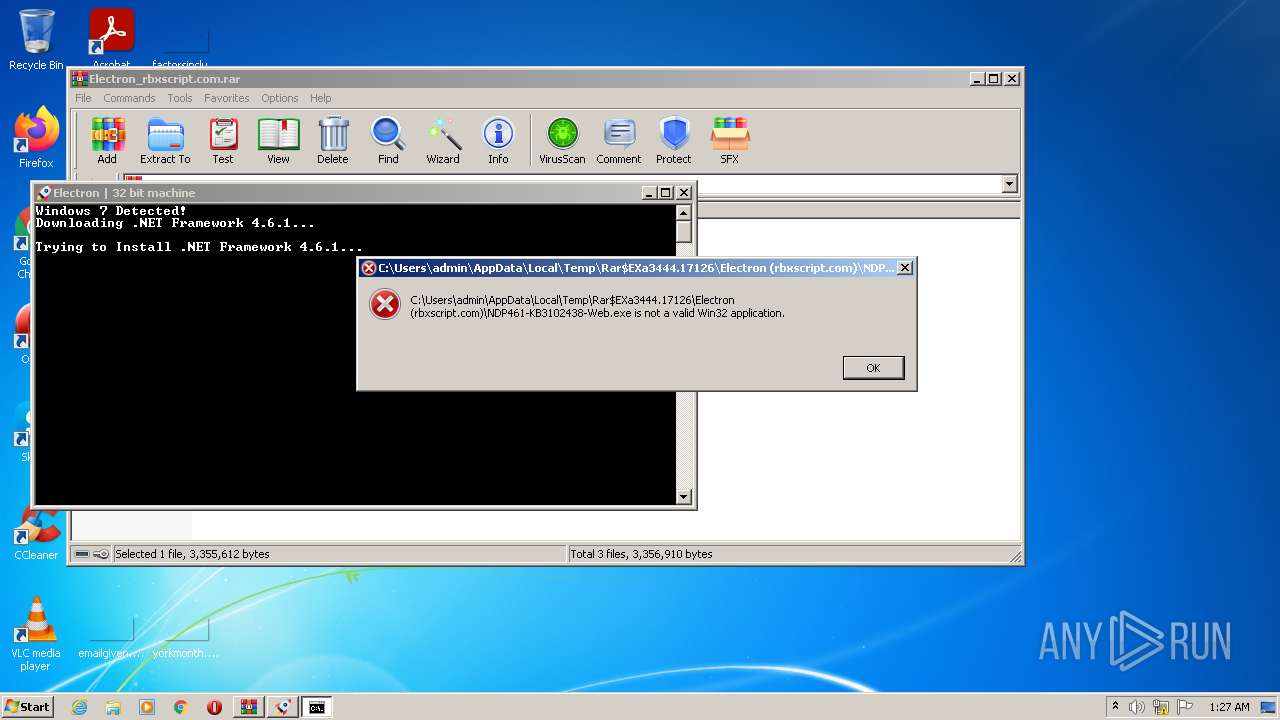
| 1236 | /C NDP461-KB3102438-Web.exe /q /norestart | C:\Windows\system32\cmd.exe | — | JITStarter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2260 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3444.17126\Electron (rbxscript.com)\JITStarter.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3444.17126\Electron (rbxscript.com)\JITStarter.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
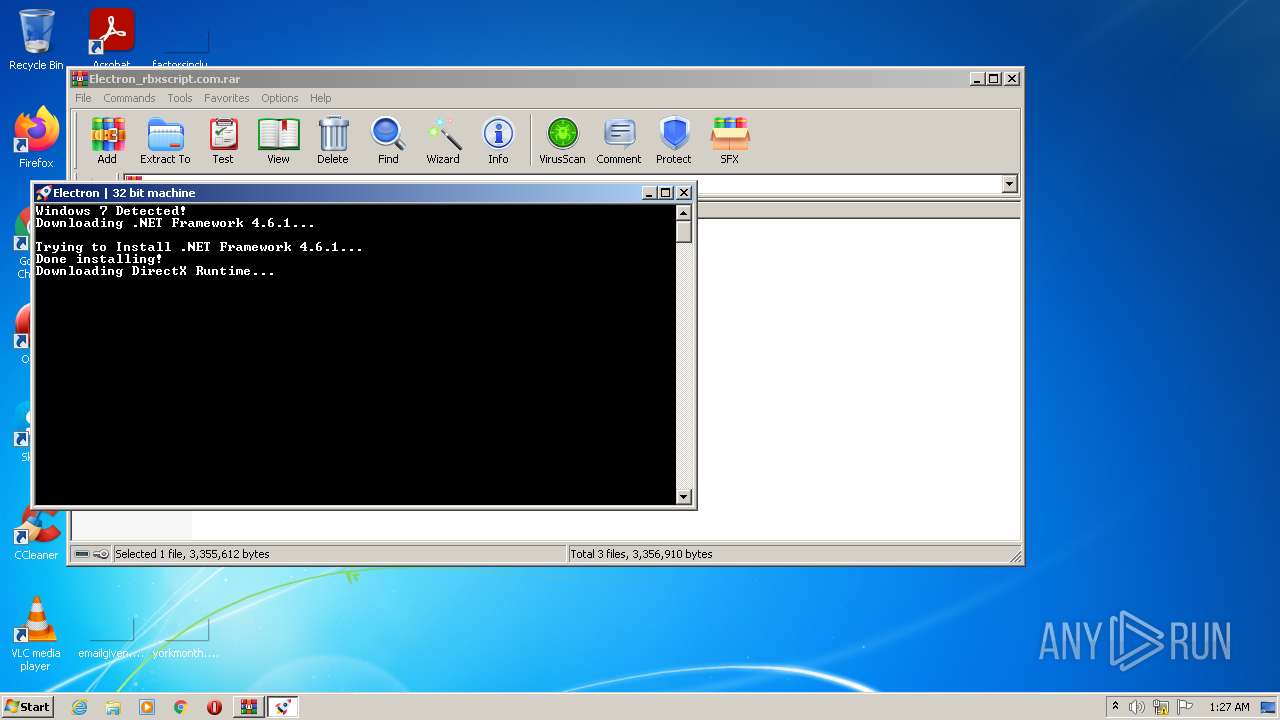
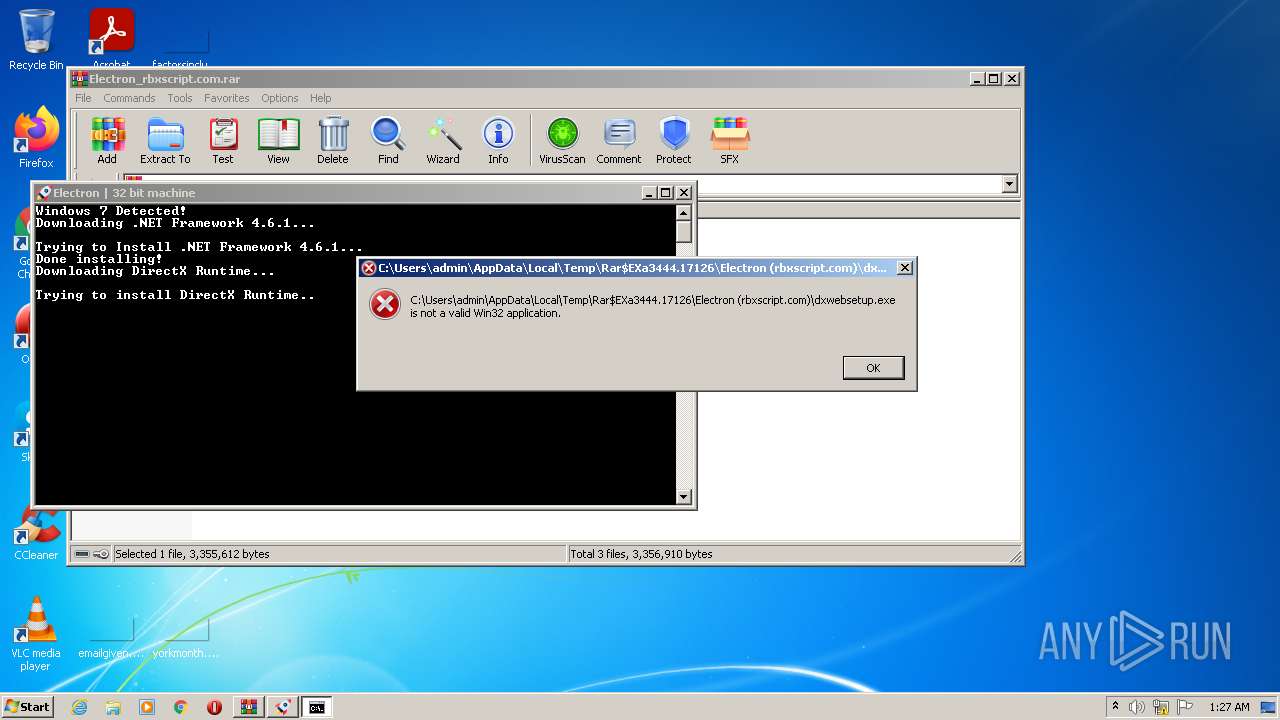
| 2760 | /C dxwebsetup.exe /Q | C:\Windows\system32\cmd.exe | — | JITStarter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
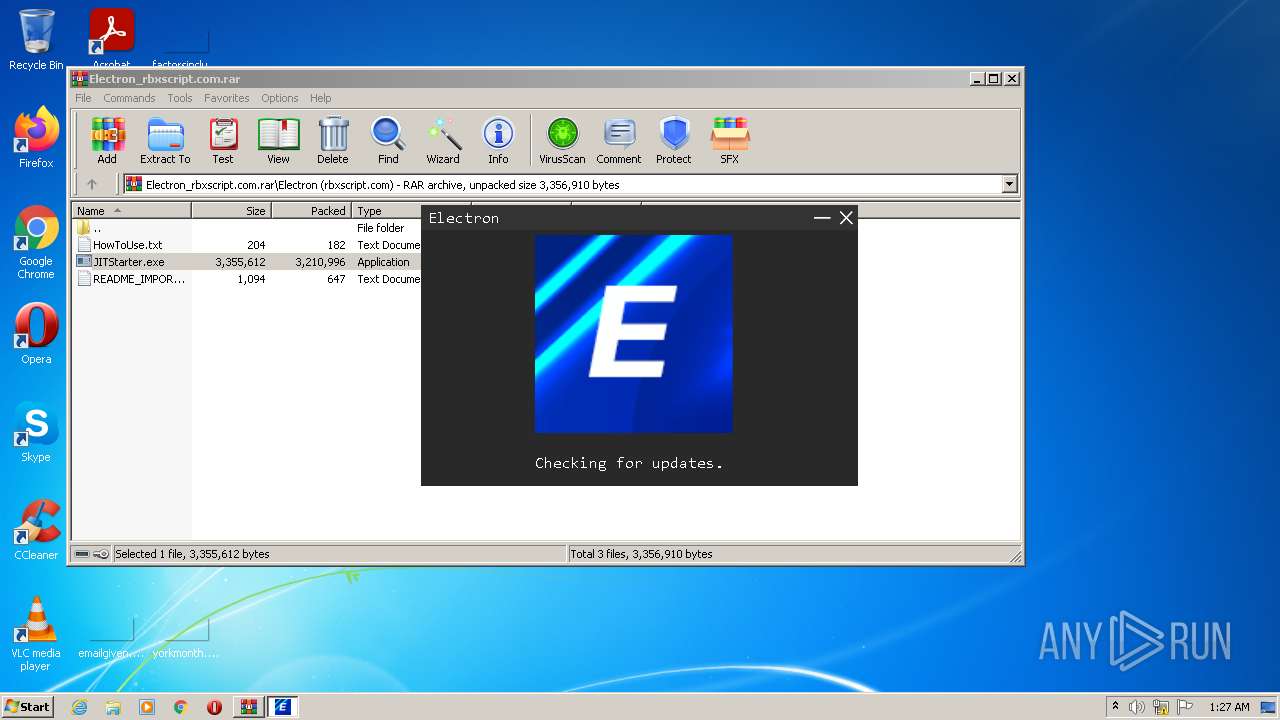
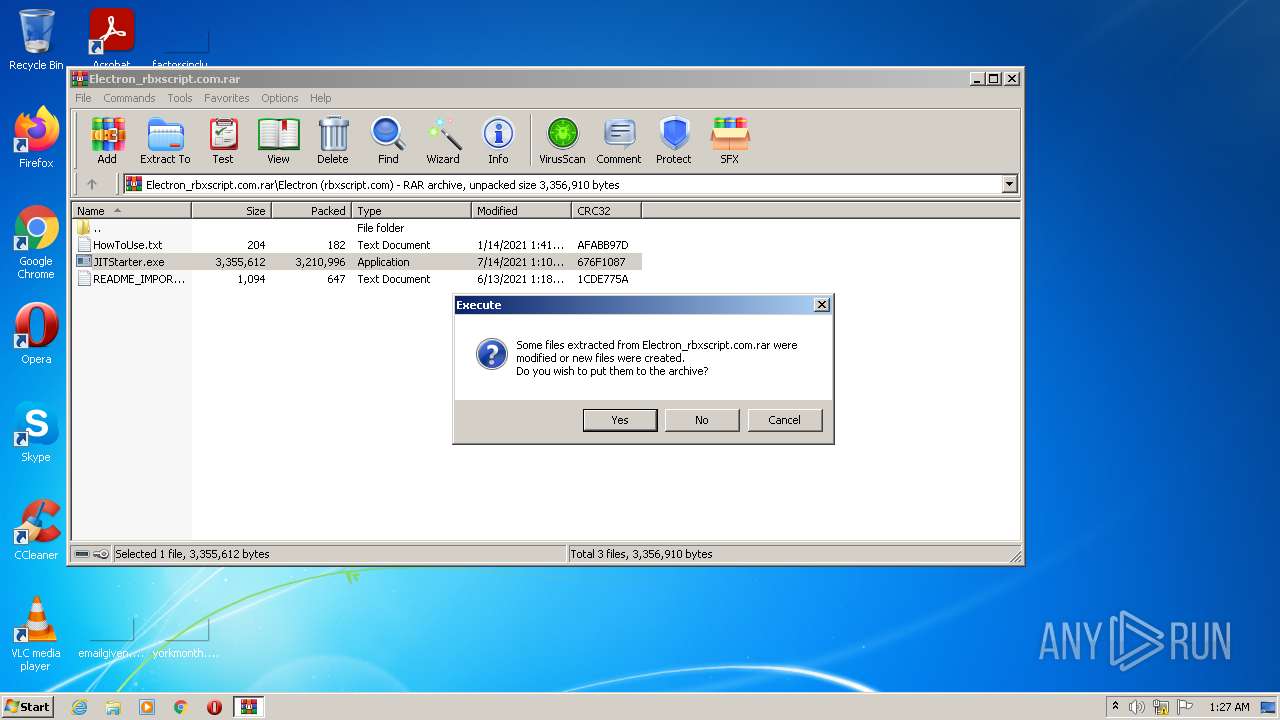
| 3444 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Electron_rbxscript.com.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3624 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3444.17126\Electron (rbxscript.com)\Electron.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3444.17126\Electron (rbxscript.com)\Electron.exe | JITStarter.exe | ||||||||||||
User: admin Company: Electron Integrity Level: HIGH Description: ElectronUI Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
4 036
Read events
3 978
Write events
58
Delete events
0
Modification events
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Electron_rbxscript.com.rar | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
3
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 400 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_Electron.exe_b3fd8c5d92a93b6e69a4aff9d74dca28aa7537_019ea302\Report.wer | — | |
MD5:— | SHA256:— | |||
| 400 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\Electron.exe.3624.dmp | — | |
MD5:— | SHA256:— | |||
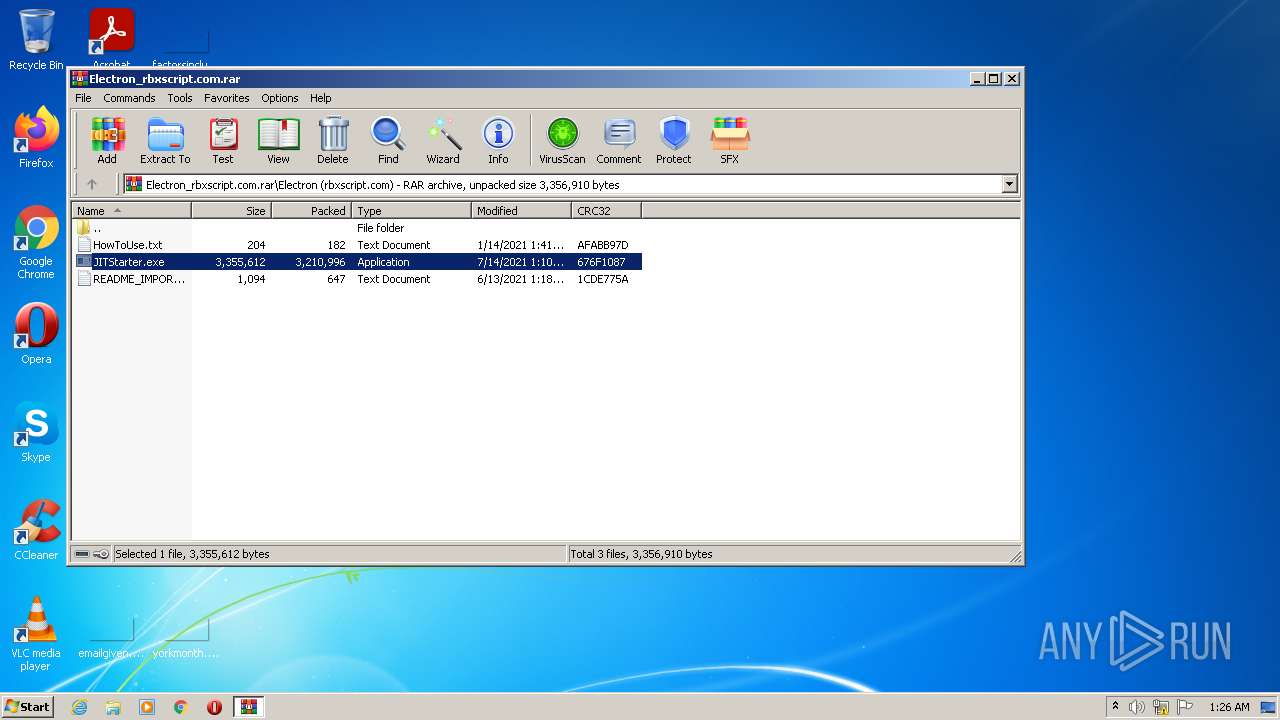
| 3444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3444.17126\Electron (rbxscript.com)\README_IMPORTANT.txt | text | |
MD5:— | SHA256:— | |||
| 3444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3444.17126\Electron (rbxscript.com)\JITStarter.exe | executable | |
MD5:— | SHA256:— | |||
| 2260 | JITStarter.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3444.17126\Electron (rbxscript.com)\temp | compressed | |
MD5:— | SHA256:— | |||
| 2260 | JITStarter.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3444.17126\Electron (rbxscript.com)\Electron.exe | executable | |
MD5:— | SHA256:— | |||
| 2260 | JITStarter.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3444.17126\Electron (rbxscript.com)\bin\uiversion | text | |
MD5:— | SHA256:— | |||
| 3444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3444.17126\Electron (rbxscript.com)\HowToUse.txt | text | |
MD5:21670A30885B42C14899543948369351 | SHA256:6523078ACA59F46D4FB4EC12A2B4C3E7204D175E2BE3AE464234E4428BB78012 | |||
| 3624 | Electron.exe | C:\Users\admin\AppData\Local\Temp\fe18e516-f12f-4073-bf13-52a839118bfb\GunaDotNetRT.dll | executable | |
MD5:9AF5EB006BB0BAB7F226272D82C896C7 | SHA256:77DC05A6BDA90757F66552EE3F469B09F1E00732B4EDCA0F542872FB591ED9DB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
8
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
996 | lsass.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
996 | lsass.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?647ec432d6354502 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2260 | JITStarter.exe | 172.67.175.197:443 | ryos.best | — | US | suspicious |
— | — | 185.199.109.133:443 | raw.githubusercontent.com | GitHub, Inc. | NL | malicious |
2260 | JITStarter.exe | 104.21.17.113:443 | ryos.best | Cloudflare Inc | US | unknown |
996 | lsass.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
996 | lsass.exe | 13.107.4.50:80 | ctldl.windowsupdate.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ryos.best |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cache.ryos.best |
| suspicious |
raw.githubusercontent.com |
| shared |