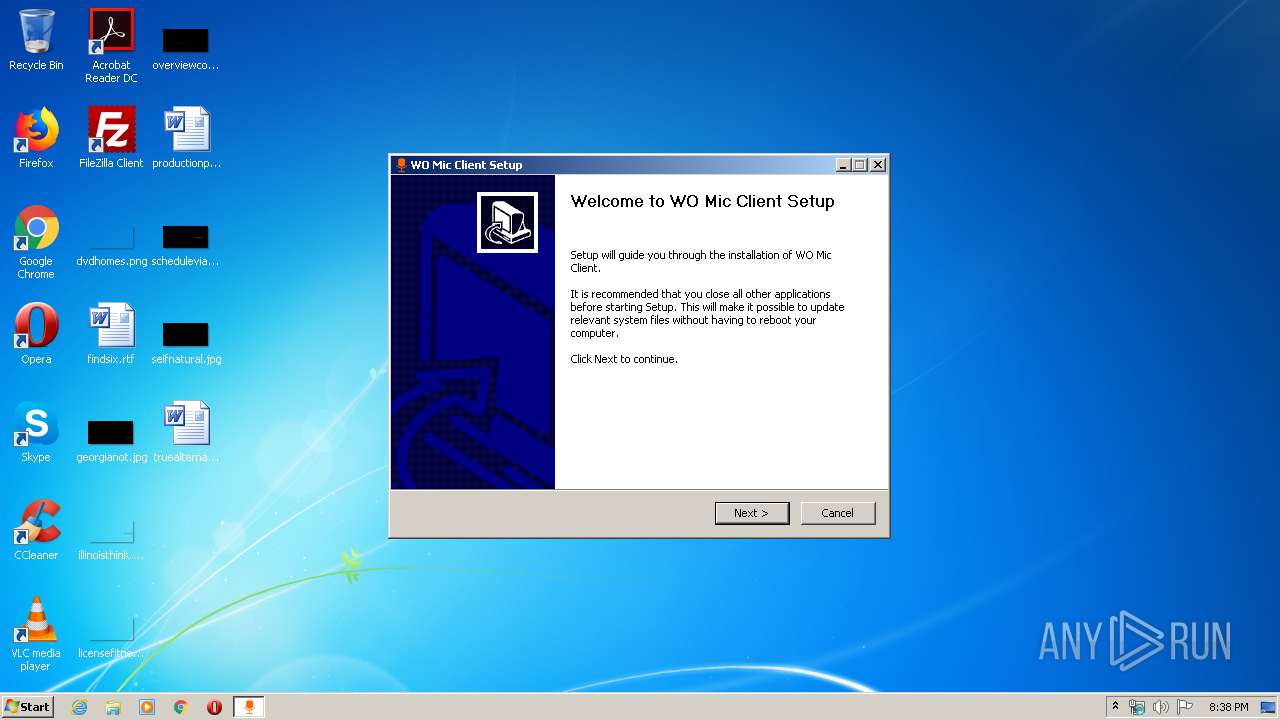
| File name: | wo_mic_client_setup.exe |
| Full analysis: | https://app.any.run/tasks/721d2790-55ff-48be-8b3e-aad8441917b0 |
| Verdict: | Malicious activity |
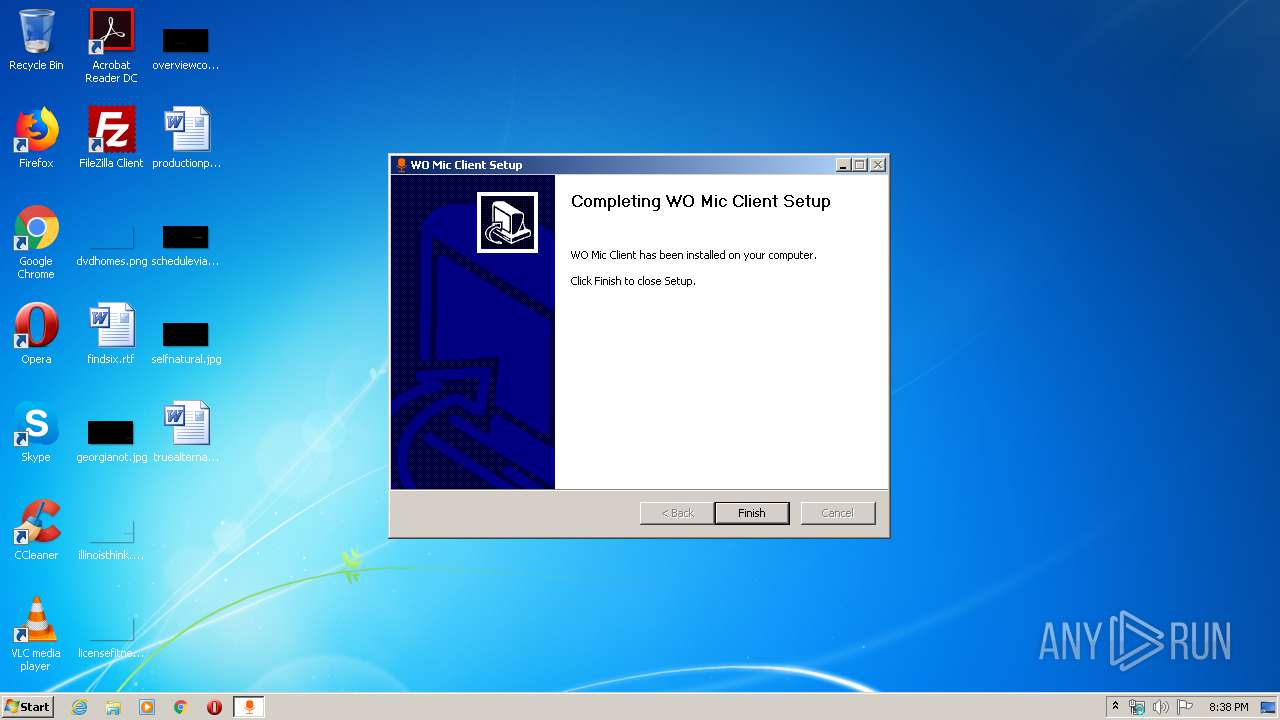
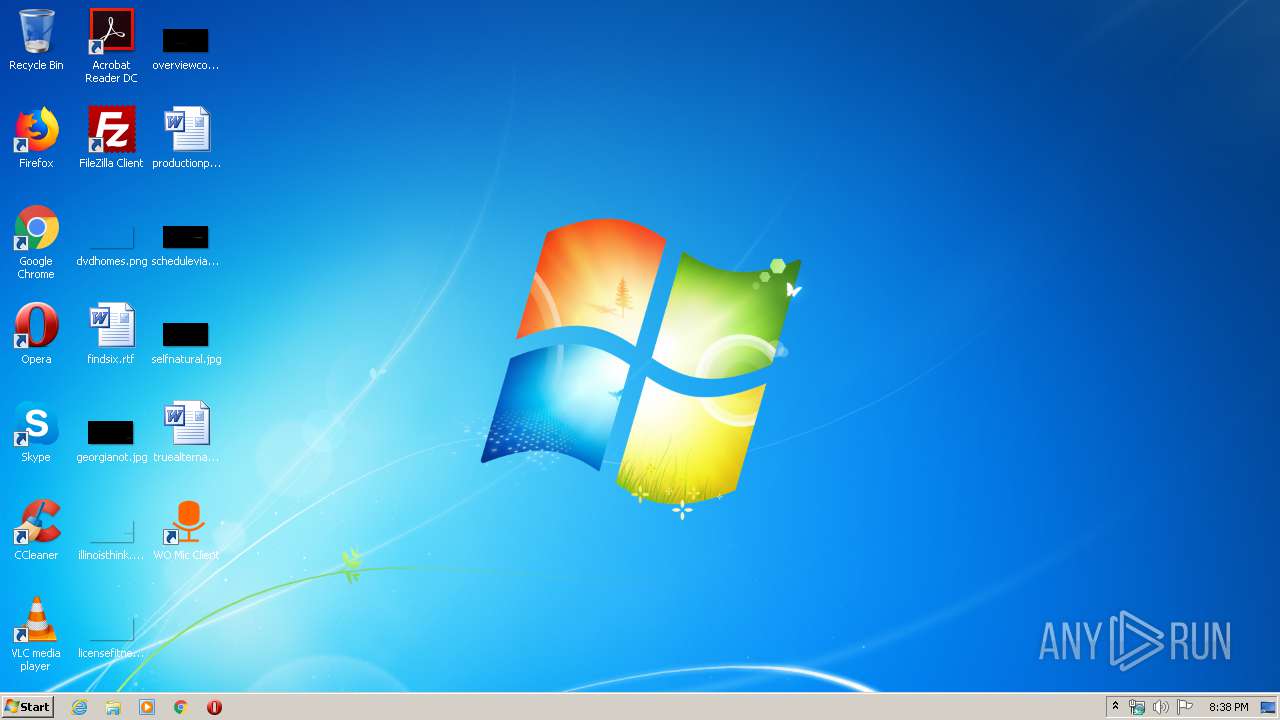
| Analysis date: | February 28, 2020, 20:37:52 |
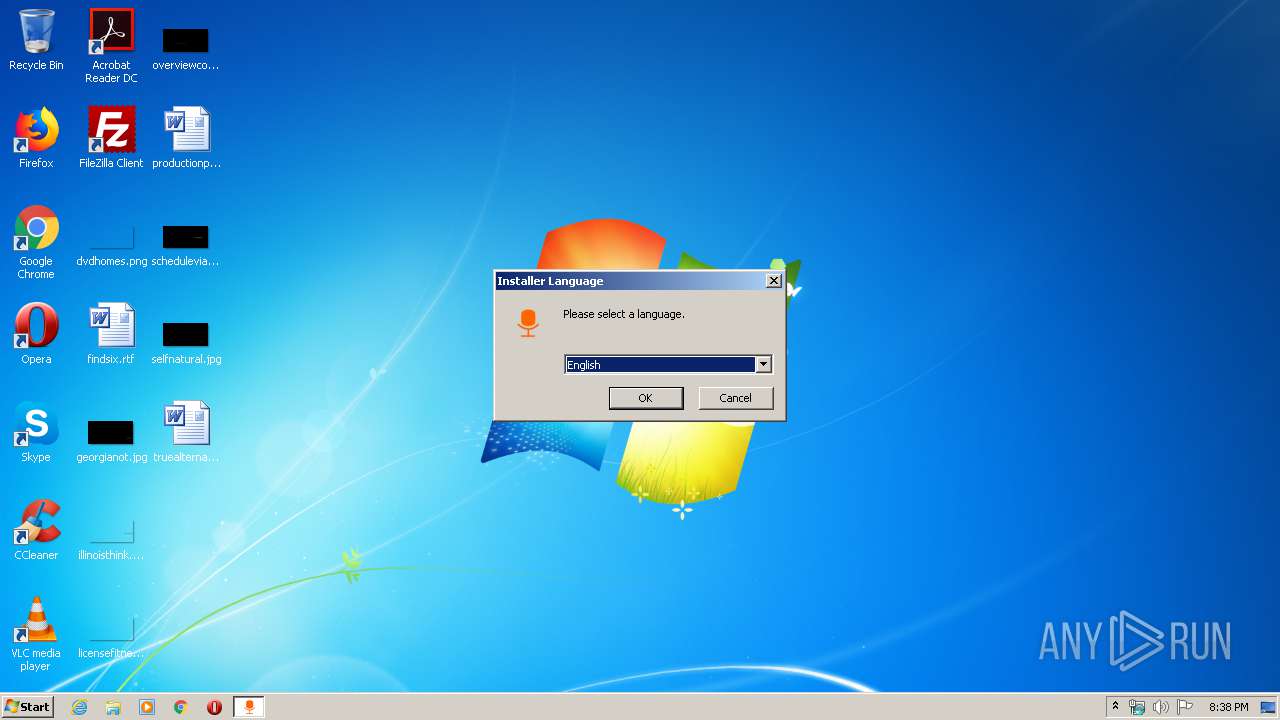
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 42B97C171E2555F56AF75A8FC5E965A7 |
| SHA1: | 5ED9A241B3DAB2CE32518DAC0E4ACED2BC701ACA |
| SHA256: | 3559426BDE167D1417830C253BDDAFB33CC18C0DB35C39E75C764E1772CB48BF |
| SSDEEP: | 24576:G3z/qkTl7g1lmTZh5GYP7INP4w6ZtwZdsIAljoXHNAi7JYqDwLYp0LpgiwZAiS5e:XK7YmlDzBaZfuo3HYYw0Pelu8G5UoN |
MALICIOUS
Loads dropped or rewritten executable
- wo_mic_client_setup.exe (PID: 2152)
Writes to a start menu file
- wo_mic_client_setup.exe (PID: 2152)
SUSPICIOUS
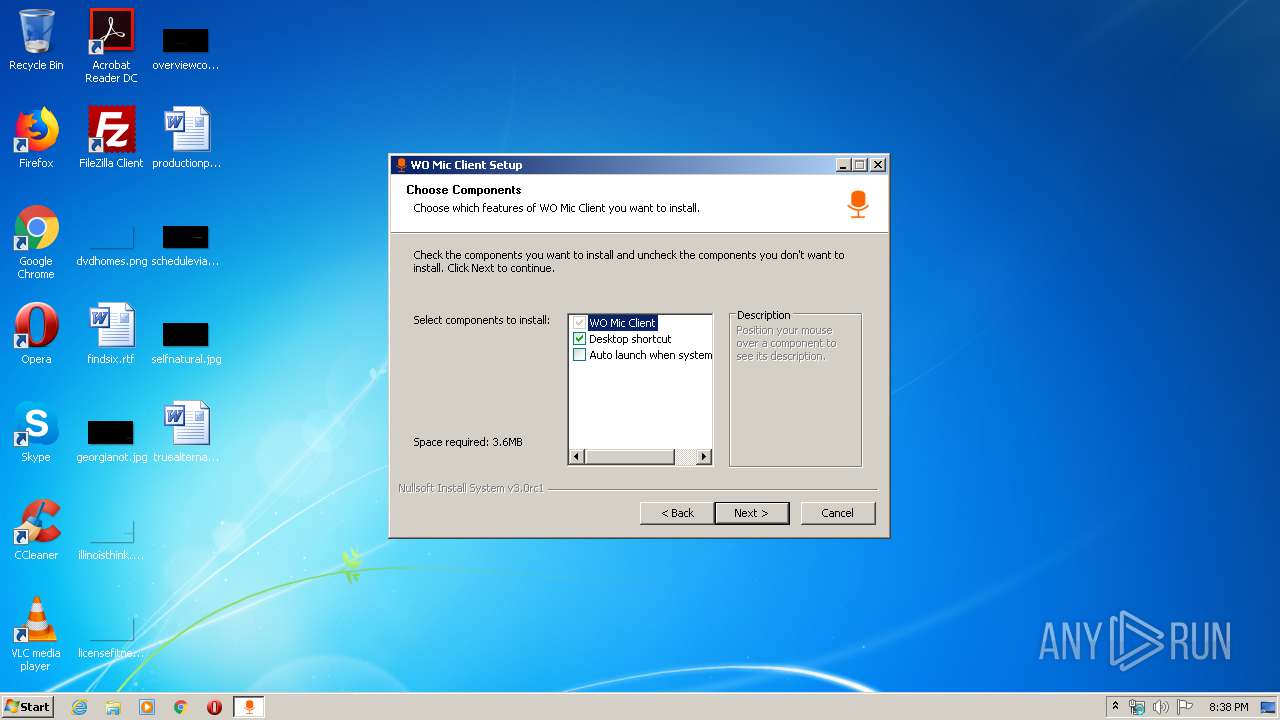
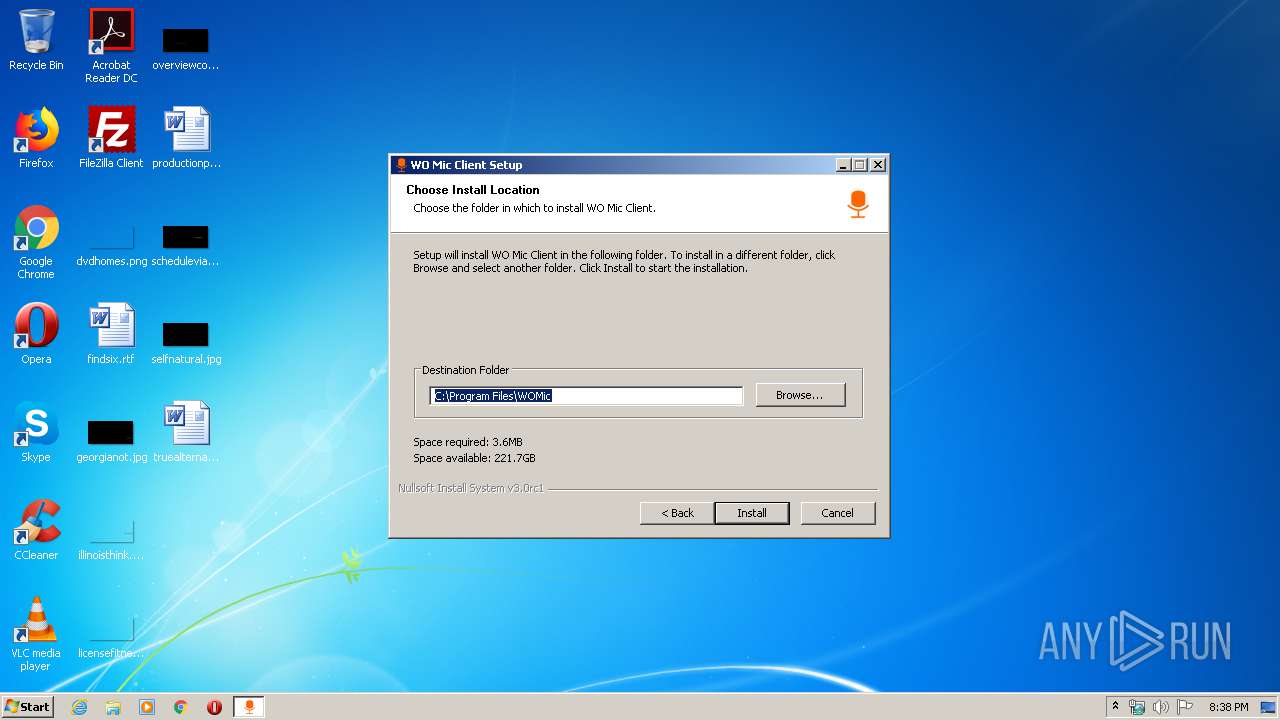
Creates files in the program directory
- wo_mic_client_setup.exe (PID: 2152)
Creates a software uninstall entry
- wo_mic_client_setup.exe (PID: 2152)
Executable content was dropped or overwritten
- wo_mic_client_setup.exe (PID: 2152)
Uses NETSH.EXE for network configuration
- wo_mic_client_setup.exe (PID: 2152)
Creates files in the user directory
- wo_mic_client_setup.exe (PID: 2152)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:03 22:19:02+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x32a0 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Apr-2016 20:19:02 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Apr-2016 20:19:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000637B | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4848 |
.rdata | 0x00008000 | 0x000014B0 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.03367 |
.data | 0x0000A000 | 0x0002AFD8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03955 |
.ndata | 0x00035000 | 0x0002C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00061000 | 0x0000A3A8 | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.74012 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28725 | 1072 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.98899 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.19826 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.37022 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.98002 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70411 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | C:\Windows\system32\netsh.exe advfirewall firewall add rule name="WOMic Media" dir=in action=allow program="C:\Program Files\WOMic\womicclient.exe" enable=yes protocol=UDP | C:\Windows\system32\netsh.exe | — | wo_mic_client_setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2152 | "C:\Users\admin\AppData\Local\Temp\wo_mic_client_setup.exe" | C:\Users\admin\AppData\Local\Temp\wo_mic_client_setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3884 | "C:\Users\admin\AppData\Local\Temp\wo_mic_client_setup.exe" | C:\Users\admin\AppData\Local\Temp\wo_mic_client_setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
421
Read events
342
Write events
79
Delete events
0
Modification events
| (PID) Process: | (2152) wo_mic_client_setup.exe | Key: | HKEY_CURRENT_USER\Software\Wolicheng\WOMic |
| Operation: | write | Name: | bluetoothDevice |
Value: 00:00:00:00:00:00 | |||
| (PID) Process: | (2152) wo_mic_client_setup.exe | Key: | HKEY_CURRENT_USER\Software\Wolicheng\WOMic |
| Operation: | write | Name: | hotSpot |
Value: 192.168.43.1 | |||
| (PID) Process: | (2152) wo_mic_client_setup.exe | Key: | HKEY_CURRENT_USER\Software\Wolicheng\WOMic |
| Operation: | write | Name: | wifiAddr |
Value: 192.168.1.101 | |||
| (PID) Process: | (2152) wo_mic_client_setup.exe | Key: | HKEY_CURRENT_USER\Software\Wolicheng\WOMic |
| Operation: | write | Name: | language |
Value: 1033 | |||
| (PID) Process: | (2152) wo_mic_client_setup.exe | Key: | HKEY_CURRENT_USER\Software\Wolicheng\WOMic |
| Operation: | write | Name: | transport |
Value: 1 | |||
| (PID) Process: | (2152) wo_mic_client_setup.exe | Key: | HKEY_CURRENT_USER\Software\Wolicheng\WOMic |
| Operation: | write | Name: | bufferSize |
Value: 5 | |||
| (PID) Process: | (2152) wo_mic_client_setup.exe | Key: | HKEY_CURRENT_USER\Software\Wolicheng\WOMic |
| Operation: | write | Name: | controlPort |
Value: 8125 | |||
| (PID) Process: | (2152) wo_mic_client_setup.exe | Key: | HKEY_CURRENT_USER\Software\Wolicheng\WOMic |
| Operation: | write | Name: | mediaPort |
Value: 30000 | |||
| (PID) Process: | (2152) wo_mic_client_setup.exe | Key: | HKEY_CURRENT_USER\Software\Wolicheng\WOMic |
| Operation: | write | Name: | x |
Value: 500 | |||
| (PID) Process: | (2152) wo_mic_client_setup.exe | Key: | HKEY_CURRENT_USER\Software\Wolicheng\WOMic |
| Operation: | write | Name: | y |
Value: 200 | |||
Executable files
13
Suspicious files
0
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2152 | wo_mic_client_setup.exe | C:\Users\admin\AppData\Local\Temp\nsa6EB1.tmp\LangDLL.dll | executable | |
MD5:174708997758321CF926B69318C6C3F5 | SHA256:F577B66492E97C7B8BF515398D8DEB745ABAFD74F56FC03E67FCE248EBBEB873 | |||
| 2152 | wo_mic_client_setup.exe | C:\Program Files\WOMic\Resource_en.dll | executable | |
MD5:D8AABB7F6BE00B22539A7F34F0F41FBE | SHA256:354C2351D94828E344E97CFD730E34CC3E2A70D77205548802F66F6DA0739885 | |||
| 2152 | wo_mic_client_setup.exe | C:\Program Files\WOMic\msvcr120.dll | executable | |
MD5:034CCADC1C073E4216E9466B720F9849 | SHA256:86E39B5995AF0E042FCDAA85FE2AEFD7C9DDC7AD65E6327BD5E7058BC3AB615F | |||
| 2152 | wo_mic_client_setup.exe | C:\Users\admin\AppData\Local\Temp\nsa6EB1.tmp\System.dll | executable | |
MD5:0FF2D70CFDC8095EA99CA2DABBEC3CD7 | SHA256:982C5FB7ADA7D8C9BC3E419D1C35DA6F05BC5DD845940C179AF3A33D00A36A8B | |||
| 2152 | wo_mic_client_setup.exe | C:\Program Files\WOMic\Resource_ru.dll | executable | |
MD5:9634B511026B01831F12E1B4B49B1DED | SHA256:E79BE0C91BA577D6701B18870D519E0E4D3E2877B4B8A50D09BDC04720C2F4C2 | |||
| 2152 | wo_mic_client_setup.exe | C:\Program Files\WOMic\Resource_cn.dll | executable | |
MD5:73EA6E7E930C79B9C94B08E758191CBB | SHA256:C2B61BD2EE5C2C1E1D89A5A2BFF96707A1F84A17F893059966B64B8F88B7FD99 | |||
| 2152 | wo_mic_client_setup.exe | C:\Program Files\WOMic\adb.exe | executable | |
MD5:884242FB6CBBEC1F7711B946EF669E0E | SHA256:65210CB4139672B53ACAA2222B1005D036B0B02C437AA47E0E7B616FAB0E2F6F | |||
| 2152 | wo_mic_client_setup.exe | C:\Program Files\WOMic\uninstall.exe | executable | |
MD5:007340C9A07F30973B172B26C26F544C | SHA256:06A2F7894C475B24C55B64B66DB710D247AA231C06B72A5D24871FD562ACDC34 | |||
| 2152 | wo_mic_client_setup.exe | C:\Users\admin\AppData\Local\Temp\nsa6EB1.tmp\nsDialogs.dll | executable | |
MD5:D6C3DD680C6467D07D730255D0EE5D87 | SHA256:AEDB5122C12037BCF5C79C2197D1474E759CF47C67C37CDB21CF27428854A55B | |||
| 2152 | wo_mic_client_setup.exe | C:\Users\admin\AppData\Local\Temp\nsa6EB1.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report