| download: | p7vSetup.exe |
| Full analysis: | https://app.any.run/tasks/01fb2c95-f2bf-4b49-8b76-9c88d8923c53 |
| Verdict: | Malicious activity |
| Analysis date: | September 13, 2018, 13:20:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C72B198119505DCE4F1D5F41C344F505 |
| SHA1: | 5EA2BAB64073D5637F30FDC417775F2D0B3D6A34 |
| SHA256: | 354525A06614991765918151766D5A69AD363B6FD04C9F9B3D702E7B488A1979 |
| SSDEEP: | 49152:l/Pm552DbVlYh7u2ol/i9GZjhDxaxAnav3BeiiHFZXzMLMUhyLlp2KJa3/KKV:Rg52tuHCq90NqfBUHNUhyaL3Cm |
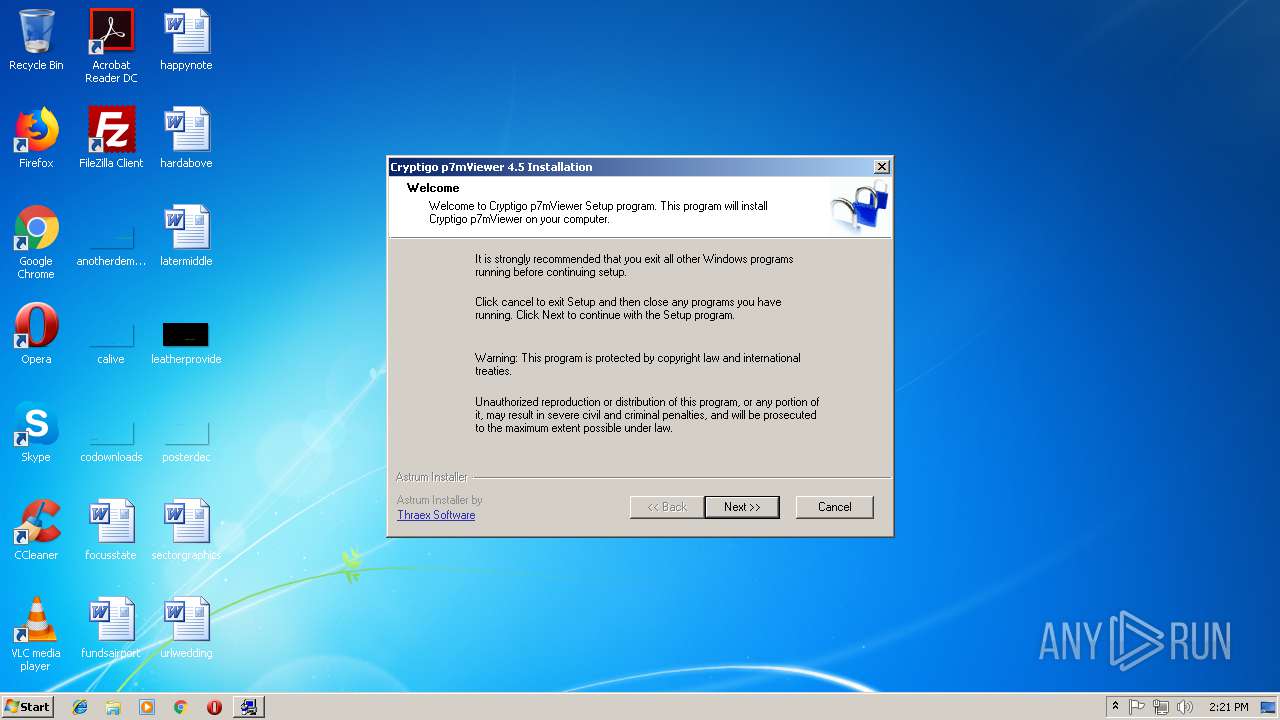
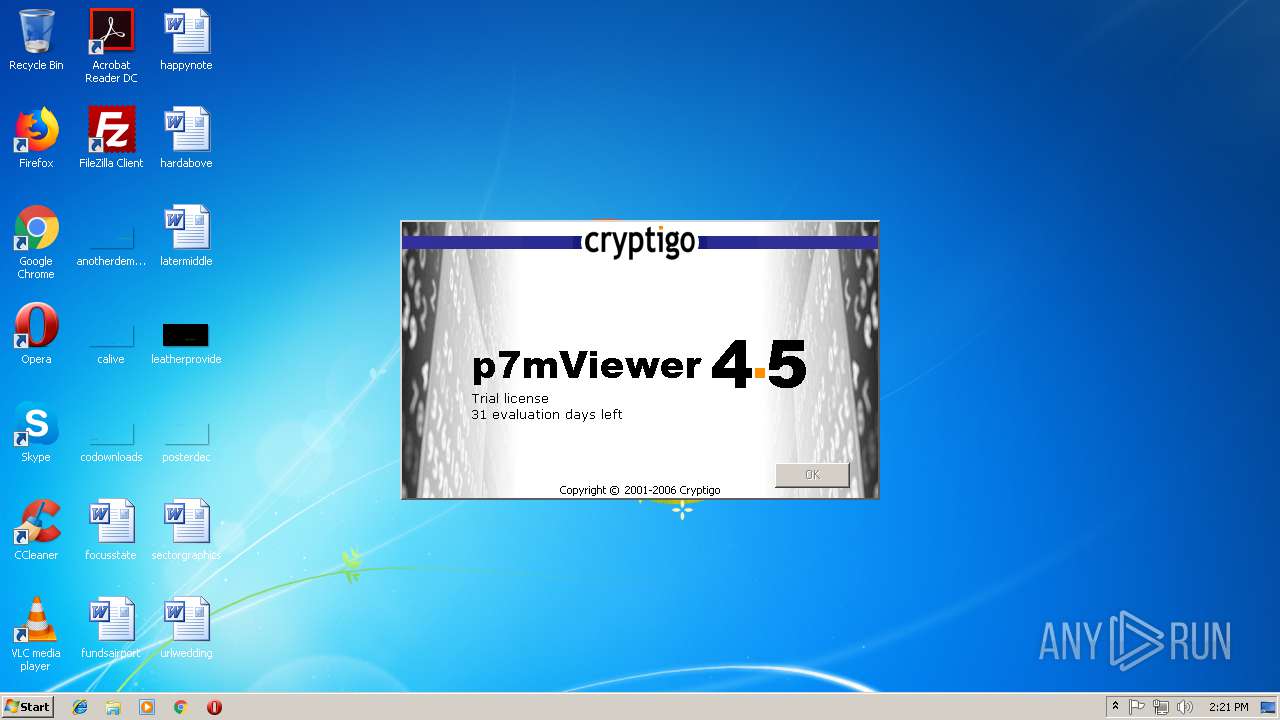
MALICIOUS
Loads dropped or rewritten executable
- p7vSetup.exe (PID: 3164)
Application was dropped or rewritten from another process
- p7mViewer.exe (PID: 3348)
- p7mViewer.exe (PID: 4008)
SUSPICIOUS
Executable content was dropped or overwritten
- p7vSetup.exe (PID: 3164)
Creates COM task schedule object
- p7vSetup.exe (PID: 3164)
Modifies the open verb of a shell class
- p7mViewer.exe (PID: 3348)
Reads internet explorer settings
- p7mViewer.exe (PID: 4008)
Creates files in the user directory
- p7mViewer.exe (PID: 4008)
Creates files in the program directory
- p7vSetup.exe (PID: 3164)
Reads Internet Cache Settings
- p7mViewer.exe (PID: 4008)
INFO
Dropped object may contain Bitcoin addresses
- p7vSetup.exe (PID: 3164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (33) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (23.9) |
| .exe | | | Win64 Executable (generic) (21.2) |
| .scr | | | Windows screen saver (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:02:12 21:19:14+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 156672 |
| InitializedDataSize: | 359424 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x24d1a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Feb-2004 20:19:14 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 12-Feb-2004 20:19:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000262D5 | 0x00026400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59877 |
.rdata | 0x00028000 | 0x000021F8 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76488 |
.data | 0x0002B000 | 0x00054818 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.49681 |
.rsrc | 0x00080000 | 0x00000FB0 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.30928 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89965 | 696 | UNKNOWN | Finnish - Finland | RT_MANIFEST |
2 | 2.59572 | 308 | UNKNOWN | Finnish - Finland | RT_CURSOR |
18 | 3.20217 | 240 | UNKNOWN | Finnish - Finland | RT_DIALOG |
101 | 2.16096 | 20 | UNKNOWN | Finnish - Finland | RT_GROUP_ICON |
114 | 3.41672 | 480 | UNKNOWN | Finnish - Finland | RT_DIALOG |
127 | 3.4905 | 468 | UNKNOWN | Finnish - Finland | RT_BITMAP |
138 | 2.69978 | 166 | UNKNOWN | Finnish - Finland | RT_DIALOG |
152 | 1.91924 | 20 | UNKNOWN | Finnish - Finland | RT_GROUP_CURSOR |
154 | 3.02015 | 182 | UNKNOWN | Finnish - Finland | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
WINMM.dll |
comdlg32.dll |
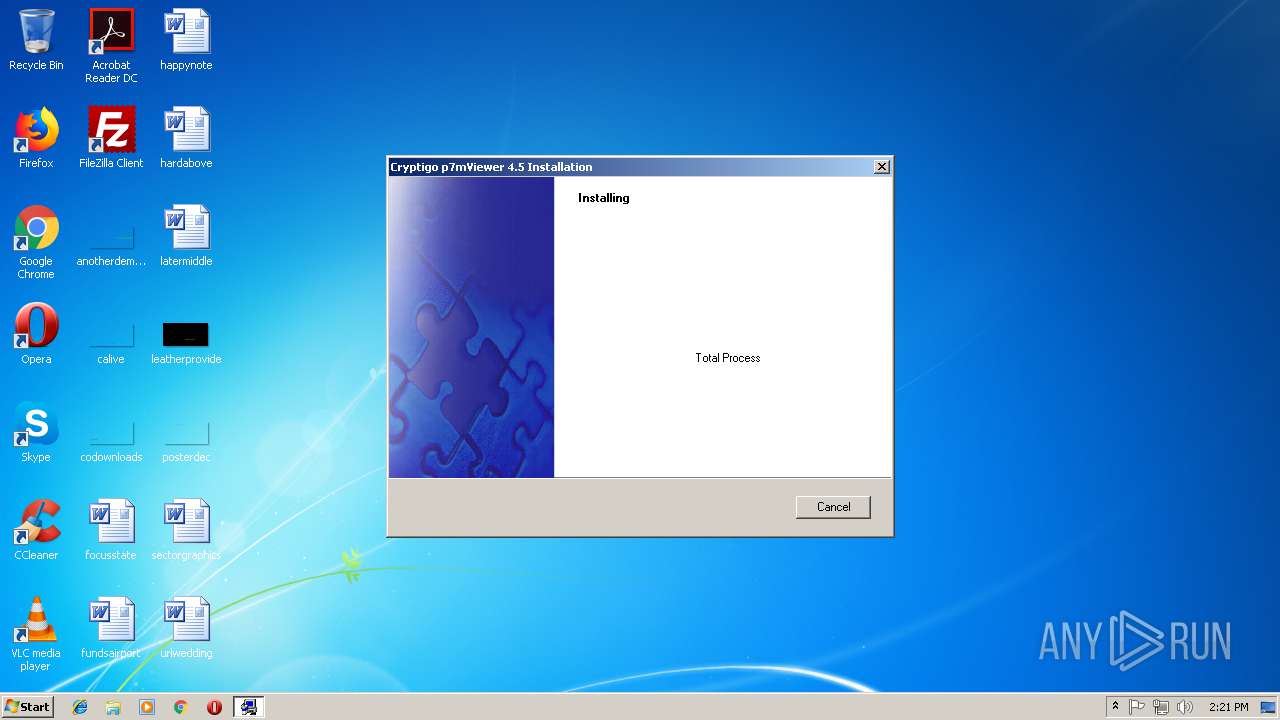
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
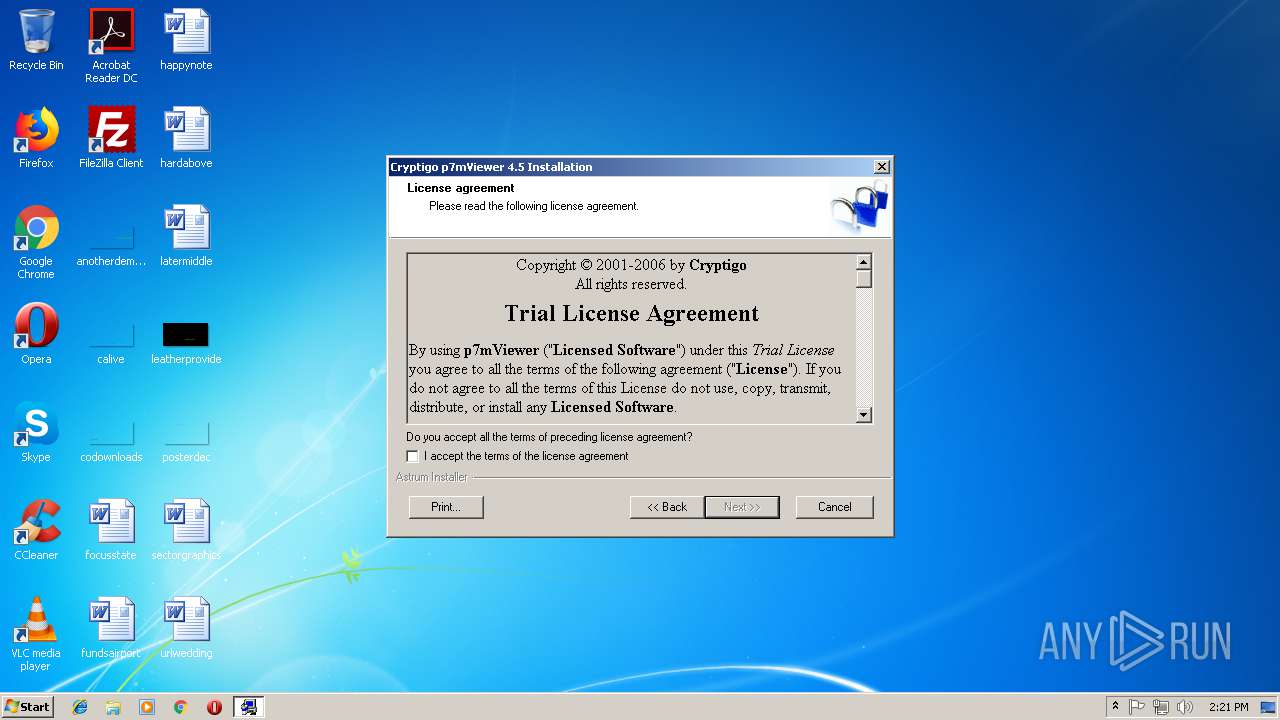
| 624 | "C:\Users\admin\AppData\Local\Temp\p7vSetup.exe" | C:\Users\admin\AppData\Local\Temp\p7vSetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Local\Temp\p7vSetup.exe" | C:\Users\admin\AppData\Local\Temp\p7vSetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
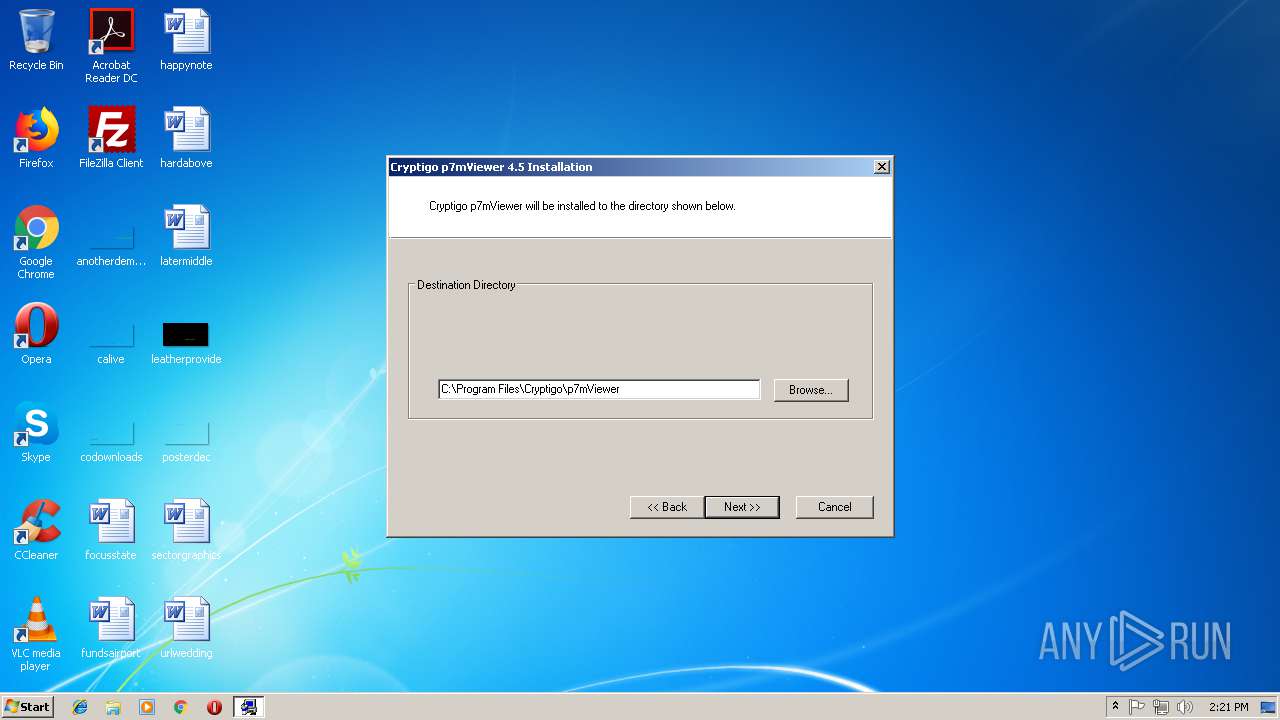
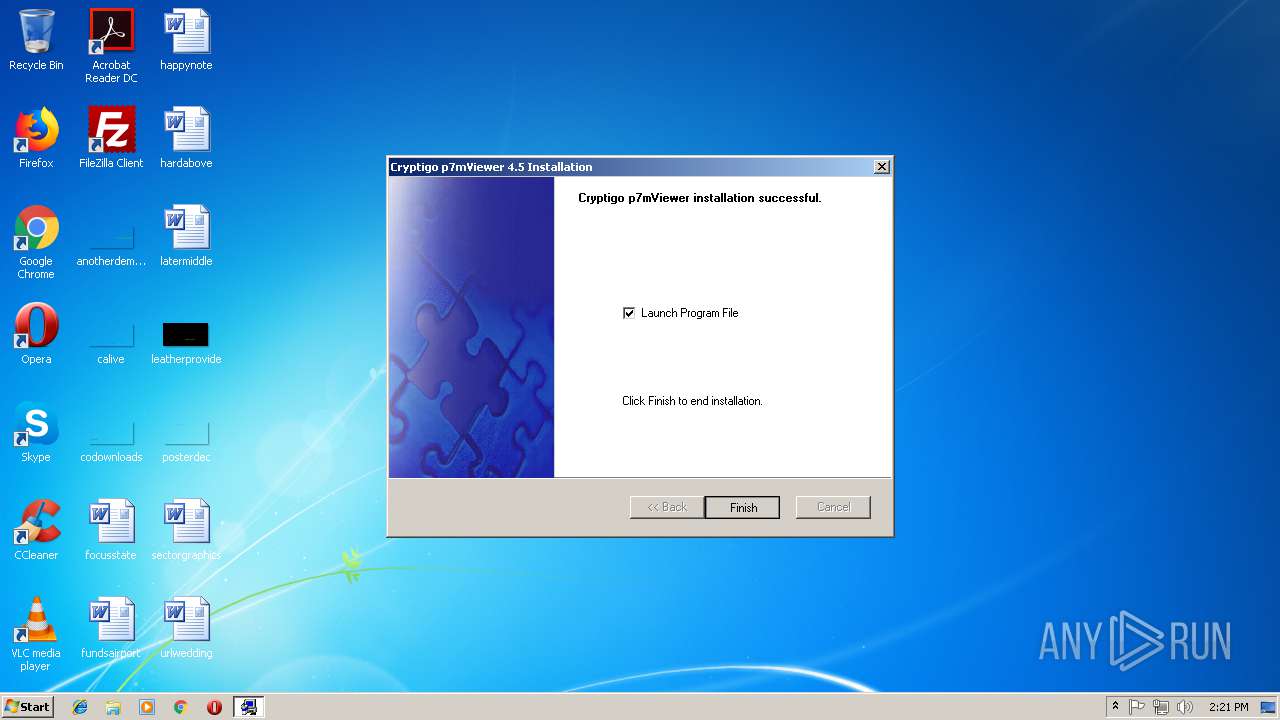
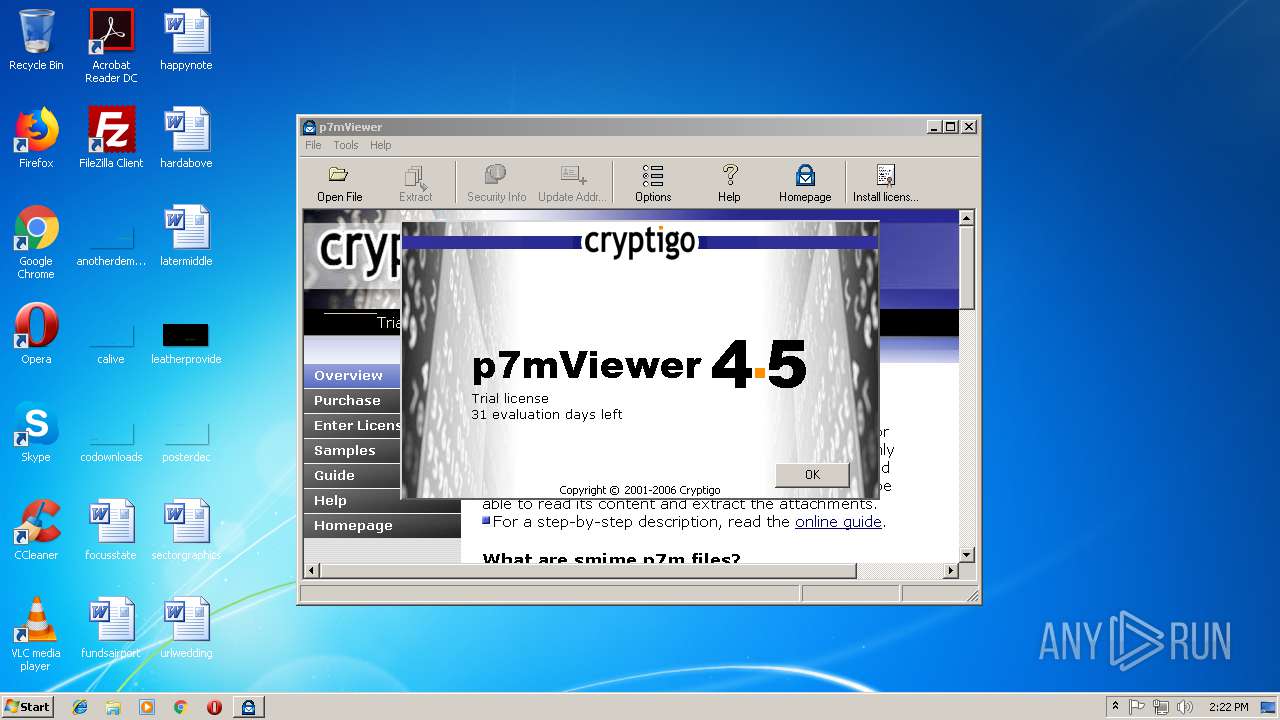
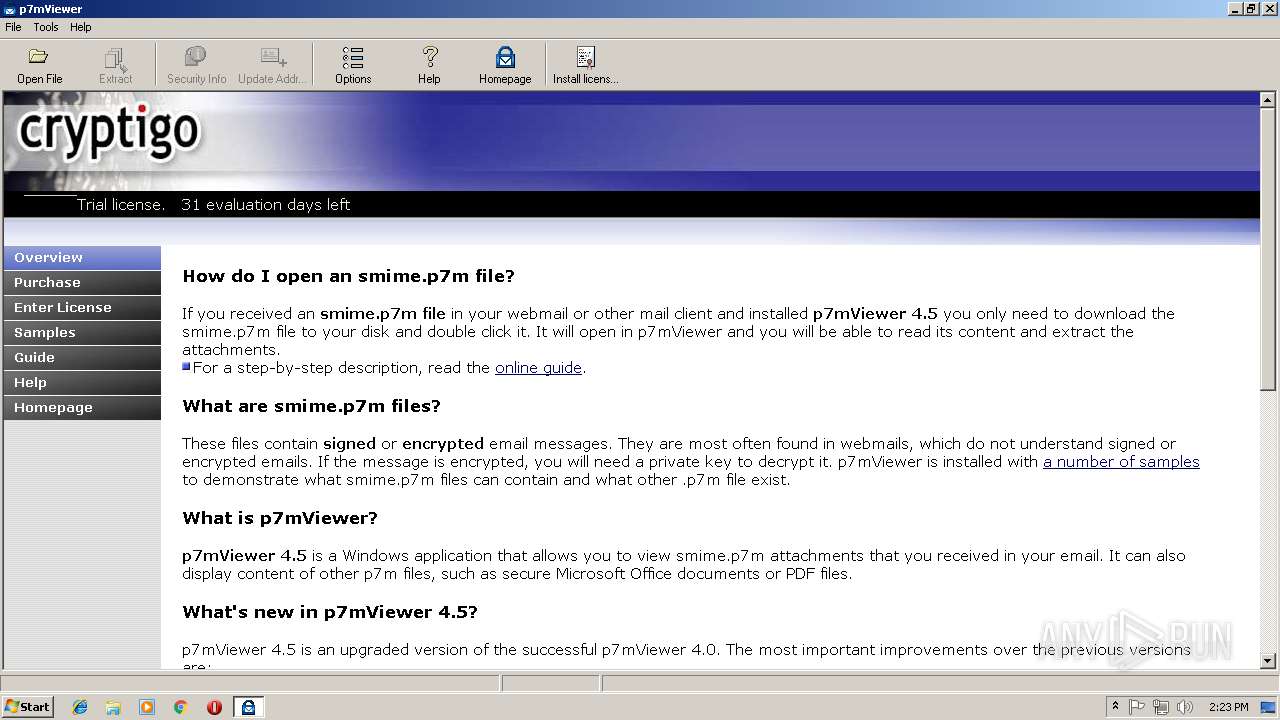
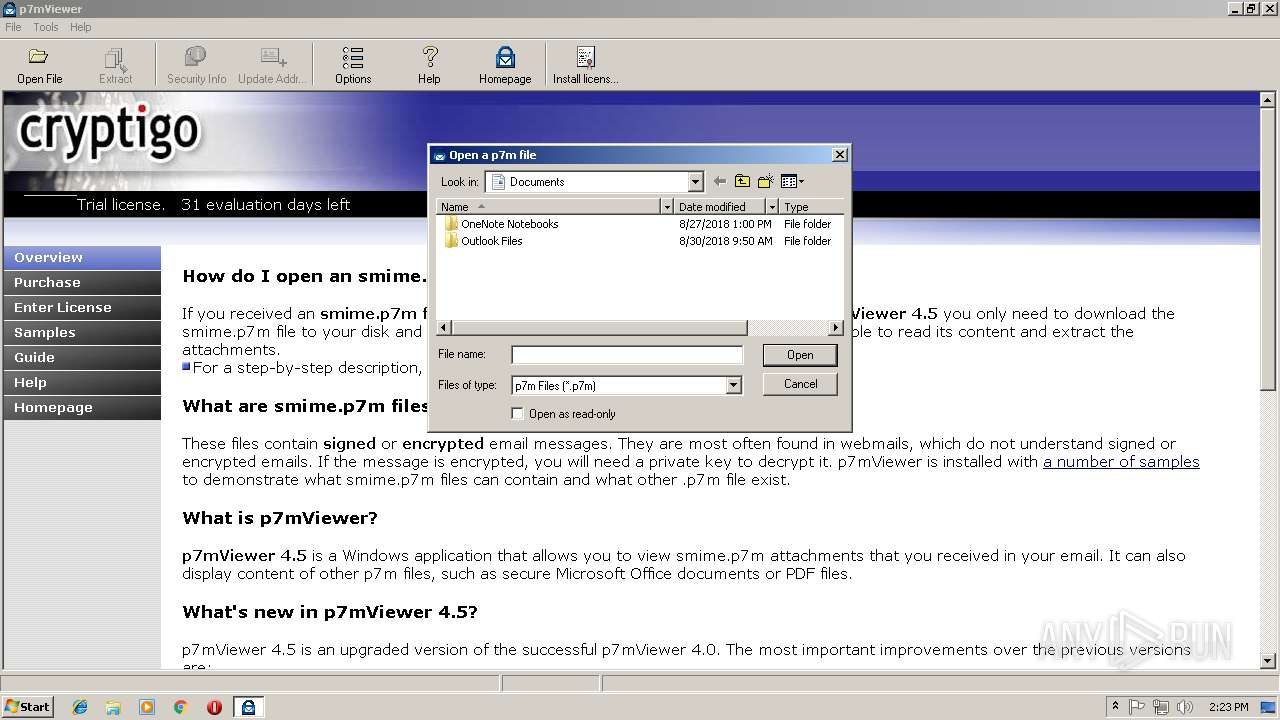
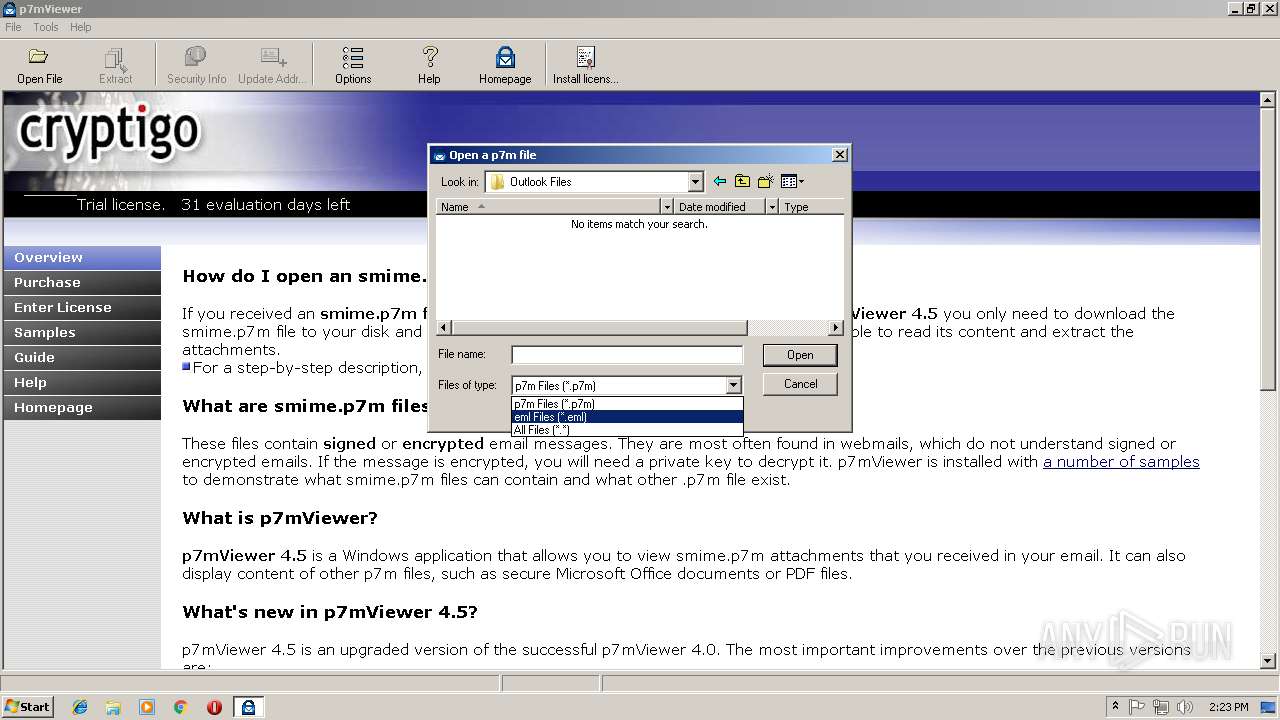
| 3348 | "C:\Program Files\Cryptigo\p7mViewer\p7mViewer.exe" -Install | C:\Program Files\Cryptigo\p7mViewer\p7mViewer.exe | — | p7vSetup.exe | |||||||||||
User: admin Company: Cryptigo Integrity Level: HIGH Description: p7mViewer Exit code: 0 Version: 4.6.16.1286 Modules
| |||||||||||||||
| 4008 | "C:\Program Files\Cryptigo\p7mViewer\p7mViewer.exe " | C:\Program Files\Cryptigo\p7mViewer\p7mViewer.exe | — | p7vSetup.exe | |||||||||||
User: admin Company: Cryptigo Integrity Level: HIGH Description: p7mViewer Exit code: 0 Version: 4.6.16.1286 Modules
| |||||||||||||||
Total events
955
Read events
758
Write events
196
Delete events
1
Modification events
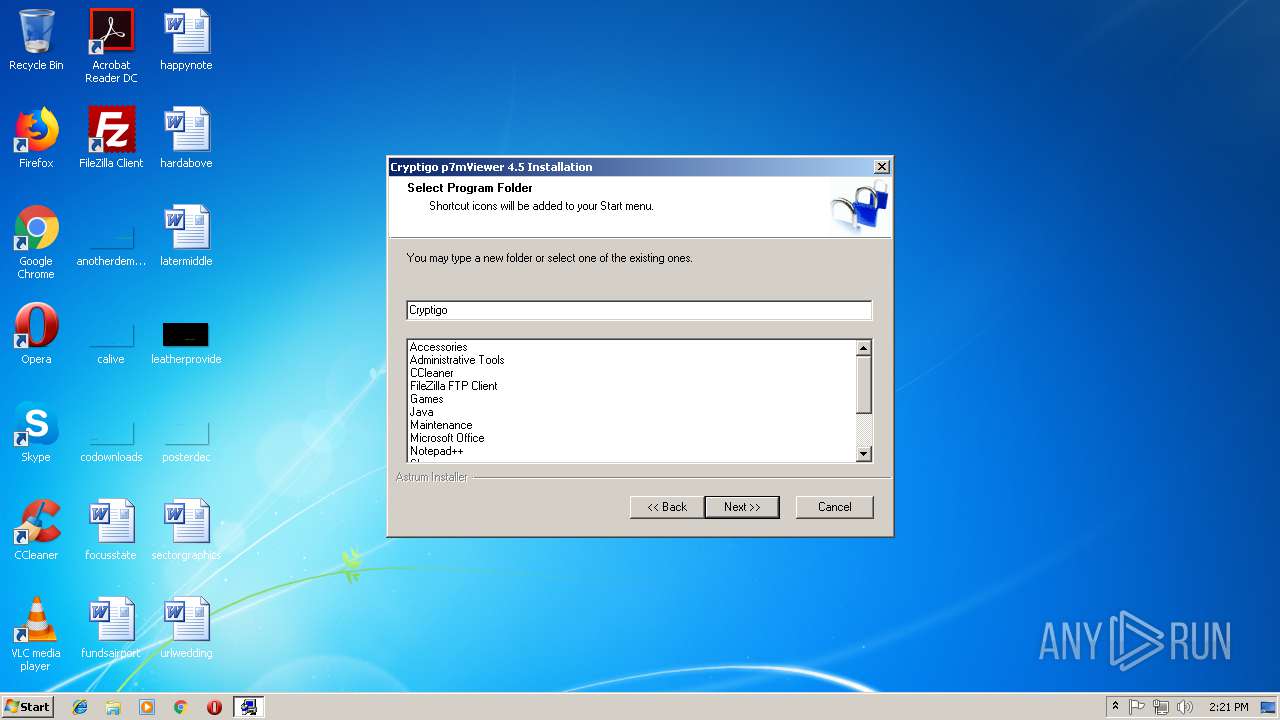
| (PID) Process: | (3164) p7vSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Applications\p7mViewer.exe |
| Operation: | write | Name: | |
Value: | |||
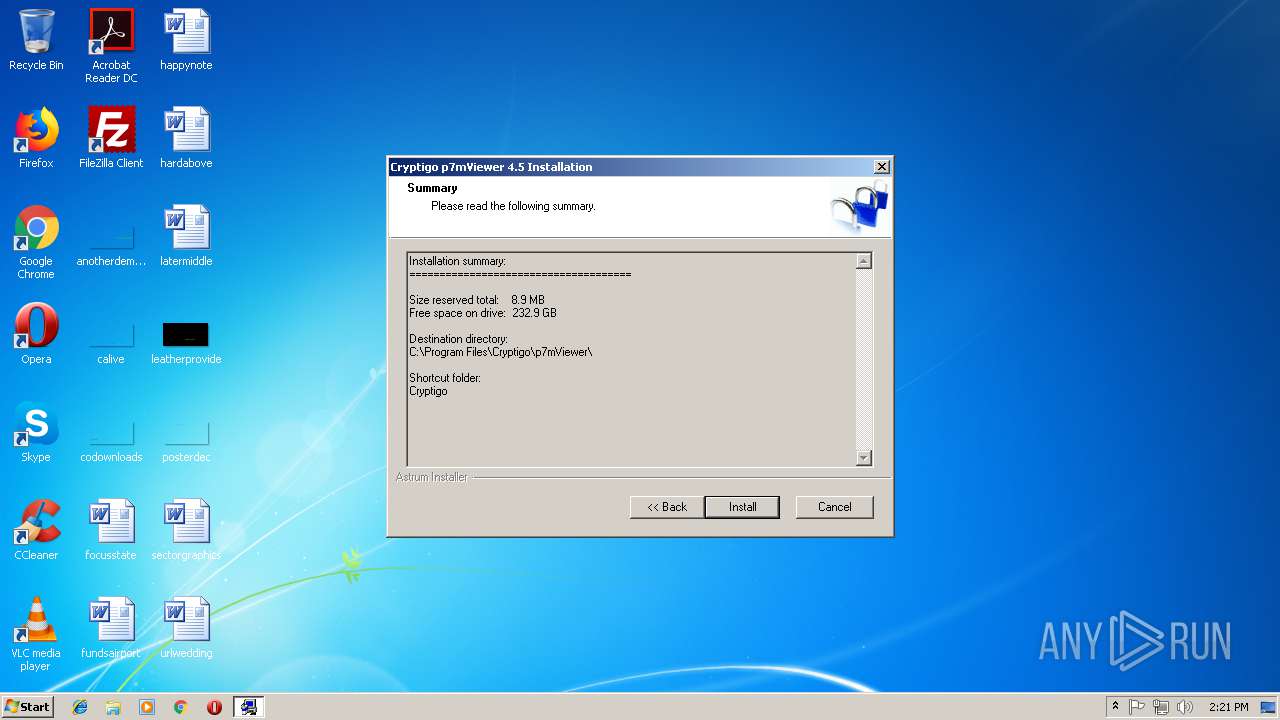
| (PID) Process: | (3164) p7vSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Applications\p7mViewer.exe\install |
| Operation: | write | Name: | Directory |
Value: C:\Program Files\Cryptigo\p7mViewer | |||
| (PID) Process: | (3164) p7vSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Applications\p7mViewer.exe\install |
| Operation: | write | Name: | Version |
Value: 4.5 | |||
| (PID) Process: | (3164) p7vSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Applications\p7mViewer.exe\install |
| Operation: | write | Name: | Uninstaller |
Value: C:\Program Files\Cryptigo\p7mViewer\Uninstall.exe | |||
| (PID) Process: | (3164) p7vSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files\Cryptigo\p7mViewer\CryptigoUtils.ocx |
Value: 1 | |||
| (PID) Process: | (3164) p7vSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{E4EC6663-E433-4C76-AA4A-7643CC487513} |
| Operation: | write | Name: | |
Value: Shell.Utils | |||
| (PID) Process: | (3164) p7vSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{E4EC6663-E433-4C76-AA4A-7643CC487513}\InprocServer32 |
| Operation: | write | Name: | |
Value: %SystemRoot%\system32\shell32.dll | |||
| (PID) Process: | (3164) p7vSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{E4EC6663-E433-4C76-AA4A-7643CC487513}\ProgId |
| Operation: | write | Name: | |
Value: Shell.Utils | |||
| (PID) Process: | (3164) p7vSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{E4EC6663-E433-4C76-AA4A-7643CC487513}\TypeLib |
| Operation: | write | Name: | |
Value: {1B8E5FE3-6A3C-4CD2-BF40-569170474137} | |||
| (PID) Process: | (3164) p7vSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{E4EC6663-E433-4C76-AA4A-7643CC487513}\Version |
| Operation: | write | Name: | |
Value: 1.0 | |||
Executable files
7
Suspicious files
11
Text files
15
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3164 | p7vSetup.exe | C:\Users\admin\AppData\Local\Temp\aaiw1094594.bmp | image | |
MD5:0D2449D8B0683FC2153B5A62ABD70358 | SHA256:E31E7FA84F4D4FB178327C5A87705DE0E2246409E67D3D9FBA906F2020B76D75 | |||
| 3164 | p7vSetup.exe | C:\Program Files\Cryptigo\p7mViewer\smime\scenarios\A1-OPEN-View.pvc | xml | |
MD5:06D4F466EA296E92B29575D2278367D1 | SHA256:F4A3EEBB4D4BED9766B70F42E0D0FD7E8A99F6EC440A8C34717CAD5272DBBDEA | |||
| 3164 | p7vSetup.exe | C:\Program Files\Cryptigo\p7mViewer\samples\sample.doc.p7m | text | |
MD5:8B830A528E334C869229F798A86F5800 | SHA256:3C297164A9AB4439AEEB76236F70EAD8909561866ACD3DCB5B4FFB01686E2036 | |||
| 3164 | p7vSetup.exe | C:\Users\admin\AppData\Local\Temp\aaiw1094596.bmp | image | |
MD5:4CF7475E76CB7892A79CC4DA8DAC51A5 | SHA256:EA7860C41776B228B3C6E8286A237933C15A015451CDC78DE891C1CA86FF080F | |||
| 3164 | p7vSetup.exe | C:\Program Files\Cryptigo\p7mViewer\smime\scenarios\B2-EXTRACTTO-Extract to here.pvc | xml | |
MD5:3C92B736503374F092EA41731C31365E | SHA256:79F85D153E1A8B28A5A7BEF55770C3EF61C89F564A8637BDEFED52E1C8B3D571 | |||
| 3164 | p7vSetup.exe | C:\Program Files\Cryptigo\p7mViewer\samples\sample_pdf.p7m | binary | |
MD5:8FB510759F38CA6EB2BDF2FBA3157583 | SHA256:1AF5FF294FDB2F33248C2BE835266F4FECEBD742FCB7A348B10488BD0DDC4D2B | |||
| 3164 | p7vSetup.exe | C:\Program Files\Cryptigo\p7mViewer\smime\scenarios\C1-CONFIGURE-Configure....pvc | xml | |
MD5:091EF7849A21DE3ADE372957EE37F7F3 | SHA256:CB99C788BA9B31B976912AEF7C996535EFE48CADD216E62715A0D44CB209C7F8 | |||
| 3164 | p7vSetup.exe | C:\Program Files\Cryptigo\p7mViewer\samples\sample.xls.p7m | binary | |
MD5:B7082B0458560CA1988FA141E720D38A | SHA256:CF8DB66DCAD4C36A8CB821D17DBBE35058B3D6B8F0DC5712478F06257F4EADD4 | |||
| 3164 | p7vSetup.exe | C:\Program Files\Cryptigo\p7mViewer\samples\sample_jpg.p7m | text | |
MD5:AE4FA5A5A0FB968DD804A941B1C9641B | SHA256:B6F9215C2CE38543652F7FD82F6A1153B39439CC33EF42AC59B29ECDFBBA5897 | |||
| 3164 | p7vSetup.exe | C:\Users\admin\AppData\Local\Temp\aiw1094593.bmp | image | |
MD5:E765FF8C8C4F07FC1565539B7A0D9EA8 | SHA256:2A70254F17EF98B982174BD93E18B37894482B04693AB09E8A70D052337E8651 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report