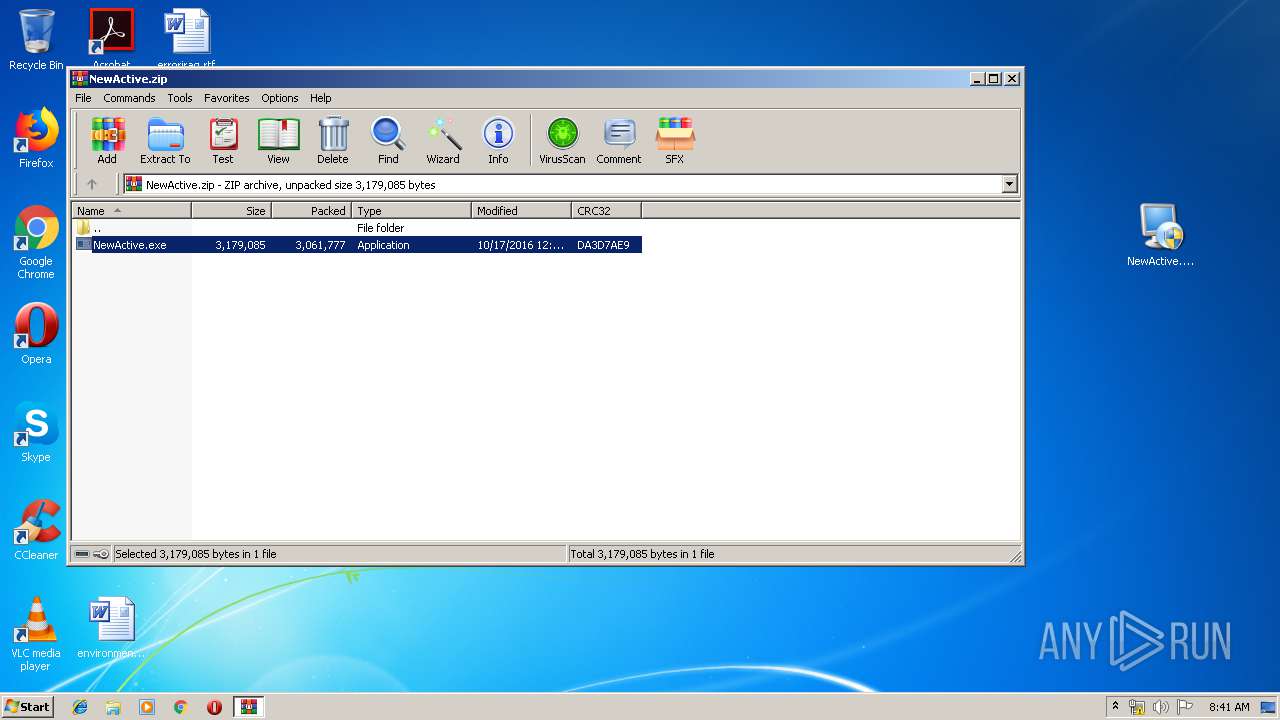
| File name: | NewActive.zip |
| Full analysis: | https://app.any.run/tasks/6a3f5e3d-fd39-4d2b-92ef-0209f595ef9d |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2019, 08:40:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 59A62272DB17DF7651CB711955445303 |
| SHA1: | 8A55EF7AFDEBDCBEFA25D9729D1F827268B1A5BD |
| SHA256: | 3530BA709463E0BEF251292F79924308DC4DF00CA467A94066C08AABFA27A12C |
| SSDEEP: | 49152:7DxRZspHSqB1Vek4FR0152hNSZOIctZiei9yNWsNPvCwI36czoCzkxc+FD6w:7DLZsHt1s7L0152WZZZONWs1C6Orzkxr |
MALICIOUS
Application was dropped or rewritten from another process
- NewActive.exe (PID: 2452)
- irsetup.exe (PID: 1800)
- NewActive.exe (PID: 3460)
Registers / Runs the DLL via REGSVR32.EXE
- irsetup.exe (PID: 1800)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3516)
SUSPICIOUS
Executable content was dropped or overwritten
- irsetup.exe (PID: 1800)
- NewActive.exe (PID: 3460)
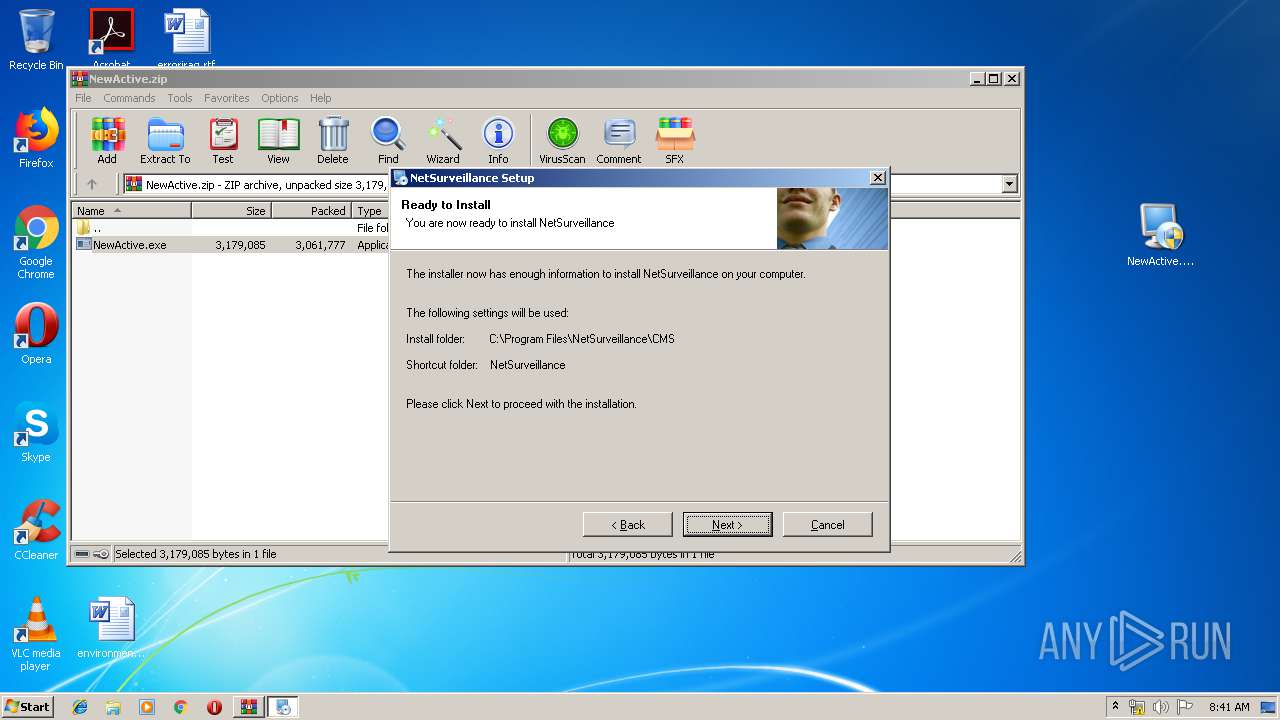
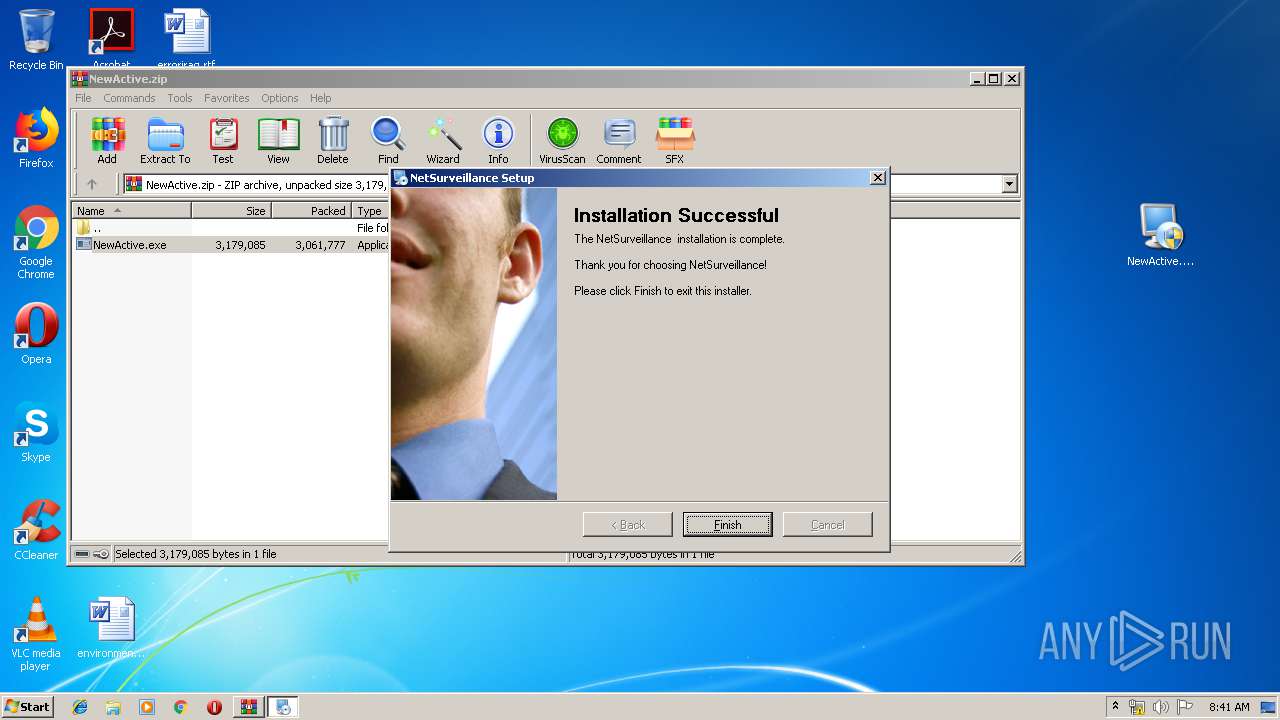
Creates a software uninstall entry
- irsetup.exe (PID: 1800)
Creates files in the program directory
- irsetup.exe (PID: 1800)
INFO
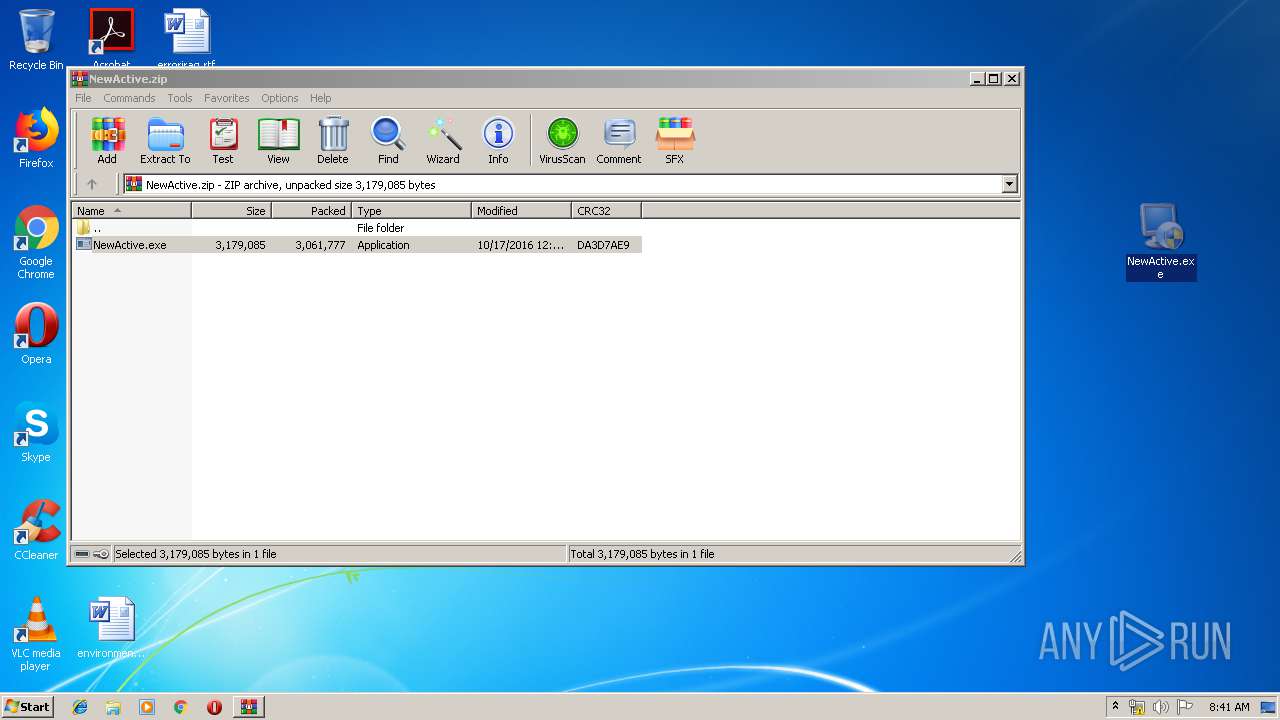
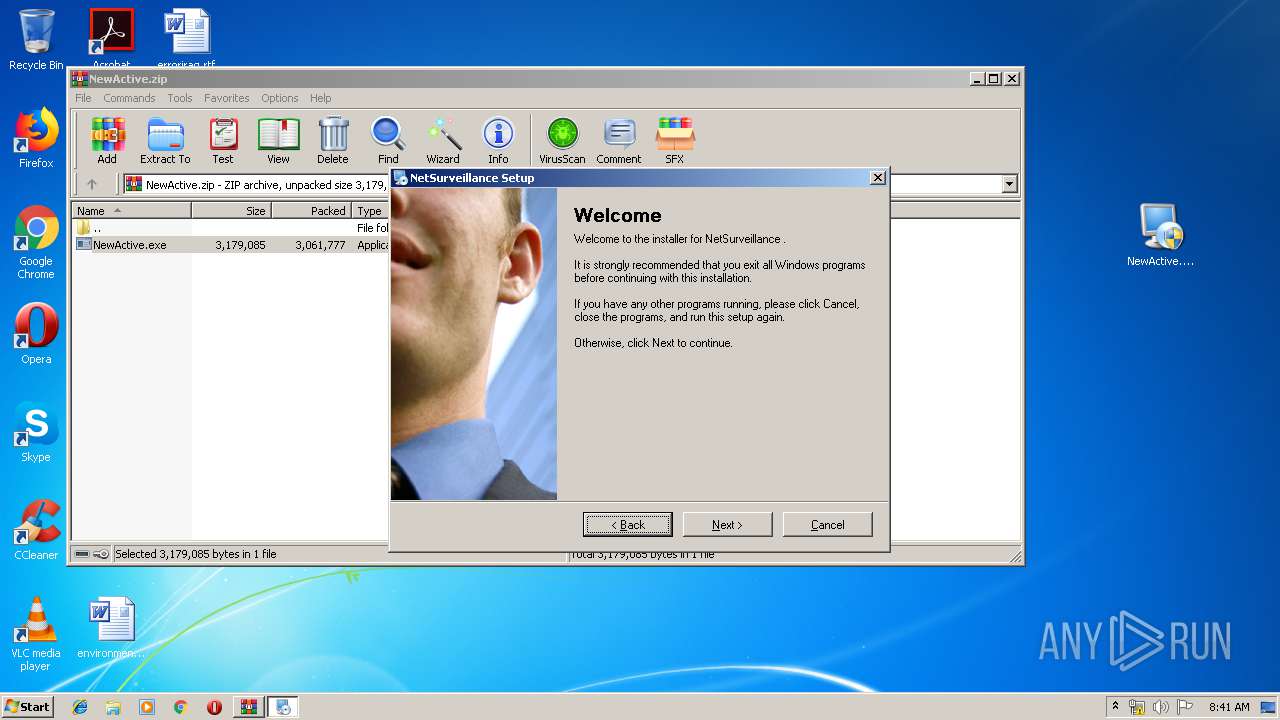
Manual execution by user
- NewActive.exe (PID: 2452)
- NewActive.exe (PID: 3460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
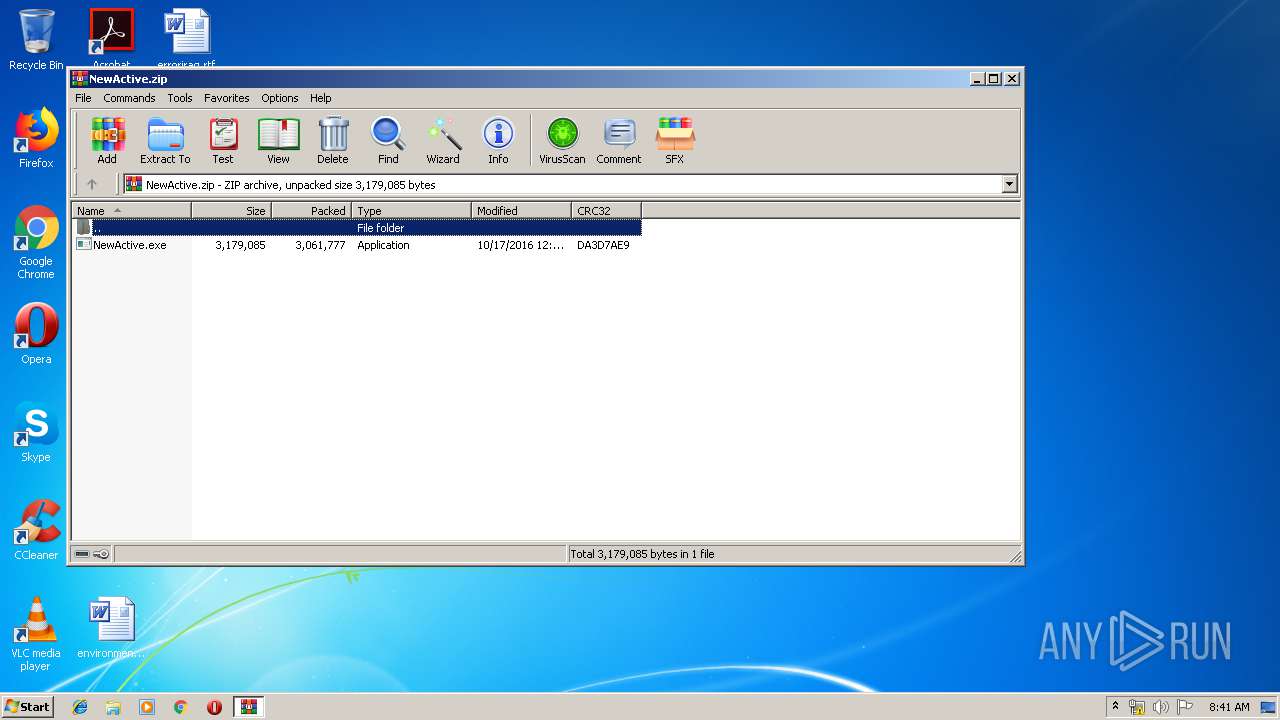
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2016:10:17 14:57:14 |
| ZipCRC: | 0xda3d7ae9 |
| ZipCompressedSize: | 3061777 |
| ZipUncompressedSize: | 3179085 |
| ZipFileName: | NewActive.exe |
Total processes
42
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
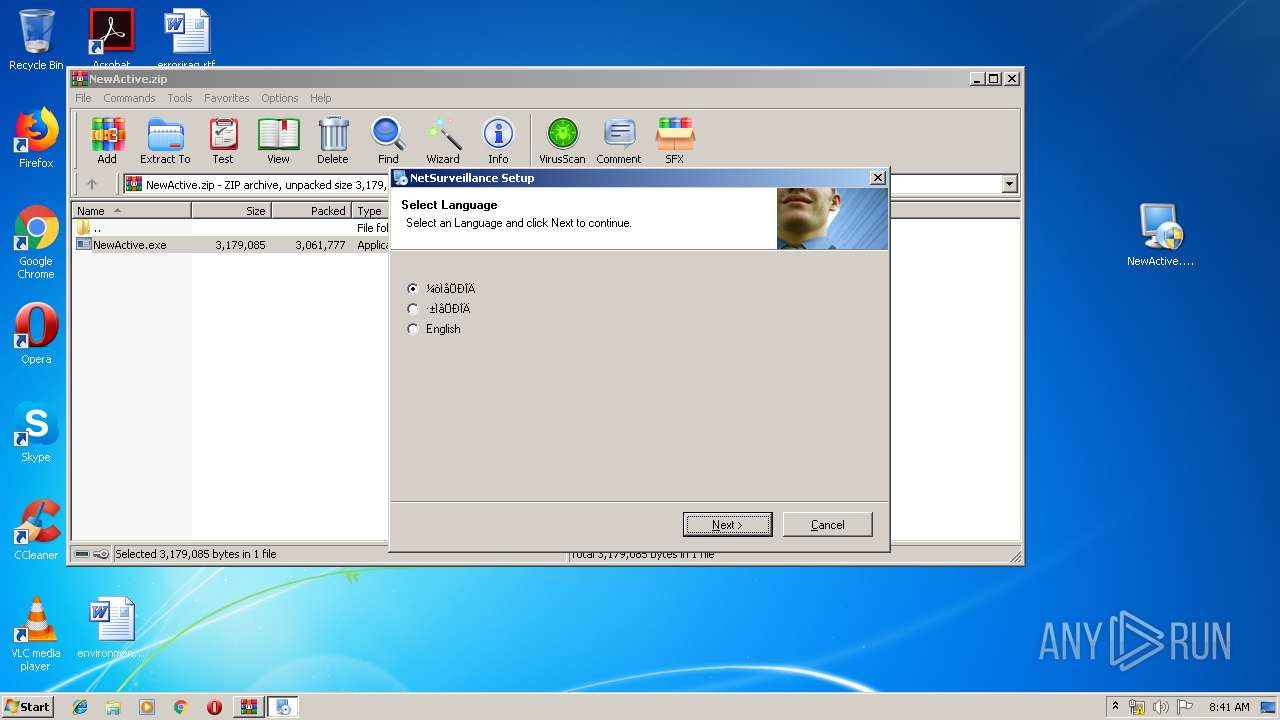
| 1800 | __IRAOFF:520716 "__IRAFN:C:\Users\admin\Desktop\NewActive.exe" | C:\Users\admin\AppData\Local\Temp\_ir_sf7_temp_0\irsetup.exe | NewActive.exe | ||||||||||||
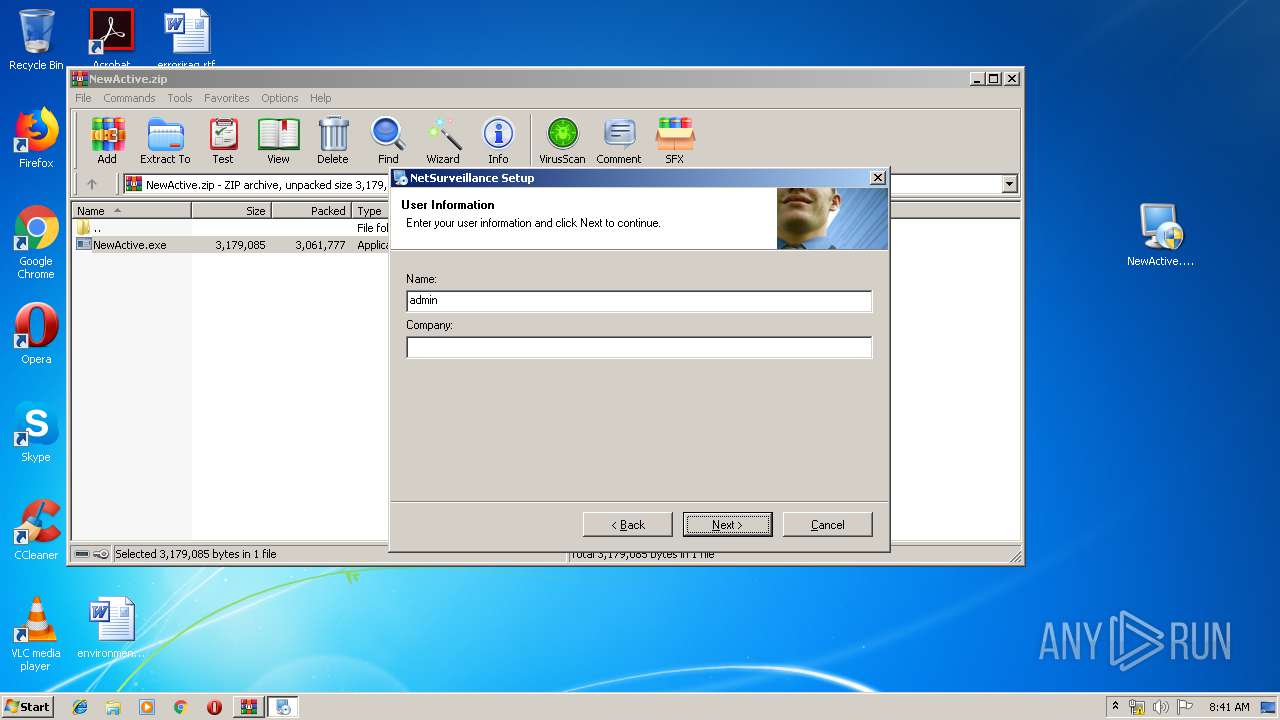
User: admin Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 7.0.1.0 Modules
| |||||||||||||||
| 2452 | "C:\Users\admin\Desktop\NewActive.exe" | C:\Users\admin\Desktop\NewActive.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Application Exit code: 3221226540 Version: 7.0.1.0 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\NewActive.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3460 | "C:\Users\admin\Desktop\NewActive.exe" | C:\Users\admin\Desktop\NewActive.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 7.0.1.0 Modules
| |||||||||||||||
| 3516 | "C:\Windows\System32\regsvr32.exe" /s "C:\Program Files\NetSurveillance\CMS\web.ocx" | C:\Windows\System32\regsvr32.exe | — | irsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
664
Read events
616
Write events
48
Delete events
0
Modification events
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\NewActive.zip | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1800) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | DisplayName |
Value: NetSurveillance | |||
| (PID) Process: | (1800) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
Executable files
14
Suspicious files
2
Text files
50
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2612.27260\NewActive.exe | — | |
MD5:— | SHA256:— | |||
| 1800 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf7_temp_0\irsetup.dat | — | |
MD5:— | SHA256:— | |||
| 1800 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\Uninstall\uni95C.tmp | — | |
MD5:— | SHA256:— | |||
| 1800 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\Uninstall\uninstall.dat | binary | |
MD5:8E0B1A4D14453FE5BBB676195024DA53 | SHA256:C84395DBC0C5C2BCE92FE289F8F605E782557081A9D9BFCD7446BE72155E1F95 | |||
| 1800 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\Uninstall\uninstall.xml | text | |
MD5:817AE69B988AB393DA69132C70B2B901 | SHA256:8F575ADCE29DC46A76E90BBB31C8143E6A3A438D7616507A87DFCFBA64E1EAB5 | |||
| 1800 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\H264Play.dll | executable | |
MD5:3282BC08059381512A242F2526ED46F9 | SHA256:48156255E5E14B72E41BFC85D8C481C04F3C5322A262238D9CA631E442A0763E | |||
| 1800 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\dlg_right.bmp | image | |
MD5:43D2127525BDF1D889FB3446AB89C08C | SHA256:BFE6B2D6E7A25E8CA44A09476CCDFAC4AA87EC77D88CC39CE0FC2B389AA601C2 | |||
| 1800 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf7_temp_0\IRIMG2.JPG | image | |
MD5:8D774F6D54492A39B8C10832BDFE44FA | SHA256:F68D37B790E727228A0846996024F7624CDDD463730CD087123A4BD9B3ED4389 | |||
| 1800 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\plcb_back.JPG | image | |
MD5:FBDF0F4FBD0CB907EA2DCB393BF64113 | SHA256:0D29ABBC125CA0A19A61671B4722E8597D16A44E9F80095E425FD27E2A56D1A0 | |||
| 1800 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\mp_channel.JPG | image | |
MD5:0C47ED6CD47314B14314E876DC08DE0A | SHA256:2F6ED1882504D41908EF5E4106A392257010F24D2094D534457E5FA4C3A967D5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report