| File name: | bug_bounty_gui_original.exe |
| Full analysis: | https://app.any.run/tasks/dc147c1e-4893-46c6-afad-a3e72ae3a3c9 |
| Verdict: | Malicious activity |
| Analysis date: | May 31, 2025, 18:10:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 26267FE68B08CC7FB8AD3BC52EBCF66D |
| SHA1: | E9DA03920DB9932EBBC69E2698A604FAD65F1381 |
| SHA256: | 352F860F4A45070A5659F1109491E8428132879D078BA9E58FD4D7CF807DCC8F |
| SSDEEP: | 98304:wCYzBJltevRa7MC2xumzy722pACb9RvOYVAYwVf9TtYw9pk9dbXtpEKLuIgqNT9s:I7I4Df6EEZ5KAOznv/L5Bug |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- bug_bounty_gui_original.exe (PID: 2104)
The process drops C-runtime libraries
- bug_bounty_gui_original.exe (PID: 2104)
Process drops python dynamic module
- bug_bounty_gui_original.exe (PID: 2104)
Executable content was dropped or overwritten
- bug_bounty_gui_original.exe (PID: 2104)
There is functionality for taking screenshot (YARA)
- bug_bounty_gui_original.exe (PID: 2104)
- bug_bounty_gui_original.exe (PID: 5248)
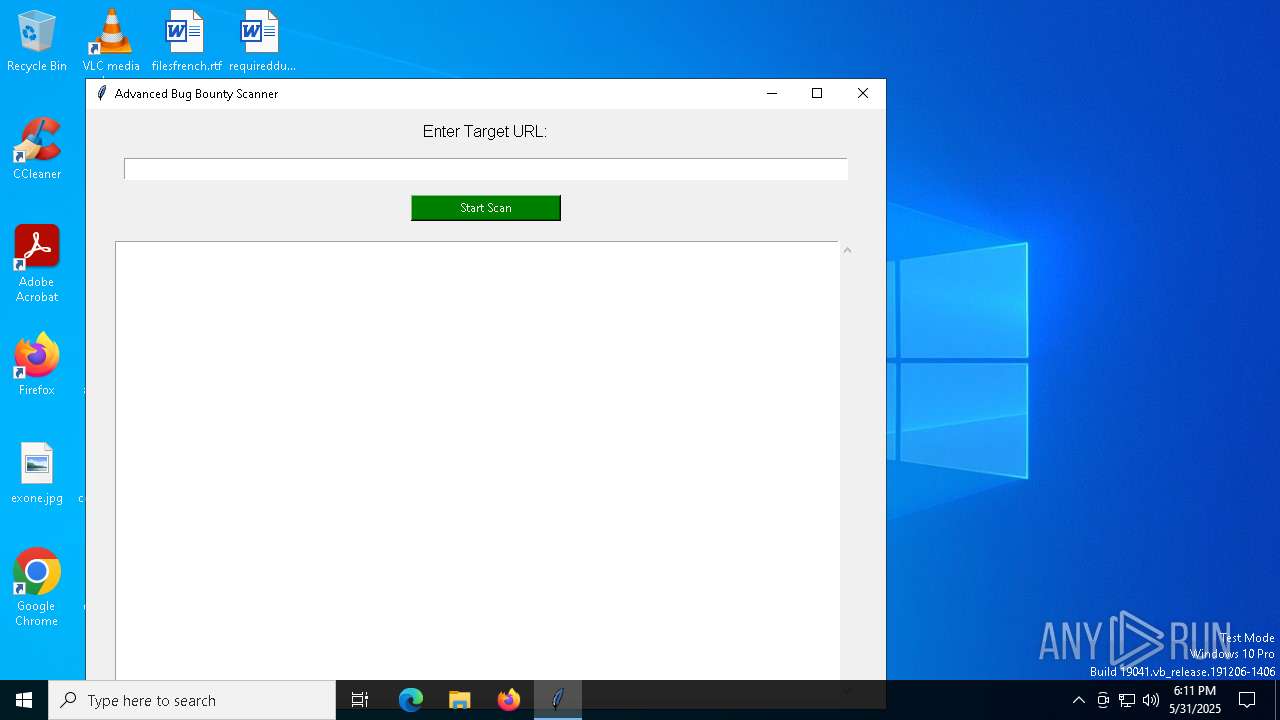
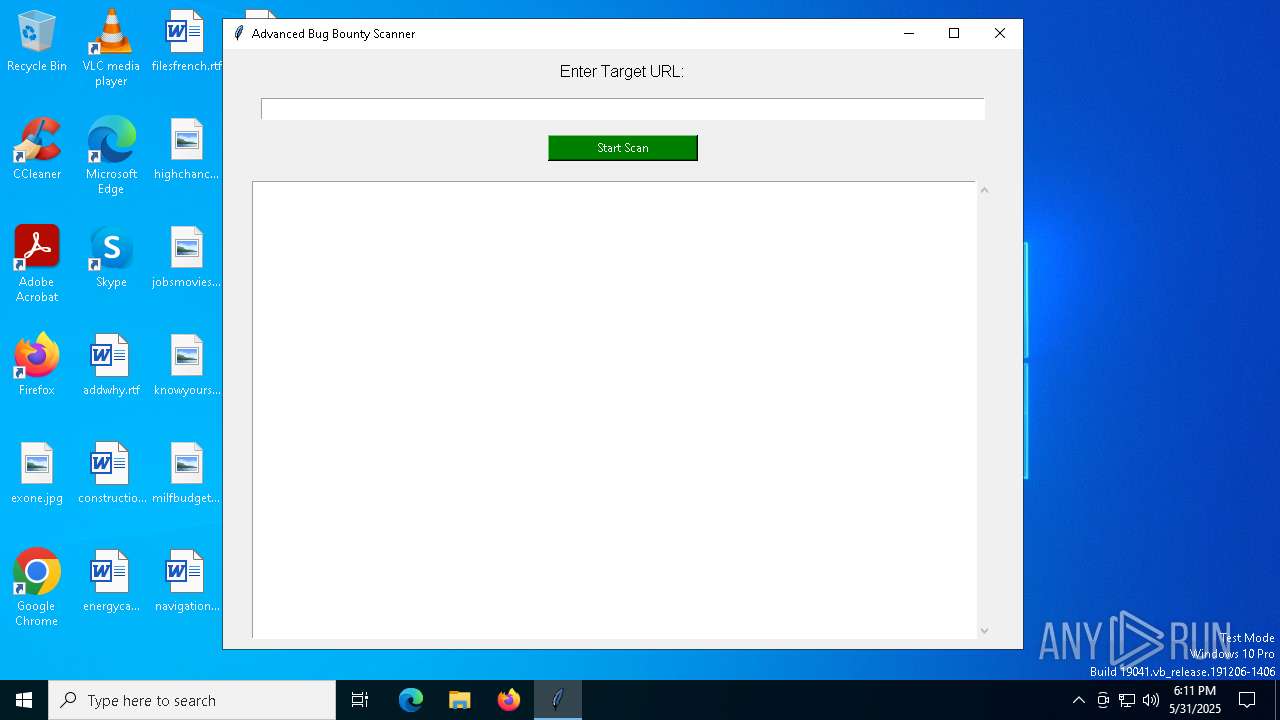
Application launched itself
- bug_bounty_gui_original.exe (PID: 2104)
Loads Python modules
- bug_bounty_gui_original.exe (PID: 5248)
INFO
Reads the computer name
- bug_bounty_gui_original.exe (PID: 2104)
- bug_bounty_gui_original.exe (PID: 5248)
The sample compiled with english language support
- bug_bounty_gui_original.exe (PID: 2104)
Checks supported languages
- bug_bounty_gui_original.exe (PID: 2104)
- bug_bounty_gui_original.exe (PID: 5248)
Create files in a temporary directory
- bug_bounty_gui_original.exe (PID: 2104)
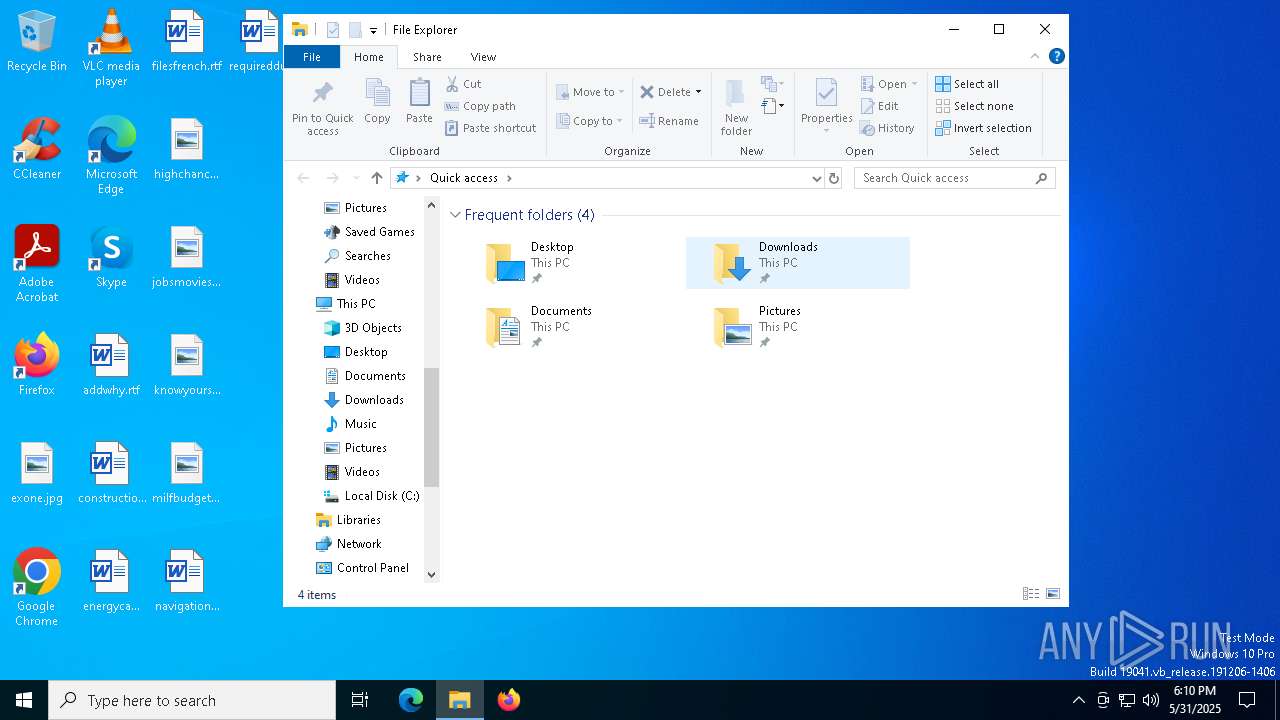
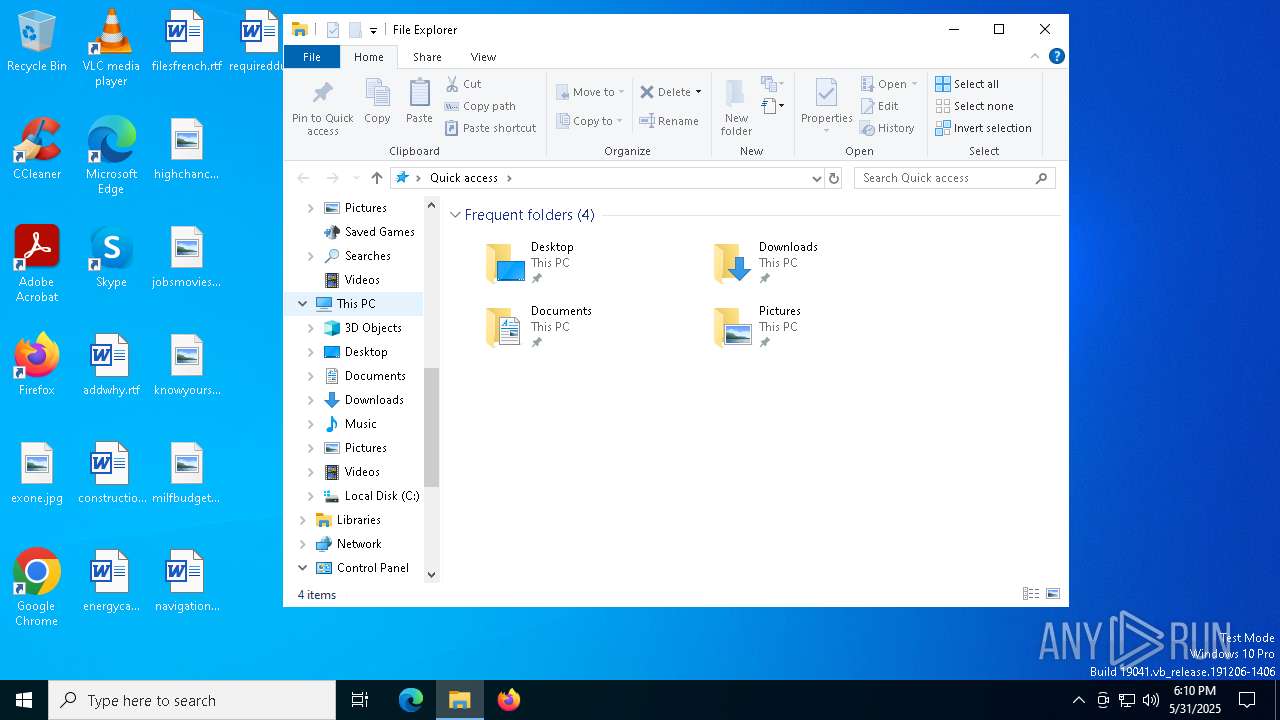
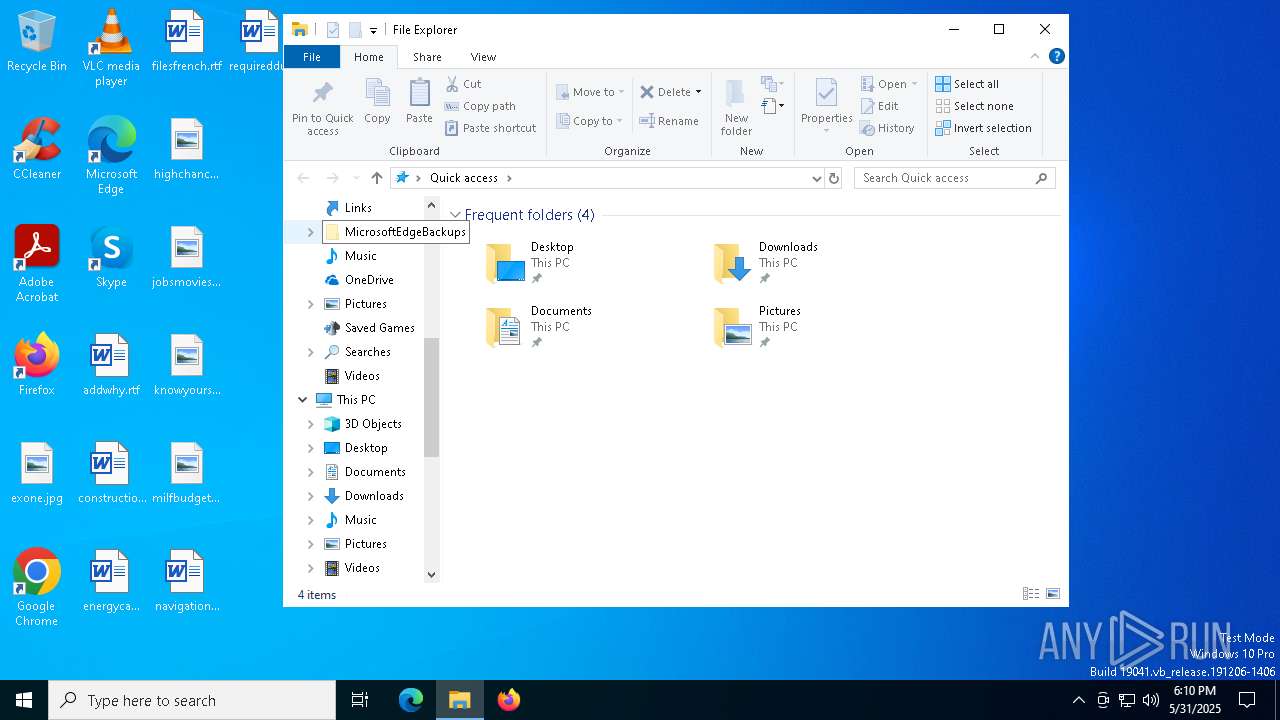
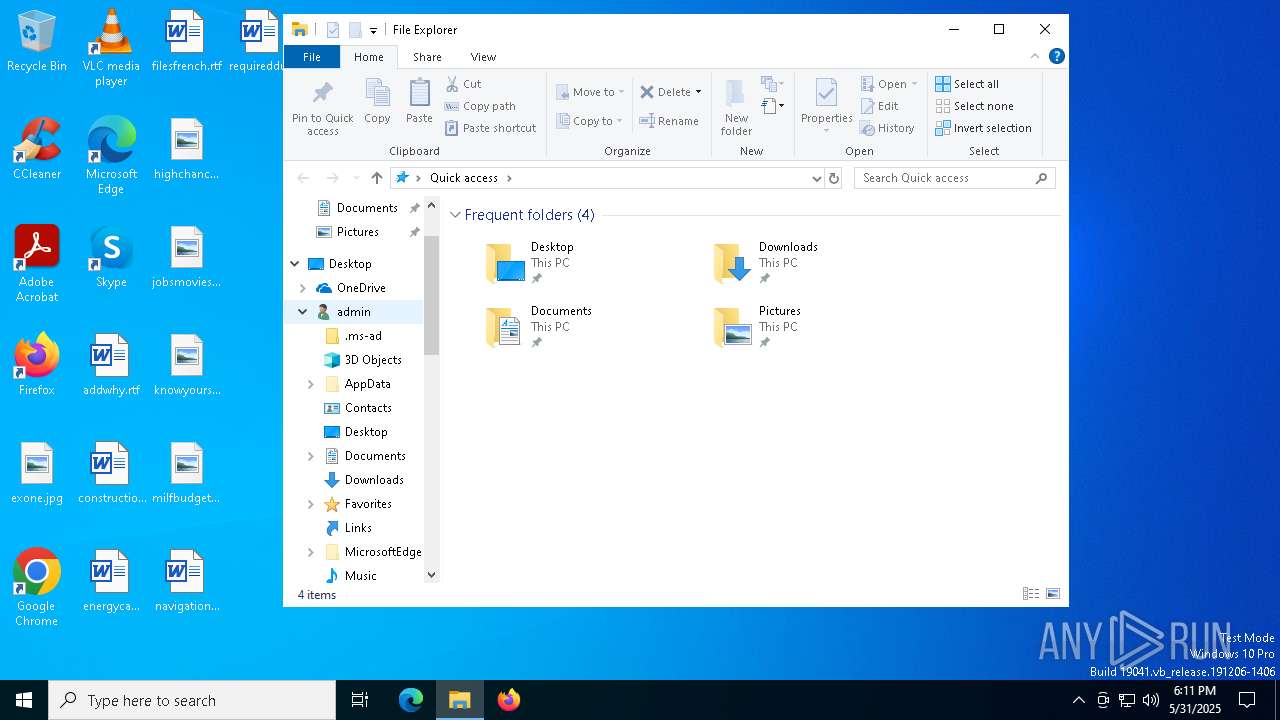
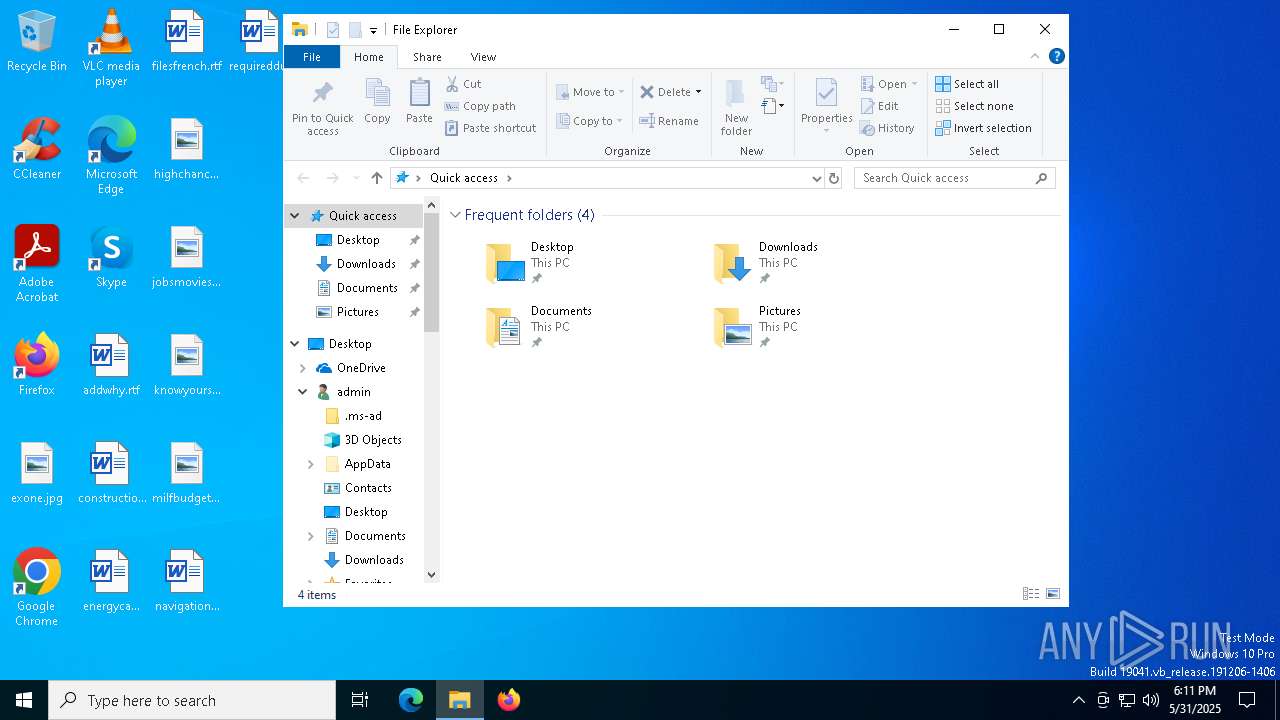
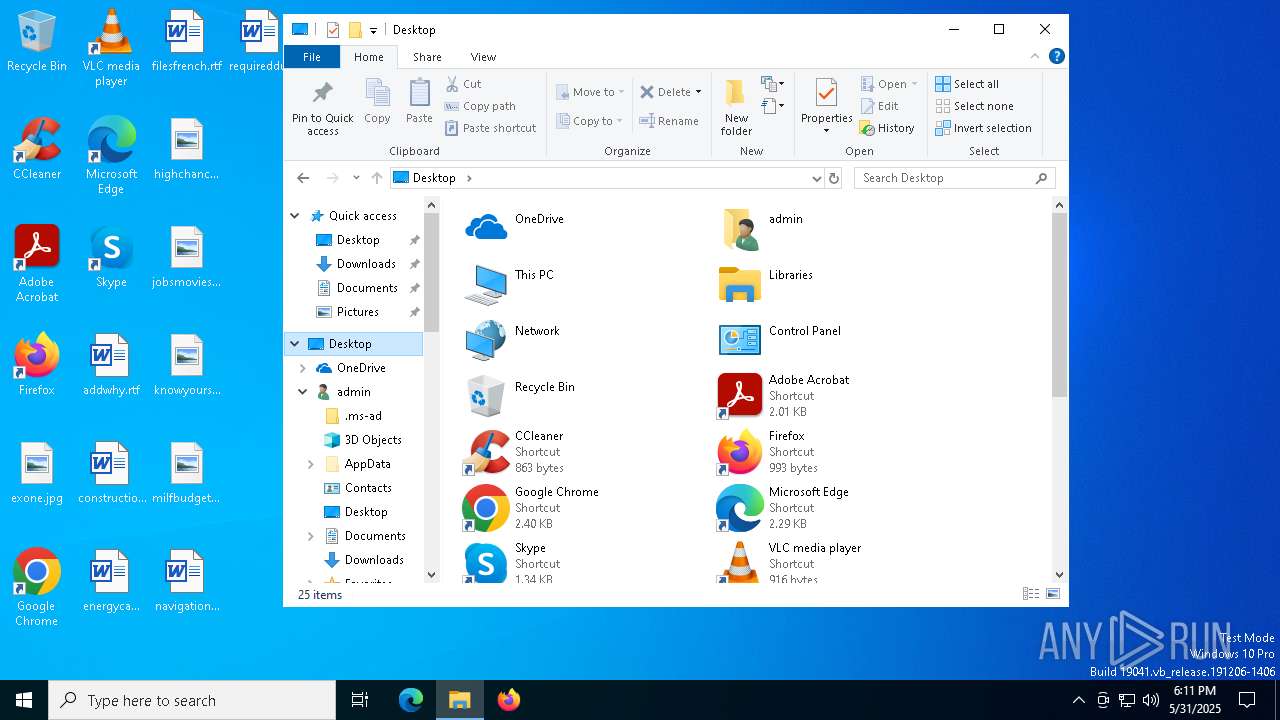
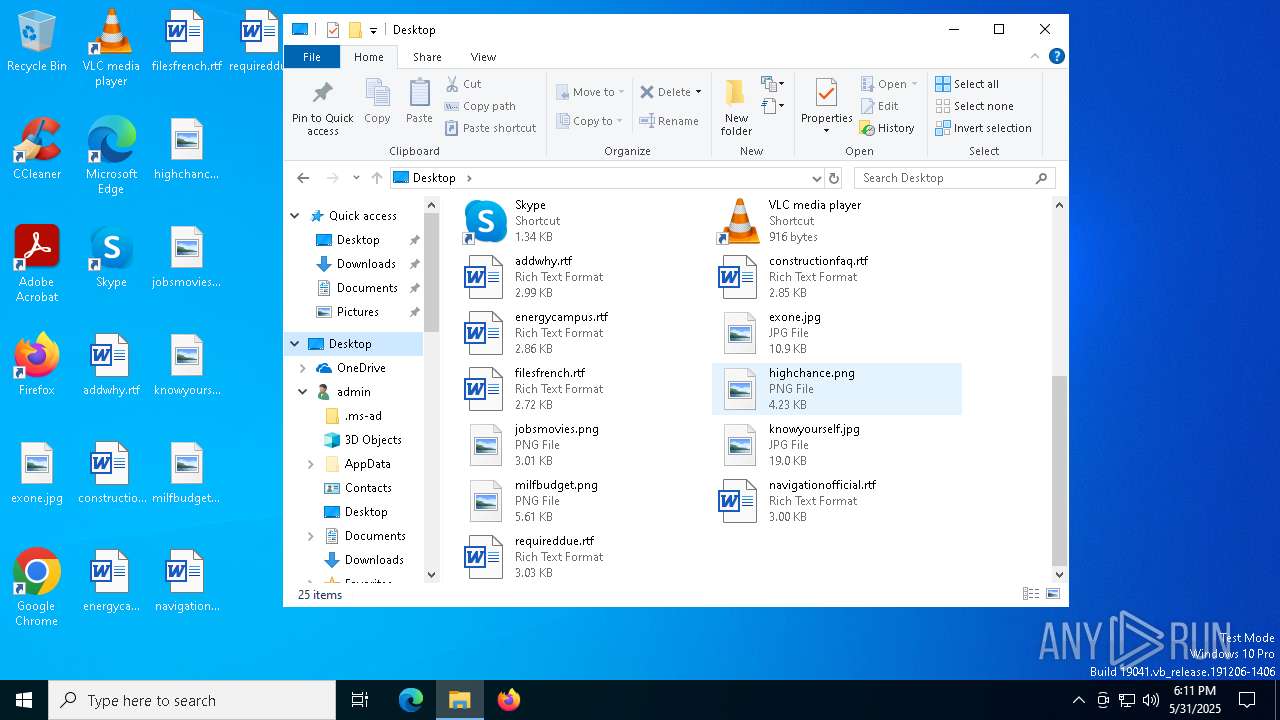
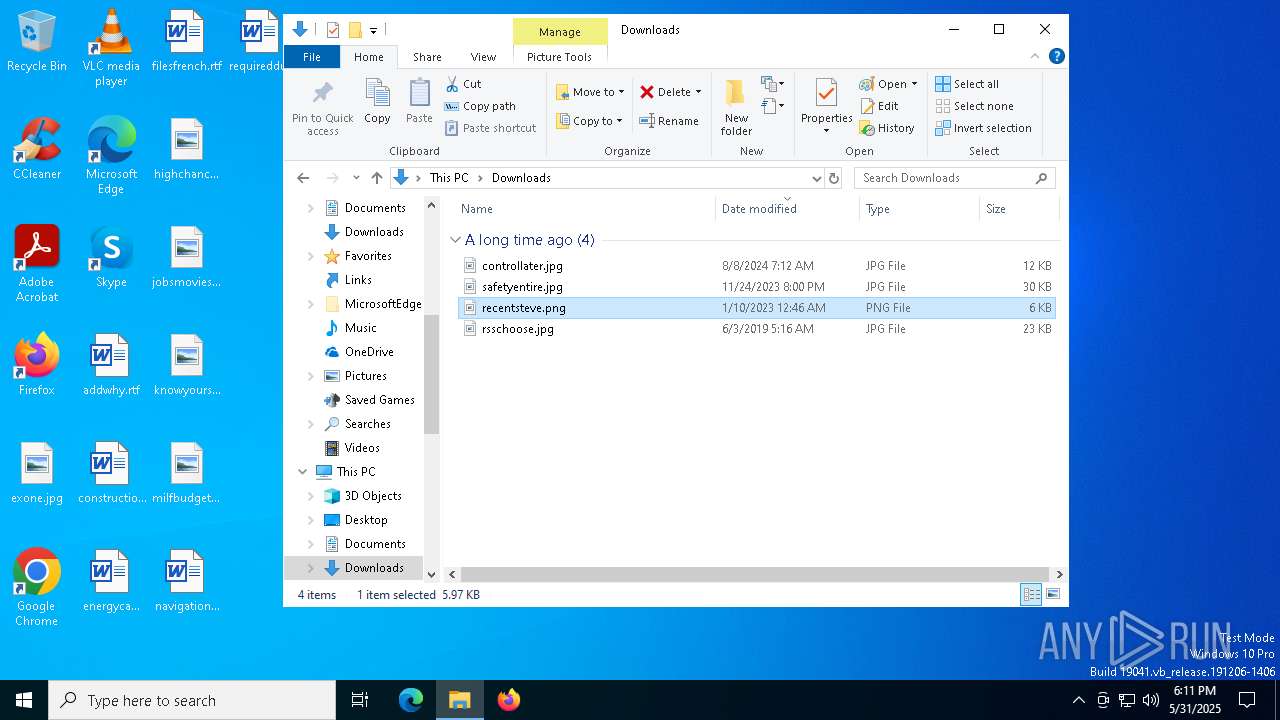
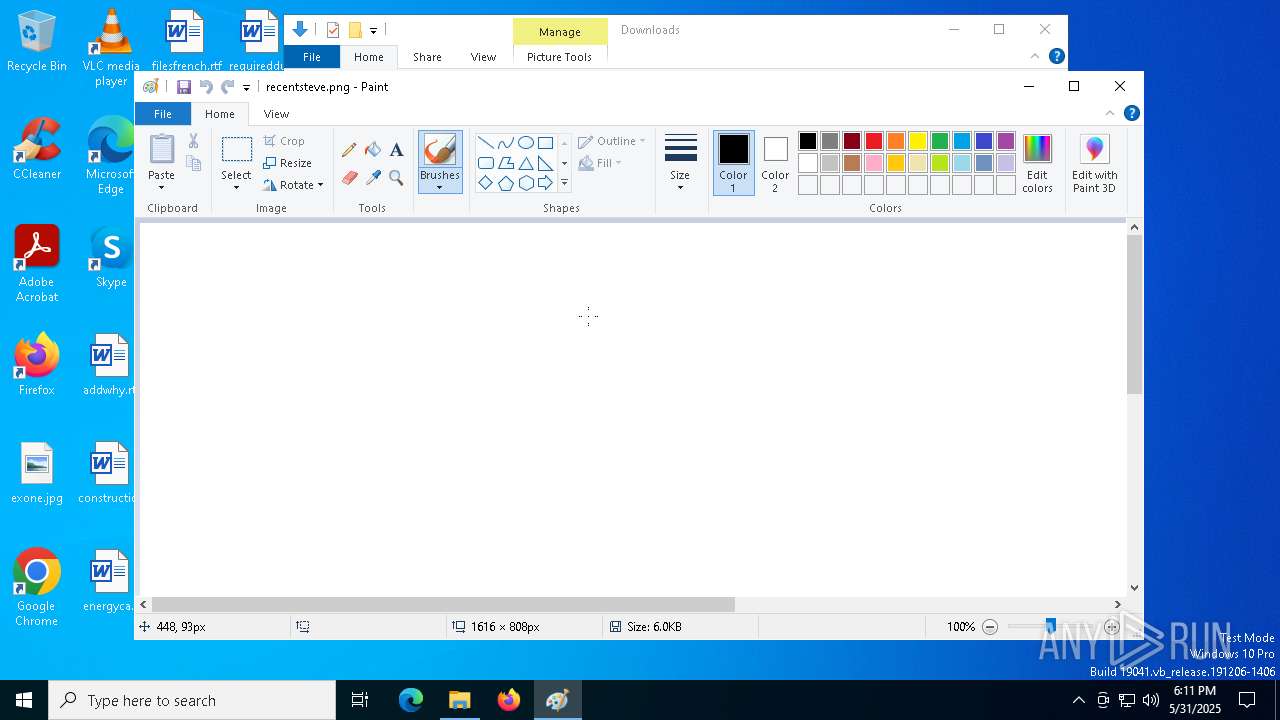
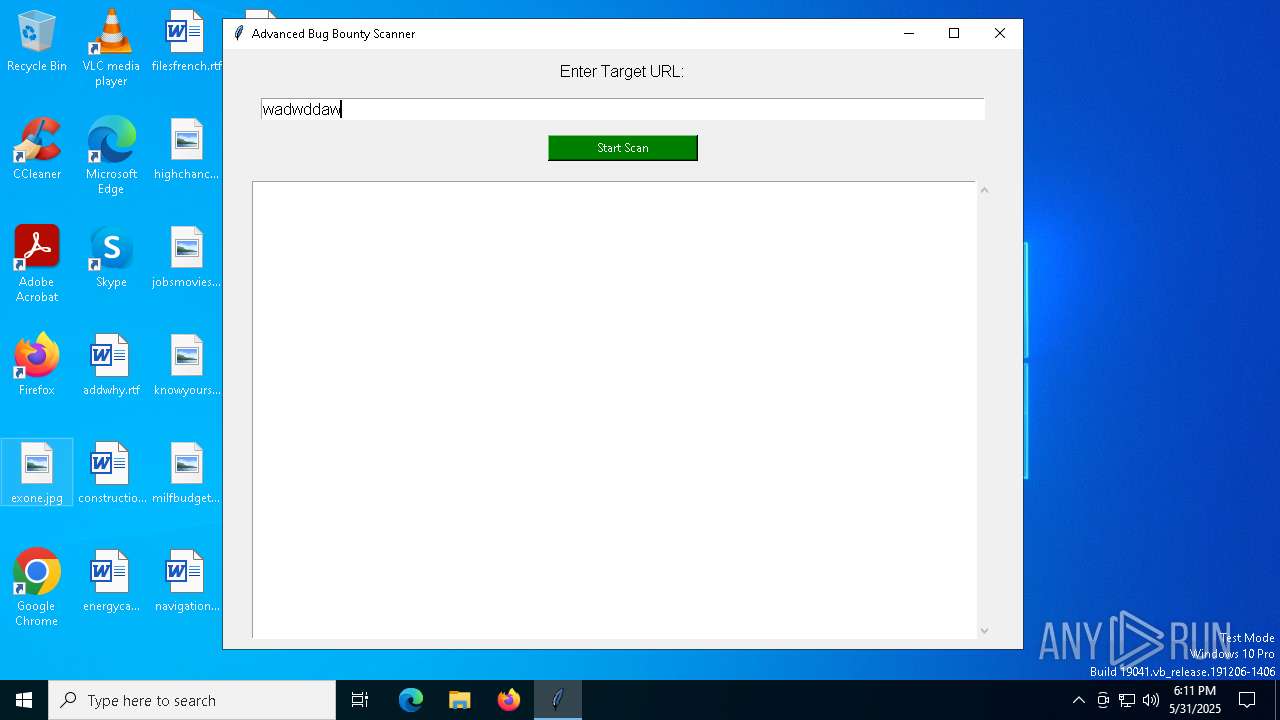
Manual execution by a user
- mspaint.exe (PID: 2568)
PyInstaller has been detected (YARA)
- bug_bounty_gui_original.exe (PID: 2104)
- bug_bounty_gui_original.exe (PID: 5248)
Reads the software policy settings
- slui.exe (PID: 7348)
Checks proxy server information
- slui.exe (PID: 7348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:20 18:01:35+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 173568 |
| InitializedDataSize: | 155648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce30 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
130
Monitored processes
5
Malicious processes
1
Suspicious processes
0
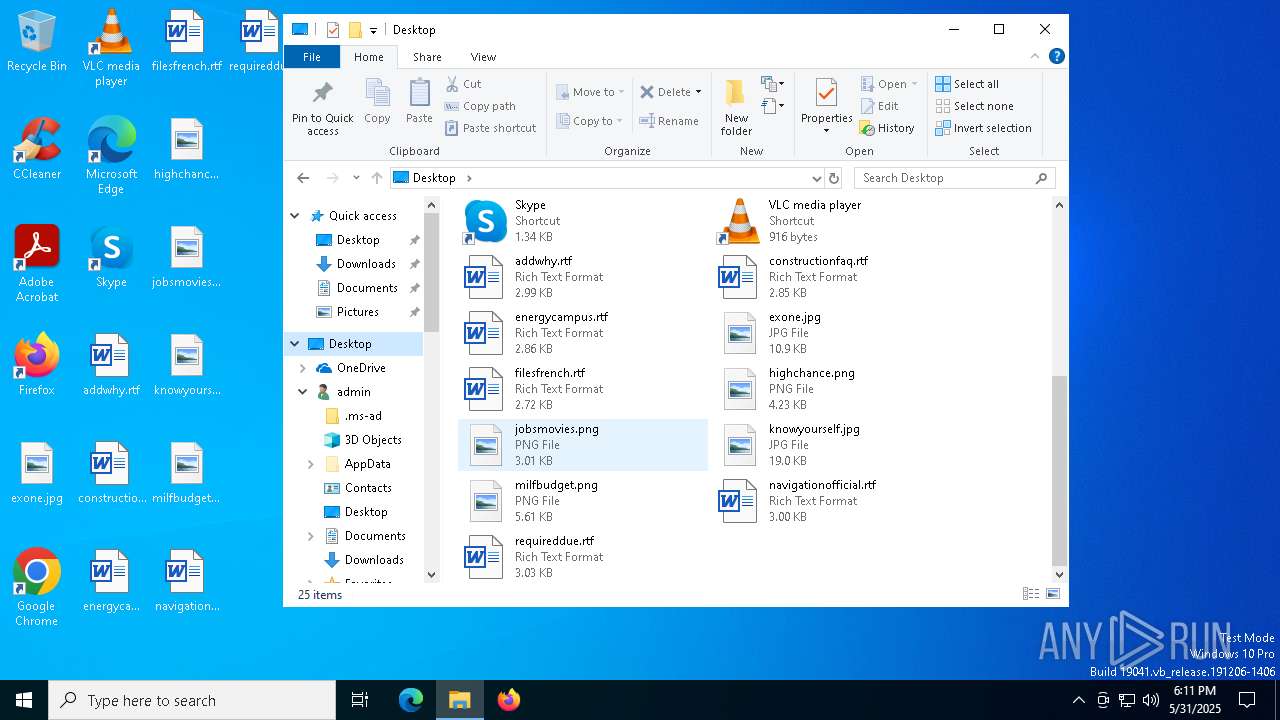
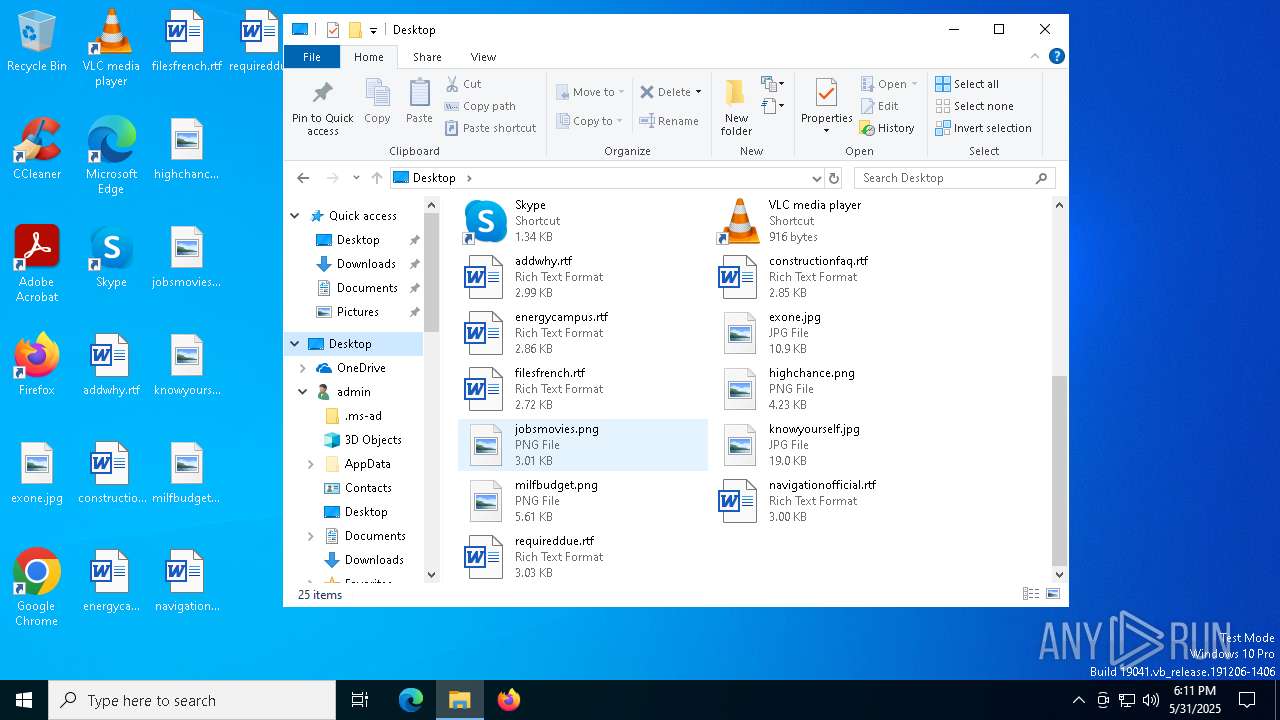
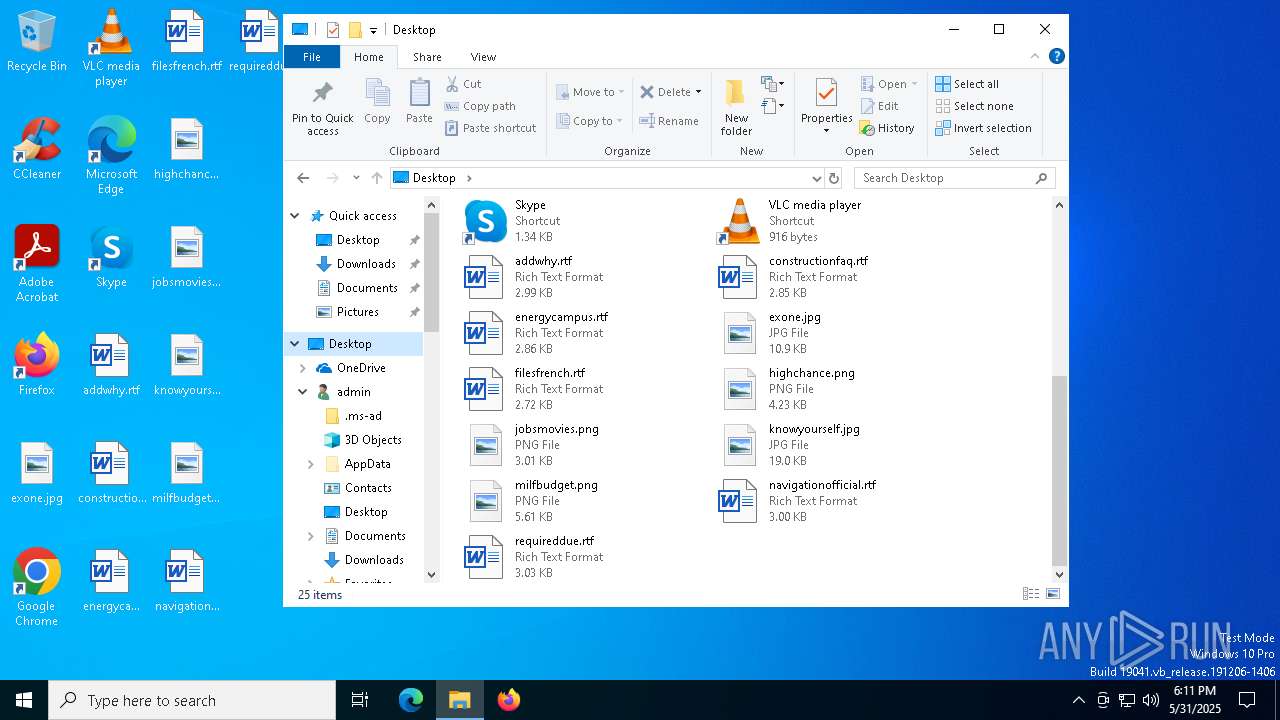
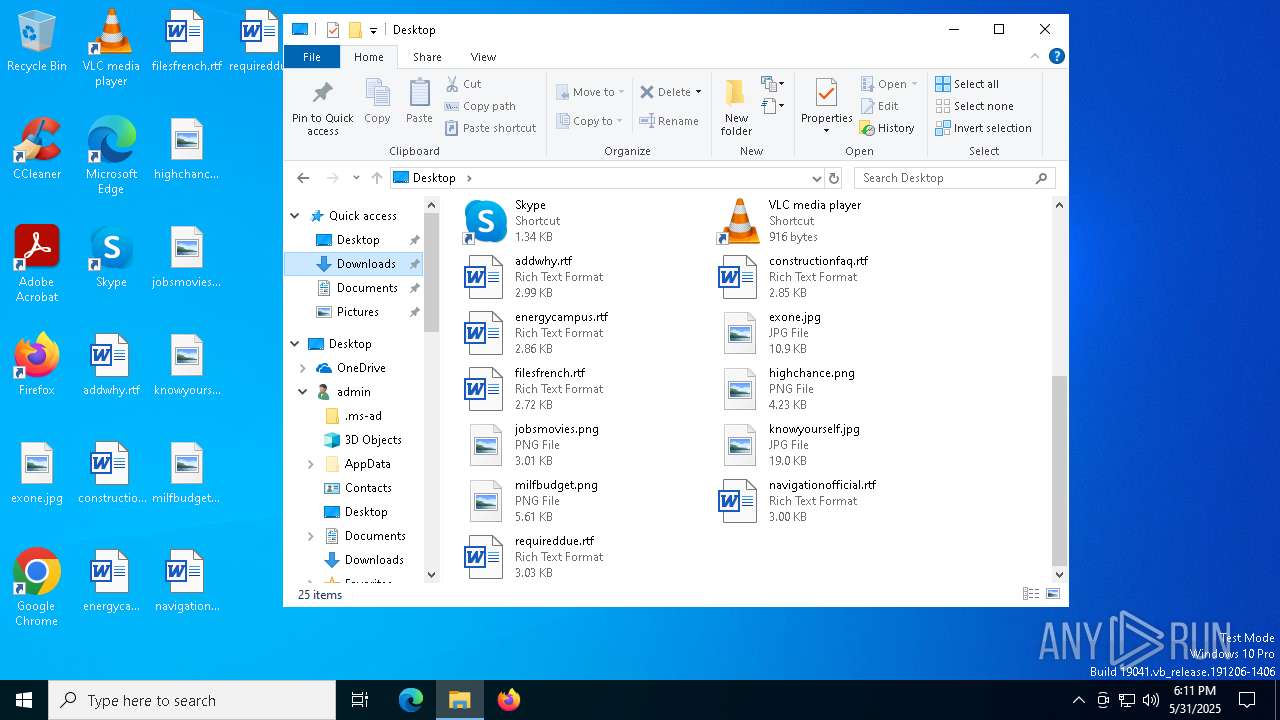
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2104 | "C:\Users\admin\AppData\Local\Temp\bug_bounty_gui_original.exe" | C:\Users\admin\AppData\Local\Temp\bug_bounty_gui_original.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
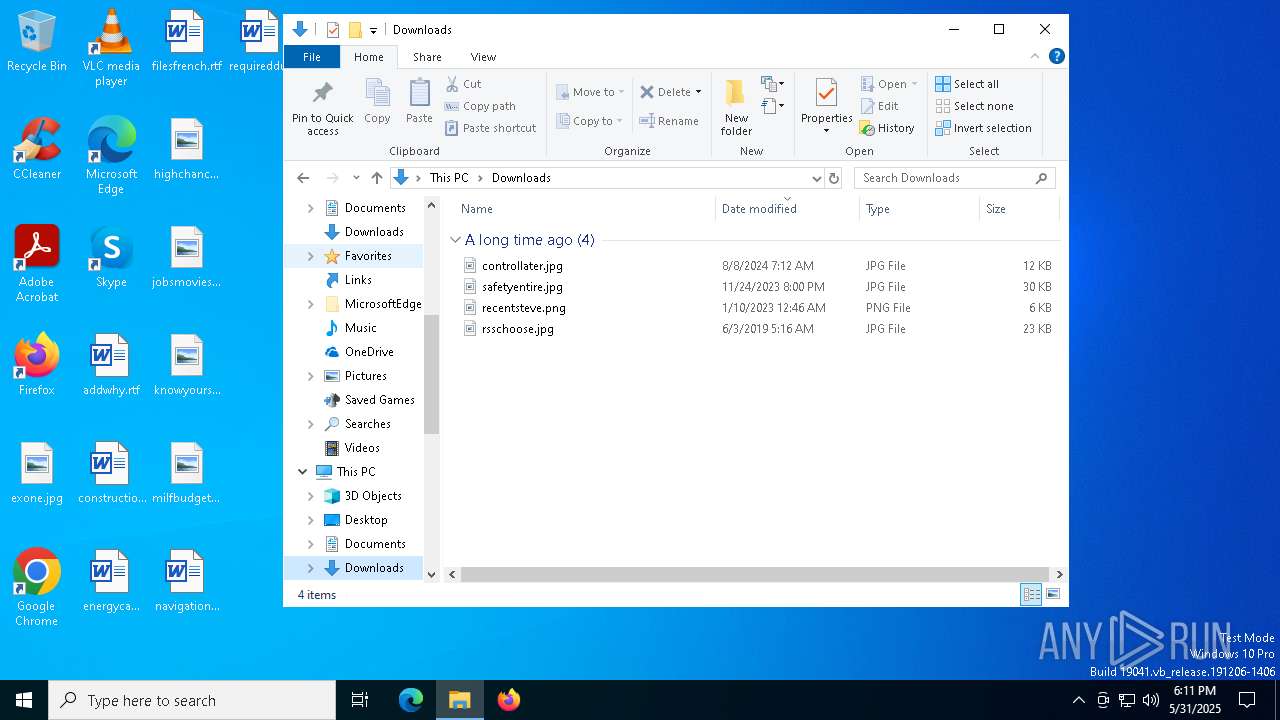
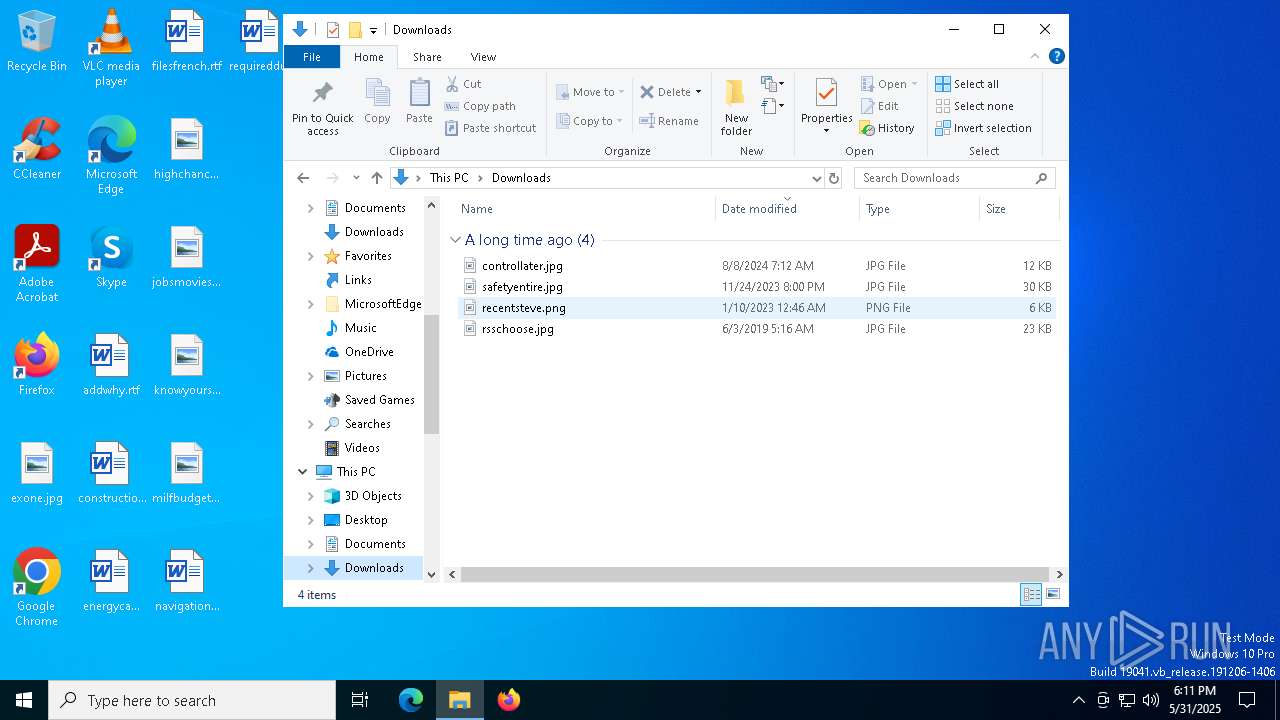
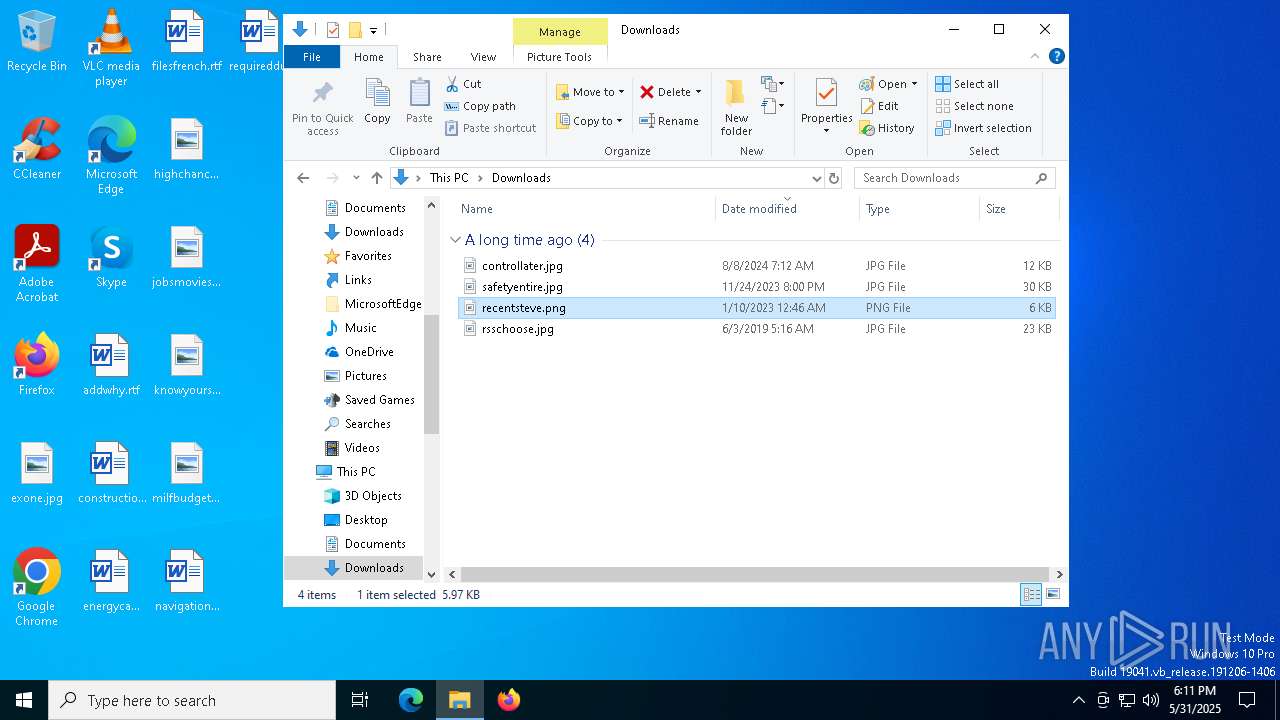
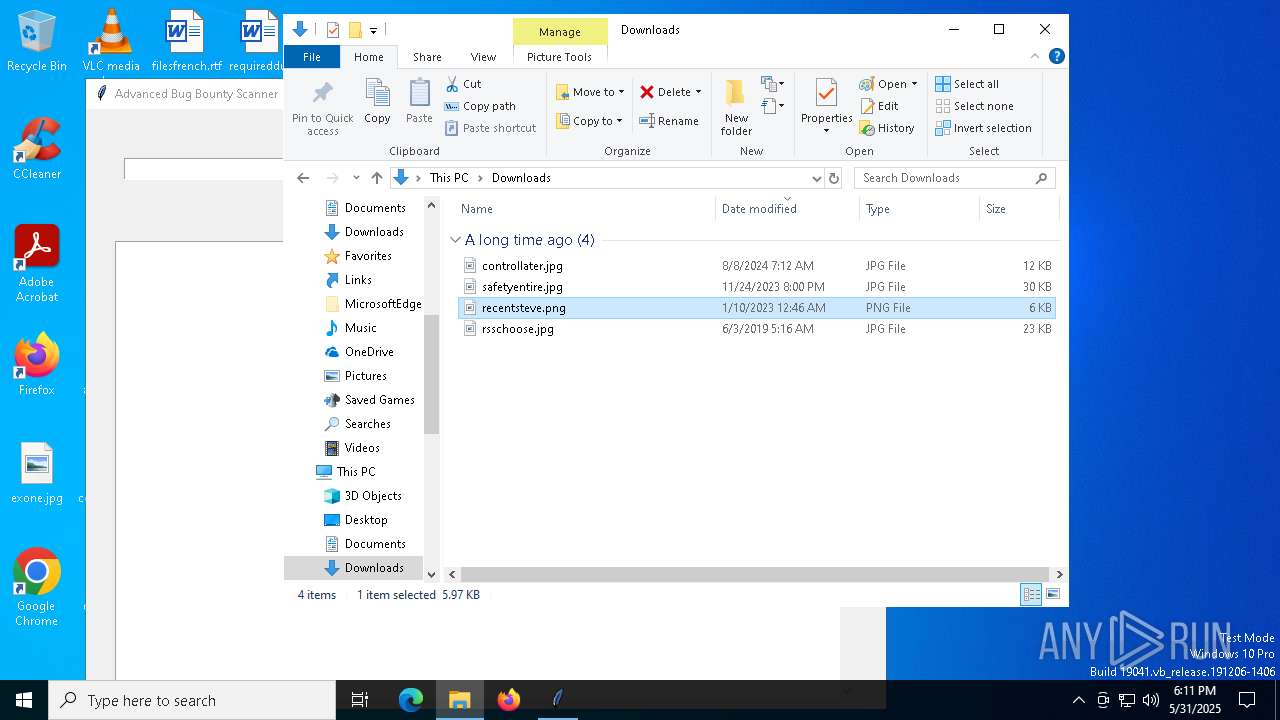
| 2568 | "C:\WINDOWS\system32\mspaint.exe" "C:\Users\admin\Downloads\recentsteve.png" | C:\Windows\System32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4380 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5248 | "C:\Users\admin\AppData\Local\Temp\bug_bounty_gui_original.exe" | C:\Users\admin\AppData\Local\Temp\bug_bounty_gui_original.exe | — | bug_bounty_gui_original.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7348 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 237
Read events
1 208
Write events
28
Delete events
1
Modification events
| (PID) Process: | (2568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | WindowPlacement |
Value: 2C00000000000000010000000000000000000000FFFFFFFFFFFFFFFF7F000000470000007F04000087020000 | |||
| (PID) Process: | (2568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ShowThumbnail |
Value: 0 | |||
| (PID) Process: | (2568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | BMPWidth |
Value: 0 | |||
| (PID) Process: | (2568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | BMPHeight |
Value: 0 | |||
| (PID) Process: | (2568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbXPos |
Value: 0 | |||
| (PID) Process: | (2568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbYPos |
Value: 0 | |||
| (PID) Process: | (2568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbWidth |
Value: 0 | |||
| (PID) Process: | (2568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbHeight |
Value: 0 | |||
| (PID) Process: | (2568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | UnitSetting |
Value: 0 | |||
| (PID) Process: | (2568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ShowRulers |
Value: 0 | |||
Executable files
24
Suspicious files
3
Text files
921
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2104 | bug_bounty_gui_original.exe | C:\Users\admin\AppData\Local\Temp\_MEI21042\VCRUNTIME140.dll | executable | |
MD5:BE8DBE2DC77EBE7F88F910C61AEC691A | SHA256:4D292623516F65C80482081E62D5DADB759DC16E851DE5DB24C3CBB57B87DB83 | |||
| 2104 | bug_bounty_gui_original.exe | C:\Users\admin\AppData\Local\Temp\_MEI21042\_hashlib.pyd | executable | |
MD5:B4FF25B1ACA23D48897FC616E102E9B6 | SHA256:87DD0C858620287454FD6D31D52B6A48EDDBB2A08E09E8B2D9FDB0B92200D766 | |||
| 2104 | bug_bounty_gui_original.exe | C:\Users\admin\AppData\Local\Temp\_MEI21042\_lzma.pyd | executable | |
MD5:B86B9F292AF12006187EBE6C606A377D | SHA256:F5E01B516C2C23035F7703E23569DEC26C5616C05A929B2580AE474A5C6722C5 | |||
| 2104 | bug_bounty_gui_original.exe | C:\Users\admin\AppData\Local\Temp\_MEI21042\_ctypes.pyd | executable | |
MD5:565D011CE1CEE4D48E722C7421300090 | SHA256:C148292328F0AAB7863AF82F54F613961E7CB95B7215F7A81CAFAF45BD4C42B7 | |||
| 2104 | bug_bounty_gui_original.exe | C:\Users\admin\AppData\Local\Temp\_MEI21042\_asyncio.pyd | executable | |
MD5:07A6E6DCC30E1C4C7E0CDC41A457A887 | SHA256:746BC8FA88282AFE19DC60E426CC0A75BEA3BD137CCA06A0B57A30BD31459403 | |||
| 2104 | bug_bounty_gui_original.exe | C:\Users\admin\AppData\Local\Temp\_MEI21042\_bz2.pyd | executable | |
MD5:AA1083BDE6D21CABFC630A18F51B1926 | SHA256:00B8CA9A338D2B47285C9E56D6D893DB2A999B47216756F18439997FB80A56E3 | |||
| 2104 | bug_bounty_gui_original.exe | C:\Users\admin\AppData\Local\Temp\_MEI21042\_tcl_data\encoding\big5.enc | text | |
MD5:41A874778111CC218BD421CF9C795EC2 | SHA256:AD1ED201B69855BFD353BF969DFC55576DA35A963ABF1BF7FC6D8B5142A61A61 | |||
| 2104 | bug_bounty_gui_original.exe | C:\Users\admin\AppData\Local\Temp\_MEI21042\_tcl_data\auto.tcl | text | |
MD5:08EDF746B4A088CB4185C165177BD604 | SHA256:517204EE436D08EFC287ABC97433C3BFFCAF42EC6592A3009B9FD3B985AD772C | |||
| 2104 | bug_bounty_gui_original.exe | C:\Users\admin\AppData\Local\Temp\_MEI21042\_tcl_data\encoding\cp1252.enc | text | |
MD5:E9117326C06FEE02C478027CB625C7D8 | SHA256:741859CF238C3A63BBB20EC6ED51E46451372BB221CFFF438297D261D0561C2E | |||
| 2104 | bug_bounty_gui_original.exe | C:\Users\admin\AppData\Local\Temp\_MEI21042\_tcl_data\encoding\cns11643.enc | text | |
MD5:B6A7C59E6A48D91CC2DBCB2BBA7E4510 | SHA256:8924545CC92584169138AADB64683C07BBF846A57014C2E668D23B63F43F3610 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
22
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7560 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6068 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6068 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7344 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7560 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7560 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |