| File name: | file |
| Full analysis: | https://app.any.run/tasks/c279ccd7-7156-48a2-a619-fdd6e571f747 |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2026, 17:13:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 (with BOM) text, with CRLF line terminators |
| MD5: | D8639344F3A604DF748DD7459B49F0EB |
| SHA1: | 49096B44B648F7DBEBEB29ABF81134D2BFD3AD92 |
| SHA256: | 3529B005E9E461139AF037E3A42C5ABB35EDC5F159EA5C8C08FB5BBEC49203A7 |
| SSDEEP: | 192:ru04kKiMcB0kJOEBF4aG7S5H/0csLqA9nM:rlrT0kJOEBFU8H/6qSM |
MALICIOUS
No malicious indicators.SUSPICIOUS
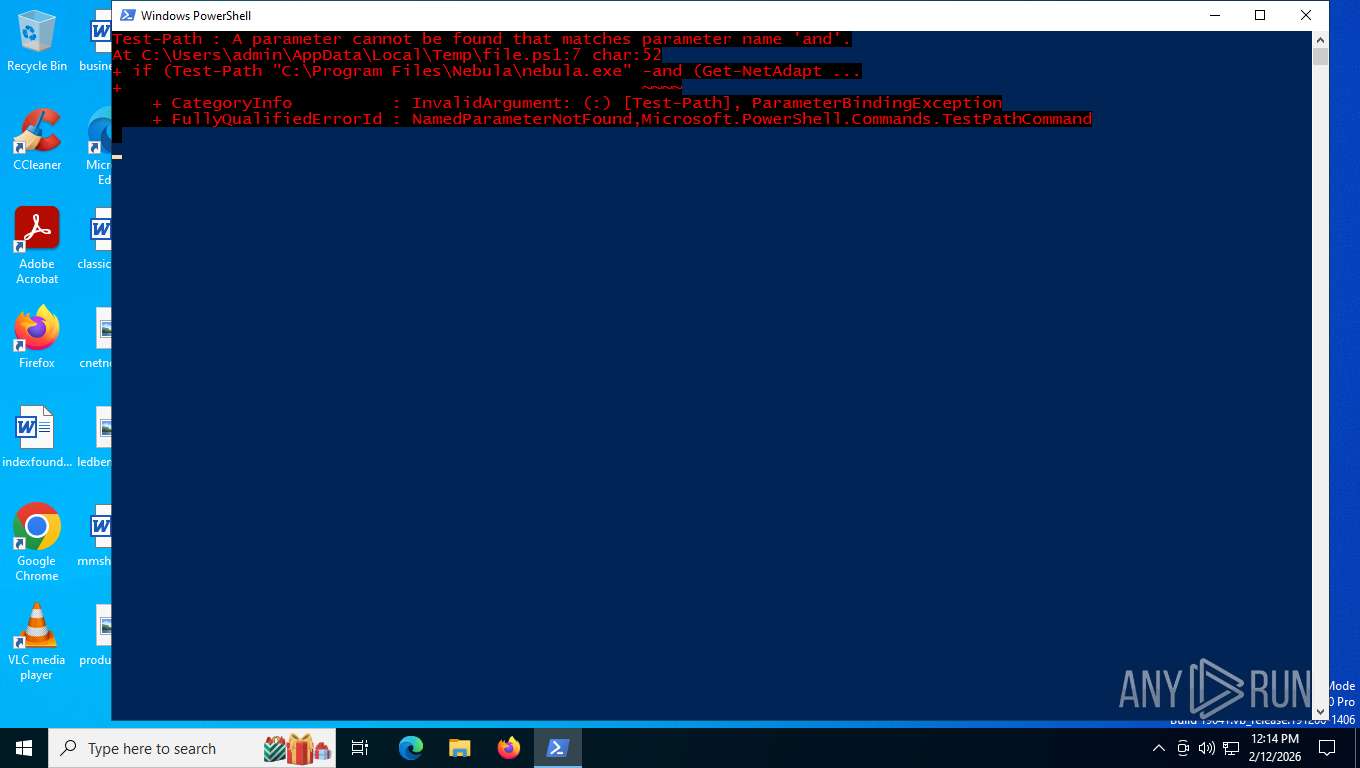
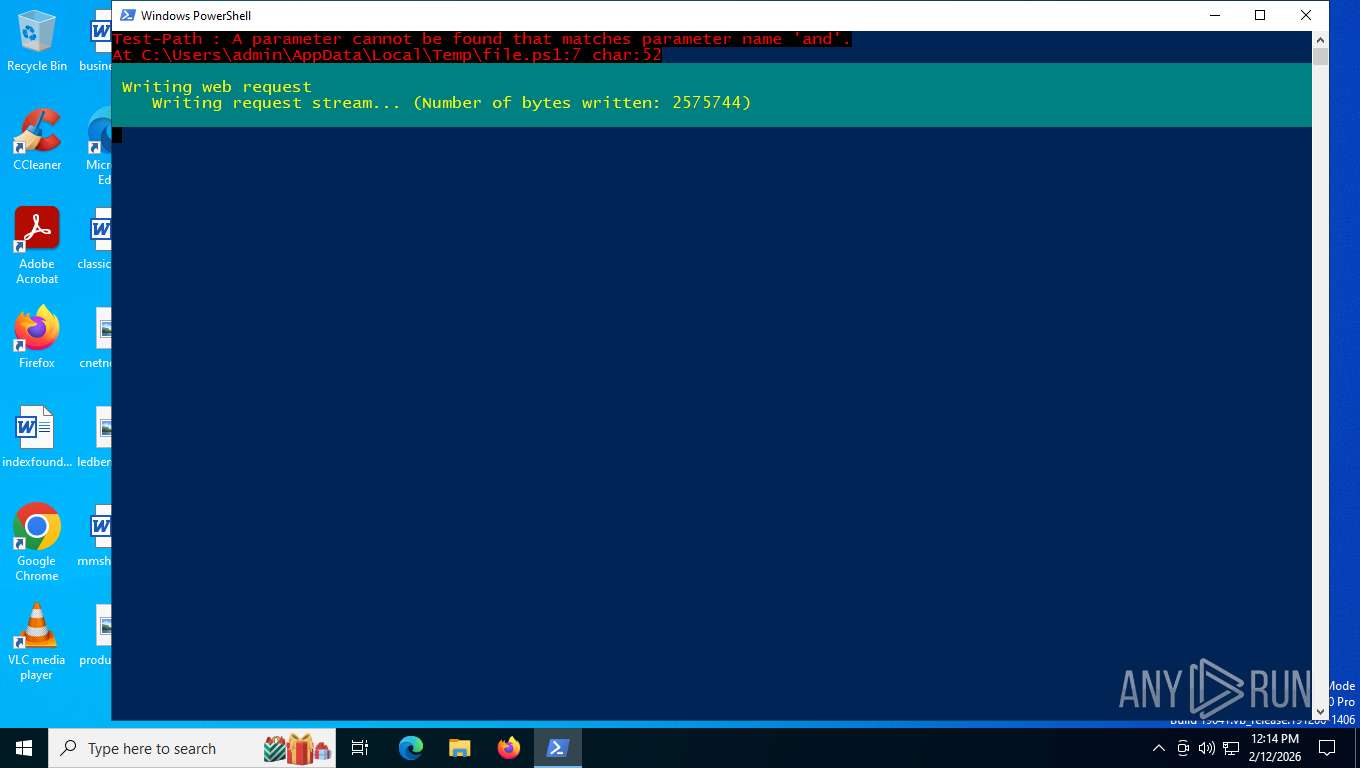
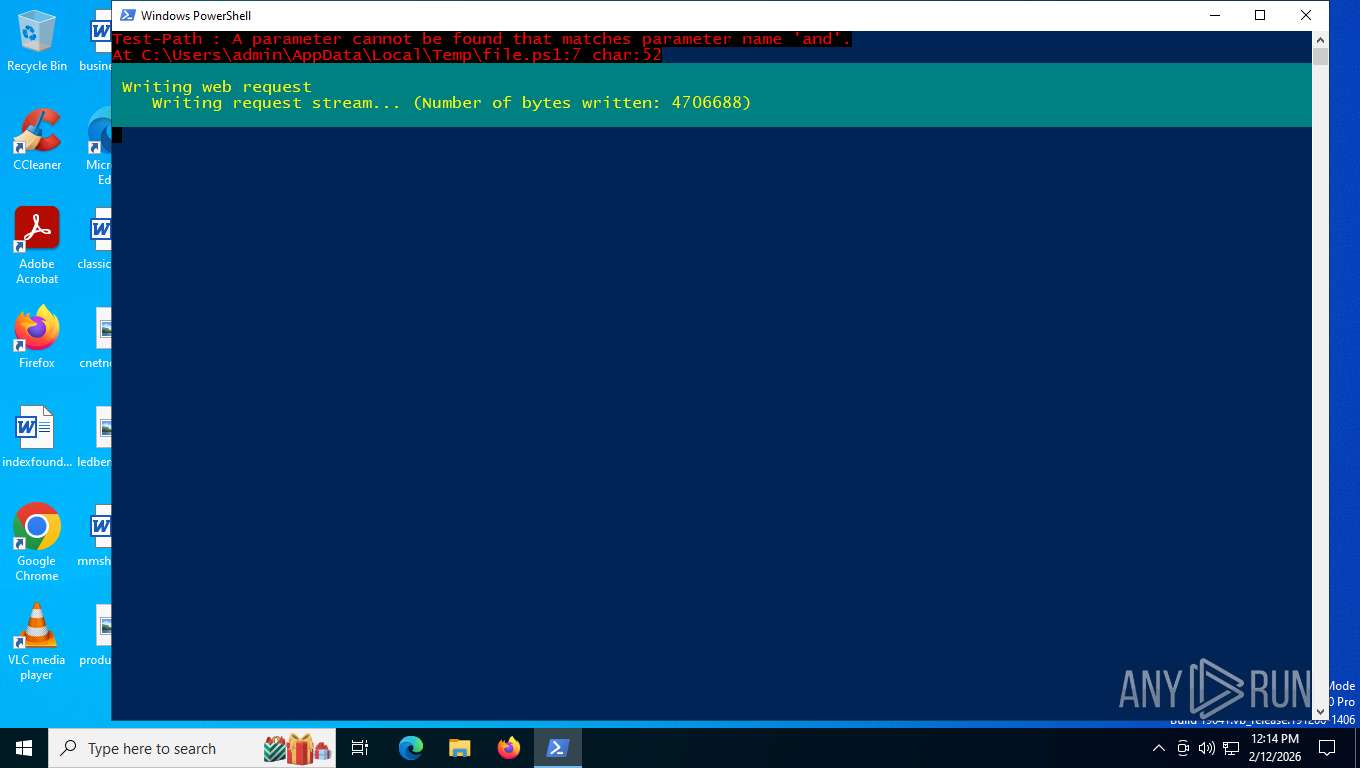
Bypass execution policy to execute commands
- powershell.exe (PID: 5080)
- powershell.exe (PID: 5520)
- powershell.exe (PID: 8632)
- powershell.exe (PID: 8308)
- powershell.exe (PID: 1848)
The process executes Powershell scripts
- powershell.exe (PID: 5080)
- powershell.exe (PID: 1848)
- powershell.exe (PID: 5520)
- powershell.exe (PID: 8632)
- powershell.exe (PID: 8308)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 5520)
- powershell.exe (PID: 8308)
INFO
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5080)
Disables trace logs
- powershell.exe (PID: 5080)
Drops script file
- powershell.exe (PID: 5080)
- powershell.exe (PID: 8308)
- powershell.exe (PID: 1848)
- powershell.exe (PID: 5520)
- powershell.exe (PID: 8632)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5080)
- powershell.exe (PID: 8308)
- powershell.exe (PID: 1848)
- powershell.exe (PID: 8632)
- powershell.exe (PID: 5520)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5080)
Checks proxy server information
- powershell.exe (PID: 5080)
- slui.exe (PID: 6468)
The sample compiled with english language support
- powershell.exe (PID: 5080)
Checks supported languages
- ssh-shellhost.exe (PID: 5888)
- sftp.exe (PID: 3988)
- sftp-server.exe (PID: 5680)
- scp.exe (PID: 5164)
- sshd.exe (PID: 524)
- sshd-session.exe (PID: 3232)
- ssh-agent.exe (PID: 8828)
Reads the computer name
- sftp.exe (PID: 3988)
- sftp-server.exe (PID: 5680)
- sshd.exe (PID: 524)
- scp.exe (PID: 5164)
- sshd-session.exe (PID: 3232)
- ssh-agent.exe (PID: 8828)
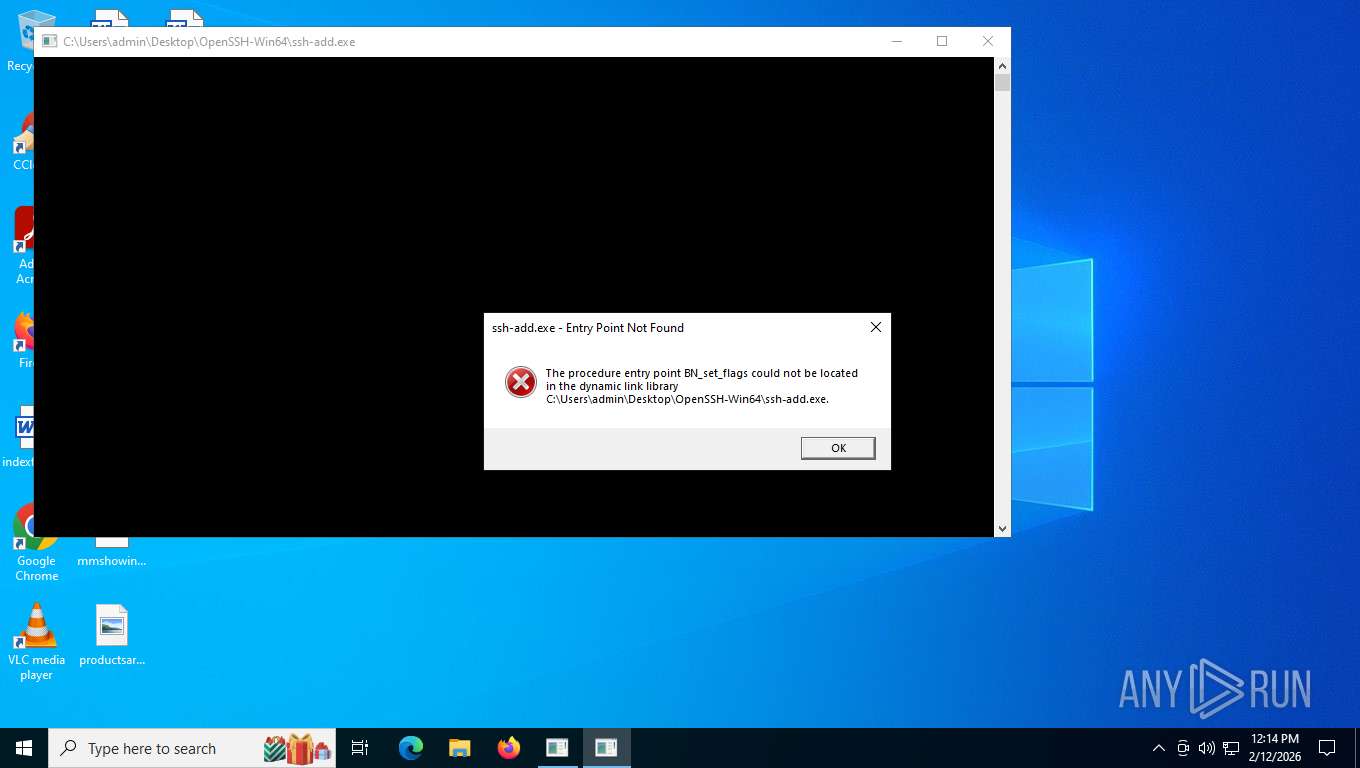
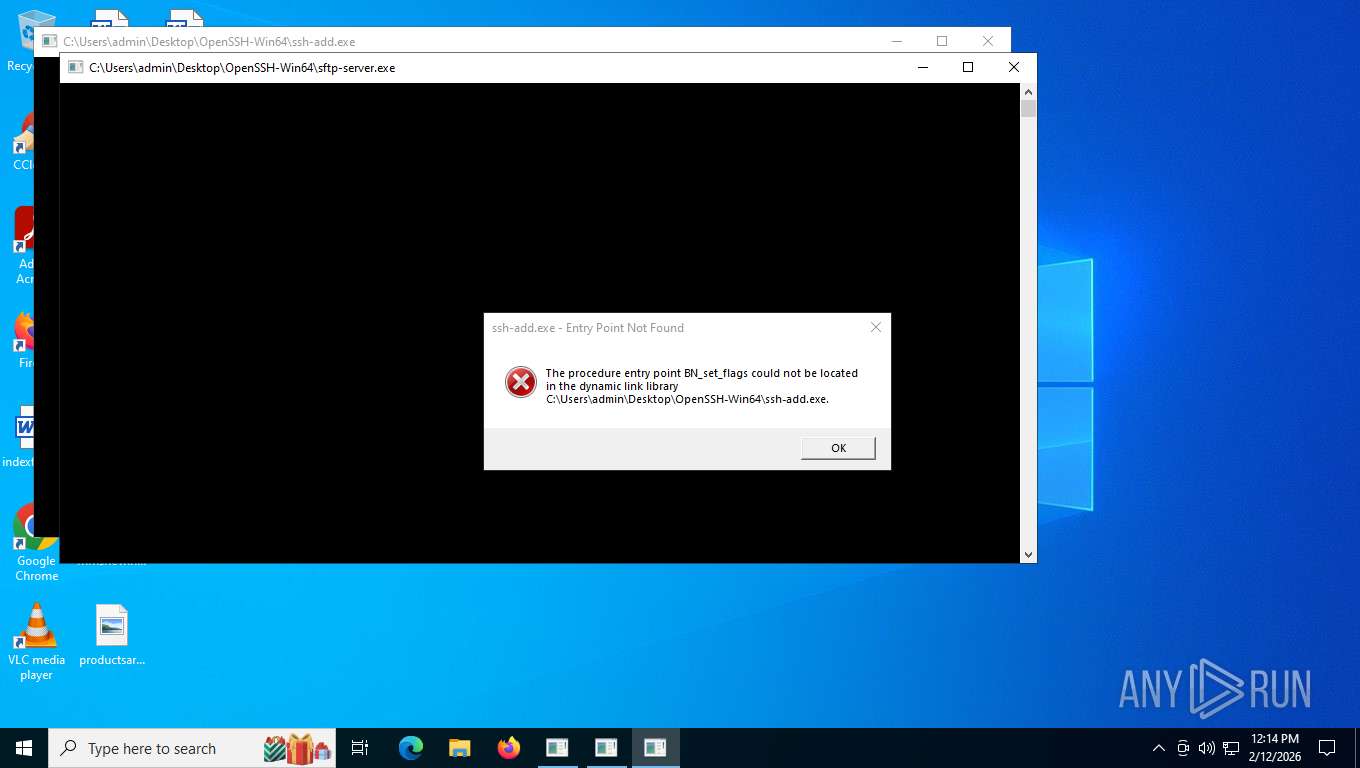
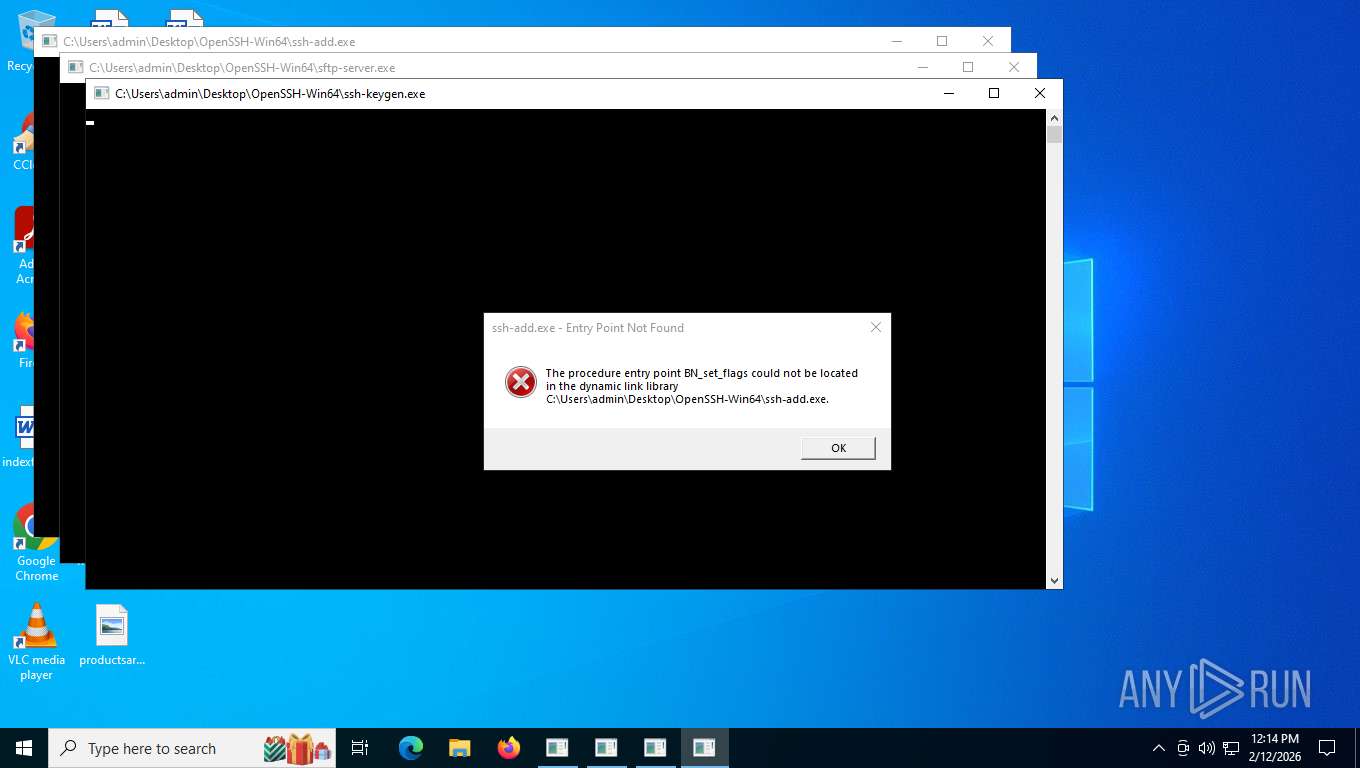
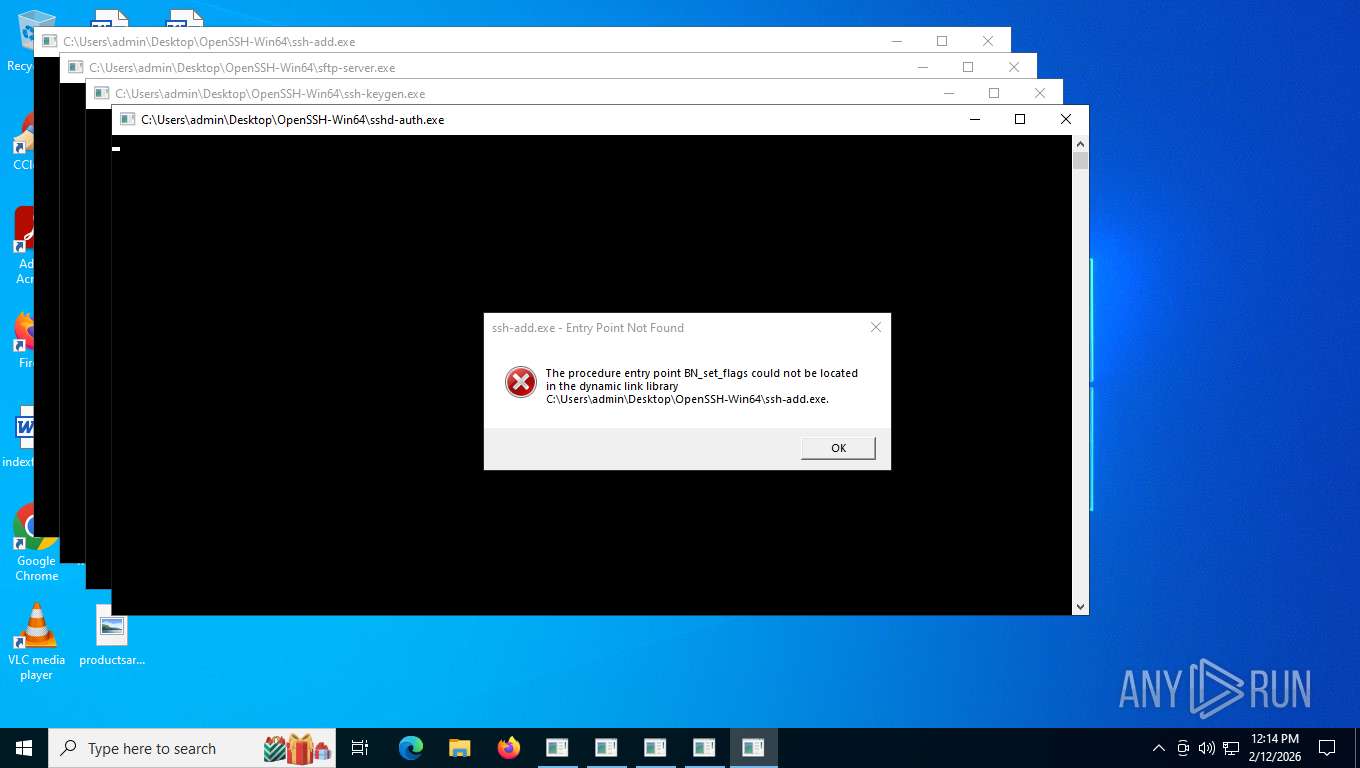
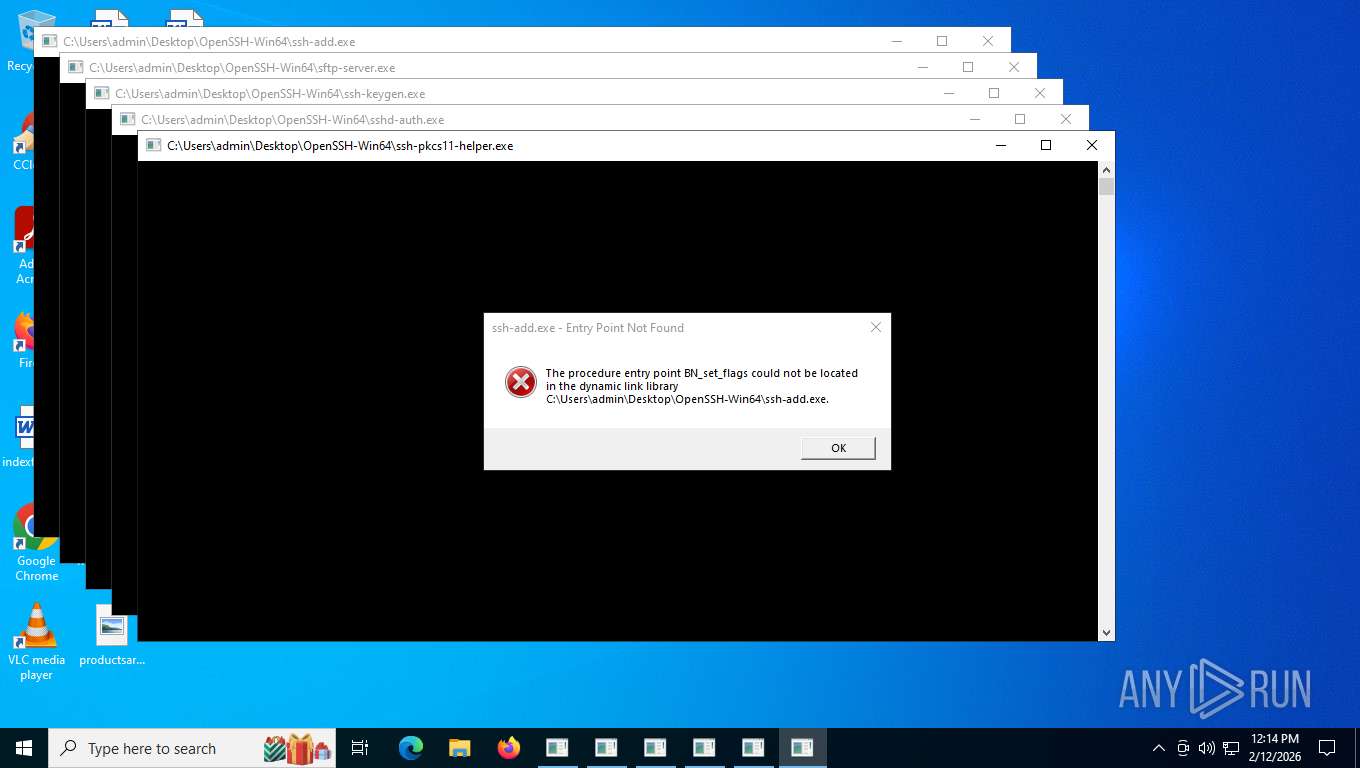
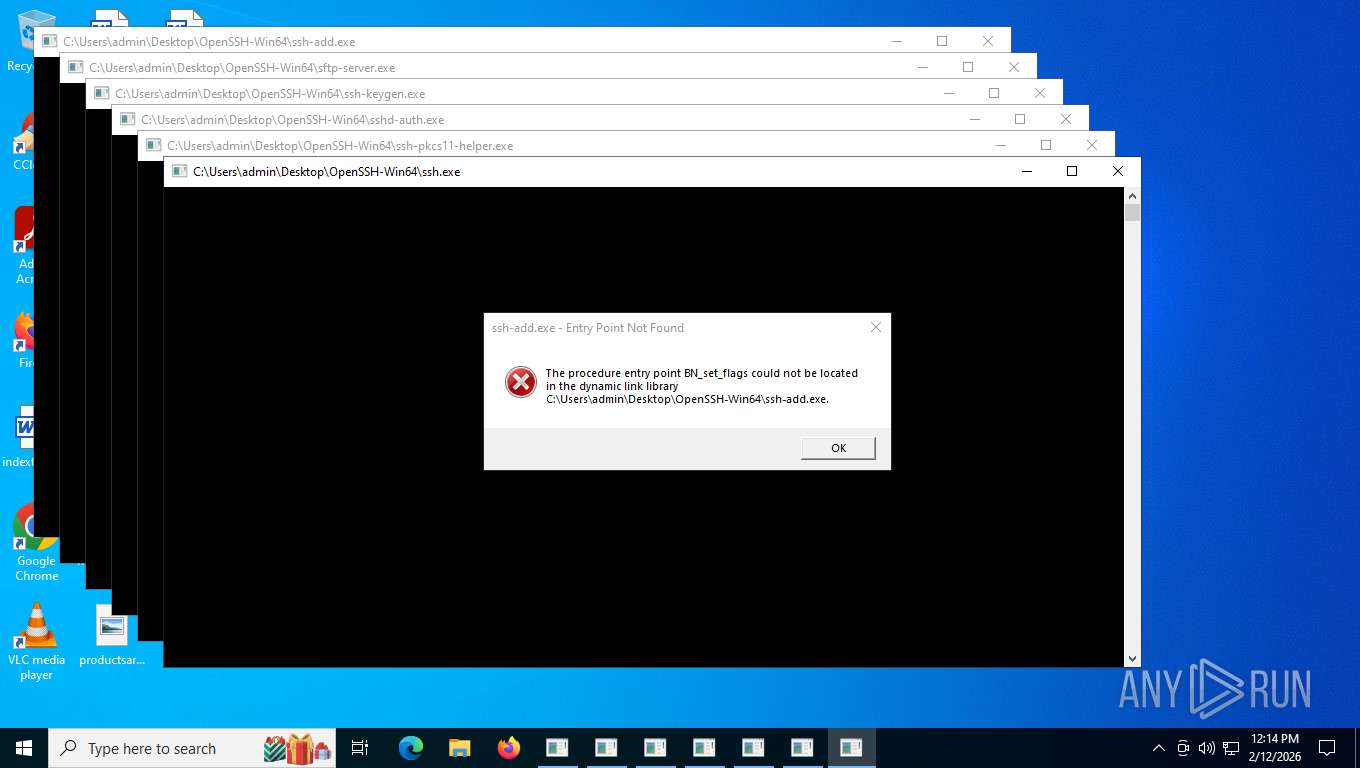
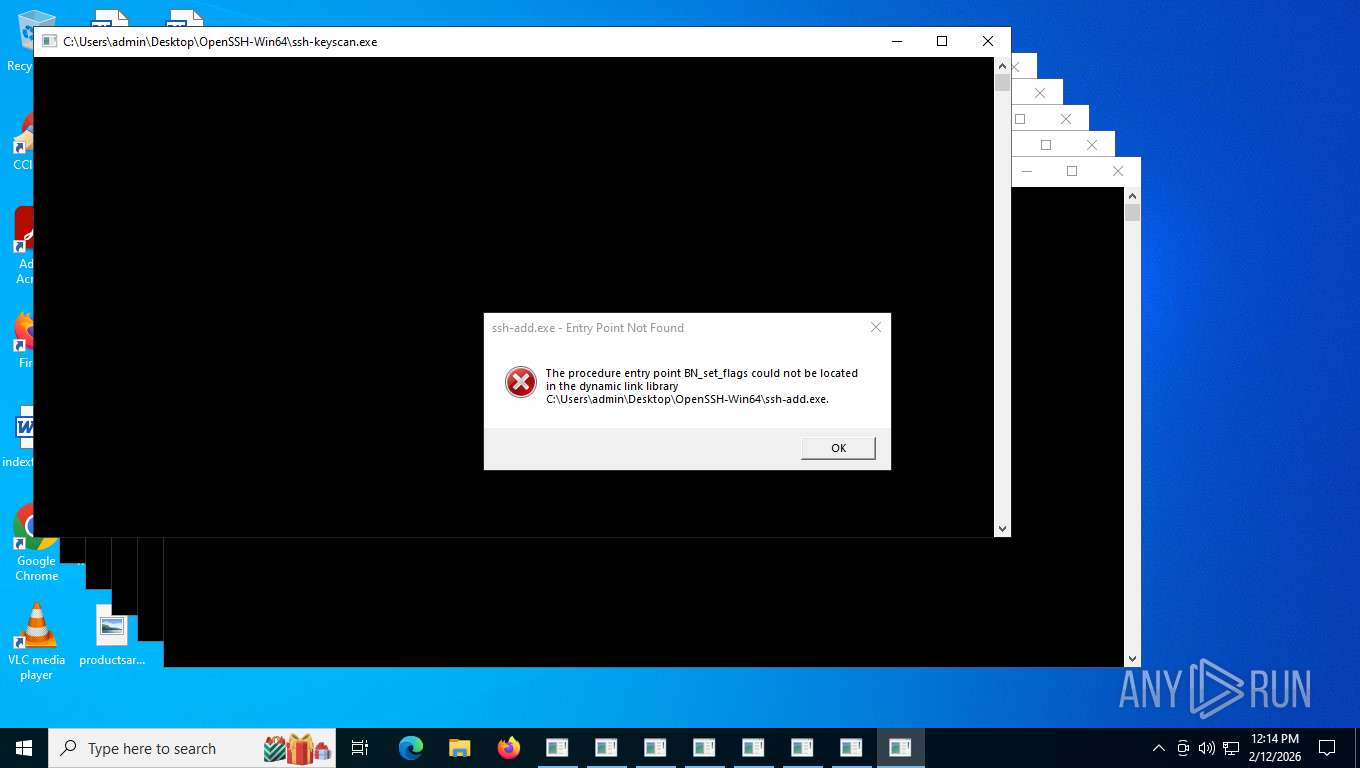
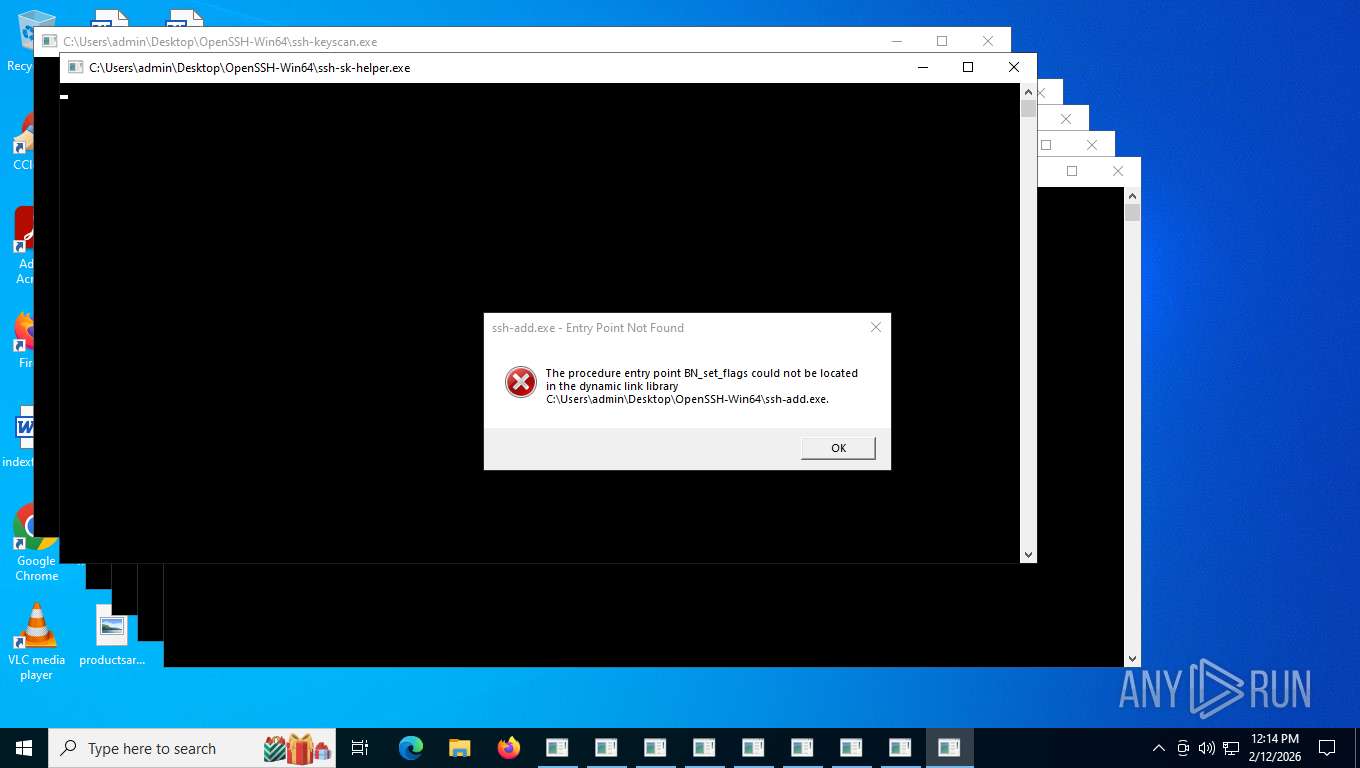
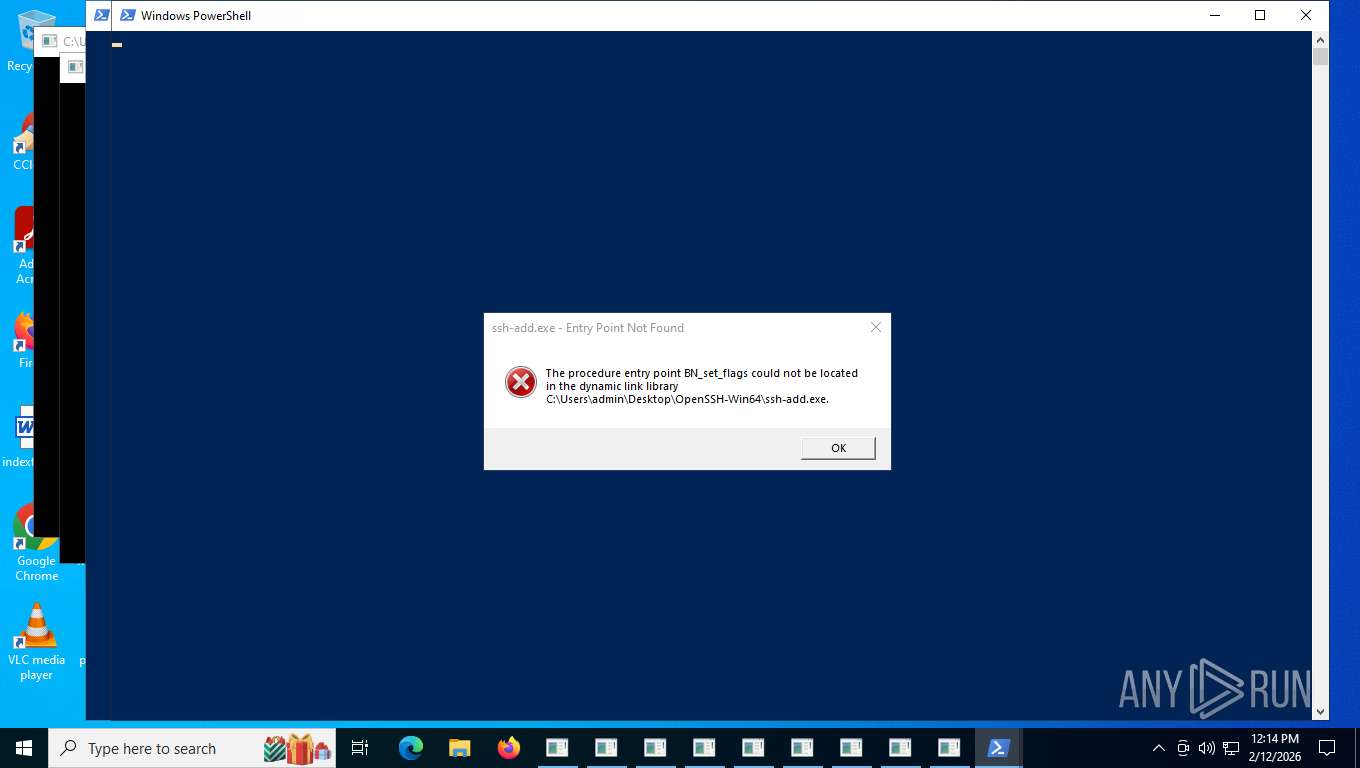
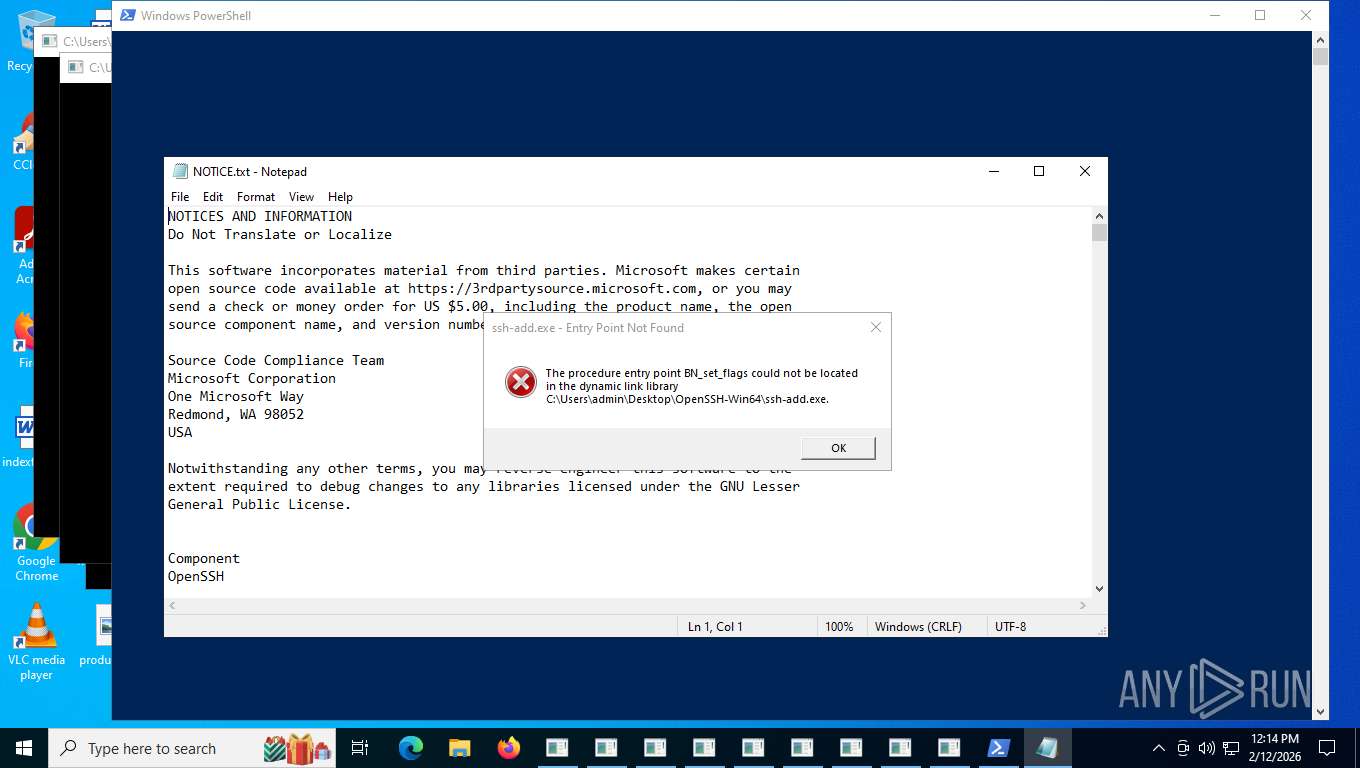
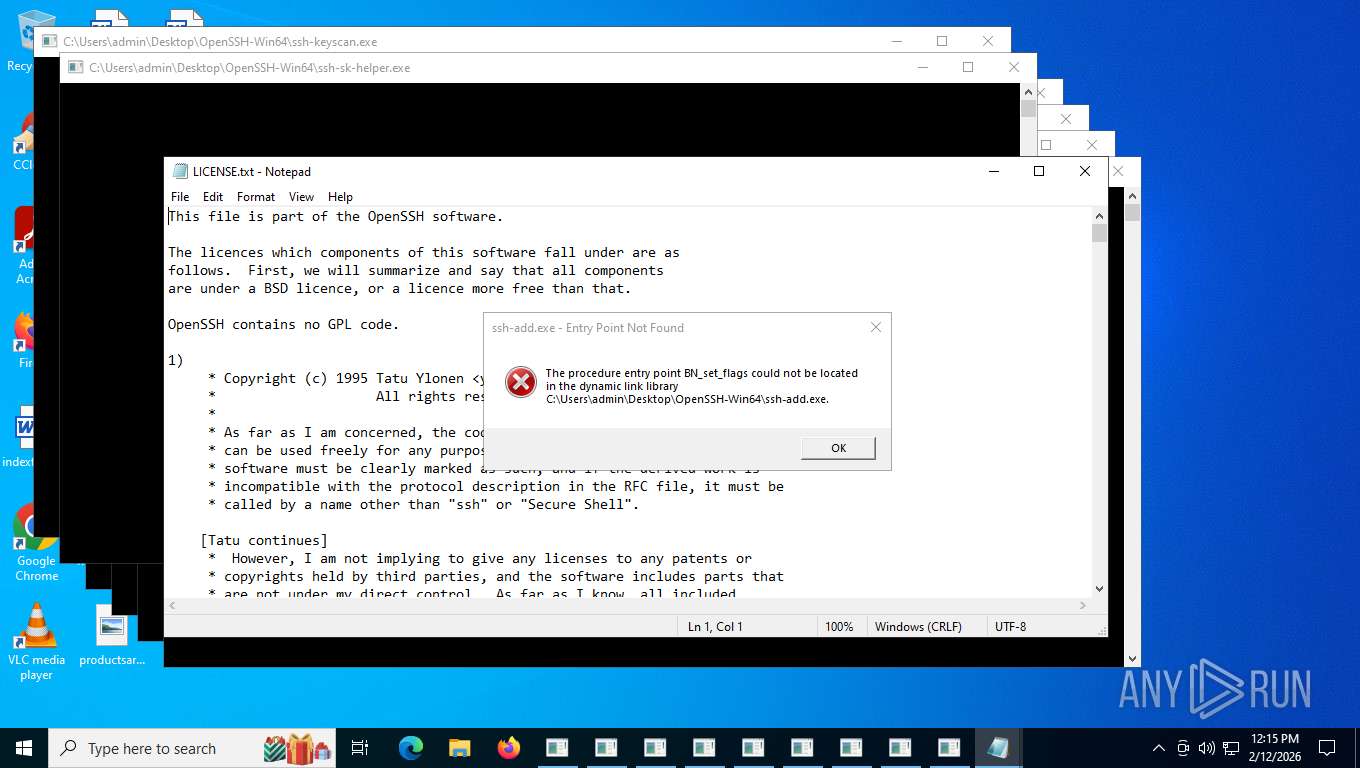
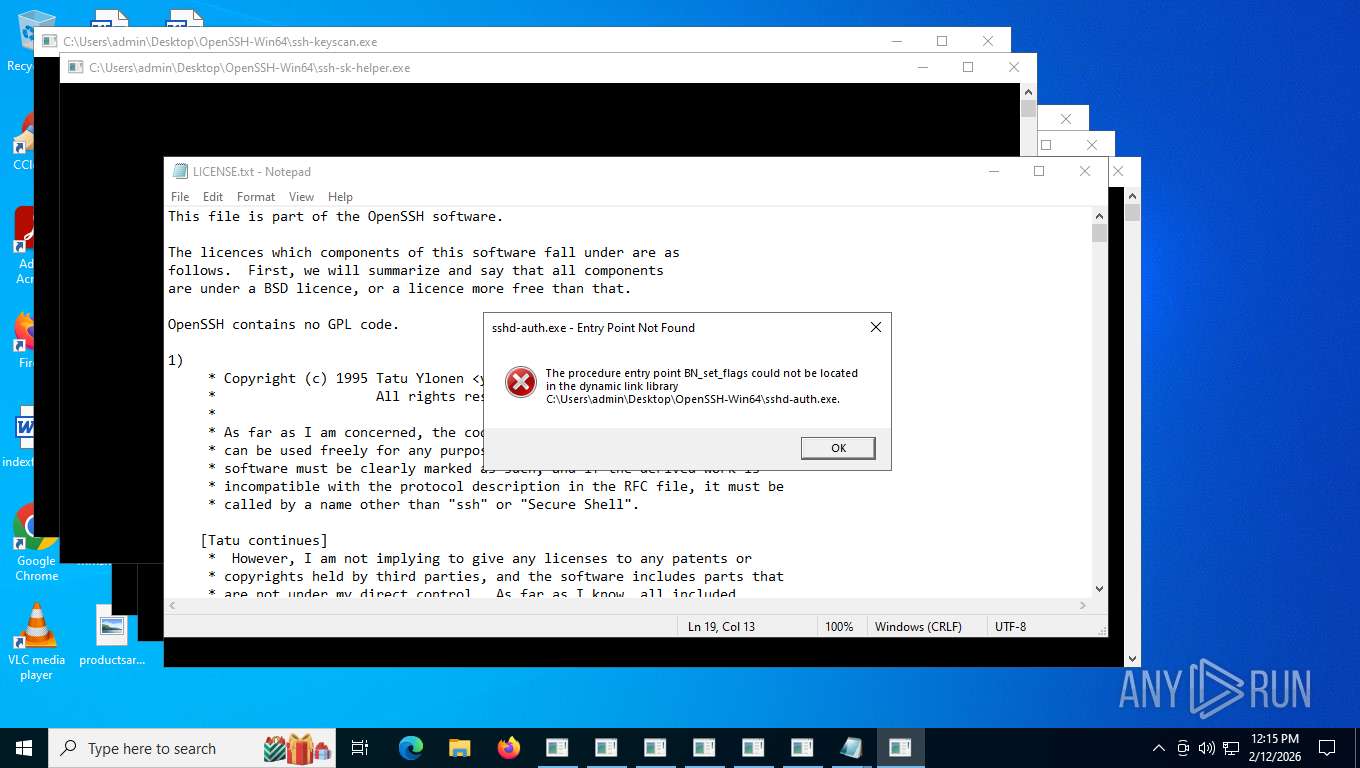
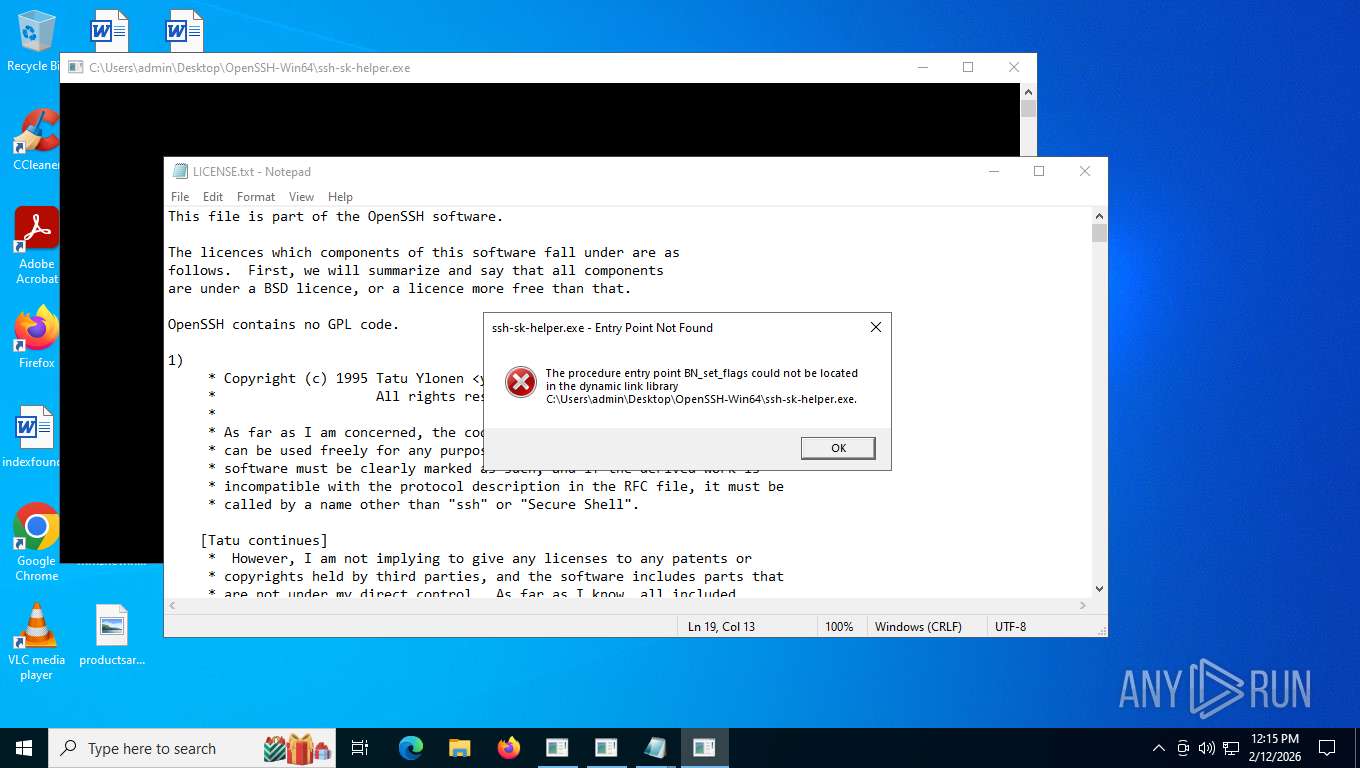
Manual execution by a user
- ssh-add.exe (PID: 936)
- ssh-shellhost.exe (PID: 5888)
- sftp-server.exe (PID: 5680)
- sftp.exe (PID: 3988)
- ssh-keygen.exe (PID: 4188)
- ssh-pkcs11-helper.exe (PID: 9168)
- ssh.exe (PID: 2232)
- ssh-sk-helper.exe (PID: 7244)
- ssh-keyscan.exe (PID: 6096)
- scp.exe (PID: 5164)
- sshd.exe (PID: 524)
- ssh-agent.exe (PID: 8828)
- sshd-session.exe (PID: 3232)
- sshd-auth.exe (PID: 7308)
- powershell.exe (PID: 1848)
- powershell.exe (PID: 8632)
- powershell.exe (PID: 5520)
- powershell.exe (PID: 8308)
- notepad.exe (PID: 4604)
- notepad.exe (PID: 8960)
Reads security settings of Internet Explorer
- notepad.exe (PID: 4604)
- notepad.exe (PID: 8960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-8 encoded (100) |
|---|
Total processes
187
Monitored processes
41
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 524 | "C:\Users\admin\Desktop\OpenSSH-Win64\sshd.exe" | C:\Users\admin\Desktop\OpenSSH-Win64\sshd.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 10.0.0.0 Modules
| |||||||||||||||
| 936 | "C:\Users\admin\Desktop\OpenSSH-Win64\ssh-add.exe" | C:\Users\admin\Desktop\OpenSSH-Win64\ssh-add.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225785 Version: 10.0.0.0 Modules
| |||||||||||||||
| 1212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sshd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ssh-sk-helper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1848 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\OpenSSH-Win64/FixHostFilePermissions.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2232 | "C:\Users\admin\Desktop\OpenSSH-Win64\ssh.exe" | C:\Users\admin\Desktop\OpenSSH-Win64\ssh.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225785 Version: 10.0.0.0 Modules
| |||||||||||||||
| 2868 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sshd-session.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2900 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sftp-server.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3232 | "C:\Users\admin\Desktop\OpenSSH-Win64\sshd-session.exe" | C:\Users\admin\Desktop\OpenSSH-Win64\sshd-session.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 255 Version: 10.0.0.0 Modules
| |||||||||||||||
Total events
39 754
Read events
39 754
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
17
Text files
12
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1e4e7b.TMP | binary | |
MD5:00A03B286E6E0EBFF8D9C492365D5EC2 | SHA256:4DBFC417D053BA6867308671F1C61F4DCAFC61F058D4044DB532DA6D3BDE3615 | |||
| 5080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\315I4PMGXR6D1AEQ5UJF.temp | binary | |
MD5:089670F607820BC2AB896C55025926DD | SHA256:F399F3D0A4A7CBBA47A354FBE83A5260335133186AF6C9A0EAD02D4E76A767AB | |||
| 5080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:089670F607820BC2AB896C55025926DD | SHA256:F399F3D0A4A7CBBA47A354FBE83A5260335133186AF6C9A0EAD02D4E76A767AB | |||
| 8308 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gwwfrh1g.fb4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\OpenSSH-Win64.zip | compressed | |
MD5:27D4C78392AC7D77DCB641436969A5DE | SHA256:23F50F3458C4C5D0B12217C6A5DDFDE0137210A30FA870E98B29827F7B43ABA5 | |||
| 8308 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1f1239.TMP | binary | |
MD5:089670F607820BC2AB896C55025926DD | SHA256:F399F3D0A4A7CBBA47A354FBE83A5260335133186AF6C9A0EAD02D4E76A767AB | |||
| 1848 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4POALU1G40P2TH4CGUKM.temp | binary | |
MD5:FC58BC2496EEF22F69082FDA8560DD1A | SHA256:E018201C0C8AEE2062152D4278B69642F3C227951A8896ABE7A105C5CC83B772 | |||
| 8308 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ybk0zudq.l4l.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1848 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1f16dc.TMP | binary | |
MD5:A3B039F26C08E11A008C5CA4D8D91452 | SHA256:018373BD81200888537213180C31105E91698A8063358CF4FE886C0605C7380A | |||
| 1848 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sv3zgfzk.psz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
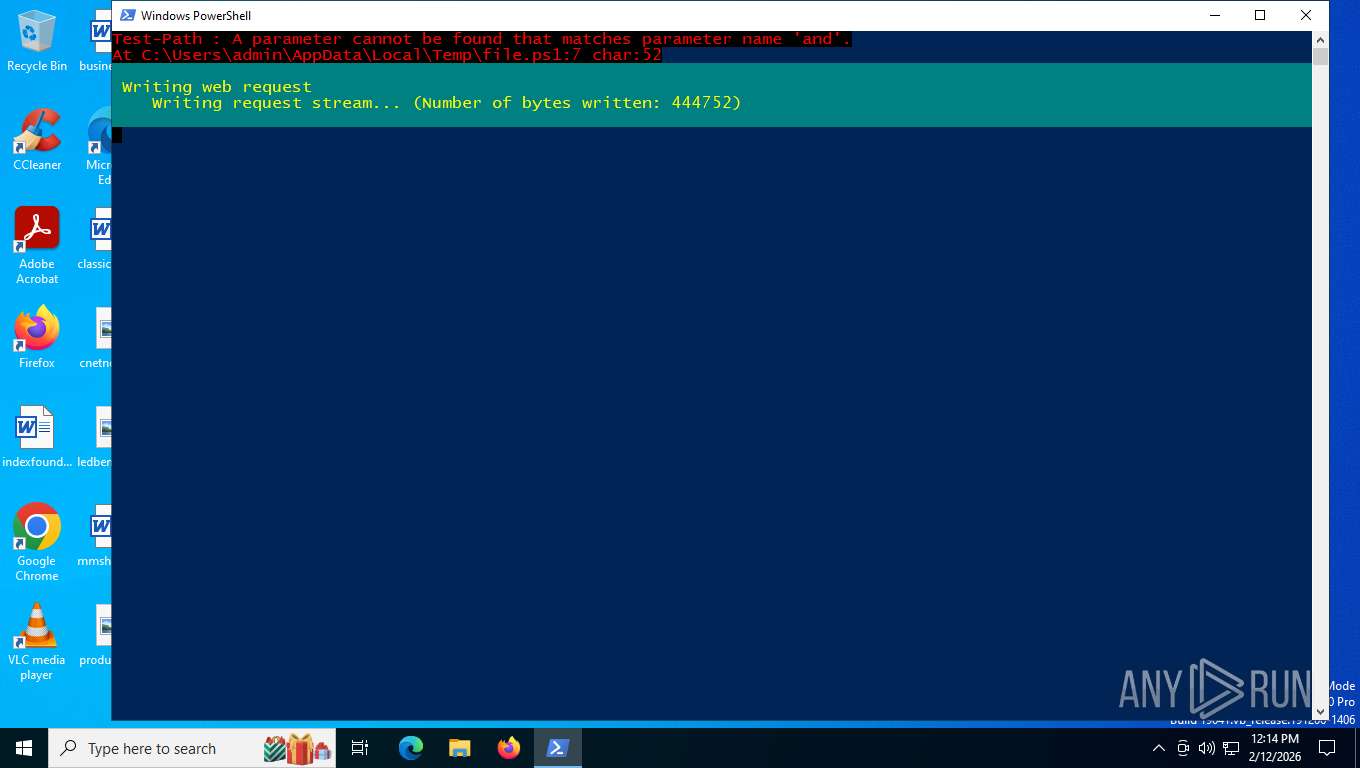
HTTP(S) requests
29
TCP/UDP connections
31
DNS requests
23
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5080 | powershell.exe | GET | 302 | 140.82.121.3:443 | https://github.com/PowerShell/Win32-OpenSSH/releases/latest/download/OpenSSH-Win64.zip | unknown | — | — | unknown |
5080 | powershell.exe | GET | 302 | 140.82.121.3:443 | https://github.com/PowerShell/Win32-OpenSSH/releases/download/10.0.0.0p2-Preview/OpenSSH-Win64.zip | unknown | — | — | unknown |
6768 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
4936 | svchost.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
4724 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
4724 | SIHClient.exe | GET | 200 | 20.242.39.171:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
4724 | SIHClient.exe | GET | 200 | 135.232.92.137:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
4724 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
3292 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4936 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7588 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 92.123.104.16:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5080 | powershell.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
github.com |
| whitelisted |
release-assets.githubusercontent.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
5080 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5080 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
4936 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
5080 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |