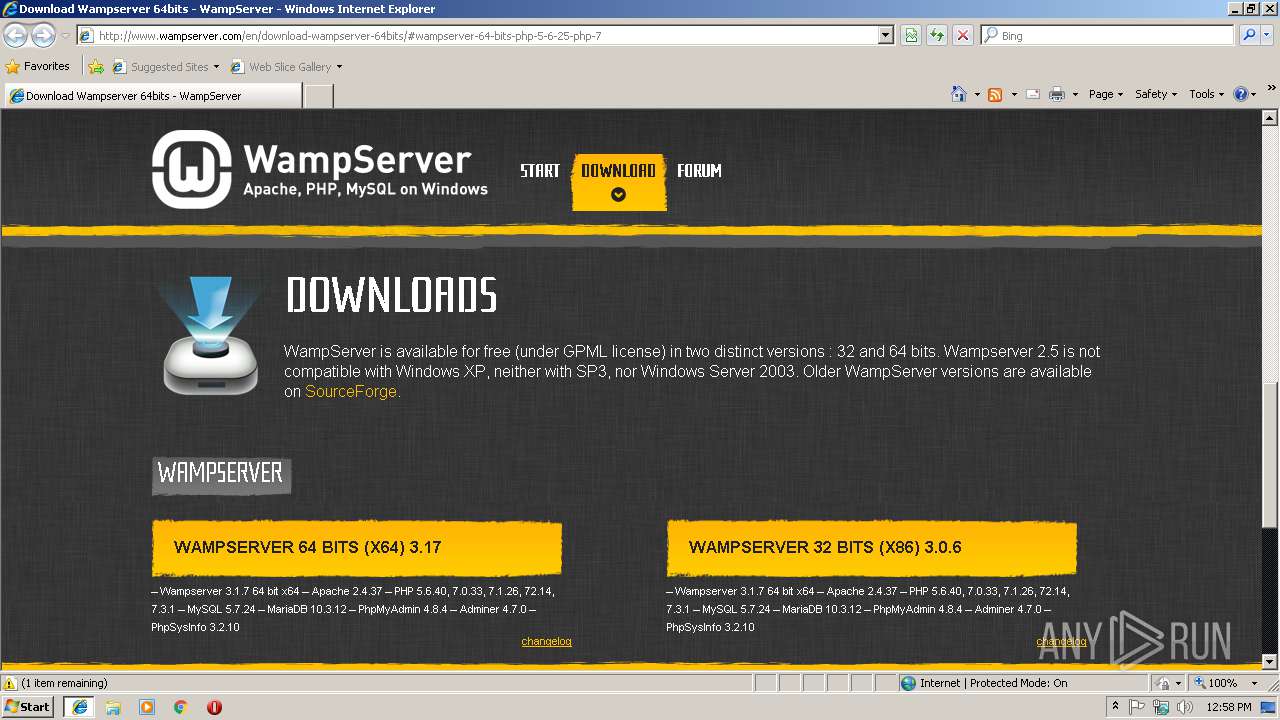
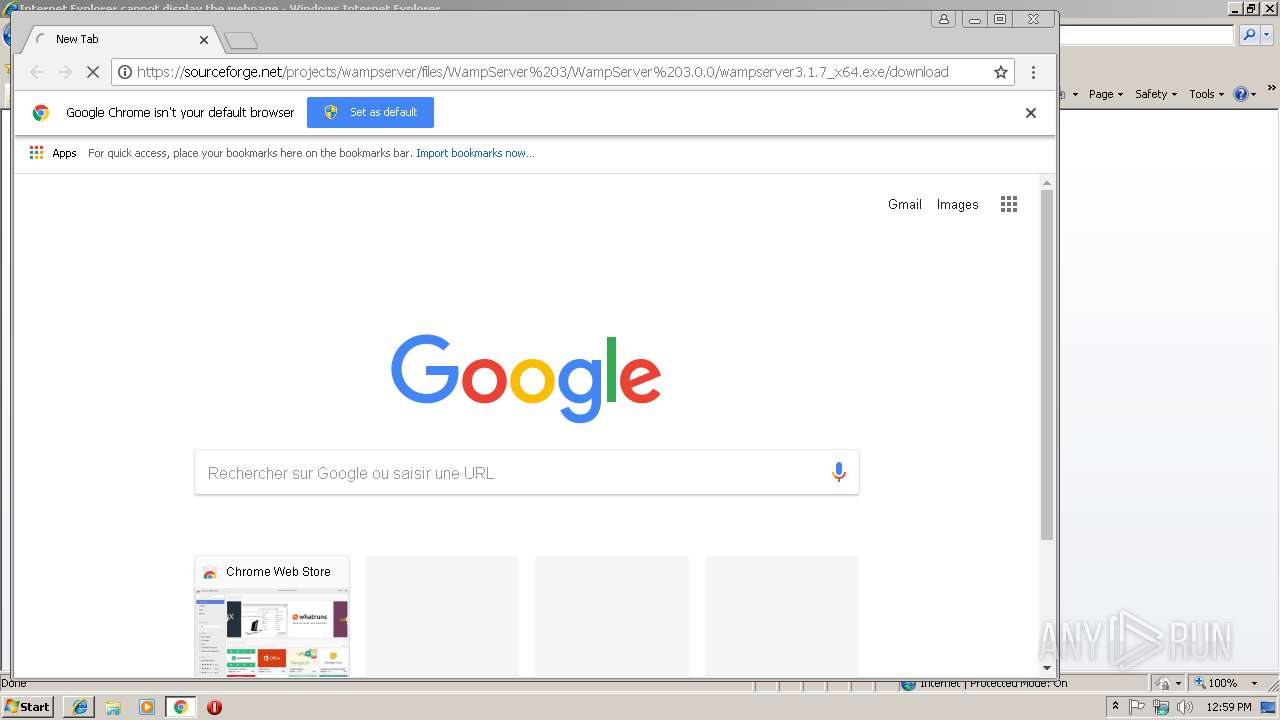
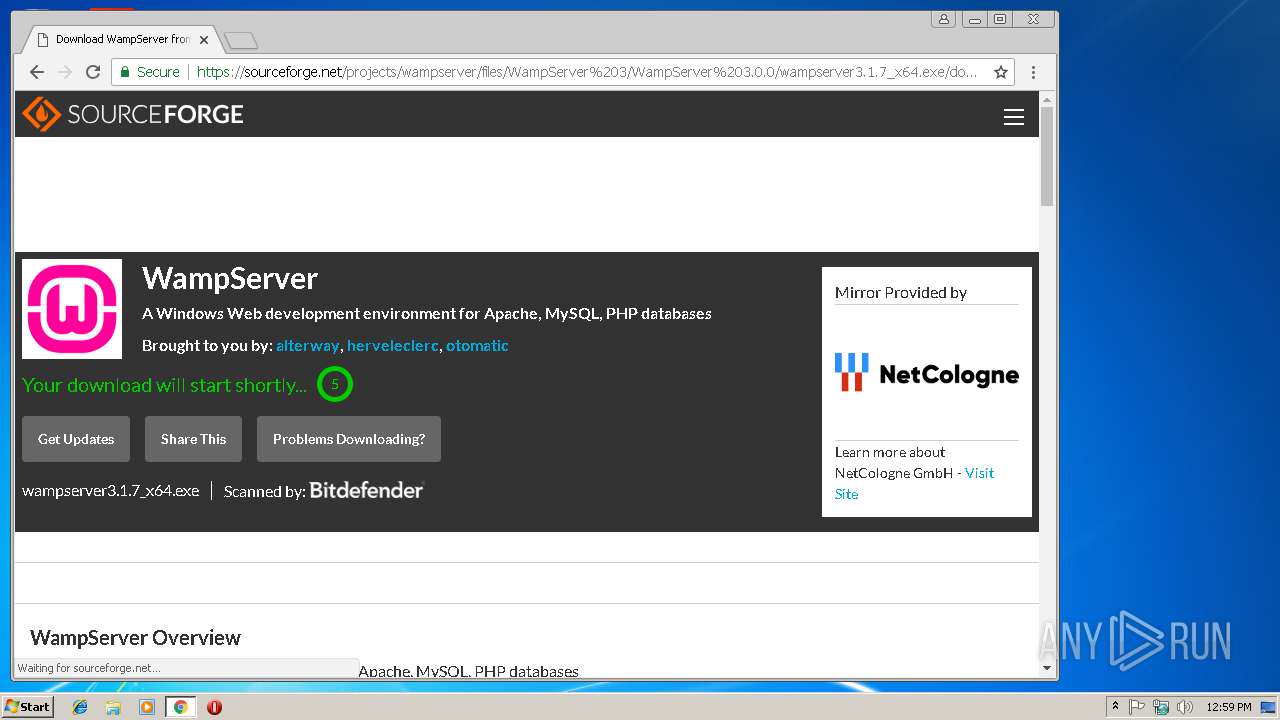
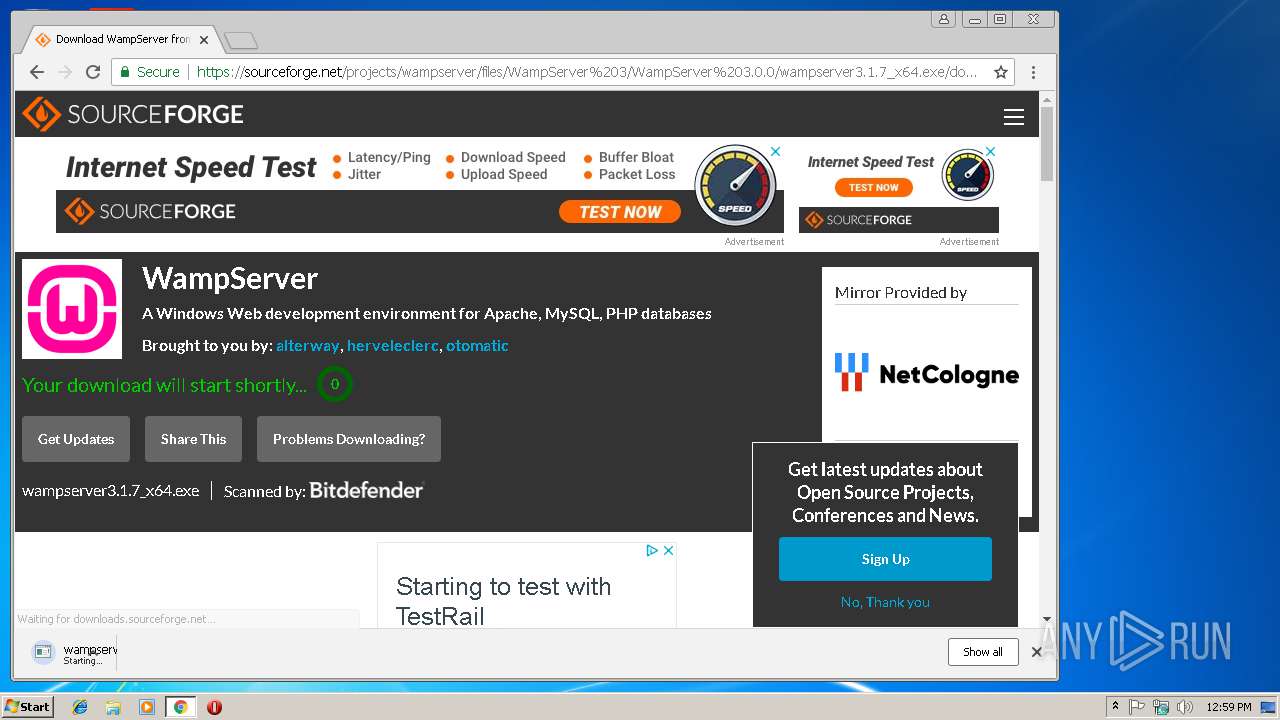
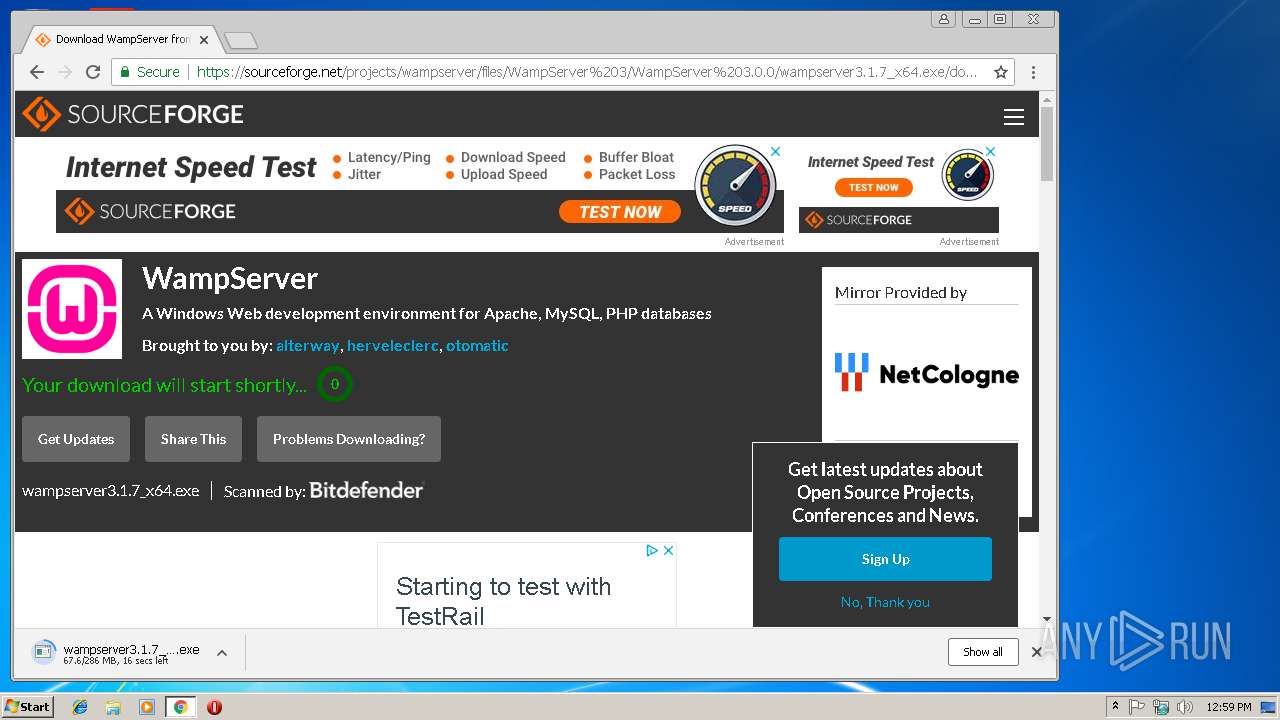
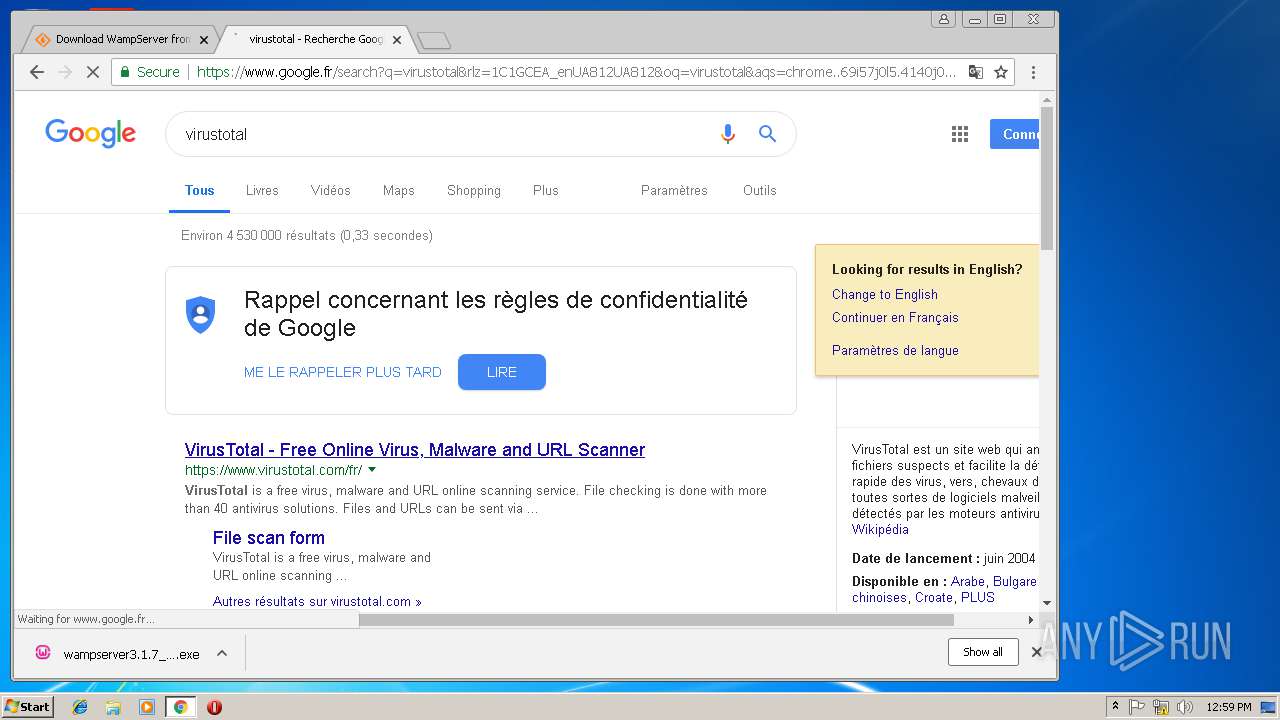
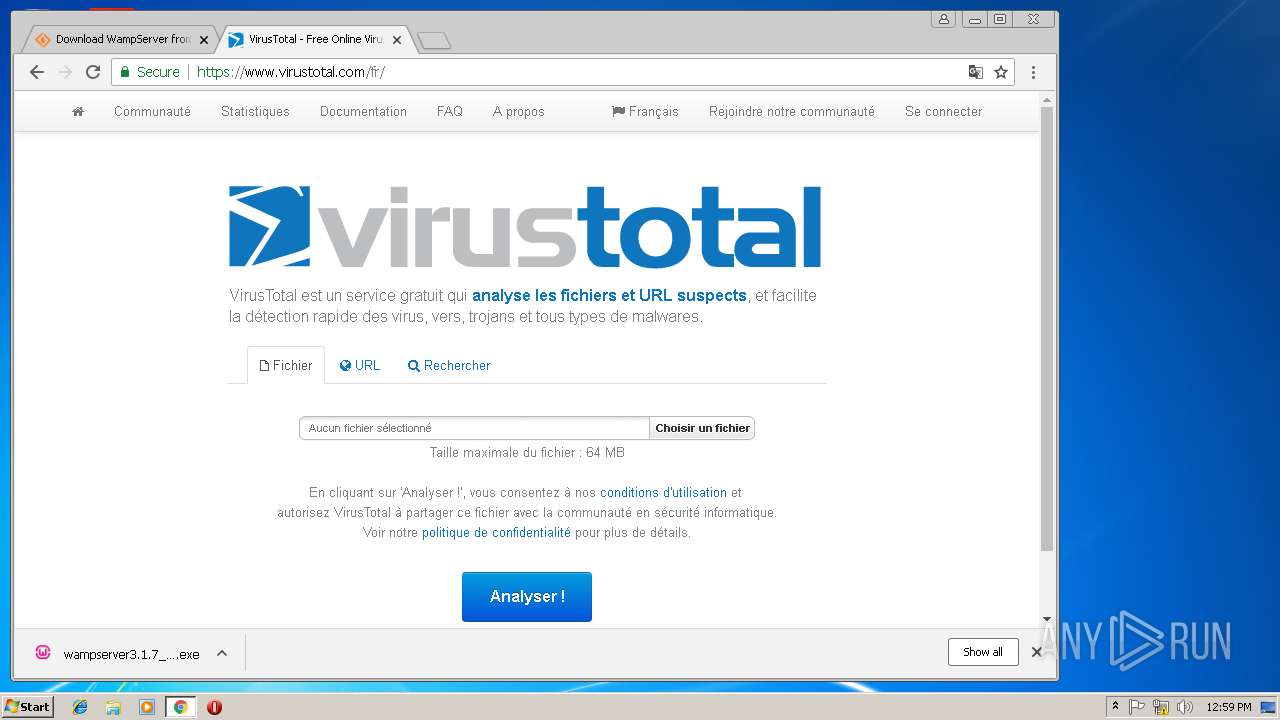
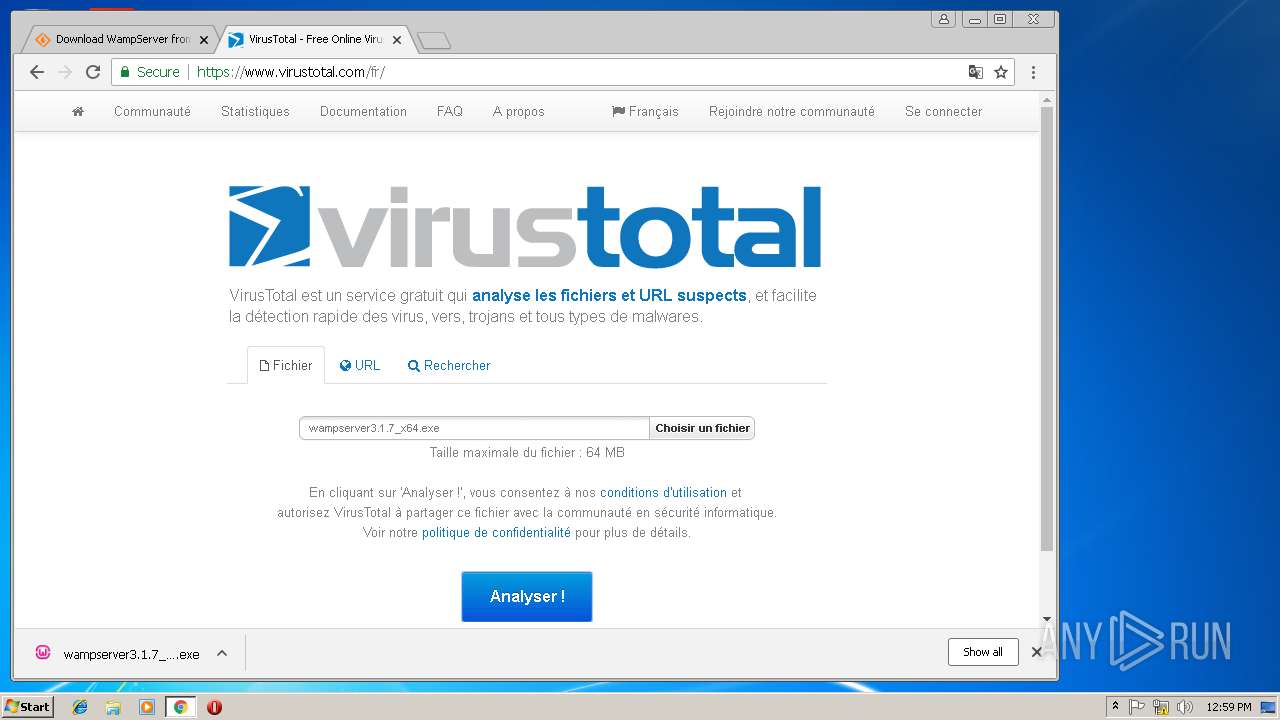
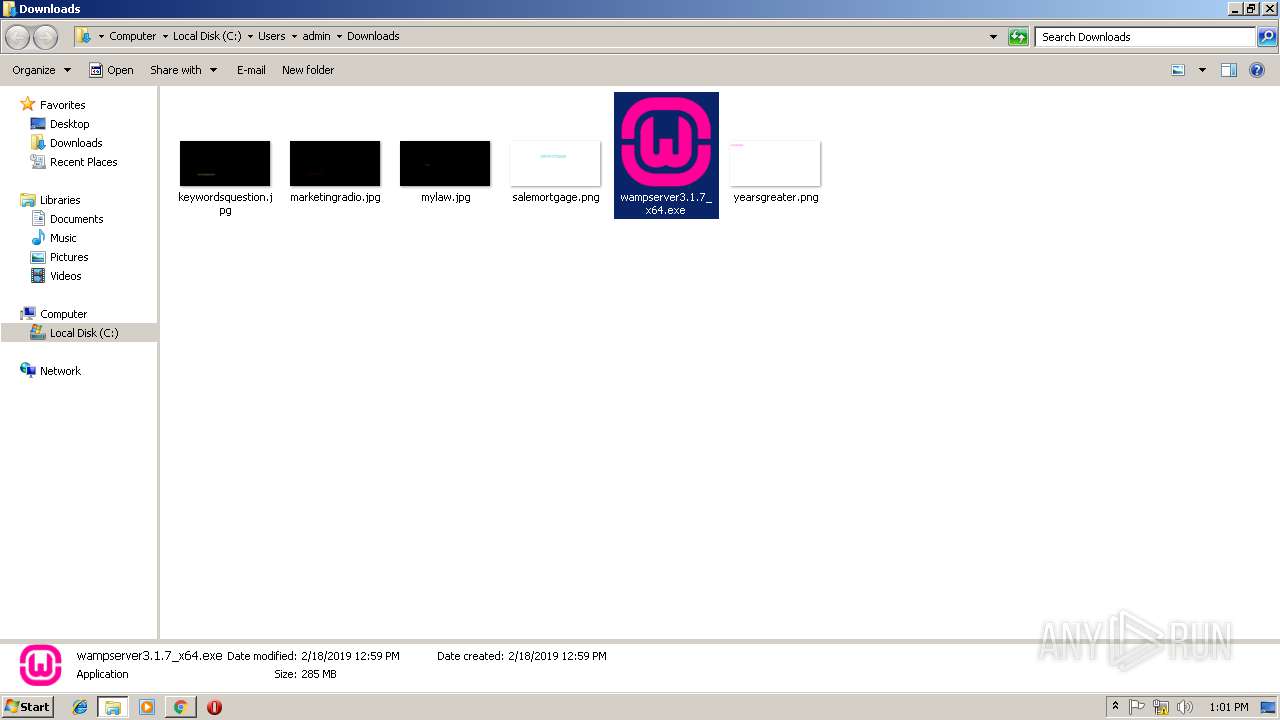
| URL: | http://www.wampserver.com/en/download-wampserver-64bits/#wampserver-64-bits-php-5-6-25-php-7 |
| Full analysis: | https://app.any.run/tasks/70ab36fd-a9bd-47db-958e-aa3909da680f |
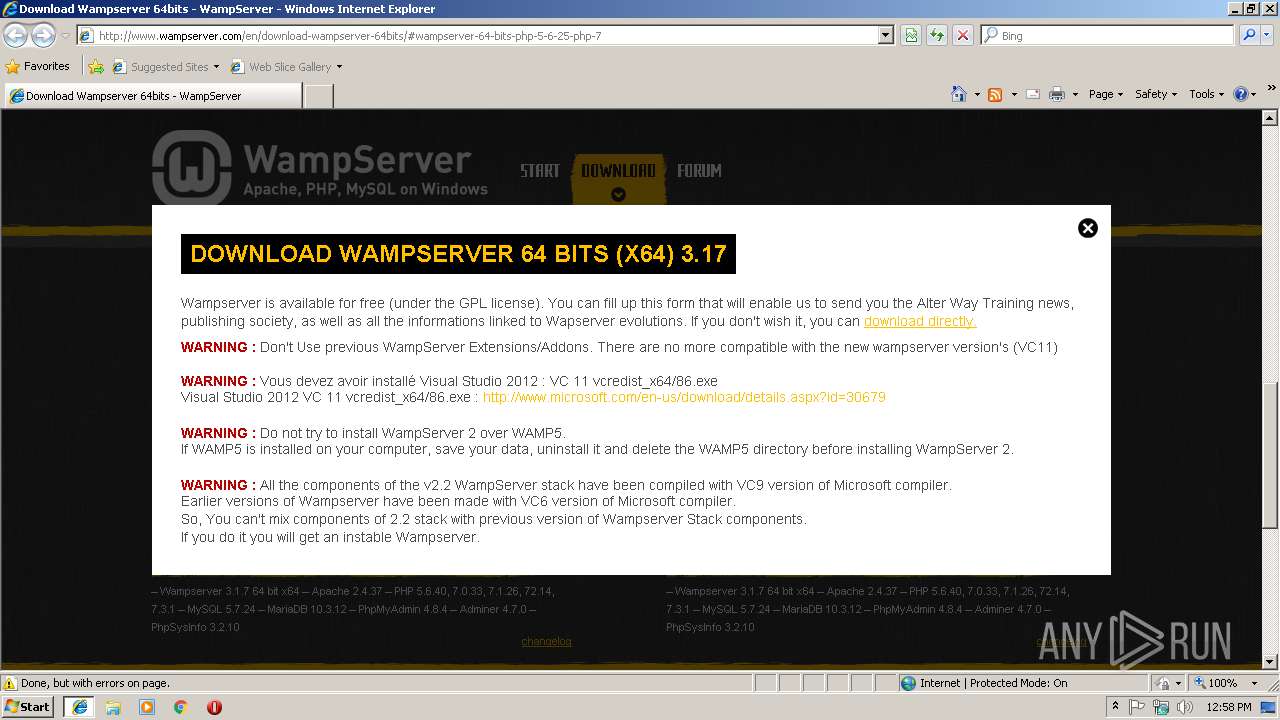
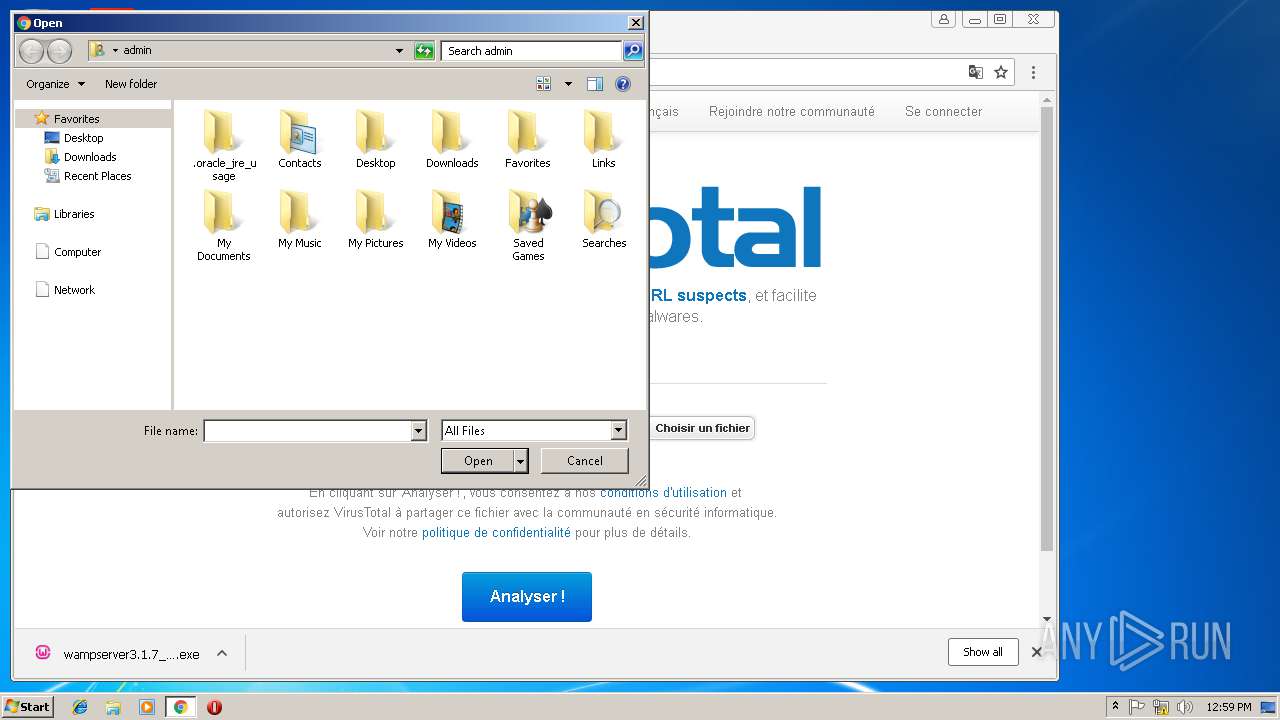
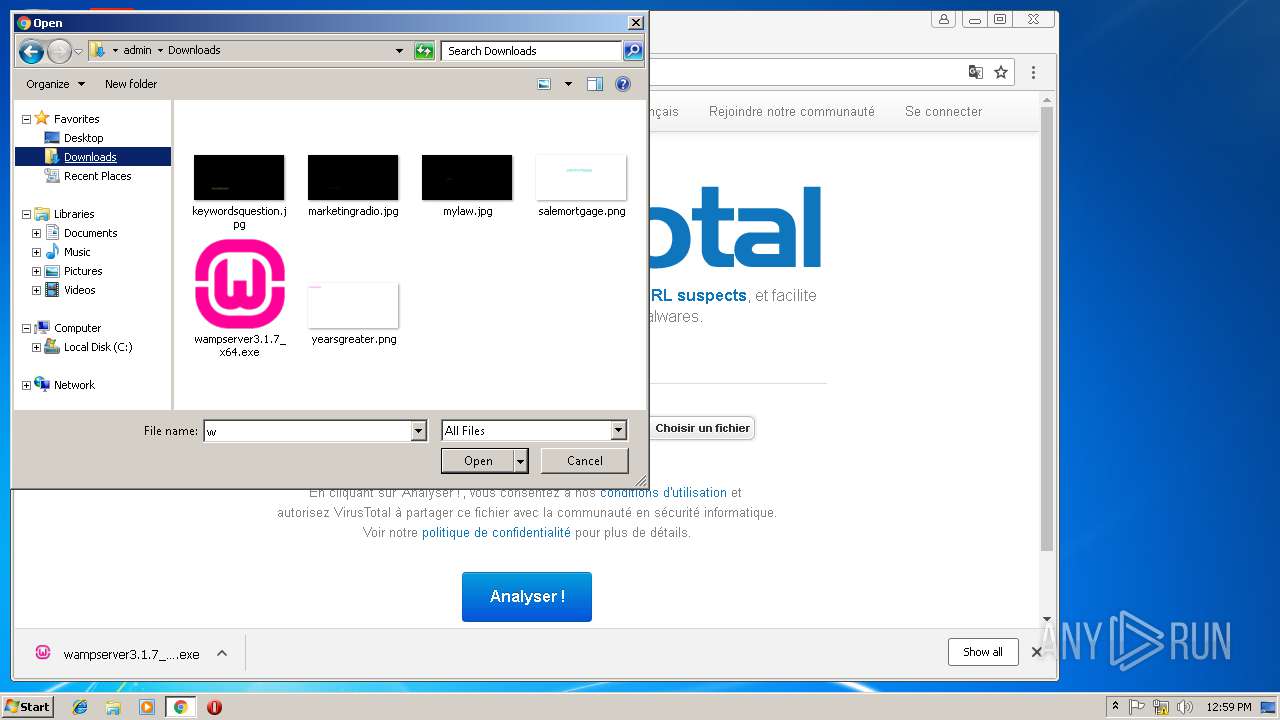
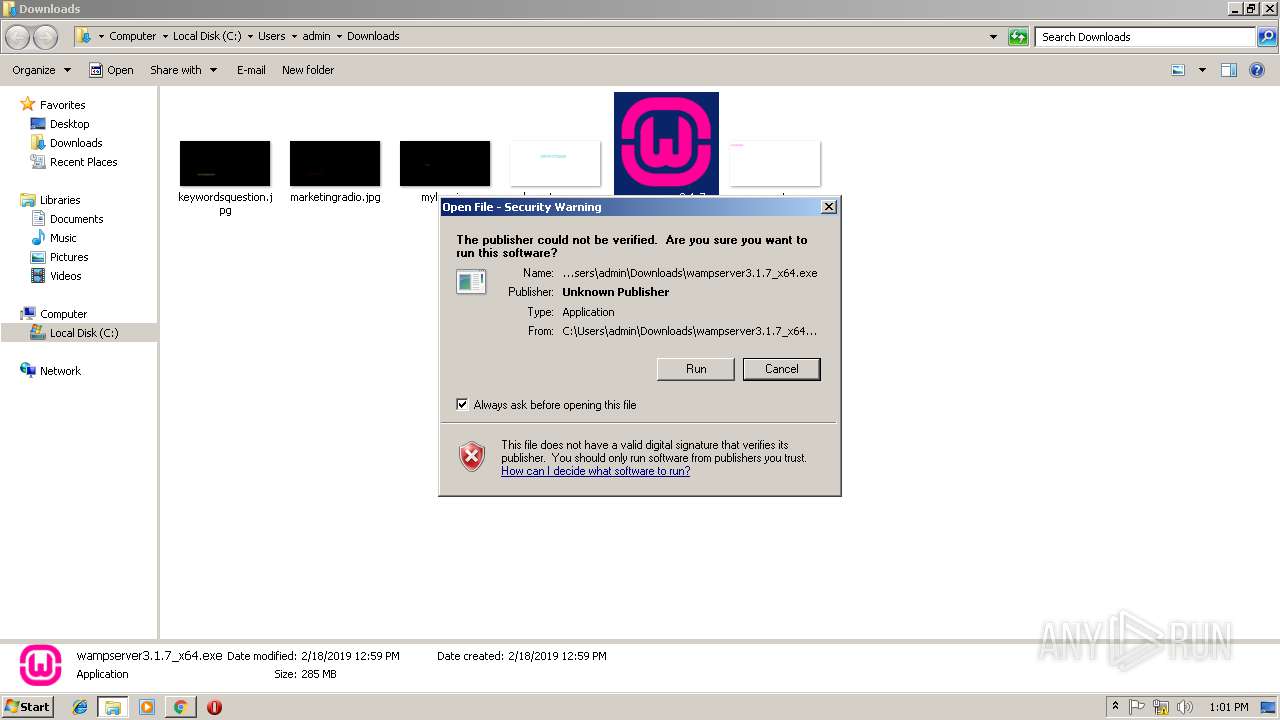
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 12:58:25 |
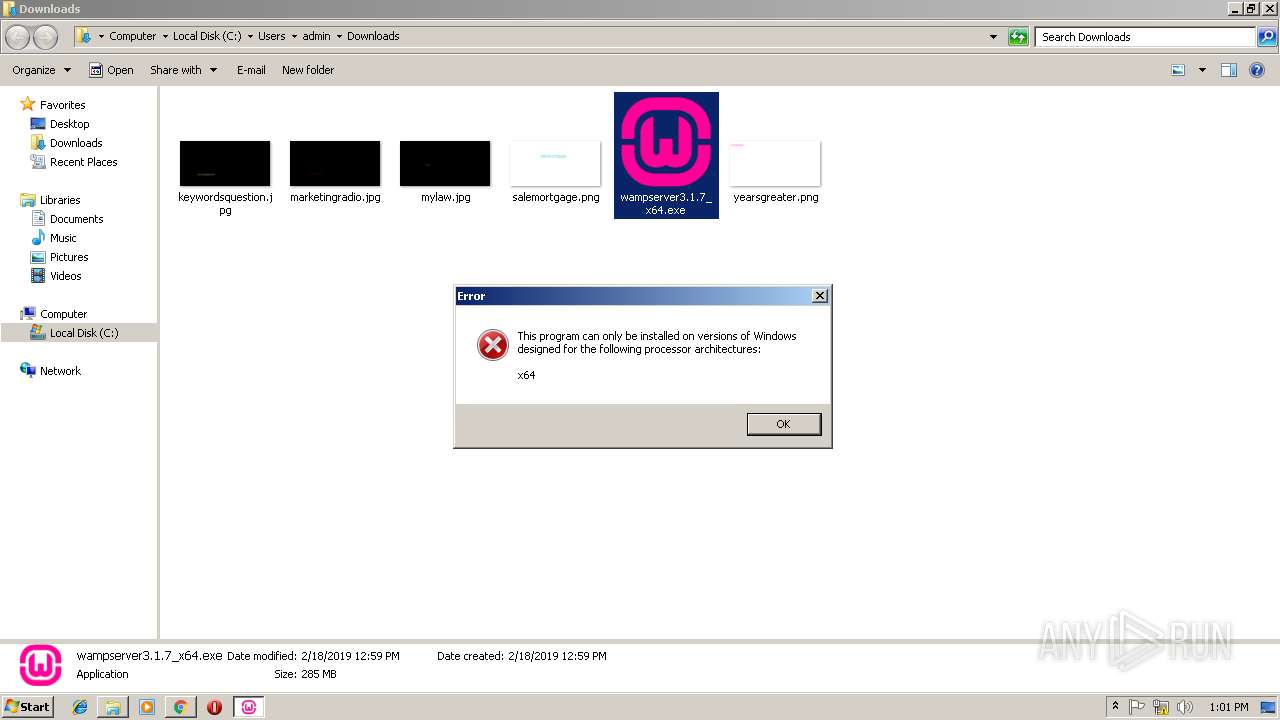
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BC8C7AB9BAA91B5CE8DD3E471340D9CE |
| SHA1: | 6C54E9F5ADAF15BAB32DAC7AF5812F7D41D4A068 |
| SHA256: | 351C435A7365AF958FFBF99A9E2D15F40AD0A459EF1C4EE1F56A05E5EB9480AE |
| SSDEEP: | 3:N1KJS4YWADSBKSASEchQWdS/usLVv:Cc4YjSB5E4Dsxv |
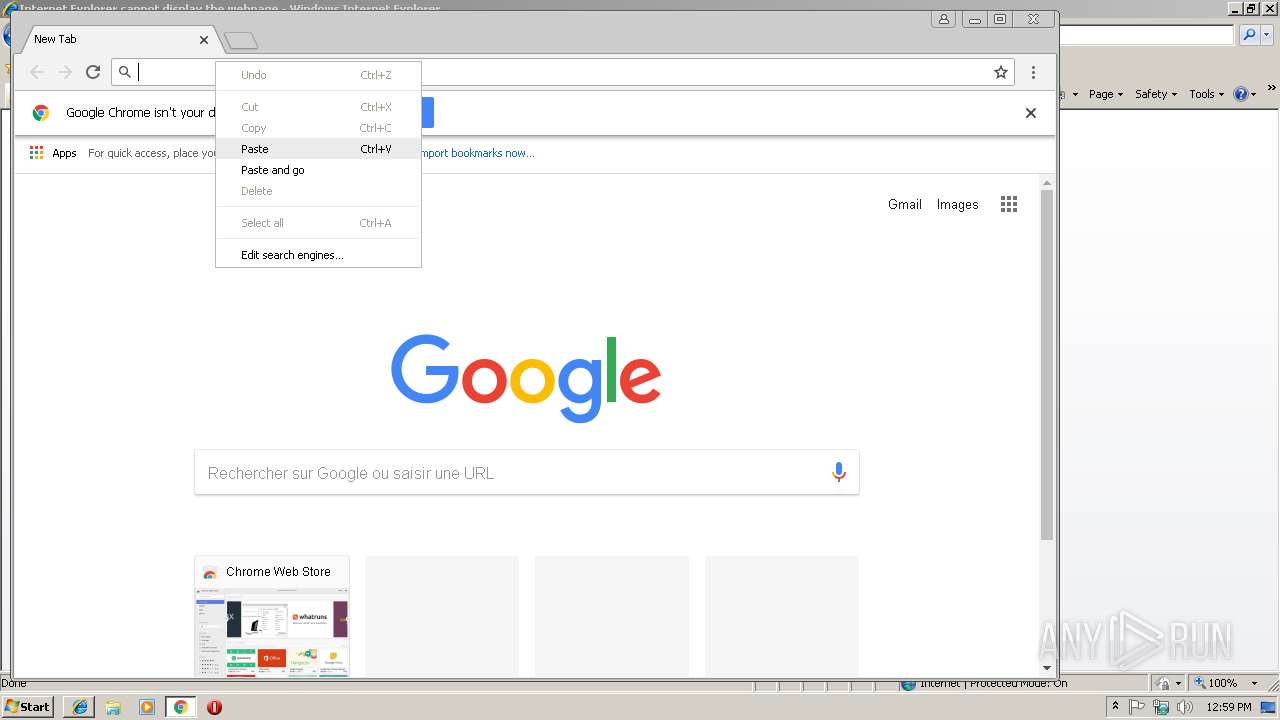
MALICIOUS
Application was dropped or rewritten from another process
- wampserver3.1.7_x64.exe (PID: 3272)
- wampserver3.1.7_x64.exe (PID: 3772)
SUSPICIOUS
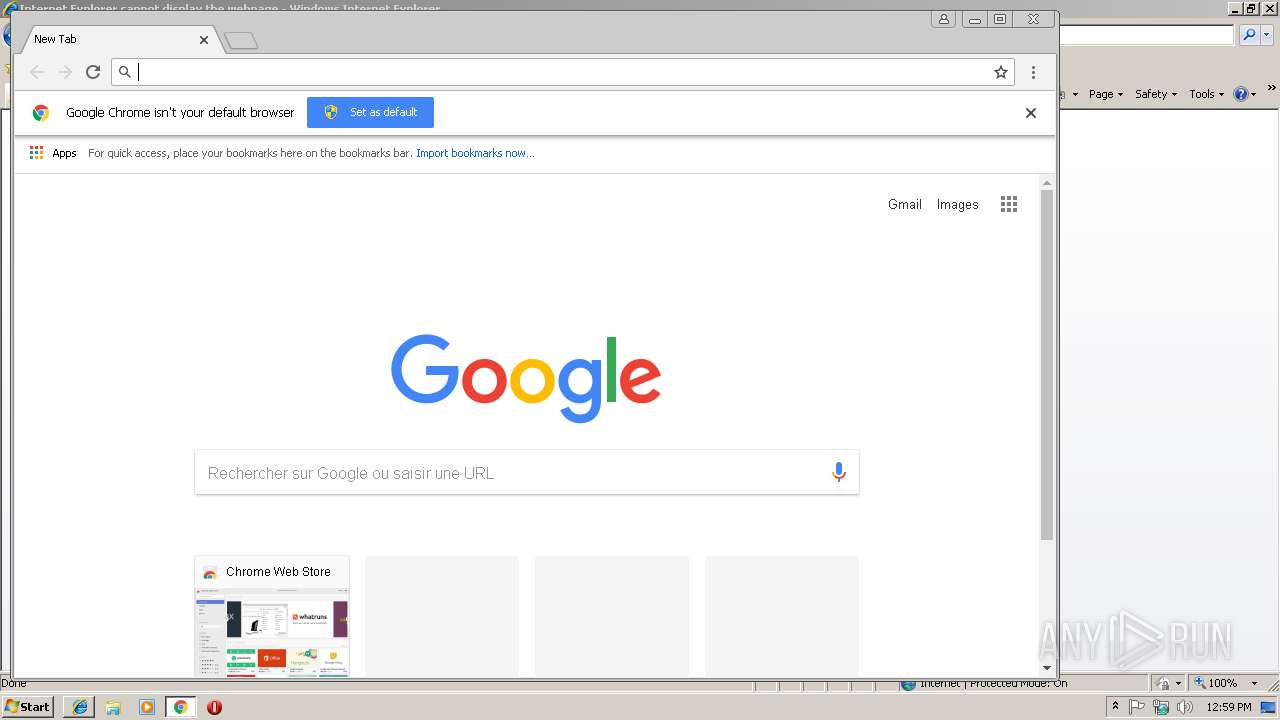
Executable content was dropped or overwritten
- chrome.exe (PID: 2928)
- wampserver3.1.7_x64.exe (PID: 3772)
- wampserver3.1.7_x64.exe (PID: 3272)
INFO
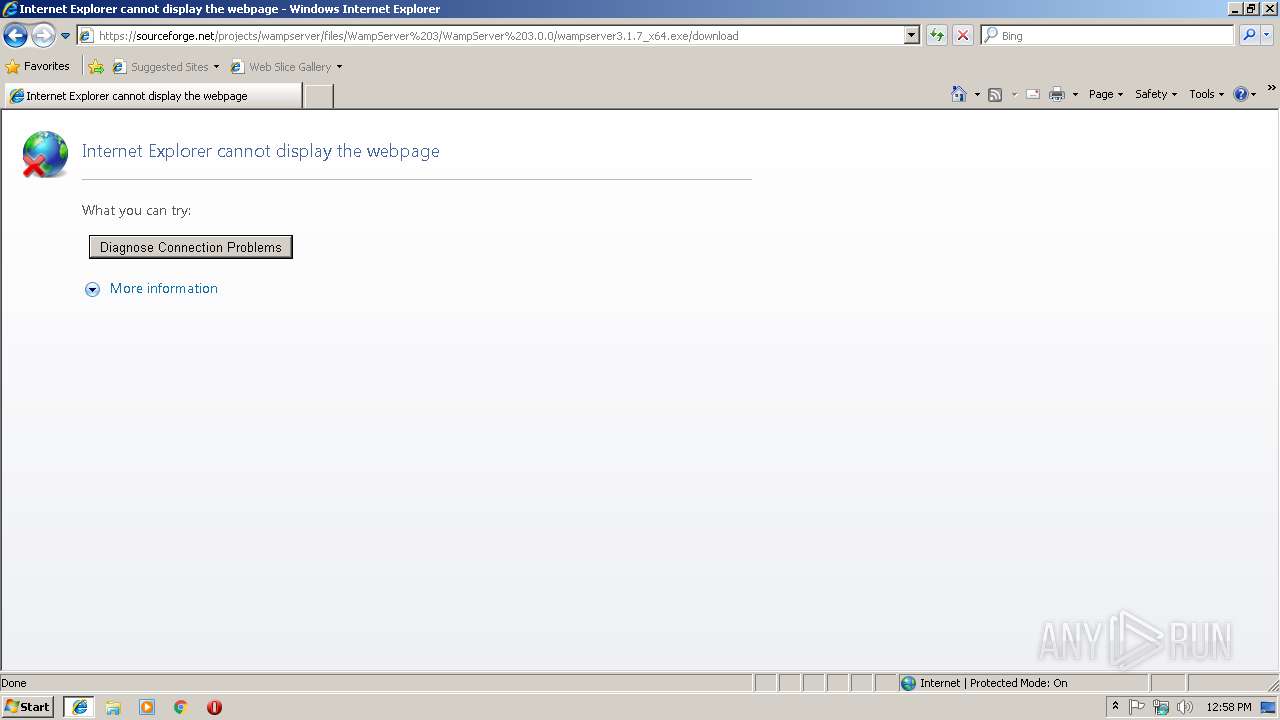
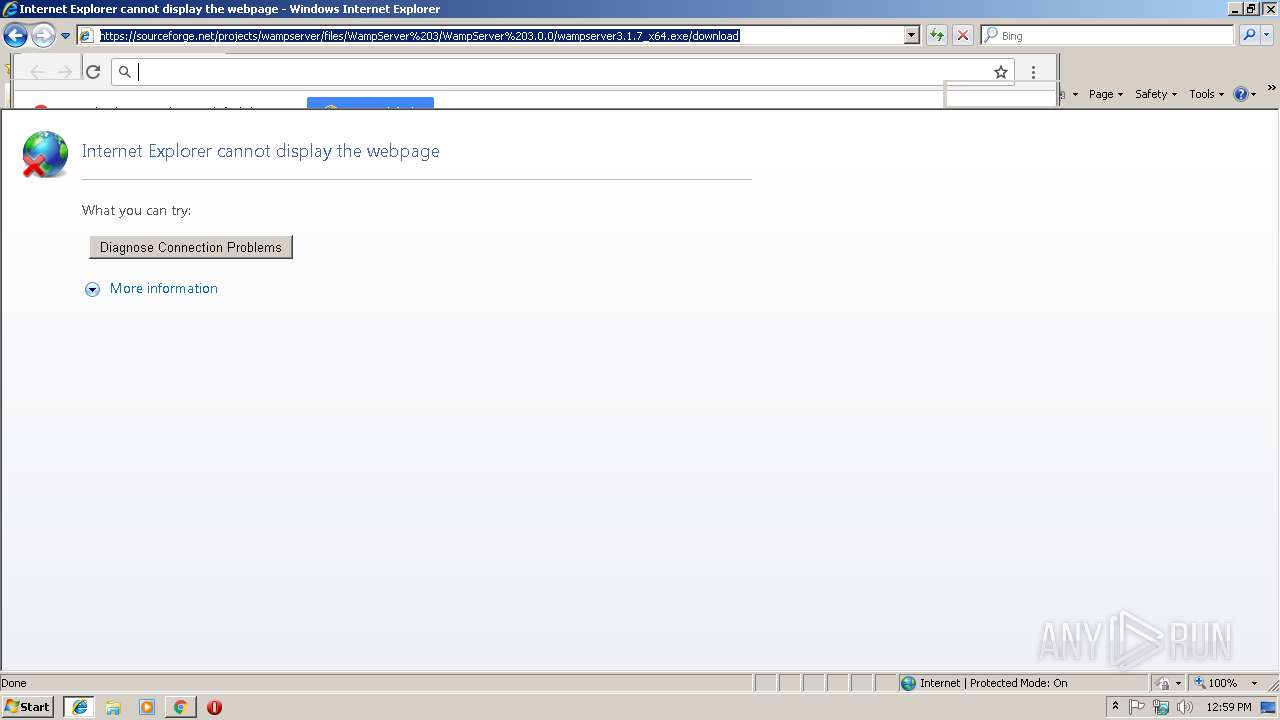
Reads internet explorer settings
- iexplore.exe (PID: 3236)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3724)
- iexplore.exe (PID: 3236)
Application launched itself
- iexplore.exe (PID: 2964)
- chrome.exe (PID: 2928)
Changes internet zones settings
- iexplore.exe (PID: 2964)
Reads Internet Cache Settings
- iexplore.exe (PID: 3236)
- chrome.exe (PID: 2928)
Changes settings of System certificates
- chrome.exe (PID: 2928)
Reads settings of System Certificates
- chrome.exe (PID: 2928)
- iexplore.exe (PID: 3236)
Application was dropped or rewritten from another process
- wampserver3.1.7_x64.tmp (PID: 2720)
- wampserver3.1.7_x64.tmp (PID: 3700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
25
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,12997756325858415940,8452646692784825825,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=82AF283611558CD28DF9739A8BA38ABF --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=82AF283611558CD28DF9739A8BA38ABF --renderer-client-id=10 --mojo-platform-channel-handle=3932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,12997756325858415940,8452646692784825825,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=B9ADB2324579FC8511868FBB3187EA7C --mojo-platform-channel-handle=512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,12997756325858415940,8452646692784825825,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=0D9C7DB964737E8D3F9ACB8C8134D86A --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0D9C7DB964737E8D3F9ACB8C8134D86A --renderer-client-id=6 --mojo-platform-channel-handle=3108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,12997756325858415940,8452646692784825825,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9563CC72CDEE3FA8E1C5D410650BA11A --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9563CC72CDEE3FA8E1C5D410650BA11A --renderer-client-id=9 --mojo-platform-channel-handle=3940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=920,12997756325858415940,8452646692784825825,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=2273959E5F57BCFC7BB6A3357F845880 --mojo-platform-channel-handle=4212 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,12997756325858415940,8452646692784825825,131072 --enable-features=PasswordImport --service-pipe-token=C2B2CAA750CCA8700BA5DB34EB97EC91 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C2B2CAA750CCA8700BA5DB34EB97EC91 --renderer-client-id=3 --mojo-platform-channel-handle=1528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=920,12997756325858415940,8452646692784825825,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=DD10797A961329527B3B0911CB41DE7A --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,12997756325858415940,8452646692784825825,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6080D2C389610C68EE8DE6EAB9933D78 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6080D2C389610C68EE8DE6EAB9933D78 --renderer-client-id=17 --mojo-platform-channel-handle=3656 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,12997756325858415940,8452646692784825825,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7E2D189F16EB829EAE88FBE1811EF16D --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7E2D189F16EB829EAE88FBE1811EF16D --renderer-client-id=7 --mojo-platform-channel-handle=3712 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
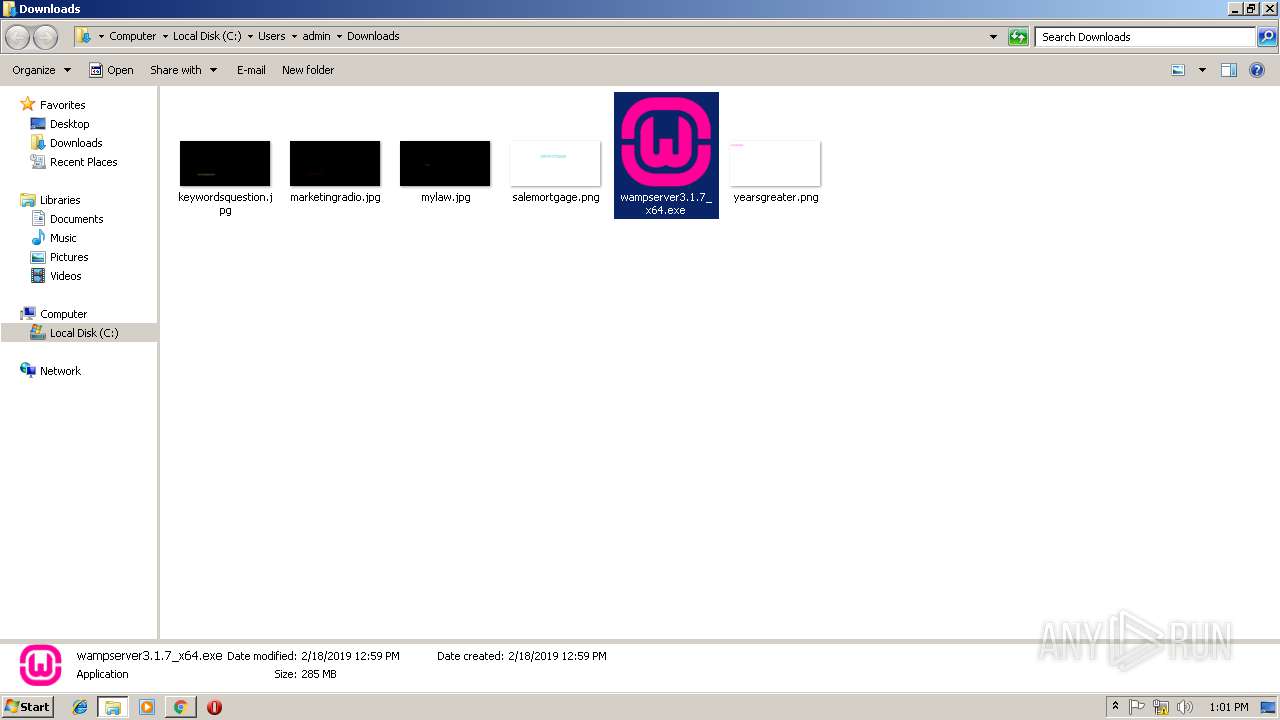
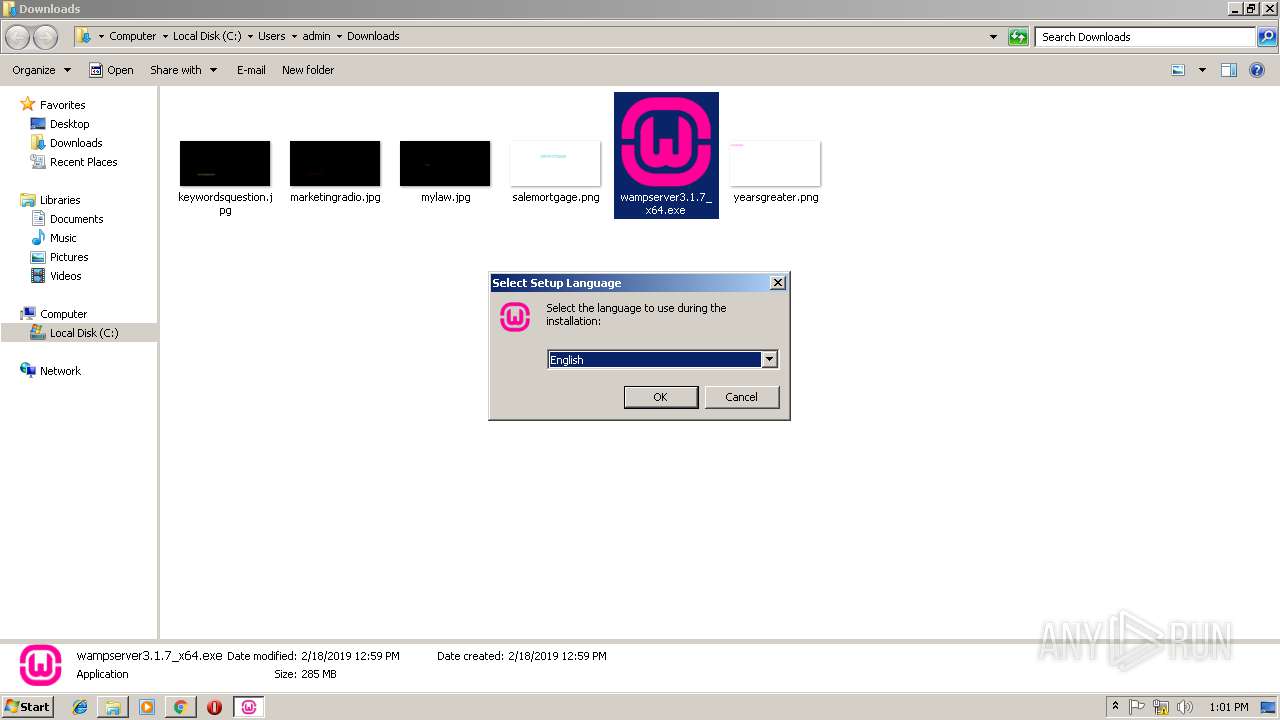
| 2720 | "C:\Users\admin\AppData\Local\Temp\is-ODICJ.tmp\wampserver3.1.7_x64.tmp" /SL5="$5015C,298722124,320000,C:\Users\admin\Downloads\wampserver3.1.7_x64.exe" | C:\Users\admin\AppData\Local\Temp\is-ODICJ.tmp\wampserver3.1.7_x64.tmp | — | wampserver3.1.7_x64.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
2 024
Read events
1 781
Write events
234
Delete events
9
Modification events
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {E9D2BF9B-337C-11E9-AA93-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070200010012000C003A0029008403 | |||
Executable files
3
Suspicious files
142
Text files
214
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\download-wampserver-64bits[1].txt | — | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\jquery.nav.min[1].js | text | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\language-selector[1].css | text | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\download-wampserver-64bits[1].htm | html | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@www.wampserver[1].txt | text | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 3236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\jquery.feedback[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
135
DNS requests
92
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3236 | iexplore.exe | GET | 200 | 89.31.144.71:80 | http://www.wampserver.com/wp-content/plugins/sitepress-multilingual-cms/res/css/language-selector.css?v=2.6.0 | FR | text | 1.45 Kb | suspicious |
3236 | iexplore.exe | GET | 200 | 89.31.144.71:80 | http://www.wampserver.com/wp-content/themes/wampserver/style.css | FR | text | 216 b | suspicious |
3236 | iexplore.exe | GET | 200 | 216.58.207.74:80 | http://fonts.googleapis.com/css?family=Rationale | US | text | 163 b | whitelisted |
3236 | iexplore.exe | GET | 200 | 89.31.144.71:80 | http://www.wampserver.com/wp-content/plugins/lightbox-plus/css/shadowed/colorbox.min.css?ver=2.7.2 | FR | text | 987 b | suspicious |
3236 | iexplore.exe | GET | 200 | 89.31.144.71:80 | http://www.wampserver.com/wp-content/themes/wampserver/js/localscroll/jquery.nav.min.js | FR | text | 849 b | suspicious |
3236 | iexplore.exe | GET | 200 | 23.210.248.44:80 | http://s7.addthis.com/js/250/addthis_widget.js | NL | text | 111 Kb | whitelisted |
3236 | iexplore.exe | GET | 200 | 89.31.144.71:80 | http://www.wampserver.com/wp-content/themes/wampserver/js/jquery.feedback.js | FR | text | 1.60 Kb | suspicious |
3236 | iexplore.exe | GET | 200 | 89.31.144.71:80 | http://www.wampserver.com/wp-content/themes/wampserver/js/jquery.fancybox-1.3.4.pack.js | FR | text | 5.47 Kb | suspicious |
3236 | iexplore.exe | GET | 200 | 89.31.144.71:80 | http://www.wampserver.com/wp-content/themes/wampserver/css/colorbox.css | FR | text | 874 b | suspicious |
3236 | iexplore.exe | GET | 200 | 89.31.144.71:80 | http://www.wampserver.com/wp-content/themes/wampserver/js/lancement.js | FR | text | 274 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3236 | iexplore.exe | 89.31.144.71:80 | www.wampserver.com | Alter Way Hosting SAS | FR | unknown |
3236 | iexplore.exe | 216.58.205.234:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3236 | iexplore.exe | 216.58.207.74:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3236 | iexplore.exe | 23.210.248.44:80 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
3236 | iexplore.exe | 172.217.23.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3236 | iexplore.exe | 31.13.90.6:80 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3236 | iexplore.exe | 172.217.23.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3236 | iexplore.exe | 31.13.90.6:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2964 | iexplore.exe | 89.31.144.71:80 | www.wampserver.com | Alter Way Hosting SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.wampserver.com |
| suspicious |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
www.facebook.com |
| whitelisted |
sourceforge.net |
| whitelisted |