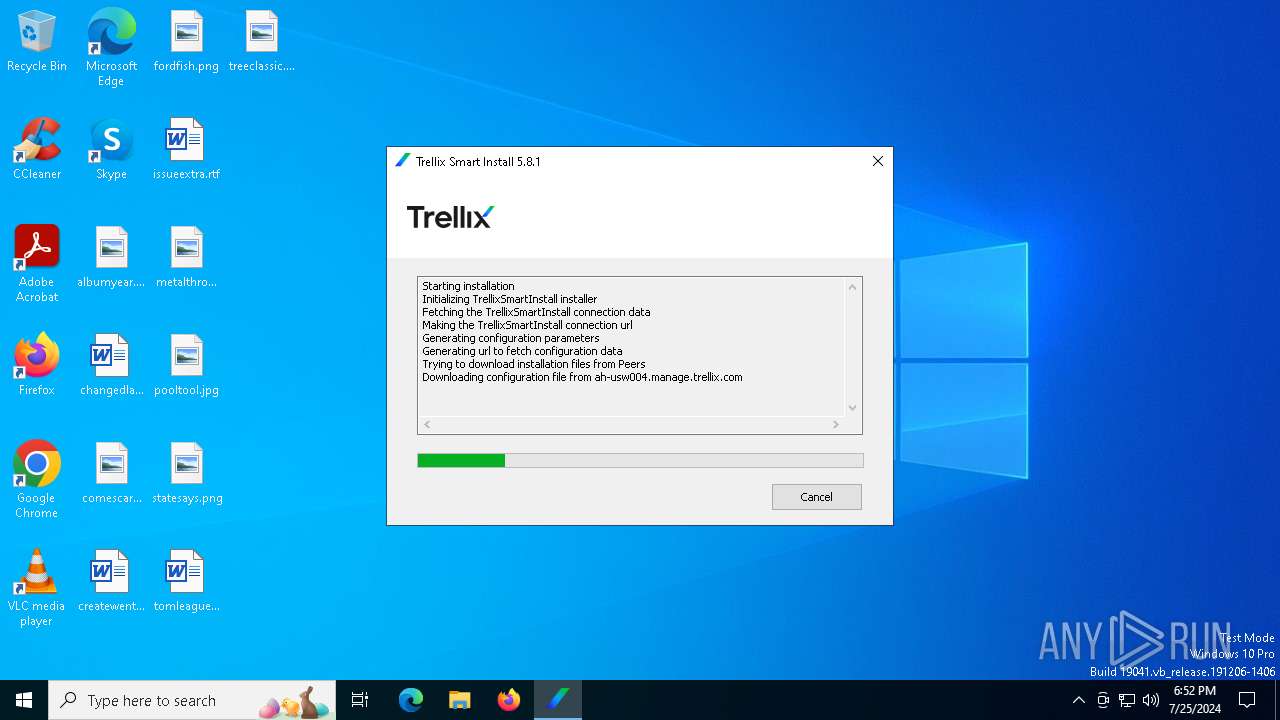
| File name: | TrellixSmartInstall.exe |
| Full analysis: | https://app.any.run/tasks/46f6ca1a-908d-4fee-a728-f7f6303e2374 |
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2024, 18:52:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | AA0D22C4F3129F81AA75CB8CD530A13D |
| SHA1: | F3BB815F346EF99283475F351AC73D84F25A7661 |
| SHA256: | 351AD51DB1F7476608D8CEA391C6A92964539C26B1419300419815E635BFFE7B |
| SSDEEP: | 49152:7Pn0vzOdauelEjZRXuB42Ym+PmjOFD6Vw6W6peszMNY1Yp1FvZ+ua/BvuyLVWJHA:7Pn0xlEjZR+B3JimjW7YoPvAZ/dPR2HA |
MALICIOUS
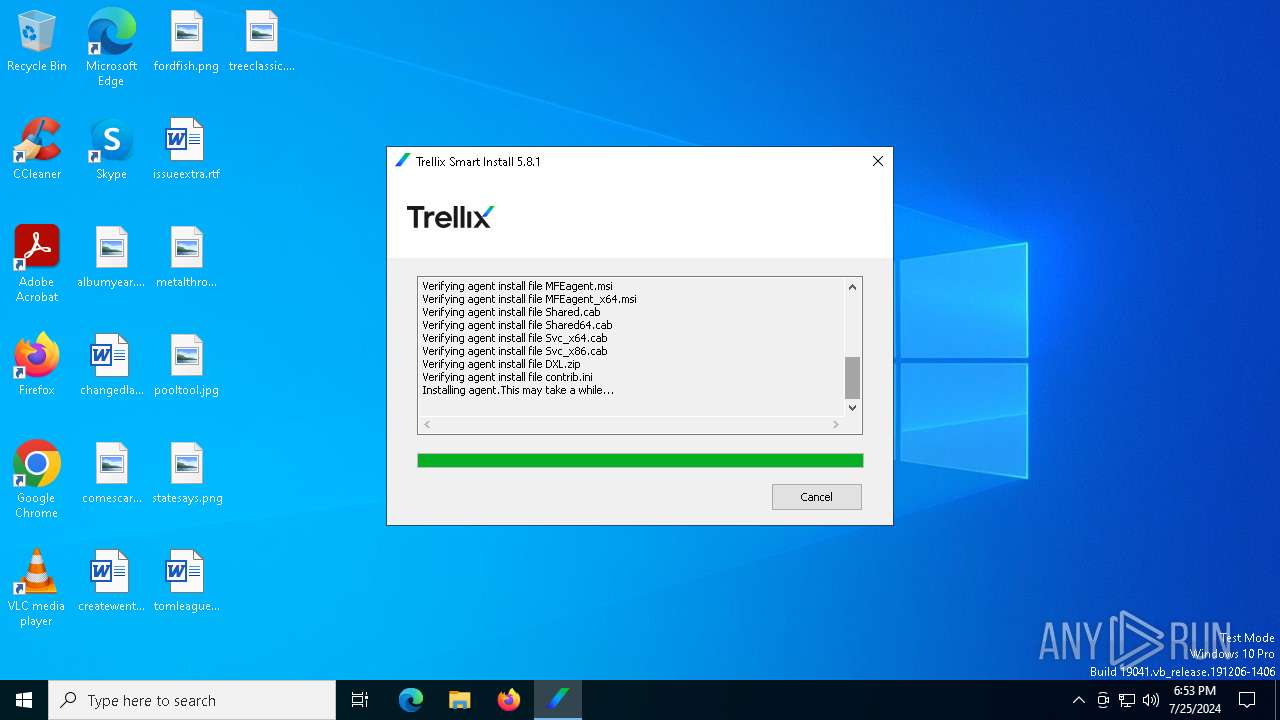
Drops the executable file immediately after the start
- TrellixSmartInstall.exe (PID: 6440)
- FrmInst.exe (PID: 6656)
- msiexec.exe (PID: 3572)
Changes the autorun value in the registry
- msiexec.exe (PID: 3572)
SUSPICIOUS
Checks Windows Trust Settings
- msiexec.exe (PID: 3572)
- mfemactl.exe (PID: 4476)
- msiexec.exe (PID: 6928)
- FrmInst.exe (PID: 6656)
Executable content was dropped or overwritten
- FrmInst.exe (PID: 6656)
- TrellixSmartInstall.exe (PID: 6440)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3572)
The process verifies whether the antivirus software is installed
- msiexec.exe (PID: 884)
- mfemactl.exe (PID: 4476)
- maconfig.exe (PID: 528)
- macmnsvc.exe (PID: 5528)
- msiexec.exe (PID: 6928)
- msiexec.exe (PID: 3572)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 3572)
The process drops C-runtime libraries
- msiexec.exe (PID: 3572)
Process drops legitimate windows executable
- msiexec.exe (PID: 3572)
The process creates files with name similar to system file names
- msiexec.exe (PID: 3572)
Adds/modifies Windows certificates
- msiexec.exe (PID: 3572)
Executes as Windows Service
- macmnsvc.exe (PID: 5528)
Creates or modifies Windows services
- maconfig.exe (PID: 528)
Reads security settings of Internet Explorer
- FrmInst.exe (PID: 6656)
INFO
Create files in a temporary directory
- TrellixSmartInstall.exe (PID: 6440)
- FrmInst.exe (PID: 6656)
- msiexec.exe (PID: 884)
- maconfig.exe (PID: 528)
- mfemactl.exe (PID: 4476)
Checks supported languages
- msiexec.exe (PID: 3572)
- TrellixSmartInstall.exe (PID: 6440)
- msiexec.exe (PID: 884)
- msiexec.exe (PID: 6928)
- maconfig.exe (PID: 528)
- mfemactl.exe (PID: 4476)
- macmnsvc.exe (PID: 5528)
- FrmInst.exe (PID: 6656)
Reads the computer name
- msiexec.exe (PID: 3572)
- TrellixSmartInstall.exe (PID: 6440)
- msiexec.exe (PID: 884)
- msiexec.exe (PID: 6928)
- mfemactl.exe (PID: 4476)
- maconfig.exe (PID: 528)
- macmnsvc.exe (PID: 5528)
- FrmInst.exe (PID: 6656)
Reads the machine GUID from the registry
- FrmInst.exe (PID: 6656)
- msiexec.exe (PID: 3572)
- TrellixSmartInstall.exe (PID: 6440)
- msiexec.exe (PID: 6928)
- mfemactl.exe (PID: 4476)
- maconfig.exe (PID: 528)
- macmnsvc.exe (PID: 5528)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3572)
- msiexec.exe (PID: 6928)
Reads the software policy settings
- msiexec.exe (PID: 3572)
Creates files or folders in the user directory
- msiexec.exe (PID: 3572)
Dropped object may contain TOR URL's
- msiexec.exe (PID: 3572)
Creates a software uninstall entry
- msiexec.exe (PID: 3572)
Creates files in the program directory
- maconfig.exe (PID: 528)
- macmnsvc.exe (PID: 5528)
UPX packer has been detected
- FrmInst.exe (PID: 6656)
- TrellixSmartInstall.exe (PID: 6440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:07 19:36:30+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 937984 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1724416 |
| EntryPoint: | 0x28a7c0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.8.1.313 |
| ProductVersionNumber: | 5.8.1.313 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Musarubra US LLC. |
| FileDescription: | Trellix Smart Installer |
| FileVersion: | 5.8.1.313 |
| InternalName: | TrellixSmartInstall.exe |
| LegalCopyright: | Copyright (C) 2024 Musarubra US LLC. All rights reserved |
| OriginalFileName: | TrellixSmartInstall.exe |
| ProductName: | Trellix Agent |
| ProductVersion: | 5.8.1.313 |
Total processes
173
Monitored processes
38
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | /FO CSV /NH | C:\Windows\SysWOW64\tasklist.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 528 | -provision -managed -dir "C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall" -logdir "C:\Users\admin\AppData\Local\Temp\McAfeeLogs" -nostart -check -guid {fc3a745f-201b-472b-b8ca-69590fb1d70e} -tenantid 0FA527C3-7AA3-4AD3-A579-14F47FFF891A | C:\Program Files\McAfee\Agent\maconfig.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Musarubra US LLC. Integrity Level: SYSTEM Description: Trellix Agent Configurator Exit code: 0 Version: 5.8.1.313 Modules
| |||||||||||||||
| 884 | C:\Windows\syswow64\MsiExec.exe -Embedding 3558DE02AF65E564BBC77177BD3F5963 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | /FI "IMAGENAME eq macompatsvc.exe" /FO CSV /NH | C:\Windows\SysWOW64\tasklist.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | /FI "IMAGENAME eq UpdaterUI.exe" /FO CSV /NH | C:\Windows\SysWOW64\tasklist.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1772 | /FO CSV /NH | C:\Windows\SysWOW64\tasklist.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | /FI "IMAGENAME eq masvc.exe" /FO CSV /NH | C:\Windows\SysWOW64\tasklist.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2068 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tasklist.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2204 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tasklist.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2348 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tasklist.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 788
Read events
15 307
Write events
475
Delete events
6
Modification events
| (PID) Process: | (3572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | 4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
Value: | |||
| (PID) Process: | (3572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000E94FB54871208C00DF70F708AC47085B0F0000000100000030000000C130BBA37B8B350E89FD5ED76B4F78777FEEE220D3B9E729042BEF6AF46E8E4C1B252E32B3080C681BC9A8A1AFDD0A3C0300000001000000140000004EFC31460C619ECAE59C1BCE2C008036D94C84B809000000010000000C000000300A06082B060105050703031D00000001000000100000005467B0ADDE8D858E30EE517B1A19ECD91400000001000000140000001F00BF46800AFC7839B7A5B443D95650BBCE963B53000000010000001F000000301D301B060567810C010330123010060A2B0601040182373C0101030200C06200000001000000200000007B9D553E1C92CB6E8803E137F4F287D4363757F5D44B37D52F9FCA22FB97DF860B000000010000004200000047006C006F00620061006C005300690067006E00200043006F006400650020005300690067006E0069006E006700200052006F006F007400200052003400350000001900000001000000100000005D1B8FF2C30F63F5B536EDD400F7F9B4200000000100000076050000308205723082035AA00302010202107653FEAC75464893F5E5D74A483A4EF8300D06092A864886F70D01010C05003053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F7420523435301E170D3230303331383030303030305A170D3435303331383030303030305A3053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F742052343530820222300D06092A864886F70D01010105000382020F003082020A0282020100B62DC530DD7AE8AB903D0372B03A4B991661B2E5FFA5671D371CE57EEC9383AA84F5A3439B98458AB863575D9B00880425E9F868924B82D84BC94A03F3A87F6A8F8A6127BDA144D0FDF53F22C2A34F918DB305B22882915DFB5988050B9706C298F82CA73324EE503A41CCF0A0B07B1D4DD2A8583896E9DFF91B91BB8B102CD2C7431DA20974A180AF7BE6330A0C596B8EBCF4AB5A977B7FAE55FB84F080FE844CD7E2BABDC475A16FBD61107444B29807E274ABFF68DC6C263EE91FE5E00487AD30D30C8D037C55B816705C24782025EB676788ABBA4E34986B7011DE38CAD4BEA1C09CE1DF1E0201D83BE1674384B6CFFC74B72F84A3BFBA09373D676CB1455C1961AB4183F5AC1DEB770D464773CEBFBD9595ED9D2B8810FEFA58E8A757E1B3CFA85AE907259B12C49E80723D93DC8C94DF3B44E62680FCD2C303F08C0CD245D62EE78F989EE604EE426E677E42167162E704F960C664A1B69C81214E2BC66D689486C699747367317A91F2D48C796E7CA6BB7E466F4DC585122BCF9A224408A88537CE07615706171224C0C43173A1983557477E103A45D92DA4519098A9A00737C4651AAA1C6B1677F7A797EC3F1930996F31FBEA40B2E7D2C4FAC9D0F050767459FA8D6D1732BEF8E97E03F4E787759AD44A912C850313022B4280F2896A36CFC84CA0CE9EF8CB8DAD16A7D3DED59B18A7C6923AF18263F12E0E2464DF0203010001A3423040300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E041604141F00BF46800AFC7839B7A5B443D95650BBCE963B300D06092A864886F70D01010C050003820201005E2BBA749734445F764828408493EE016EE9A1B3D68025E67BE4BC09913D0FFC76ADD7D43020BB8F60D091D61CF29CEF781A2B943202C12496525202D0F3D1FCF29B396E99E11F8E43417D9A1E5BC95D9A84FC26E687F3747226ADA41BD93D3B6A52A03C091E2F1E7BB333B445C7F7ACB1AF9360AD76AEB8B21578EB836AEBFFDB46AB24E5EE02FA901F59C02F5DD6B75DA45C10B77253F8414ECCFA781A254ACAFE85624361C3B437AA81D2F4D63A0FBD8D597E3047DE2B6BE72150335FD4679BD4B8679F3C279903FF85438E7312CA20CDE861D5B166DC17D6396D0FDBCF2337A182894E1C6B3FD6A0CDAA079D3E4226AAD70CEEFA47BF1A527ED17581D3C98A62176D4F88A021A0263EAF6DD962301FE99828AE6E8DD58E4C726693808D2AE355C760679042565C22510FB3DC4E39EE4DDDD91D7810543B6ED0976F03B51EB22373C612B29A64D0FC958524A8FFDFA1B0DC9140AEDF0933ABB9DD92B7F1CC91743B69EB67971B90BFE7C7A06F71BB57BFB78F5AED7A406A16CD80842D2FE102D4249443B315FC0C2B1BFD716FFCCBBC75173A5E83D2C9B32F1BD59C8D7F54FE7E7EE456A387A79DE1595294418F6D5BBE86959AFF1A76DD40D2514A70B41F336323773FEC271E59E40887ED34824A0F3FFEA01DC1F56773458678F4AA29E92787C619DBC61314C33949874DA097E06513F59D7756E9DAB358C73AF2C0CD82 | |||
| (PID) Process: | (3572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000001000001900000001000000100000005D1B8FF2C30F63F5B536EDD400F7F9B40B000000010000004200000047006C006F00620061006C005300690067006E00200043006F006400650020005300690067006E0069006E006700200052006F006F007400200052003400350000006200000001000000200000007B9D553E1C92CB6E8803E137F4F287D4363757F5D44B37D52F9FCA22FB97DF8653000000010000001F000000301D301B060567810C010330123010060A2B0601040182373C0101030200C01400000001000000140000001F00BF46800AFC7839B7A5B443D95650BBCE963B1D00000001000000100000005467B0ADDE8D858E30EE517B1A19ECD909000000010000000C000000300A06082B060105050703030300000001000000140000004EFC31460C619ECAE59C1BCE2C008036D94C84B80F0000000100000030000000C130BBA37B8B350E89FD5ED76B4F78777FEEE220D3B9E729042BEF6AF46E8E4C1B252E32B3080C681BC9A8A1AFDD0A3C040000000100000010000000E94FB54871208C00DF70F708AC47085B200000000100000076050000308205723082035AA00302010202107653FEAC75464893F5E5D74A483A4EF8300D06092A864886F70D01010C05003053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F7420523435301E170D3230303331383030303030305A170D3435303331383030303030305A3053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F742052343530820222300D06092A864886F70D01010105000382020F003082020A0282020100B62DC530DD7AE8AB903D0372B03A4B991661B2E5FFA5671D371CE57EEC9383AA84F5A3439B98458AB863575D9B00880425E9F868924B82D84BC94A03F3A87F6A8F8A6127BDA144D0FDF53F22C2A34F918DB305B22882915DFB5988050B9706C298F82CA73324EE503A41CCF0A0B07B1D4DD2A8583896E9DFF91B91BB8B102CD2C7431DA20974A180AF7BE6330A0C596B8EBCF4AB5A977B7FAE55FB84F080FE844CD7E2BABDC475A16FBD61107444B29807E274ABFF68DC6C263EE91FE5E00487AD30D30C8D037C55B816705C24782025EB676788ABBA4E34986B7011DE38CAD4BEA1C09CE1DF1E0201D83BE1674384B6CFFC74B72F84A3BFBA09373D676CB1455C1961AB4183F5AC1DEB770D464773CEBFBD9595ED9D2B8810FEFA58E8A757E1B3CFA85AE907259B12C49E80723D93DC8C94DF3B44E62680FCD2C303F08C0CD245D62EE78F989EE604EE426E677E42167162E704F960C664A1B69C81214E2BC66D689486C699747367317A91F2D48C796E7CA6BB7E466F4DC585122BCF9A224408A88537CE07615706171224C0C43173A1983557477E103A45D92DA4519098A9A00737C4651AAA1C6B1677F7A797EC3F1930996F31FBEA40B2E7D2C4FAC9D0F050767459FA8D6D1732BEF8E97E03F4E787759AD44A912C850313022B4280F2896A36CFC84CA0CE9EF8CB8DAD16A7D3DED59B18A7C6923AF18263F12E0E2464DF0203010001A3423040300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E041604141F00BF46800AFC7839B7A5B443D95650BBCE963B300D06092A864886F70D01010C050003820201005E2BBA749734445F764828408493EE016EE9A1B3D68025E67BE4BC09913D0FFC76ADD7D43020BB8F60D091D61CF29CEF781A2B943202C12496525202D0F3D1FCF29B396E99E11F8E43417D9A1E5BC95D9A84FC26E687F3747226ADA41BD93D3B6A52A03C091E2F1E7BB333B445C7F7ACB1AF9360AD76AEB8B21578EB836AEBFFDB46AB24E5EE02FA901F59C02F5DD6B75DA45C10B77253F8414ECCFA781A254ACAFE85624361C3B437AA81D2F4D63A0FBD8D597E3047DE2B6BE72150335FD4679BD4B8679F3C279903FF85438E7312CA20CDE861D5B166DC17D6396D0FDBCF2337A182894E1C6B3FD6A0CDAA079D3E4226AAD70CEEFA47BF1A527ED17581D3C98A62176D4F88A021A0263EAF6DD962301FE99828AE6E8DD58E4C726693808D2AE355C760679042565C22510FB3DC4E39EE4DDDD91D7810543B6ED0976F03B51EB22373C612B29A64D0FC958524A8FFDFA1B0DC9140AEDF0933ABB9DD92B7F1CC91743B69EB67971B90BFE7C7A06F71BB57BFB78F5AED7A406A16CD80842D2FE102D4249443B315FC0C2B1BFD716FFCCBBC75173A5E83D2C9B32F1BD59C8D7F54FE7E7EE456A387A79DE1595294418F6D5BBE86959AFF1A76DD40D2514A70B41F336323773FEC271E59E40887ED34824A0F3FFEA01DC1F56773458678F4AA29E92787C619DBC61314C33949874DA097E06513F59D7756E9DAB358C73AF2C0CD82 | |||
| (PID) Process: | (3572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates |
| Operation: | delete value | Name: | D69B561148F01C77C54578C10926DF5B856976AD |
Value: | |||
| (PID) Process: | (3572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D69B561148F01C77C54578C10926DF5B856976AD |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000C5DFB849CA051355EE2DBA1AC33EB0281400000001000000140000008FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC0B000000010000003000000047006C006F00620061006C005300690067006E00200052006F006F00740020004300410020002D002000520033000000090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703080F00000001000000200000005229BA15B31B0C6F4CCA89C2985177974327D1B689A3B935A0BD975532AF22AB030000000100000014000000D69B561148F01C77C54578C10926DF5B856976AD190000000100000010000000D0FD3C9C380D7B65E26B9A3FEDD39B8F530000000100000040000000303E301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C0620000000100000020000000CBB522D7B7F127AD6A0113865BDF1CD4102E7D0759AF635A7CF4720DC963C53B1D000000010000001000000001728E1ECF7A9D86FB3CEC8948ABA9532000000001000000630300003082035F30820247A003020102020B04000000000121585308A2300D06092A864886F70D01010B0500304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3039303331383130303030305A170D3239303331383130303030305A304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E30820122300D06092A864886F70D01010105000382010F003082010A0282010100CC2576907906782216F5C083B684CA289EFD057611C5AD8872FC460243C7B28A9D045F24CB2E4BE1608246E152AB0C8147706CDD64D1EBF52CA30F823D0C2BAE97D7B614861079BB3B1380778C08E149D26A622F1F5EFA9668DF892795389F06D73EC9CB26590D73DEB0C8E9260E8315C6EF5B8BD20460CA49A628F6693BF6CBC82891E59D8A615737AC7414DC74E03AEE722F2E9CFBD0BBBFF53D00E10633E8822BAE53A63A16738CDD410E203AC0B4A7A1E9B24F902E3260E957CBB904926868E538266075B29F77FF9114EFAE2049FCAD401548D1023161195EB897EFAD77B7649A7ABF5FC113EF9B62FB0D6CE0546916A903DA6EE983937176C6698582170203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604148FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC300D06092A864886F70D01010B050003820101004B40DBC050AAFEC80CEFF796544549BB96000941ACB3138686280733CA6BE674B9BA002DAEA40AD3F5F1F10F8ABF73674A83C7447B78E0AF6E6C6F03298E333945C38EE4B9576CAAFC1296EC53C62DE4246CB99463FBDC536867563E83B8CF3521C3C968FECEDAC253AACC908AE9F05D468C95DD7A58281A2F1DDECD0037418FED446DD75328977EF367041E15D78A96B4D3DE4C27A44C1B737376F41799C21F7A0EE32D08AD0A1C2CFF3CAB550E0F917E36EBC35749BEE12E2D7C608BC3415113239DCEF7326B9401A899E72C331F3A3B25D28640CE3B2C8678C9612F14BAEEDB556FDF84EE05094DBD28D872CED36250651EEB92978331D9B3B5CA47583F5F | |||
| (PID) Process: | (3572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D69B561148F01C77C54578C10926DF5B856976AD |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000000800001D000000010000001000000001728E1ECF7A9D86FB3CEC8948ABA953620000000100000020000000CBB522D7B7F127AD6A0113865BDF1CD4102E7D0759AF635A7CF4720DC963C53B530000000100000040000000303E301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C0190000000100000010000000D0FD3C9C380D7B65E26B9A3FEDD39B8F030000000100000014000000D69B561148F01C77C54578C10926DF5B856976AD0F00000001000000200000005229BA15B31B0C6F4CCA89C2985177974327D1B689A3B935A0BD975532AF22AB090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703080B000000010000003000000047006C006F00620061006C005300690067006E00200052006F006F00740020004300410020002D0020005200330000001400000001000000140000008FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC040000000100000010000000C5DFB849CA051355EE2DBA1AC33EB0282000000001000000630300003082035F30820247A003020102020B04000000000121585308A2300D06092A864886F70D01010B0500304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3039303331383130303030305A170D3239303331383130303030305A304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E30820122300D06092A864886F70D01010105000382010F003082010A0282010100CC2576907906782216F5C083B684CA289EFD057611C5AD8872FC460243C7B28A9D045F24CB2E4BE1608246E152AB0C8147706CDD64D1EBF52CA30F823D0C2BAE97D7B614861079BB3B1380778C08E149D26A622F1F5EFA9668DF892795389F06D73EC9CB26590D73DEB0C8E9260E8315C6EF5B8BD20460CA49A628F6693BF6CBC82891E59D8A615737AC7414DC74E03AEE722F2E9CFBD0BBBFF53D00E10633E8822BAE53A63A16738CDD410E203AC0B4A7A1E9B24F902E3260E957CBB904926868E538266075B29F77FF9114EFAE2049FCAD401548D1023161195EB897EFAD77B7649A7ABF5FC113EF9B62FB0D6CE0546916A903DA6EE983937176C6698582170203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604148FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC300D06092A864886F70D01010B050003820101004B40DBC050AAFEC80CEFF796544549BB96000941ACB3138686280733CA6BE674B9BA002DAEA40AD3F5F1F10F8ABF73674A83C7447B78E0AF6E6C6F03298E333945C38EE4B9576CAAFC1296EC53C62DE4246CB99463FBDC536867563E83B8CF3521C3C968FECEDAC253AACC908AE9F05D468C95DD7A58281A2F1DDECD0037418FED446DD75328977EF367041E15D78A96B4D3DE4C27A44C1B737376F41799C21F7A0EE32D08AD0A1C2CFF3CAB550E0F917E36EBC35749BEE12E2D7C608BC3415113239DCEF7326B9401A899E72C331F3A3B25D28640CE3B2C8678C9612F14BAEEDB556FDF84EE05094DBD28D872CED36250651EEB92978331D9B3B5CA47583F5F | |||
| (PID) Process: | (3572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (3572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\e9587.rbs |
Value: 31121091 | |||
| (PID) Process: | (3572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\e9587.rbsLow |
Value: | |||
| (PID) Process: | (3572) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\CDEAFA460BC451444A76C24659F225CA |
| Operation: | write | Name: | 04B0F9A2294EE01469572590EE320CD9 |
Value: C:\Program Files\McAfee\Agent\ | |||
Executable files
310
Suspicious files
106
Text files
114
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6440 | TrellixSmartInstall.exe | C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\Shared.cab | — | |
MD5:— | SHA256:— | |||
| 6440 | TrellixSmartInstall.exe | C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\cabundle.cer | text | |
MD5:38CEDA6F94EB434B4F04F27D3124FA07 | SHA256:F78F0BCB3EAB2536B785A744019698B9F09CD450514D9542EB39507C351945E8 | |||
| 6440 | TrellixSmartInstall.exe | C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\req2048seckey.bin | binary | |
MD5:5191848515739AA65CDD97E3D2E283C8 | SHA256:8BA9397BDE9834209CE78BFBDED75C05B98924D1D16DE882A7E26C91EE2A2EAE | |||
| 6440 | TrellixSmartInstall.exe | C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\SiteList.xml | text | |
MD5:E4007741FE2BA9809FDDD2100F236DCC | SHA256:98BF983D7A08C8EE37BB3985FE2569FCDAA4A3497C2BFF2C3CDA499836BEFEEA | |||
| 6440 | TrellixSmartInstall.exe | C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\agent.ini | ini | |
MD5:B742DE65F4A64355666B9A9C807BEC33 | SHA256:738E3D028C333CCF9D16EB3B1D366B2FD65E4B342B4175DB167576728A921DD7 | |||
| 6440 | TrellixSmartInstall.exe | C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\coninfo.xml | xml | |
MD5:3CFEC0DC8AF87F31C22209941D835B23 | SHA256:937867A4298A02F5B7E529C1DCFED27CBB1A694FA27AD1545DFBA407412F8A9E | |||
| 6440 | TrellixSmartInstall.exe | C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\BootstrapInfo.xml | xml | |
MD5:4491B8E18CEF975FDA9290FE816D6765 | SHA256:0DD5800FE2DC803C1601E0C4921EBEC837AFCD95732BCA155C3A3F49EE2EE69E | |||
| 6440 | TrellixSmartInstall.exe | C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\RepoKeys.ini | ini | |
MD5:4C9FA315DA6856C1BC0D74520167F519 | SHA256:EDC63E39BDA39C600E426D5380F0913C825C522F3EE14DBC6750000720D89712 | |||
| 6440 | TrellixSmartInstall.exe | C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\sr2048pubkey.bin | binary | |
MD5:FB599B28155C00E05882C33FE06E5DF8 | SHA256:B8F6AB4BBD8FE6C6BE3456BAA668945F71BA156D8D1D51C4BF335BFE98718642 | |||
| 6440 | TrellixSmartInstall.exe | C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\Shared64.cab | compressed | |
MD5:D2680DD6CDF4C19887505045D247226A | SHA256:A4976046E44773B93165157956B58D06D85284668B20855645152CAEC0DC7BC0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
49
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 13.225.78.26:80 | http://cdn-usw004.manage.trellix.com/Software/Current/EPOAGENT3000/Install/0409/FrameworkInstall.zip | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5272 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1320 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3076 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3572 | msiexec.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDQHuXxad%2F5c1K2Rl1mo%3D | unknown | — | — | whitelisted |
3572 | msiexec.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgOhtwj4VKsGchDZBEc%3D | unknown | — | — | whitelisted |
3572 | msiexec.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGEJFcIpBz28BuO60qVQ%3D | unknown | — | — | whitelisted |
3572 | msiexec.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr45codesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTLuA3ygnKW%2F7xuSx%2F09F%2BhHVuEUQQU2rONwCSQo2t30wygWd0hZ2R2C3gCDFzND7mMLNAClZYo2Q%3D%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4204 | svchost.exe | 4.209.32.198:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3380 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6012 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.209.133:443 | — | Akamai International B.V. | GB | unknown |
3960 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
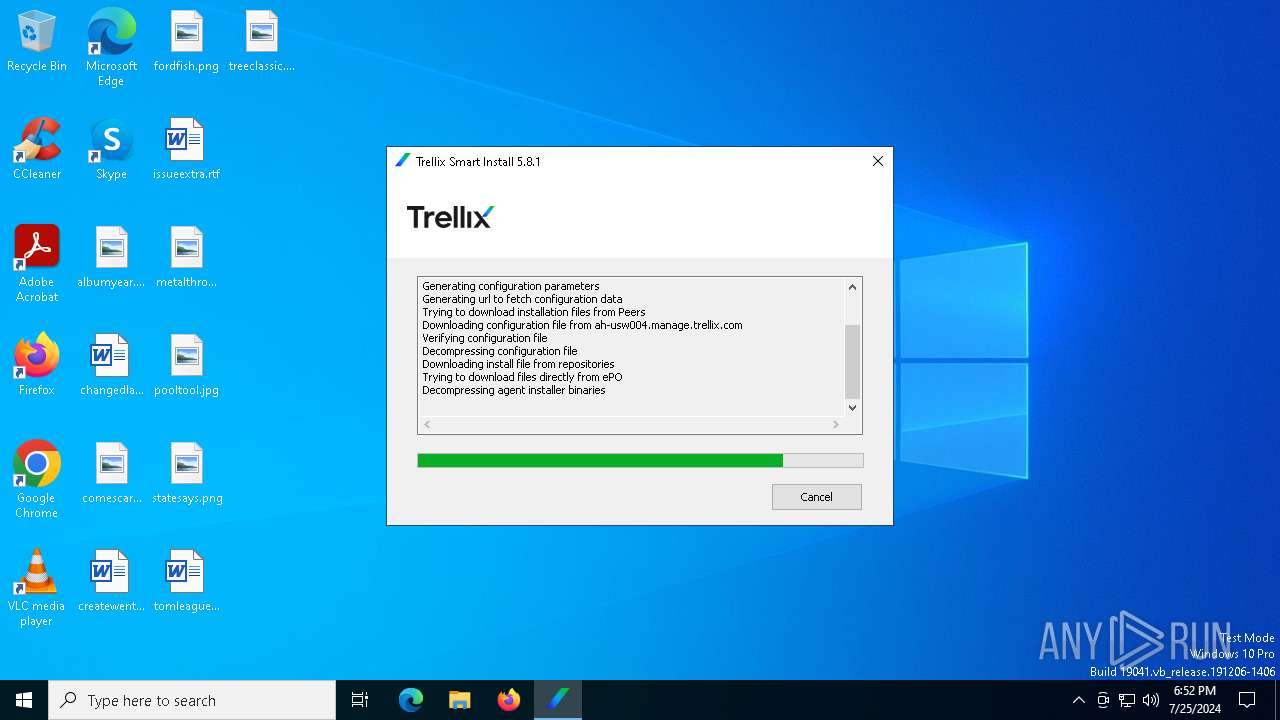
6440 | TrellixSmartInstall.exe | 52.35.38.154:443 | ah-usw004.manage.trellix.com | AMAZON-02 | US | unknown |
3380 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ah-usw004.manage.trellix.com |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
cdn-usw004.manage.trellix.com |
| unknown |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
Process | Message |
|---|---|
FrmInst.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory
|
FrmInst.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\FrmInst.exe loading C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\mfevtpa.dll, WinVerifyTrust failed with 80092003
|
FrmInst.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory
|
FrmInst.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\FrmInst.exe loading C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
FrmInst.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory
|
FrmInst.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\FrmInst.exe loading C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
FrmInst.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory
|
FrmInst.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\FrmInst.exe loading C:\Users\admin\AppData\Local\Temp\McAfeeSmartInstall\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
FrmInst.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory
|
FrmInst.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory
|