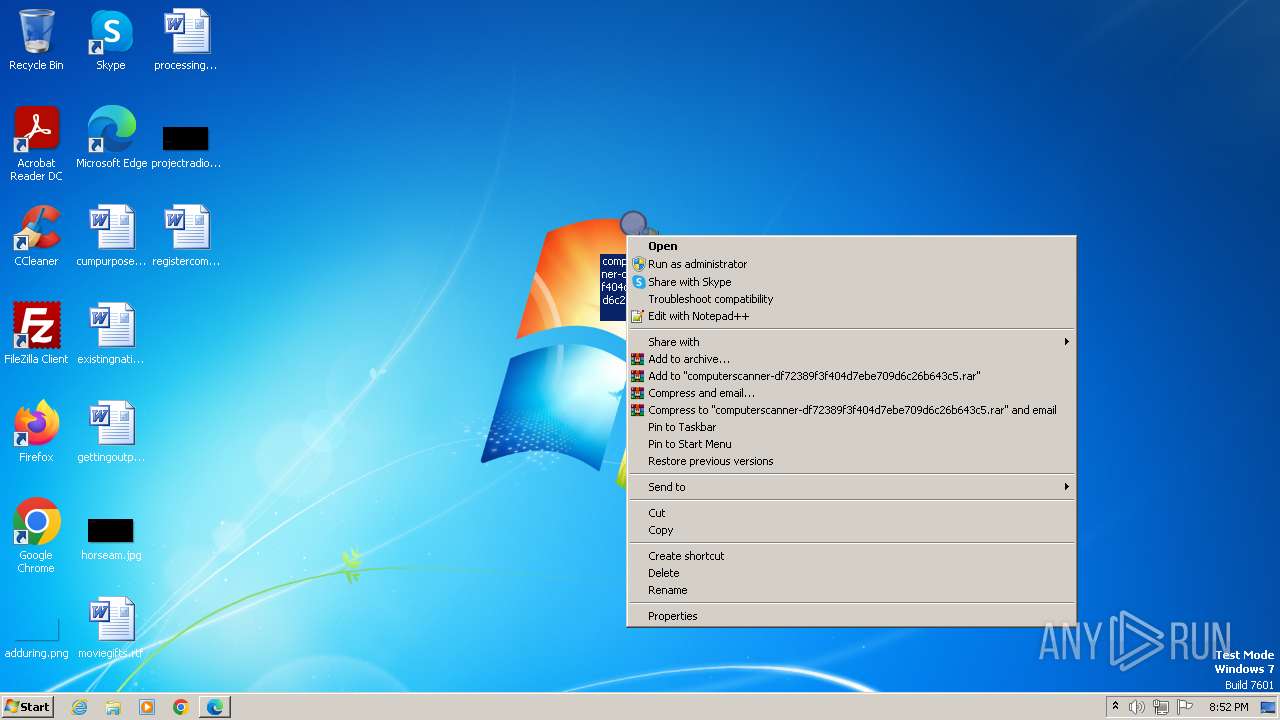
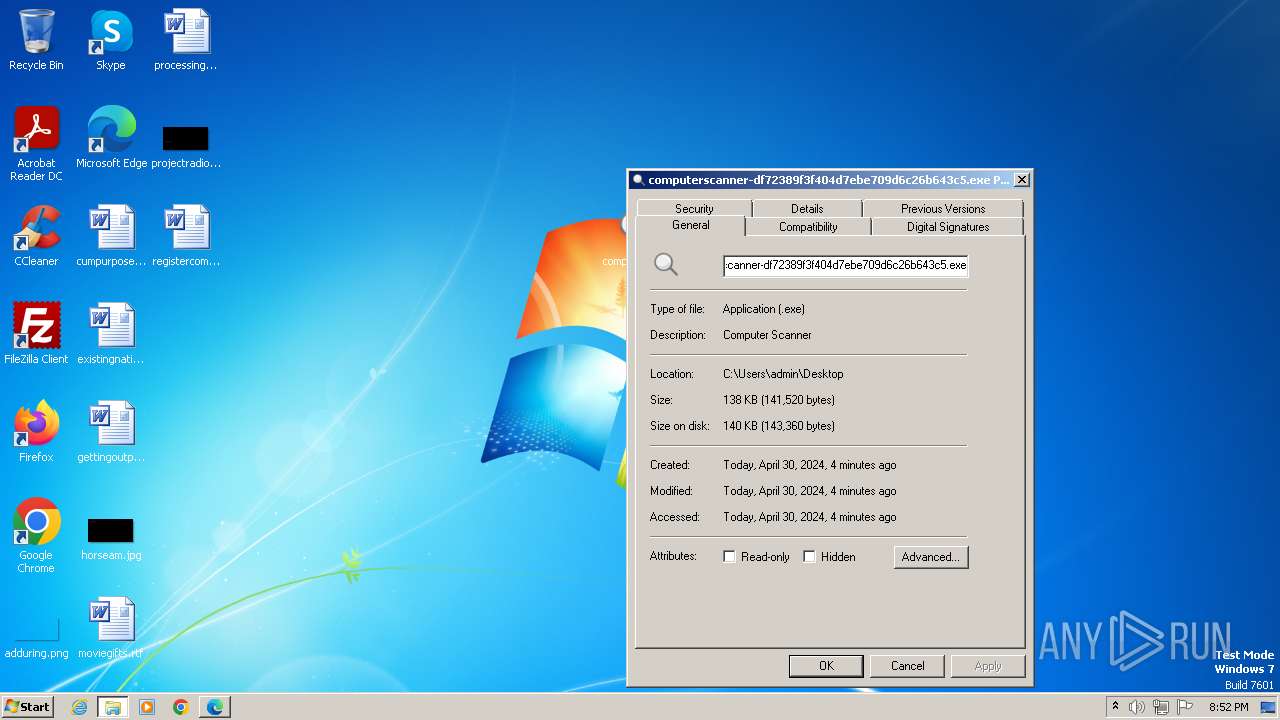
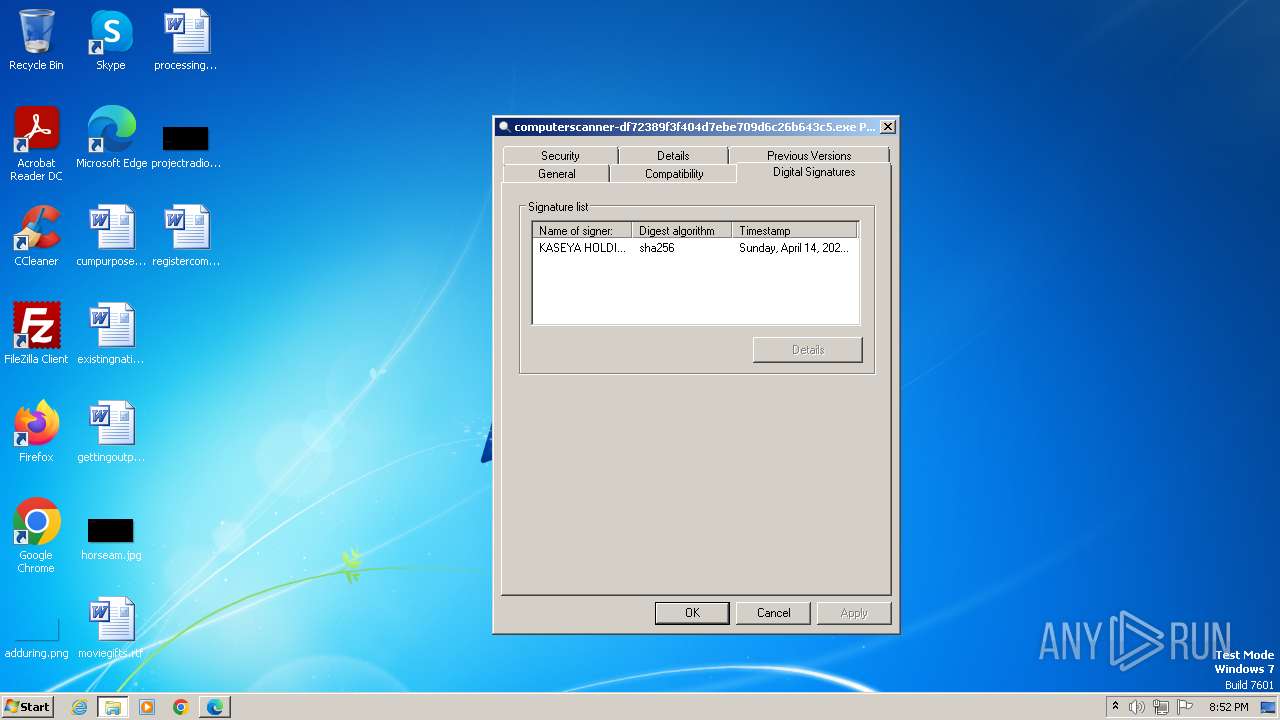
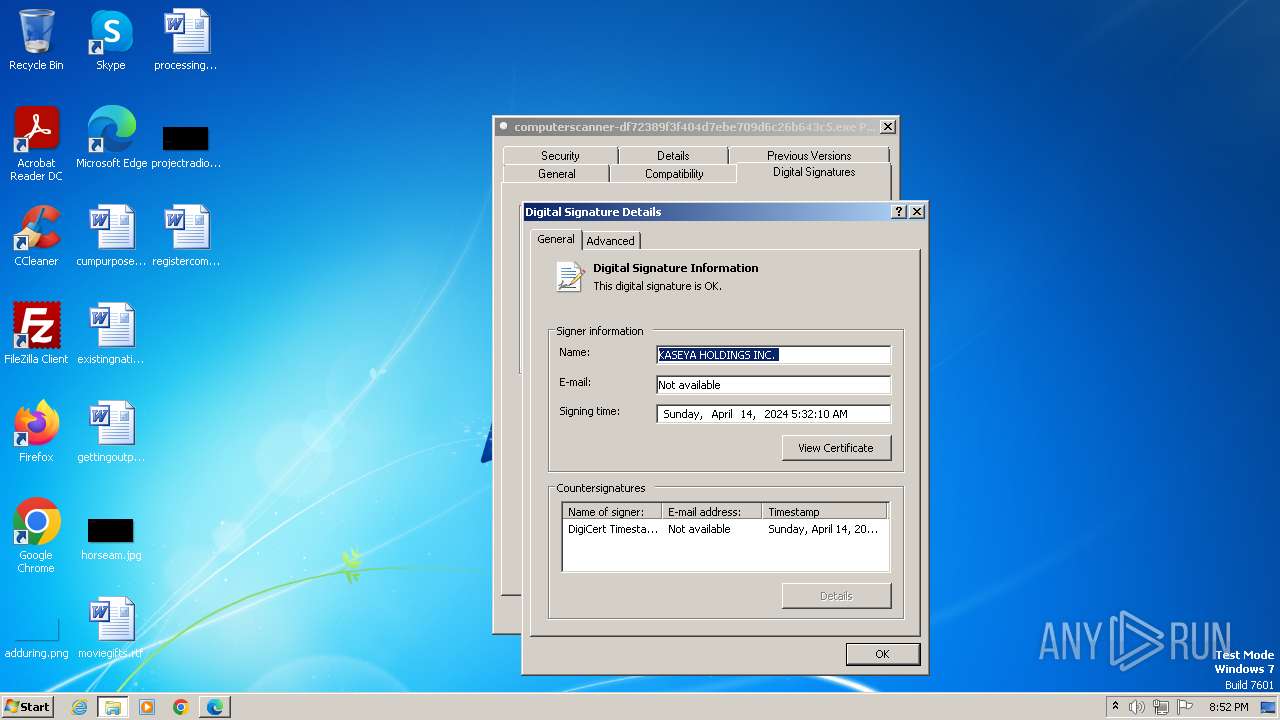
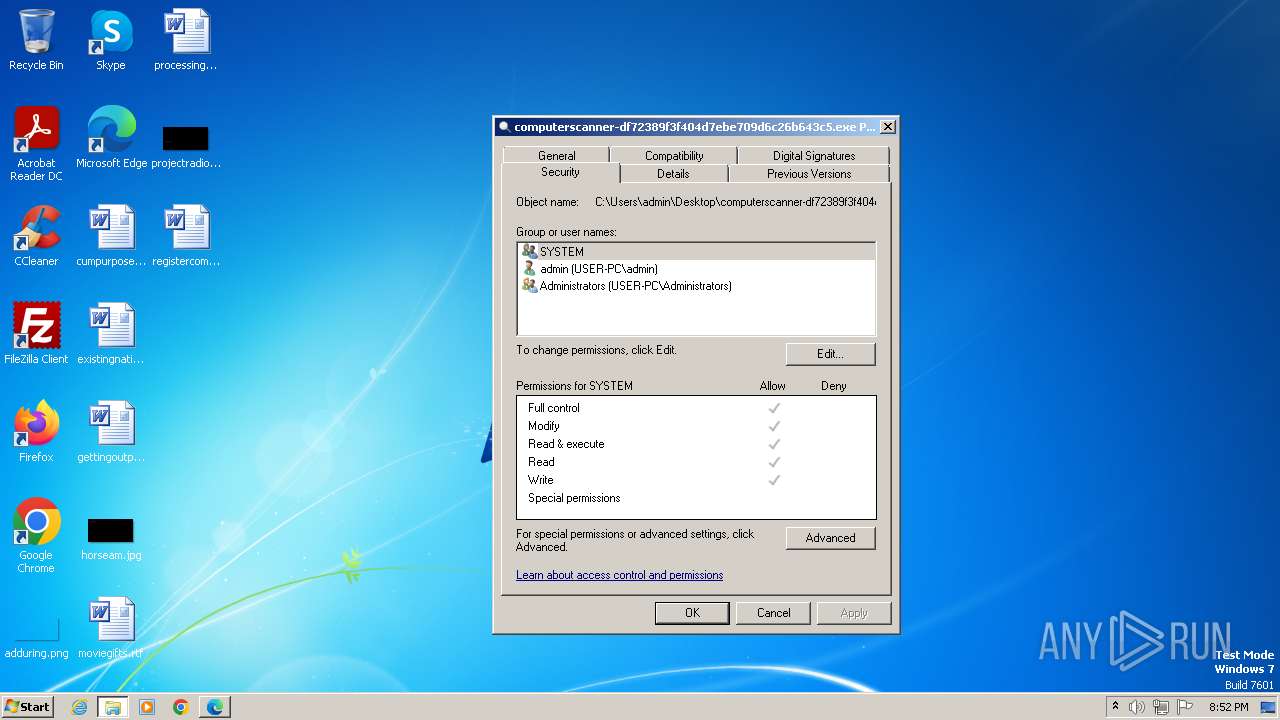
| File name: | computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe |
| Full analysis: | https://app.any.run/tasks/f9c46ad9-5bac-4790-ad35-86e7e4ad1c9b |
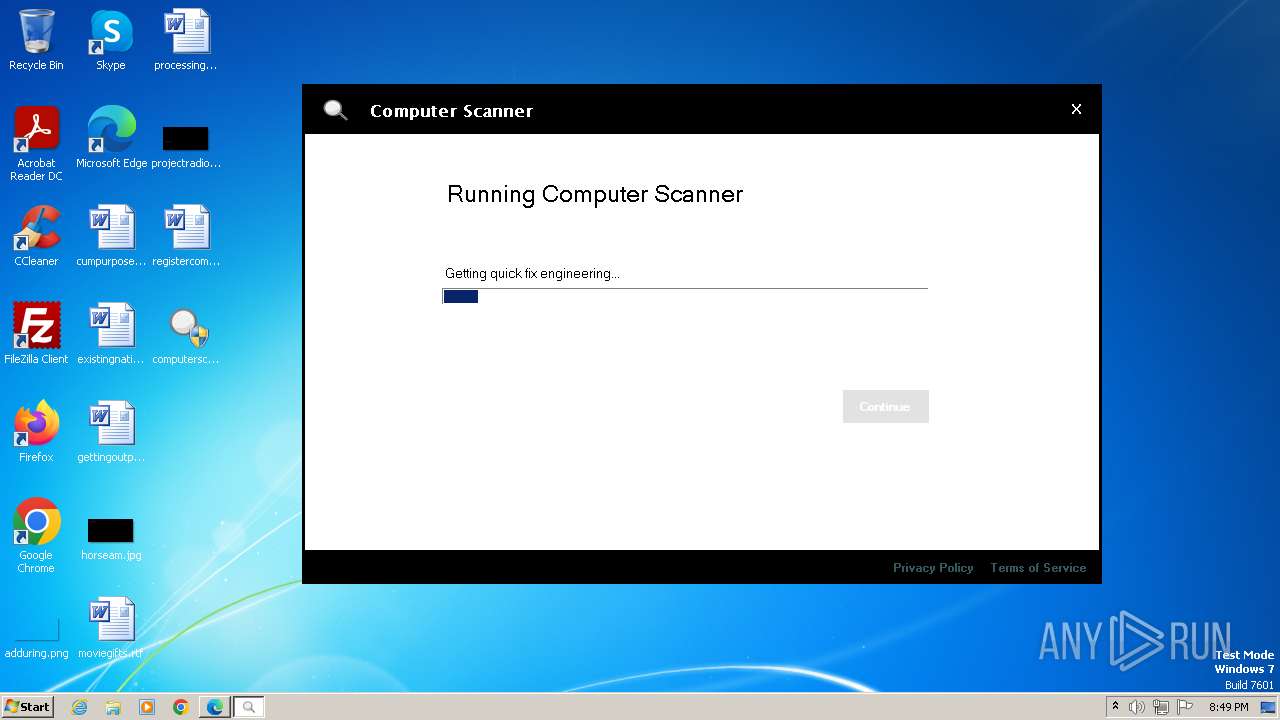
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | April 30, 2024, 19:48:04 |
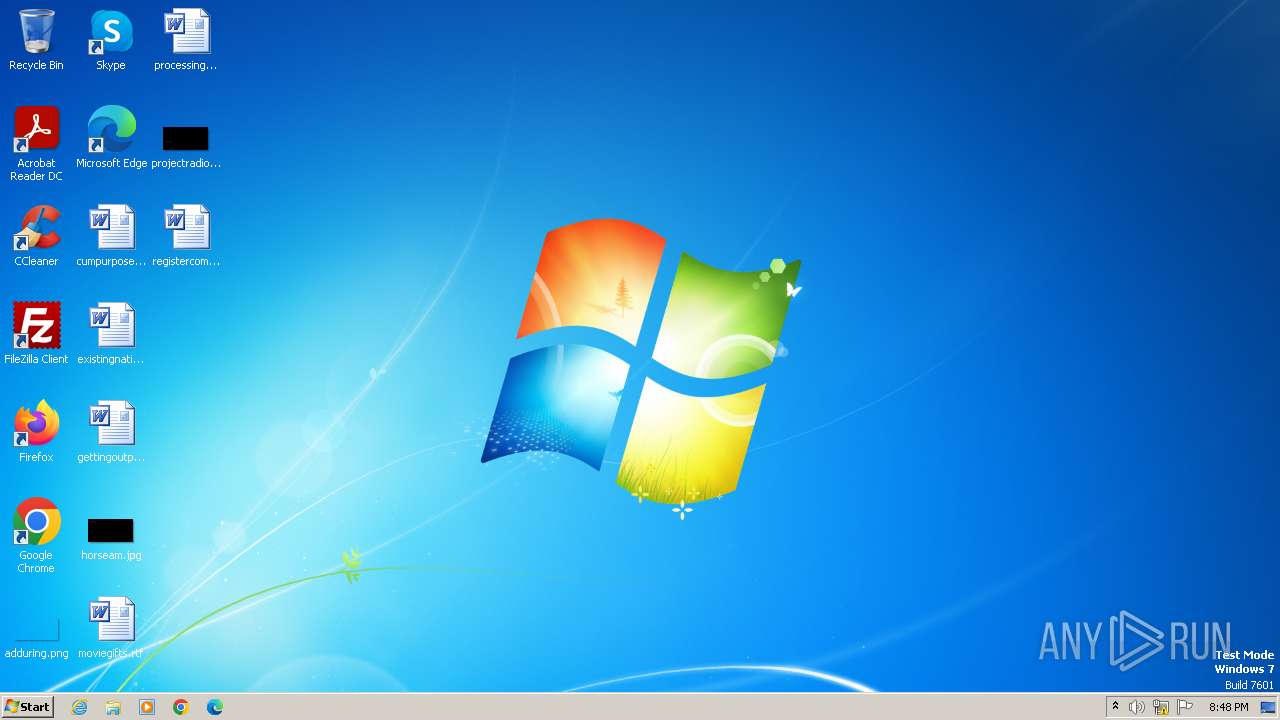
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 21E4AAF136CE9E2300889A3D56E76E77 |
| SHA1: | 28AAD500ECA647A1557D8A0805C934E5B0F4A1C8 |
| SHA256: | 3515FB4B2398DEF4BFDE98F9E38859954C4896F3DA25A5C4B04BF75950F0EC6C |
| SSDEEP: | 3072:PId3kt2Jkq7MbH079fJaTwvKf6pdZLsc3H6rJaMUvKf6pTZ8A/YNDO:PIdmqXJaTOdRB3HkJaMqTv/cK |
MALICIOUS
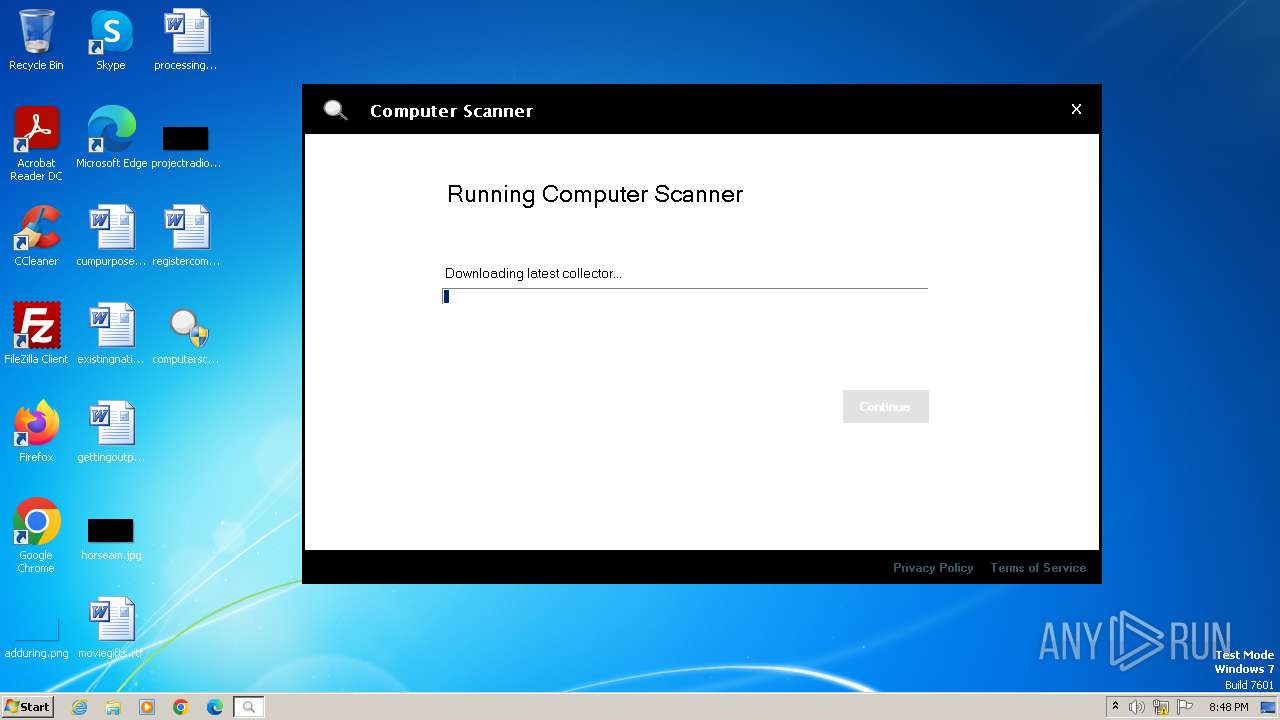
Drops the executable file immediately after the start
- computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe (PID: 820)
Changes the Windows auto-update feature
- mmc.exe (PID: 2060)
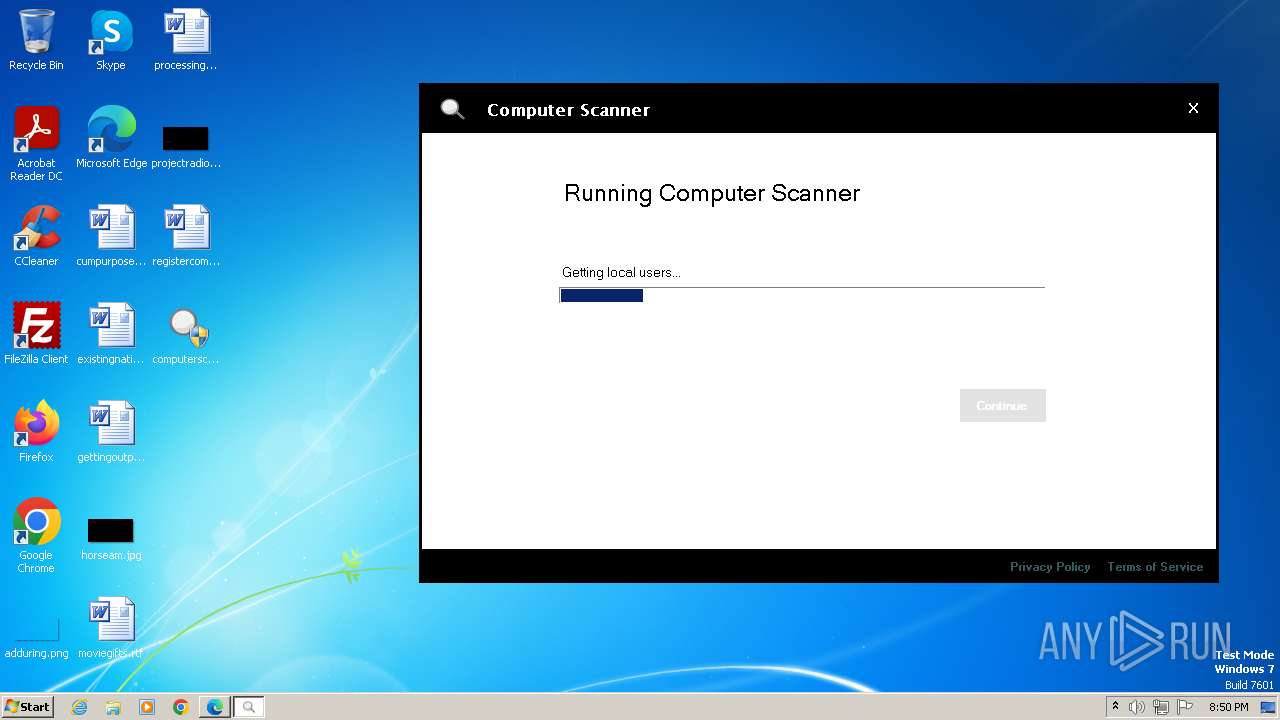
Actions looks like stealing of personal data
- nacmdline.exe (PID: 3860)
Steals credentials
- nacmdline.exe (PID: 3860)
The EICAR Standard Anti-Virus Test File is detected
- caramfddownloader.exe (PID: 1680)
- caramfddownloader.exe (PID: 2068)
- caramfddownloader.exe (PID: 188)
SUSPICIOUS
Reads the Internet Settings
- computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe (PID: 820)
- ndconnector.exe (PID: 3092)
- ndconnector.exe (PID: 2996)
- ndconnector.exe (PID: 3468)
- cscript.exe (PID: 112)
- cscript.exe (PID: 1200)
- nacmdline.exe (PID: 3860)
- caramfddownloader.exe (PID: 1680)
- caramfddownloader.exe (PID: 2068)
- caramfddownloader.exe (PID: 188)
- ndconnector.exe (PID: 1580)
Reads settings of System Certificates
- computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe (PID: 820)
- ndconnector.exe (PID: 2996)
- ndconnector.exe (PID: 3468)
- ndconnector.exe (PID: 3092)
- nacmdline.exe (PID: 3860)
- caramfddownloader.exe (PID: 1680)
- caramfddownloader.exe (PID: 2068)
- caramfddownloader.exe (PID: 188)
- ndconnector.exe (PID: 1580)
Process drops legitimate windows executable
- computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe (PID: 820)
Executable content was dropped or overwritten
- computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe (PID: 820)
The process creates files with name similar to system file names
- computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe (PID: 820)
Reads security settings of Internet Explorer
- ndconnector.exe (PID: 2996)
- ndconnector.exe (PID: 3092)
- ndconnector.exe (PID: 3468)
- nacmdline.exe (PID: 3860)
- ndconnector.exe (PID: 1580)
Adds/modifies Windows certificates
- ndconnector.exe (PID: 2996)
- ndconnector.exe (PID: 3092)
- nacmdline.exe (PID: 3860)
Checks Windows Trust Settings
- ndconnector.exe (PID: 3092)
- ndconnector.exe (PID: 2996)
- ndconnector.exe (PID: 3468)
- nacmdline.exe (PID: 3860)
- ndconnector.exe (PID: 1580)
Group Policy Discovery via Microsoft GPResult Utility
- nacmdline.exe (PID: 3860)
Searches for installed software
- nacmdline.exe (PID: 3860)
Connects to SMTP port
- nacmdline.exe (PID: 3860)
Connects to FTP
- nacmdline.exe (PID: 3860)
Reads the Windows owner or organization settings
- nacmdline.exe (PID: 3860)
Reads browser cookies
- nacmdline.exe (PID: 3860)
Connects to unusual port
- nacmdline.exe (PID: 3860)
INFO
Checks supported languages
- computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe (PID: 820)
- wmpnscfg.exe (PID: 2304)
- ndconnector.exe (PID: 2996)
- ndconnector.exe (PID: 3092)
- nacmdline.exe (PID: 3860)
- ndconnector.exe (PID: 3468)
- caramfddc.exe (PID: 1036)
- caramfddownloader.exe (PID: 1680)
- caramfddownloader.exe (PID: 2068)
- caramfddownloader.exe (PID: 188)
- ndconnector.exe (PID: 1580)
Reads Environment values
- computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe (PID: 820)
- ndconnector.exe (PID: 2996)
- ndconnector.exe (PID: 3092)
- ndconnector.exe (PID: 3468)
- nacmdline.exe (PID: 3860)
- caramfddownloader.exe (PID: 1680)
- caramfddownloader.exe (PID: 2068)
- caramfddownloader.exe (PID: 188)
- ndconnector.exe (PID: 1580)
Reads the computer name
- computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe (PID: 820)
- wmpnscfg.exe (PID: 2304)
- ndconnector.exe (PID: 2996)
- ndconnector.exe (PID: 3092)
- ndconnector.exe (PID: 3468)
- nacmdline.exe (PID: 3860)
- caramfddc.exe (PID: 1036)
- caramfddownloader.exe (PID: 1680)
- caramfddownloader.exe (PID: 2068)
- caramfddownloader.exe (PID: 188)
- ndconnector.exe (PID: 1580)
Reads the machine GUID from the registry
- computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe (PID: 820)
- ndconnector.exe (PID: 3092)
- ndconnector.exe (PID: 2996)
- ndconnector.exe (PID: 3468)
- nacmdline.exe (PID: 3860)
- caramfddownloader.exe (PID: 1680)
- caramfddownloader.exe (PID: 2068)
- ndconnector.exe (PID: 1580)
- caramfddownloader.exe (PID: 188)
Reads the software policy settings
- computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe (PID: 820)
- ndconnector.exe (PID: 2996)
- ndconnector.exe (PID: 3468)
- ndconnector.exe (PID: 3092)
- nacmdline.exe (PID: 3860)
- caramfddownloader.exe (PID: 1680)
- caramfddownloader.exe (PID: 2068)
- caramfddownloader.exe (PID: 188)
- ndconnector.exe (PID: 1580)
Manual execution by a user
- wmpnscfg.exe (PID: 2304)
- msedge.exe (PID: 1796)
Application launched itself
- msedge.exe (PID: 1764)
- msedge.exe (PID: 1796)
Create files in a temporary directory
- computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe (PID: 820)
- ndconnector.exe (PID: 2996)
- nacmdline.exe (PID: 3860)
- auditpol.exe (PID: 3604)
- SecEdit.exe (PID: 3832)
- caramfddc.exe (PID: 1036)
- caramfddownloader.exe (PID: 1680)
- mmc.exe (PID: 2060)
- caramfddownloader.exe (PID: 2068)
- caramfddownloader.exe (PID: 188)
- ndconnector.exe (PID: 1580)
Creates files or folders in the user directory
- ndconnector.exe (PID: 2996)
Reads product name
- nacmdline.exe (PID: 3860)
Reads security settings of Internet Explorer
- cscript.exe (PID: 112)
- cscript.exe (PID: 1200)
Reads CPU info
- nacmdline.exe (PID: 3860)
Checks proxy server information
- nacmdline.exe (PID: 3860)
Reads Windows Product ID
- nacmdline.exe (PID: 3860)
Reads Microsoft Office registry keys
- nacmdline.exe (PID: 3860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
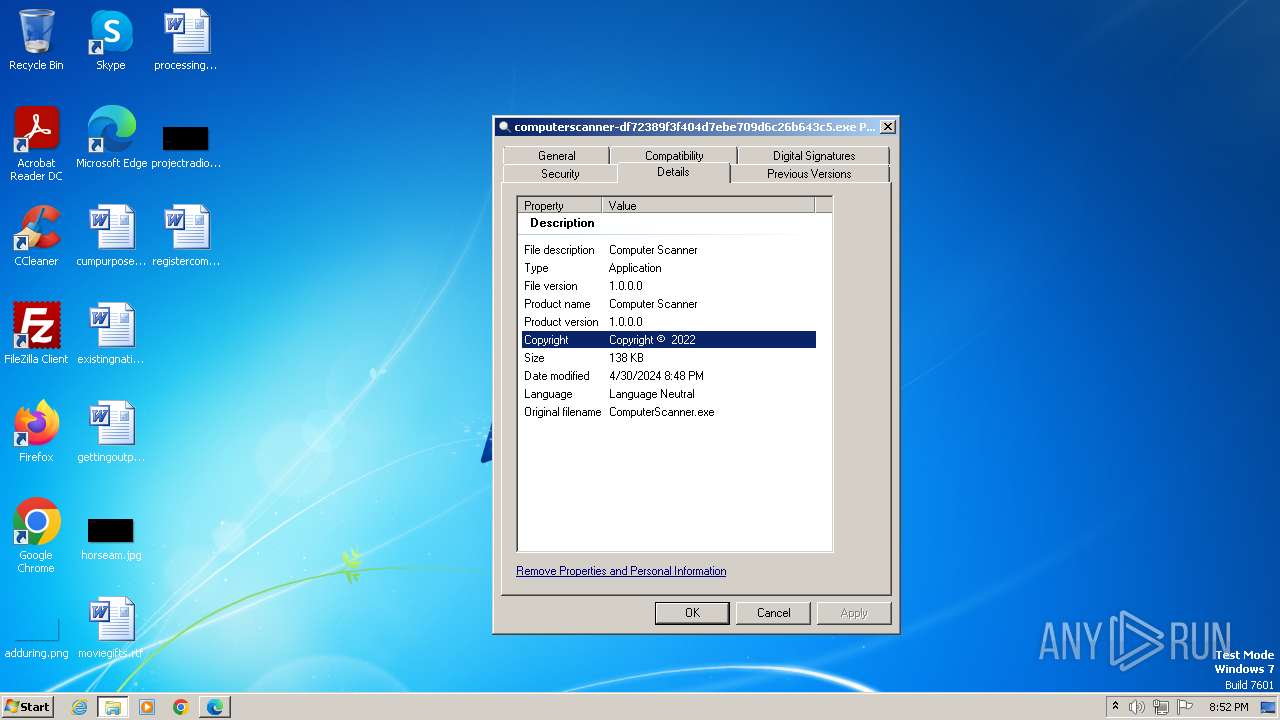
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:04:03 20:58:39+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 91648 |
| InitializedDataSize: | 37888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x185e6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
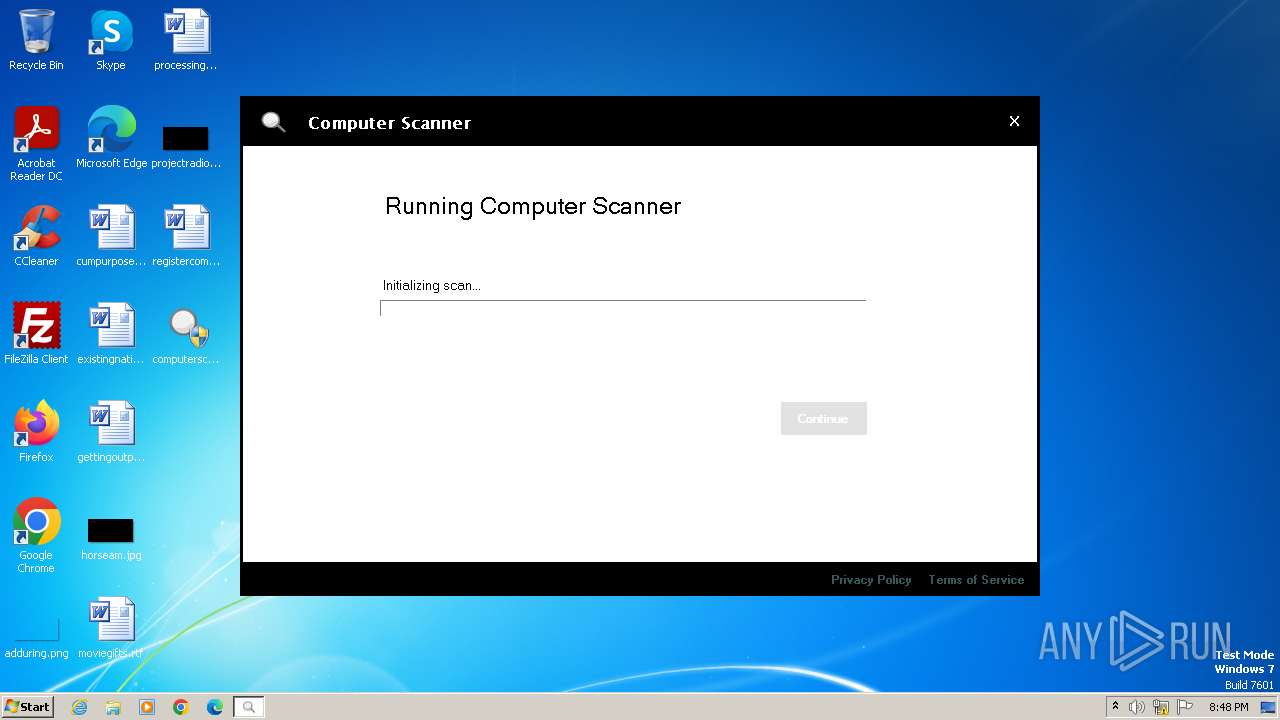
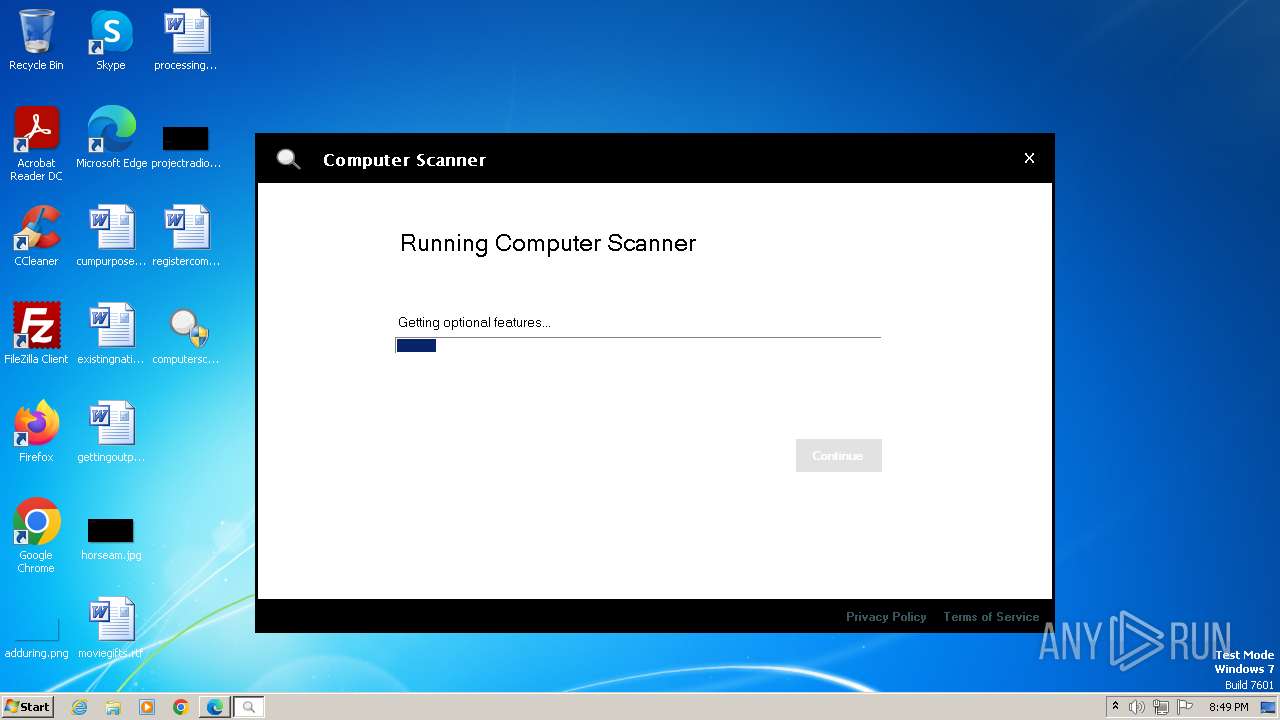
| FileDescription: | Computer Scanner |
| FileVersion: | 1.0.0.0 |
| InternalName: | ComputerScanner.exe |
| LegalCopyright: | Copyright © 2022 |
| LegalTrademarks: | - |
| OriginalFileName: | ComputerScanner.exe |
| ProductName: | Computer Scanner |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
101
Monitored processes
43
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 112 | "cscript.exe" /nologo GetReportsForGPO.wsf "Default Domain Policy" "C:\Users\admin\AppData\Local\Temp\x5reer2y.eor" | C:\Windows\System32\cscript.exe | — | nacmdline.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 188 | "caramfddownloader.exe" -url https://secure.eicar.org/eicarcom2.zip -outfile C:\Users\admin\AppData\Local\Temp\x5reer2y.eor\tmpdl\eicarcom2.zip -timeout 60000 | C:\Users\admin\AppData\Local\Temp\x5reer2y.eor\caramfddownloader.exe | caramfddc.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: CaraMfdDownloader Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 308 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6db0f598,0x6db0f5a8,0x6db0f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 820 | "C:\Users\admin\Desktop\computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe" | C:\Users\admin\Desktop\computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Computer Scanner Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --mojo-platform-channel-handle=3812 --field-trial-handle=1260,i,17238777248531062891,13176258209909172561,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1616 --field-trial-handle=1260,i,17238777248531062891,13176258209909172561,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2224 --field-trial-handle=1260,i,17238777248531062891,13176258209909172561,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1036 | "caramfddc.exe" -results "C:\Users\admin\AppData\Local\Temp\x5reer2y.eor\caramfddc-results.txt" | C:\Users\admin\AppData\Local\Temp\x5reer2y.eor\caramfddc.exe | — | nacmdline.exe | |||||||||||
User: admin Integrity Level: HIGH Description: CaraMfdDc Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1200 | "cscript.exe" /nologo GetReportsForGPO.wsf "Default Domain Controllers Policy" "C:\Users\admin\AppData\Local\Temp\x5reer2y.eor" | C:\Windows\System32\cscript.exe | — | nacmdline.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --first-renderer-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2208 --field-trial-handle=1260,i,17238777248531062891,13176258209909172561,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
70 462
Read events
69 853
Write events
587
Delete events
22
Modification events
| (PID) Process: | (820) computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\computerscanner-df72389f3f404d7ebe709d6c26b643c5_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (820) computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\computerscanner-df72389f3f404d7ebe709d6c26b643c5_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (820) computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\computerscanner-df72389f3f404d7ebe709d6c26b643c5_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (820) computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\computerscanner-df72389f3f404d7ebe709d6c26b643c5_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (820) computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\computerscanner-df72389f3f404d7ebe709d6c26b643c5_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (820) computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\computerscanner-df72389f3f404d7ebe709d6c26b643c5_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (820) computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\computerscanner-df72389f3f404d7ebe709d6c26b643c5_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (820) computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\computerscanner-df72389f3f404d7ebe709d6c26b643c5_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (820) computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\computerscanner-df72389f3f404d7ebe709d6c26b643c5_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (820) computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\computerscanner-df72389f3f404d7ebe709d6c26b643c5_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
187
Suspicious files
149
Text files
127
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\919660c4-a898-401e-9039-e5a53f1c4e39.tmp | — | |
MD5:— | SHA256:— | |||
| 1764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\e63f382b-144f-42dc-8485-15d152e07afd.tmp | — | |
MD5:— | SHA256:— | |||
| 1932 | msedge.exe | — | ||
MD5:— | SHA256:— | |||
| 1764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF106321.TMP | — | |
MD5:— | SHA256:— | |||
| 1796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1064e6.TMP | — | |
MD5:— | SHA256:— | |||
| 1796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF106524.TMP | — | |
MD5:— | SHA256:— | |||
| 1796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF106534.TMP | — | |
MD5:— | SHA256:— | |||
| 1796 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1065d0.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
184
DNS requests
128
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2996 | ndconnector.exe | GET | 200 | 151.101.130.133:80 | http://secure.globalsign.com/cacert/codesigningrootr45.crt | US | binary | 1.37 Kb | unknown |
3860 | nacmdline.exe | GET | 301 | 157.240.0.35:80 | http://www.facebook.com/ | US | — | — | unknown |
2996 | ndconnector.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b22752994c8bd8f0 | US | compressed | 68.3 Kb | unknown |
3860 | nacmdline.exe | GET | 301 | 87.248.119.252:80 | http://mail.yahoo.com/ | GB | html | 305 b | unknown |
3860 | nacmdline.exe | GET | 502 | 104.18.11.206:80 | http://www.playboy.com/ | unknown | html | 155 b | unknown |
3860 | nacmdline.exe | GET | 301 | 34.111.176.156:80 | http://www.myspace.com/ | US | — | — | unknown |
3860 | nacmdline.exe | GET | 301 | 142.250.181.238:80 | http://gmail.google.com/ | US | html | 215 b | unknown |
3860 | nacmdline.exe | GET | 301 | 142.250.181.238:80 | http://gmail.google.com/mail/ | US | html | 215 b | unknown |
3860 | nacmdline.exe | GET | 301 | 54.230.228.42:80 | http://espn.com/ | US | html | 229 b | unknown |
3860 | nacmdline.exe | POST | 200 | 52.54.38.130:80 | http://go.rapidfiretools.com/remotews3/fmit_na_ws.asmx | US | xml | 389 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
820 | computerscanner-df72389f3f404d7ebe709d6c26b643c5.exe | 108.138.36.71:443 | download.rapidfiretools.com | AMAZON-02 | US | unknown |
2520 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2520 | msedge.exe | 99.83.231.61:443 | www.rapidfiretools.com | AMAZON-02 | US | unknown |
1796 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
2520 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
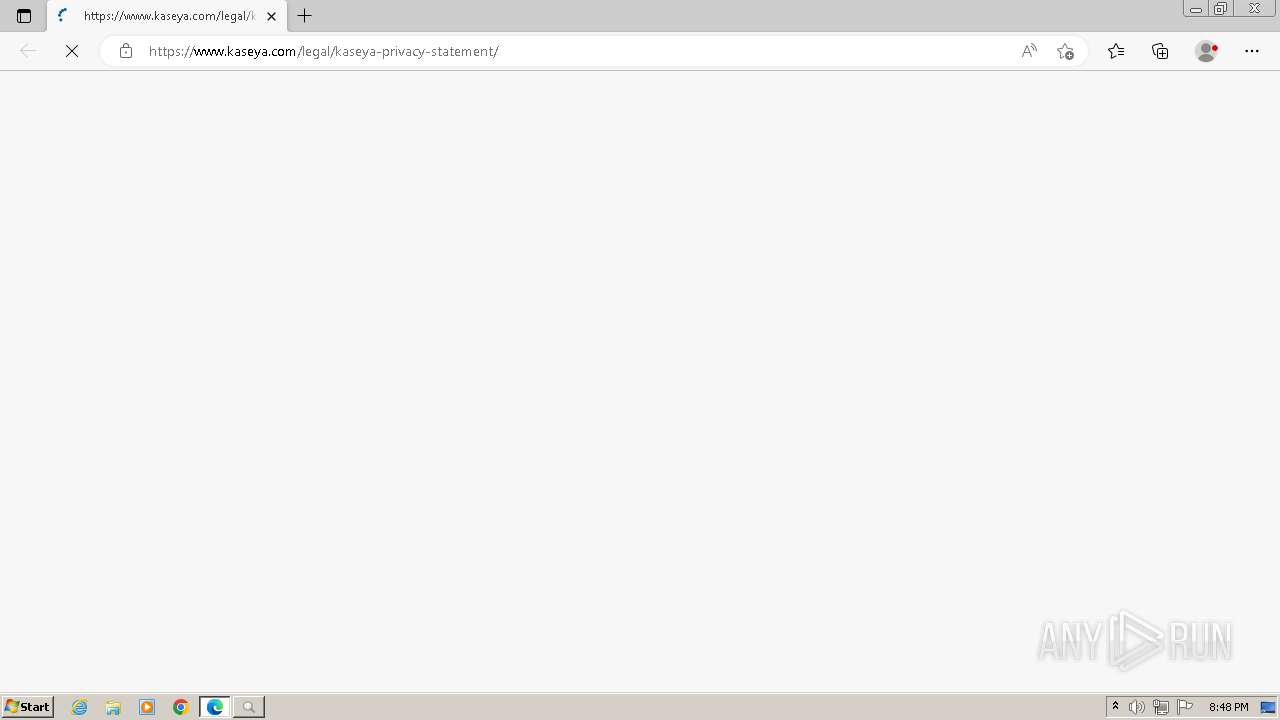
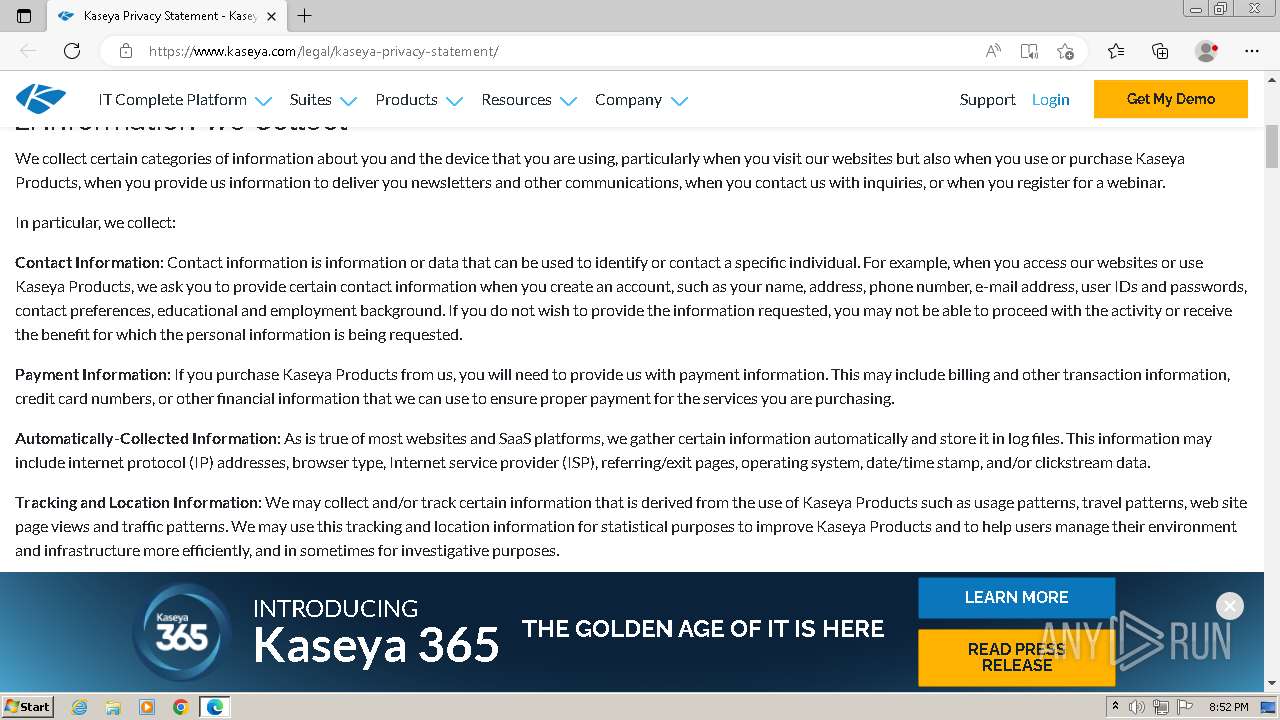
2520 | msedge.exe | 141.193.213.21:443 | www.kaseya.com | — | — | whitelisted |
2520 | msedge.exe | 18.173.187.125:443 | cdn.neverbounce.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.rapidfiretools.com |
| unknown |
config.edge.skype.com |
| whitelisted |
www.rapidfiretools.com |
| unknown |
edge.microsoft.com |
| whitelisted |
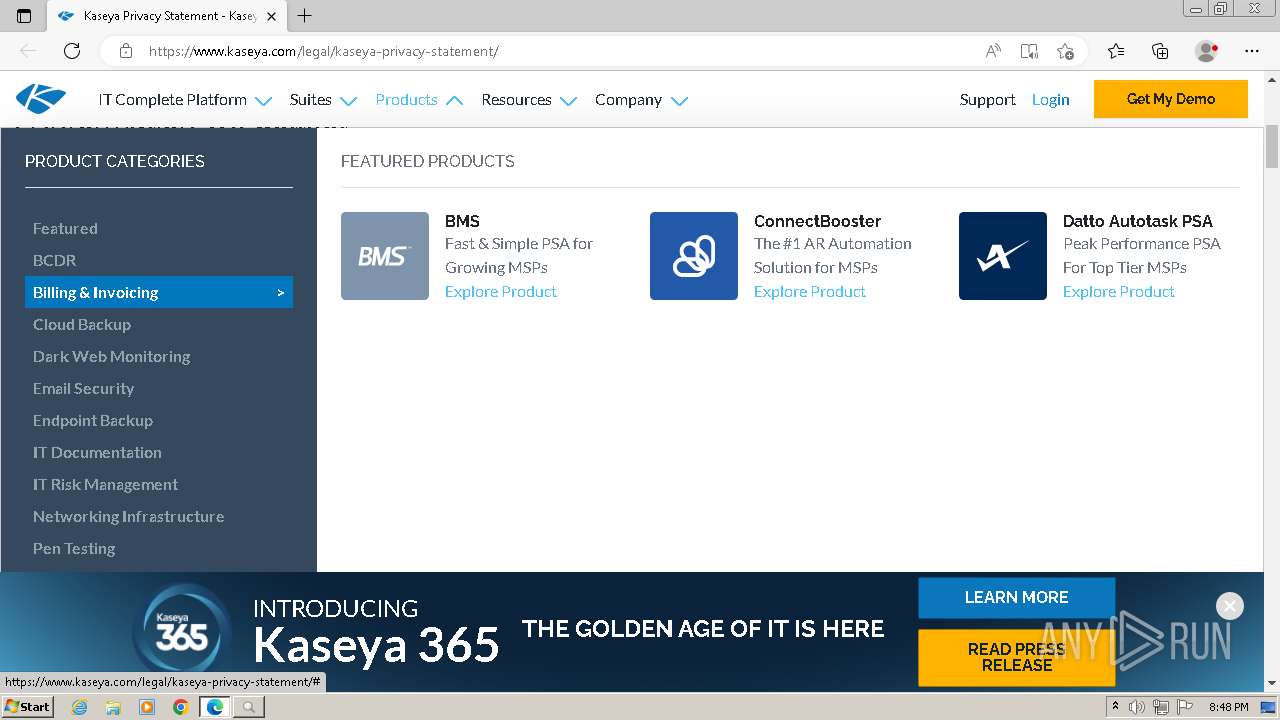
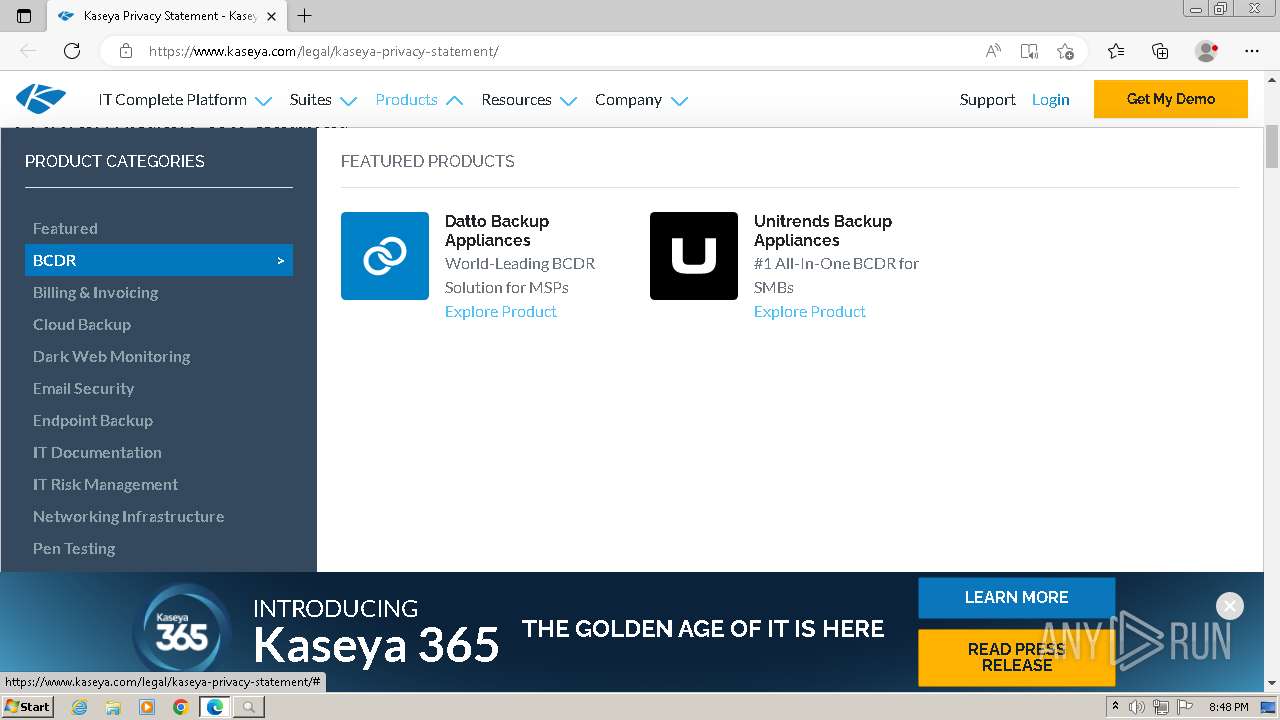
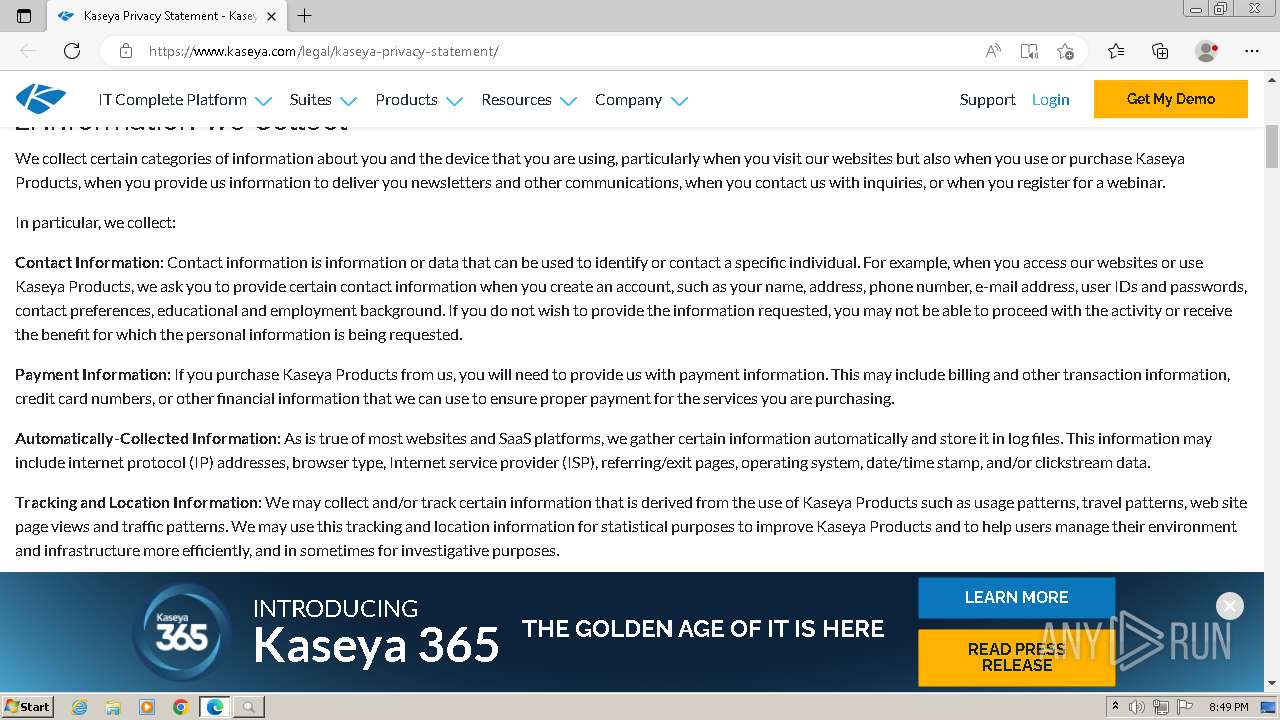
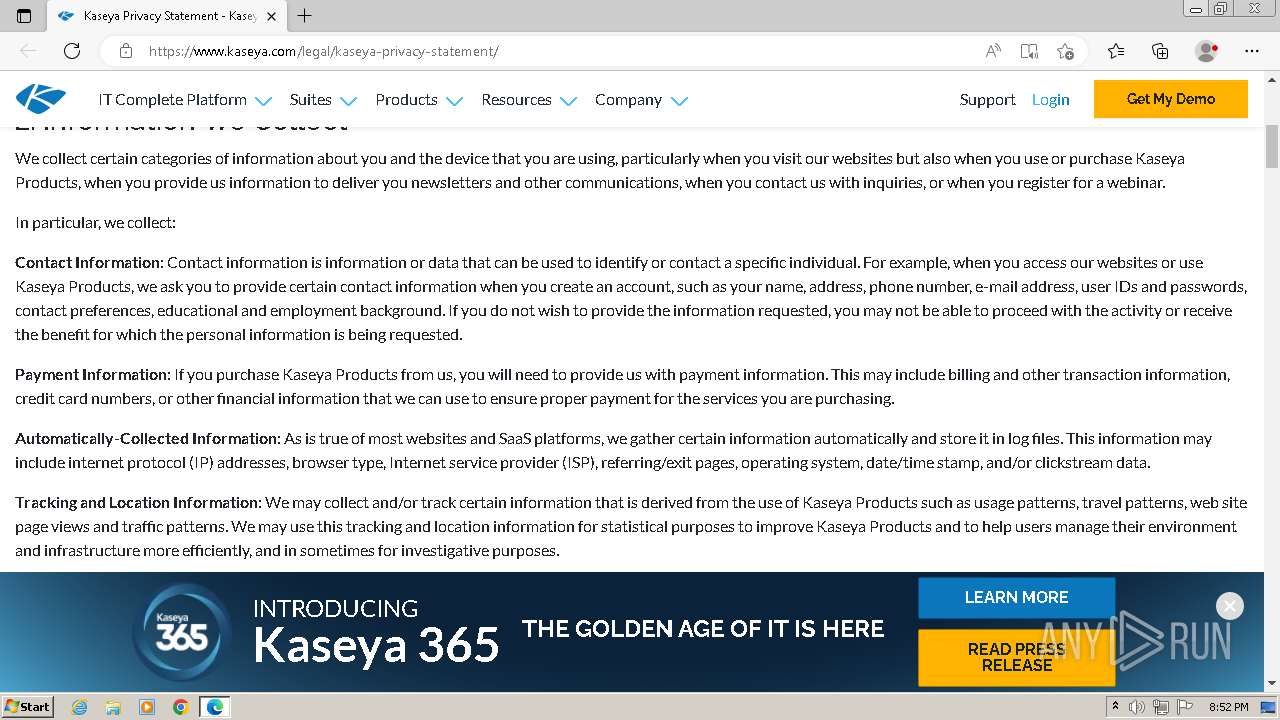
www.kaseya.com |
| unknown |
a.omappapi.com |
| unknown |
cdn.neverbounce.com |
| whitelisted |
kit.fontawesome.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3860 | nacmdline.exe | A Network Trojan was detected | ET HUNTING Terse Unencrypted Request for Google - Likely Connectivity Check |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
nacmdline.exe | Native library pre-loader is trying to load native SQLite library "C:\Users\admin\AppData\Local\Temp\x5reer2y.eor\x86\SQLite.Interop.dll"...
|
nacmdline.exe | SQLite error (1): no such table: eventlogs
|
nacmdline.exe | SQLite error (1): no such table: eventlogs
|
nacmdline.exe | SQLite error (1): no such table: eventlogs
|
nacmdline.exe | SQLite error (1): no such table: eventlogs
|
nacmdline.exe | SQLite error (1): no such table: eventlogs
|
nacmdline.exe | SQLite error (1): no such table: eventlogs
|
nacmdline.exe | SQLite error (1): no such table: eventlogs
|
nacmdline.exe | SQLite error (1): no such table: eventlogs
|
nacmdline.exe | SQLite error (1): no such table: eventlogs
|