| File name: | BLTools v2.2.exe |
| Full analysis: | https://app.any.run/tasks/2b2e4b36-28df-4d7e-bd53-a32bf881145b |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 18:33:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | C5F00AD1E40B07A62D44A6E03856249F |
| SHA1: | 0254F337D817AAA6E7BB0DDAA8E03A02FEF6814C |
| SHA256: | 35059D9250CE74D1048175F7ABEA89B0946B57050E51E24B52DD1891A69064F6 |
| SSDEEP: | 24576:3Uv6CtZFuFxte97o2JpbDp/ymFpbSmOpSPLMOTER2na5Um/Ks0CRxUyPLFrcYIto:3USk13FnpySD0Gij//Nqyp4Y4o |
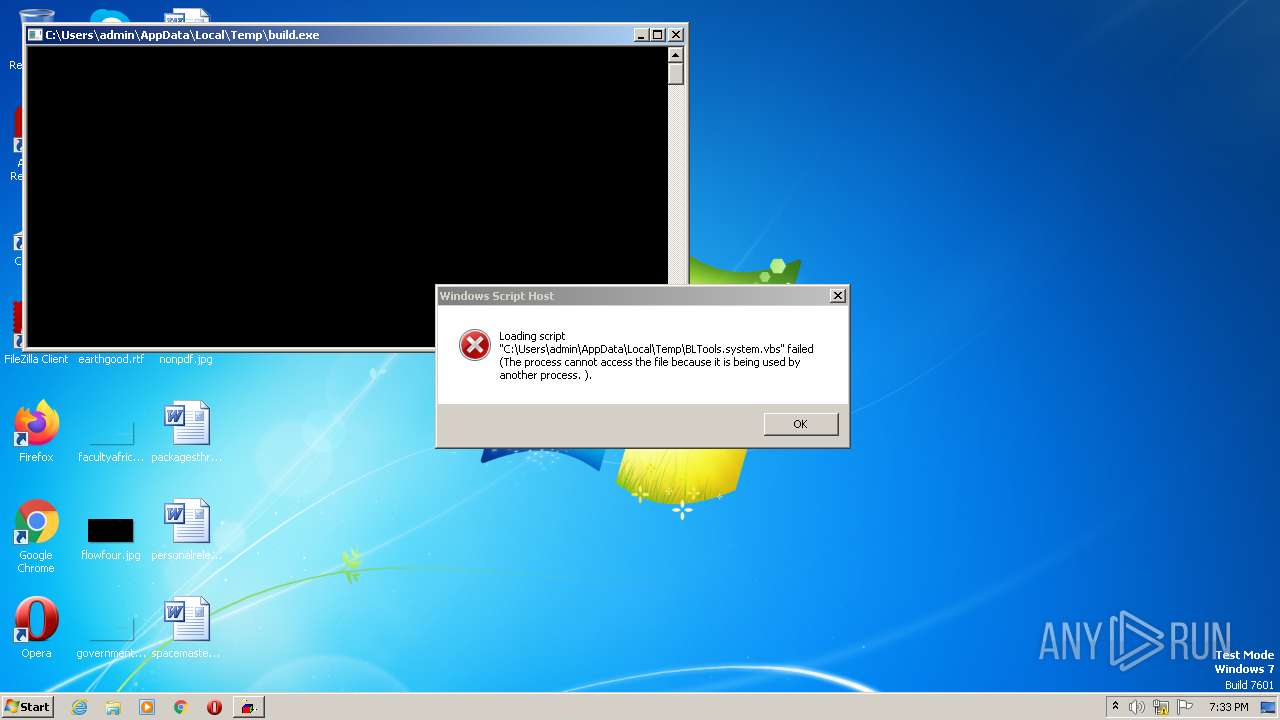
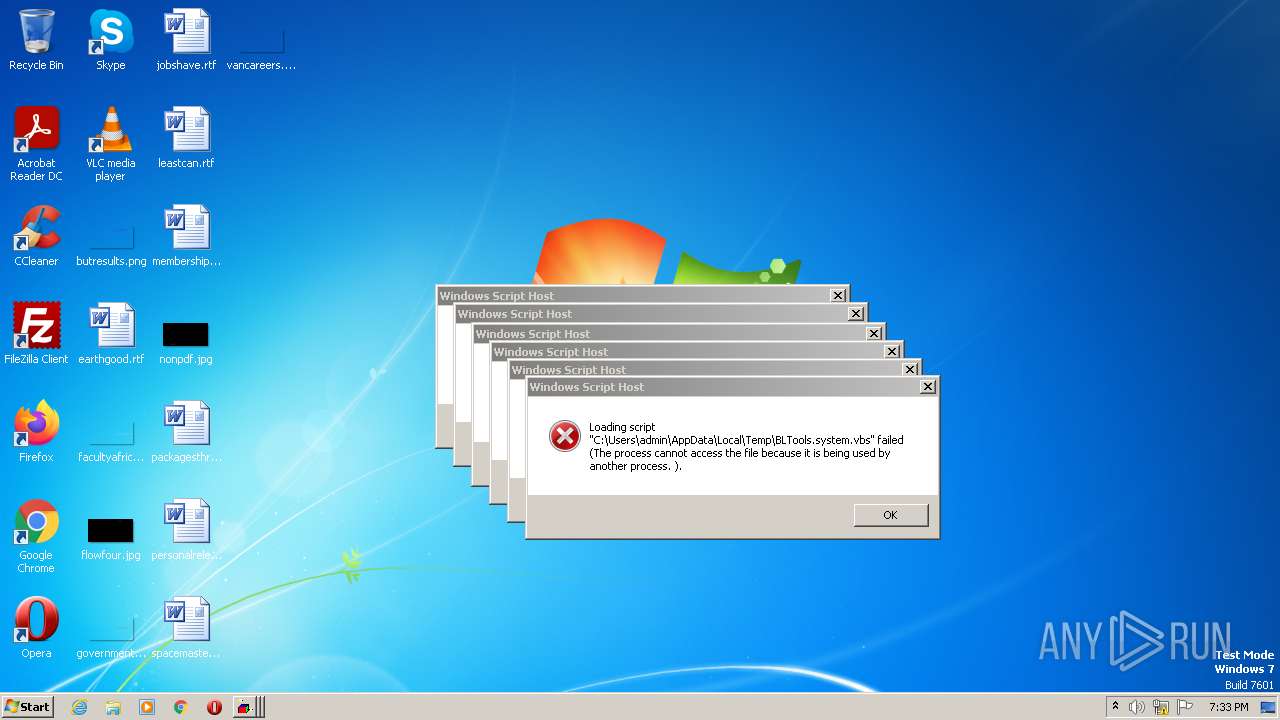
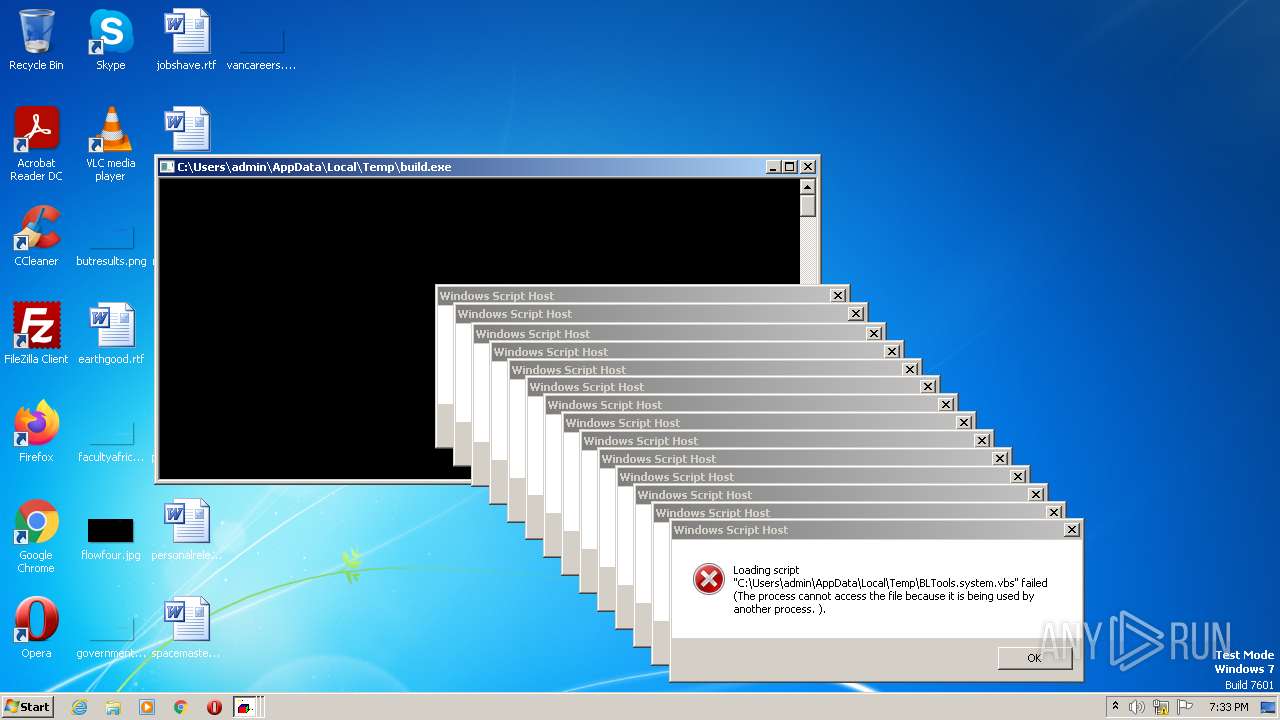
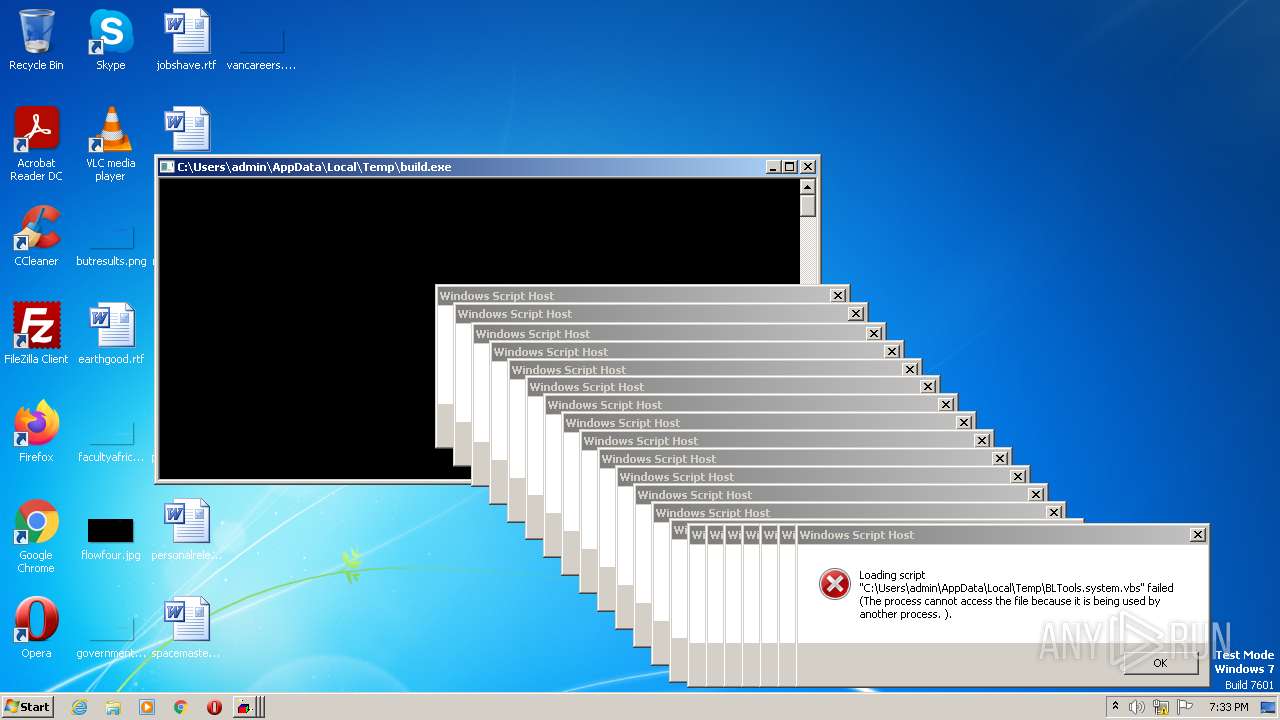
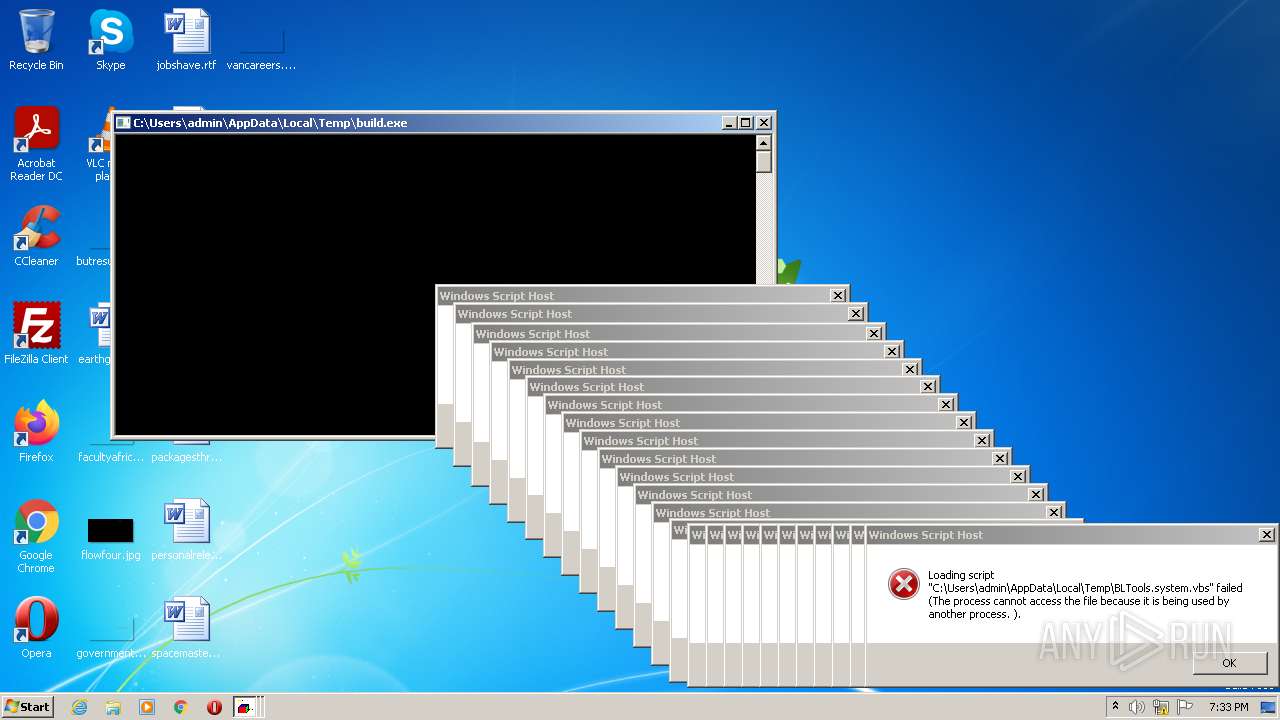
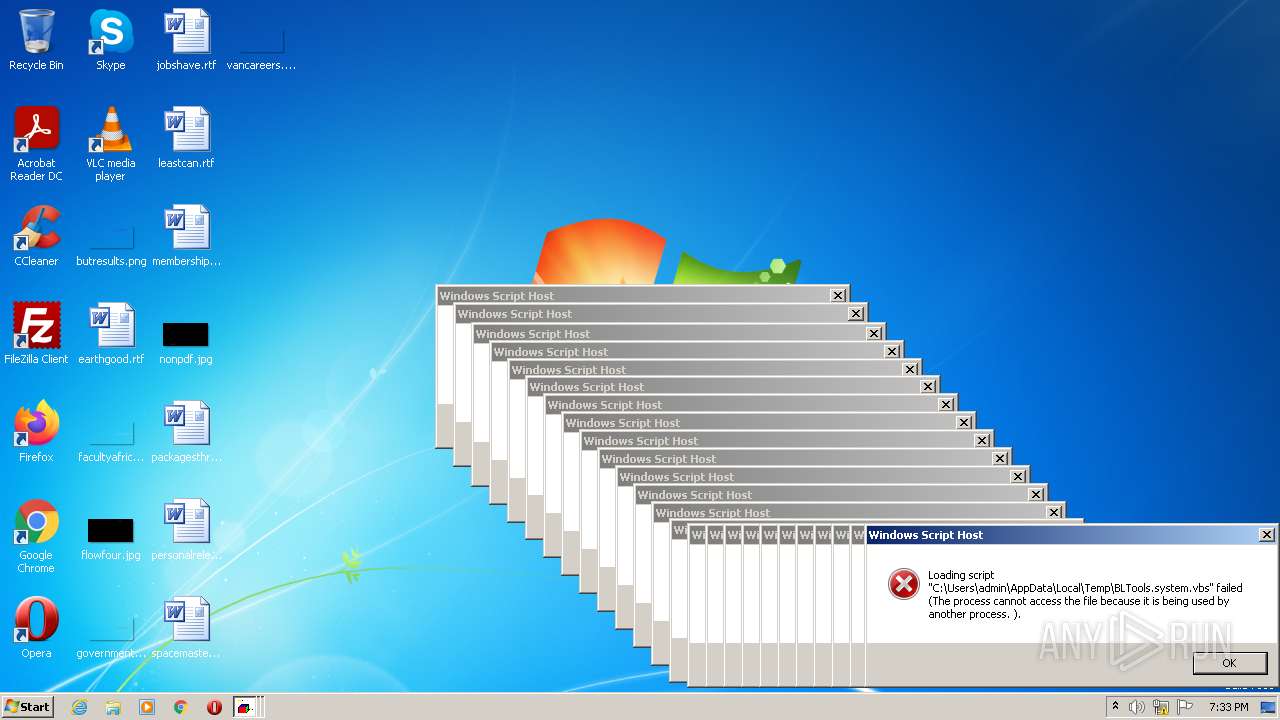
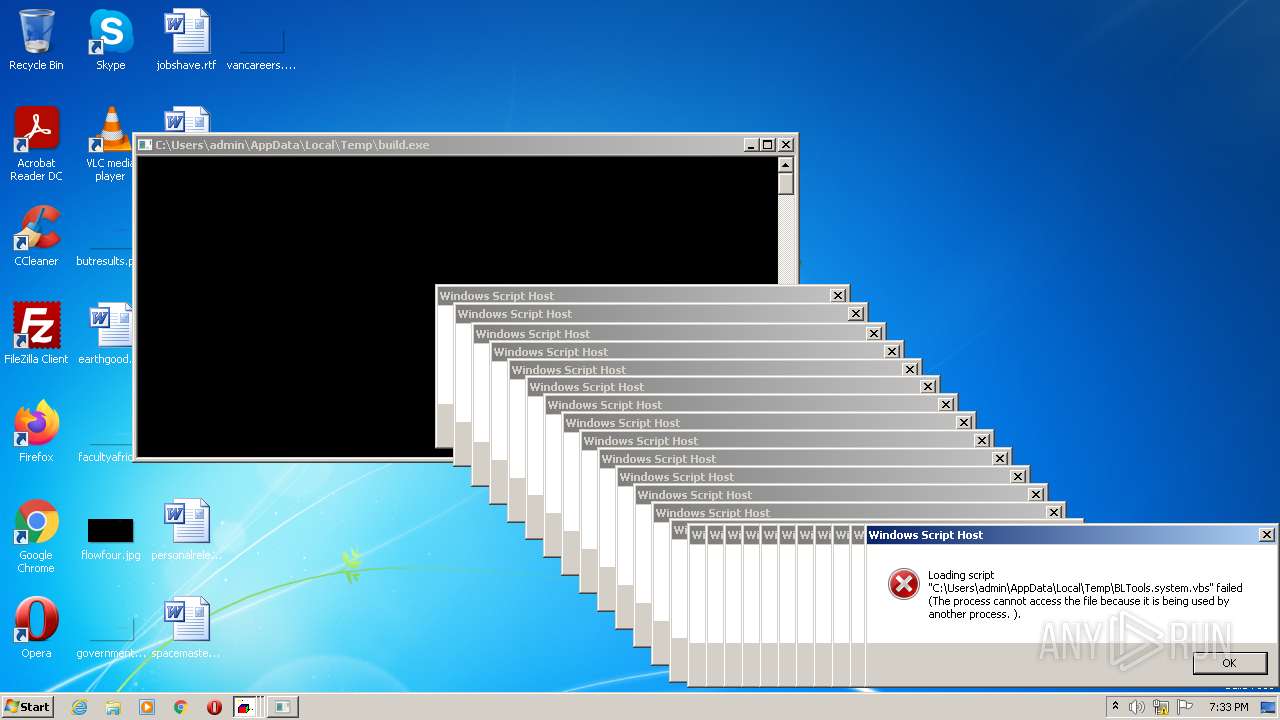
MALICIOUS
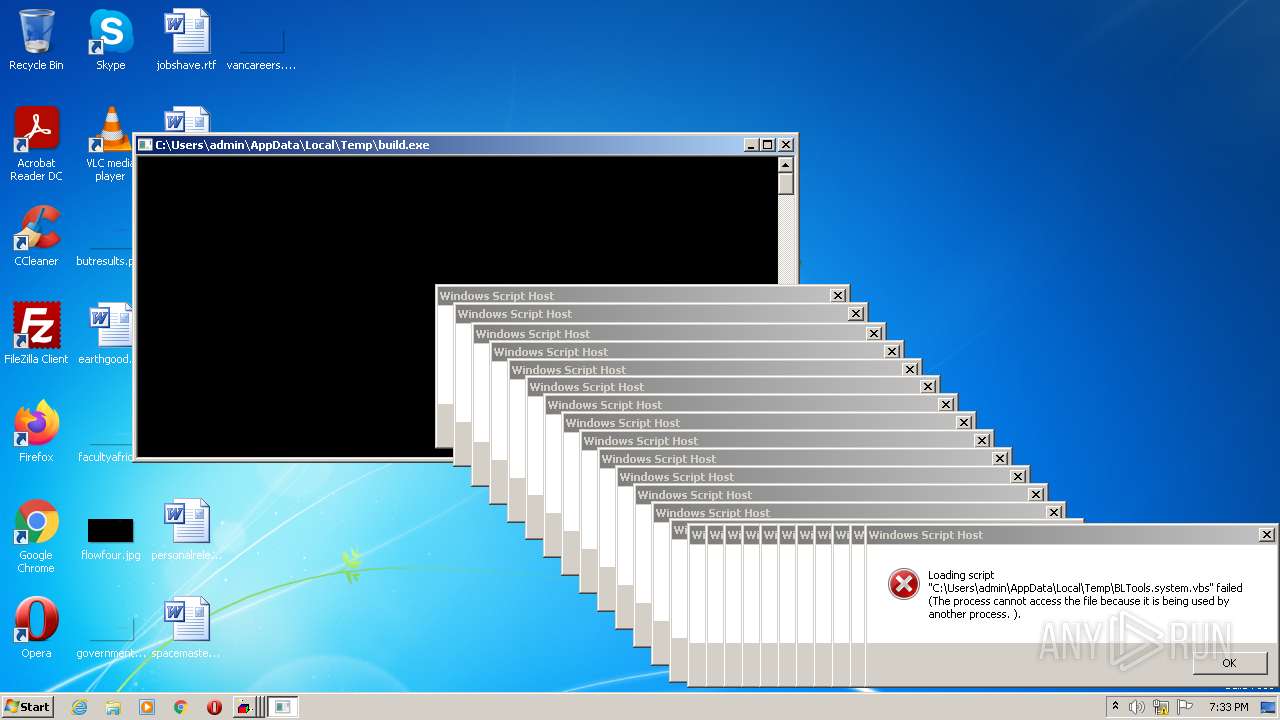
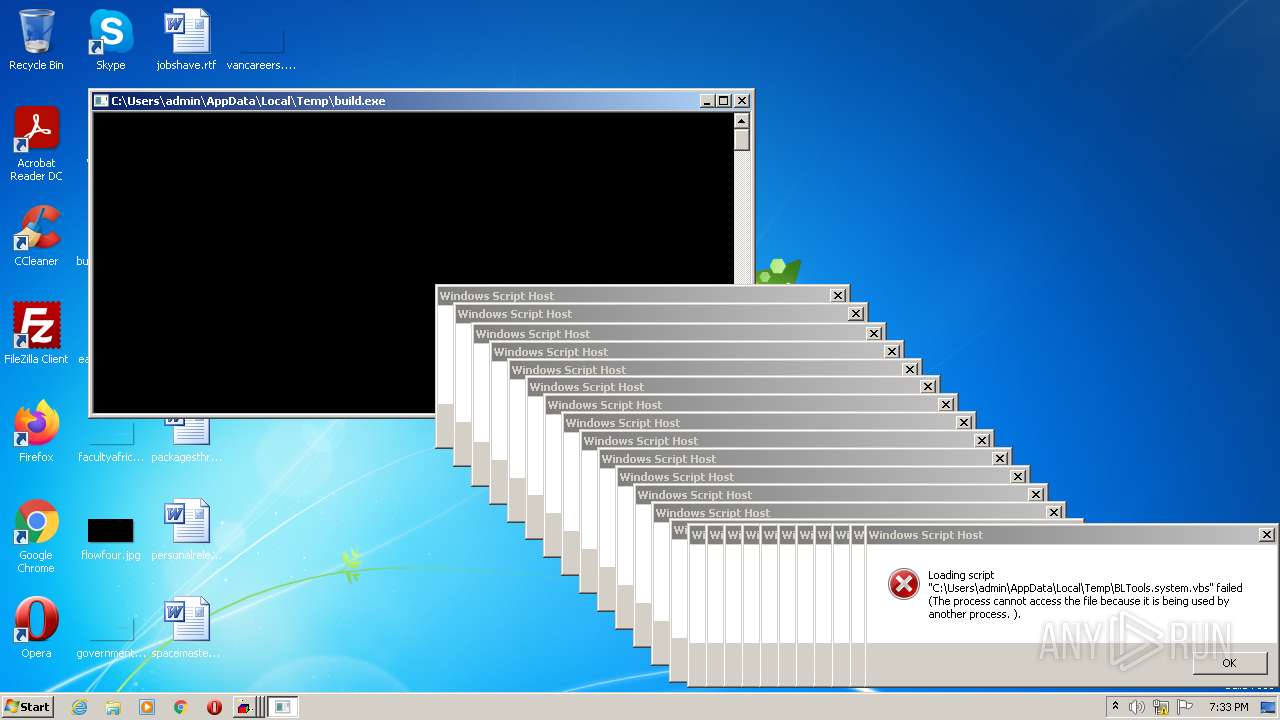
Application was dropped or rewritten from another process
- build.exe (PID: 3784)
- build.exe (PID: 2064)
- build.exe (PID: 3632)
- build.exe (PID: 3280)
- build.exe (PID: 1788)
- build.exe (PID: 568)
- build.exe (PID: 3316)
- build.exe (PID: 1920)
- build.exe (PID: 3648)
- build.exe (PID: 3612)
- build.exe (PID: 2380)
- build.exe (PID: 2472)
- build.exe (PID: 3820)
- build.exe (PID: 900)
- build.exe (PID: 3372)
- build.exe (PID: 3312)
- build.exe (PID: 3116)
- build.exe (PID: 3400)
- build.exe (PID: 1352)
- build.exe (PID: 3080)
- build.exe (PID: 2964)
- build.exe (PID: 4324)
- build.exe (PID: 5220)
- build.exe (PID: 3068)
- build.exe (PID: 4036)
- build.exe (PID: 920)
- build.exe (PID: 4924)
- build.exe (PID: 6016)
- build.exe (PID: 6036)
- build.exe (PID: 6076)
- build.exe (PID: 4996)
- build.exe (PID: 5028)
- build.exe (PID: 4184)
- build.exe (PID: 5424)
- build.exe (PID: 4600)
- build.exe (PID: 6004)
- build.exe (PID: 5388)
- build.exe (PID: 5936)
- build.exe (PID: 5212)
- build.exe (PID: 4952)
- build.exe (PID: 4356)
- build.exe (PID: 5712)
- build.exe (PID: 4656)
- build.exe (PID: 4396)
- build.exe (PID: 6060)
- build.exe (PID: 3204)
- build.exe (PID: 5236)
- build.exe (PID: 6100)
- build.exe (PID: 4416)
- build.exe (PID: 4240)
- build.exe (PID: 5920)
- build.exe (PID: 7388)
- build.exe (PID: 4984)
- build.exe (PID: 7124)
- build.exe (PID: 4832)
- build.exe (PID: 3144)
- build.exe (PID: 6480)
- build.exe (PID: 7072)
- build.exe (PID: 8140)
- build.exe (PID: 7144)
- build.exe (PID: 8148)
- build.exe (PID: 7924)
- build.exe (PID: 6748)
- build.exe (PID: 7368)
- build.exe (PID: 6260)
- build.exe (PID: 6284)
- build.exe (PID: 7364)
- build.exe (PID: 6648)
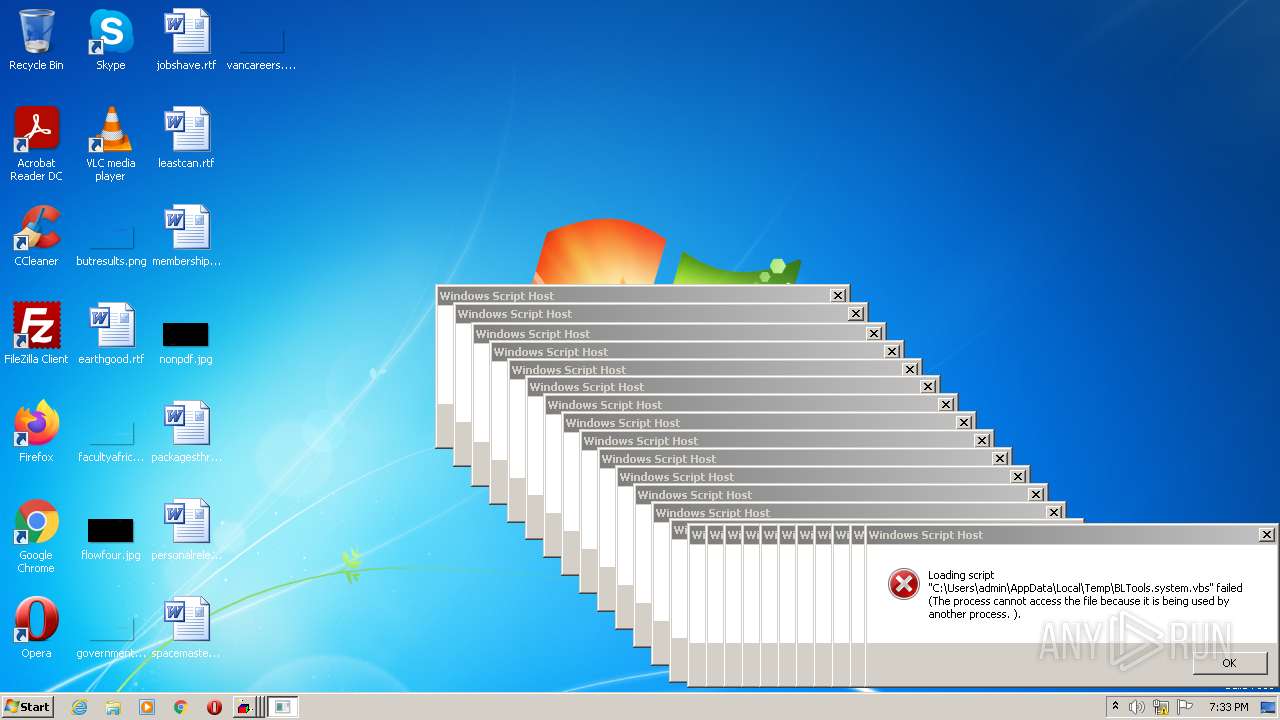
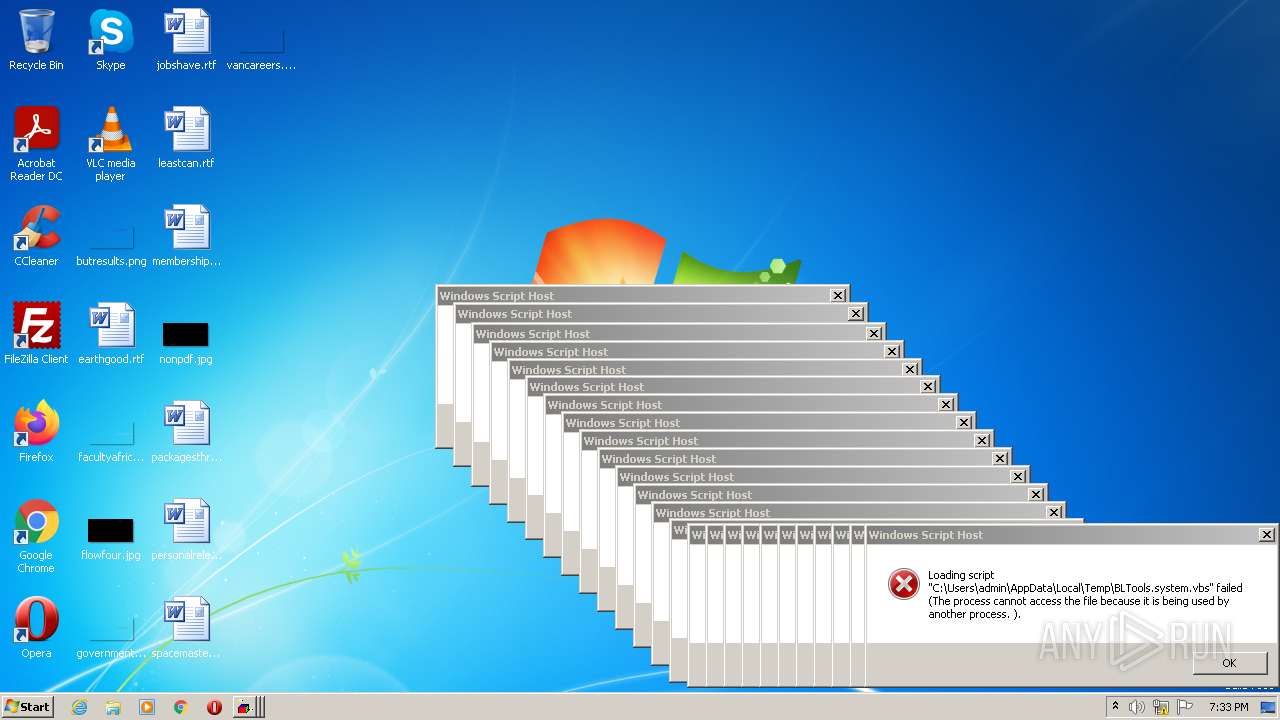
SUSPICIOUS
Application launched itself
- BLTools v2.2.exe (PID: 3340)
- BLTools v2.2.exe (PID: 3860)
- BLTools v2.2.exe (PID: 2928)
- BLTools v2.2.exe (PID: 4060)
- BLTools v2.2.exe (PID: 3104)
- BLTools v2.2.exe (PID: 2804)
- BLTools v2.2.exe (PID: 1704)
- BLTools v2.2.exe (PID: 3532)
- BLTools v2.2.exe (PID: 2428)
- BLTools v2.2.exe (PID: 2920)
- BLTools v2.2.exe (PID: 1400)
- BLTools v2.2.exe (PID: 2928)
- BLTools v2.2.exe (PID: 3692)
- BLTools v2.2.exe (PID: 3508)
- BLTools v2.2.exe (PID: 3600)
- BLTools v2.2.exe (PID: 3604)
- BLTools v2.2.exe (PID: 2824)
- BLTools v2.2.exe (PID: 3560)
- BLTools v2.2.exe (PID: 2644)
- BLTools v2.2.exe (PID: 3180)
- BLTools v2.2.exe (PID: 1764)
- BLTools v2.2.exe (PID: 2568)
- BLTools v2.2.exe (PID: 2588)
- BLTools v2.2.exe (PID: 2568)
- BLTools v2.2.exe (PID: 4428)
- BLTools v2.2.exe (PID: 1048)
- BLTools v2.2.exe (PID: 5072)
- BLTools v2.2.exe (PID: 6124)
- BLTools v2.2.exe (PID: 5016)
- BLTools v2.2.exe (PID: 2544)
- BLTools v2.2.exe (PID: 5356)
- BLTools v2.2.exe (PID: 2792)
- BLTools v2.2.exe (PID: 5252)
- BLTools v2.2.exe (PID: 4212)
- BLTools v2.2.exe (PID: 5480)
- BLTools v2.2.exe (PID: 4768)
- BLTools v2.2.exe (PID: 6132)
- BLTools v2.2.exe (PID: 5596)
- BLTools v2.2.exe (PID: 6116)
- BLTools v2.2.exe (PID: 4584)
- BLTools v2.2.exe (PID: 4288)
- BLTools v2.2.exe (PID: 2788)
- BLTools v2.2.exe (PID: 5932)
- BLTools v2.2.exe (PID: 4880)
- BLTools v2.2.exe (PID: 5516)
- BLTools v2.2.exe (PID: 3812)
- BLTools v2.2.exe (PID: 6128)
- BLTools v2.2.exe (PID: 3144)
- BLTools v2.2.exe (PID: 4748)
- BLTools v2.2.exe (PID: 4728)
- BLTools v2.2.exe (PID: 6112)
- BLTools v2.2.exe (PID: 4864)
- BLTools v2.2.exe (PID: 7492)
- BLTools v2.2.exe (PID: 5024)
- BLTools v2.2.exe (PID: 4808)
- BLTools v2.2.exe (PID: 6620)
- BLTools v2.2.exe (PID: 5988)
- BLTools v2.2.exe (PID: 6252)
- BLTools v2.2.exe (PID: 7276)
- BLTools v2.2.exe (PID: 6172)
- BLTools v2.2.exe (PID: 7212)
- BLTools v2.2.exe (PID: 7608)
- BLTools v2.2.exe (PID: 6768)
- BLTools v2.2.exe (PID: 8136)
- BLTools v2.2.exe (PID: 7620)
- BLTools v2.2.exe (PID: 6928)
- BLTools v2.2.exe (PID: 7288)
- BLTools v2.2.exe (PID: 6328)
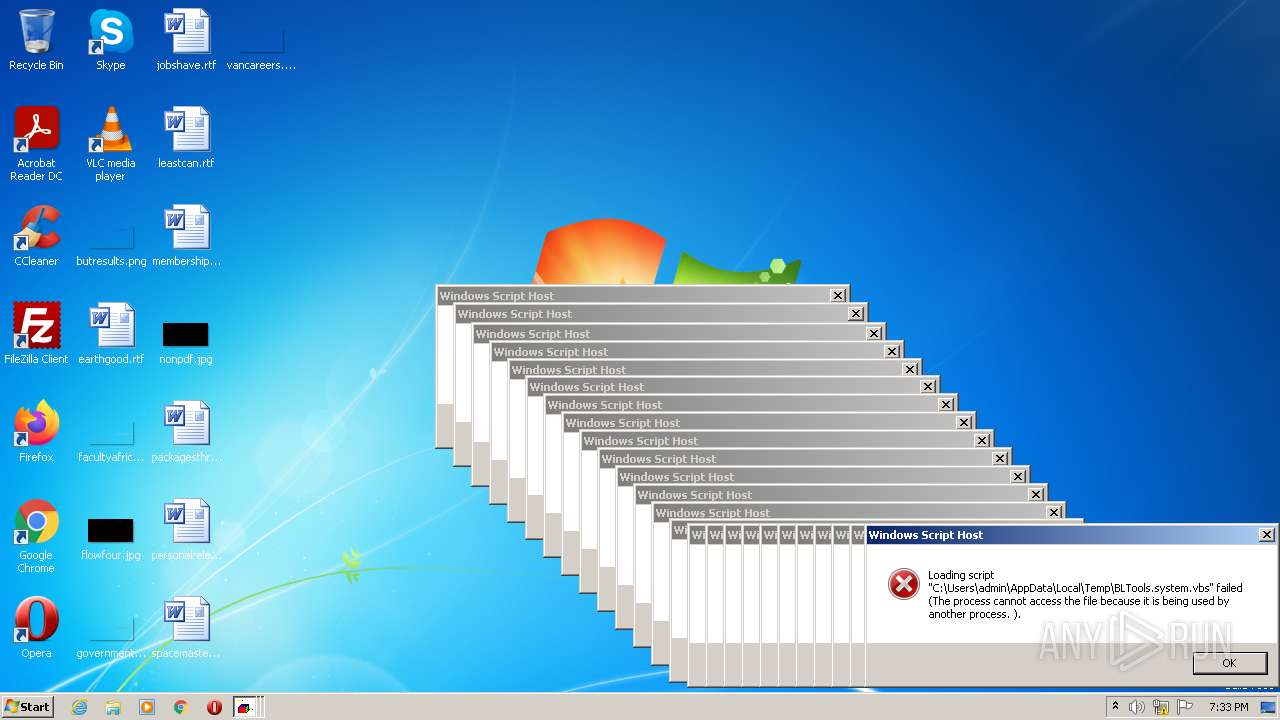
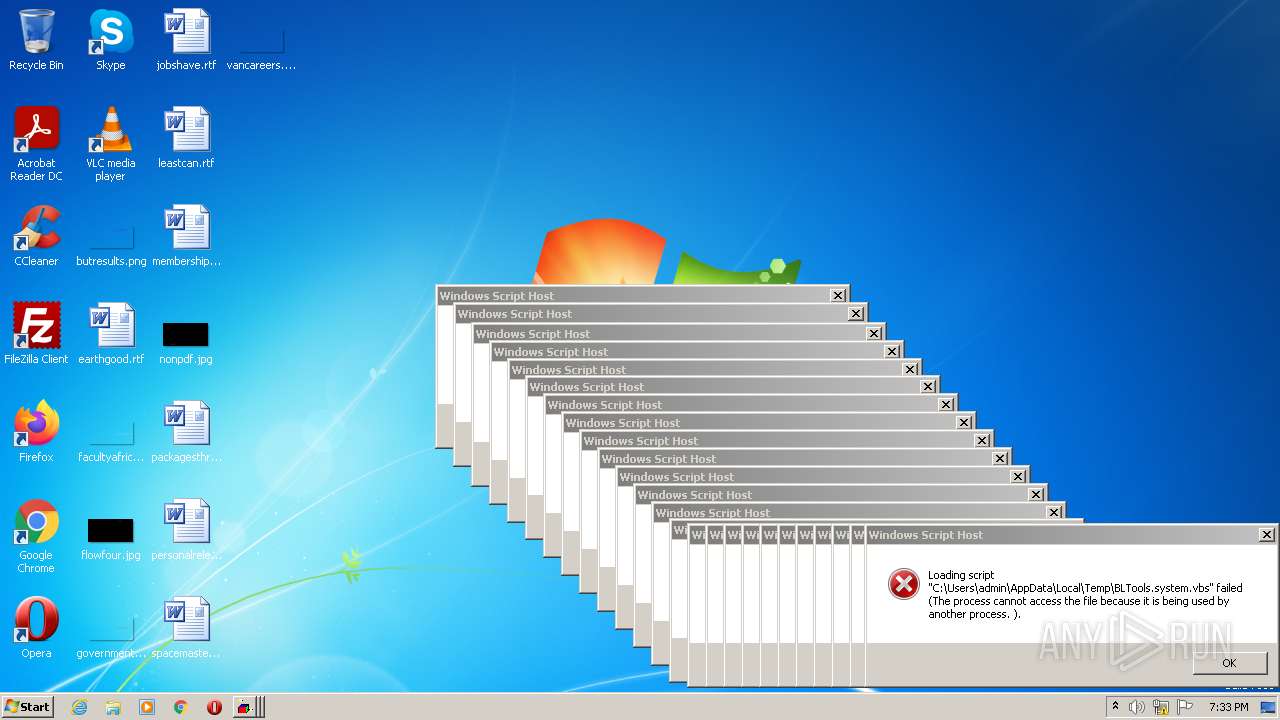
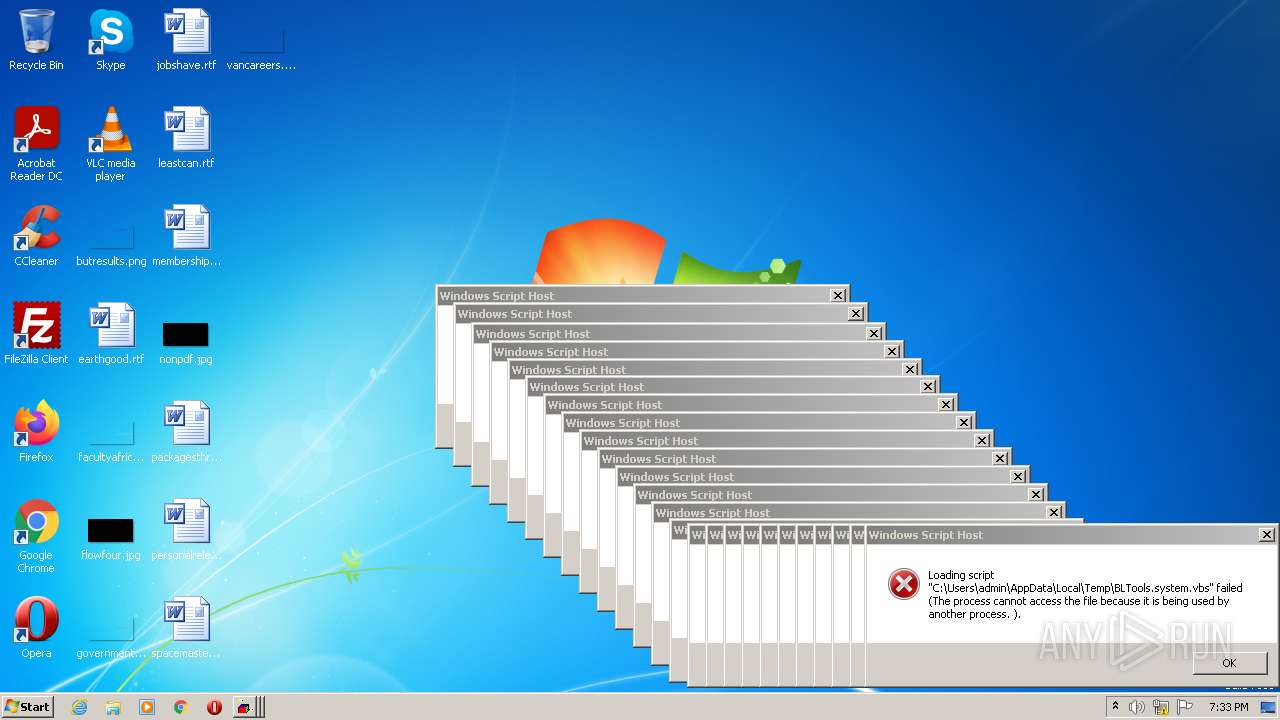
The process executes VB scripts
- BLTools v2.2.exe (PID: 3340)
- BLTools v2.2.exe (PID: 3860)
- BLTools v2.2.exe (PID: 2928)
- BLTools v2.2.exe (PID: 4060)
- BLTools v2.2.exe (PID: 3104)
- BLTools v2.2.exe (PID: 2804)
- BLTools v2.2.exe (PID: 1704)
- BLTools v2.2.exe (PID: 2920)
- BLTools v2.2.exe (PID: 2428)
- BLTools v2.2.exe (PID: 1400)
- BLTools v2.2.exe (PID: 3692)
- BLTools v2.2.exe (PID: 3532)
- BLTools v2.2.exe (PID: 3600)
- BLTools v2.2.exe (PID: 2928)
- BLTools v2.2.exe (PID: 3604)
- BLTools v2.2.exe (PID: 3508)
- BLTools v2.2.exe (PID: 2824)
- BLTools v2.2.exe (PID: 1048)
- BLTools v2.2.exe (PID: 3180)
- BLTools v2.2.exe (PID: 1764)
- BLTools v2.2.exe (PID: 3560)
- BLTools v2.2.exe (PID: 2644)
- BLTools v2.2.exe (PID: 2588)
- BLTools v2.2.exe (PID: 2568)
- BLTools v2.2.exe (PID: 5356)
- BLTools v2.2.exe (PID: 2568)
- BLTools v2.2.exe (PID: 4428)
- BLTools v2.2.exe (PID: 6124)
- BLTools v2.2.exe (PID: 5252)
- BLTools v2.2.exe (PID: 2544)
- BLTools v2.2.exe (PID: 2792)
- BLTools v2.2.exe (PID: 5072)
- BLTools v2.2.exe (PID: 5016)
- BLTools v2.2.exe (PID: 4212)
- BLTools v2.2.exe (PID: 4768)
- BLTools v2.2.exe (PID: 6132)
- BLTools v2.2.exe (PID: 5480)
- BLTools v2.2.exe (PID: 4288)
- BLTools v2.2.exe (PID: 3812)
- BLTools v2.2.exe (PID: 5596)
- BLTools v2.2.exe (PID: 6116)
- BLTools v2.2.exe (PID: 4584)
- BLTools v2.2.exe (PID: 5932)
- BLTools v2.2.exe (PID: 4880)
- BLTools v2.2.exe (PID: 5516)
- BLTools v2.2.exe (PID: 6128)
- BLTools v2.2.exe (PID: 2788)
- BLTools v2.2.exe (PID: 4728)
- BLTools v2.2.exe (PID: 6112)
- BLTools v2.2.exe (PID: 4864)
- BLTools v2.2.exe (PID: 3144)
- BLTools v2.2.exe (PID: 4748)
- BLTools v2.2.exe (PID: 6252)
- BLTools v2.2.exe (PID: 6620)
- BLTools v2.2.exe (PID: 7492)
- BLTools v2.2.exe (PID: 5024)
- BLTools v2.2.exe (PID: 4808)
- BLTools v2.2.exe (PID: 7212)
- BLTools v2.2.exe (PID: 7288)
- BLTools v2.2.exe (PID: 5988)
- BLTools v2.2.exe (PID: 7276)
- BLTools v2.2.exe (PID: 6172)
- BLTools v2.2.exe (PID: 8136)
- BLTools v2.2.exe (PID: 7620)
- BLTools v2.2.exe (PID: 6928)
- BLTools v2.2.exe (PID: 6328)
- BLTools v2.2.exe (PID: 7608)
- BLTools v2.2.exe (PID: 6768)
Executable content was dropped or overwritten
- BLTools v2.2.exe (PID: 3340)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x315d |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 165376 |
| CodeSize: | 23552 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2007:03:31 15:09:55+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Mar-2007 15:09:55 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 31-Mar-2007 15:09:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005BBA | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47701 |
.rdata | 0x00007000 | 0x000011F0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.27568 |
.data | 0x00009000 | 0x000260D4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.15843 |
.ndata | 0x00030000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00038000 | 0x00010C08 | 0x00010E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.41108 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.44469 | 67624 | UNKNOWN | English - United States | RT_ICON |
103 | 1.98048 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
312
Monitored processes
206
Malicious processes
7
Suspicious processes
55
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 568 | "C:\Users\admin\AppData\Local\Temp\build.exe" | C:\Users\admin\AppData\Local\Temp\build.exe | — | BLTools v2.2.exe |
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 | ||||
| 660 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\BLTools.system.vbs" | C:\Windows\System32\wscript.exe | — | BLTools v2.2.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 | ||||
| 900 | "C:\Users\admin\AppData\Local\Temp\build.exe" | C:\Users\admin\AppData\Local\Temp\build.exe | — | BLTools v2.2.exe |
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 | ||||
| 920 | "C:\Users\admin\AppData\Local\Temp\build.exe" | C:\Users\admin\AppData\Local\Temp\build.exe | — | BLTools v2.2.exe |
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 | ||||
| 1048 | "C:\Users\admin\AppData\Local\Temp\BLTools v2.2.exe" | C:\Users\admin\AppData\Local\Temp\BLTools v2.2.exe | — | BLTools v2.2.exe |
User: admin Integrity Level: HIGH Exit code: 0 | ||||
| 1112 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\BLTools.system.vbs" | C:\Windows\System32\wscript.exe | — | BLTools v2.2.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 | ||||
| 1352 | "C:\Users\admin\AppData\Local\Temp\build.exe" | C:\Users\admin\AppData\Local\Temp\build.exe | — | BLTools v2.2.exe |
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 | ||||
| 1400 | "C:\Users\admin\AppData\Local\Temp\BLTools v2.2.exe" | C:\Users\admin\AppData\Local\Temp\BLTools v2.2.exe | — | BLTools v2.2.exe |
User: admin Integrity Level: HIGH Exit code: 0 | ||||
| 1620 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\BLTools.system.vbs" | C:\Windows\System32\wscript.exe | — | BLTools v2.2.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 | ||||
| 1704 | "C:\Users\admin\AppData\Local\Temp\BLTools v2.2.exe" | C:\Users\admin\AppData\Local\Temp\BLTools v2.2.exe | — | BLTools v2.2.exe |
User: admin Integrity Level: HIGH Exit code: 0 | ||||
Total events
664
Read events
664
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3340 | BLTools v2.2.exe | C:\Users\admin\AppData\Local\Temp\BLTools.system.vbs | text | |
MD5:— | SHA256:— | |||
| 3760 | wscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\BLTools.system.vbs | text | |
MD5:— | SHA256:— | |||
| 3340 | BLTools v2.2.exe | C:\Users\admin\AppData\Local\Temp\build.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
xiiiolympus.hopto.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.hopto .org |