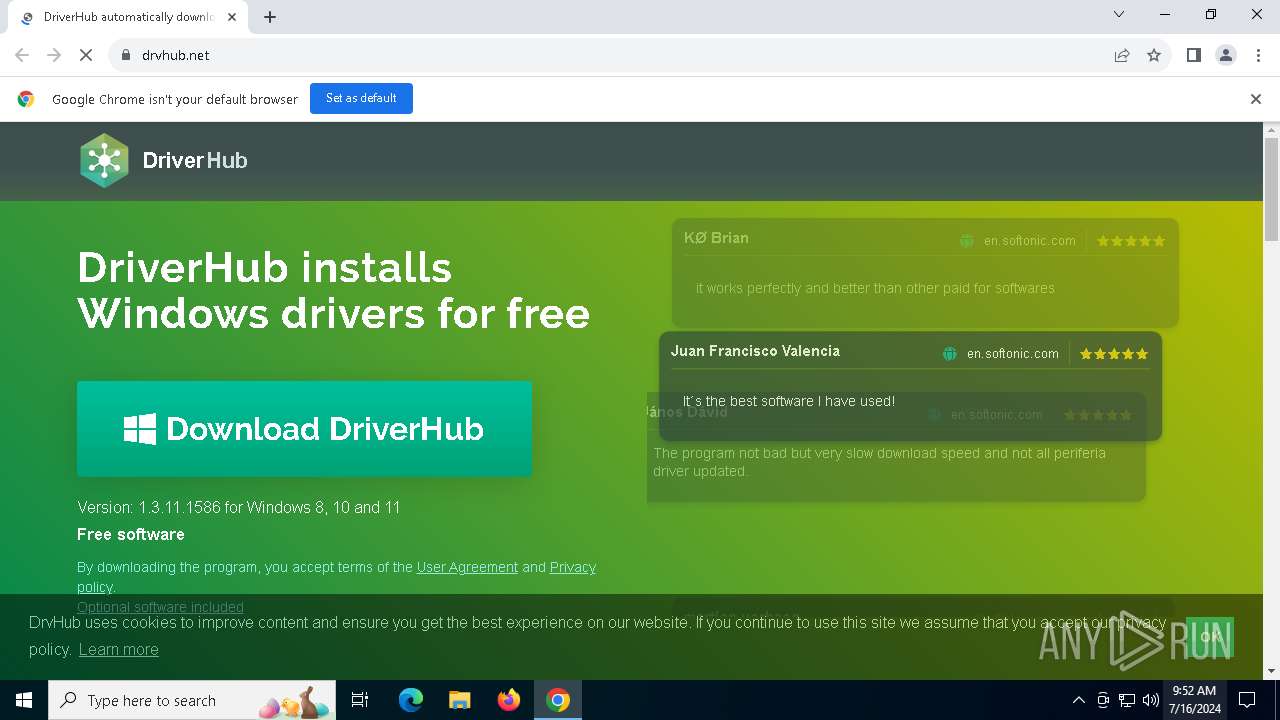
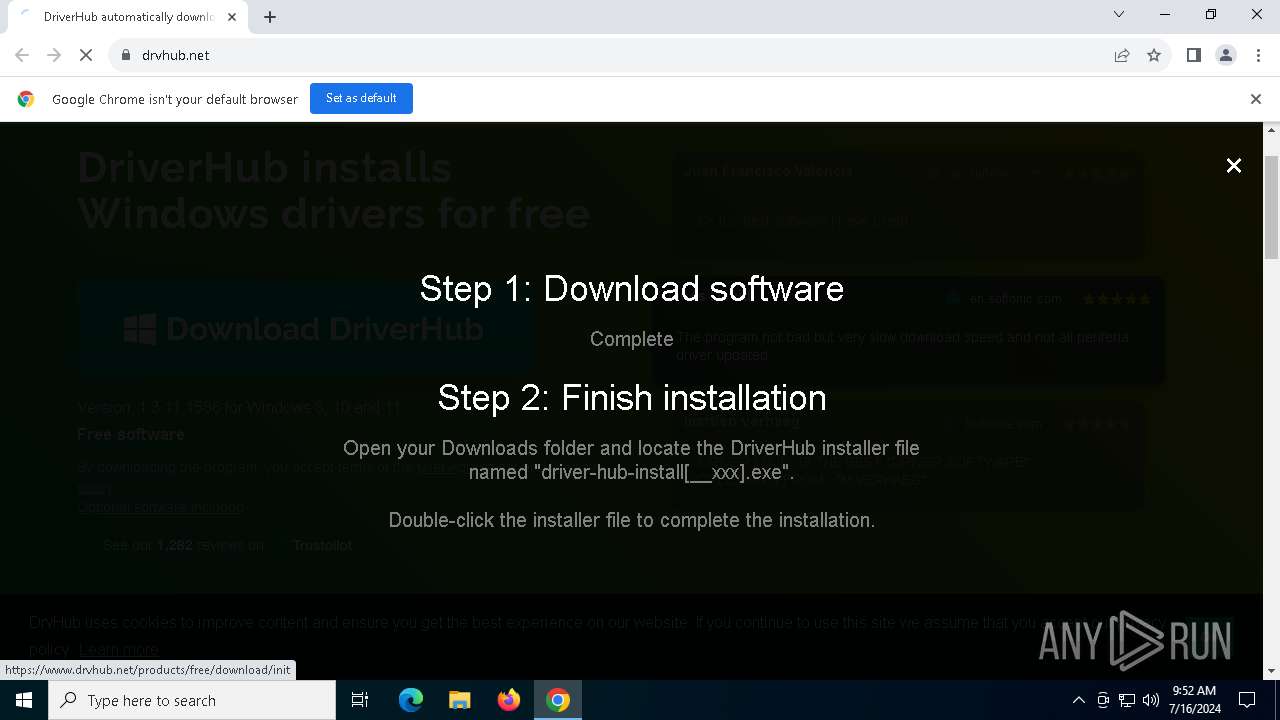
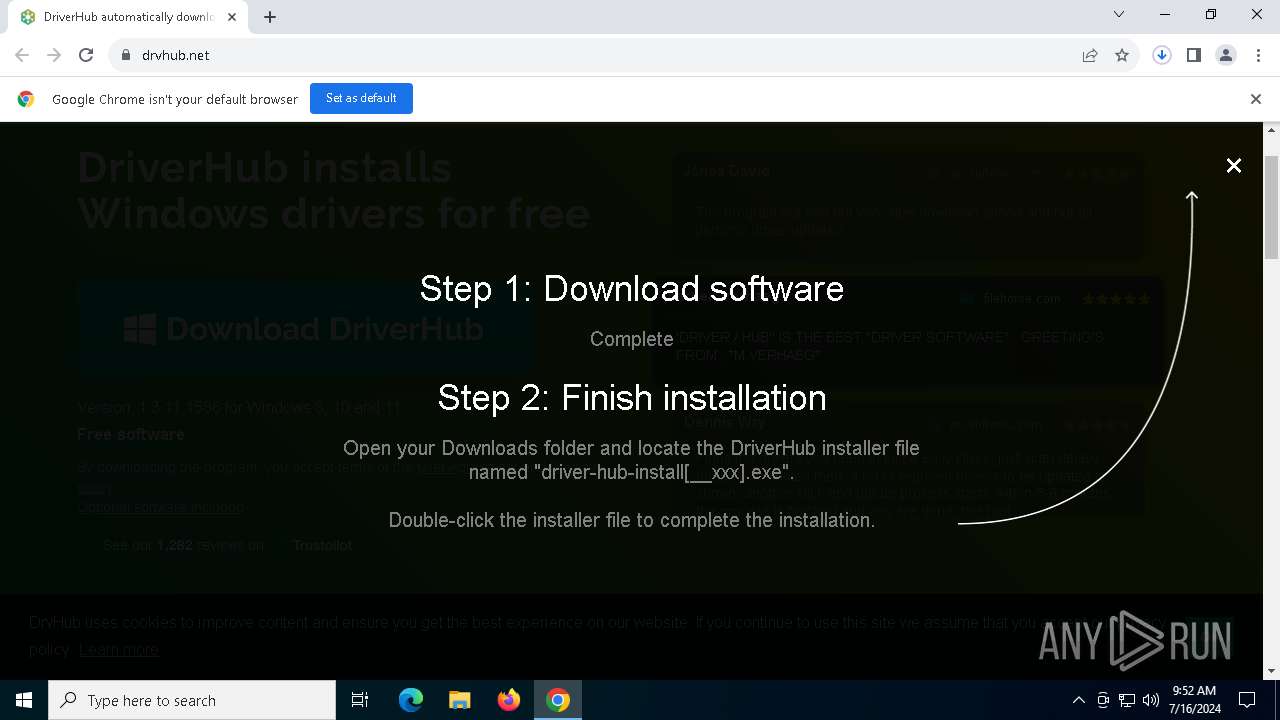
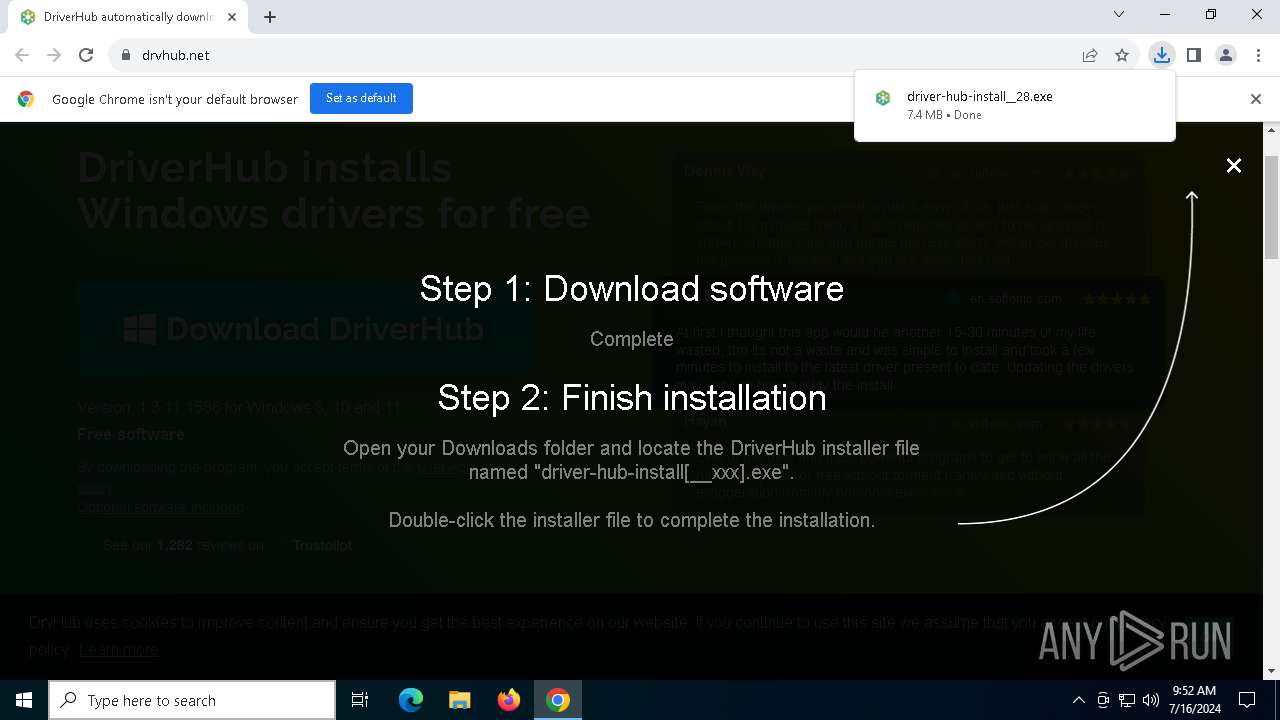
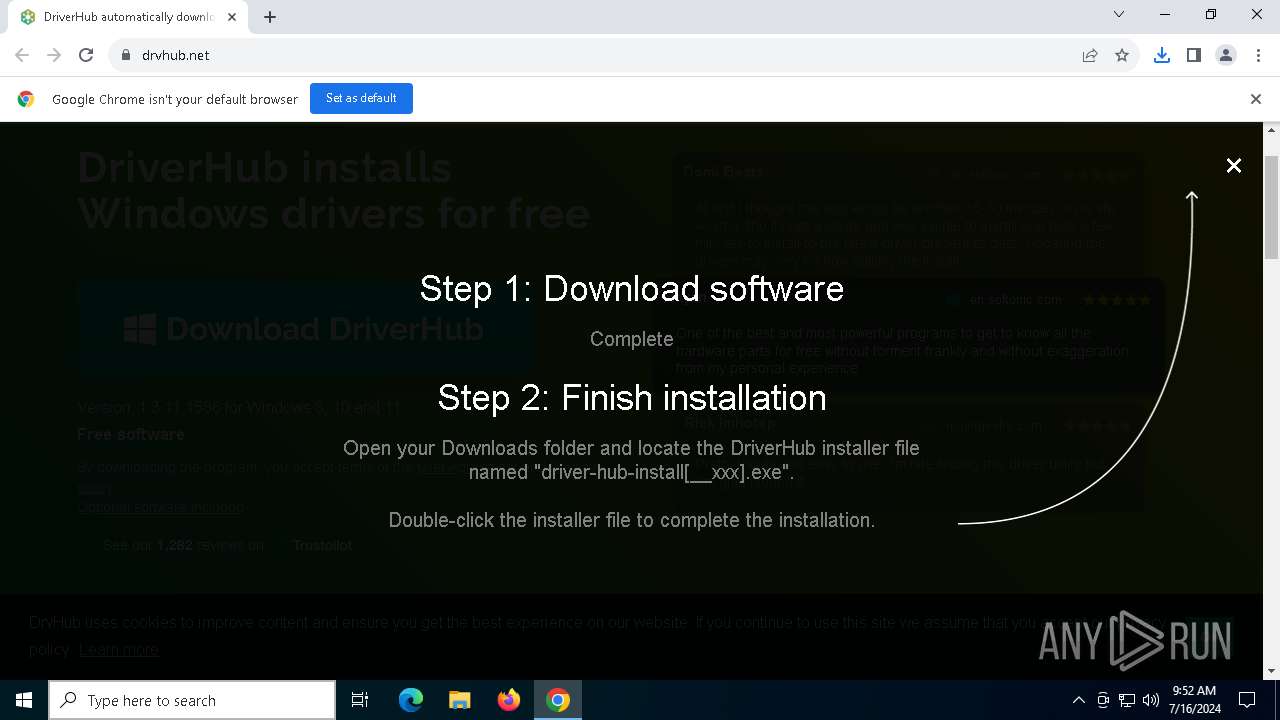
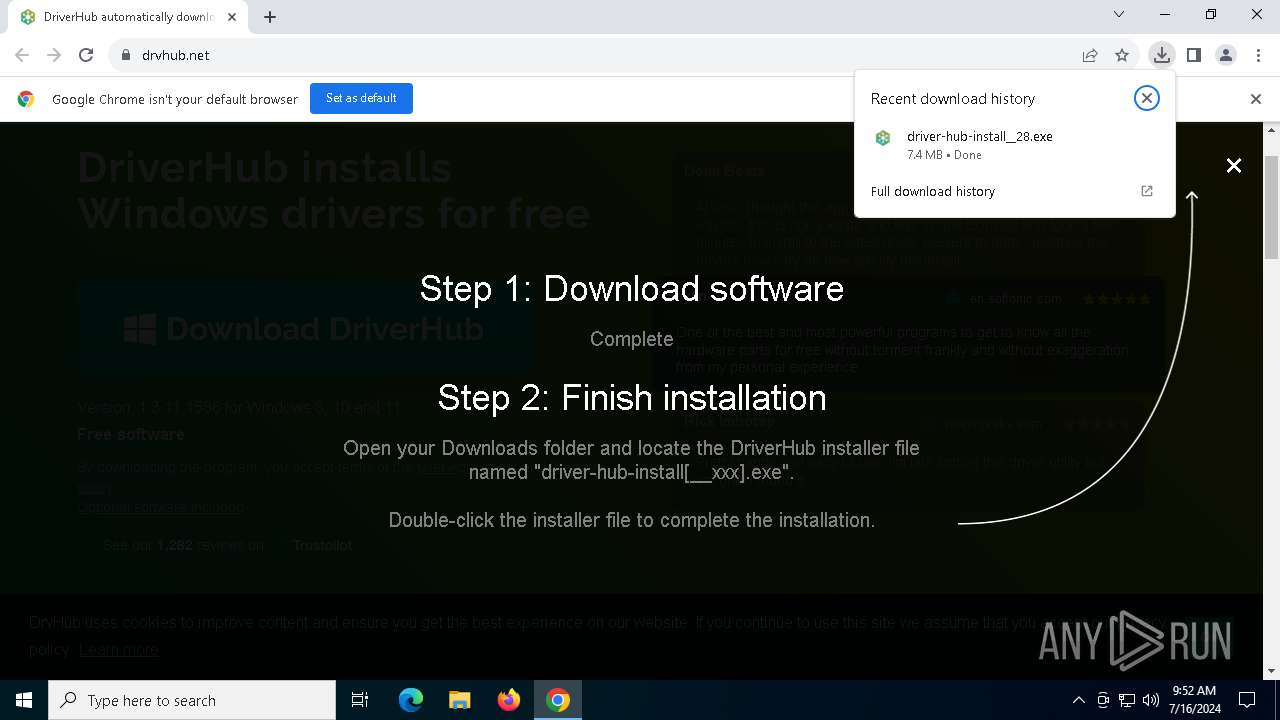
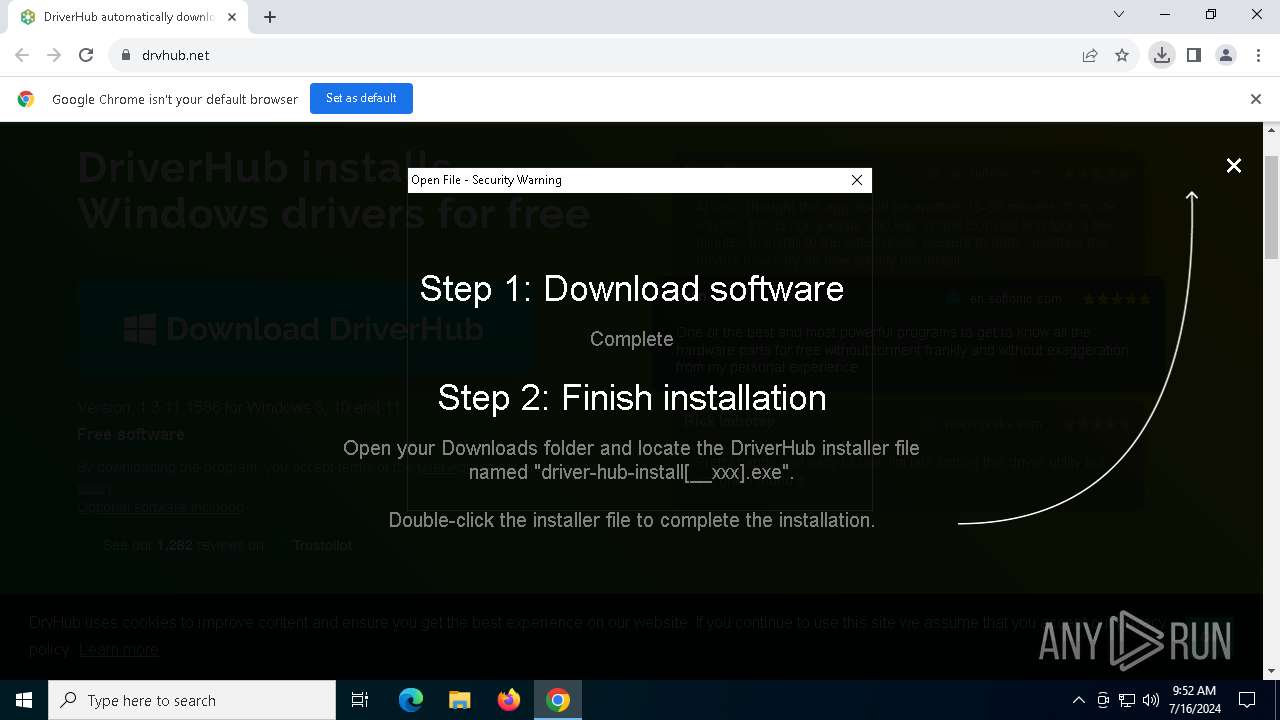
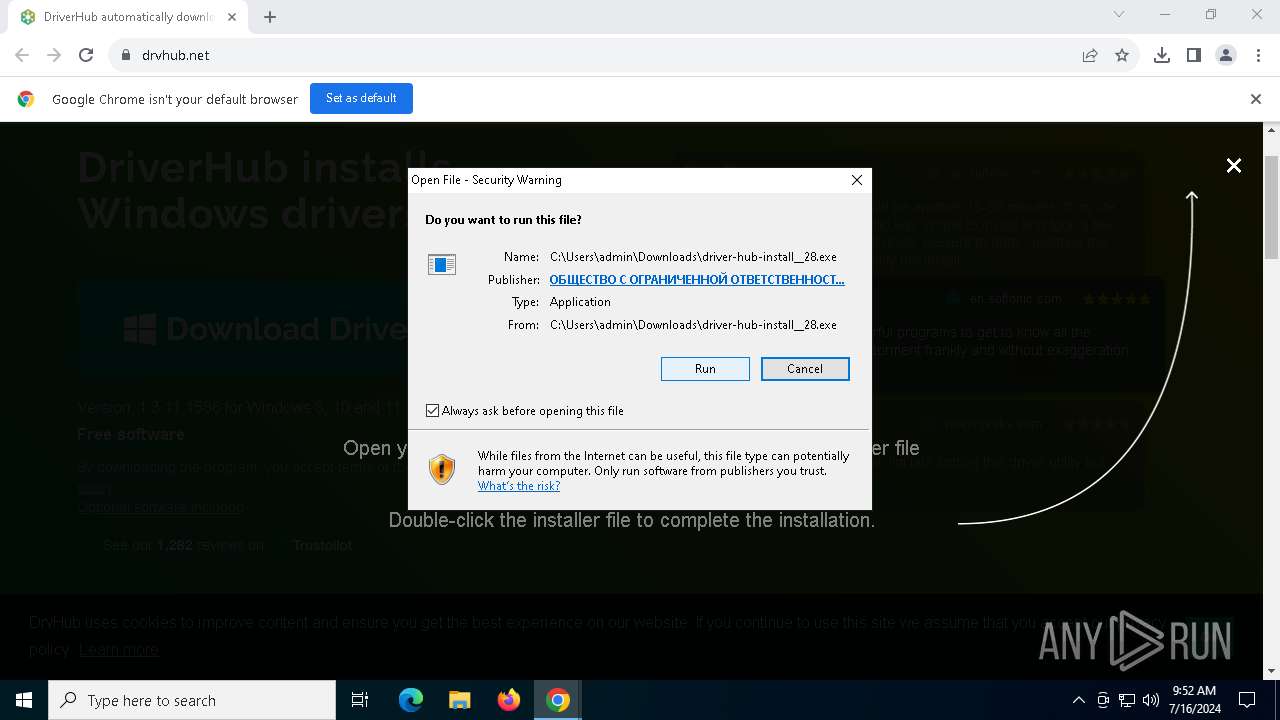
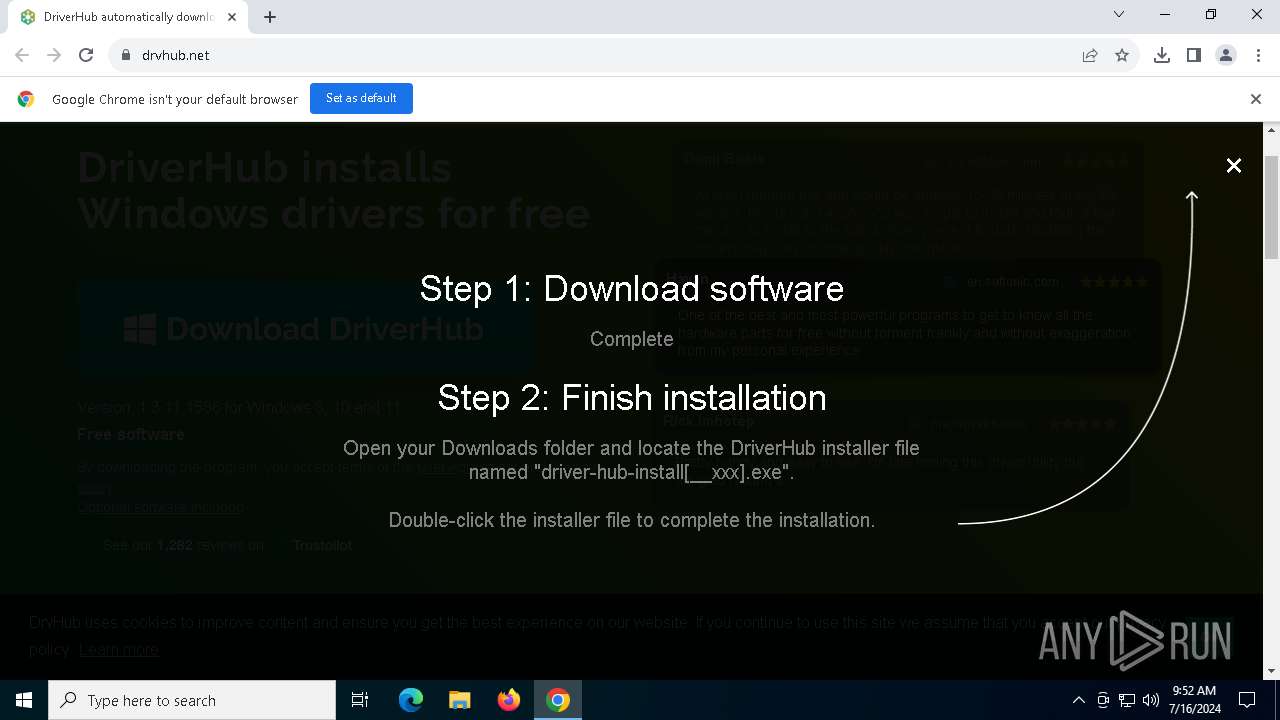
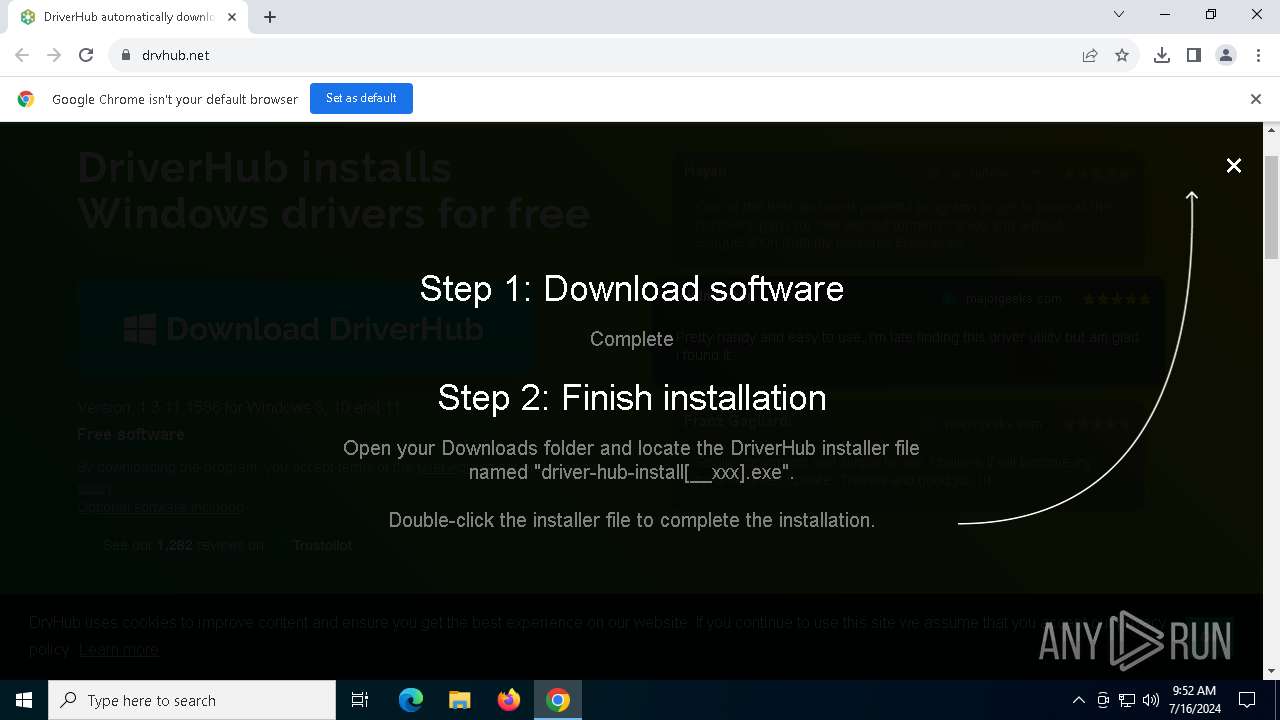
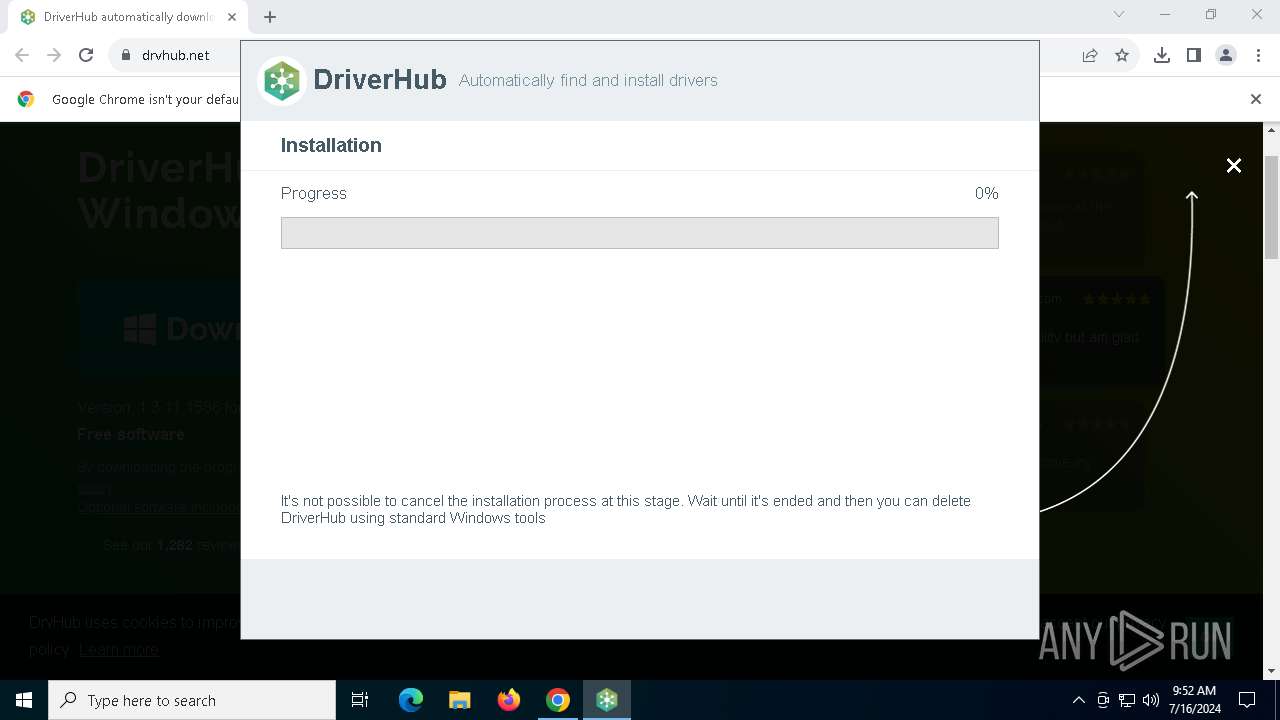
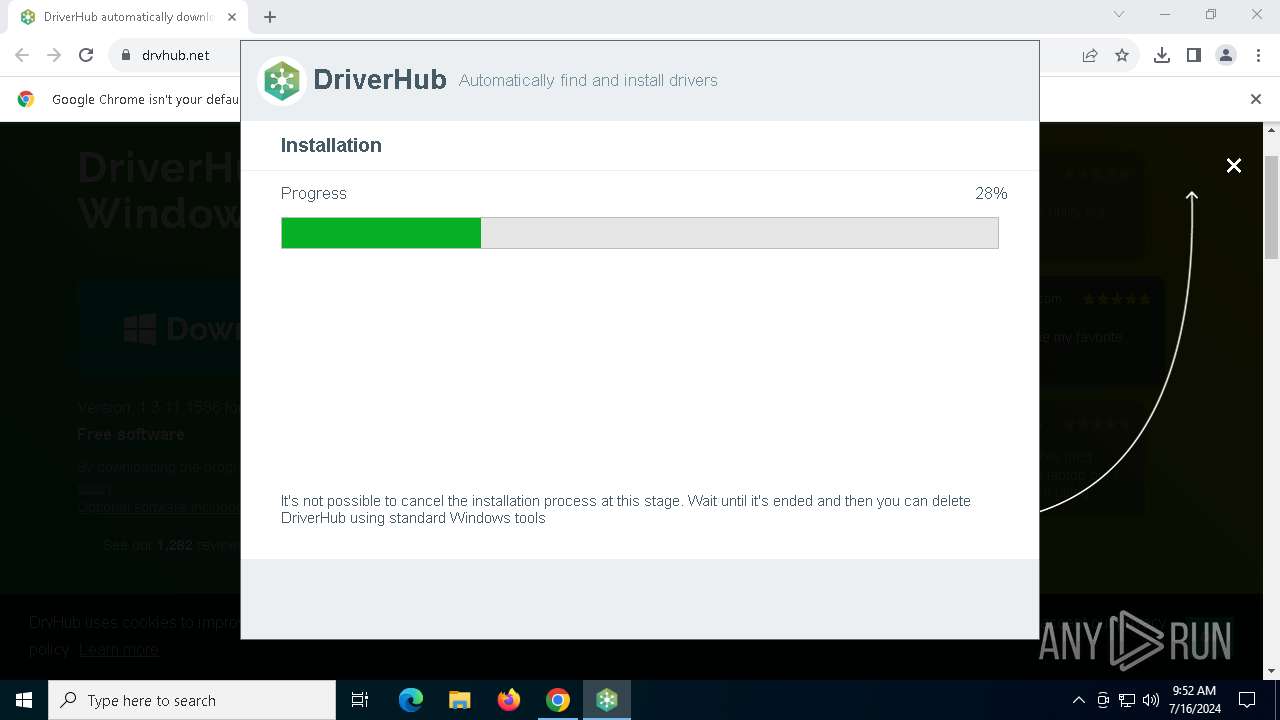
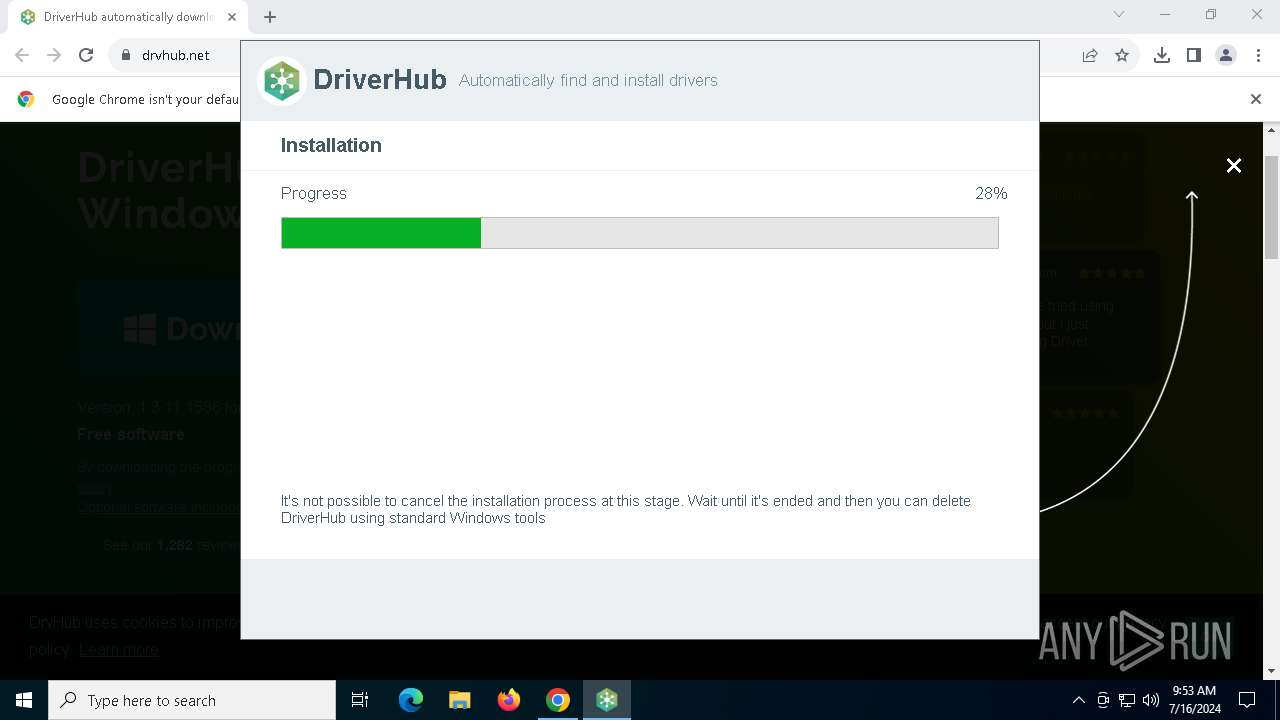
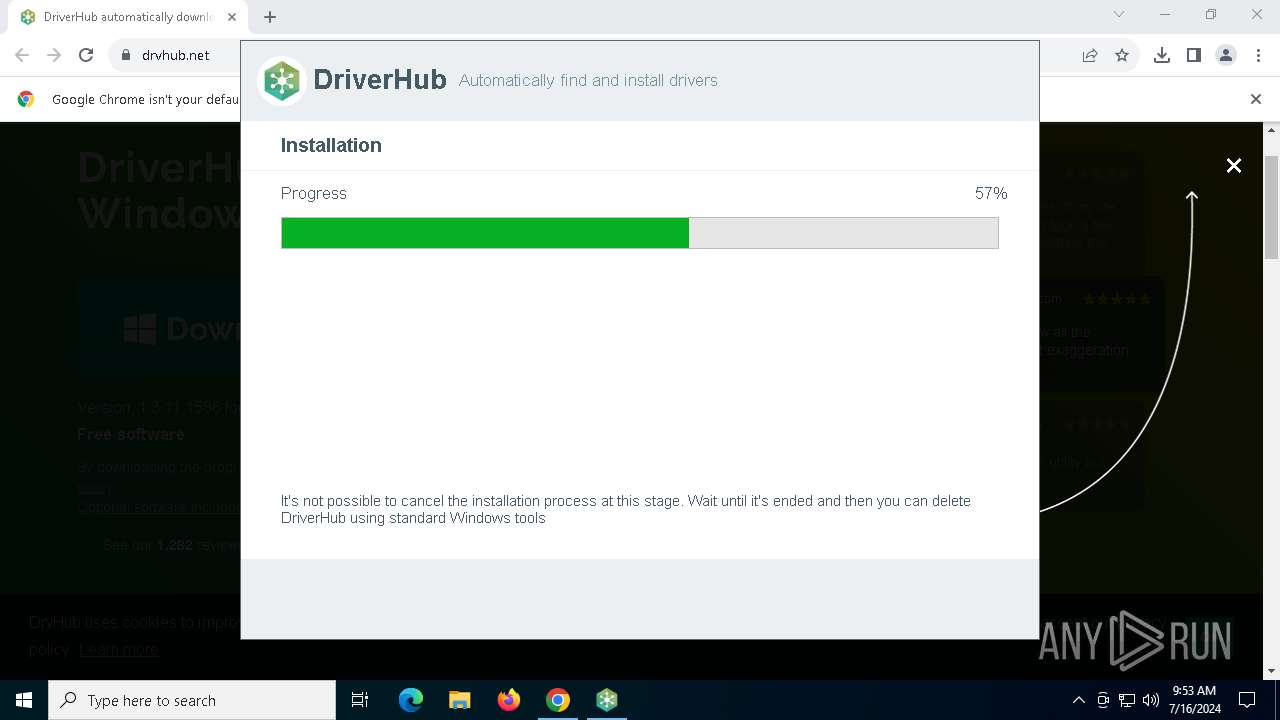
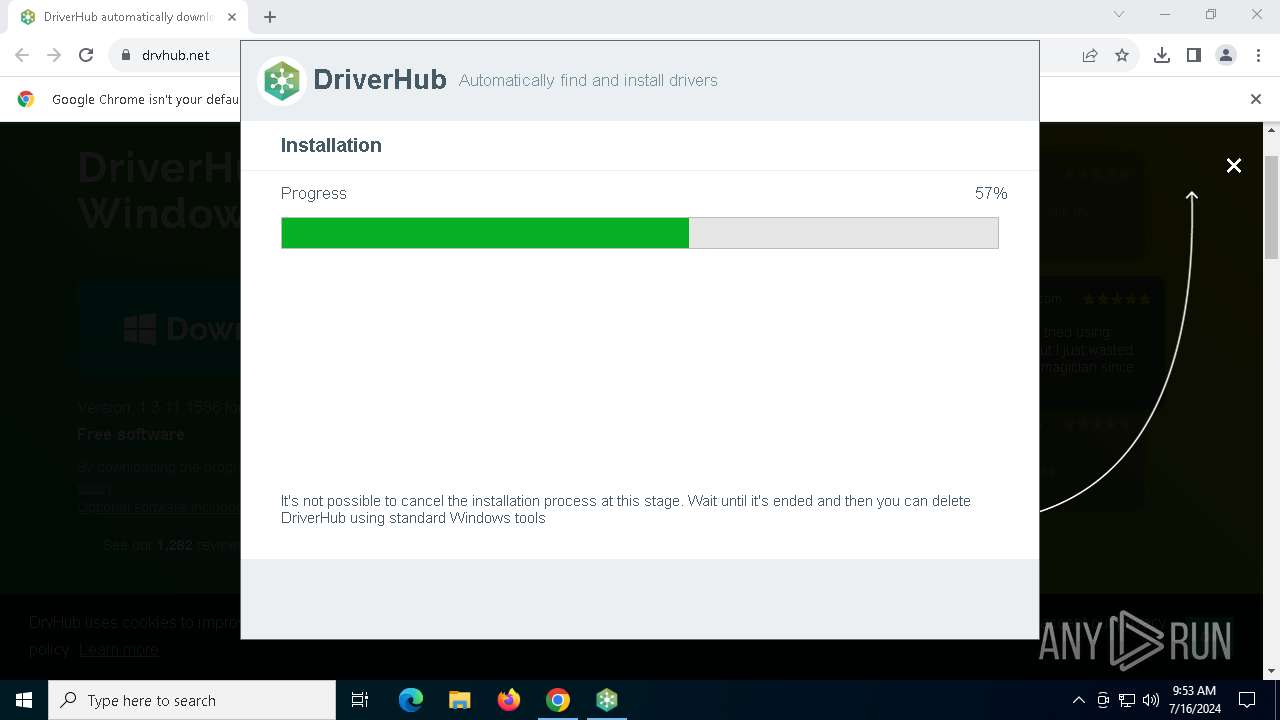
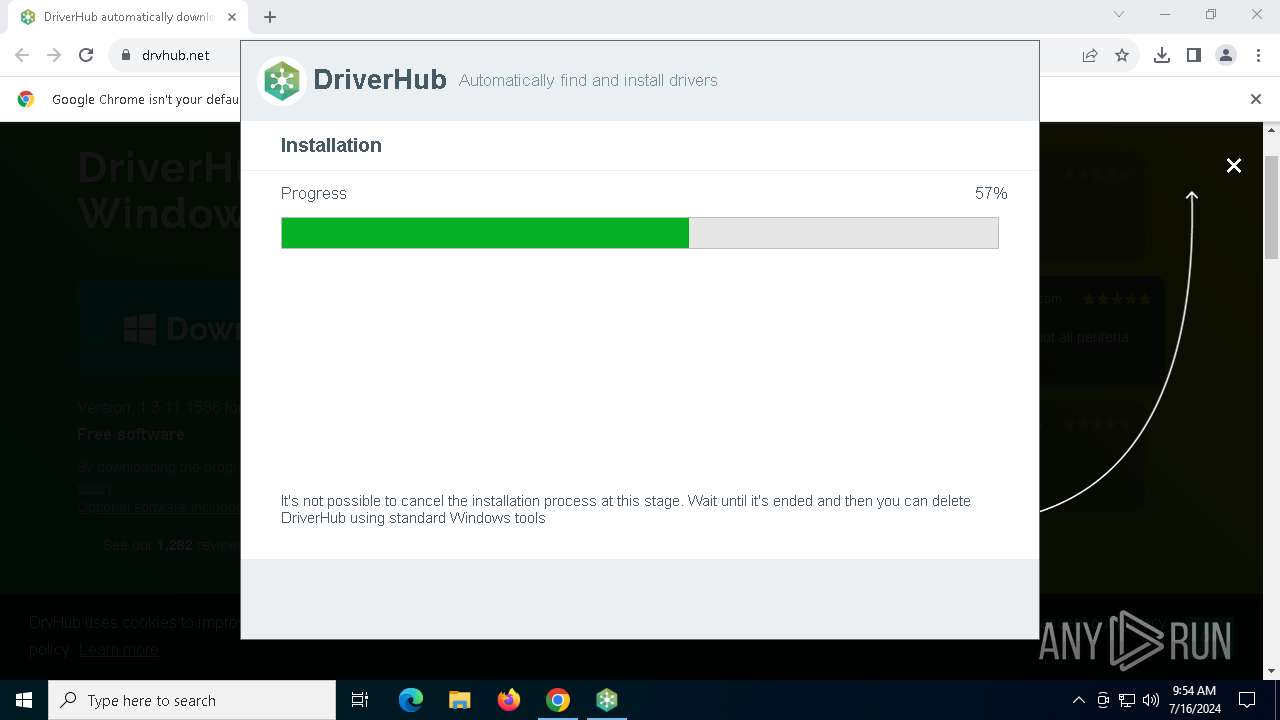
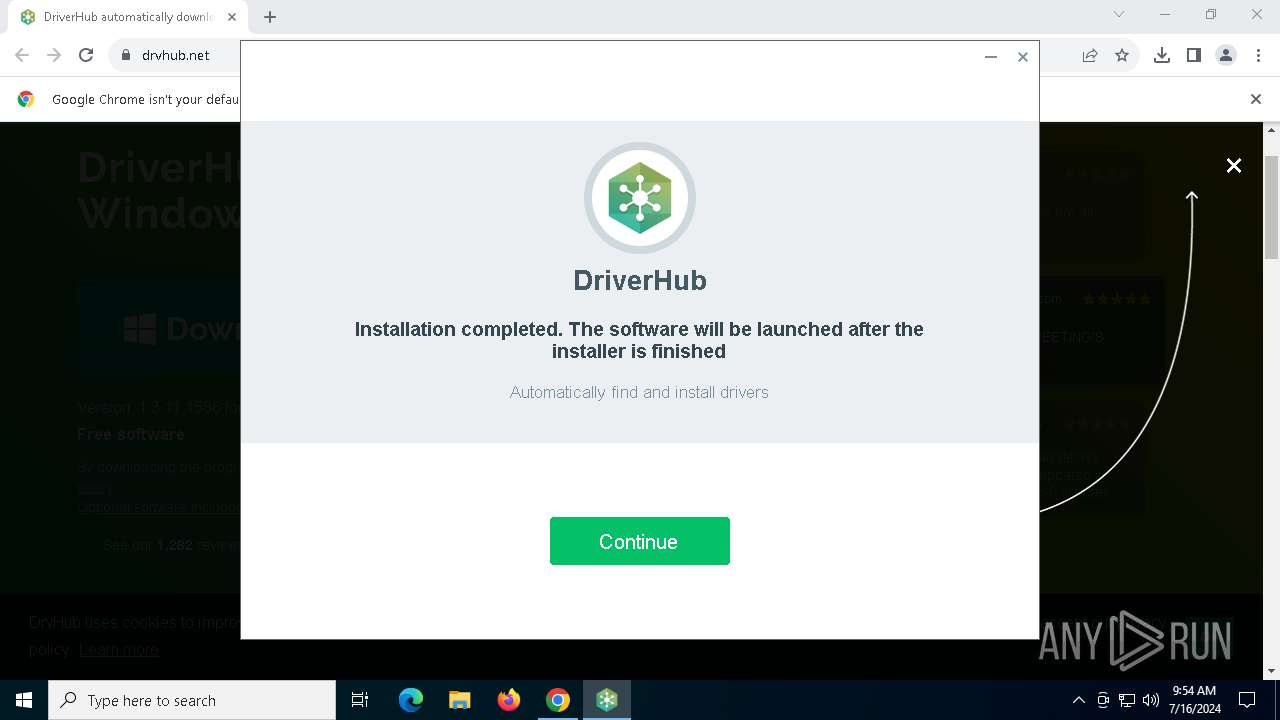
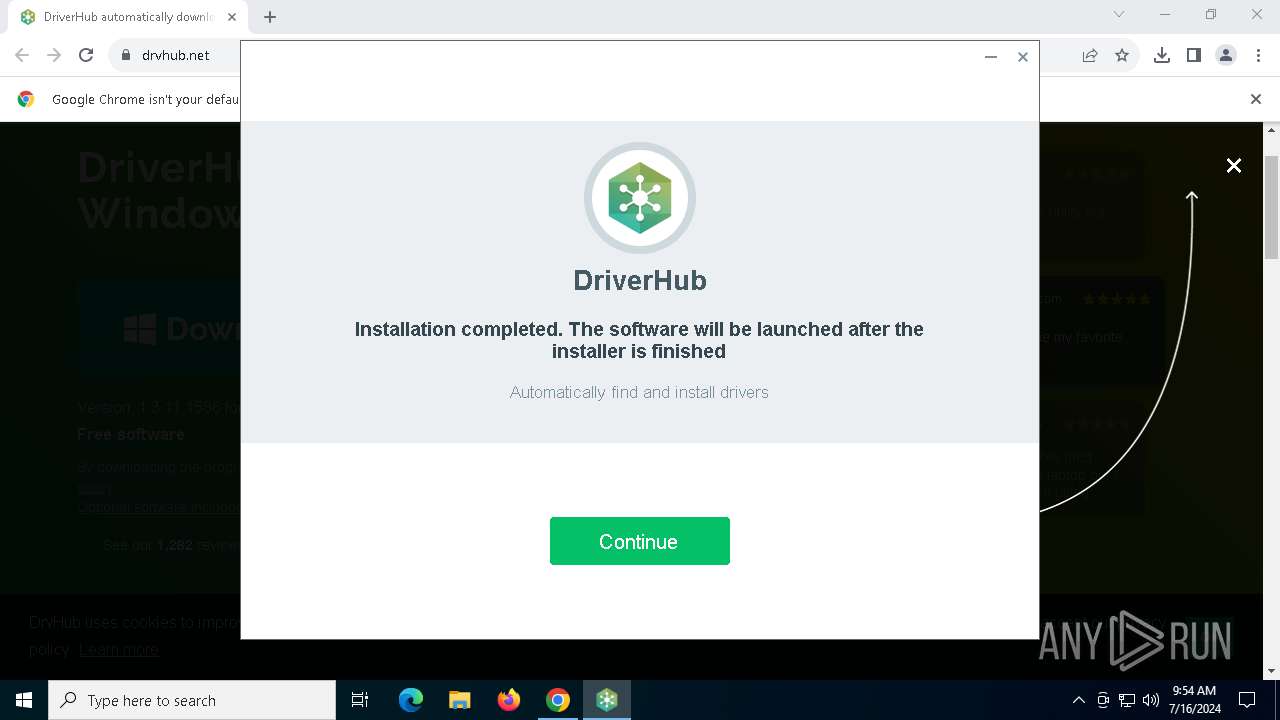
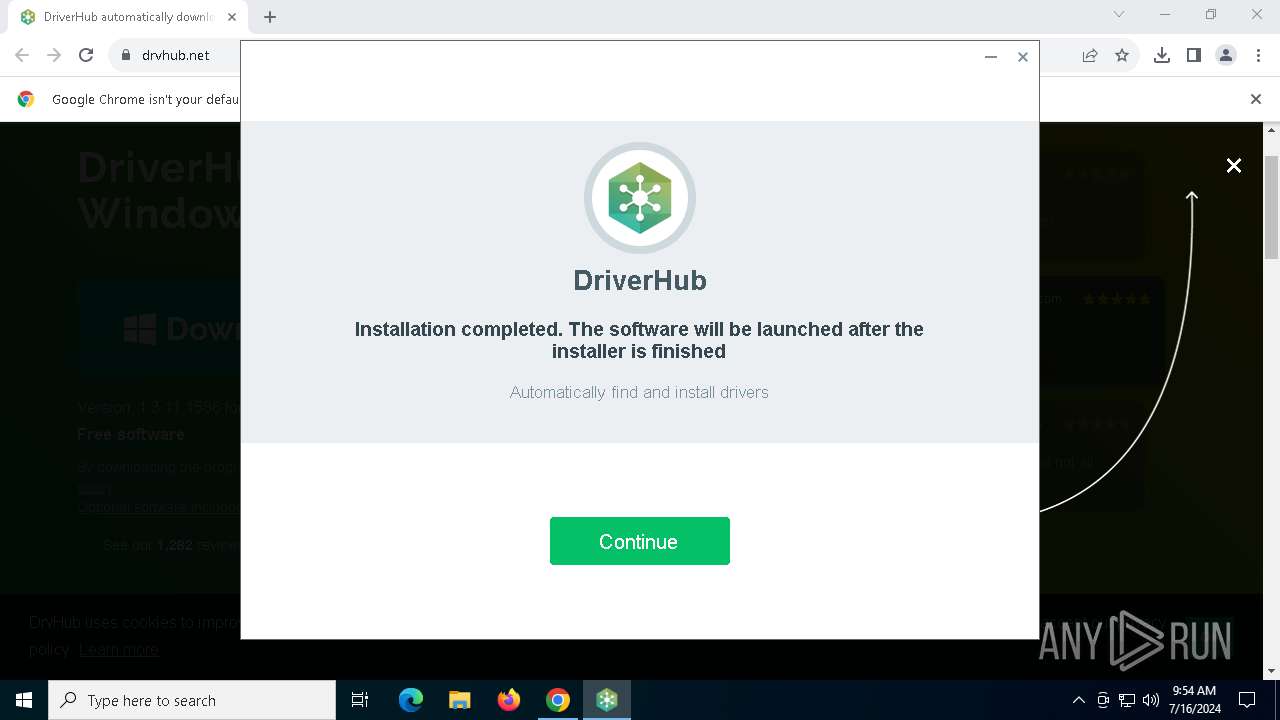
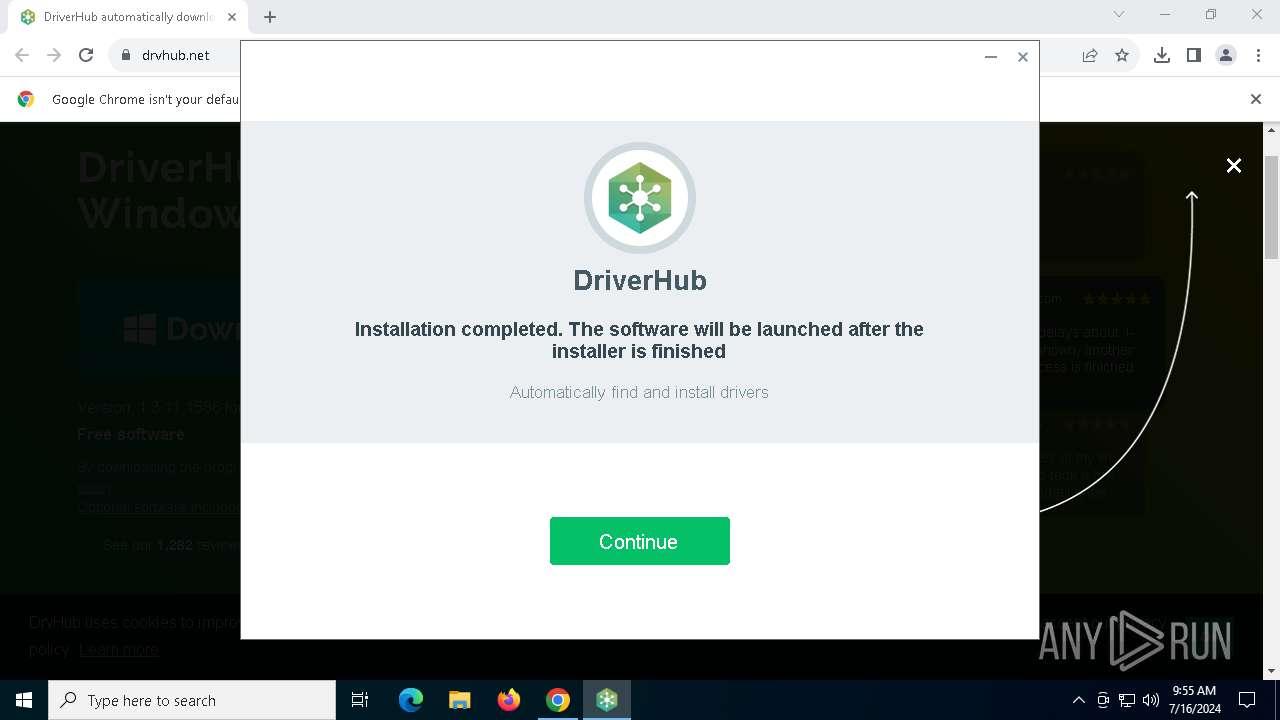
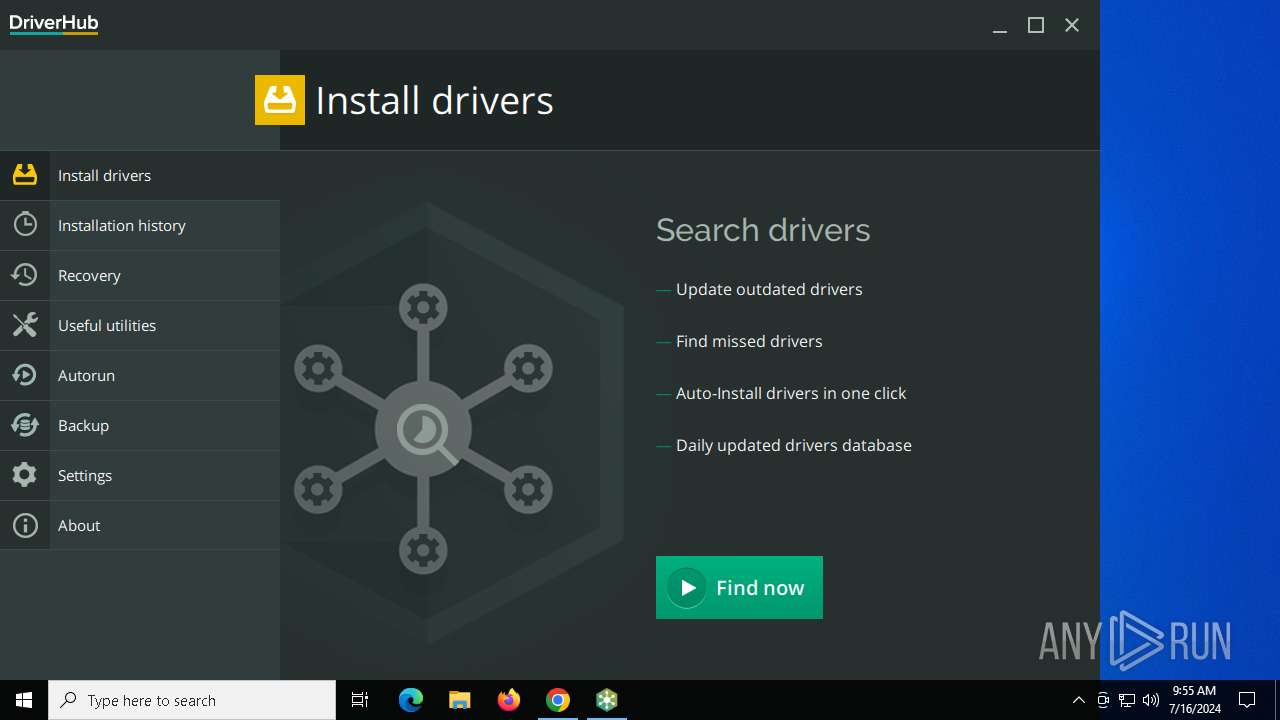
| URL: | http://www.drvhub.net |
| Full analysis: | https://app.any.run/tasks/489cadc4-f52c-4db9-9e0a-2c7a3b154a87 |
| Verdict: | Malicious activity |
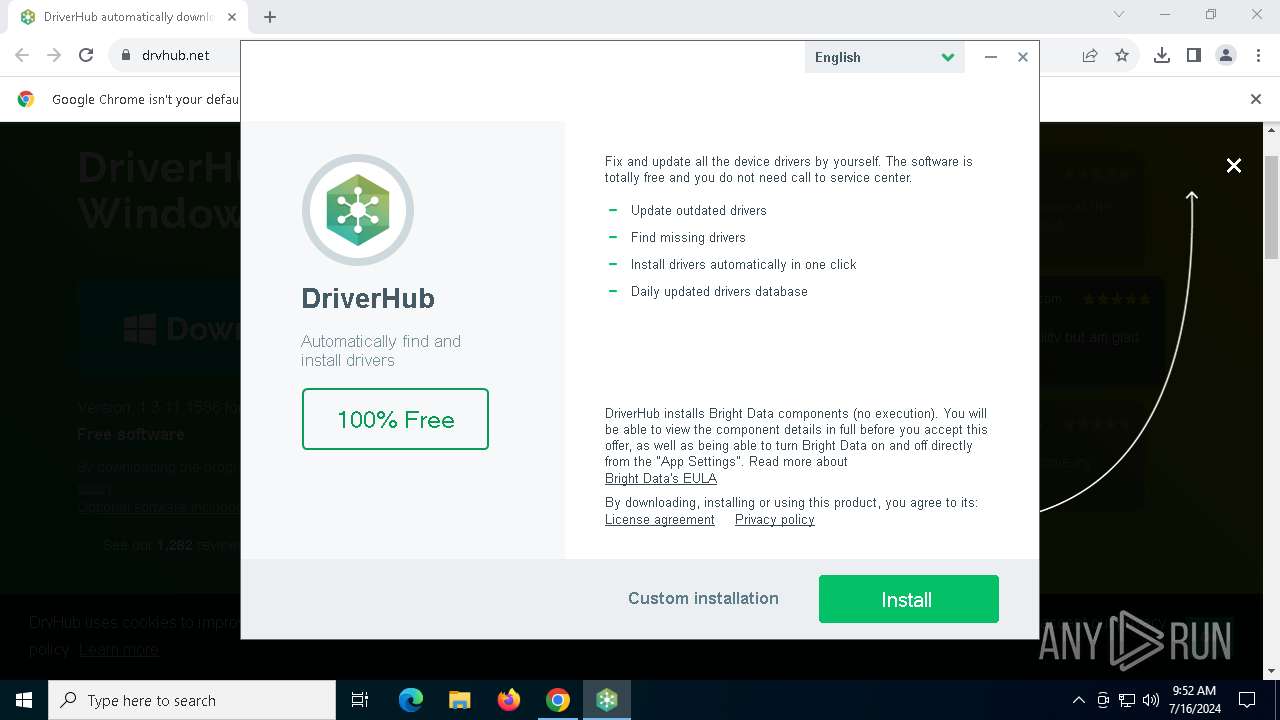
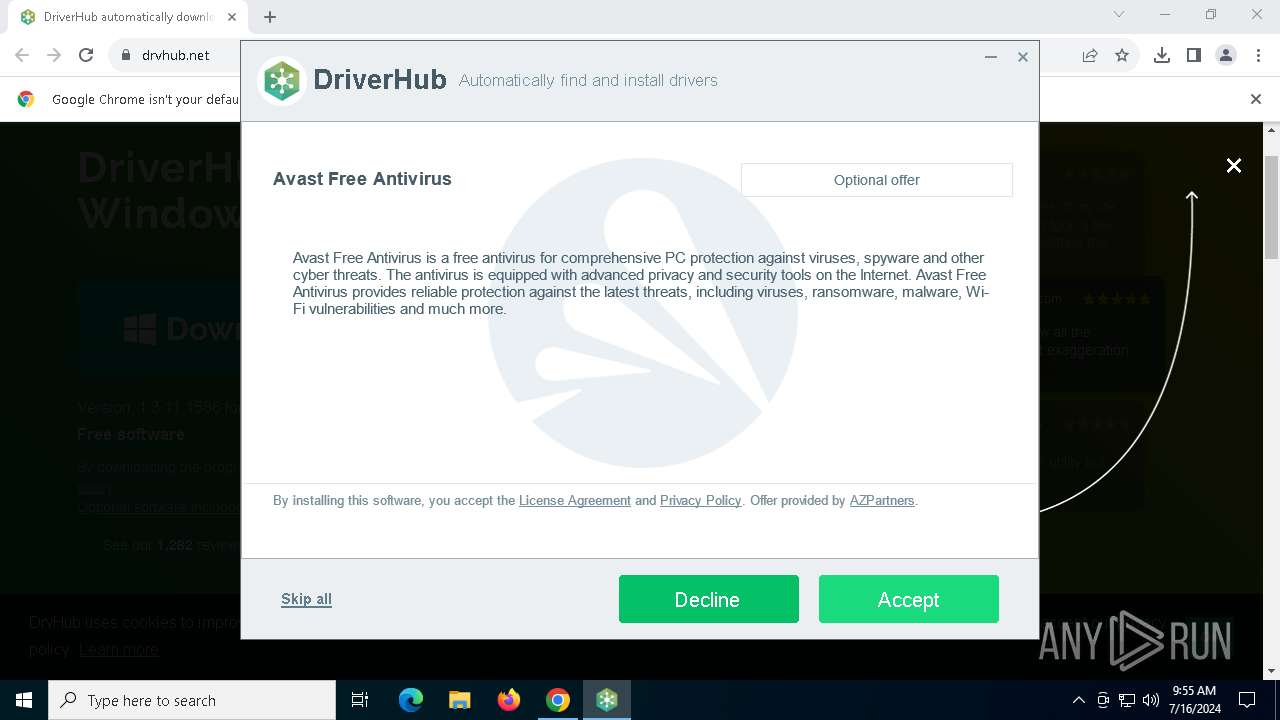
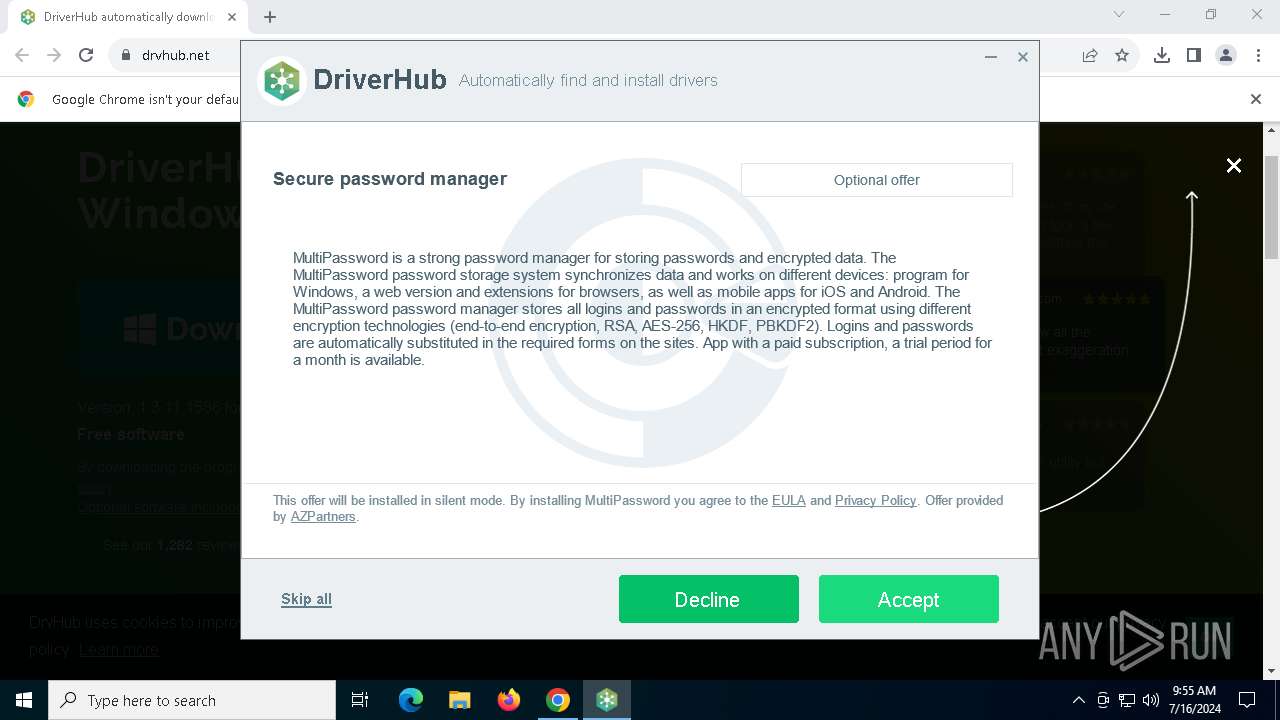
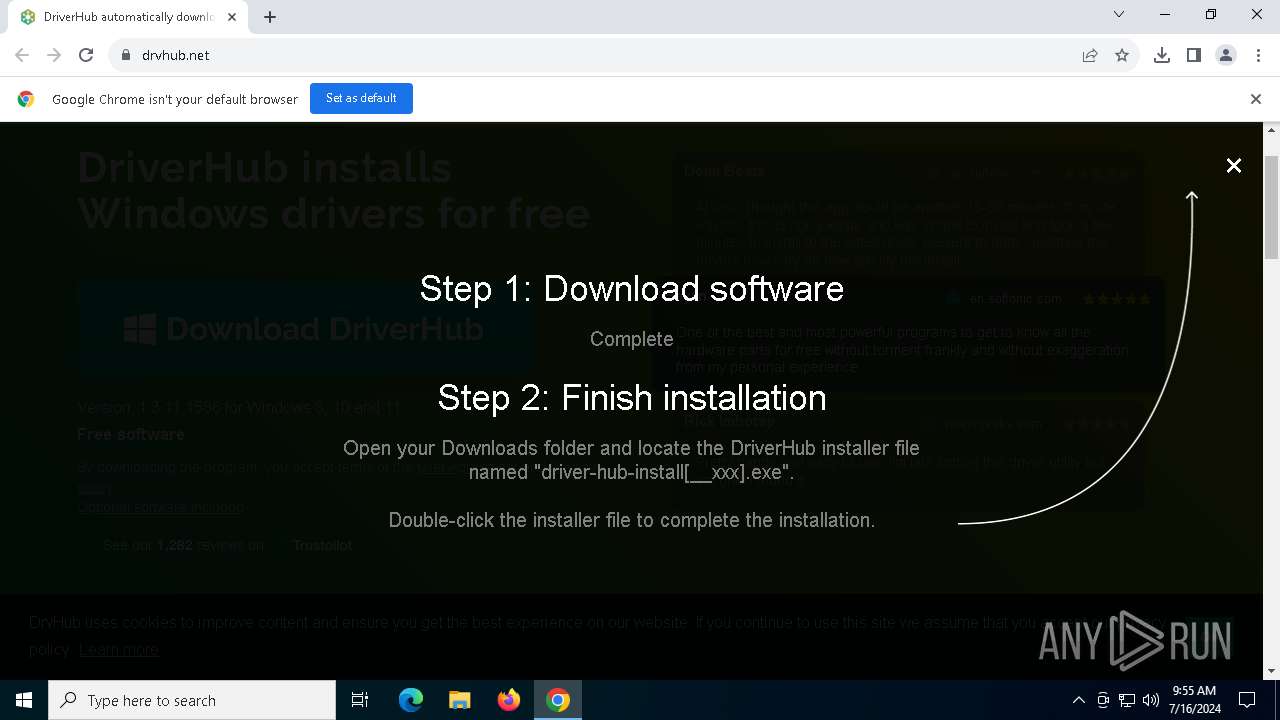
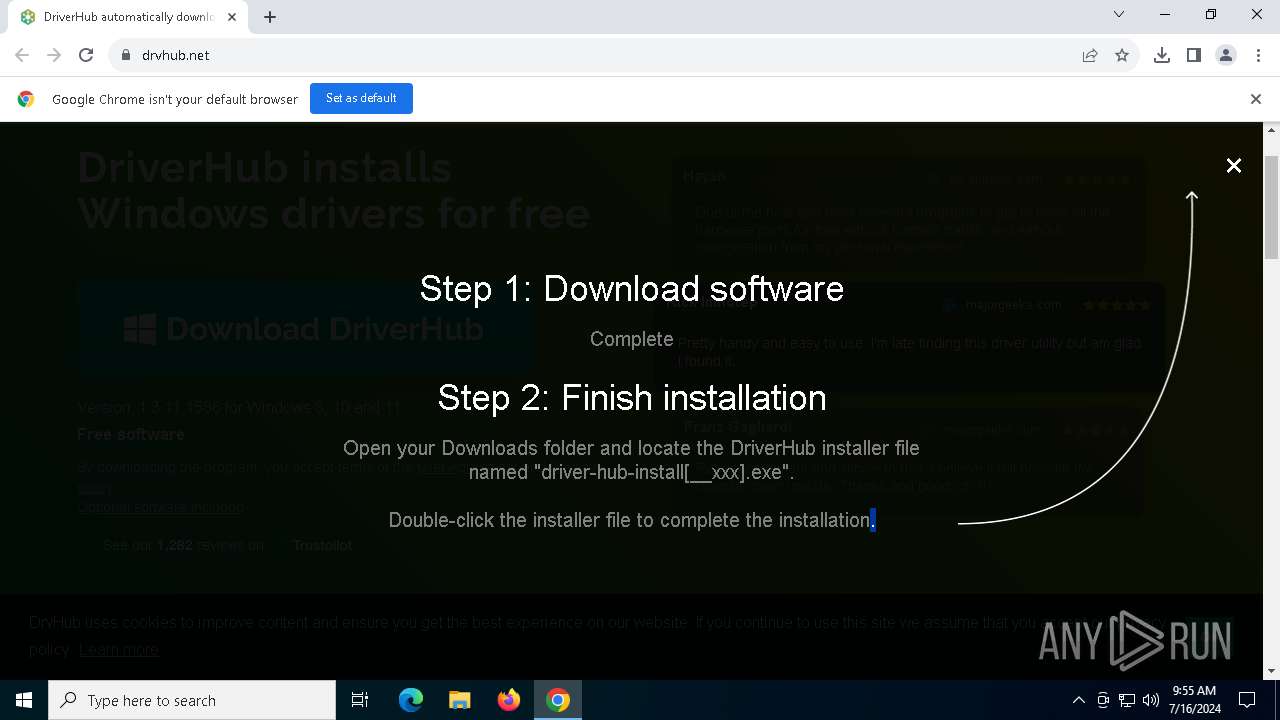
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | July 16, 2024, 09:52:20 |
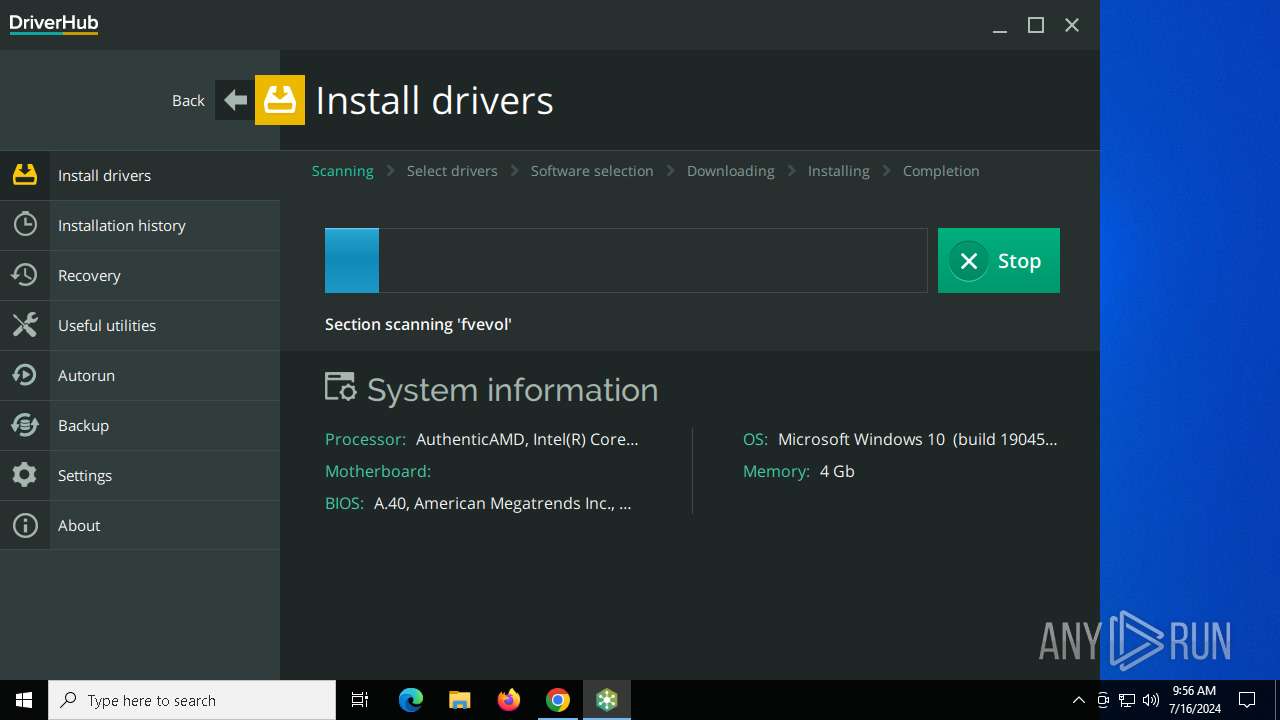
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FDB2976CD631550AF4F234FD3616FA86 |
| SHA1: | B35BB4E1638341E32A50B1F141B7E01986A38025 |
| SHA256: | 34F50FFCBDB90C997DFB669221F91C50C5A1D89C49125E0D2C2C718B4E331D80 |
| SSDEEP: | 3:N1KJS4FCoR:Cc4FCoR |
MALICIOUS
Drops the executable file immediately after the start
- driver-hub-install__28.exe (PID: 7576)
- VC_redist.x86.exe (PID: 4796)
- VC_redist.x86.exe (PID: 6396)
- VC_redist.x86.exe (PID: 7260)
- VC_redist.x86.exe (PID: 1832)
- msiexec.exe (PID: 2784)
- VC_redist.x86.exe (PID: 6796)
- DriverHub.exe (PID: 3948)
- setup.exe (PID: 2632)
- setup.exe (PID: 7292)
- setup.exe (PID: 1140)
- setup.exe (PID: 6356)
- setup.exe (PID: 6796)
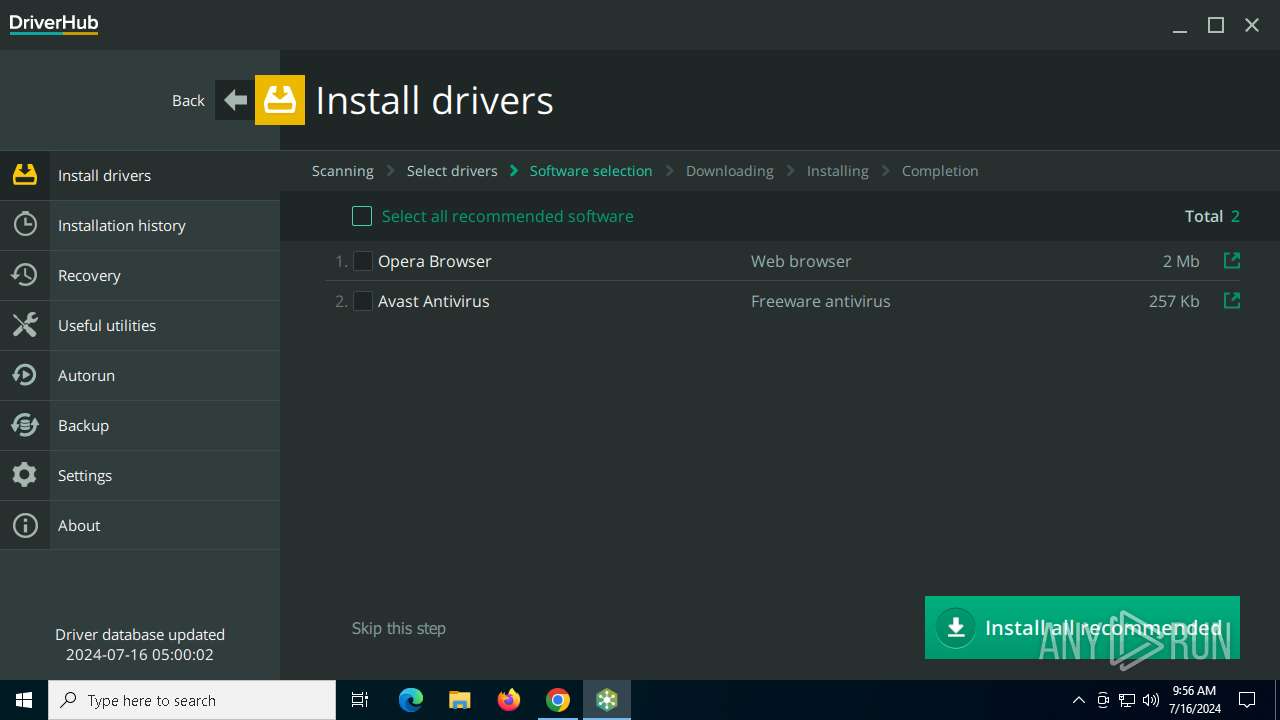
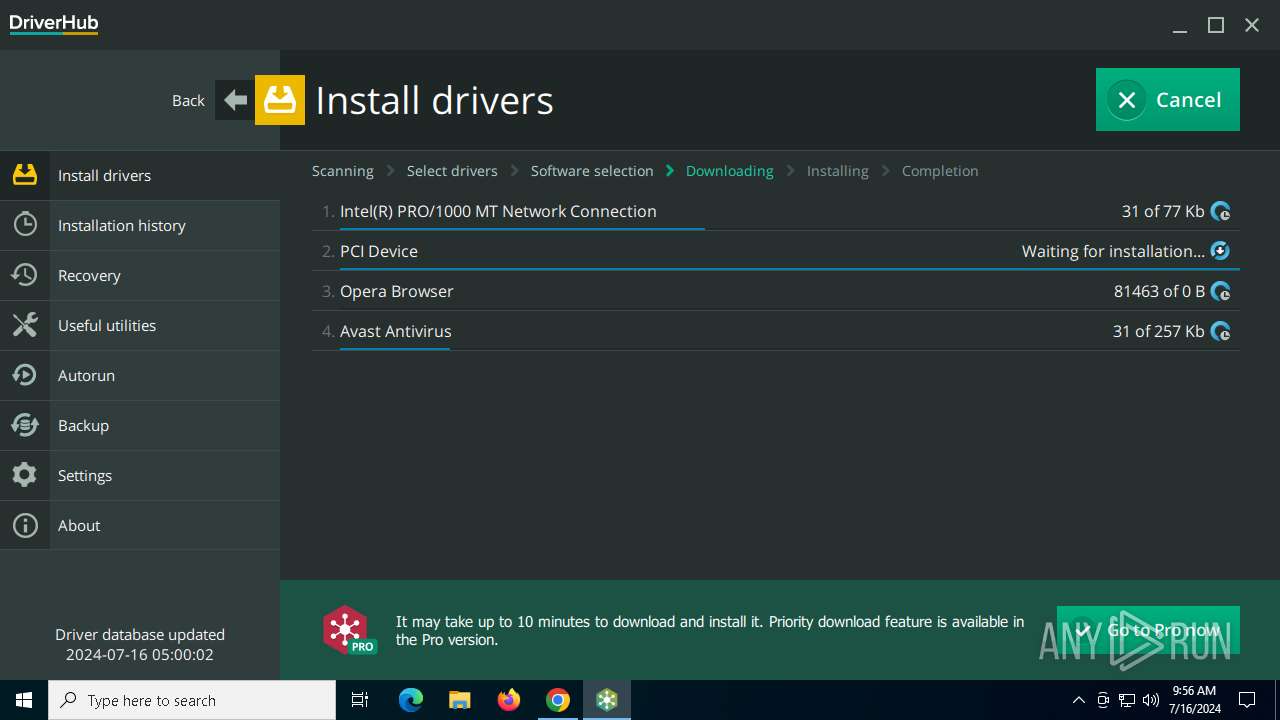
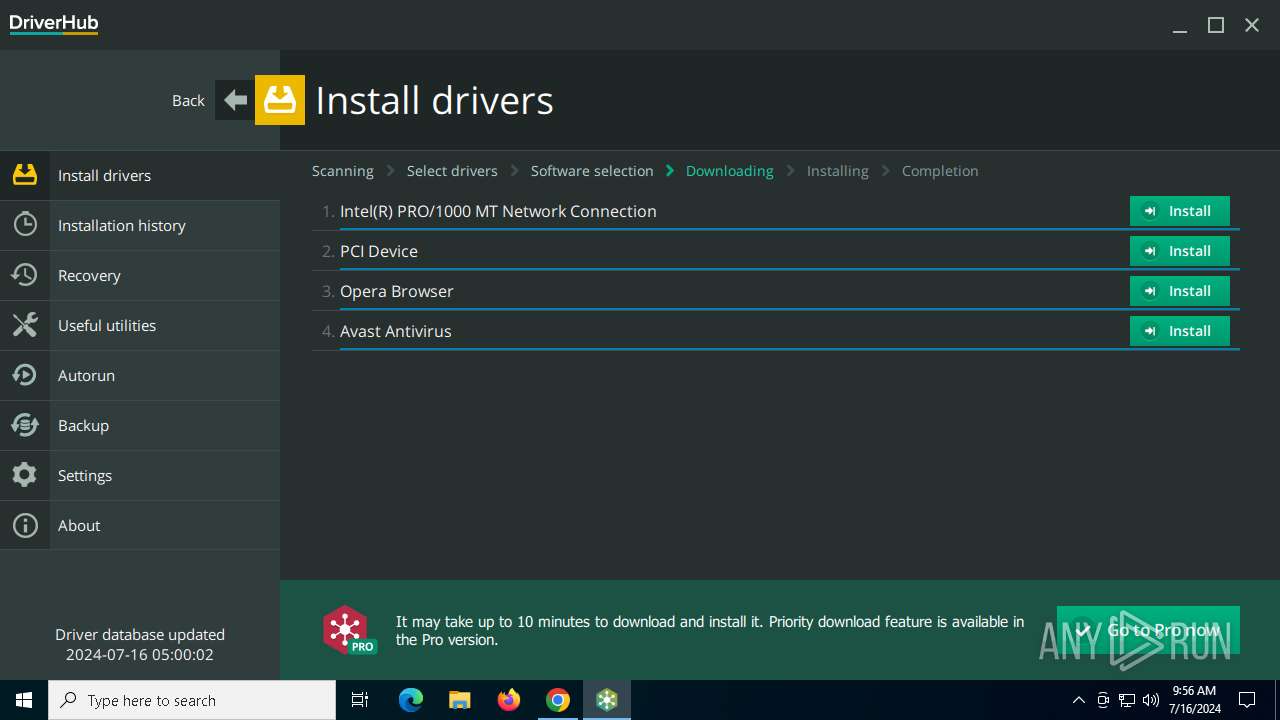
- AvastDownloader.exe (PID: 1292)
- avast_free_antivirus_setup_online_x64.exe (PID: 7152)
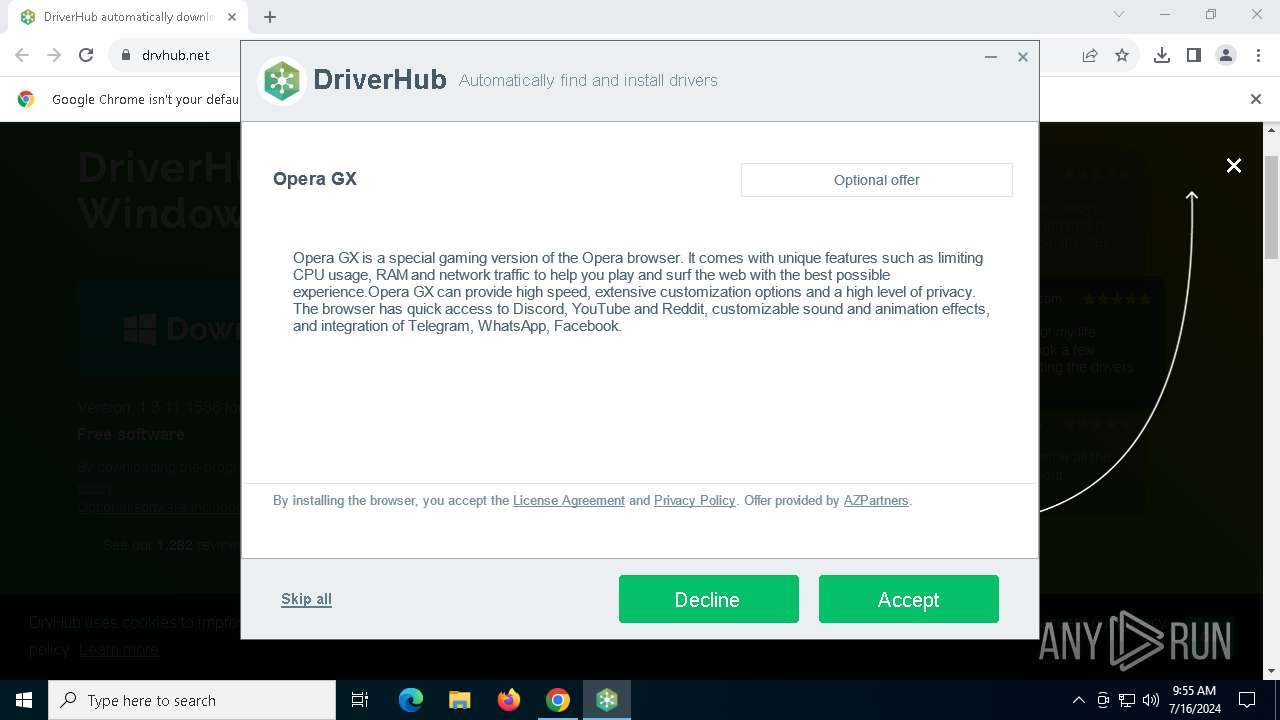
- OperaGXDownloader.exe (PID: 2056)
- Instup.exe (PID: 4308)
- net_updater32.exe (PID: 3992)
Changes the autorun value in the registry
- VC_redist.x86.exe (PID: 7260)
- instup.exe (PID: 2008)
Creates a writable file in the system directory
- msiexec.exe (PID: 2784)
- net_updater32.exe (PID: 3992)
Scans artifacts that could help determine the target
- driver-hub-install__28.exe (PID: 7576)
SUSPICIOUS
Reads security settings of Internet Explorer
- driver-hub-install__28.exe (PID: 7440)
- driver-hub-install__28.exe (PID: 7576)
- VC_redist.x86.exe (PID: 6396)
- VC_redist.x86.exe (PID: 1832)
- setup.exe (PID: 7292)
- DriverHub.exe (PID: 3948)
Reads the date of Windows installation
- driver-hub-install__28.exe (PID: 7440)
- driver-hub-install__28.exe (PID: 7576)
- VC_redist.x86.exe (PID: 6396)
- VC_redist.x86.exe (PID: 1832)
- DriverHub.exe (PID: 3948)
Reads Microsoft Outlook installation path
- driver-hub-install__28.exe (PID: 7440)
- driver-hub-install__28.exe (PID: 7576)
Application launched itself
- driver-hub-install__28.exe (PID: 7440)
- VC_redist.x86.exe (PID: 8016)
- VC_redist.x86.exe (PID: 1832)
- setup.exe (PID: 7292)
- setup.exe (PID: 6356)
Reads Internet Explorer settings
- driver-hub-install__28.exe (PID: 7440)
- driver-hub-install__28.exe (PID: 7576)
Executable content was dropped or overwritten
- driver-hub-install__28.exe (PID: 7576)
- VC_redist.x86.exe (PID: 4796)
- VC_redist.x86.exe (PID: 6396)
- VC_redist.x86.exe (PID: 7260)
- VC_redist.x86.exe (PID: 1832)
- VC_redist.x86.exe (PID: 6796)
- OperaGXDownloader.exe (PID: 2056)
- setup.exe (PID: 7292)
- DriverHub.exe (PID: 3948)
- setup.exe (PID: 2632)
- setup.exe (PID: 1140)
- setup.exe (PID: 6356)
- setup.exe (PID: 6796)
- AvastDownloader.exe (PID: 1292)
- avast_free_antivirus_setup_online_x64.exe (PID: 7152)
- Instup.exe (PID: 4308)
- net_updater32.exe (PID: 3992)
Starts a Microsoft application from unusual location
- VC_redist.x86.exe (PID: 4796)
- VC_redist.x86.exe (PID: 7260)
- VC_redist.x86.exe (PID: 6396)
Process drops legitimate windows executable
- driver-hub-install__28.exe (PID: 7576)
- VC_redist.x86.exe (PID: 4796)
- VC_redist.x86.exe (PID: 6396)
- VC_redist.x86.exe (PID: 7260)
- msiexec.exe (PID: 2784)
- VC_redist.x86.exe (PID: 6796)
- DriverHub.exe (PID: 3948)
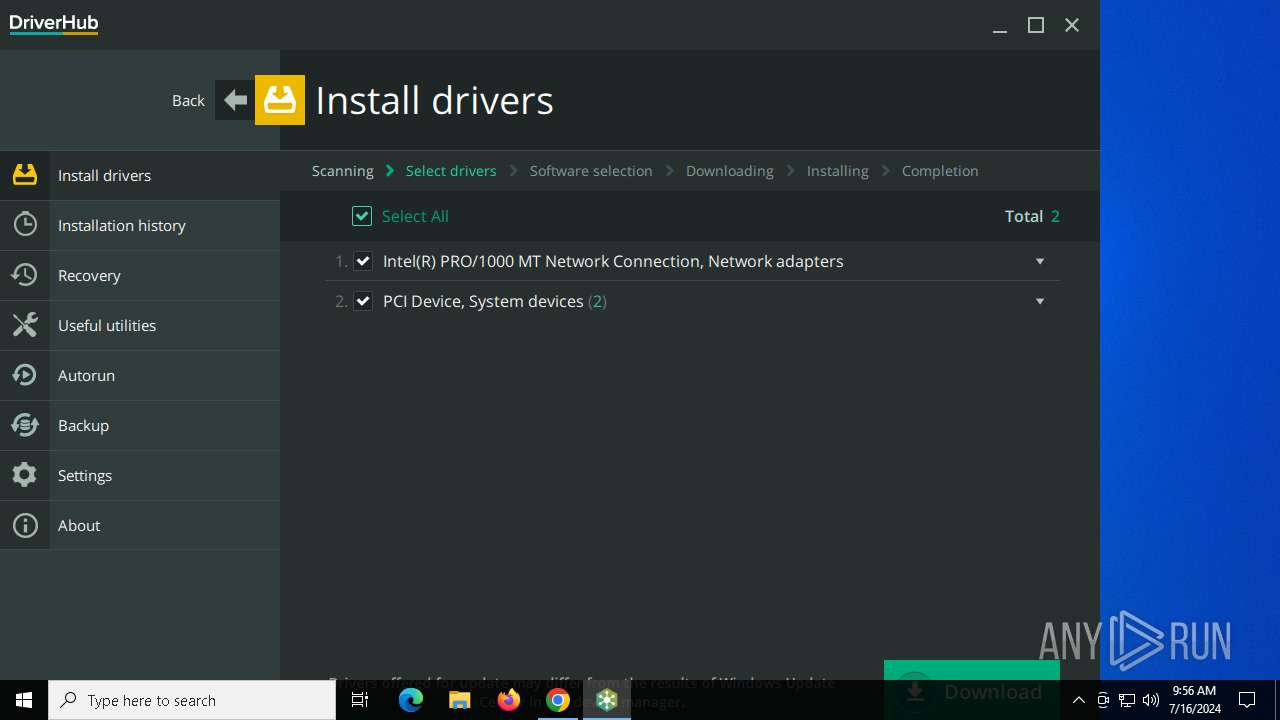
Searches for installed software
- VC_redist.x86.exe (PID: 6396)
- VC_redist.x86.exe (PID: 7260)
- dllhost.exe (PID: 4400)
- VC_redist.x86.exe (PID: 1832)
- VC_redist.x86.exe (PID: 6796)
Starts itself from another location
- VC_redist.x86.exe (PID: 6396)
- setup.exe (PID: 7292)
- Instup.exe (PID: 4308)
Executes as Windows Service
- VSSVC.exe (PID: 7300)
- net_updater32.exe (PID: 3992)
- WmiApSrv.exe (PID: 7136)
Creates a software uninstall entry
- VC_redist.x86.exe (PID: 7260)
- driver-hub-install__28.exe (PID: 7576)
- VC_redist.x86.exe (PID: 6796)
Checks Windows Trust Settings
- msiexec.exe (PID: 2784)
- driver-hub-install__28.exe (PID: 7576)
- setup.exe (PID: 7292)
- DriverHub.exe (PID: 3948)
- net_updater32.exe (PID: 3992)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 2784)
The process drops C-runtime libraries
- msiexec.exe (PID: 2784)
- DriverHub.exe (PID: 3948)
Detected use of alternative data streams (AltDS)
- DriverHub.exe (PID: 3948)
- net_updater32.exe (PID: 3992)
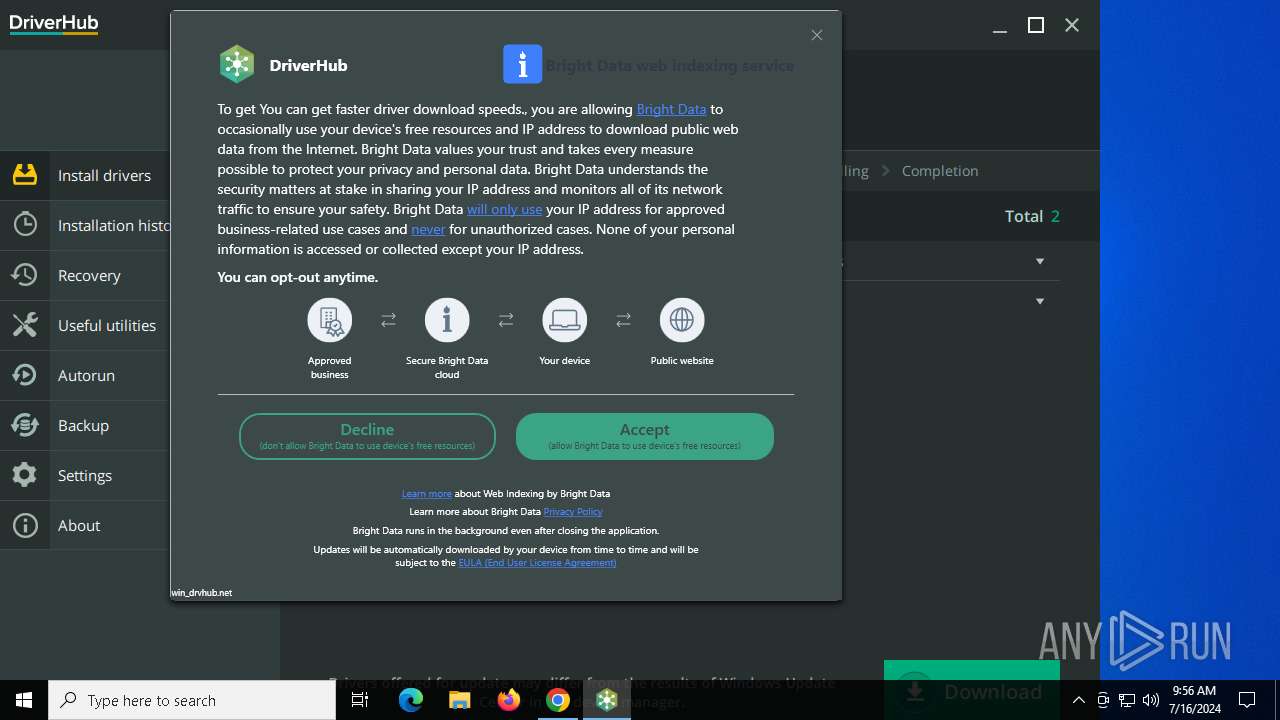
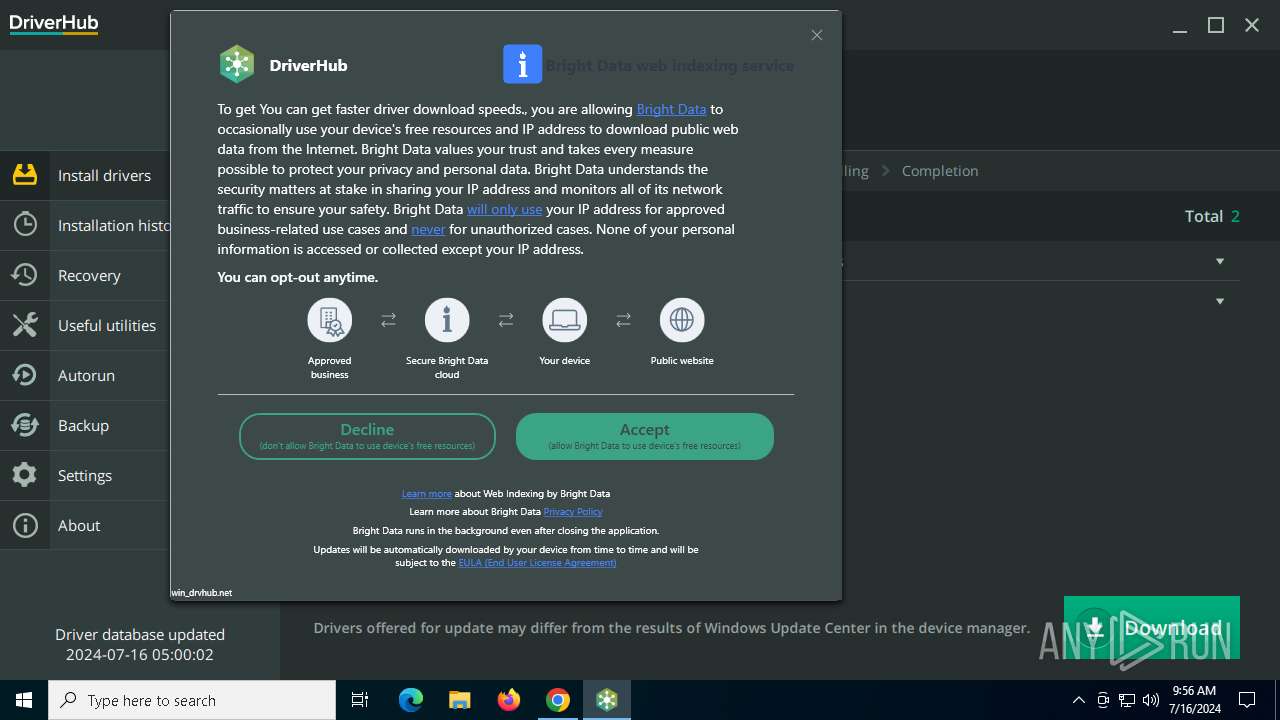
Potential Corporate Privacy Violation
- AvastDownloader.exe (PID: 1292)
- net_updater32.exe (PID: 3992)
Process requests binary or script from the Internet
- AvastDownloader.exe (PID: 1292)
The process checks if it is being run in the virtual environment
- net_updater32.exe (PID: 3992)
Checks for external IP
- net_updater32.exe (PID: 3992)
Process checks presence of unattended files
- instup.exe (PID: 2008)
The process verifies whether the antivirus software is installed
- instup.exe (PID: 2008)
INFO
Application launched itself
- chrome.exe (PID: 3232)
- msedge.exe (PID: 2120)
- msedge.exe (PID: 7628)
- msedge.exe (PID: 4308)
Drops the executable file immediately after the start
- chrome.exe (PID: 3232)
Executable content was dropped or overwritten
- chrome.exe (PID: 3232)
- msiexec.exe (PID: 2784)
Checks supported languages
- driver-hub-install__28.exe (PID: 7440)
- driver-hub-install__28.exe (PID: 7576)
- VC_redist.x86.exe (PID: 6396)
- VC_redist.x86.exe (PID: 4796)
- VC_redist.x86.exe (PID: 7260)
- msiexec.exe (PID: 2784)
- VC_redist.x86.exe (PID: 1832)
- VC_redist.x86.exe (PID: 8016)
- VC_redist.x86.exe (PID: 6796)
- DriverHub.exe (PID: 3948)
- setup.exe (PID: 7292)
- AvastDownloader.exe (PID: 1292)
- test_wpf.exe (PID: 4264)
- OperaGXDownloader.exe (PID: 2056)
- setup.exe (PID: 2632)
- setup.exe (PID: 1140)
- setup.exe (PID: 6356)
- setup.exe (PID: 6796)
- identity_helper.exe (PID: 8048)
- identity_helper.exe (PID: 2888)
- avast_free_antivirus_setup_online_x64.exe (PID: 7152)
- Instup.exe (PID: 4308)
- net_updater32.exe (PID: 3992)
- net_updater32.exe (PID: 6408)
- idle_report.exe (PID: 8052)
- brightdata.exe (PID: 640)
- test_wpf.exe (PID: 6904)
- sbr.exe (PID: 4180)
- instup.exe (PID: 2008)
Reads the computer name
- driver-hub-install__28.exe (PID: 7440)
- driver-hub-install__28.exe (PID: 7576)
- VC_redist.x86.exe (PID: 6396)
- VC_redist.x86.exe (PID: 7260)
- msiexec.exe (PID: 2784)
- VC_redist.x86.exe (PID: 1832)
- VC_redist.x86.exe (PID: 6796)
- test_wpf.exe (PID: 4264)
- DriverHub.exe (PID: 3948)
- AvastDownloader.exe (PID: 1292)
- setup.exe (PID: 7292)
- setup.exe (PID: 6356)
- identity_helper.exe (PID: 8048)
- identity_helper.exe (PID: 2888)
- avast_free_antivirus_setup_online_x64.exe (PID: 7152)
- Instup.exe (PID: 4308)
- net_updater32.exe (PID: 6408)
- net_updater32.exe (PID: 3992)
- test_wpf.exe (PID: 6904)
- idle_report.exe (PID: 8052)
- brightdata.exe (PID: 640)
- instup.exe (PID: 2008)
Process checks Internet Explorer phishing filters
- driver-hub-install__28.exe (PID: 7440)
- driver-hub-install__28.exe (PID: 7576)
Checks proxy server information
- driver-hub-install__28.exe (PID: 7440)
- driver-hub-install__28.exe (PID: 7576)
- slui.exe (PID: 7848)
- setup.exe (PID: 7292)
- DriverHub.exe (PID: 3948)
- Instup.exe (PID: 4308)
- avast_free_antivirus_setup_online_x64.exe (PID: 7152)
- instup.exe (PID: 2008)
Process checks whether UAC notifications are on
- driver-hub-install__28.exe (PID: 7576)
Reads Microsoft Office registry keys
- chrome.exe (PID: 3232)
- driver-hub-install__28.exe (PID: 7576)
- msedge.exe (PID: 2120)
- msedge.exe (PID: 4308)
- msedge.exe (PID: 7628)
The process uses the downloaded file
- chrome.exe (PID: 5508)
- chrome.exe (PID: 3232)
Process checks computer location settings
- driver-hub-install__28.exe (PID: 7440)
- driver-hub-install__28.exe (PID: 7576)
- VC_redist.x86.exe (PID: 6396)
- VC_redist.x86.exe (PID: 1832)
- DriverHub.exe (PID: 3948)
- net_updater32.exe (PID: 3992)
Creates files in the program directory
- driver-hub-install__28.exe (PID: 7576)
- VC_redist.x86.exe (PID: 7260)
- DriverHub.exe (PID: 3948)
- avast_free_antivirus_setup_online_x64.exe (PID: 7152)
- Instup.exe (PID: 4308)
- net_updater32.exe (PID: 6408)
- net_updater32.exe (PID: 3992)
- brightdata.exe (PID: 640)
- instup.exe (PID: 2008)
Reads the software policy settings
- driver-hub-install__28.exe (PID: 7576)
- msiexec.exe (PID: 2784)
- slui.exe (PID: 2916)
- AvastDownloader.exe (PID: 1292)
- DriverHub.exe (PID: 3948)
- avast_free_antivirus_setup_online_x64.exe (PID: 7152)
- Instup.exe (PID: 4308)
- net_updater32.exe (PID: 6408)
- net_updater32.exe (PID: 3992)
- setup.exe (PID: 7292)
- instup.exe (PID: 2008)
Create files in a temporary directory
- driver-hub-install__28.exe (PID: 7576)
- VC_redist.x86.exe (PID: 6396)
- VC_redist.x86.exe (PID: 7260)
- VC_redist.x86.exe (PID: 1832)
- setup.exe (PID: 7292)
- setup.exe (PID: 2632)
- setup.exe (PID: 1140)
- setup.exe (PID: 6356)
- setup.exe (PID: 6796)
- OperaGXDownloader.exe (PID: 2056)
Reads the machine GUID from the registry
- msiexec.exe (PID: 2784)
- VC_redist.x86.exe (PID: 7260)
- driver-hub-install__28.exe (PID: 7576)
- DriverHub.exe (PID: 3948)
- test_wpf.exe (PID: 4264)
- AvastDownloader.exe (PID: 1292)
- setup.exe (PID: 7292)
- avast_free_antivirus_setup_online_x64.exe (PID: 7152)
- Instup.exe (PID: 4308)
- net_updater32.exe (PID: 3992)
- test_wpf.exe (PID: 6904)
- idle_report.exe (PID: 8052)
- brightdata.exe (PID: 640)
- instup.exe (PID: 2008)
Creates files or folders in the user directory
- driver-hub-install__28.exe (PID: 7576)
- setup.exe (PID: 2632)
- setup.exe (PID: 7292)
- DriverHub.exe (PID: 3948)
Creates a software uninstall entry
- msiexec.exe (PID: 2784)
Manual execution by a user
- msedge.exe (PID: 4308)
Reads Environment values
- DriverHub.exe (PID: 3948)
- Instup.exe (PID: 4308)
- net_updater32.exe (PID: 3992)
- brightdata.exe (PID: 640)
- instup.exe (PID: 2008)
Disables trace logs
- DriverHub.exe (PID: 3948)
- net_updater32.exe (PID: 3992)
Reads CPU info
- avast_free_antivirus_setup_online_x64.exe (PID: 7152)
- Instup.exe (PID: 4308)
- net_updater32.exe (PID: 3992)
- instup.exe (PID: 2008)
Reads the time zone
- net_updater32.exe (PID: 3992)
Dropped object may contain TOR URL's
- Instup.exe (PID: 4308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
268
Monitored processes
113
Malicious processes
19
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | C:\ProgramData\BrightData\b5f277be9e9b996633e463ee548565b6bbfbe374\brightdata.exe --appid win_drvhub.net | C:\ProgramData\BrightData\b5f277be9e9b996633e463ee548565b6bbfbe374\brightdata.exe | — | net_updater32.exe | |||||||||||
User: admin Company: BrightData Ltd. (certified) Integrity Level: MEDIUM Description: BrightData service allows free use of certain features in an app you installed Version: 1.463.822 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3944 --field-trial-handle=2344,i,10191882250042411147,5449418174063602810,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1060 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x2fc,0x300,0x304,0x2f8,0x30c,0x7ffd9c945fd8,0x7ffd9c945fe4,0x7ffd9c945ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1060 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6028 --field-trial-handle=2388,i,3620802023766849250,3630379016495352432,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1064 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5528 --field-trial-handle=2388,i,3620802023766849250,3630379016495352432,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | brightdata.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | "C:\Users\admin\AppData\Local\Temp\.opera\Opera GX Installer Temp\setup.exe" --version | C:\Users\admin\AppData\Local\Temp\.opera\Opera GX Installer Temp\setup.exe | setup.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: HIGH Description: Opera GX Installer Exit code: 0 Version: 111.0.5168.54 Modules
| |||||||||||||||
| 1292 | "C:\Users\admin\AppData\Local\Temp\DriverHub\AvastDownloader.exe" /silent /WS | C:\Users\admin\AppData\Local\Temp\DriverHub\AvastDownloader.exe | driver-hub-install__28.exe | ||||||||||||
User: admin Company: AVAST Software Integrity Level: HIGH Description: Avast Installer Version: 2.1.99.0 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5840 --field-trial-handle=1880,i,258928862354901413,17856747974527749301,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1388 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
92 463
Read events
89 516
Write events
2 589
Delete events
358
Modification events
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
161
Suspicious files
838
Text files
798
Unknown types
48
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1cecb9.TMP | — | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1cecc9.TMP | — | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1ceca9.TMP | text | |
MD5:8F45965291AB2DA10EEB049FB6E917C6 | SHA256:8A0DE526945B27CDBBD87357C85FDDD37B572370F894CB0A5AC533FD465D2166 | |||
| 3232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1cedc3.TMP | text | |
MD5:13D19AD173F46FFCD5871A3309D723EF | SHA256:F74346A518C9CA378DE81E9459ACB62FE0B1B6CE4CD9F190D0729A40B75B46F3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
67
TCP/UDP connections
290
DNS requests
234
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2032 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3232 | chrome.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDH8W4DYne0Pz5Yw8qA%3D%3D | unknown | — | — | whitelisted |
8060 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
4452 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3680 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6752 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6716 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3232 | chrome.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
8060 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpqvkfvmnkfl4g52htw6e7e2yzq_66/khaoiebndkojlmppeemjhbpbandiljpe_66_win_acs6eqqbgqw4p5n5jb6zwupd5f2a.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4452 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2124 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2032 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6188 | chrome.exe | 188.130.153.33:443 | www.drvhub.net | Rostpay Ltd | RU | unknown |
3232 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6188 | chrome.exe | 188.130.153.33:80 | www.drvhub.net | Rostpay Ltd | RU | unknown |
6188 | chrome.exe | 74.125.143.84:443 | accounts.google.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.drvhub.net |
| whitelisted |
accounts.google.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
use.fontawesome.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |
widget.trustpilot.com |
| shared |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6188 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
1292 | AvastDownloader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2168 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
3992 | net_updater32.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
DriverHub.exe | qrc:/UpdateProgressDialog.qml:11:5: QML Connections: Implicitly defined onFoo properties in Connections are deprecated. Use this syntax instead: function onFoo(<arguments>) { ... }
|
DriverHub.exe | qrc:/main.qml:655:13: QML Connections: Implicitly defined onFoo properties in Connections are deprecated. Use this syntax instead: function onFoo(<arguments>) { ... }
|
DriverHub.exe | qrc:/main.qml:453:31: QML ItemDelegate: Binding loop detected for property "height"
|
DriverHub.exe | file:///C:/Program Files (x86)/DriverHub/QtQuick/Dialogs/DefaultFileDialog.qml:102:33: QML Settings: Failed to initialize QSettings instance. Status code is: 1
|
DriverHub.exe | file:///C:/Program Files (x86)/DriverHub/QtQuick/Dialogs/DefaultFileDialog.qml:102:33: QML Settings: The following application identifiers have not been set: QVector("organizationName", "organizationDomain")
|
DriverHub.exe | qrc:/SettingsPage.qml:47:9: QML MyCheckBox: Binding loop detected for property "width"
|
DriverHub.exe | qrc:/SettingsPage.qml:47:9: QML MyCheckBox: Binding loop detected for property "width"
|
DriverHub.exe | qrc:/SettingsPage.qml:47:9: QML MyCheckBox: Binding loop detected for property "width"
|
DriverHub.exe | qrc:/SettingsPage.qml:29:9: QML MyCheckBox: Binding loop detected for property "width"
|
DriverHub.exe | qrc:/SettingsPage.qml:29:9: QML MyCheckBox: Binding loop detected for property "width"
|