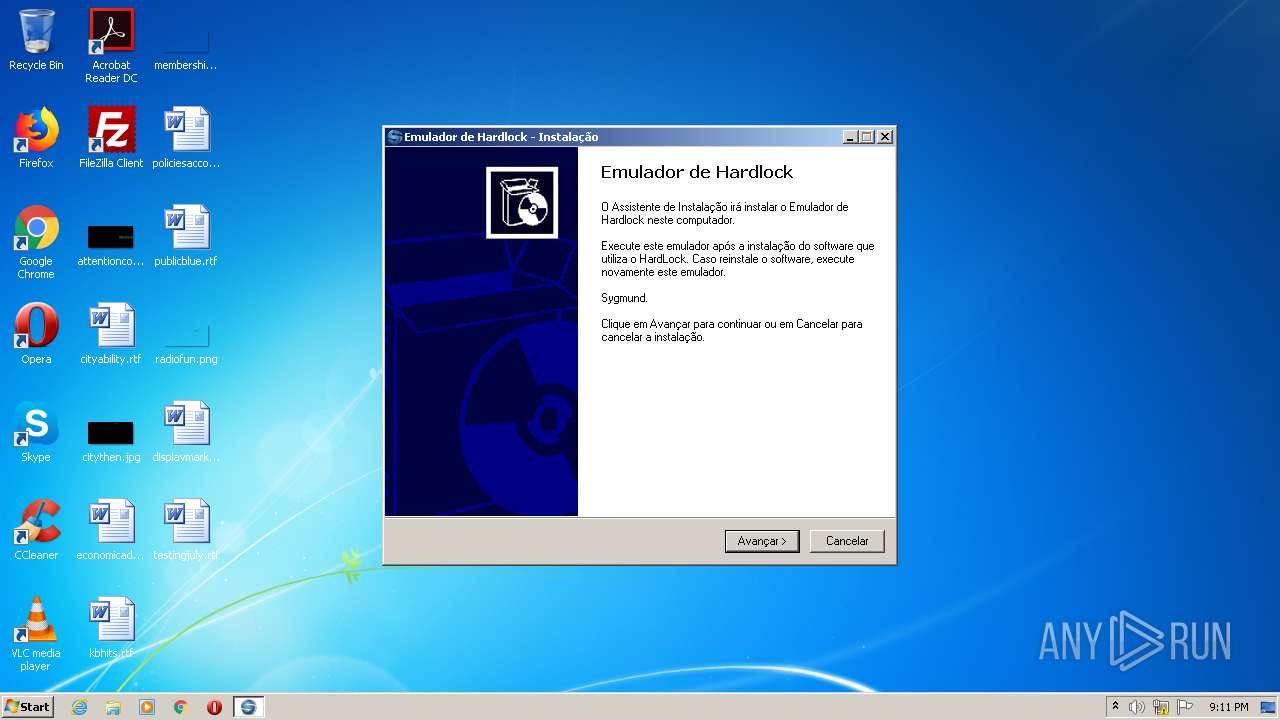
| File name: | Emulador de Hardlock Lumine.exe |
| Full analysis: | https://app.any.run/tasks/614e38ba-6346-44c3-832f-66ab6e339249 |
| Verdict: | Malicious activity |
| Analysis date: | September 24, 2020, 20:11:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InnoSetup self-extracting archive |
| MD5: | 97064857B8D072F7C38173954E979D8C |
| SHA1: | DCD32203D9247B3E7DD9050C4B77865904B68C9F |
| SHA256: | 34F3CED36D2C6CF69B4732F56B6D35576D1862432139B0EF9AB9B7A4EE86A99E |
| SSDEEP: | 6144:NKQuKR9LZP/30A2ghW12+nvJ/0Kt+r4X9z6VskyjFXjaGxvroNZnsk8VR3+JV6:NtPbLZP/ZM2+nvJ3t+UcI3qsk5Q |
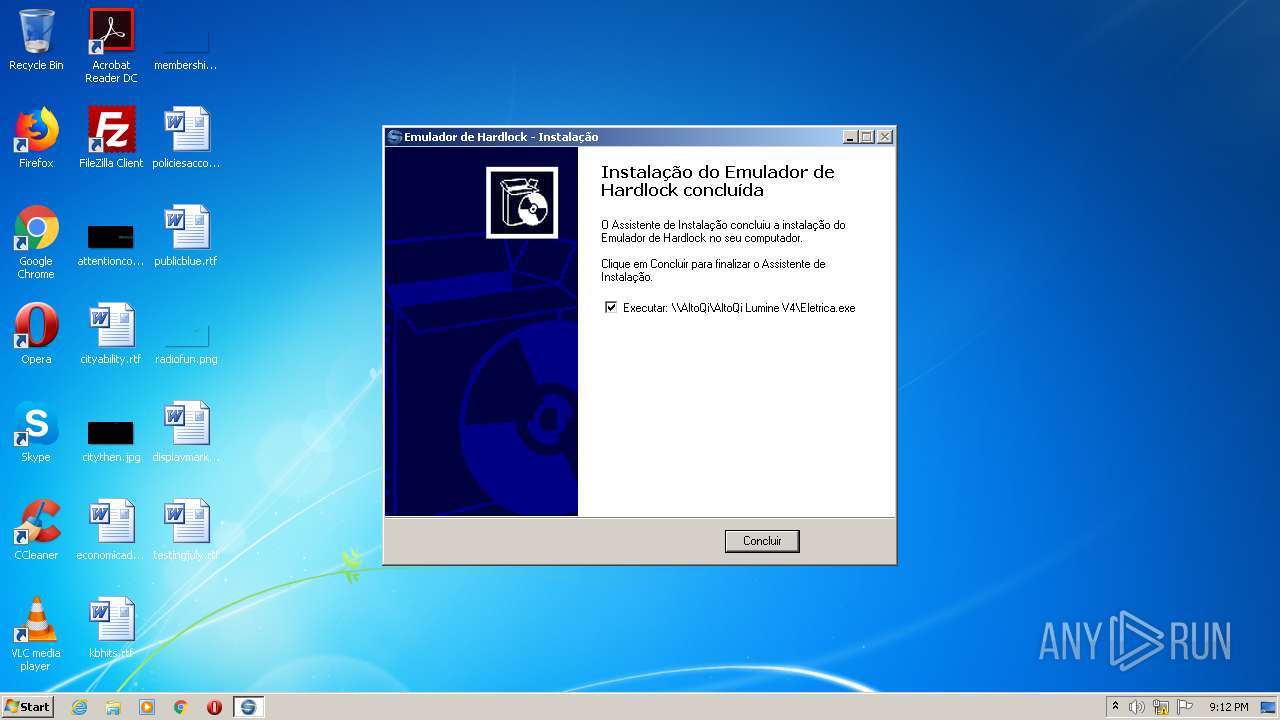
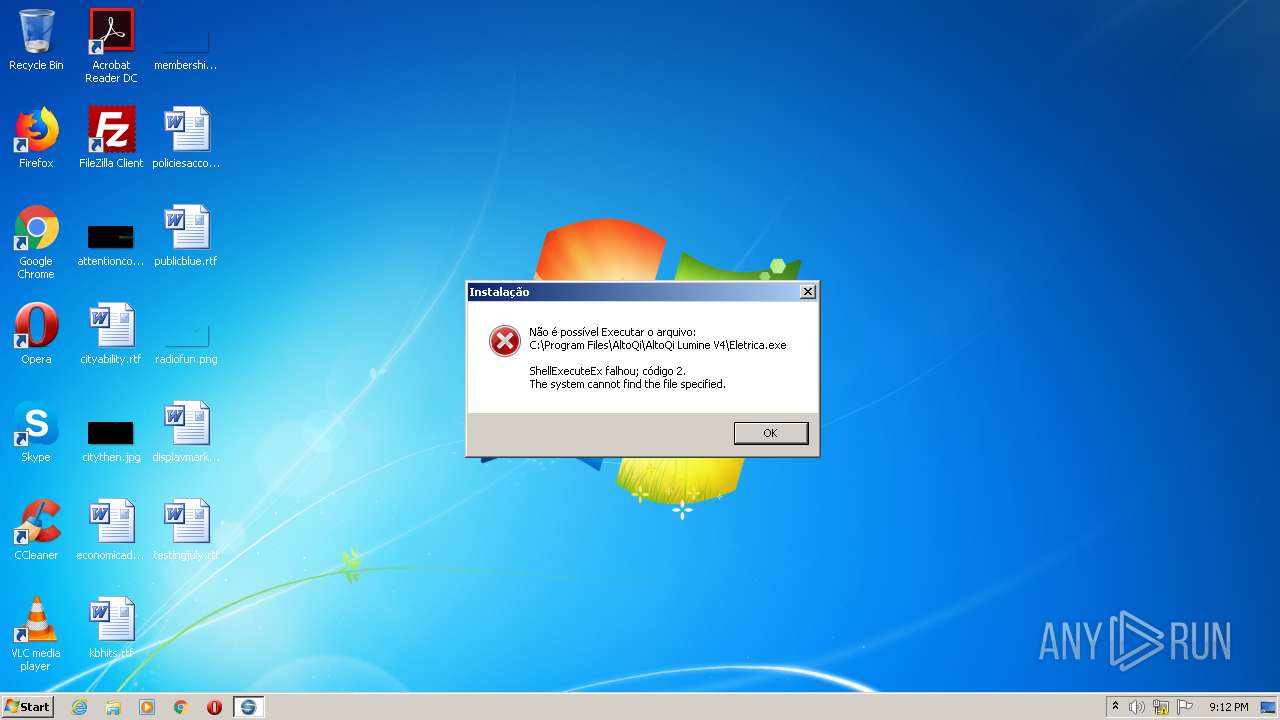
MALICIOUS
Loads dropped or rewritten executable
- mp-IRQBU.tmp (PID: 692)
Application was dropped or rewritten from another process
- mp-IRQBU.tmp (PID: 692)
Starts NET.EXE for service management
- cmd.exe (PID: 4084)
SUSPICIOUS
Executable content was dropped or overwritten
- Emulador de Hardlock Lumine.exe (PID: 936)
- mp-IRQBU.tmp (PID: 692)
Starts application with an unusual extension
- Emulador de Hardlock Lumine.exe (PID: 936)
Creates files in the Windows directory
- mp-IRQBU.tmp (PID: 692)
Creates files in the driver directory
- mp-IRQBU.tmp (PID: 692)
Starts CMD.EXE for commands execution
- mp-IRQBU.tmp (PID: 692)
Creates a software uninstall entry
- mp-IRQBU.tmp (PID: 692)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (82.8) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.7) |
| .exe | | | Win32 Executable (generic) (3.4) |
| .exe | | | Generic Win/DOS Executable (1.5) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 48128 |
| InitializedDataSize: | 28160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc3d4 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 2.1.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | AltoQI |
| FileDescription: | Emulador de Hardlock Setup |
| FileVersion: | 2.1.3.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | Mep Installer |
| ProductVersion: | 2.1.0.0 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | AltoQI |
| FileDescription: | Emulador de Hardlock Setup |
| FileVersion: | 2.1.3.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | Mep Installer |
| ProductVersion: | 2.1.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000BB44 | 0x0000BC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49723 |
DATA | 0x0000D000 | 0x000004DC | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.47467 |
BSS | 0x0000E000 | 0x00000F79 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000F000 | 0x00000B72 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.53417 |
.tls | 0x00010000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00011000 | 0x00000026 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.426353 |
.reloc | 0x00012000 | 0x00000FEC | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00013000 | 0x000059B8 | 0x00005A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.94025 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.86458 | 649 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.47109 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.91697 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.07364 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4092 | 2.8942 | 240 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.9852 | 216 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.17865 | 632 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.2417 | 844 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4096 | 3.18442 | 672 | Latin 1 / Western European | UNKNOWN | RT_STRING |
DESCRIPTION | 2.57152 | 28 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
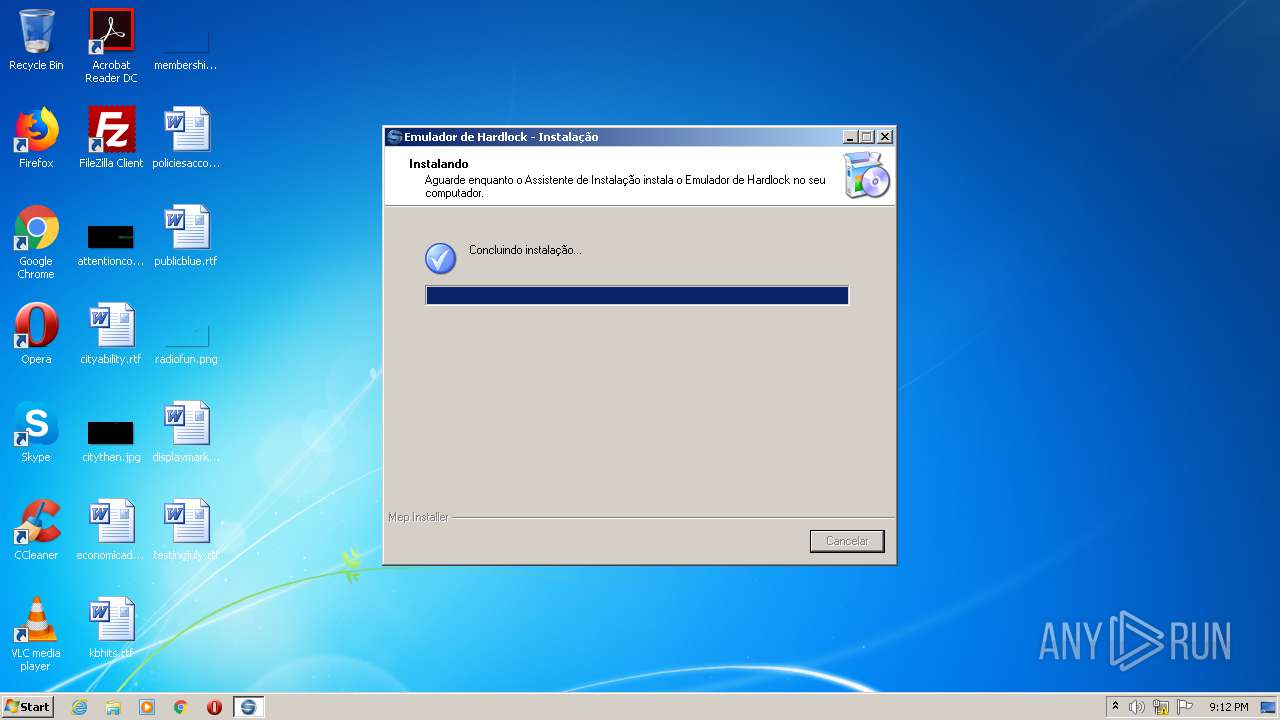
Total processes
47
Monitored processes
11
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 692 | "C:\Users\admin\AppData\Local\Temp\mp-TINDD.tmp\mp-IRQBU.tmp" /SL4 $30138 "C:\Users\admin\AppData\Local\Temp\Emulador de Hardlock Lumine.exe" 88897 77312 | C:\Users\admin\AppData\Local\Temp\mp-TINDD.tmp\mp-IRQBU.tmp | Emulador de Hardlock Lumine.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Mep Installer/UnInstaller Exit code: 0 Version: 2.1.3.0 Modules
| |||||||||||||||
| 756 | net stop hardlockfilter | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 936 | "C:\Users\admin\AppData\Local\Temp\Emulador de Hardlock Lumine.exe" | C:\Users\admin\AppData\Local\Temp\Emulador de Hardlock Lumine.exe | explorer.exe | ||||||||||||
User: admin Company: AltoQI Integrity Level: HIGH Description: Emulador de Hardlock Setup Exit code: 0 Version: 2.1.3.0 Modules
| |||||||||||||||
| 952 | C:\Windows\system32\net1 stop hardlockfilter | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2140 | net start hardlock | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2212 | C:\Windows\system32\net1 start hardlock | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2624 | "C:\Users\admin\AppData\Local\Temp\Emulador de Hardlock Lumine.exe" | C:\Users\admin\AppData\Local\Temp\Emulador de Hardlock Lumine.exe | — | explorer.exe | |||||||||||
User: admin Company: AltoQI Integrity Level: MEDIUM Description: Emulador de Hardlock Setup Exit code: 3221226540 Version: 2.1.3.0 Modules
| |||||||||||||||
| 3248 | "C:\Windows\regedit.exe" /s "C:\Windows\2197.REG" | C:\Windows\regedit.exe | — | mp-IRQBU.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3280 | net stop hardlock | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3624 | C:\Windows\system32\net1 stop hardlock | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
369
Read events
346
Write events
23
Delete events
0
Modification events
| (PID) Process: | (692) mp-IRQBU.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Hydros ID_mp1 |
| Operation: | write | Name: | Mep Installer: Setup Version |
Value: 2.1.3, BR | |||
| (PID) Process: | (692) mp-IRQBU.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Hydros ID_mp1 |
| Operation: | write | Name: | Mep Installer: App Path |
Value: | |||
| (PID) Process: | (692) mp-IRQBU.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Hydros ID_mp1 |
| Operation: | write | Name: | Mep Installer: Icon Group |
Value: (Default) | |||
| (PID) Process: | (692) mp-IRQBU.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Hydros ID_mp1 |
| Operation: | write | Name: | Mep Installer: User |
Value: admin | |||
| (PID) Process: | (692) mp-IRQBU.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Hydros ID_mp1 |
| Operation: | write | Name: | DisplayName |
Value: Services-Emulator-Dumps-HardLock | |||
| (PID) Process: | (692) mp-IRQBU.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Hydros ID_mp1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Windows\unins000.exe" | |||
| (PID) Process: | (692) mp-IRQBU.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Hydros ID_mp1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Windows\unins000.exe" /SILENT | |||
| (PID) Process: | (692) mp-IRQBU.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Hydros ID_mp1 |
| Operation: | write | Name: | Publisher |
Value: AltoQI | |||
| (PID) Process: | (692) mp-IRQBU.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Hydros ID_mp1 |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.altoqi.com.br | |||
| (PID) Process: | (692) mp-IRQBU.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Hydros ID_mp1 |
| Operation: | write | Name: | HelpLink |
Value: http://www.altoqi.com.br | |||
Executable files
4
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 692 | mp-IRQBU.tmp | C:\Windows\mp-9HCL6.tmp | — | |
MD5:— | SHA256:— | |||
| 692 | mp-IRQBU.tmp | C:\Windows\system32\drivers\mp-EF7KE.tmp | — | |
MD5:— | SHA256:— | |||
| 692 | mp-IRQBU.tmp | C:\Windows\system32\drivers\mp-U042Q.tmp | — | |
MD5:— | SHA256:— | |||
| 692 | mp-IRQBU.tmp | C:\Windows\mp-9P661.tmp | — | |
MD5:— | SHA256:— | |||
| 692 | mp-IRQBU.tmp | C:\Windows\system32\drivers\mp-UGRUC.tmp | — | |
MD5:— | SHA256:— | |||
| 692 | mp-IRQBU.tmp | C:\Windows\2197.REG | text | |
MD5:— | SHA256:— | |||
| 692 | mp-IRQBU.tmp | C:\Windows\system32\drivers\hardlock.sys | executable | |
MD5:— | SHA256:— | |||
| 692 | mp-IRQBU.tmp | C:\Windows\system32\drivers\1.bat | text | |
MD5:— | SHA256:— | |||
| 692 | mp-IRQBU.tmp | C:\Windows\unins000.exe | executable | |
MD5:— | SHA256:— | |||
| 692 | mp-IRQBU.tmp | C:\Windows\unins000.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report