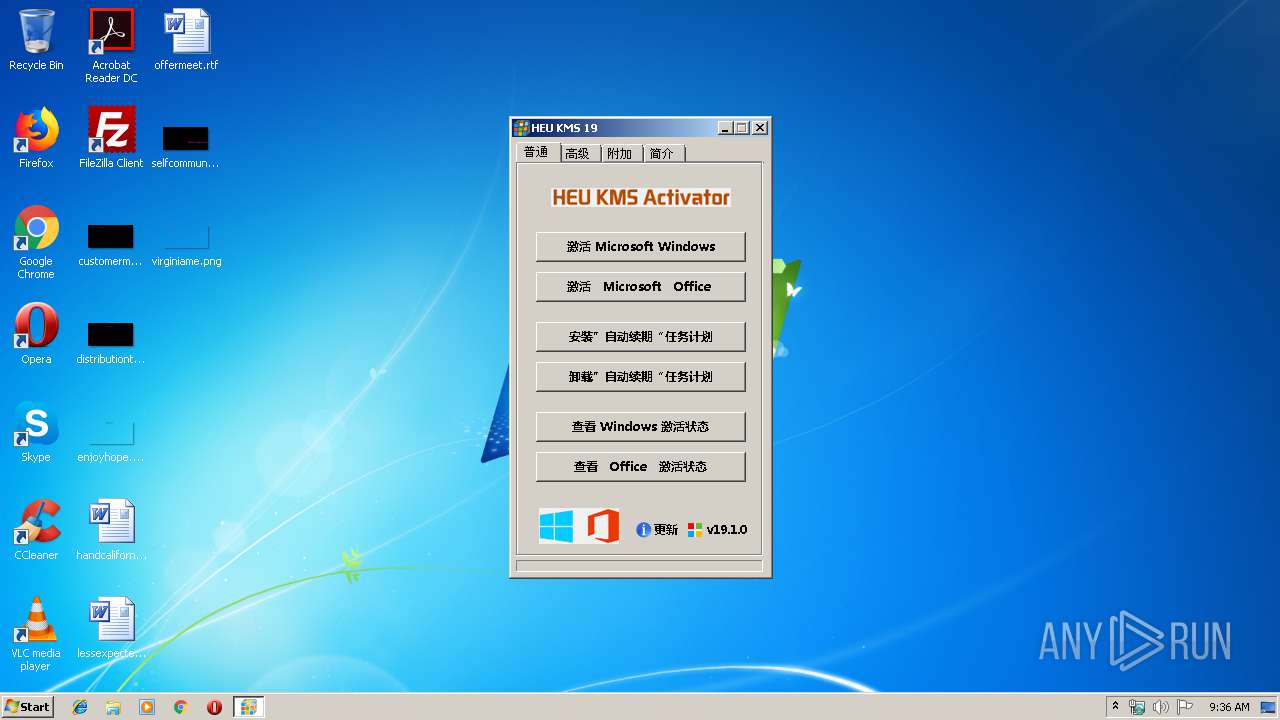
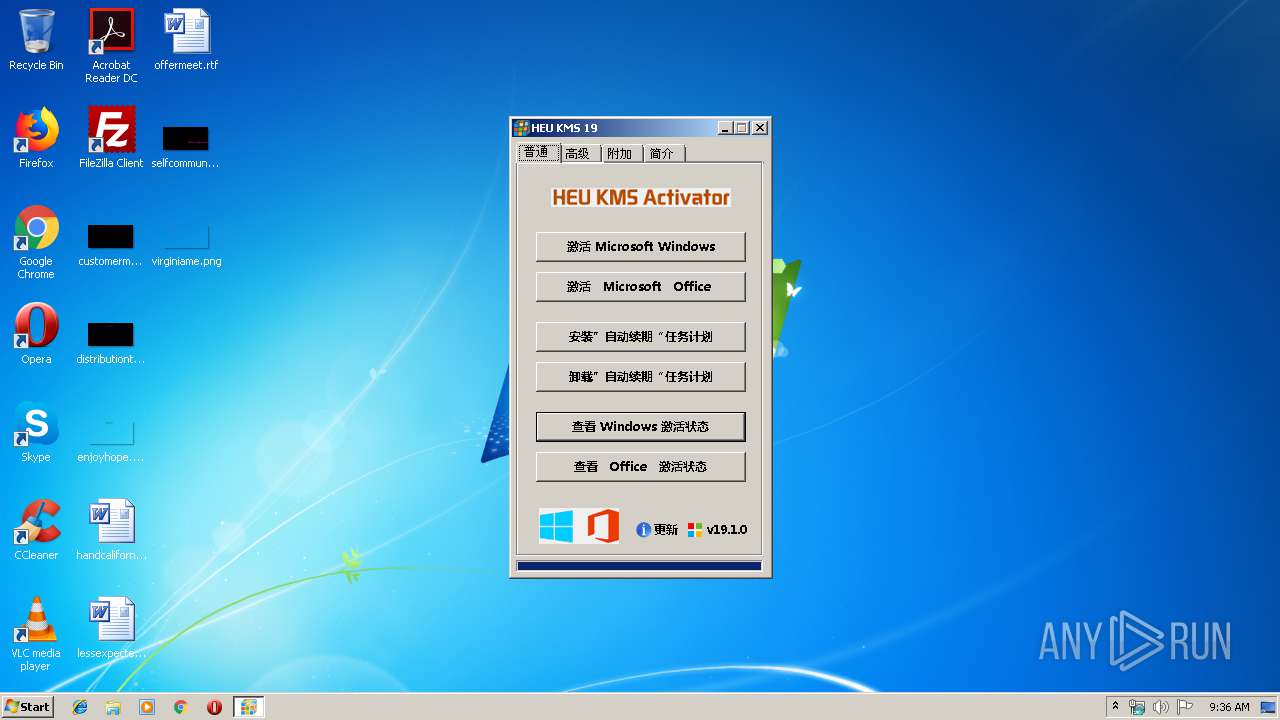
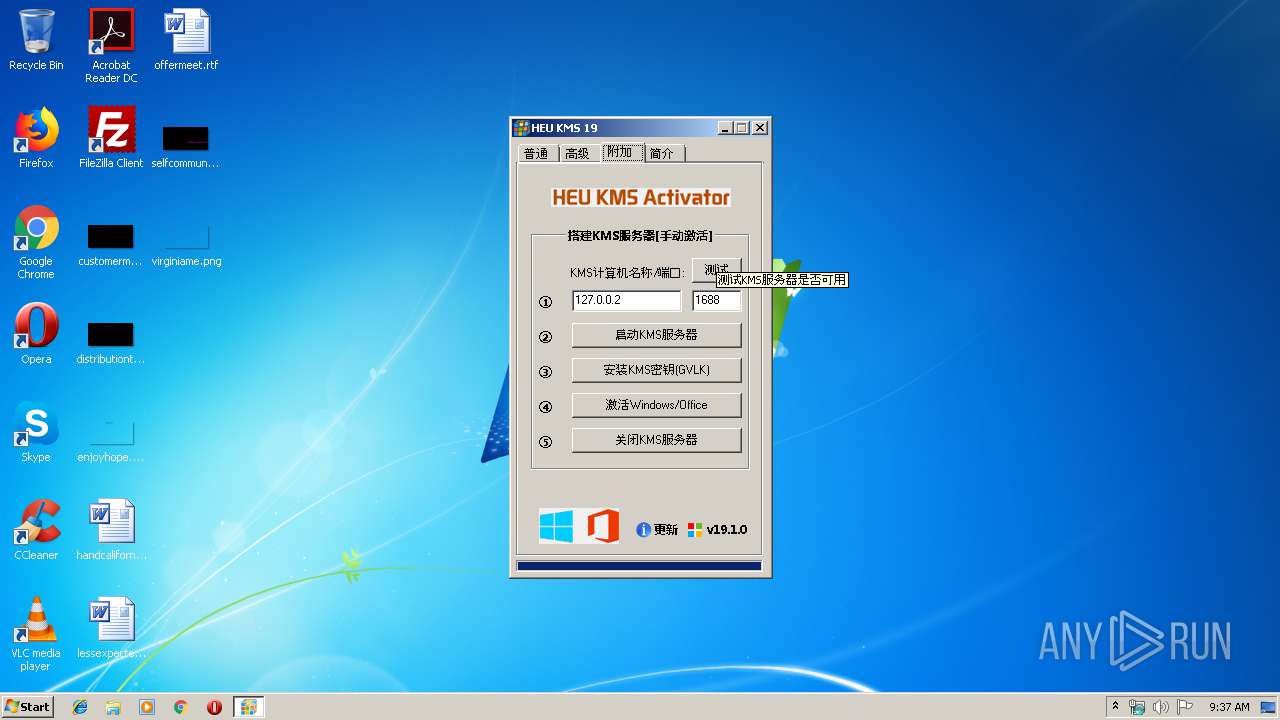
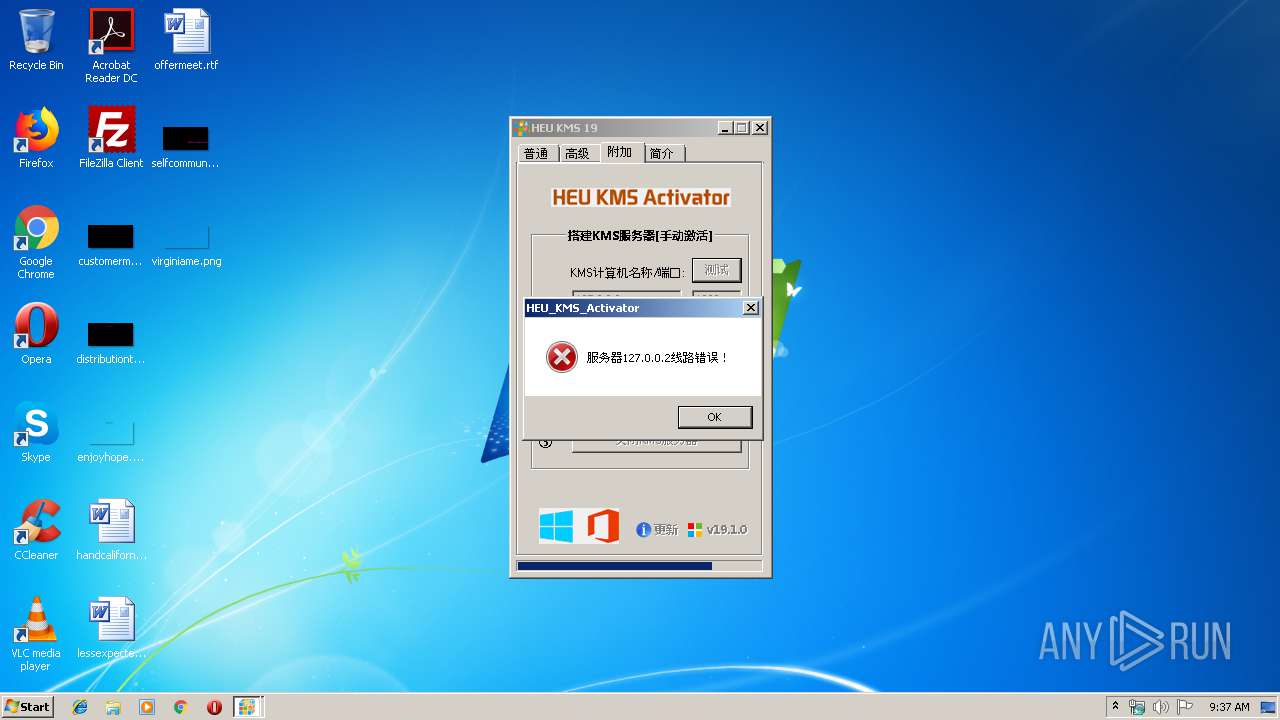
| File name: | HEU_KMS_Activator_v19.1.0.exe |
| Full analysis: | https://app.any.run/tasks/c0271c4c-5283-4e74-b2d5-75d8a09b31f6 |
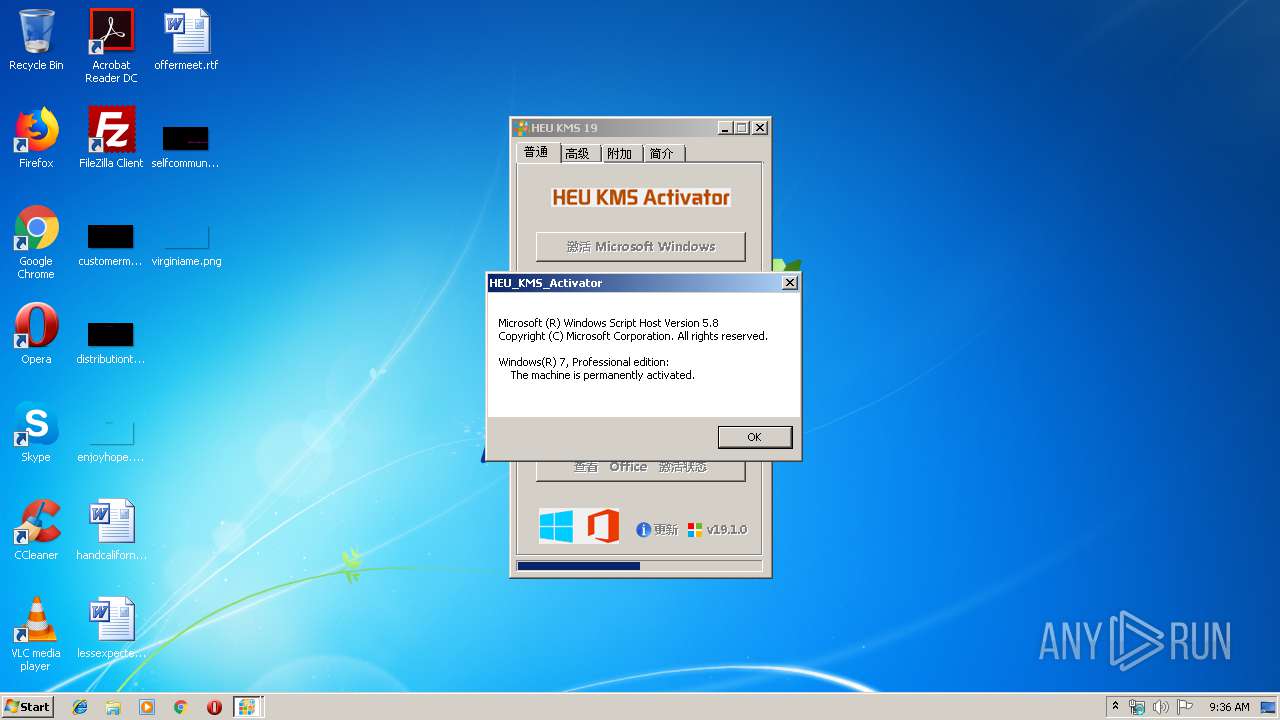
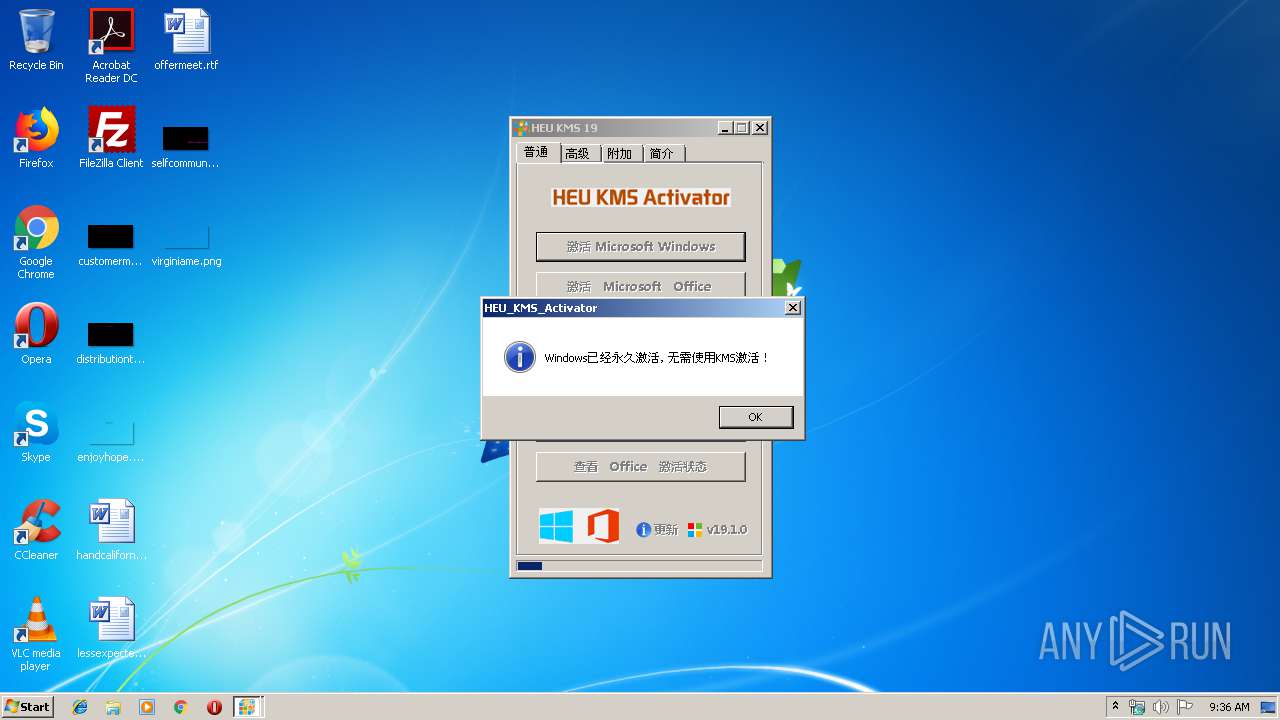
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2019, 08:35:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 08678C3D19E9F7DB2F3E9939F8792195 |
| SHA1: | 2DB58430779EF10A661B97284BC41BF53575A280 |
| SHA256: | 34E13FFFBEB831567DC4784909AE64654404E25AF46170E3DA295498D6261CE7 |
| SSDEEP: | 98304:WdnVXkY7LEvMhc/EAkN2hA02aj1fLexQ0Jr72LYV2UUKPC:CuY7Lk/1kchAMLOJu9UUKa |
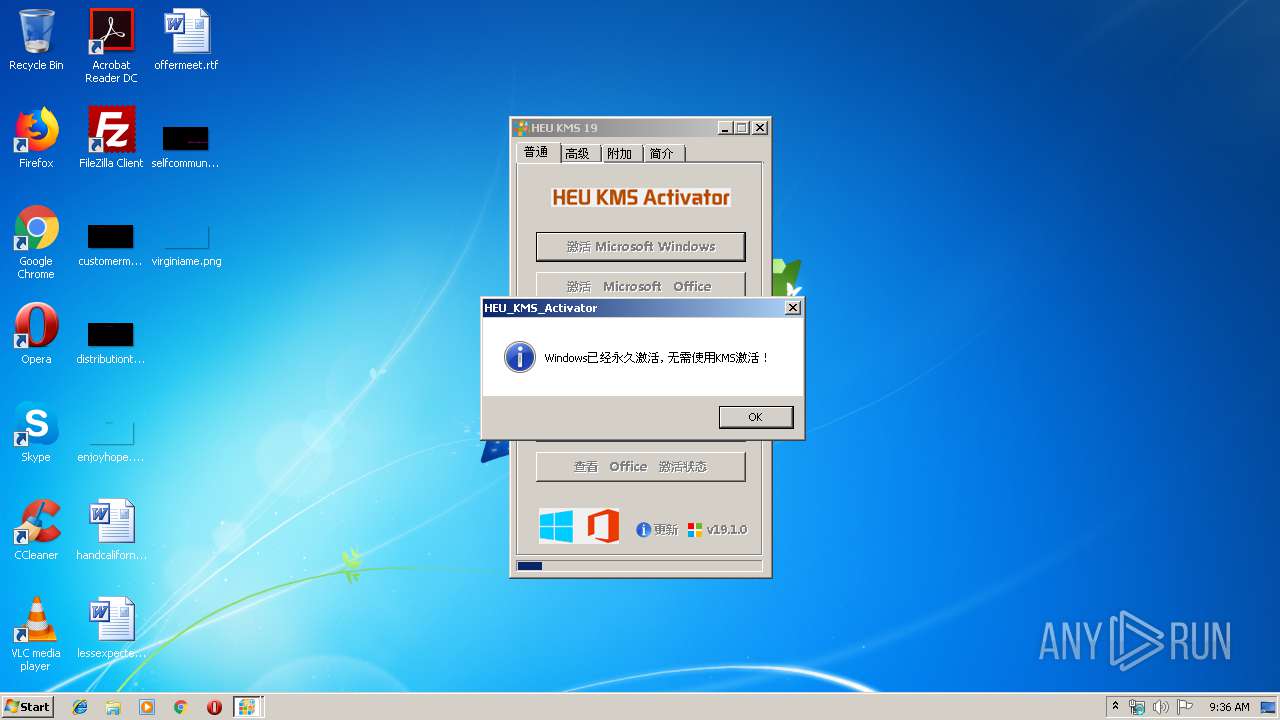
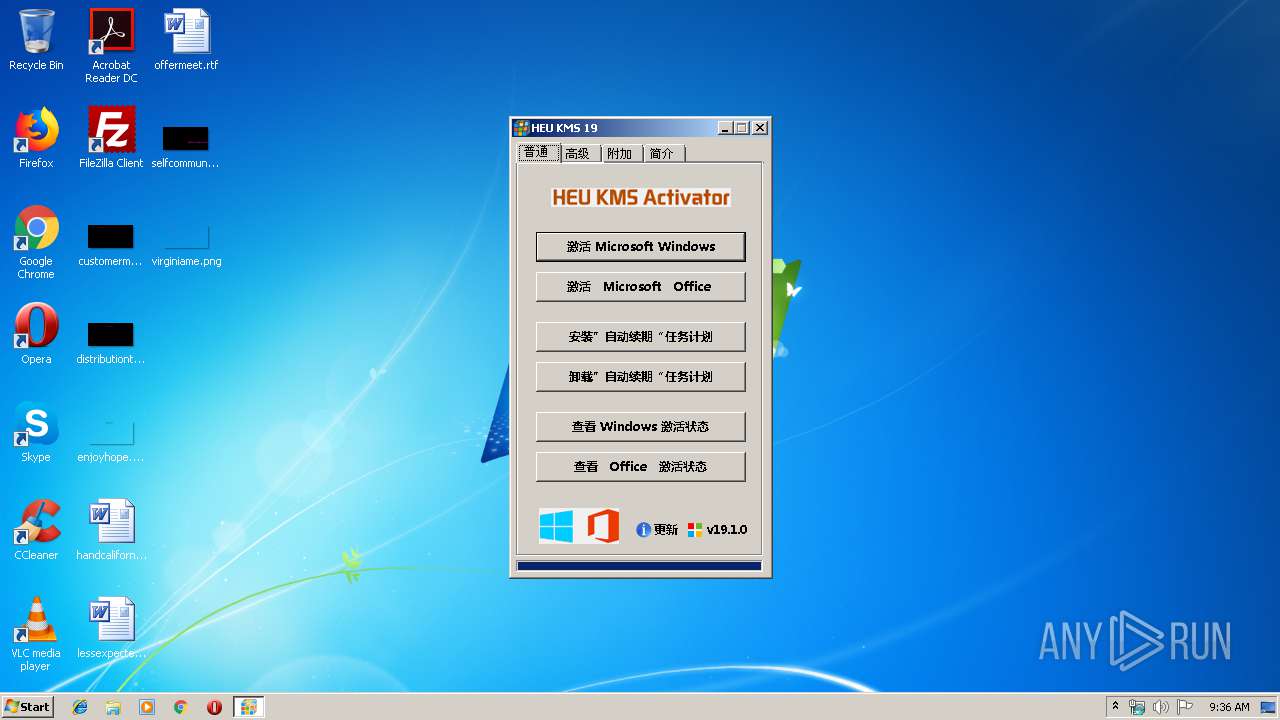
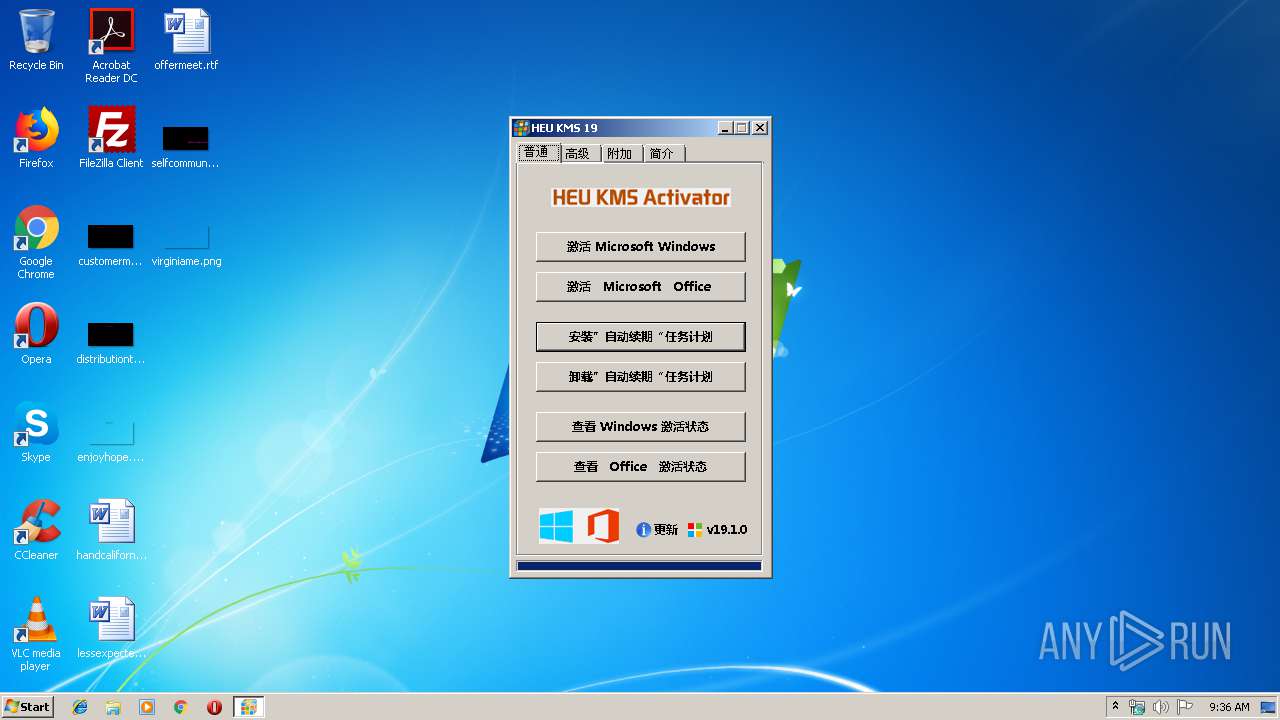
MALICIOUS
Application was dropped or rewritten from another process
- 7Z.EXE (PID: 2732)
- kms.exe (PID: 3584)
- kms-client.exe (PID: 3132)
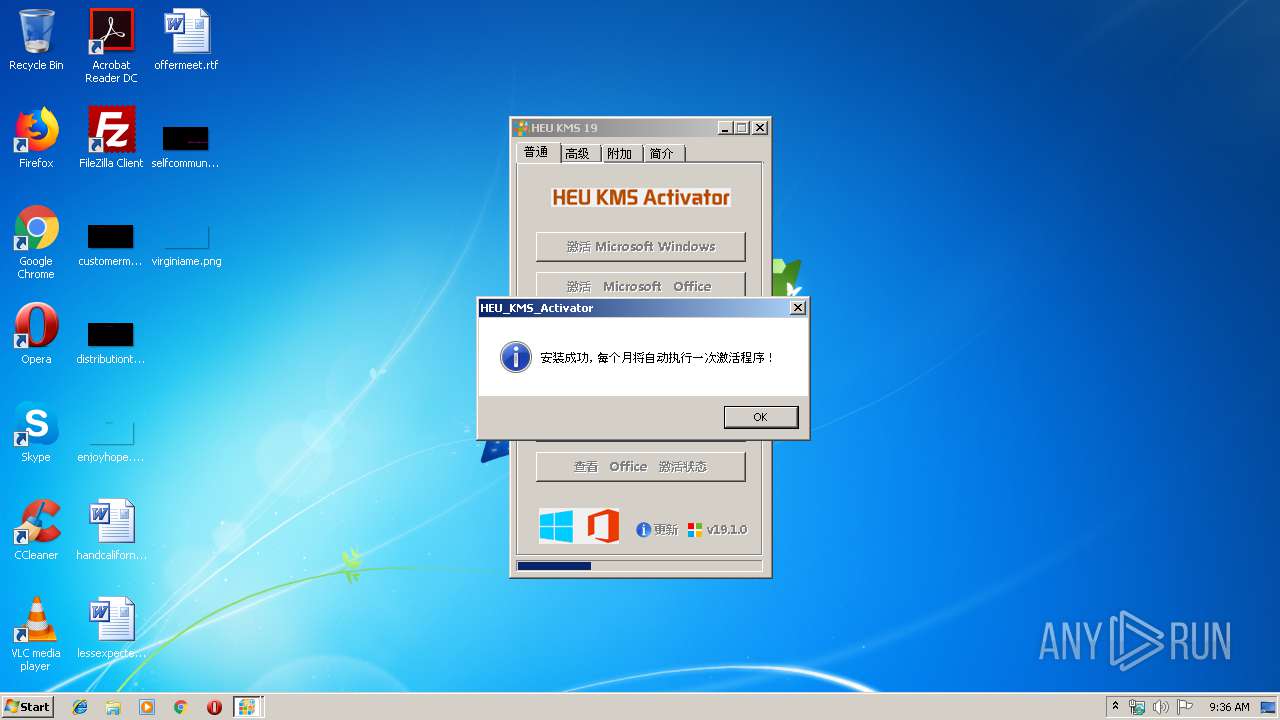
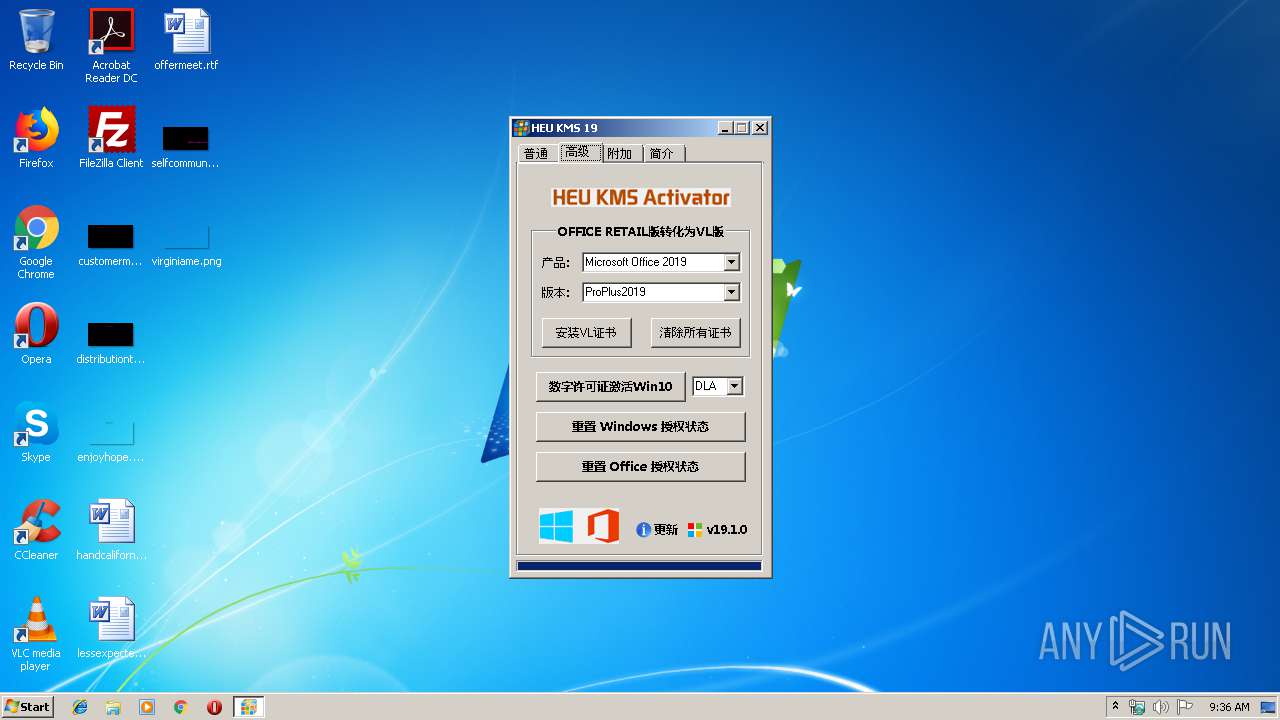
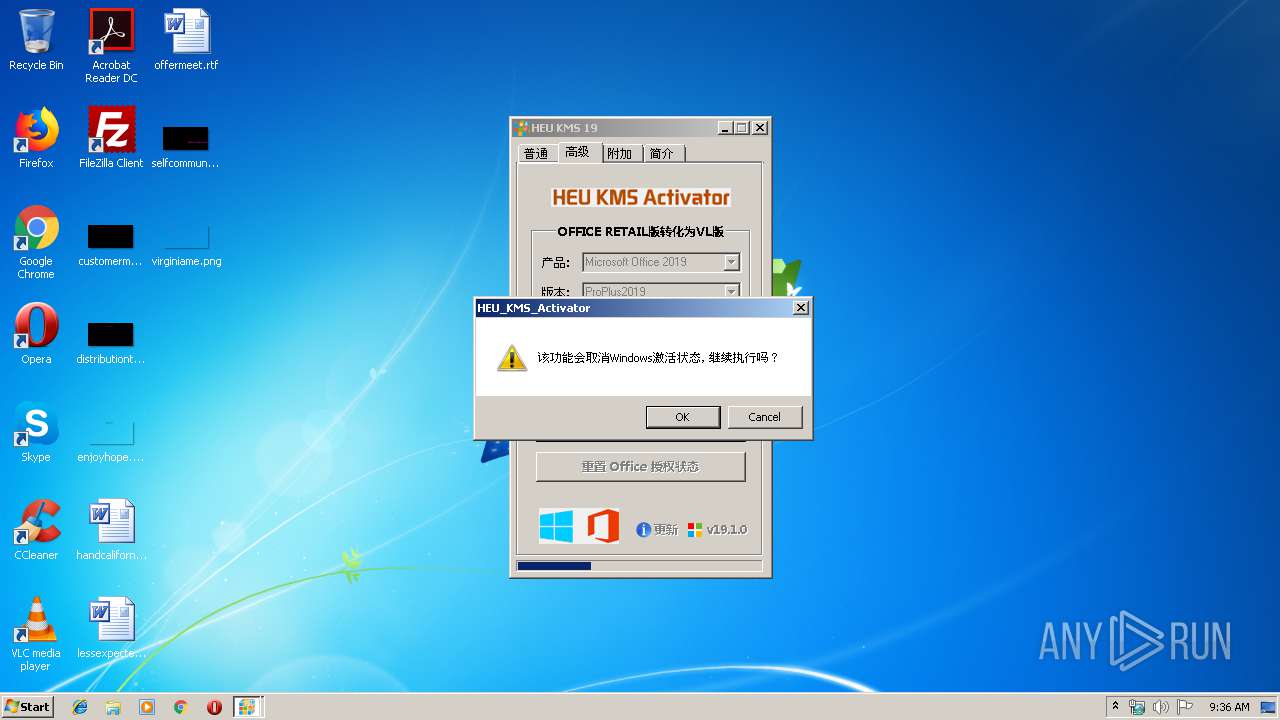
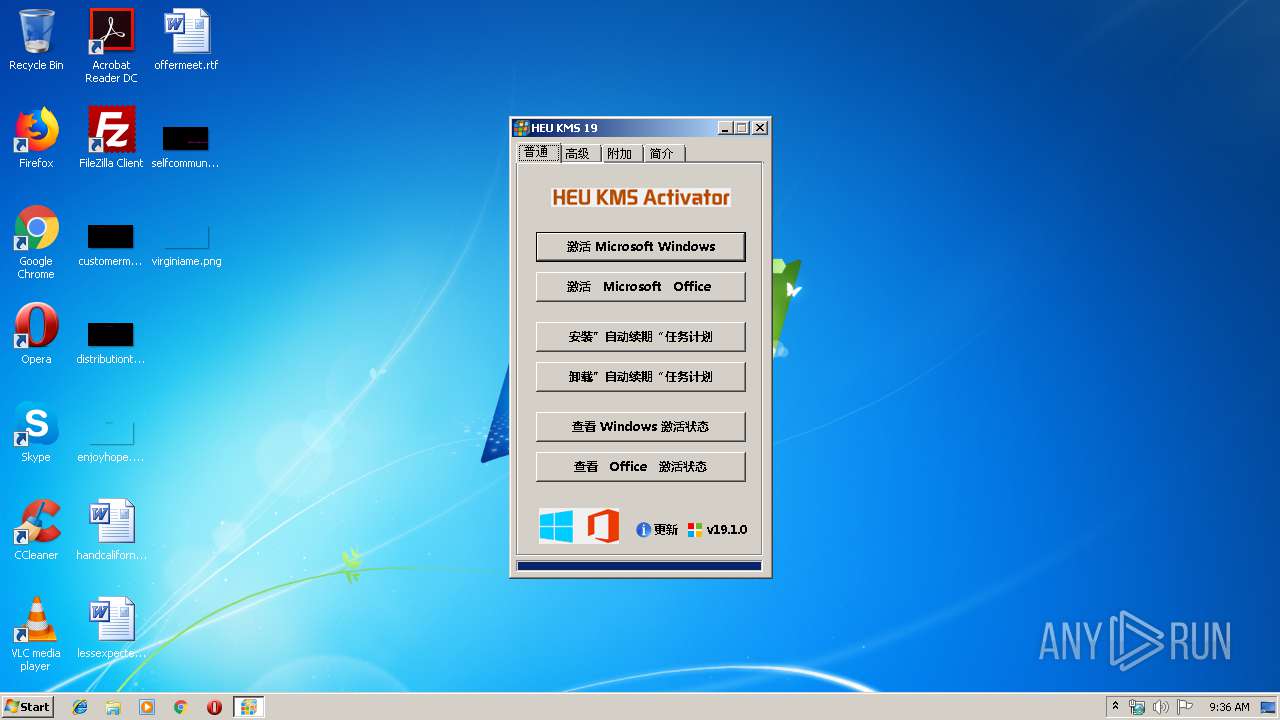
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3508)
- cmd.exe (PID: 2824)
- cmd.exe (PID: 2296)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 4036)
- schtasks.exe (PID: 3140)
- schtasks.exe (PID: 2856)
SUSPICIOUS
Creates files in the Windows directory
- HEU_KMS_Activator_v19.1.0.exe (PID: 3436)
- kms.exe (PID: 3584)
- cmd.exe (PID: 2276)
- cmd.exe (PID: 2824)
- cmd.exe (PID: 2576)
Executable content was dropped or overwritten
- HEU_KMS_Activator_v19.1.0.exe (PID: 3436)
- 7Z.EXE (PID: 2732)
- kms.exe (PID: 3584)
Starts CMD.EXE for commands execution
- kms.exe (PID: 3584)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2724)
Starts application with an unusual extension
- cmd.exe (PID: 2824)
Removes files from Windows directory
- kms.exe (PID: 3584)
Executes scripts
- cmd.exe (PID: 2276)
- cmd.exe (PID: 2668)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:05:02 13:39:51+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 573440 |
| InitializedDataSize: | 3762688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x26bf7 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 19.1.0.0 |
| ProductVersionNumber: | 19.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Fileversion: | 19.1.0.0 |
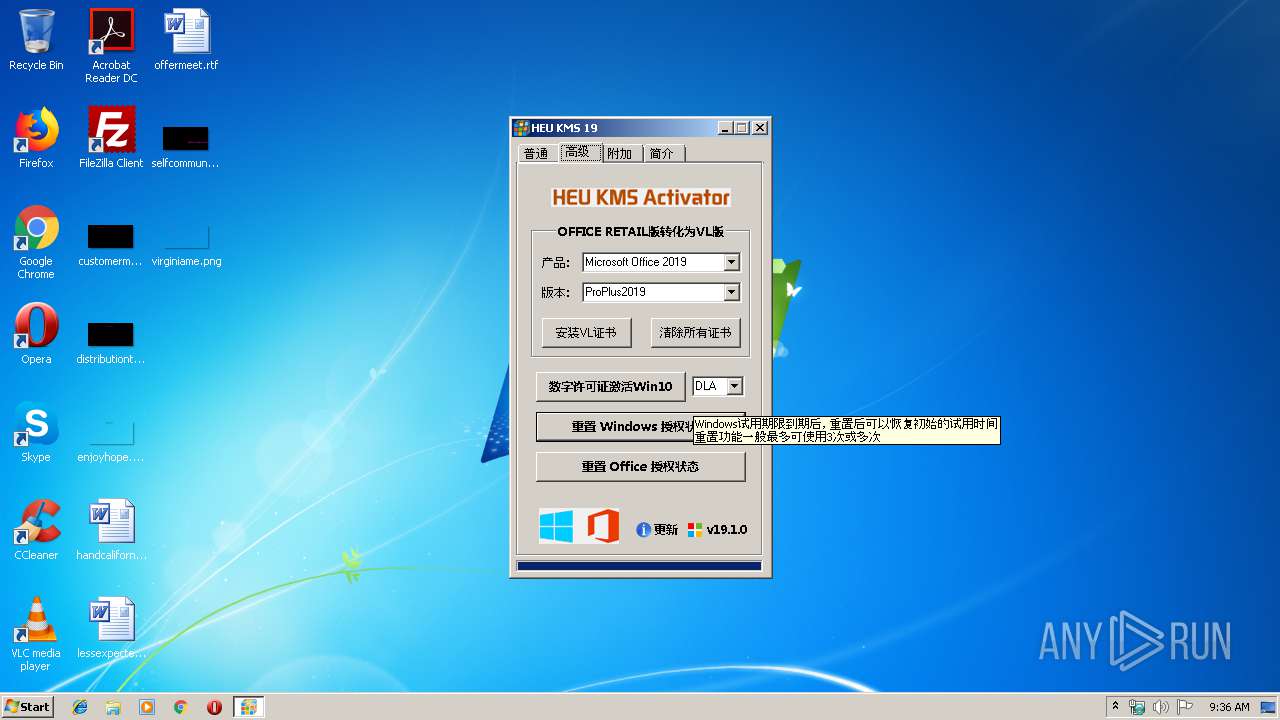
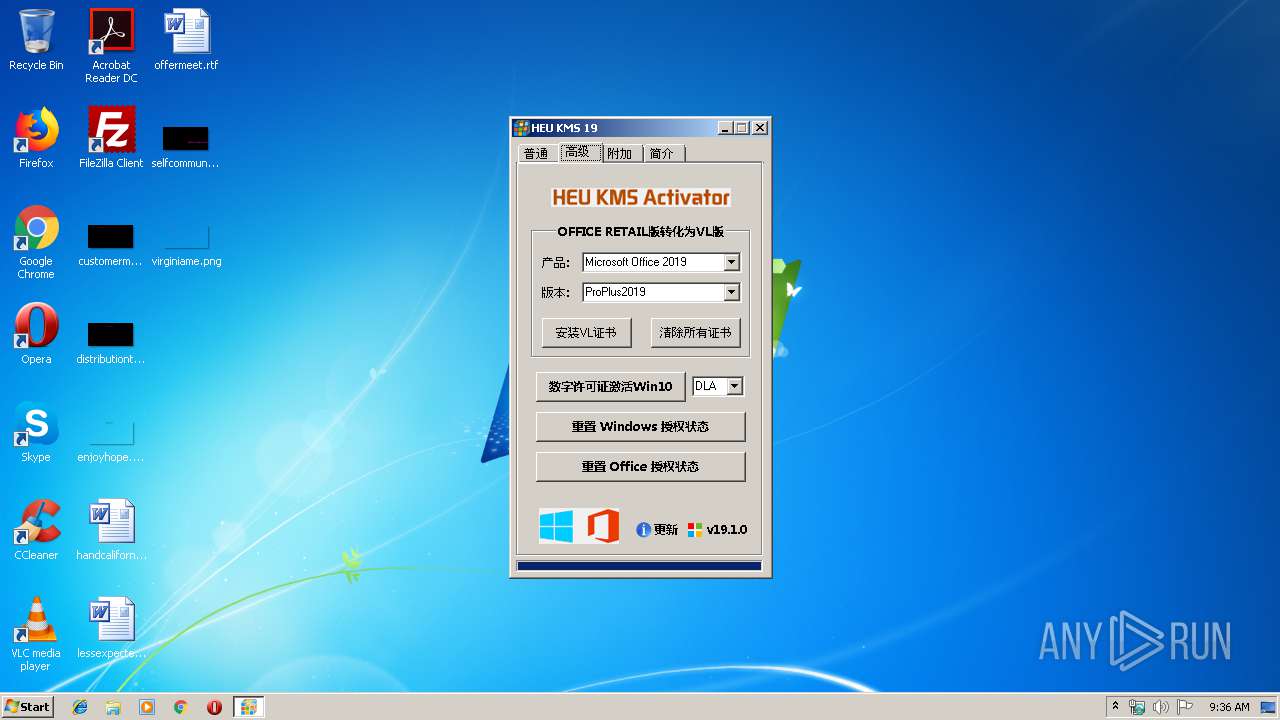
| Comments: | 本地KMS激活/Win10数字权利激活 |
| FileDescription: | HEU KMS Activator |
| ProductVersion: | 19.1.0.0 |
| LegalCopyright: | Copyright(C) 2012-2019 By 知彼而知己 |
| Productname: | HEU KMS Activator |
| CompanyName: | 知彼而知己 |
| OriginalFileName: | HEU KMS Activator |
| InternalName: | HEU KMS Activator |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-May-2019 11:39:51 |
| Detected languages: |
|
| Fileversion: | 19.1.0.0 |
| Comments: | 本地KMS激活/Win10数字权利激活 |
| FileDescription: | HEU KMS Activator |
| ProductVersion: | 19.1.0.0 |
| LegalCopyright: | Copyright(C) 2012-2019 By 知彼而知己 |
| Productname: | HEU KMS Activator |
| CompanyName: | 知彼而知己 |
| OriginalFilename: | HEU KMS Activator |
| InternalName: | HEU KMS Activator |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-May-2019 11:39:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008BE74 | 0x0008C000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.68149 |
.rdata | 0x0008D000 | 0x0002C76A | 0x0002C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.78116 |
.data | 0x000BA000 | 0x00009F34 | 0x00006200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.00477 |
.rsrc | 0x000C4000 | 0x0035990C | 0x00359A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99902 |
.reloc | 0x0041E000 | 0x0000A462 | 0x0000A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.2385 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.31767 | 1448 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 3.84845 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 4.15837 | 1384 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 6.2256 | 9640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 6.88783 | 1128 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
11 | 3.26322 | 1628 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
65
Monitored processes
20
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2276 | C:\Windows\system32\cmd.exe /c cscript "C:\Windows"\System32\slmgr.vbs -xpr > %windir%\HeuKmsLog\checkW.log | C:\Windows\system32\cmd.exe | — | kms.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2296 | C:\Windows\system32\cmd.exe /c schtasks /delete /f /tn "HEU KMS Renewal" | C:\Windows\system32\cmd.exe | — | kms.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2576 | C:\Windows\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\onP8ydjE80KpQvSS\kms-client.exe 1688 127.0.0.2>%windir%\HeuKmsLog\KMSClient.log | C:\Windows\system32\cmd.exe | — | kms.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2668 | C:\Windows\system32\cmd.exe /k slmgr -rearm | C:\Windows\system32\cmd.exe | — | kms.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2724 | C:\Windows\system32\cmd.exe /c netsh advfirewall firewall add rule name="HEU_KMS_Renewal" dir=in action=allow profile=any program="C:\Windows\HeuKmsRenewal\HEU_KMS_Renewal.exe" | C:\Windows\system32\cmd.exe | — | kms.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2732 | C:\Users\admin\AppData\Local\Temp\onP8ydjE80KpQvSS\7Z.EXE x C:\Users\admin\AppData\Local\Temp\onP8ydjE80KpQvSS\KMSmini.7z -y -oC:\Users\admin\AppData\Local\Temp\onP8ydjE80KpQvSS | C:\Users\admin\AppData\Local\Temp\onP8ydjE80KpQvSS\7Z.EXE | HEU_KMS_Activator_v19.1.0.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 2812 | cscript "C:\Windows"\System32\slmgr.vbs -xpr | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2824 | C:\Windows\system32\cmd.exe /c chcp 437 & schtasks /query /fo list | findstr /i "HEU KMS Renewal" > %windir%\HeuKmsLog\CreatTask.log | C:\Windows\system32\cmd.exe | — | kms.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2856 | schtasks /delete /f /tn "HEU KMS Renewal" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3112 | "C:\Users\admin\AppData\Local\Temp\HEU_KMS_Activator_v19.1.0.exe" | C:\Users\admin\AppData\Local\Temp\HEU_KMS_Activator_v19.1.0.exe | — | explorer.exe | |||||||||||
User: admin Company: 知彼而知己 Integrity Level: MEDIUM Description: HEU KMS Activator Exit code: 3221226540 Version: 19.1.0.0 | |||||||||||||||
Total events
230
Read events
168
Write events
62
Delete events
0
Modification events
| (PID) Process: | (3196) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3196) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (3196) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (3196) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (3196) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (3196) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (3196) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (3196) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (3196) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
| (PID) Process: | (3196) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\tsgqec.dll,-100 |
Value: RD Gateway Quarantine Enforcement Client | |||
Executable files
13
Suspicious files
3
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3436 | HEU_KMS_Activator_v19.1.0.exe | C:\Users\admin\AppData\Local\Temp\autE29E.tmp | — | |
MD5:— | SHA256:— | |||
| 3436 | HEU_KMS_Activator_v19.1.0.exe | C:\Users\admin\AppData\Local\Temp\autE2FD.tmp | — | |
MD5:— | SHA256:— | |||
| 3436 | HEU_KMS_Activator_v19.1.0.exe | C:\Users\admin\AppData\Local\Temp\autE34C.tmp | — | |
MD5:— | SHA256:— | |||
| 3436 | HEU_KMS_Activator_v19.1.0.exe | C:\Users\admin\AppData\Local\Temp\autE36C.tmp | — | |
MD5:— | SHA256:— | |||
| 3436 | HEU_KMS_Activator_v19.1.0.exe | C:\Users\admin\AppData\Local\Temp\onP8ydjE80KpQvSS\KMSmini.7z | compressed | |
MD5:2A081BFF1D9AC5988E5AA5270ED64890 | SHA256:49AEE24E866EF4661C80B4A3DD2E6C2C871AF53A34858C50F463563F65FD9D43 | |||
| 3436 | HEU_KMS_Activator_v19.1.0.exe | C:\Windows\HeuKmsRenewal\HEU_KMS_Activator.exe | executable | |
MD5:08678C3D19E9F7DB2F3E9939F8792195 | SHA256:34E13FFFBEB831567DC4784909AE64654404E25AF46170E3DA295498D6261CE7 | |||
| 3436 | HEU_KMS_Activator_v19.1.0.exe | C:\Users\admin\AppData\Local\Temp\onP8ydjE80KpQvSS\cert.7z | compressed | |
MD5:7209BAB95465246605F63D8499E490B3 | SHA256:70F9CFBA02B9A5DD1DFBDA48CF2608A6D4CCF5380A054D7C323CF972B61FE8AB | |||
| 3436 | HEU_KMS_Activator_v19.1.0.exe | C:\Users\admin\AppData\Local\Temp\onP8ydjE80KpQvSS\digital.7z | compressed | |
MD5:ED1CF5F0AB9BC9C92FA6E1A5933B4736 | SHA256:F98E9F414FC9D2ED852455EC1722DD0795D834886C0E36B7CE493C6D804AB5C7 | |||
| 2732 | 7Z.EXE | C:\Users\admin\AppData\Local\Temp\onP8ydjE80KpQvSS\pic\Windows.jpg | image | |
MD5:4262E7112F412BE7046689B5F6F14A95 | SHA256:E590CAAC9A27B54CBBF374581AECA74B0FDDB5AAED9EBCF5131020287540D134 | |||
| 2732 | 7Z.EXE | C:\Users\admin\AppData\Local\Temp\onP8ydjE80KpQvSS\pic\ewm.jpg | image | |
MD5:0A3AD9F37C75C9FBF0C133773323F55D | SHA256:83D77A0FD7A3D823BF7D27009529B10610C7A7F457227A387A987570BE348049 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report