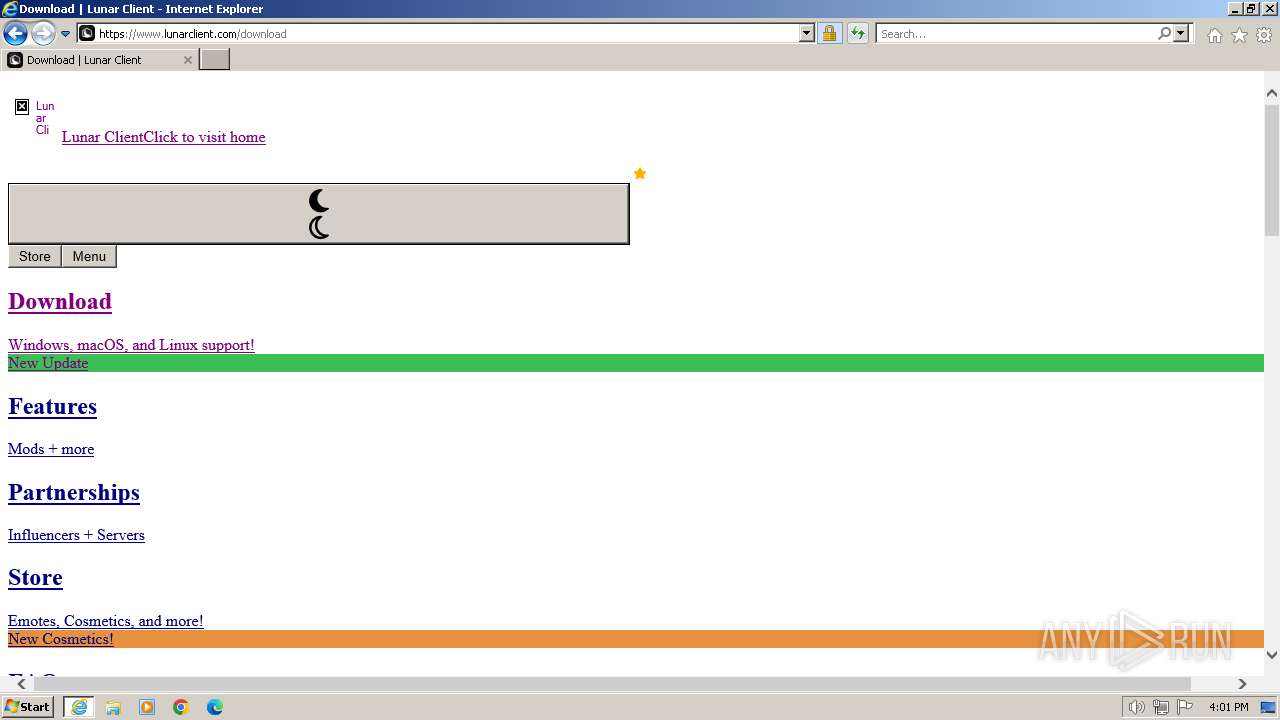
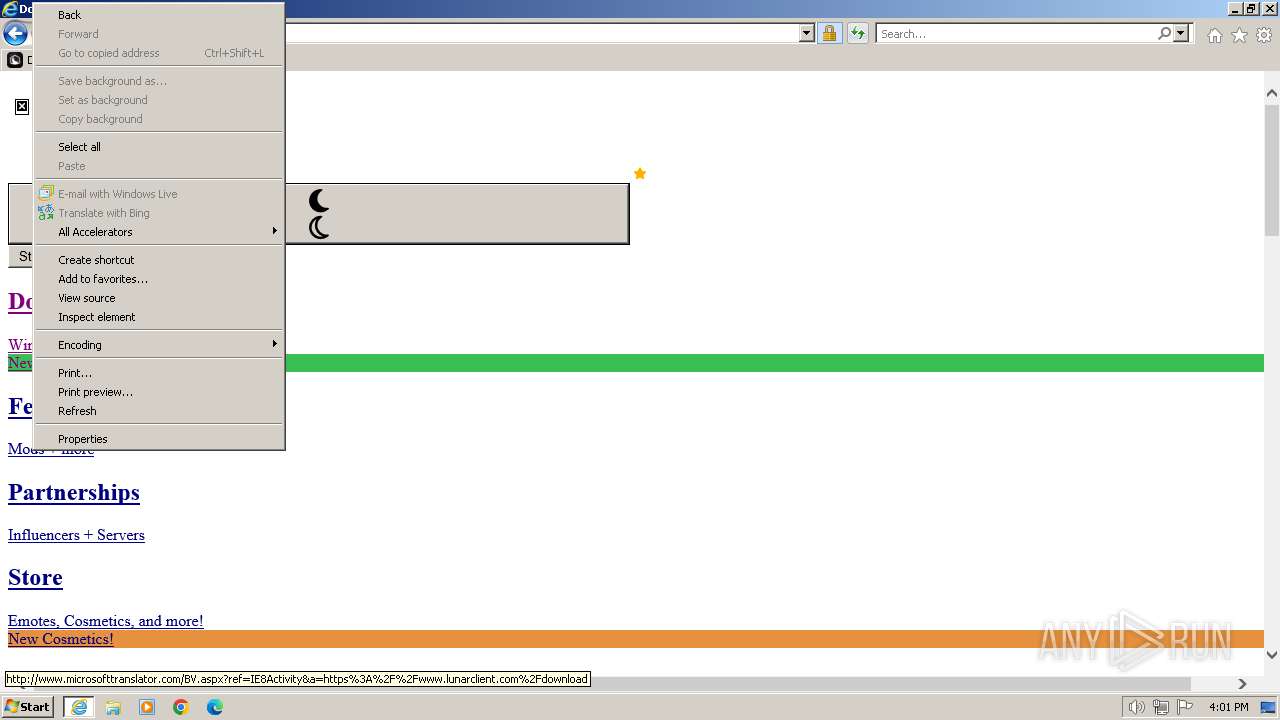
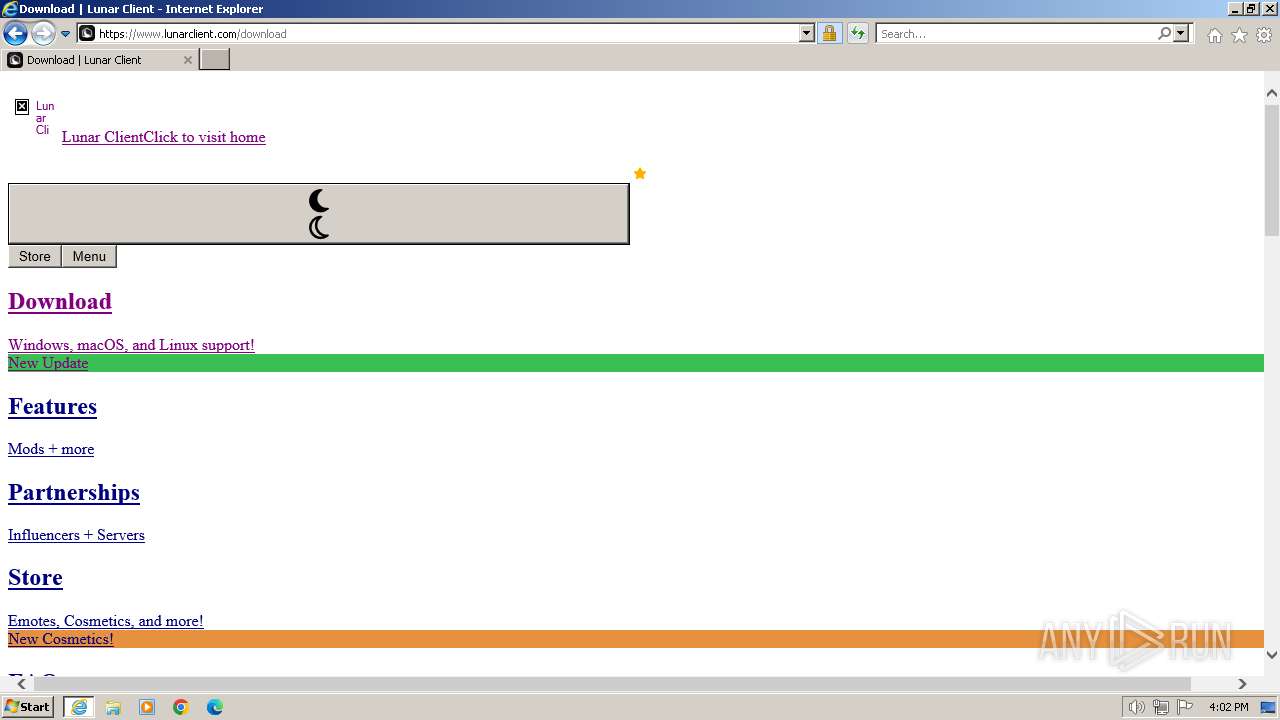
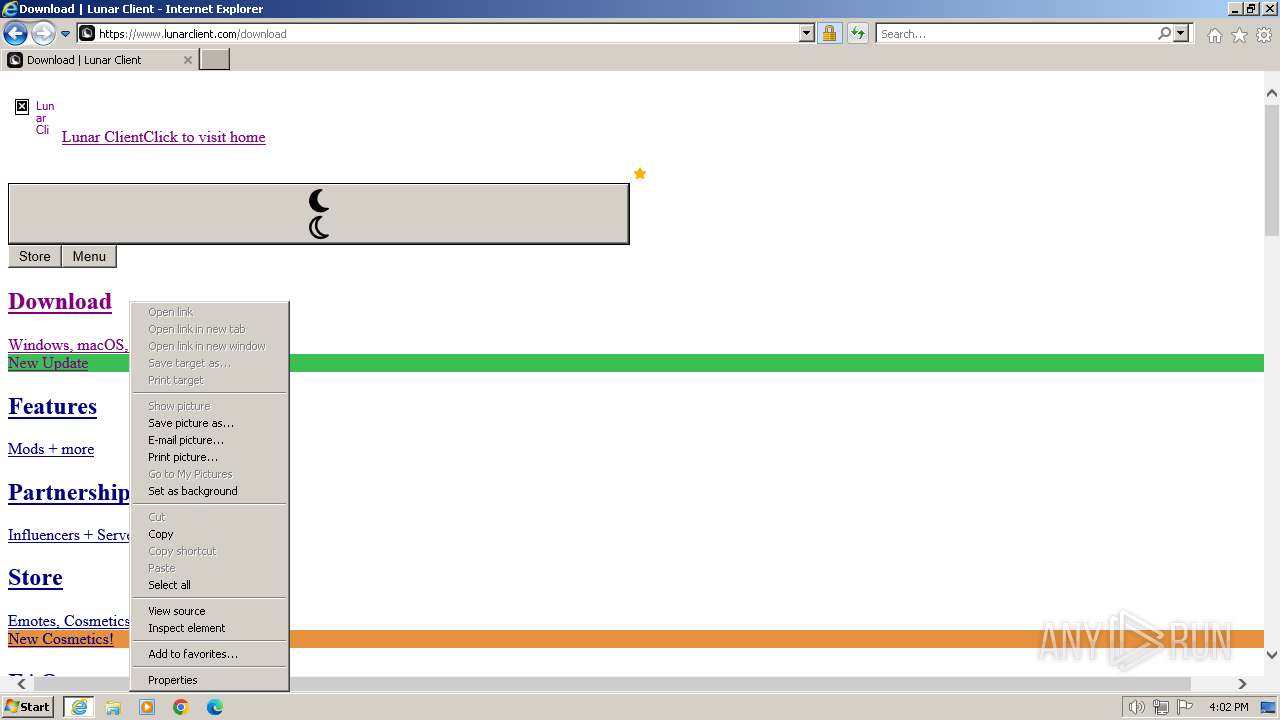
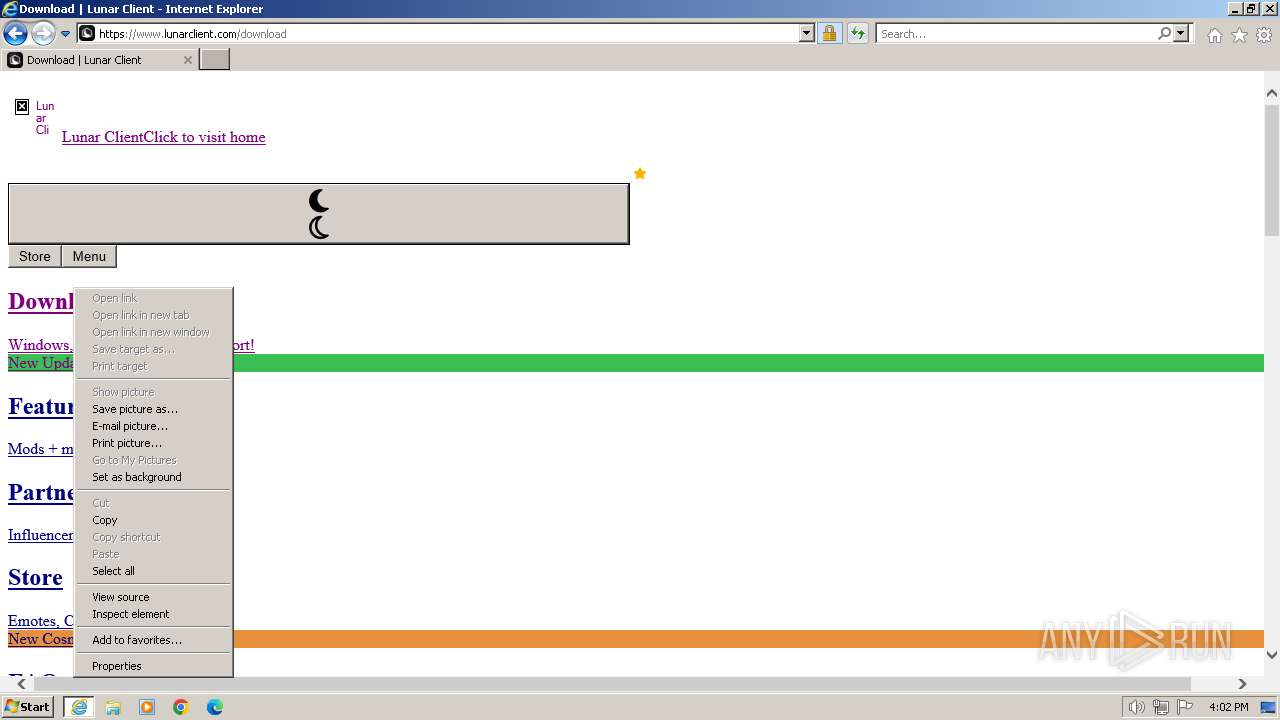
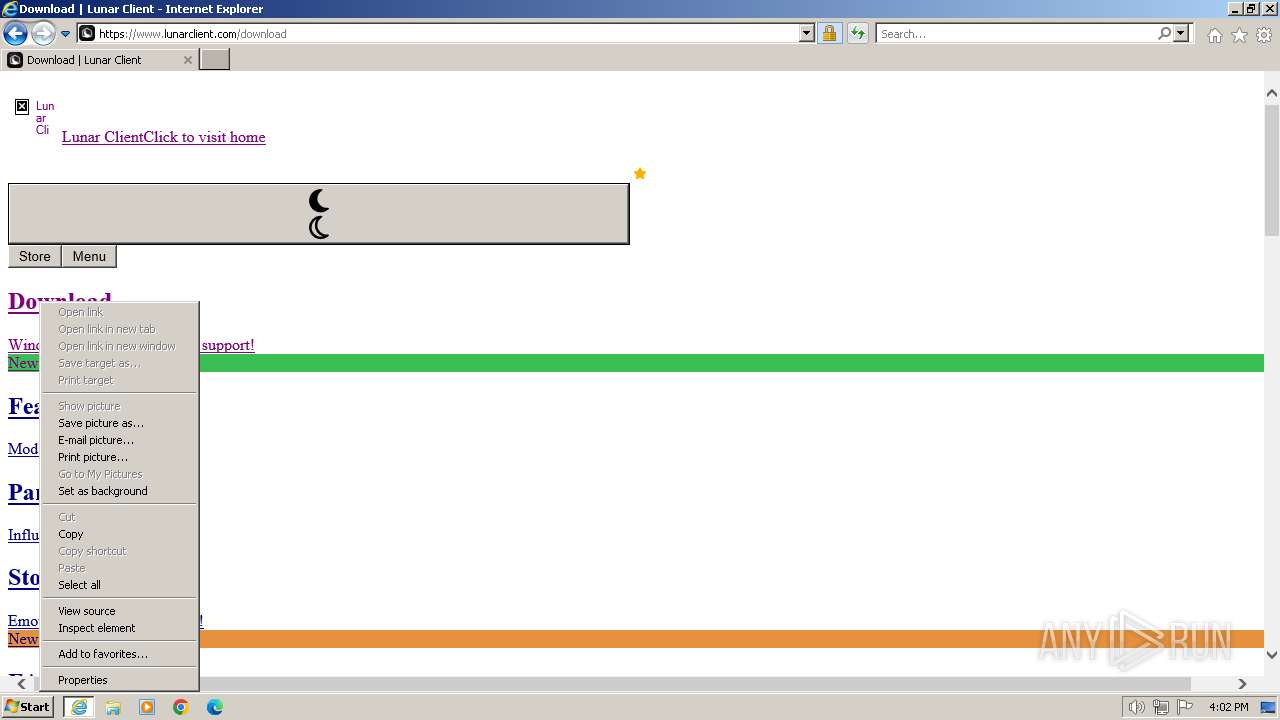
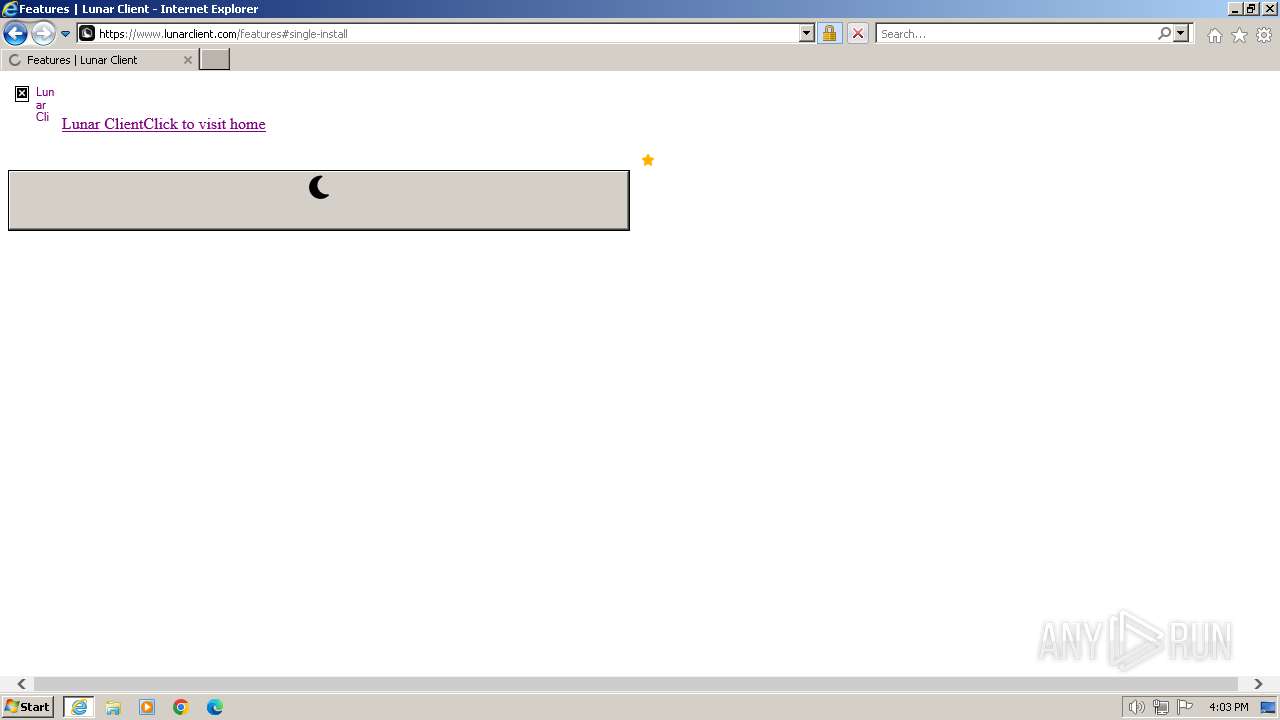
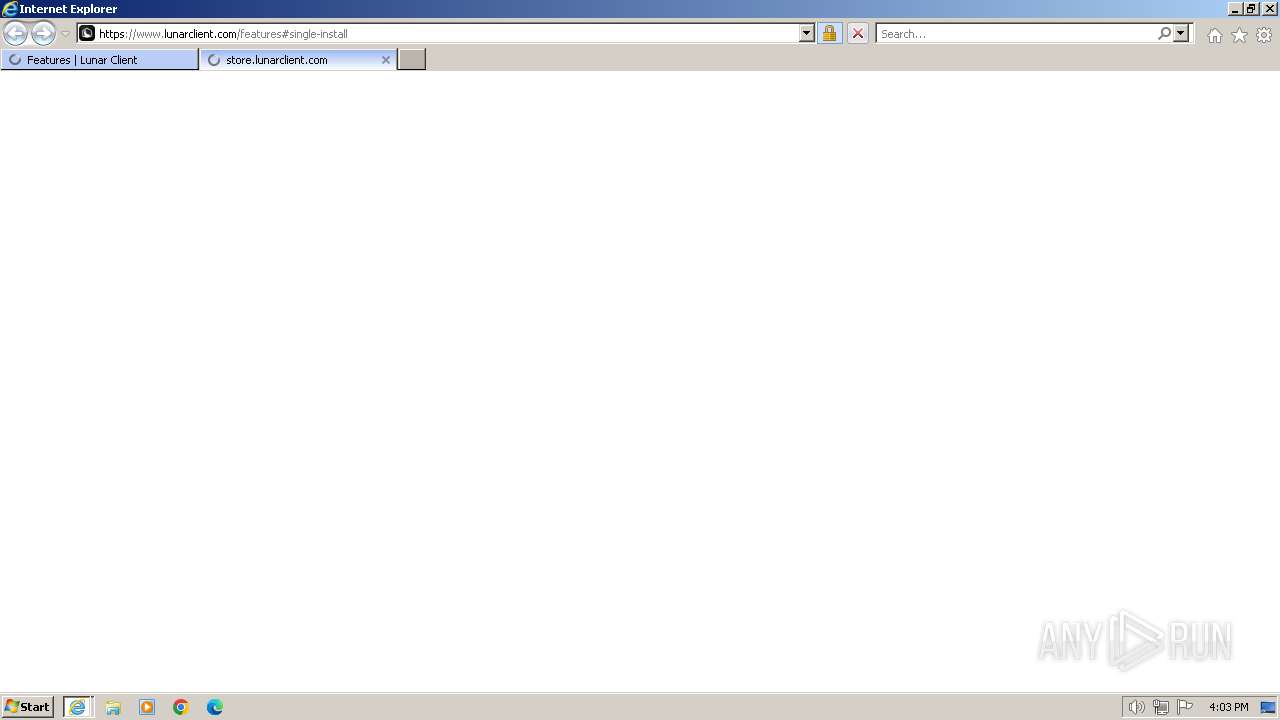
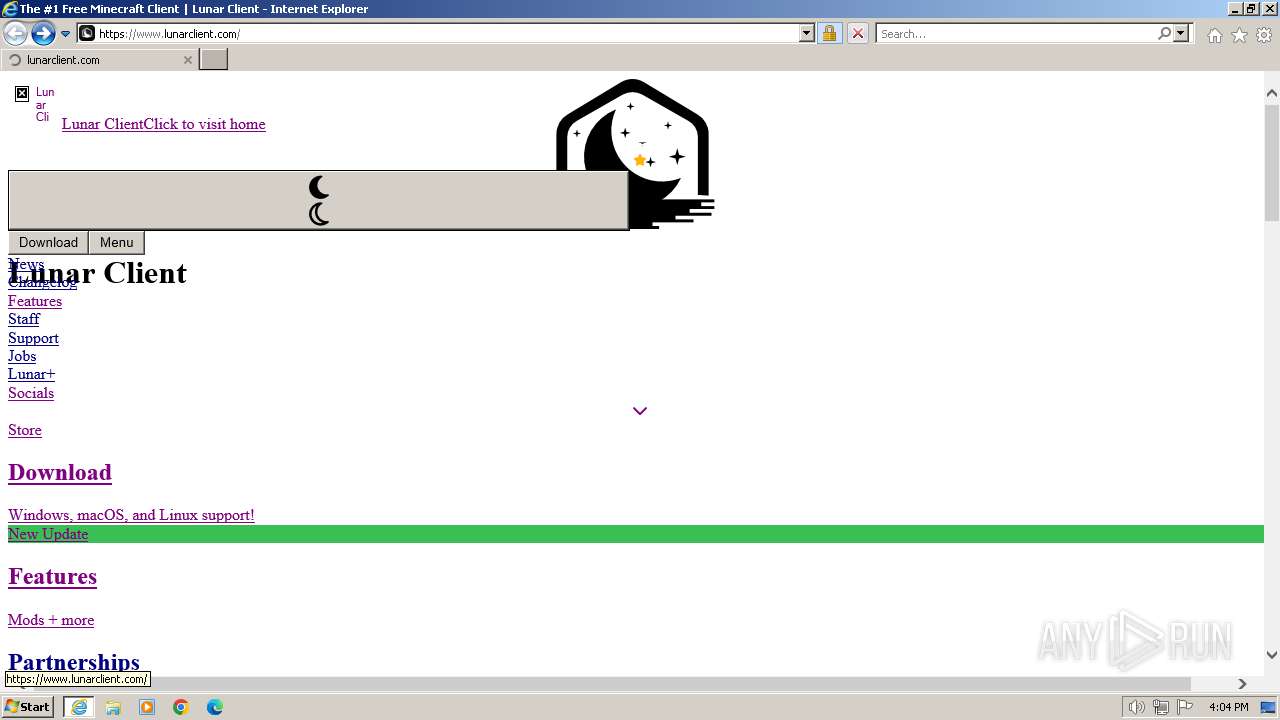
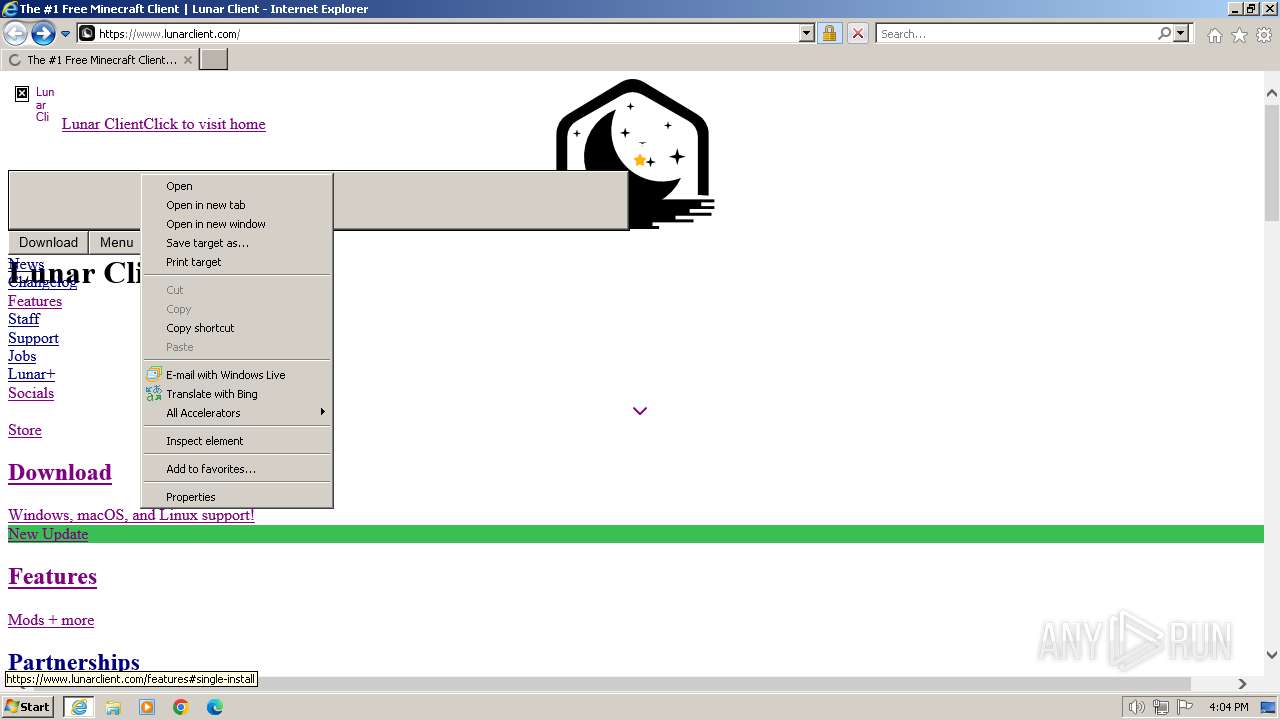
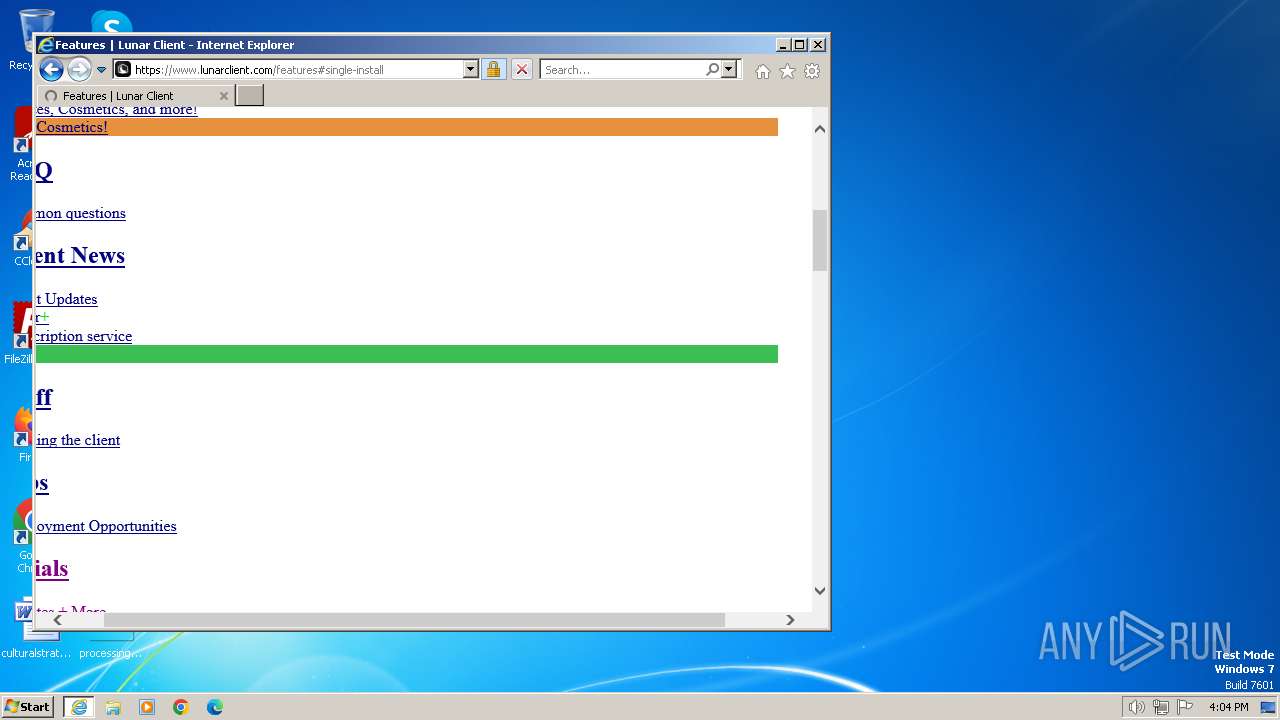
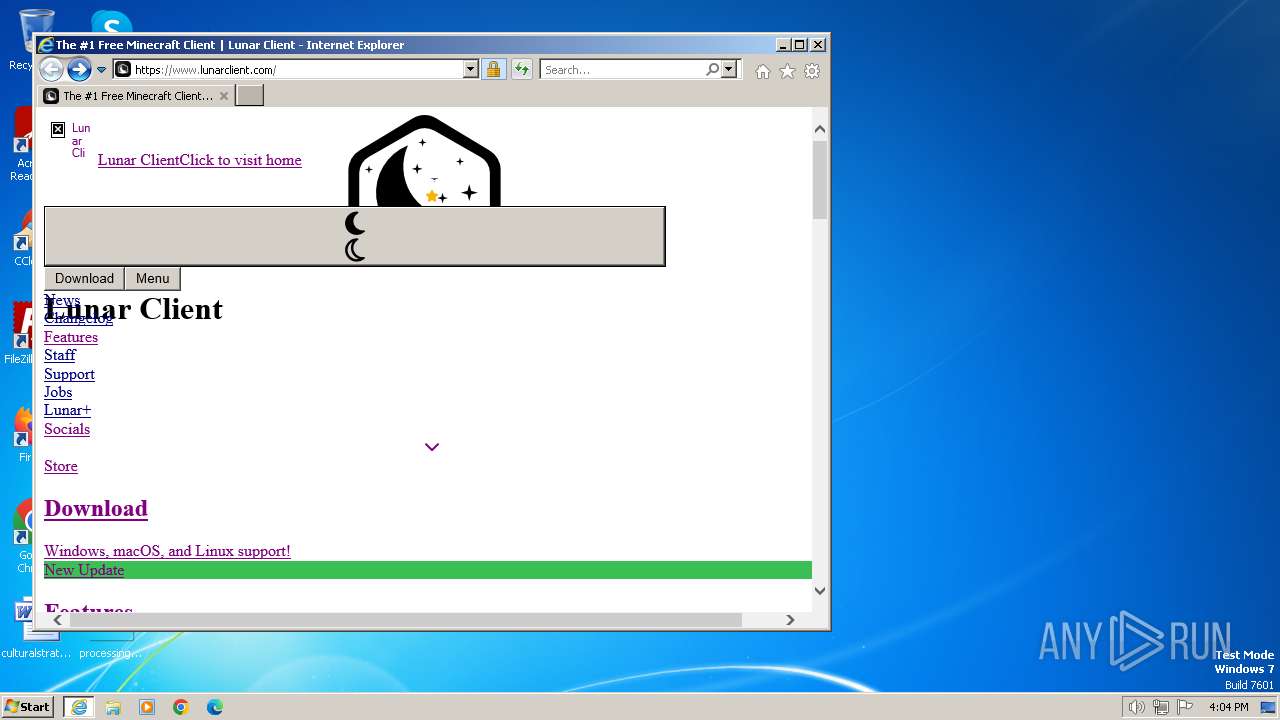
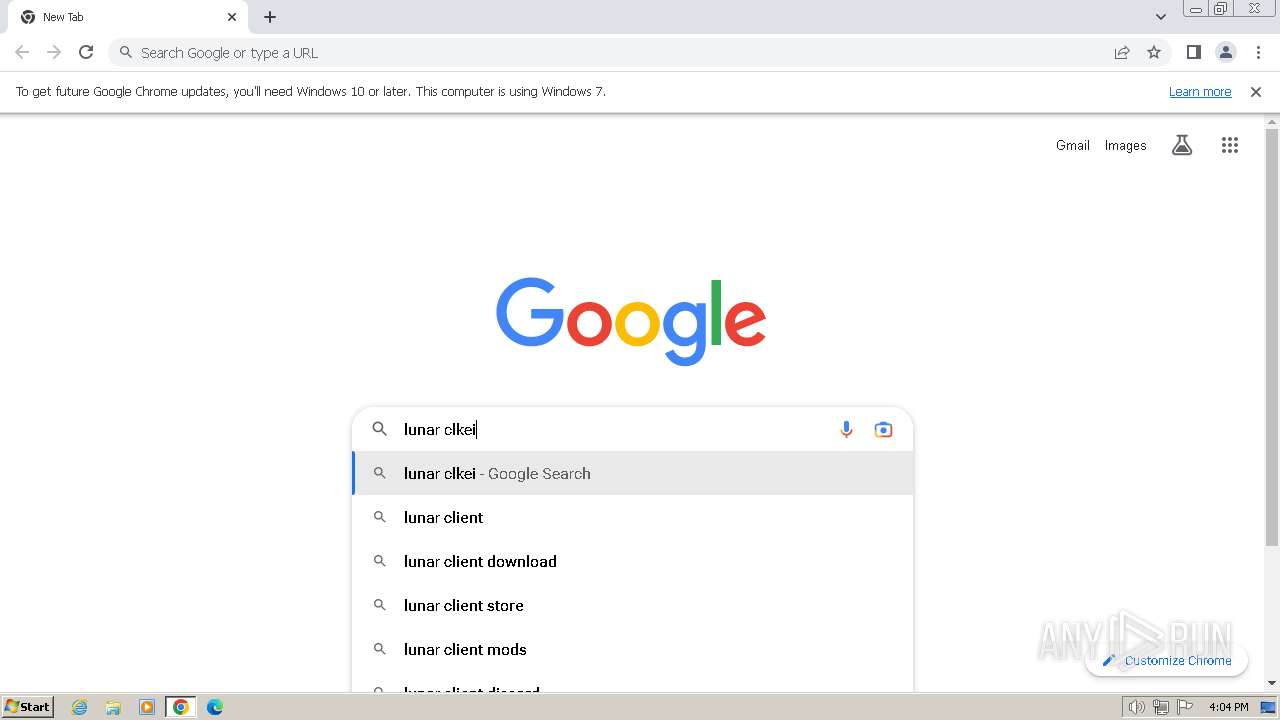
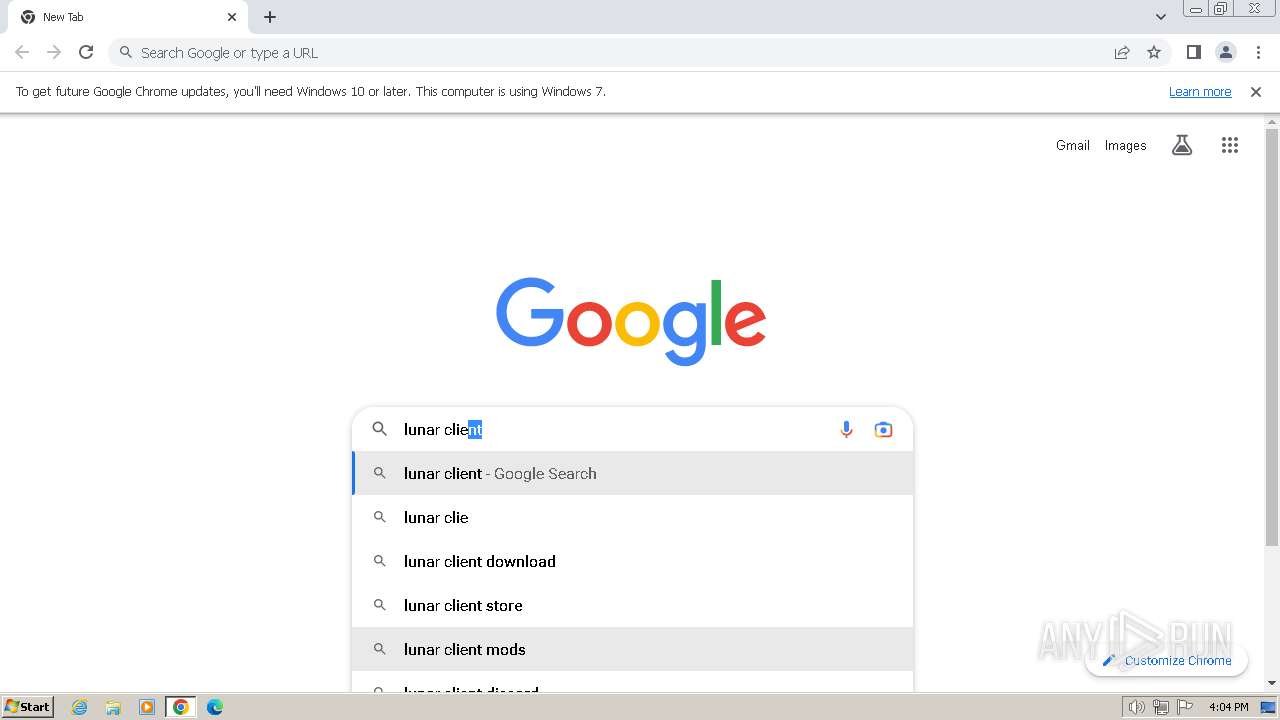
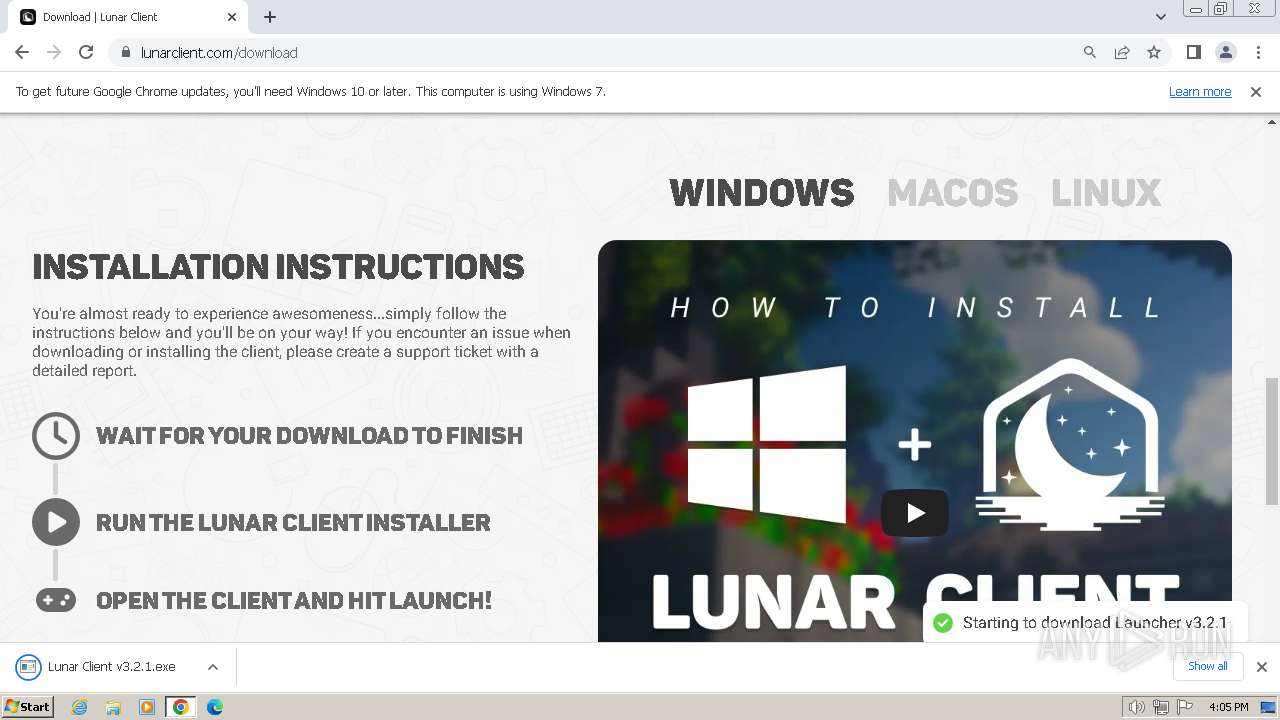
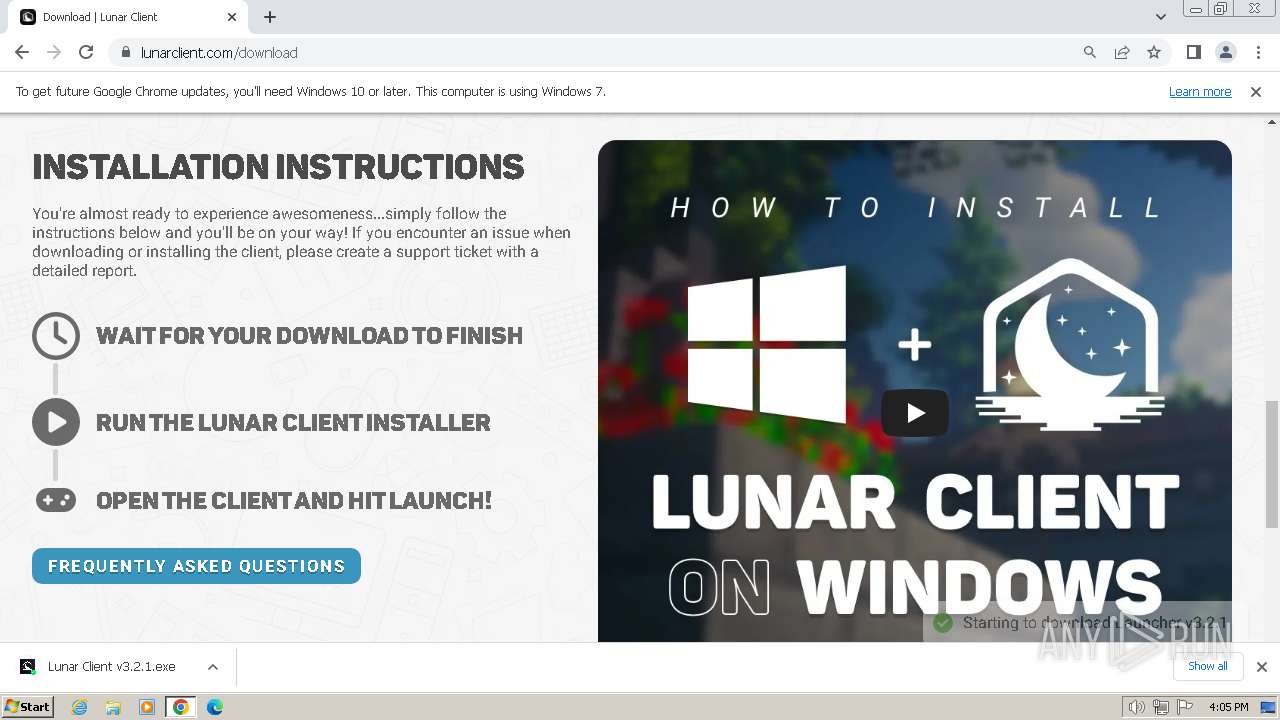
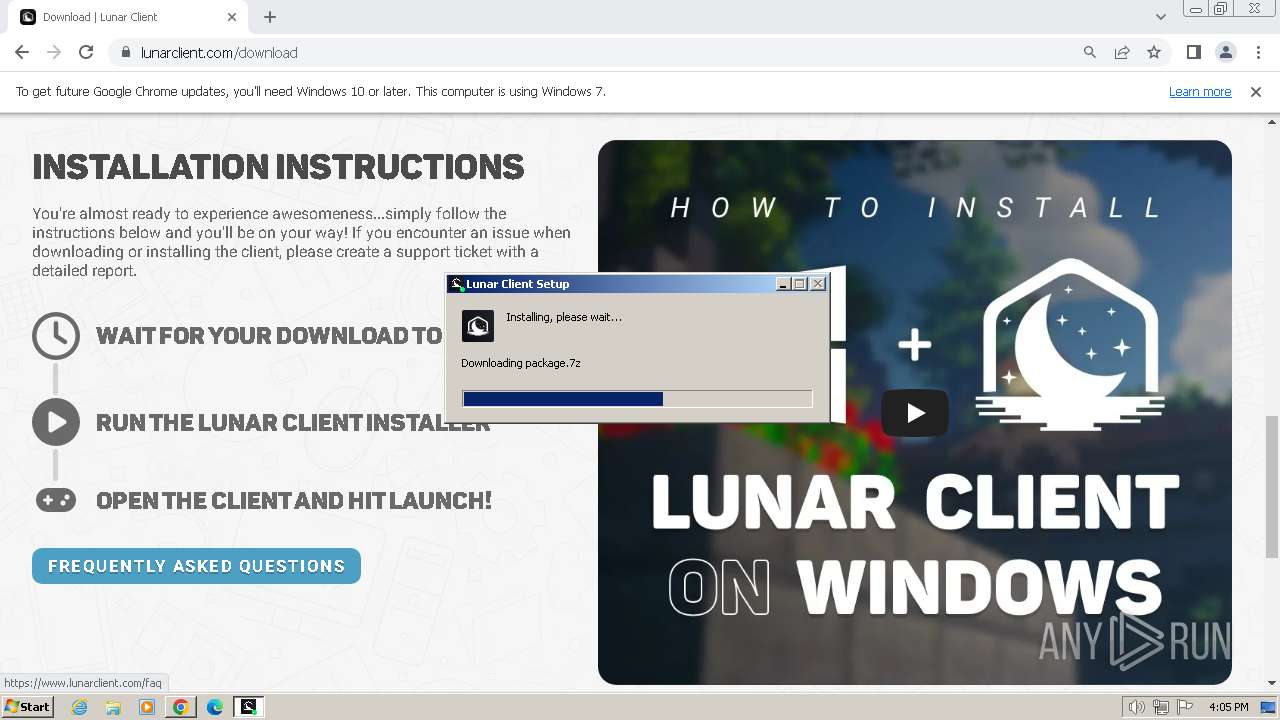
| URL: | https://www.lunarclient.com/ |
| Full analysis: | https://app.any.run/tasks/3db36c34-40ae-4a90-801a-9efc63a42bb3 |
| Verdict: | Malicious activity |
| Analysis date: | January 30, 2024, 16:00:42 |
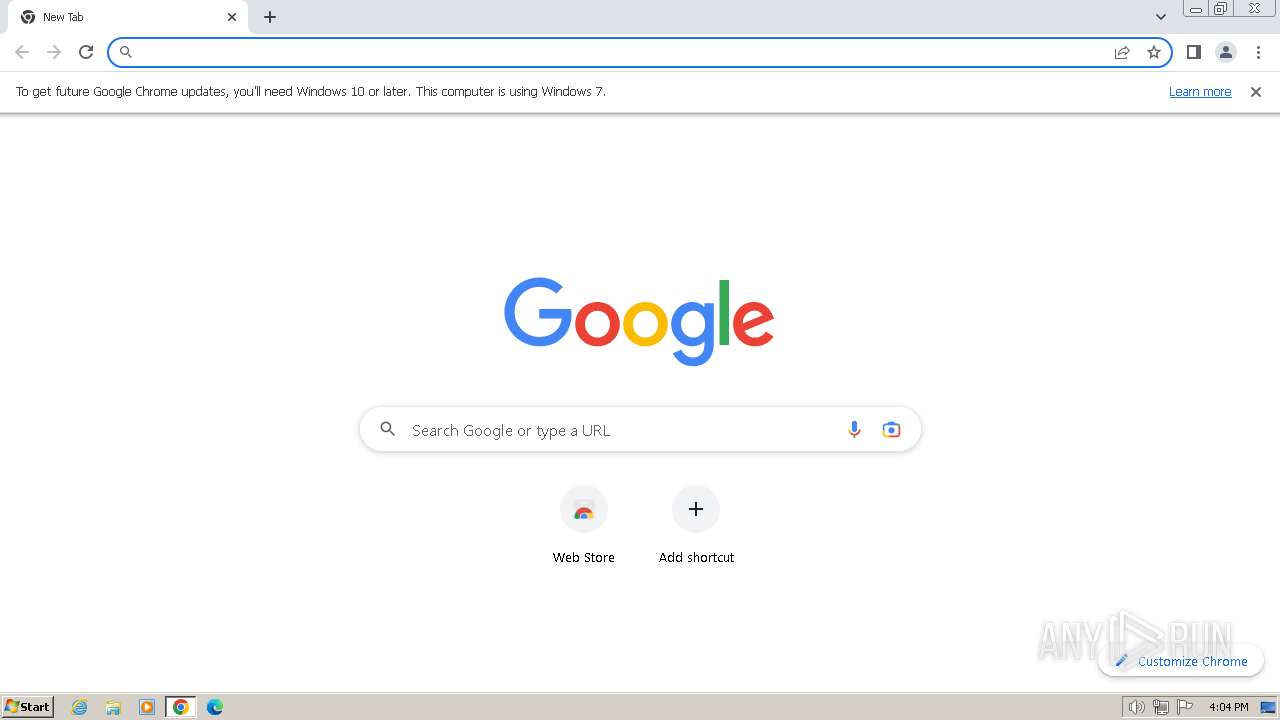
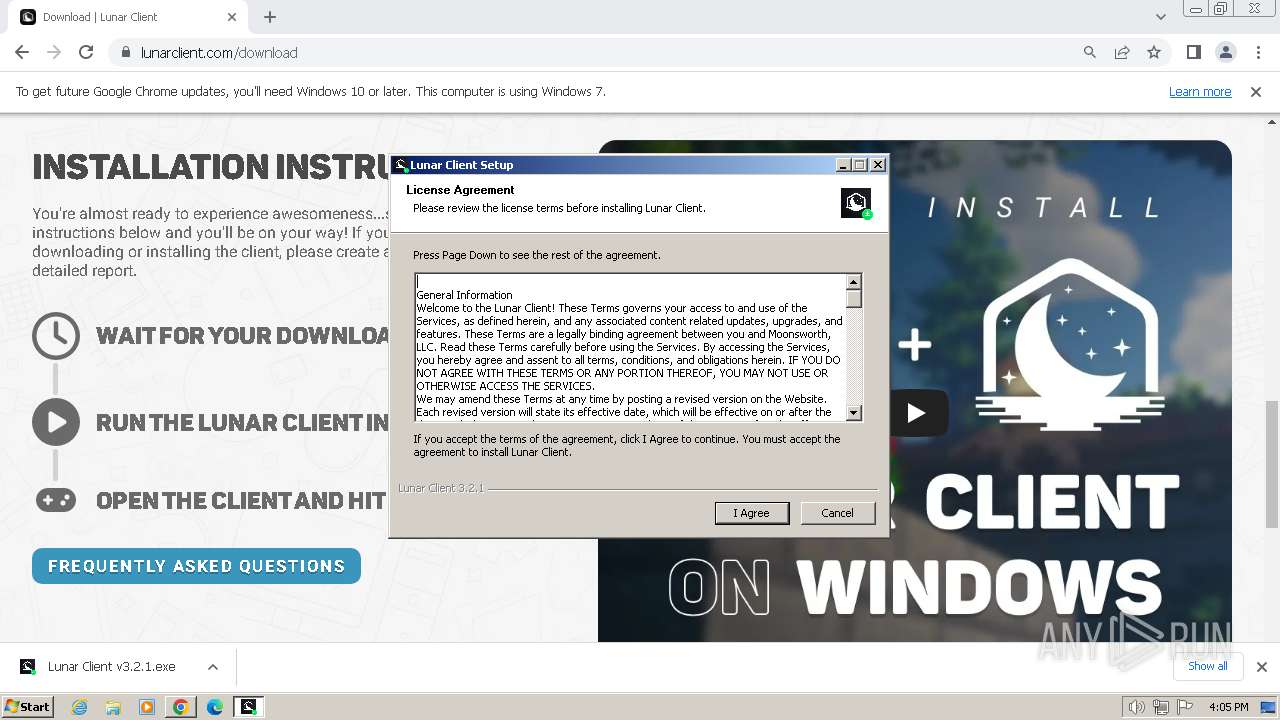
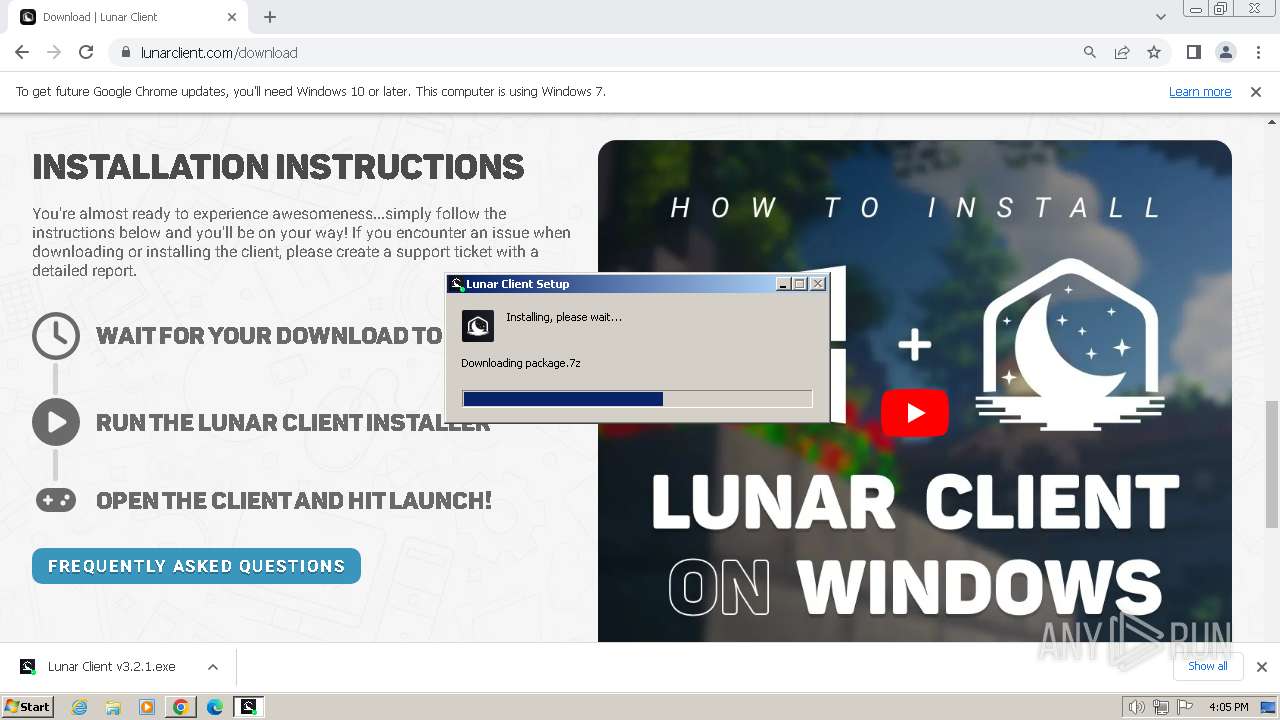
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5C6FABFA41871970A9117D833ECDE344 |
| SHA1: | 9FF51B3F5DFC5209AFC93231F59645D2F27807CF |
| SHA256: | 34E08E7A942C69ABAFC08AD7DB9182EB77D4F3B2E7311DF4FC56A1E33D3BF748 |
| SSDEEP: | 3:N8DSLUcukK:2OLRuD |
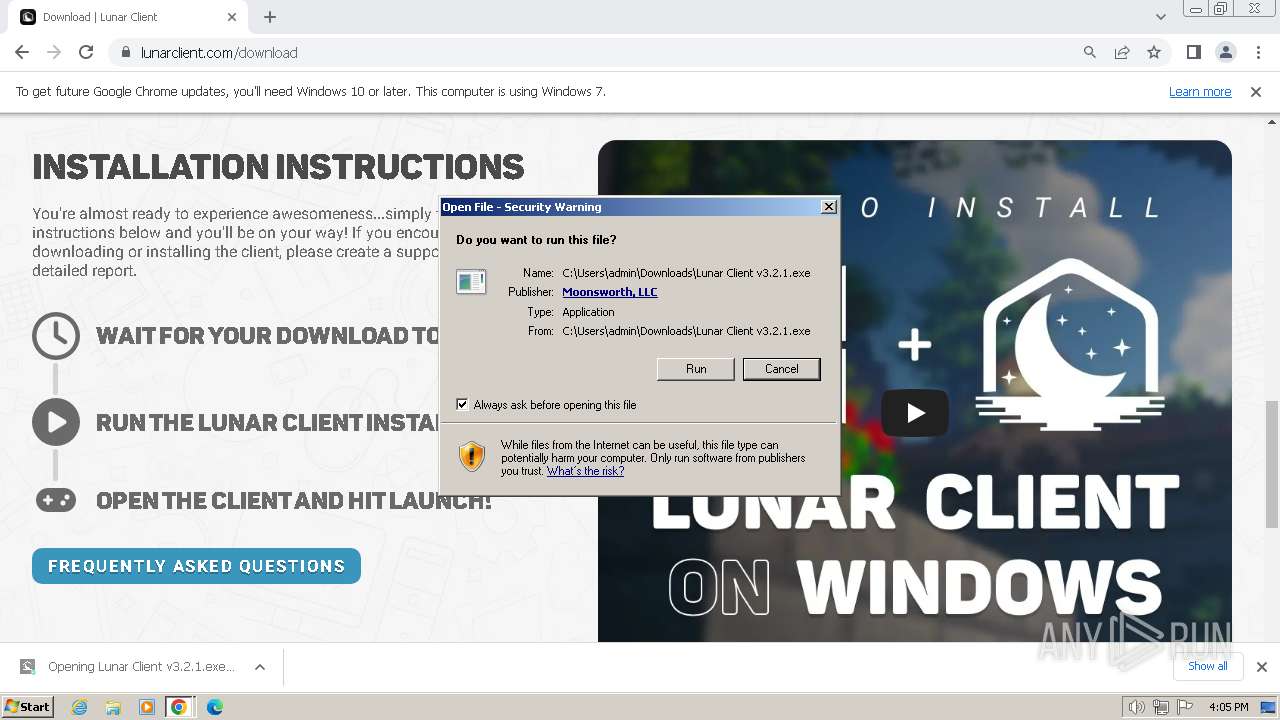
MALICIOUS
Drops the executable file immediately after the start
- Lunar Client v3.2.1.exe (PID: 3524)
SUSPICIOUS
The process creates files with name similar to system file names
- Lunar Client v3.2.1.exe (PID: 3524)
Malware-specific behavior (creating "System.dll" in Temp)
- Lunar Client v3.2.1.exe (PID: 3524)
Starts application with an unusual extension
- Lunar Client v3.2.1.exe (PID: 3524)
Executable content was dropped or overwritten
- Lunar Client v3.2.1.exe (PID: 3524)
Get information on the list of running processes
- Lunar Client v3.2.1.exe (PID: 3524)
- ns498F.tmp (PID: 3924)
- cmd.exe (PID: 3356)
Starts CMD.EXE for commands execution
- ns498F.tmp (PID: 3924)
Reads the Internet Settings
- Lunar Client v3.2.1.exe (PID: 3524)
Reads security settings of Internet Explorer
- Lunar Client v3.2.1.exe (PID: 3524)
Checks Windows Trust Settings
- Lunar Client v3.2.1.exe (PID: 3524)
Reads settings of System Certificates
- Lunar Client v3.2.1.exe (PID: 3524)
INFO
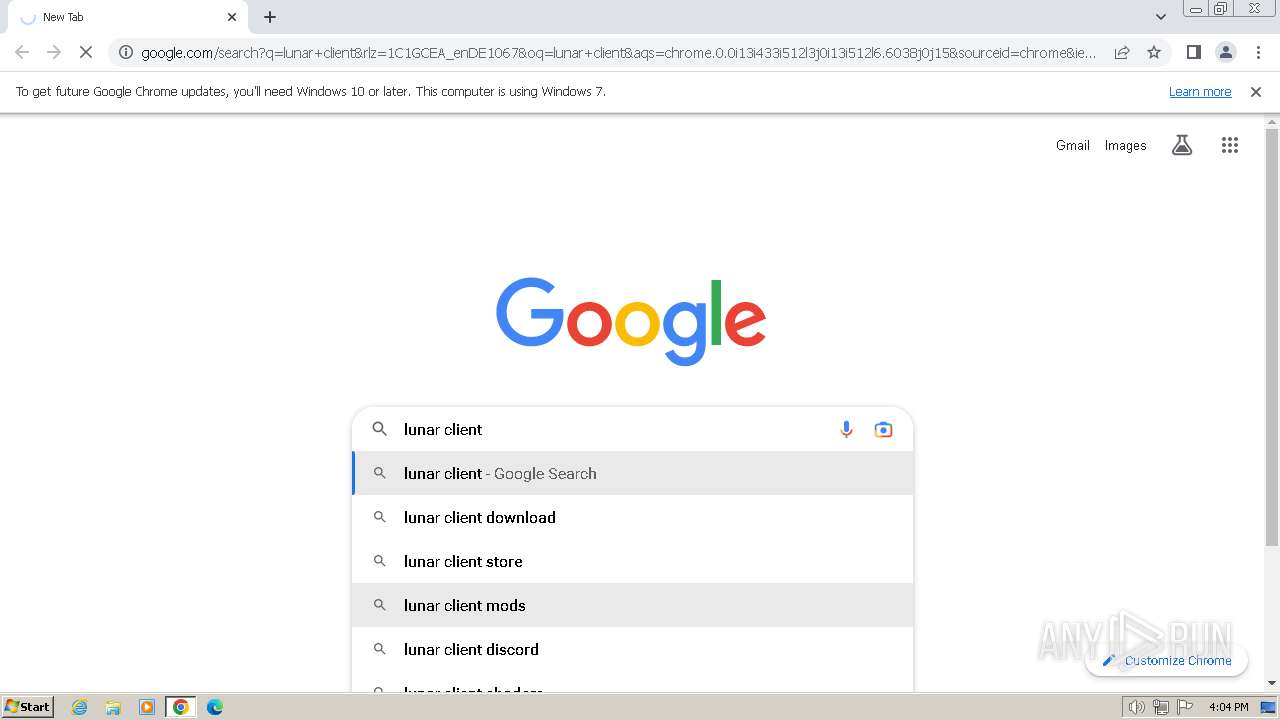
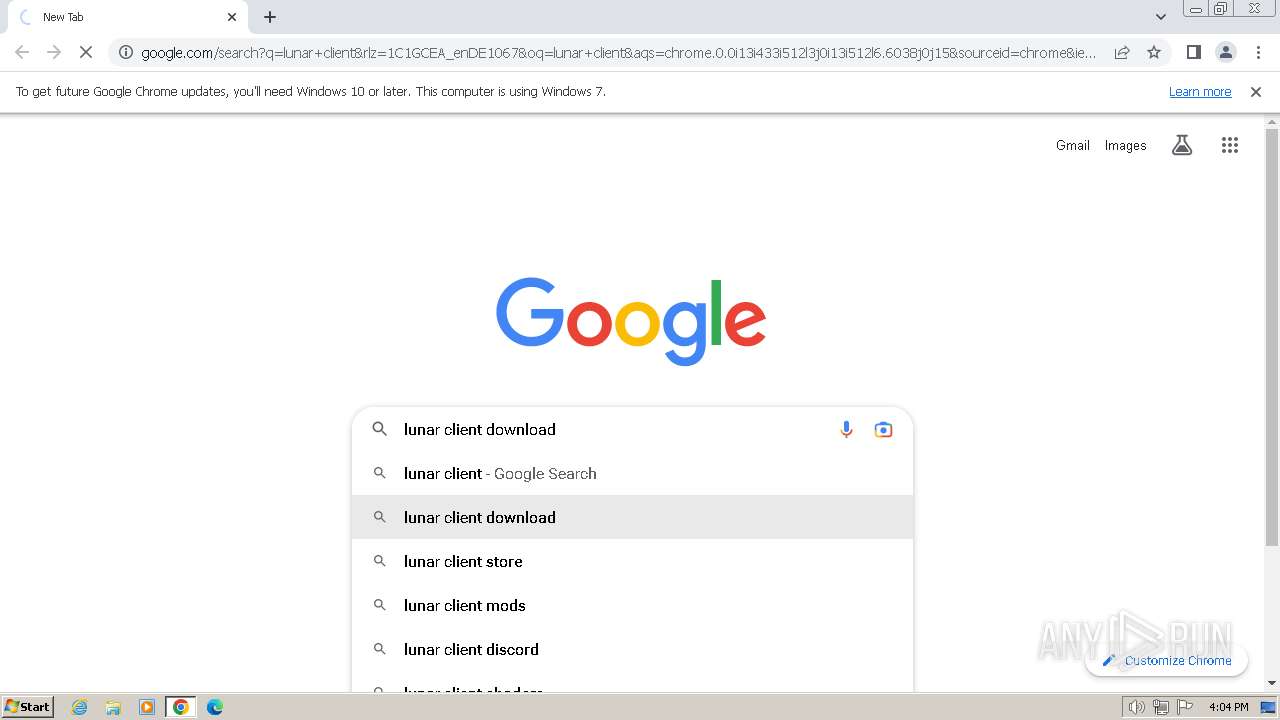
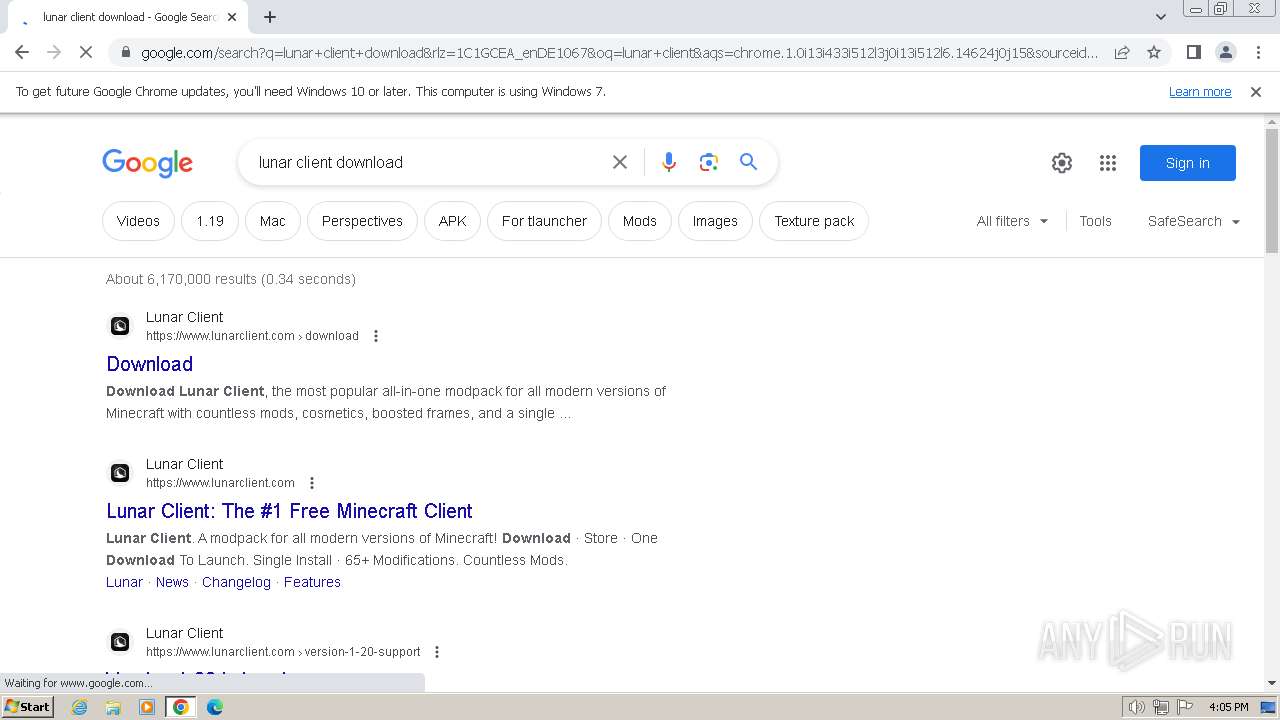
Application launched itself
- chrome.exe (PID: 2444)
- iexplore.exe (PID: 1380)
Manual execution by a user
- chrome.exe (PID: 2444)
- wmpnscfg.exe (PID: 2368)
Reads the computer name
- wmpnscfg.exe (PID: 2368)
- Lunar Client v3.2.1.exe (PID: 3524)
Checks supported languages
- wmpnscfg.exe (PID: 2368)
- Lunar Client v3.2.1.exe (PID: 3524)
- ns498F.tmp (PID: 3924)
Executable content was dropped or overwritten
- chrome.exe (PID: 2444)
- chrome.exe (PID: 2896)
Drops the executable file immediately after the start
- chrome.exe (PID: 2444)
- chrome.exe (PID: 2896)
The process uses the downloaded file
- chrome.exe (PID: 3116)
- chrome.exe (PID: 2444)
Create files in a temporary directory
- Lunar Client v3.2.1.exe (PID: 3524)
Checks proxy server information
- Lunar Client v3.2.1.exe (PID: 3524)
Creates files or folders in the user directory
- Lunar Client v3.2.1.exe (PID: 3524)
Reads the machine GUID from the registry
- Lunar Client v3.2.1.exe (PID: 3524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
77
Monitored processes
32
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3908 --field-trial-handle=1152,i,18305118105074455172,16560477874726268200,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4332 --field-trial-handle=1152,i,18305118105074455172,16560477874726268200,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3792 --field-trial-handle=1152,i,18305118105074455172,16560477874726268200,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3400 --field-trial-handle=1152,i,18305118105074455172,16560477874726268200,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.lunarclient.com/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3068 --field-trial-handle=1152,i,18305118105074455172,16560477874726268200,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4032 --field-trial-handle=1152,i,18305118105074455172,16560477874726268200,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4308 --field-trial-handle=1152,i,18305118105074455172,16560477874726268200,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2136 | tasklist /FI "USERNAME eq admin" /FI "IMAGENAME eq Lunar Client.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=2264 --field-trial-handle=1152,i,18305118105074455172,16560477874726268200,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
39 125
Read events
38 886
Write events
230
Delete events
9
Modification events
| (PID) Process: | (1380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1380) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
14
Suspicious files
167
Text files
176
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar339B.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab339A.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:7FB11028857BDE32A3FF6C06AC33919B | SHA256:B0209357D698F5F65E93E5695A7102FAF7A18CC4688722851E1449BAADB96EF2 | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:521E499E2176372AA3FDA7B0847F2583 | SHA256:11E5539F3959D6E7BC22F8E8A107DC229FC5C5FAE5DD772E881A1863372B3A7A | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:DEC6BBE308EB44937F77160A25EE32DB | SHA256:68A71DE28F488586C2B169F4652347E0A1FD632D48A6D6725393607BFA18BC7E | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:48AFCE238E29512480D3FE0E7CFD0350 | SHA256:AD1B30DFBF35B4EAE6B186D94C9C79BFA80B5779A4F334E1E399C7E678C9D438 | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\webpack-16788aae44bf6aec[1].js | text | |
MD5:1CE1B86DAFC734FFC6C8A6CFA5F1C45A | SHA256:F9A9E6B98B4F8DD2FFCD5677DCF8BA23D614FBED7644C6EB00A973C4DDEA2512 | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab3398.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
138
DNS requests
109
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3988 | iexplore.exe | GET | 304 | 173.222.108.243:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?58b09451c6662268 | unknown | — | — | unknown |
3988 | iexplore.exe | GET | 304 | 173.222.108.243:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?83c23cd8118a42bc | unknown | — | — | unknown |
3988 | iexplore.exe | GET | 200 | 173.222.108.243:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d7a4c83e7f191cf0 | unknown | compressed | 65.2 Kb | unknown |
3988 | iexplore.exe | GET | 200 | 173.222.108.243:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?5b36c47564b40877 | unknown | compressed | 65.2 Kb | unknown |
3988 | iexplore.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
3988 | iexplore.exe | GET | 200 | 2.19.245.44:80 | http://x2.c.lencr.org/ | unknown | binary | 300 b | unknown |
3988 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
3988 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
3988 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
1380 | iexplore.exe | GET | 304 | 173.222.108.210:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4c4bae6a1643aa04 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3988 | iexplore.exe | 104.18.13.46:443 | www.lunarclient.com | CLOUDFLARENET | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3988 | iexplore.exe | 173.222.108.243:80 | ctldl.windowsupdate.com | Akamai International B.V. | CH | unknown |
3988 | iexplore.exe | 2.23.197.184:80 | x1.c.lencr.org | CW Vodafone Group PLC | GB | unknown |
3988 | iexplore.exe | 2.19.245.44:80 | x2.c.lencr.org | AKAMAI-AS | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3988 | iexplore.exe | 104.18.30.194:443 | skins.mcstats.com | CLOUDFLARENET | — | unknown |
3988 | iexplore.exe | 172.217.16.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3988 | iexplore.exe | 104.18.29.96:443 | cmsassets.lunarclientcdn.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.lunarclient.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
skins.mcstats.com |
| unknown |
ocsp.pki.goog |
| whitelisted |
cmsassets.lunarclientcdn.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
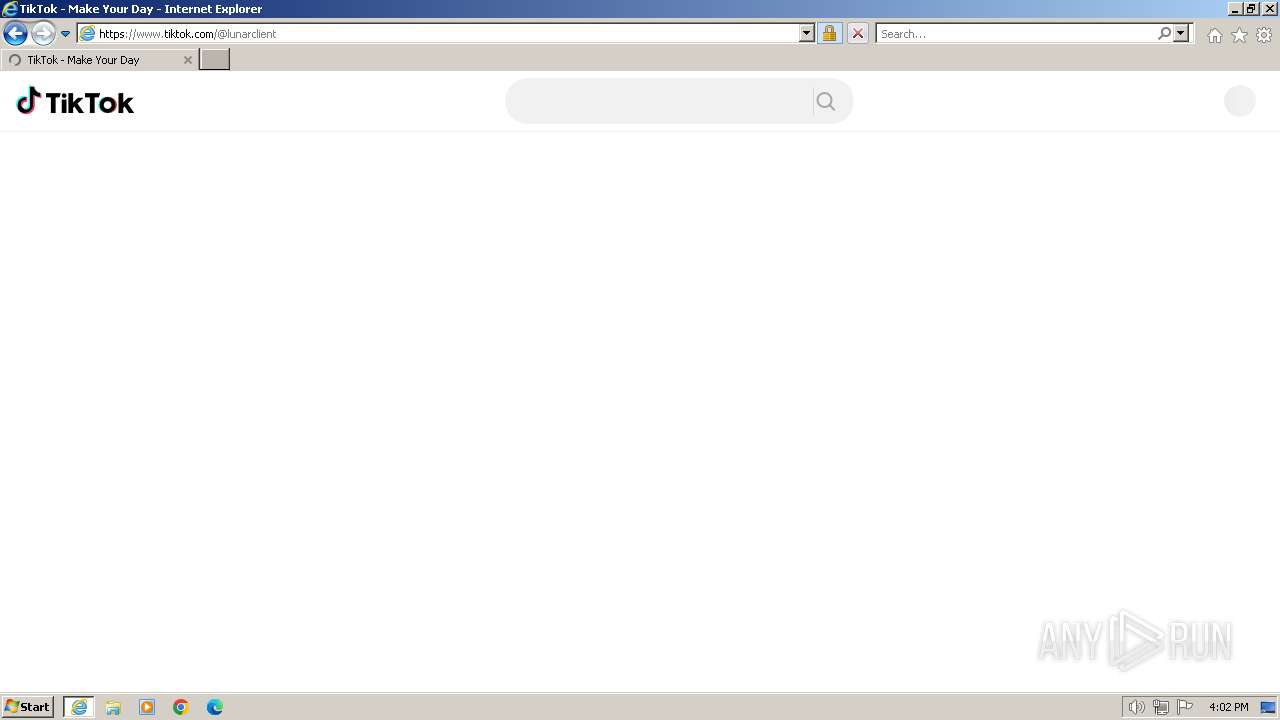
Threats
PID | Process | Class | Message |
|---|---|---|---|
3988 | iexplore.exe | Potential Corporate Privacy Violation | AV POLICY Observed TikTok Domain in TLS SNI (tiktok.com) |