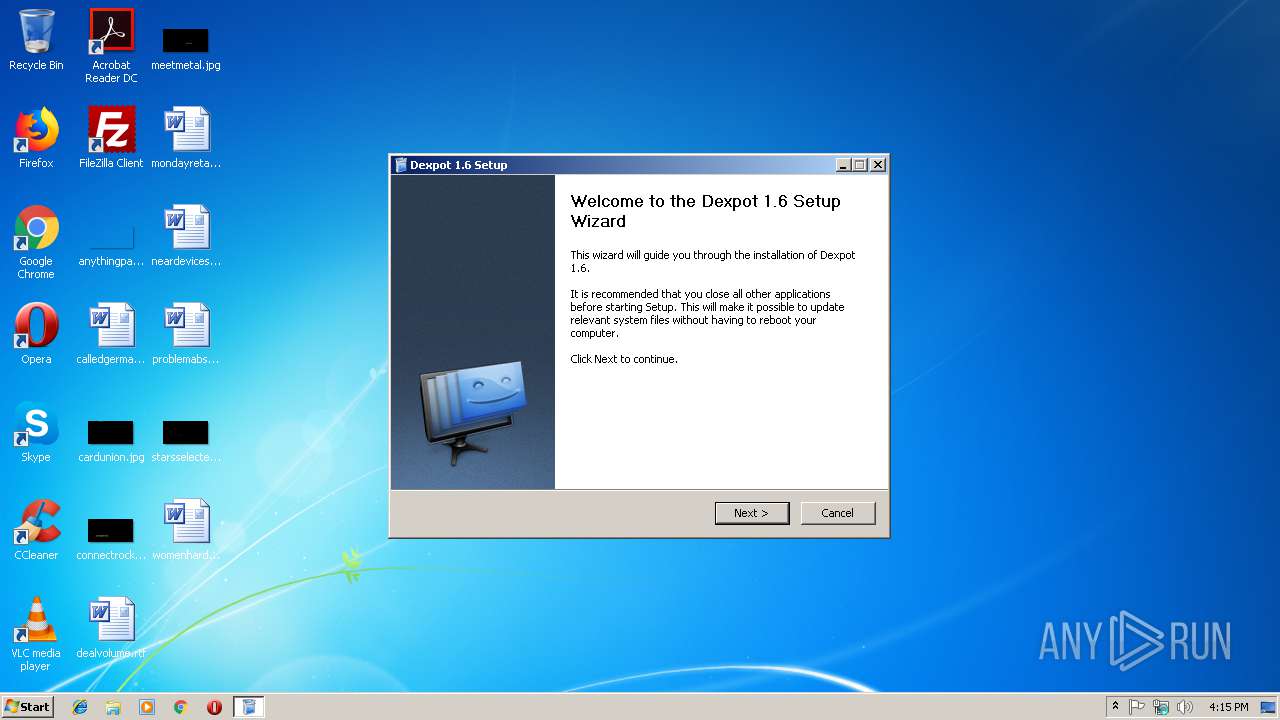
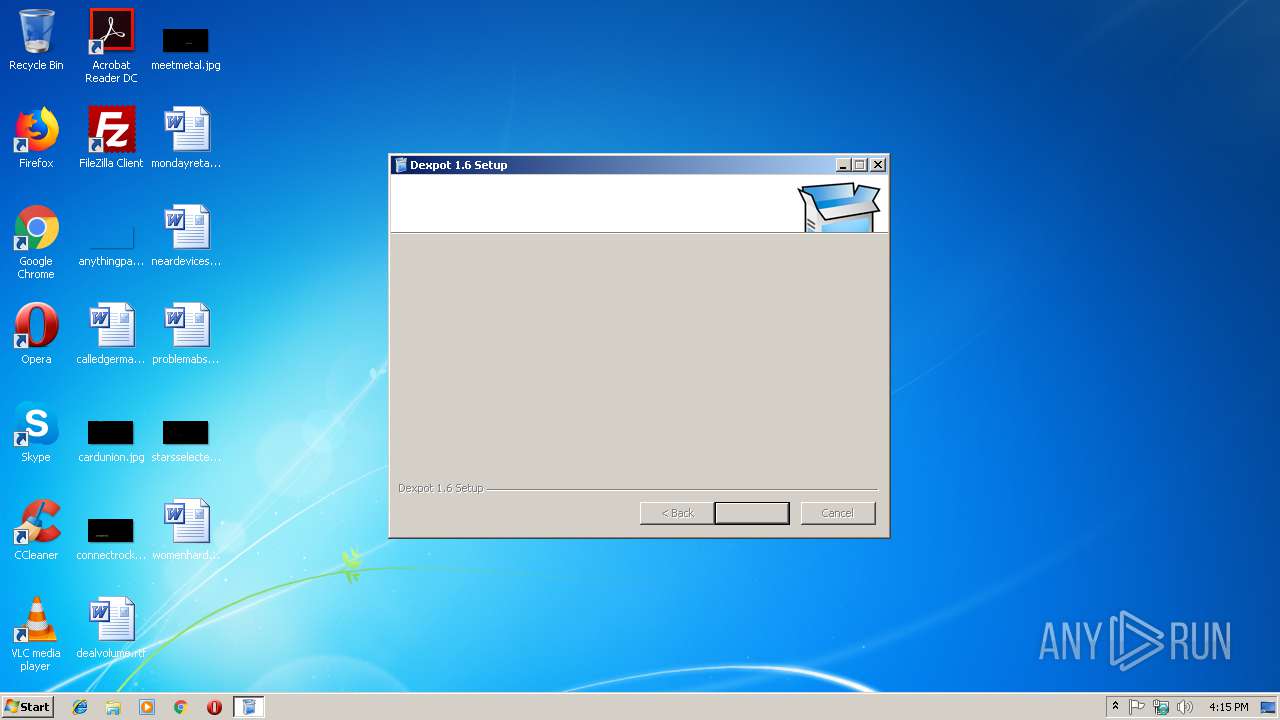
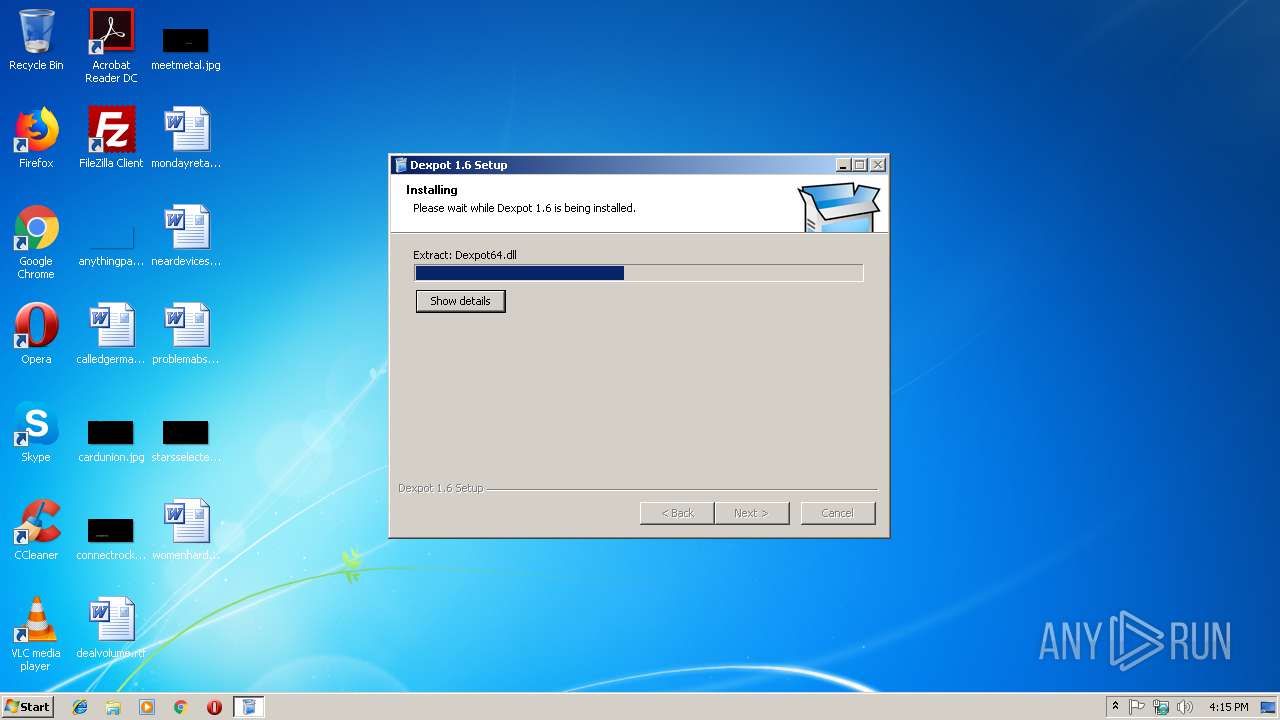
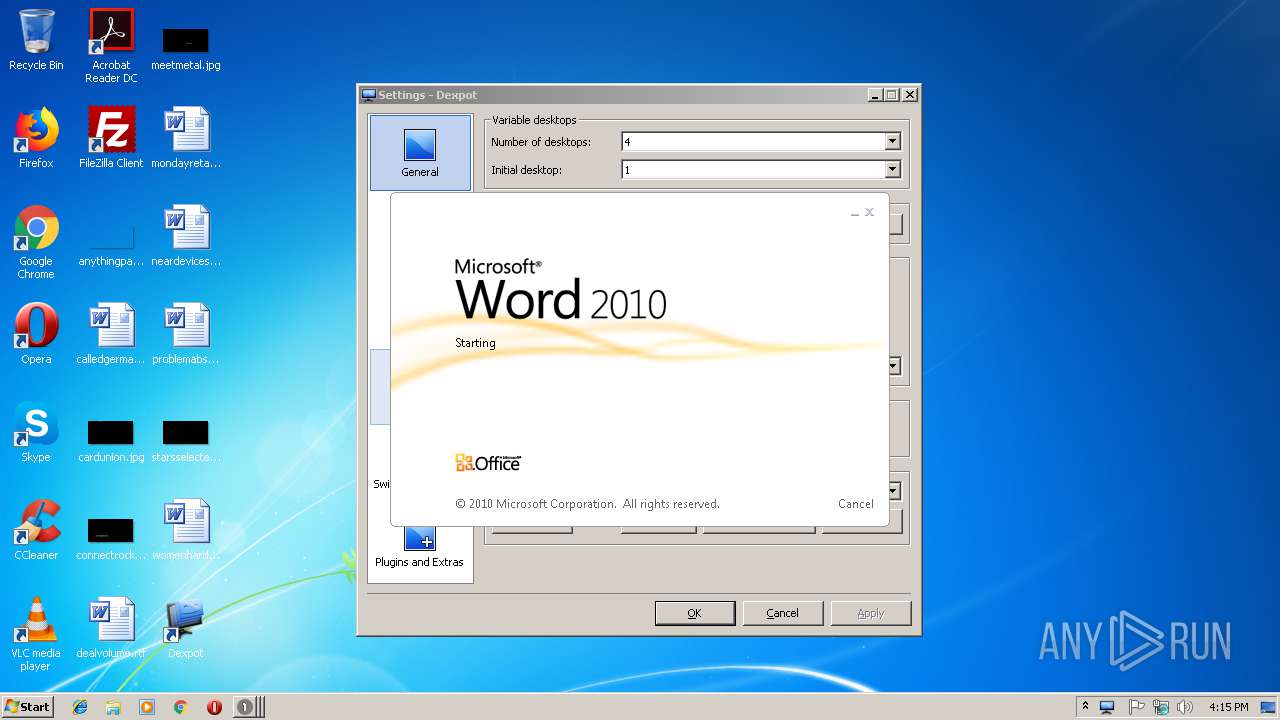
| File name: | Dexpot v1614 r2439.exe |
| Full analysis: | https://app.any.run/tasks/e27919a8-e1cf-4846-8899-38b4ce1baf85 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2018, 16:14:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 77D59E8AFFCDC1355883DA895CD32B35 |
| SHA1: | B37BE0AAB31A8EE5B370333F08A76C50A3DEC31E |
| SHA256: | 34DE9036D0D16EF10129962BE5EBB4F6D001D1FF6677C0AEC6FF530322EA099C |
| SSDEEP: | 98304:LUeOU72+G79pndMEvVp89qzk900Oz+k6+OVCXOmPnaOoIcQvLThoc0sJ:1OU7U7j+EvVcqzk900W6BsXPaOoULThL |
MALICIOUS
Loads dropped or rewritten executable
- Dexpot v1614 r2439.exe (PID: 3156)
- SevenDex.exe (PID: 3188)
- dexpot.exe (PID: 2212)
- DllHost.exe (PID: 2412)
- explorer.exe (PID: 2028)
- dwm.exe (PID: 1968)
- dexpot.exe (PID: 3740)
- WINWORD.EXE (PID: 1520)
- DllHost.exe (PID: 3092)
- RunDll32.exe (PID: 3128)
- Dexpot v1614 r2439.exe (PID: 2976)
Application was dropped or rewritten from another process
- dexpot.exe (PID: 2212)
- dexpot.exe (PID: 3740)
- SevenDex.exe (PID: 3188)
SUSPICIOUS
Application launched itself
- Dexpot v1614 r2439.exe (PID: 3156)
Executable content was dropped or overwritten
- Dexpot v1614 r2439.exe (PID: 3156)
- Dexpot v1614 r2439.exe (PID: 2976)
Modifies the open verb of a shell class
- Dexpot v1614 r2439.exe (PID: 2976)
Creates files in the user directory
- Dexpot v1614 r2439.exe (PID: 3156)
- dexpot.exe (PID: 2212)
- SevenDex.exe (PID: 3188)
- explorer.exe (PID: 2028)
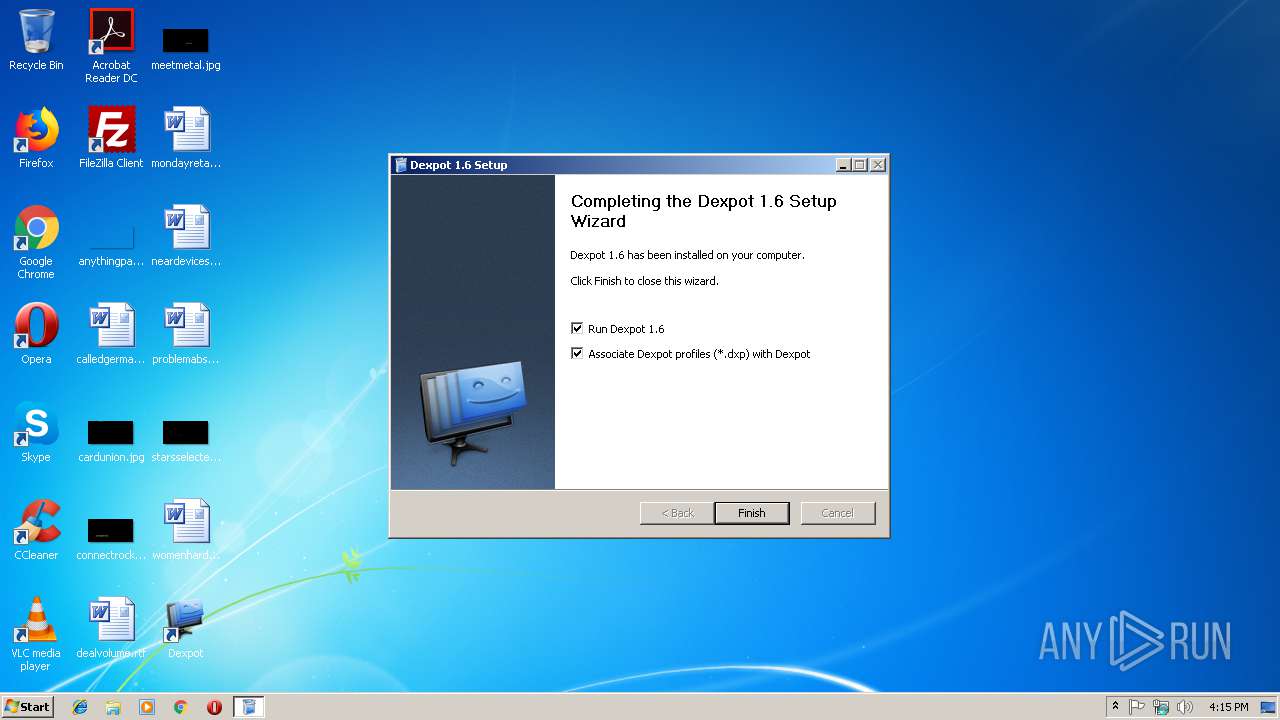
Creates a software uninstall entry
- Dexpot v1614 r2439.exe (PID: 3156)
Reads Internet Cache Settings
- explorer.exe (PID: 2028)
Creates files in the program directory
- Dexpot v1614 r2439.exe (PID: 2976)
Uses RUNDLL32.EXE to load library
- Dexpot v1614 r2439.exe (PID: 2976)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 2028)
Creates files in the user directory
- WINWORD.EXE (PID: 1520)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.6.14.0 |
| ProductVersionNumber: | 1.6.14.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
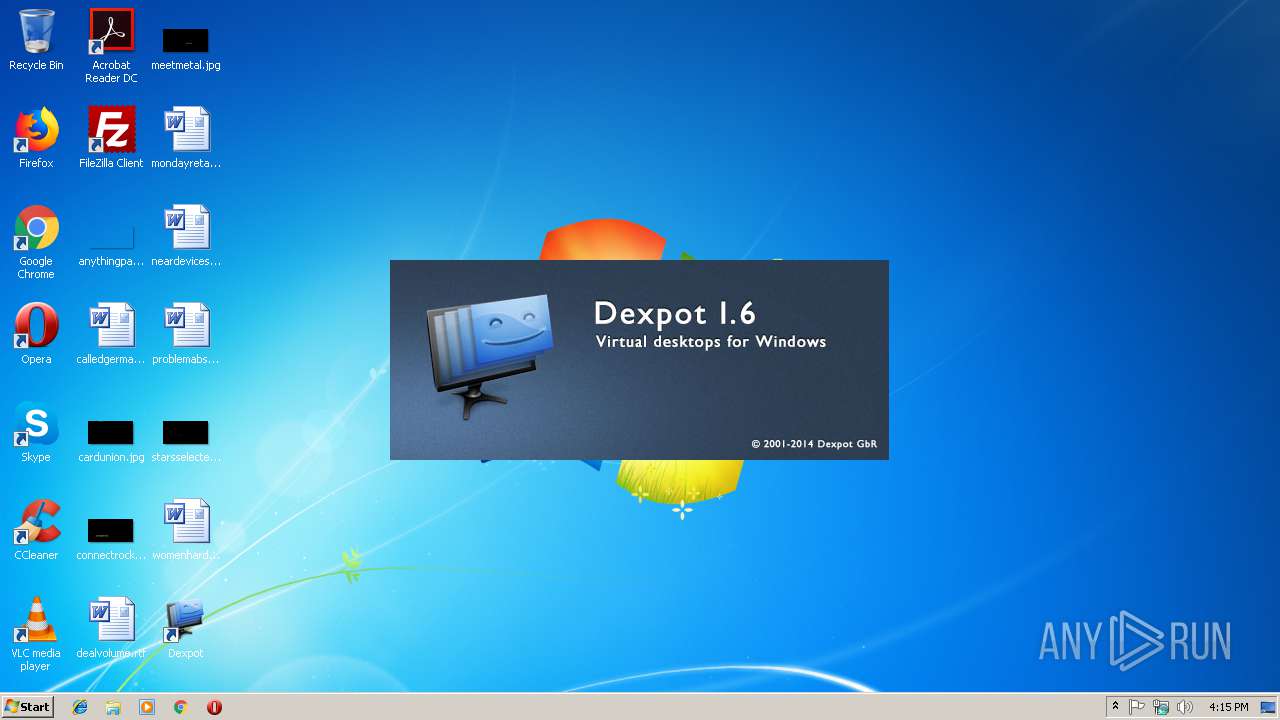
| CompanyName: | Dexpot GbR |
| FileDescription: | Installer for Dexpot 1.6 |
| FileVersion: | 1.6.14 |
| LegalCopyright: | © 2001-2014 Dexpot GbR |
| ProductName: | Dexpot 1.6 Setup |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:52 |
| Detected languages: |
|
| CompanyName: | Dexpot GbR |
| FileDescription: | Installer for Dexpot 1.6 |
| FileVersion: | 1.6.14 |
| LegalCopyright: | © 2001-2014 Dexpot GbR |
| ProductName: | Dexpot 1.6 Setup |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x0001D000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0004C000 | 0x0000F9B0 | 0x0000FA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.91124 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22437 | 947 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.99175 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.21855 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.66663 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.44608 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68372 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
44
Monitored processes
13
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1520 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\mondayretail.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1968 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2028 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
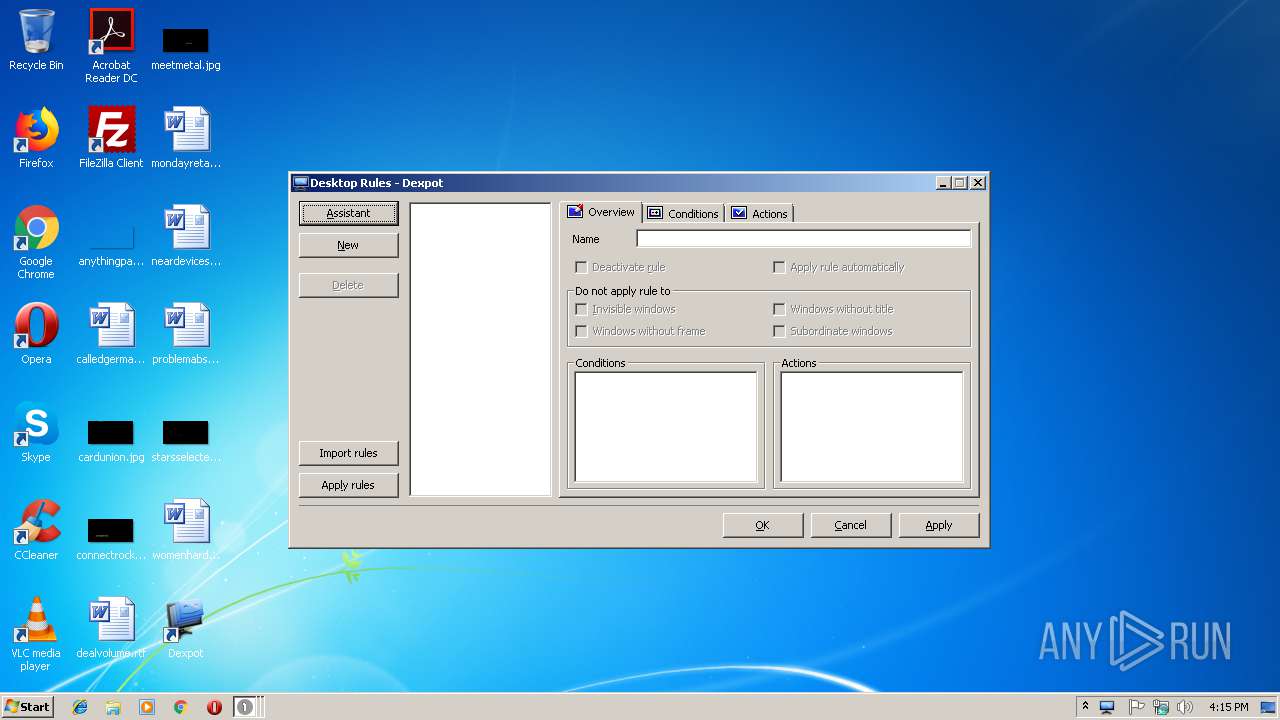
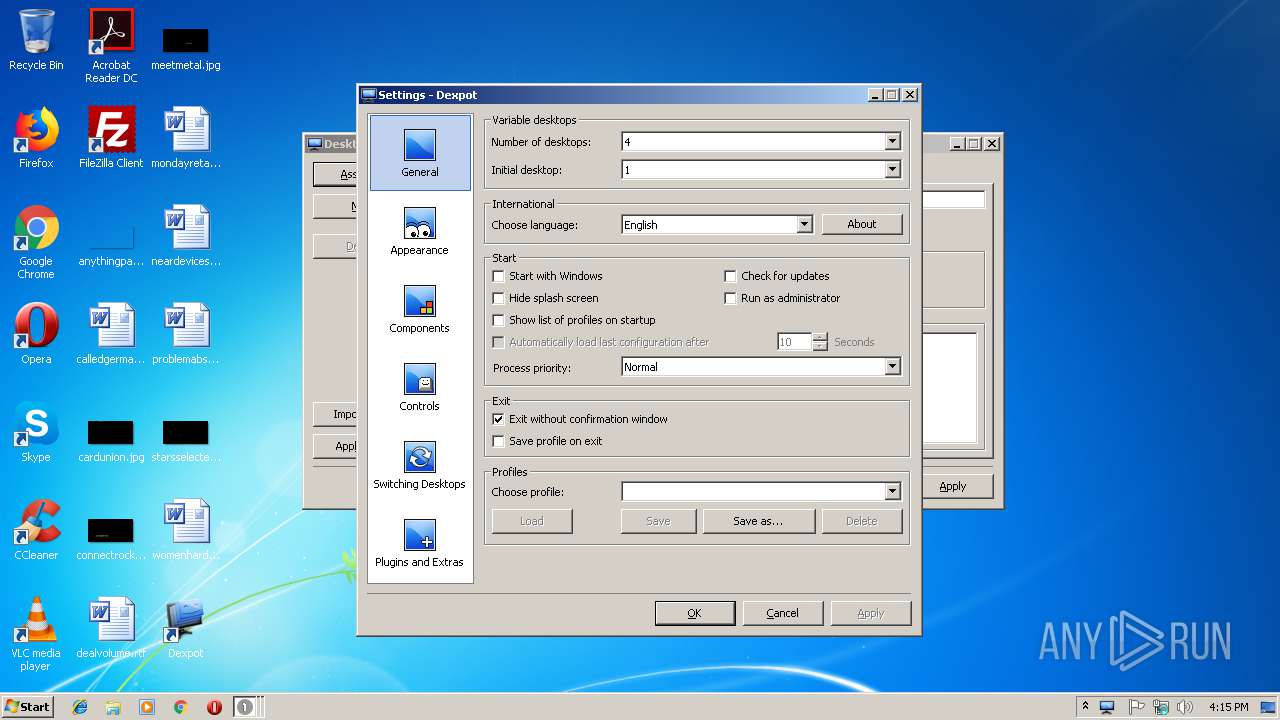
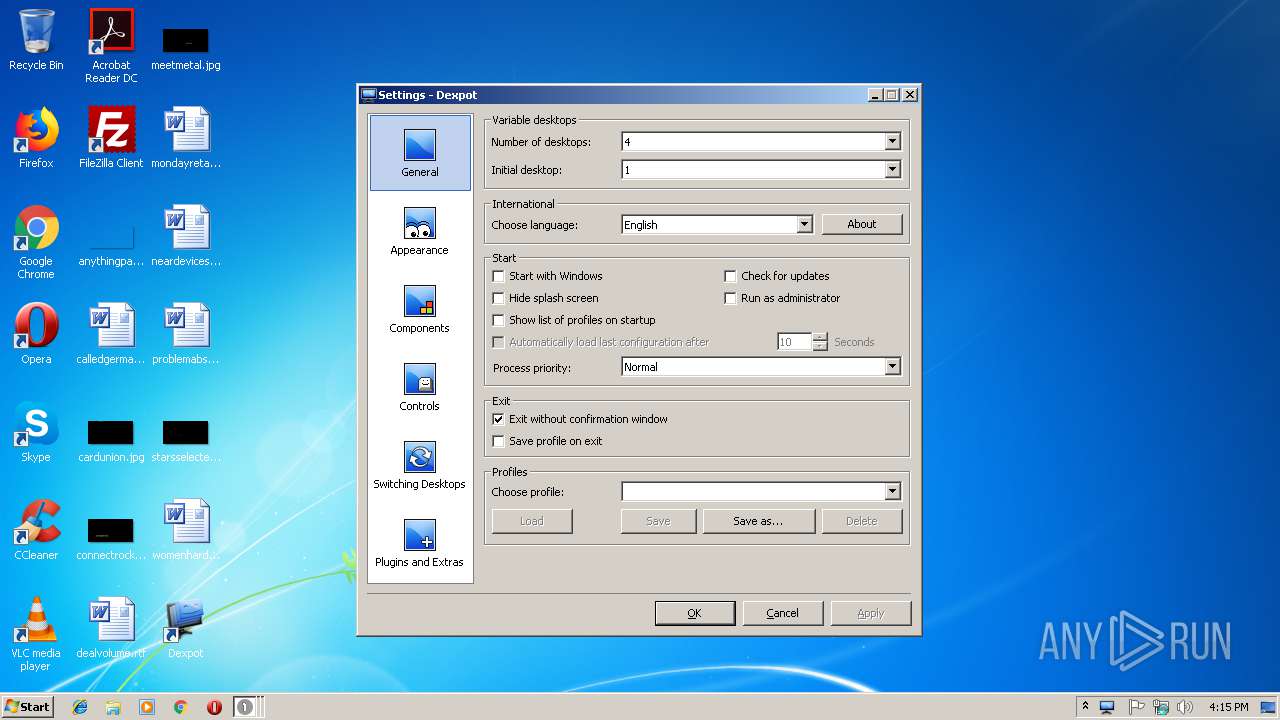
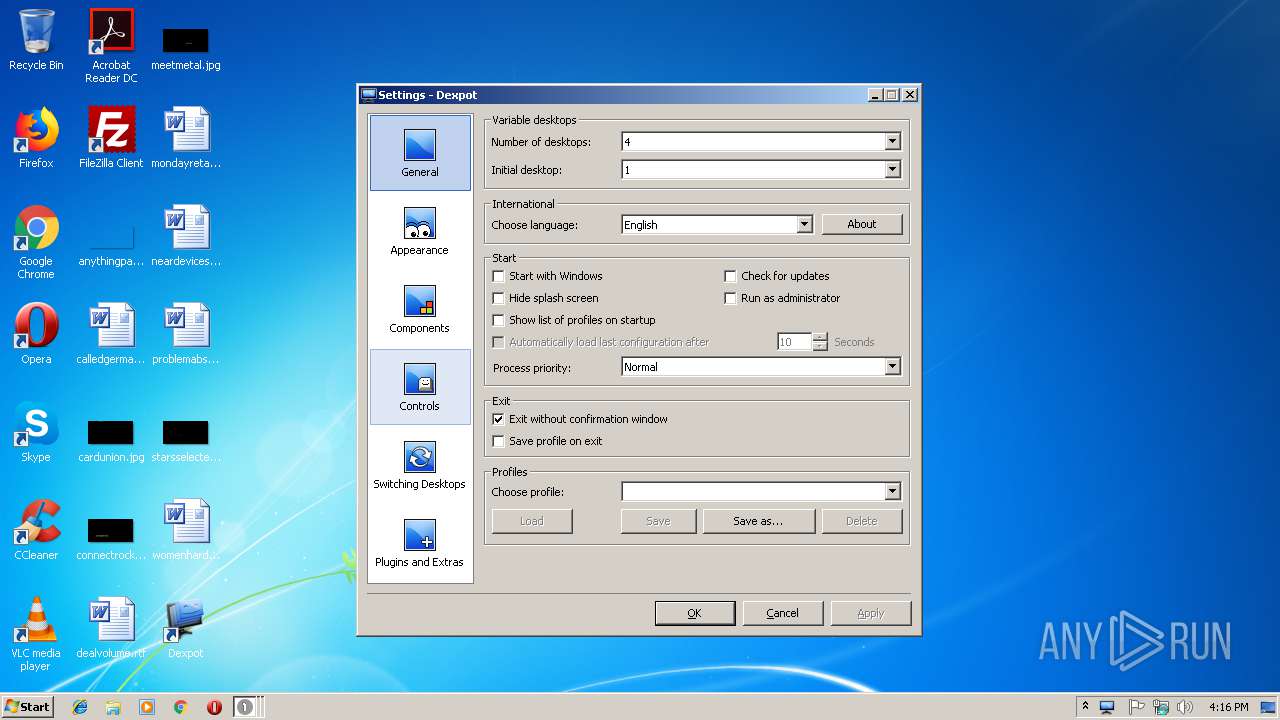
| 2212 | "C:\Program Files\Dexpot\dexpot.exe" | C:\Program Files\Dexpot\dexpot.exe | — | explorer.exe | |||||||||||
User: admin Company: Dexpot GbR Integrity Level: MEDIUM Description: Dexpot - Virtual desktops for Windows Exit code: 0 Version: 1.06.0014 Modules
| |||||||||||||||
| 2412 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2976 | "C:\Users\admin\AppData\Local\Temp\Dexpot v1614 r2439.exe" /UAC:30110 /NCRC | C:\Users\admin\AppData\Local\Temp\Dexpot v1614 r2439.exe | Dexpot v1614 r2439.exe | ||||||||||||
User: admin Company: Dexpot GbR Integrity Level: HIGH Description: Installer for Dexpot 1.6 Exit code: 0 Version: 1.6.14 Modules
| |||||||||||||||
| 3044 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3092 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3100 | "C:\Windows\explorer.exe" "C:\Program Files\Dexpot\dexpot.exe" | C:\Windows\explorer.exe | — | Dexpot v1614 r2439.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3128 | RunDll32.exe "C:\Users\admin\AppData\Local\Temp\nss5FD5.tmp\OCSetupHlp.dll",_OCPID163OpenCandy2@16 2976,F14DFEE9D07947E9988C799538752553,1912D08838694A9E913296095A98FCF7,B3A1A77598C2401BA889E0AC4B2874CF | C:\Windows\system32\RunDll32.exe | — | Dexpot v1614 r2439.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 964
Read events
6 148
Write events
724
Delete events
92
Modification events
| (PID) Process: | (2028) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\Qrkcbg i1614 e2439.rkr |
Value: 00000000000000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (2028) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002D0000003D000000B34B1500090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000F000000E21705007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E006500780065000000D201B0E536027CE43602A532DC75BCE4360294E5360200000000B432DC75F4E536020145DC756A00CA028C00CA02B8ACCA0278E336020001000101000000000100000000000028FCA802C8E53602E0E2BF02A4E53602CAFEBF02A0E33602D4E536026000CA022B0000006A00CA0228FCA802000000008C00CA025CE536020A00CA020000000005000500A823D3016601CA022B0000000F000000F4E53602BCE5360228FCA8021000000074FFA802050017004E1ED301BCE436021600000002000000B8ACCA020400360228FCA80203000000000000000909090009090909000911110000000011000000B8452700B04527000000000000000000000000000000000000000000000000001CE400005A743083D0E336028291F5751CE43602CCB700002E743083E4E33602B69CF575D0B7DD024C060000FCE3360240B3DD0208E43602789CF57511000000B8452700B045270060B3DD026CE40000E67330831CE436028291F5756CE4360220E436022795F57500000000CCB7DD0248E43602CD94F575CCB7DD02F4E4360240B3DD02E194F5750000000040B3DD02F4E4360250E43602090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802 | |||
| (PID) Process: | (3128) RunDll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RunDll32_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3128) RunDll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RunDll32_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3128) RunDll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RunDll32_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3128) RunDll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RunDll32_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3128) RunDll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RunDll32_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3128) RunDll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RunDll32_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3128) RunDll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RunDll32_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3128) RunDll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RunDll32_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
32
Suspicious files
5
Text files
214
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3156 | Dexpot v1614 r2439.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Dexpot\Dexpot Uninstall.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3156 | Dexpot v1614 r2439.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Dexpot\Dexpot-Updater.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3156 | Dexpot v1614 r2439.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Dexpot\Dexpot.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2976 | Dexpot v1614 r2439.exe | C:\Windows\system32\mscomctl.ocx | executable | |
MD5:E52859FCB7A827CACFCE7963184C7D24 | SHA256:45B6EEF5BBF223CF8FF78F5014B68A72F0BC2CCEAED030DECE0A1ABACF88F1F8 | |||
| 2976 | Dexpot v1614 r2439.exe | C:\Users\admin\AppData\Local\Temp\nss5FD5.tmp\dexpot.ini | text | |
MD5:4040CC17D2AA8C637D24BB5B77B378DC | SHA256:4FA2A862E69F8C55D1D2BDAEA2F3AC350E871C3D1AF7708ADFA7761AD649DB0B | |||
| 3156 | Dexpot v1614 r2439.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Dexpot\Dexpot Homepage.url | text | |
MD5:— | SHA256:— | |||
| 3156 | Dexpot v1614 r2439.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Dexpot\Main menu\Desktops\Desktop 3.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2976 | Dexpot v1614 r2439.exe | C:\Users\admin\AppData\Local\Temp\nss5FD5.tmp\InstallOptions.dll | executable | |
MD5:325B008AEC81E5AAA57096F05D4212B5 | SHA256:C9CD5C9609E70005926AE5171726A4142FFBCCCC771D307EFCD195DAFC1E6B4B | |||
| 3156 | Dexpot v1614 r2439.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Dexpot\Main menu\Desktops\Next desktop.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2976 | Dexpot v1614 r2439.exe | C:\Users\admin\AppData\Local\Temp\nss5FD5.tmp\UAC.dll | executable | |
MD5:88AD3FD90FC52AC3EE0441A38400A384 | SHA256:E58884695378CF02715373928BB8ADE270BAF03144369463F505C3B3808CBC42 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.opencandy.com |
| whitelisted |