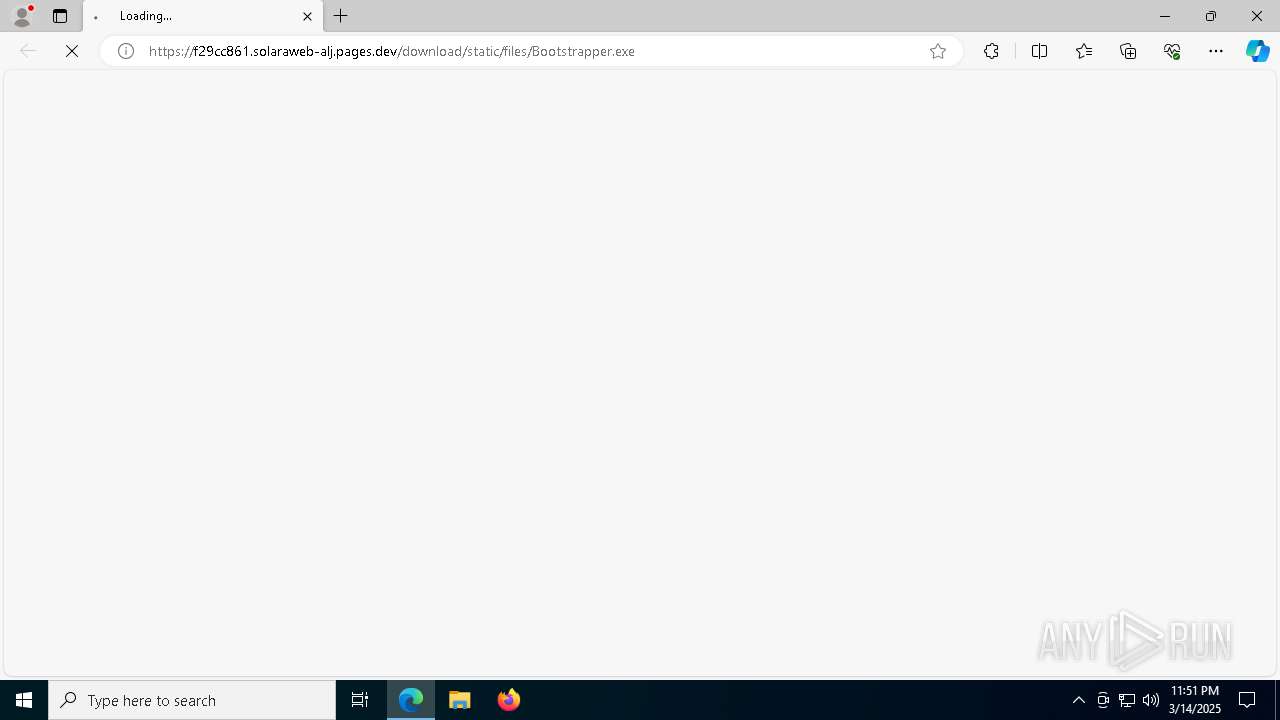
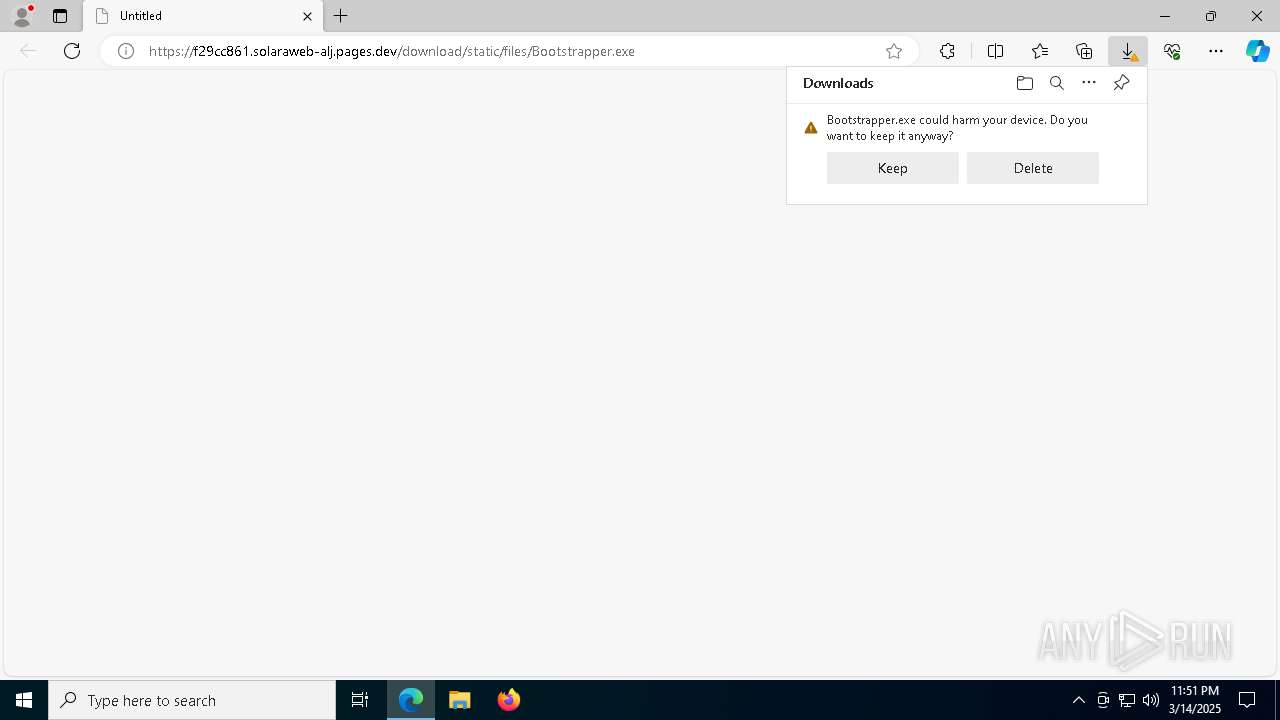
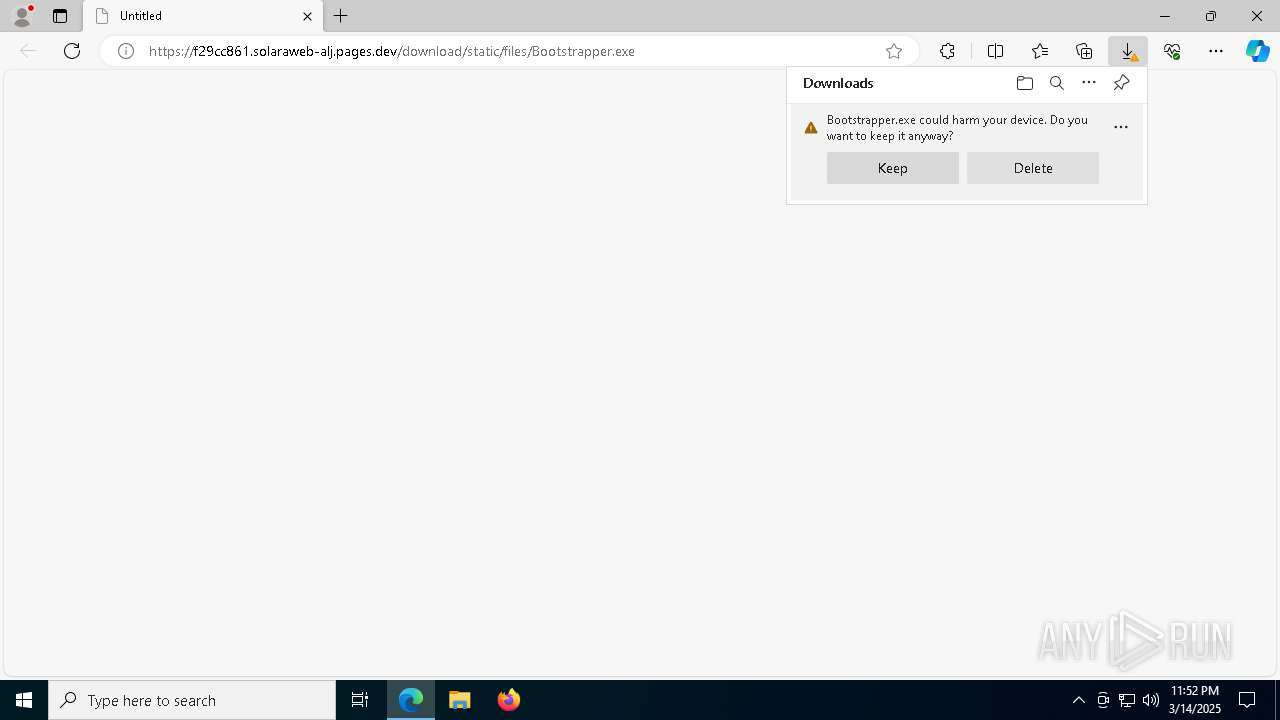
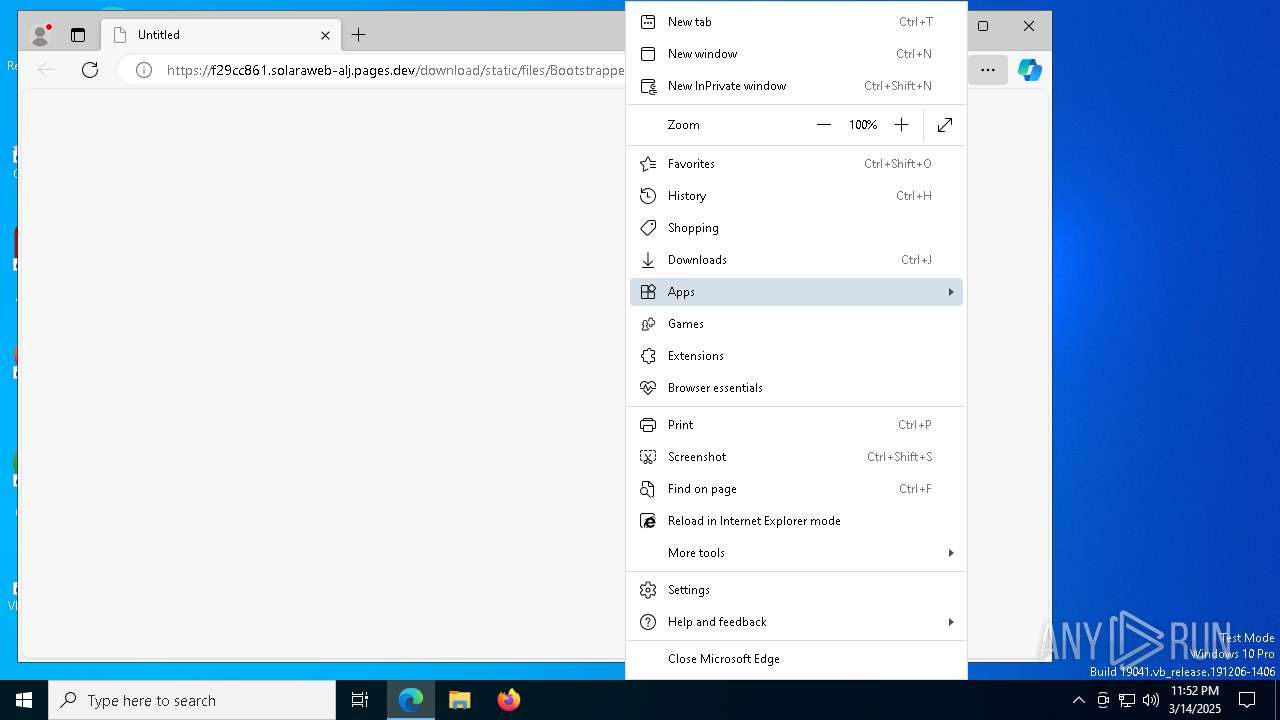
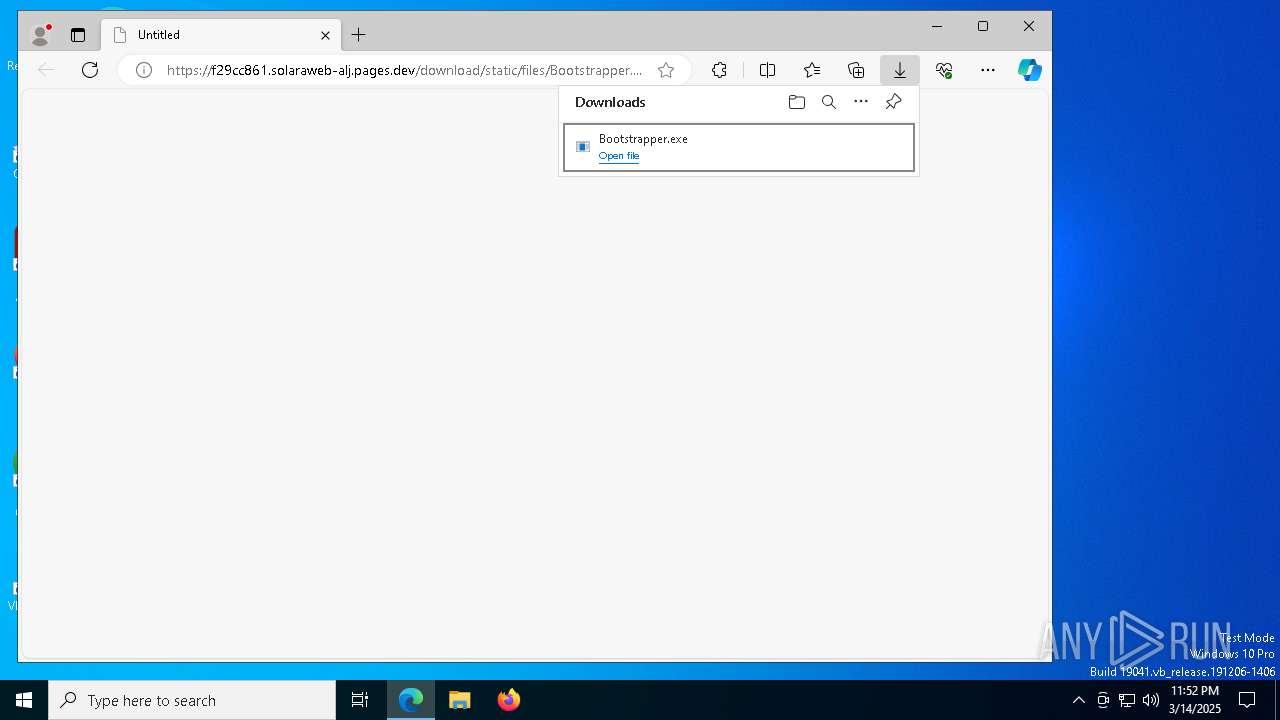
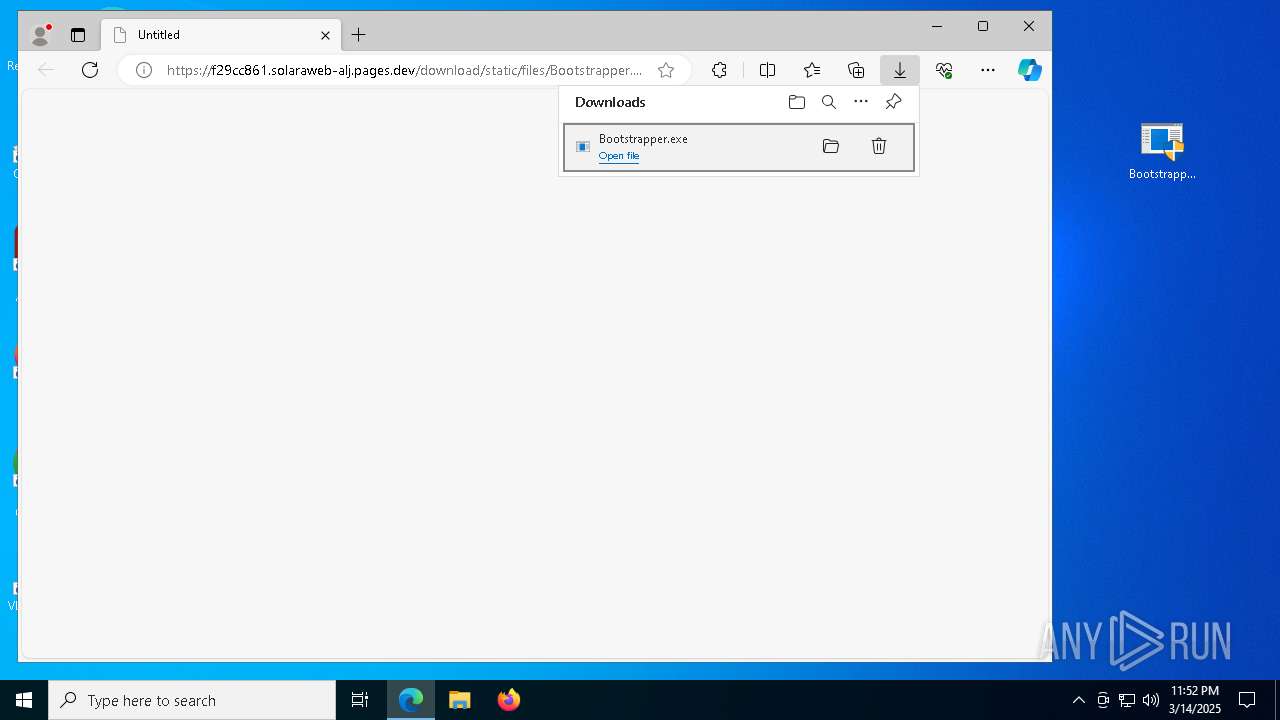
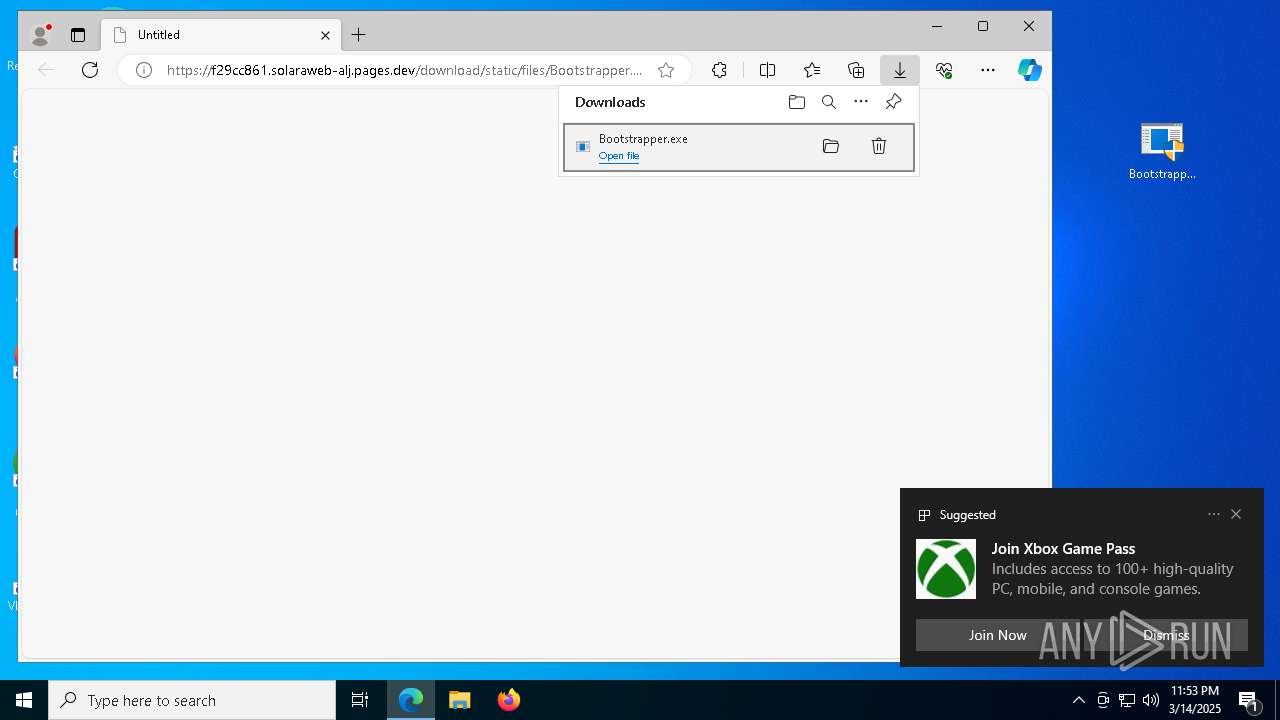
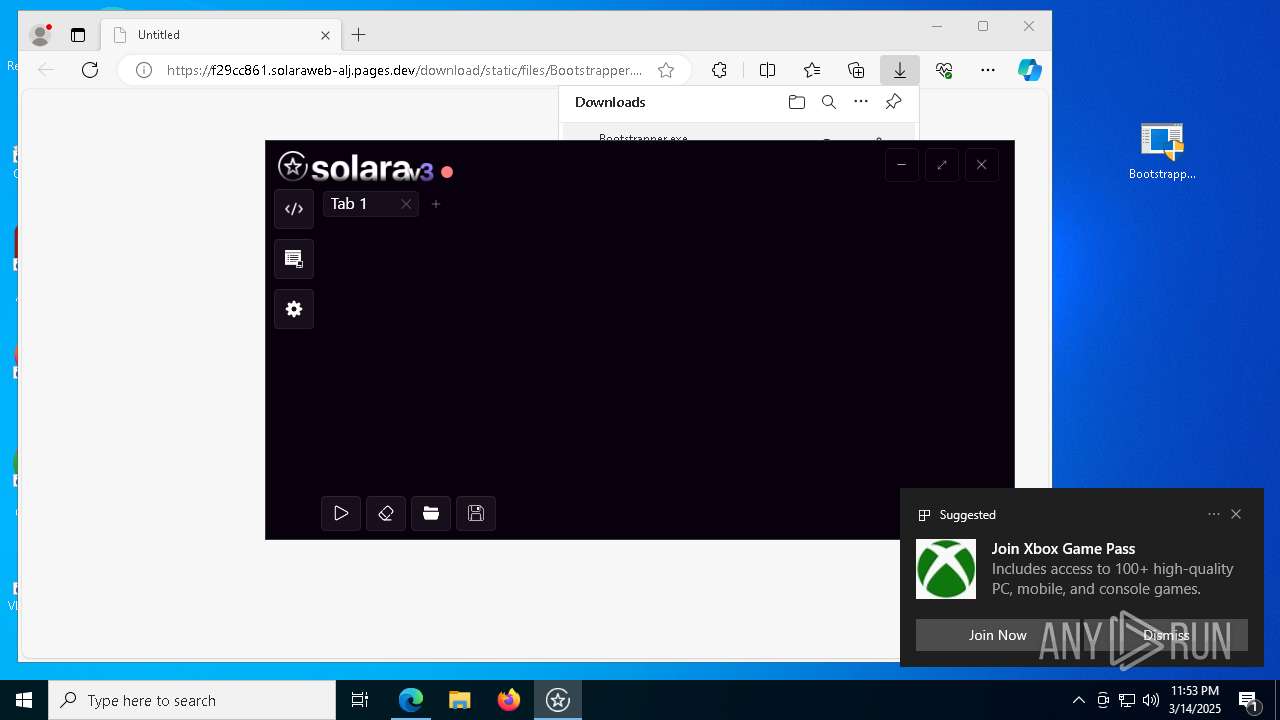
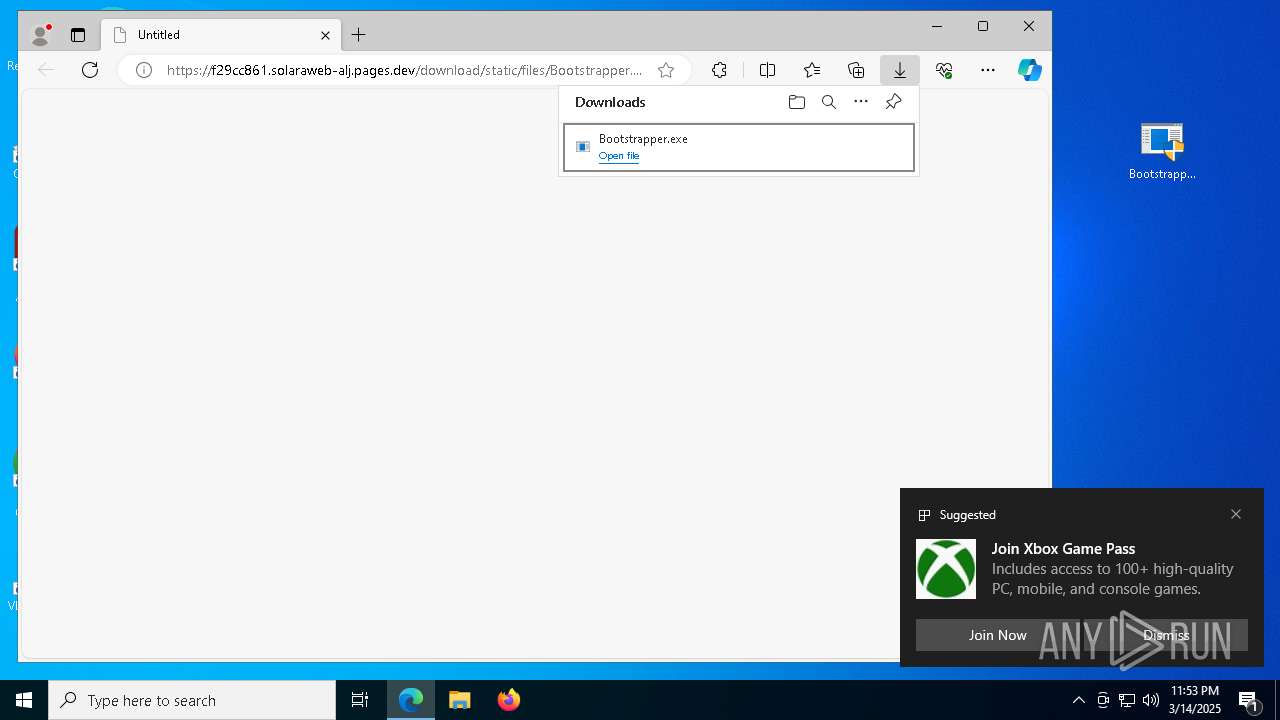
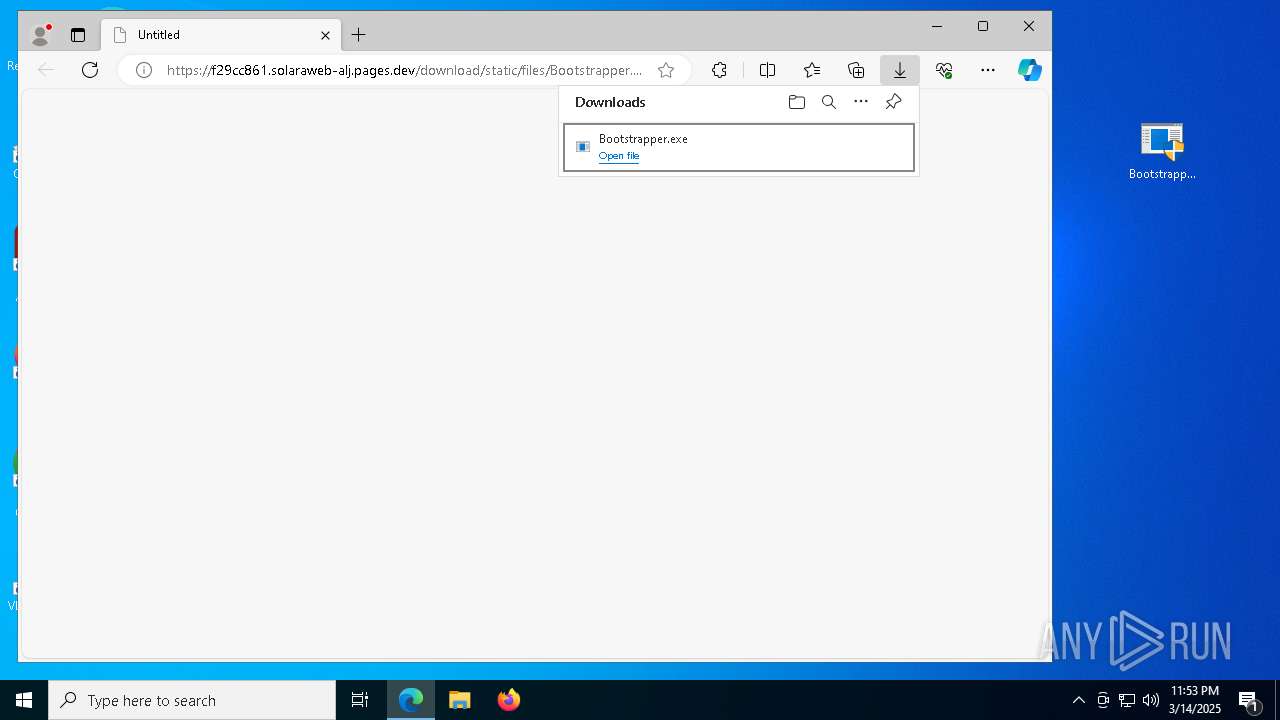
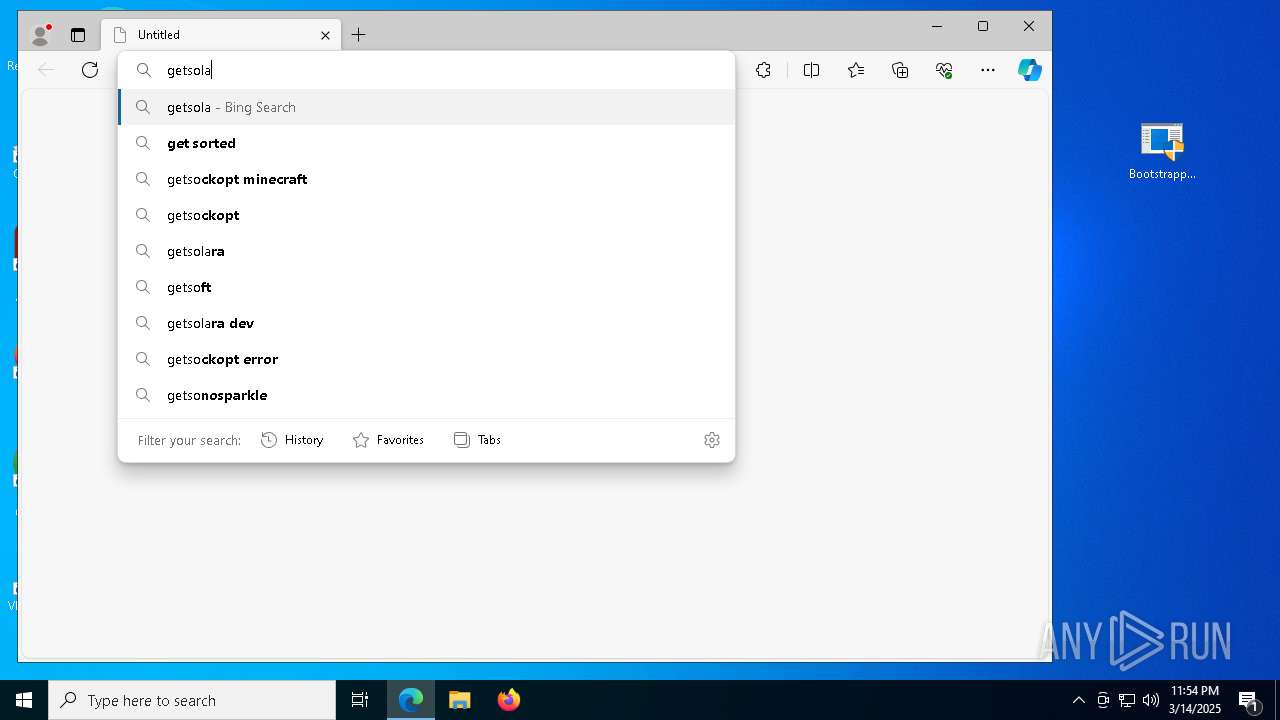
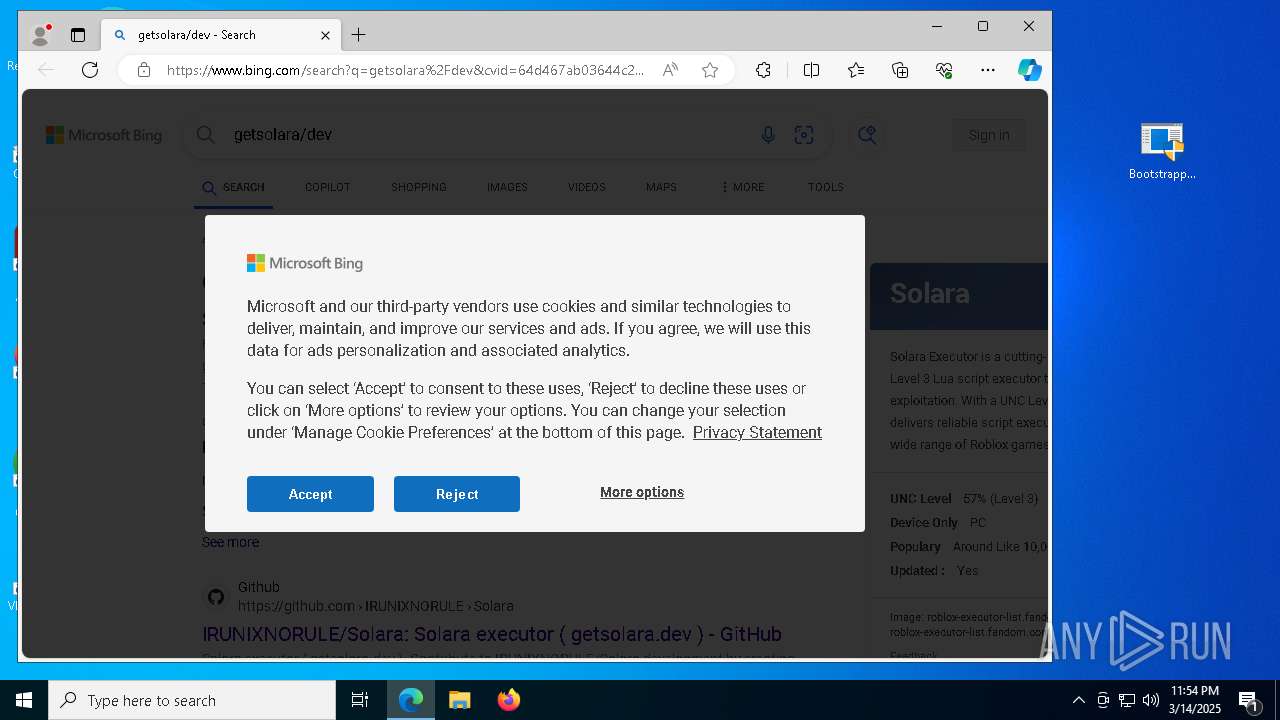
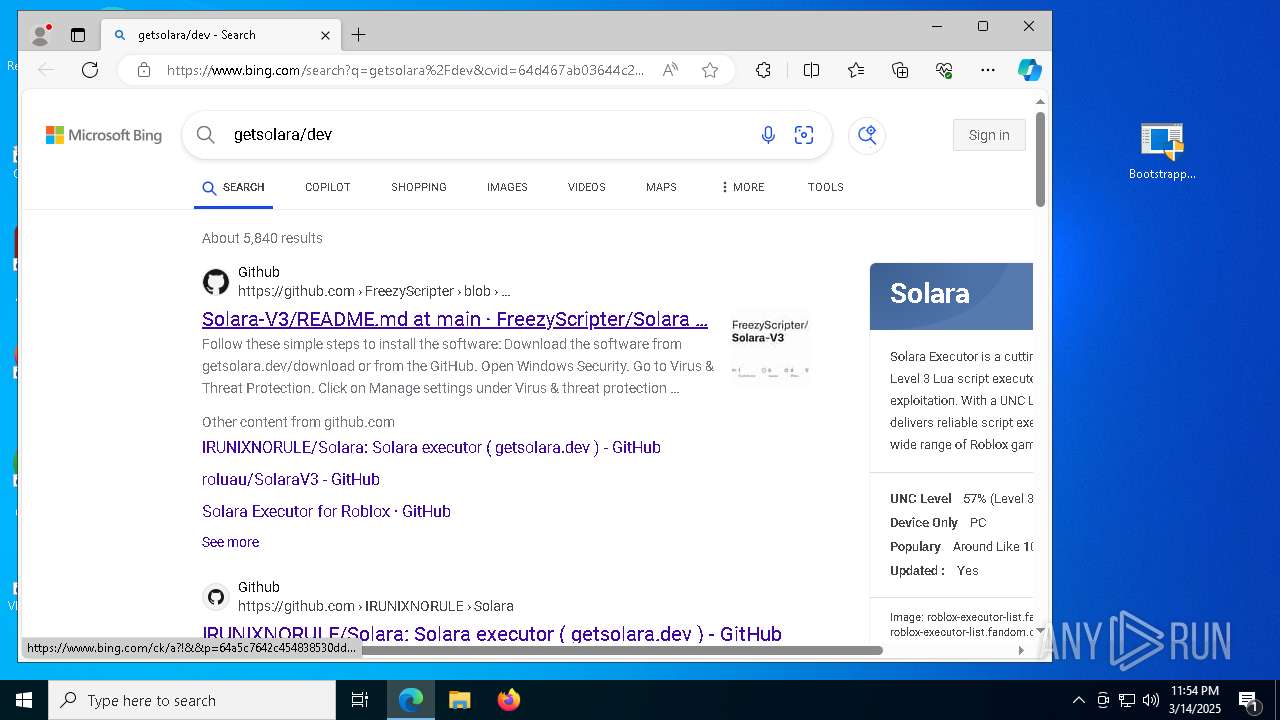
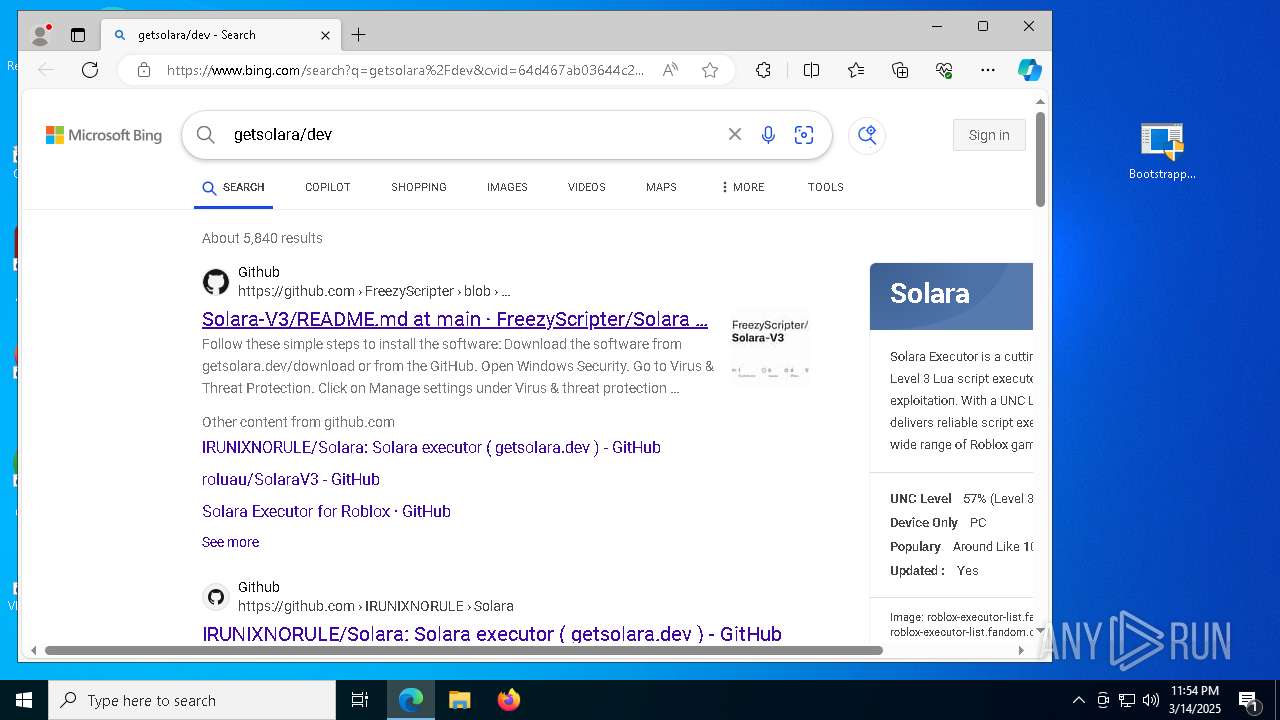
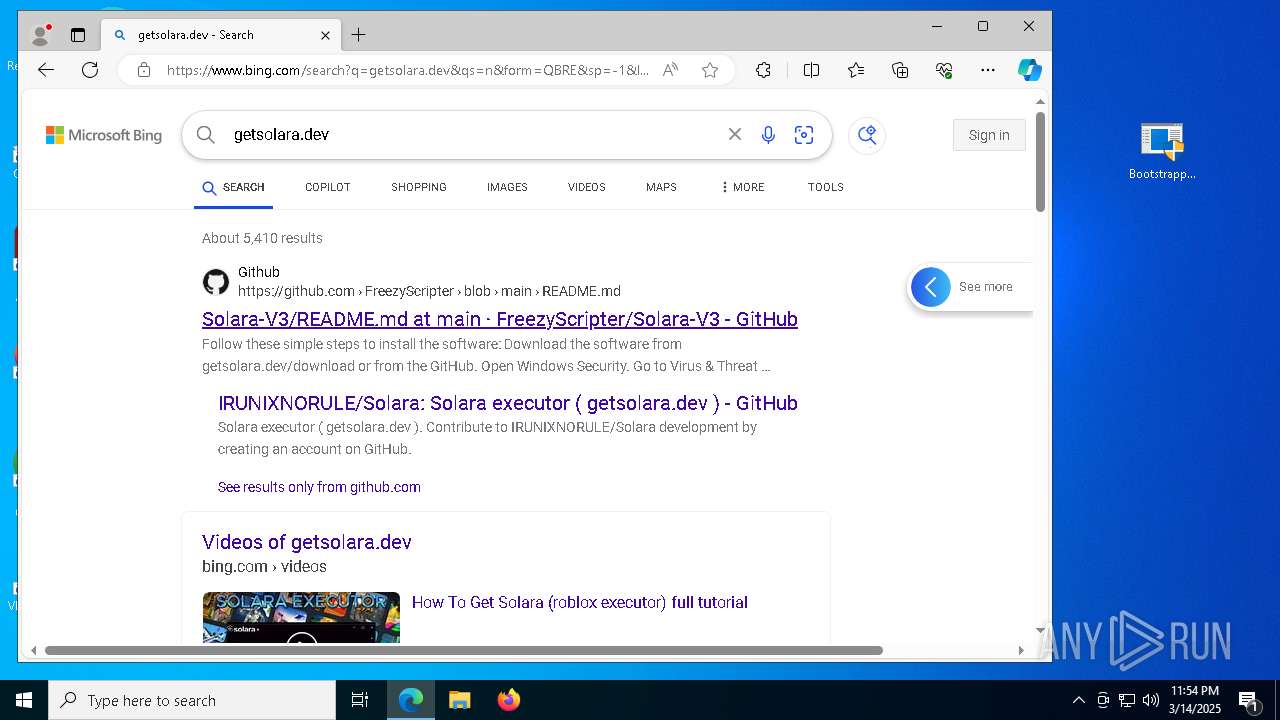
| URL: | https://f29cc861.solaraweb-alj.pages.dev/download/static/files/Bootstrapper.exe |
| Full analysis: | https://app.any.run/tasks/b57a9abf-946c-4ccb-a2b7-6bcdac170a17 |
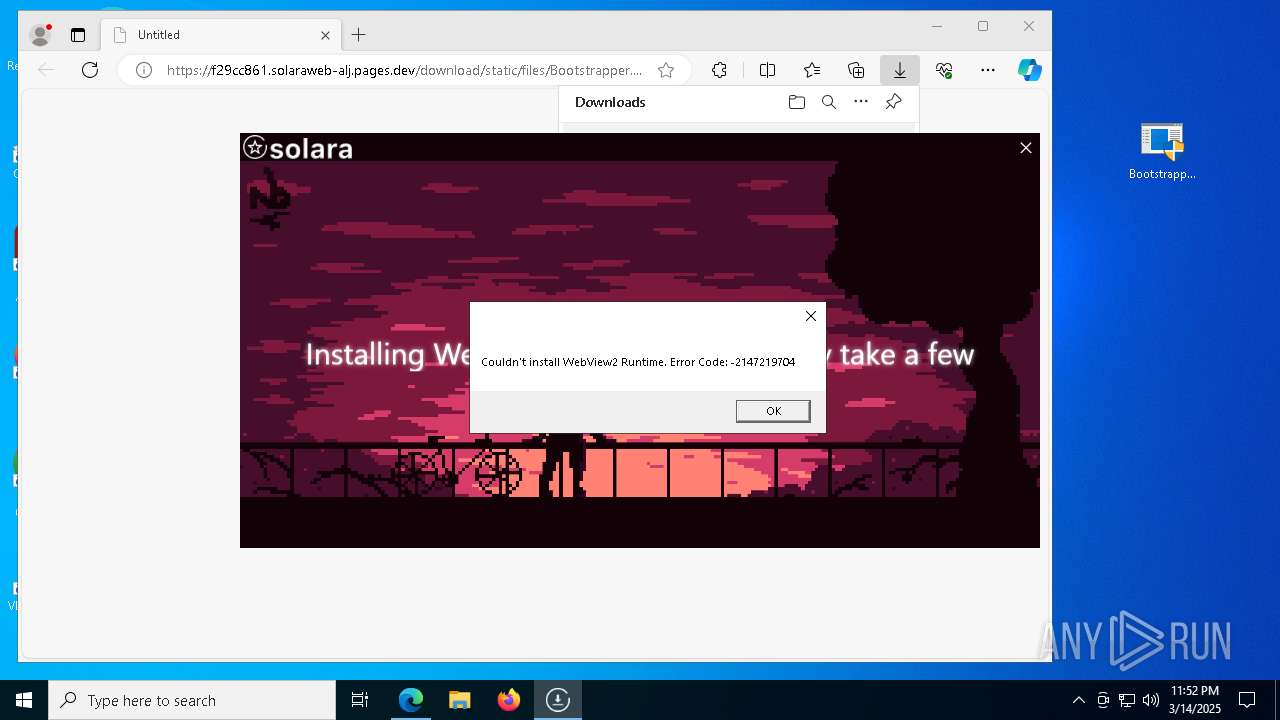
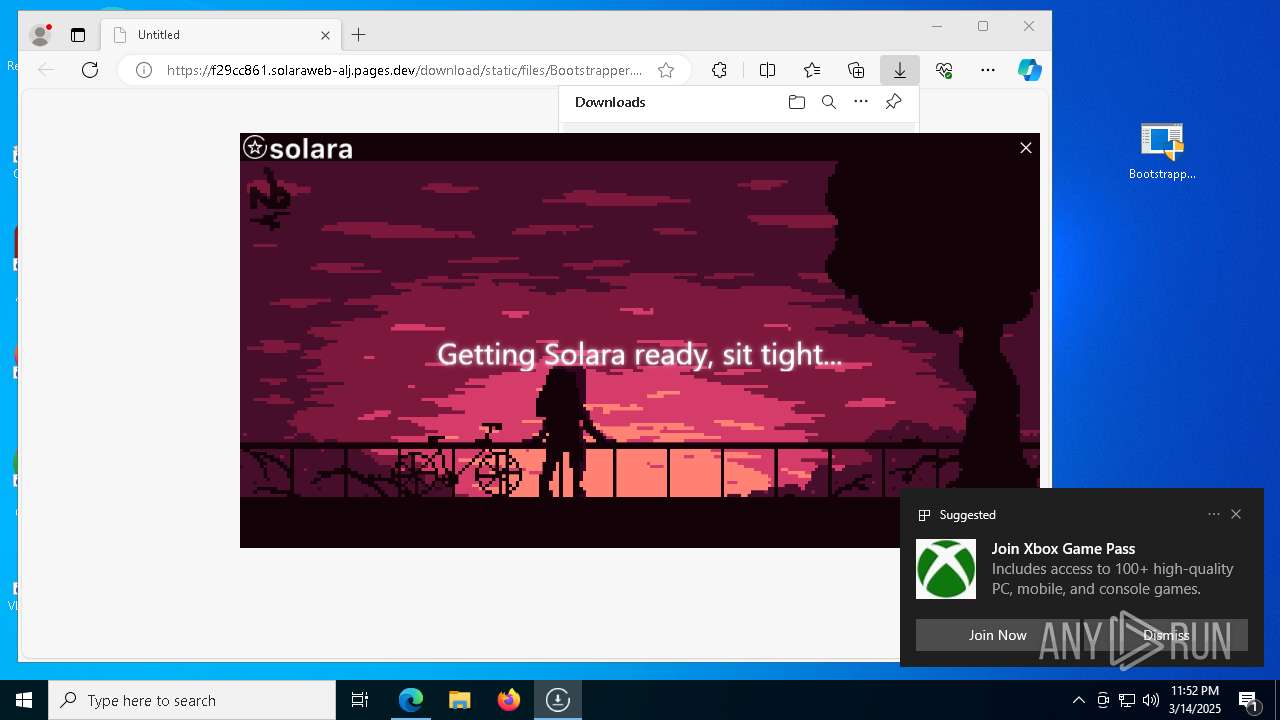
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2025, 23:51:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7A7B3E41CA3A8E81A14F79A6ABBBE373 |
| SHA1: | AC814A9E84BA5BBAB8A5113E51BBE7EE603CFAA1 |
| SHA256: | 34DB3203C05458E95CCDF1112EAFAD355FFA0F297684F1746B8A9878254D2F29 |
| SSDEEP: | 3:N8l4QKXE19Nn2NZKQ5KRRRw4A:2+QKgAow4A |
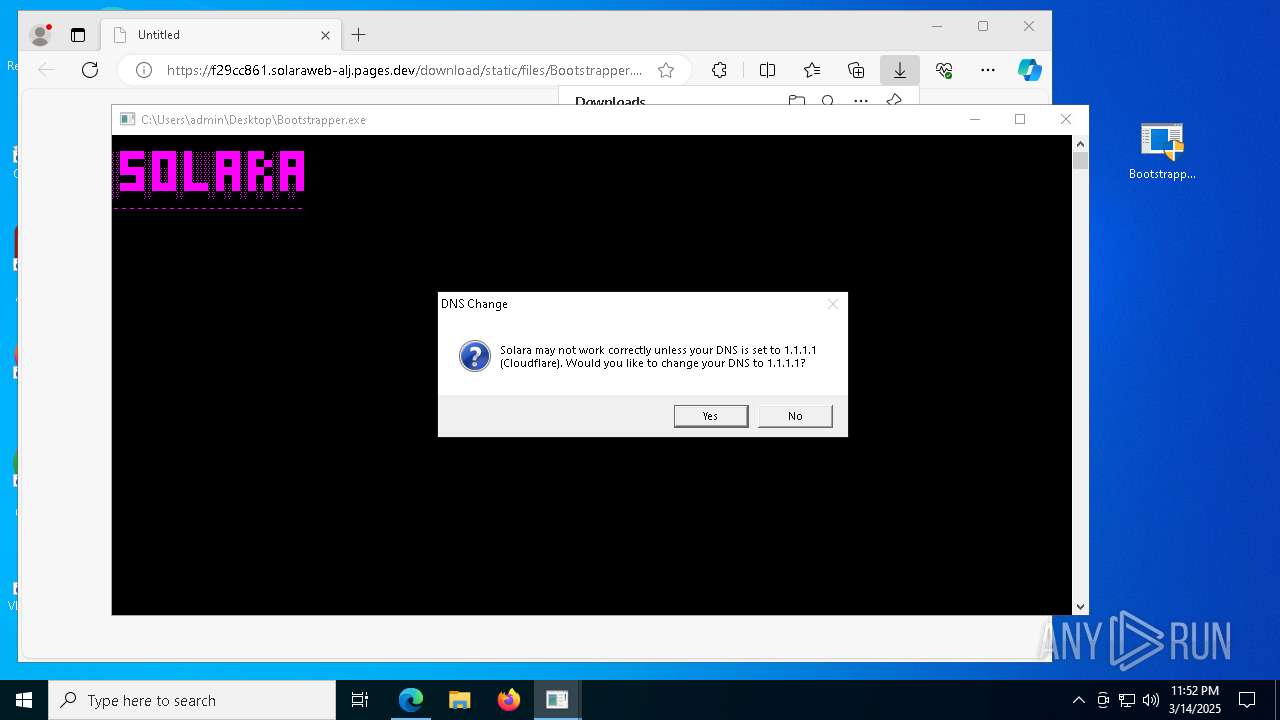
MALICIOUS
Changes Windows Defender settings
- BootstrapperV2.21.exe (PID: 5512)
Adds path to the Windows Defender exclusion list
- BootstrapperV2.21.exe (PID: 5512)
SUSPICIOUS
Uses WMIC.EXE to obtain information about the network interface controller
- cmd.exe (PID: 5228)
Executable content was dropped or overwritten
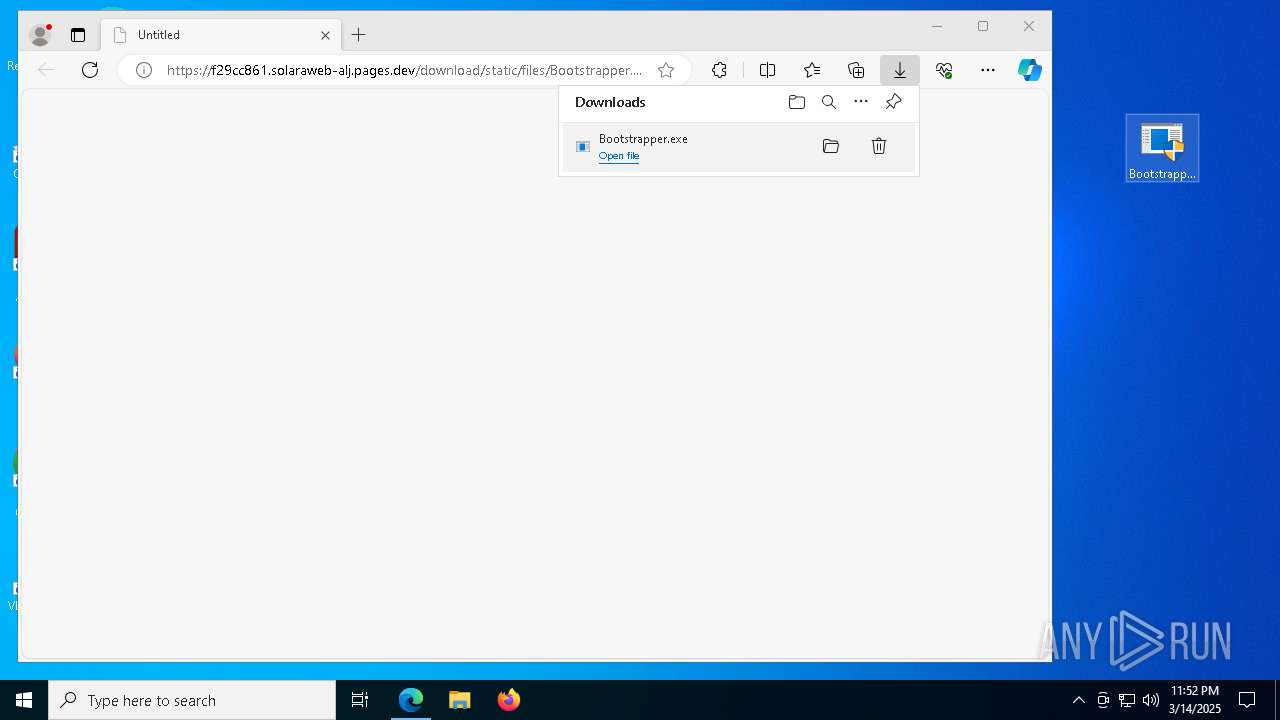
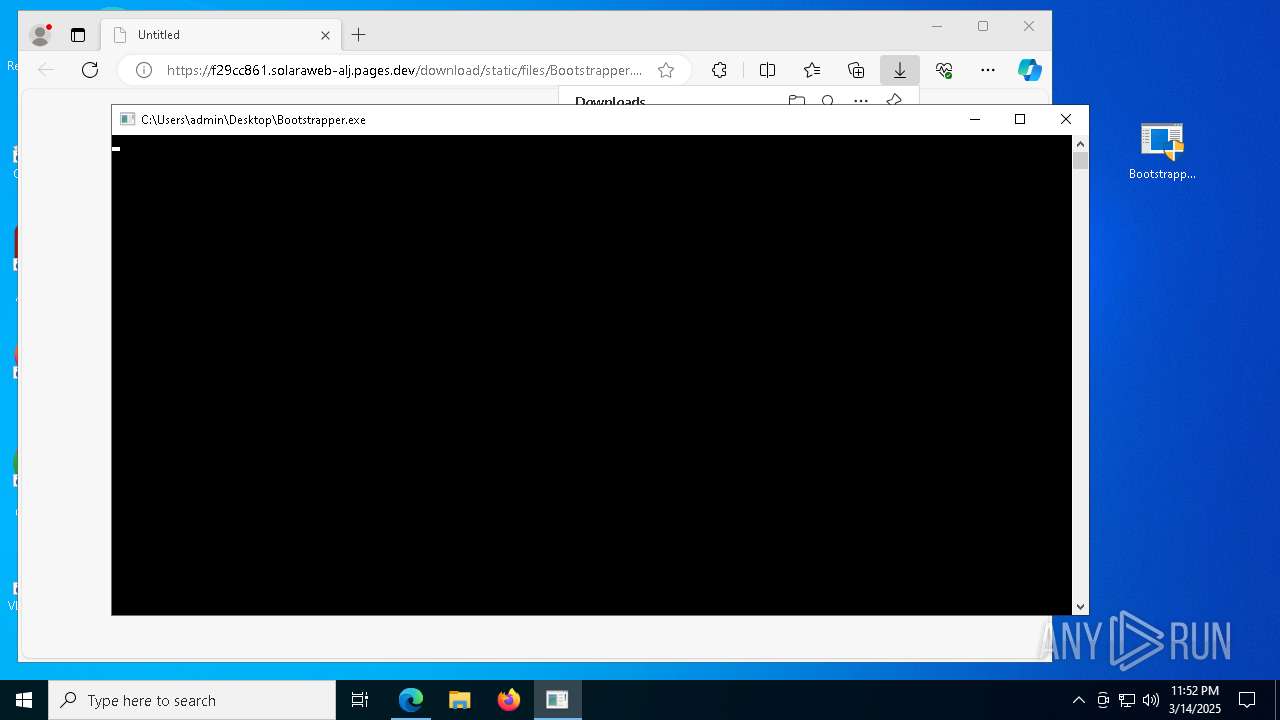
- Bootstrapper.exe (PID: 7532)
- BootstrapperV2.21.exe (PID: 5512)
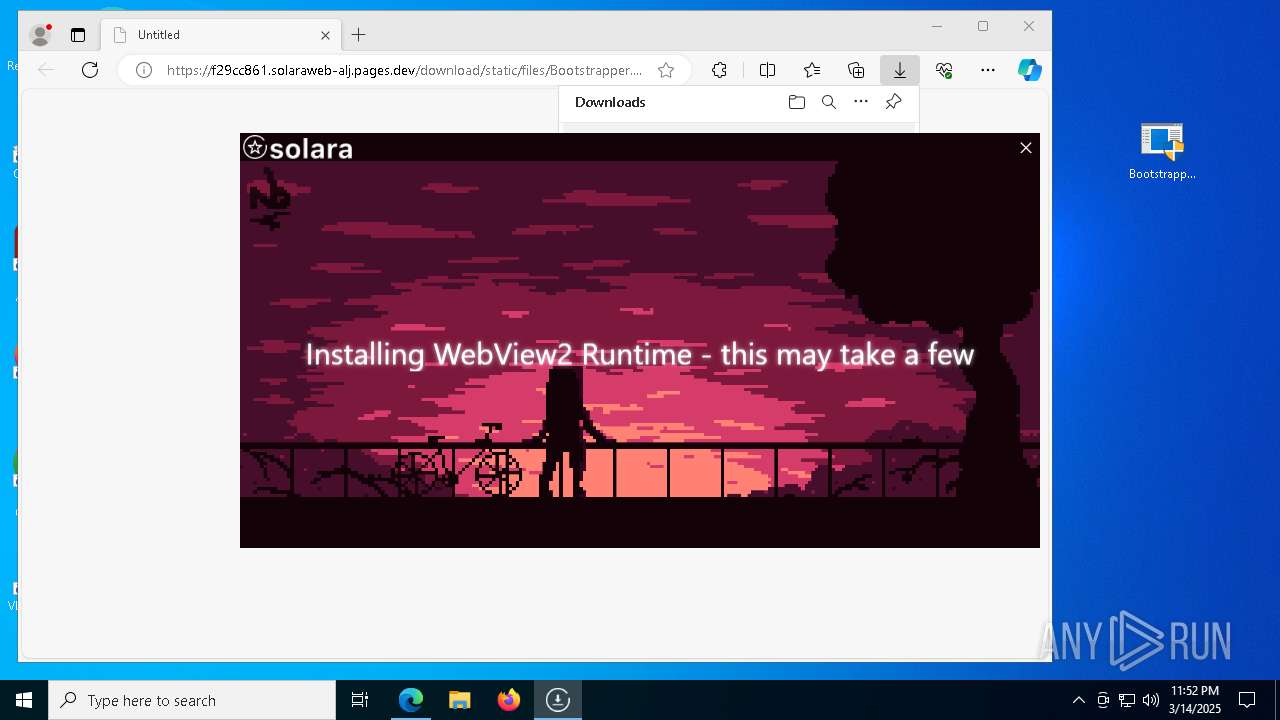
- MicrosoftEdgeWebview2Setup.exe (PID: 8072)
Reads security settings of Internet Explorer
- Bootstrapper.exe (PID: 7532)
- BootstrapperV2.21.exe (PID: 5512)
- MicrosoftEdgeUpdate.exe (PID: 7020)
- ShellExperienceHost.exe (PID: 4740)
- Solara.exe (PID: 472)
Reads the date of Windows installation
- Bootstrapper.exe (PID: 7532)
- BootstrapperV2.21.exe (PID: 5512)
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 6824)
Starts CMD.EXE for commands execution
- Bootstrapper.exe (PID: 7532)
Starts POWERSHELL.EXE for commands execution
- BootstrapperV2.21.exe (PID: 5512)
Query Microsoft Defender preferences
- BootstrapperV2.21.exe (PID: 5512)
Script adds exclusion path to Windows Defender
- BootstrapperV2.21.exe (PID: 5512)
Process drops legitimate windows executable
- BootstrapperV2.21.exe (PID: 5512)
- MicrosoftEdgeWebview2Setup.exe (PID: 8072)
- MicrosoftEdgeUpdate.exe (PID: 7020)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 7020)
- MicrosoftEdgeWebview2Setup.exe (PID: 8072)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 7020)
The process drops C-runtime libraries
- BootstrapperV2.21.exe (PID: 5512)
Reads the BIOS version
- Solara.exe (PID: 472)
Executes application which crashes
- Solara.exe (PID: 472)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 6576)
- BackgroundTransferHost.exe (PID: 5064)
- BackgroundTransferHost.exe (PID: 3300)
- BackgroundTransferHost.exe (PID: 856)
- BackgroundTransferHost.exe (PID: 5964)
- WMIC.exe (PID: 5384)
Reads the computer name
- identity_helper.exe (PID: 5512)
- BootstrapperV2.21.exe (PID: 5512)
- Bootstrapper.exe (PID: 7532)
- MicrosoftEdgeUpdate.exe (PID: 7020)
- ShellExperienceHost.exe (PID: 4740)
- Solara.exe (PID: 472)
Executable content was dropped or overwritten
- msedge.exe (PID: 7312)
- msedge.exe (PID: 744)
- msedge.exe (PID: 7712)
Reads Environment values
- identity_helper.exe (PID: 5512)
- Bootstrapper.exe (PID: 7532)
- BootstrapperV2.21.exe (PID: 5512)
- MicrosoftEdgeUpdate.exe (PID: 7020)
- Solara.exe (PID: 472)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5064)
- Bootstrapper.exe (PID: 7532)
- BootstrapperV2.21.exe (PID: 5512)
- wermgr.exe (PID: 5020)
- MicrosoftEdgeUpdate.exe (PID: 7020)
- Solara.exe (PID: 472)
- slui.exe (PID: 4868)
Checks supported languages
- identity_helper.exe (PID: 5512)
- Bootstrapper.exe (PID: 7532)
- BootstrapperV2.21.exe (PID: 5512)
- MicrosoftEdgeWebview2Setup.exe (PID: 8072)
- MicrosoftEdgeUpdate.exe (PID: 7020)
- ShellExperienceHost.exe (PID: 4740)
- Solara.exe (PID: 472)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5064)
- wermgr.exe (PID: 5020)
- WerFault.exe (PID: 8124)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5064)
- Bootstrapper.exe (PID: 7532)
- BootstrapperV2.21.exe (PID: 5512)
- MicrosoftEdgeUpdate.exe (PID: 7020)
- wermgr.exe (PID: 5020)
- Solara.exe (PID: 472)
- slui.exe (PID: 4040)
- slui.exe (PID: 4868)
Manual execution by a user
- Bootstrapper.exe (PID: 7760)
- Bootstrapper.exe (PID: 7532)
Process checks computer location settings
- Bootstrapper.exe (PID: 7532)
- MicrosoftEdgeUpdate.exe (PID: 7020)
- BootstrapperV2.21.exe (PID: 5512)
Reads the machine GUID from the registry
- Bootstrapper.exe (PID: 7532)
- BootstrapperV2.21.exe (PID: 5512)
- Solara.exe (PID: 472)
Disables trace logs
- Bootstrapper.exe (PID: 7532)
- BootstrapperV2.21.exe (PID: 5512)
- Solara.exe (PID: 472)
Application launched itself
- msedge.exe (PID: 744)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1348)
- powershell.exe (PID: 4988)
Create files in a temporary directory
- BootstrapperV2.21.exe (PID: 5512)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4988)
Creates files in the program directory
- BootstrapperV2.21.exe (PID: 5512)
- MicrosoftEdgeWebview2Setup.exe (PID: 8072)
- Solara.exe (PID: 472)
The sample compiled with english language support
- BootstrapperV2.21.exe (PID: 5512)
- MicrosoftEdgeWebview2Setup.exe (PID: 8072)
- MicrosoftEdgeUpdate.exe (PID: 7020)
- msedge.exe (PID: 7712)
Process checks whether UAC notifications are on
- Solara.exe (PID: 472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
240
Monitored processes
94
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=42 --mojo-platform-channel-handle=4324 --field-trial-handle=2412,i,13235459640894205784,8082290880463835479,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 472 | "C:\ProgramData\Solara\Solara.exe" --bootstrapperPath "C:\Users\admin\Desktop" --bootstrapperExe "C:\Users\admin\Desktop\BootstrapperV2.21.exe" | C:\ProgramData\Solara\Solara.exe | BootstrapperV2.21.exe | ||||||||||||
User: admin Company: CMD Softworks Integrity Level: HIGH Description: Solara V3 Exit code: 3762504530 Version: 3.0.0.0 Modules
| |||||||||||||||
| 672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5344 --field-trial-handle=2412,i,13235459640894205784,8082290880463835479,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5328 --field-trial-handle=2412,i,13235459640894205784,8082290880463835479,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://f29cc861.solaraweb-alj.pages.dev/download/static/files/Bootstrapper.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 856 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7424 --field-trial-handle=2412,i,13235459640894205784,8082290880463835479,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=4256 --field-trial-handle=2412,i,13235459640894205784,8082290880463835479,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5756 --field-trial-handle=2412,i,13235459640894205784,8082290880463835479,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
34 073
Read events
33 930
Write events
138
Delete events
5
Modification events
| (PID) Process: | (744) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 76EC3E68EC8E2F00 | |||
| (PID) Process: | (744) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (744) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (744) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (744) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (744) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (744) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 40FF4768EC8E2F00 | |||
| (PID) Process: | (744) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459400 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {82D3B8CF-0B3B-4701-BCE3-E4359F98151B} | |||
| (PID) Process: | (744) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AB639368EC8E2F00 | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000008E81C2163C95DB01 | |||
Executable files
237
Suspicious files
644
Text files
116
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 744 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ba78.TMP | — | |
MD5:— | SHA256:— | |||
| 744 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 744 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ba88.TMP | — | |
MD5:— | SHA256:— | |||
| 744 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 744 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ba97.TMP | — | |
MD5:— | SHA256:— | |||
| 744 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 744 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ba97.TMP | — | |
MD5:— | SHA256:— | |||
| 744 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 744 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bab7.TMP | — | |
MD5:— | SHA256:— | |||
| 744 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
123
DNS requests
71
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7968 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
4220 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
5064 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
1388 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
1388 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
1312 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1742389758&P2=404&P3=2&P4=J3VNSG8raNRMk%2blUCL08CfFdRnqUqs5IFVYKoPRqIiN7%2bTw17pGQ7X8eEIP1zOGGjCgK%2fWjtnfIxAhqpyroZEg%3d%3d | US | — | — | whitelisted |
5020 | wermgr.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5020 | wermgr.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7312 | msedge.exe | 172.66.44.59:443 | f29cc861.solaraweb-alj.pages.dev | — | — | shared |
7312 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
744 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7312 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7312 | msedge.exe | 13.107.246.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7312 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
f29cc861.solaraweb-alj.pages.dev |
| shared |
bzib.nelreports.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7312 | msedge.exe | Misc activity | ET INFO DNS Query to Cloudflare Page Developer Domain (pages .dev) |
7312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
7312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
7312 | msedge.exe | Misc activity | ET INFO Observed Cloudflare DNS over HTTPS Domain (cloudflare-dns .com in TLS SNI) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
7532 | Bootstrapper.exe | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |