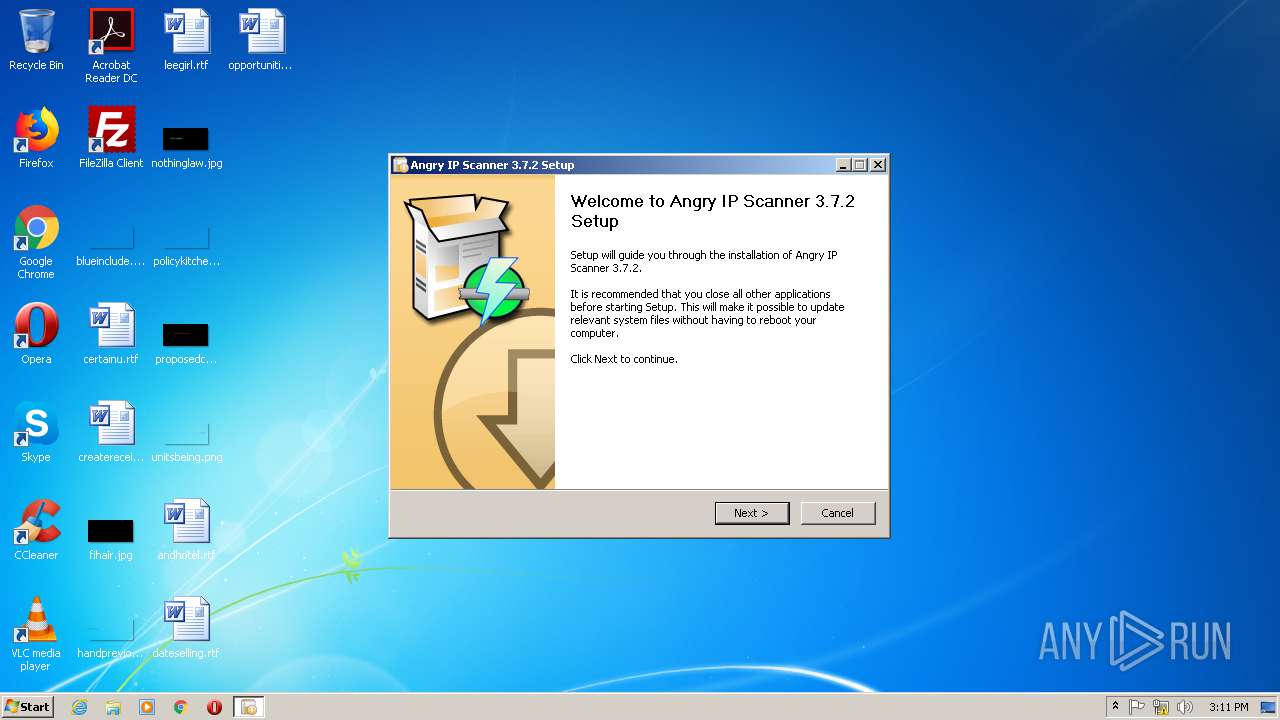
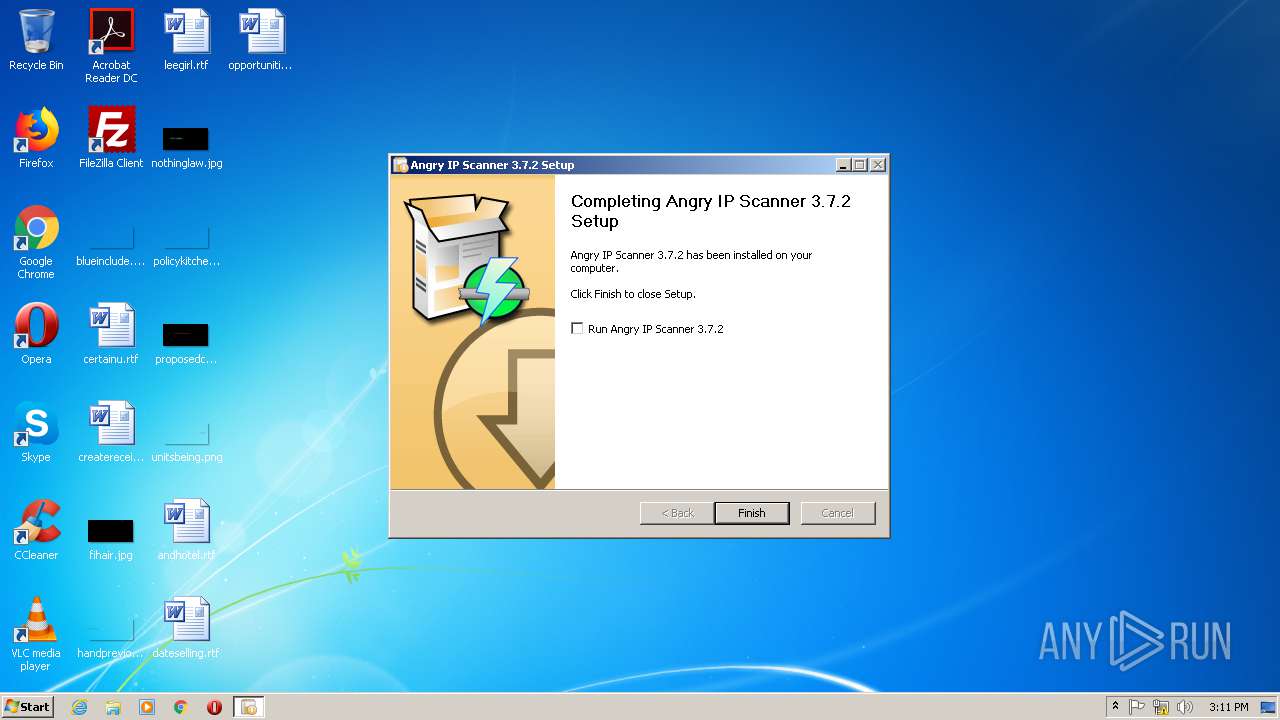
| File name: | ipscan-3.7.2-setup.exe |
| Full analysis: | https://app.any.run/tasks/54ac59bc-2085-4c44-b37b-91ae1cf4d6fd |
| Verdict: | Malicious activity |
| Analysis date: | June 03, 2020, 14:10:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 768E445A437E96DC4F4A782DC4E22A6A |
| SHA1: | 2108A30276BA56335C89A26AC12426FC63D5F679 |
| SHA256: | 34D8C2352FA1C264B7D9146069EBC780495B896BC767C10BA916E5A55CB9D1A6 |
| SSDEEP: | 49152:hfCI2JWNn1Eueoy2p1towM4B+lOiuZm8XDEsk6/p8Wu81xFmuEYsEnSXkj45cX0V:ADJu1EueB2/t/Z3ZdzVxuS33ElYSC45L |
MALICIOUS
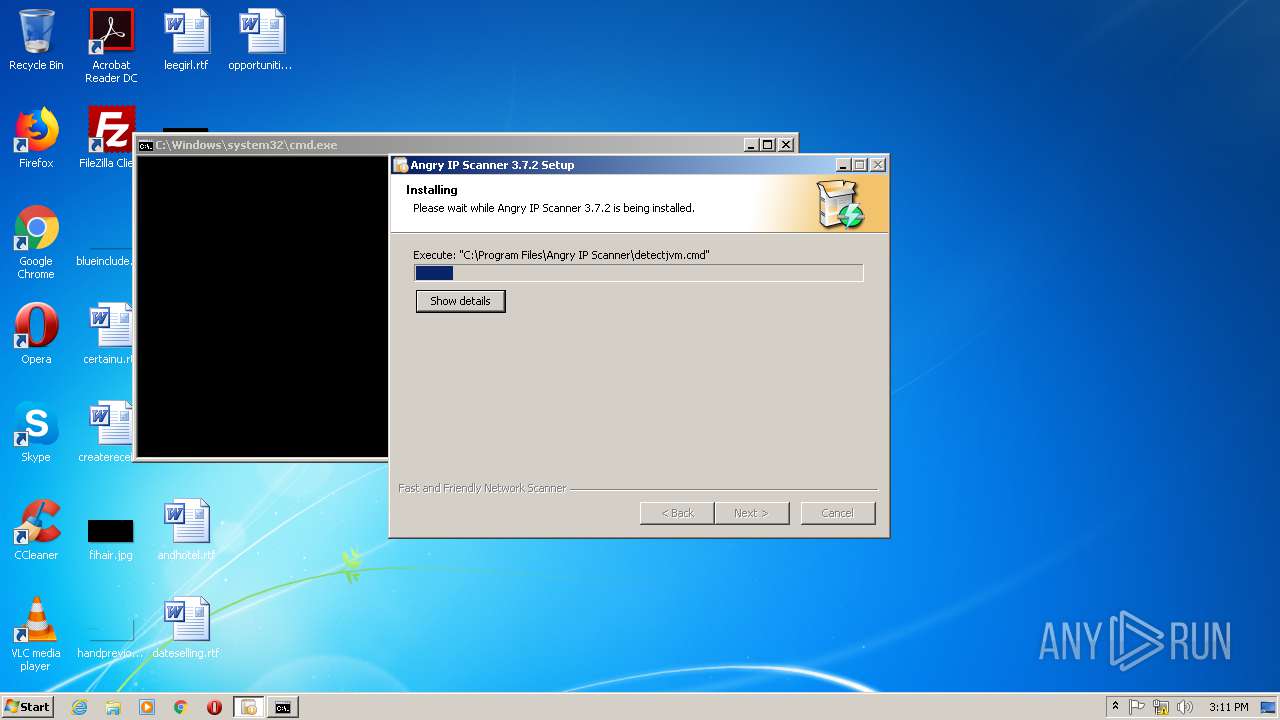
Loads dropped or rewritten executable
- ipscan-3.7.2-setup.exe (PID: 3200)
SUSPICIOUS
Creates a software uninstall entry
- ipscan-3.7.2-setup.exe (PID: 3200)
Starts CMD.EXE for commands execution
- ipscan-3.7.2-setup.exe (PID: 3200)
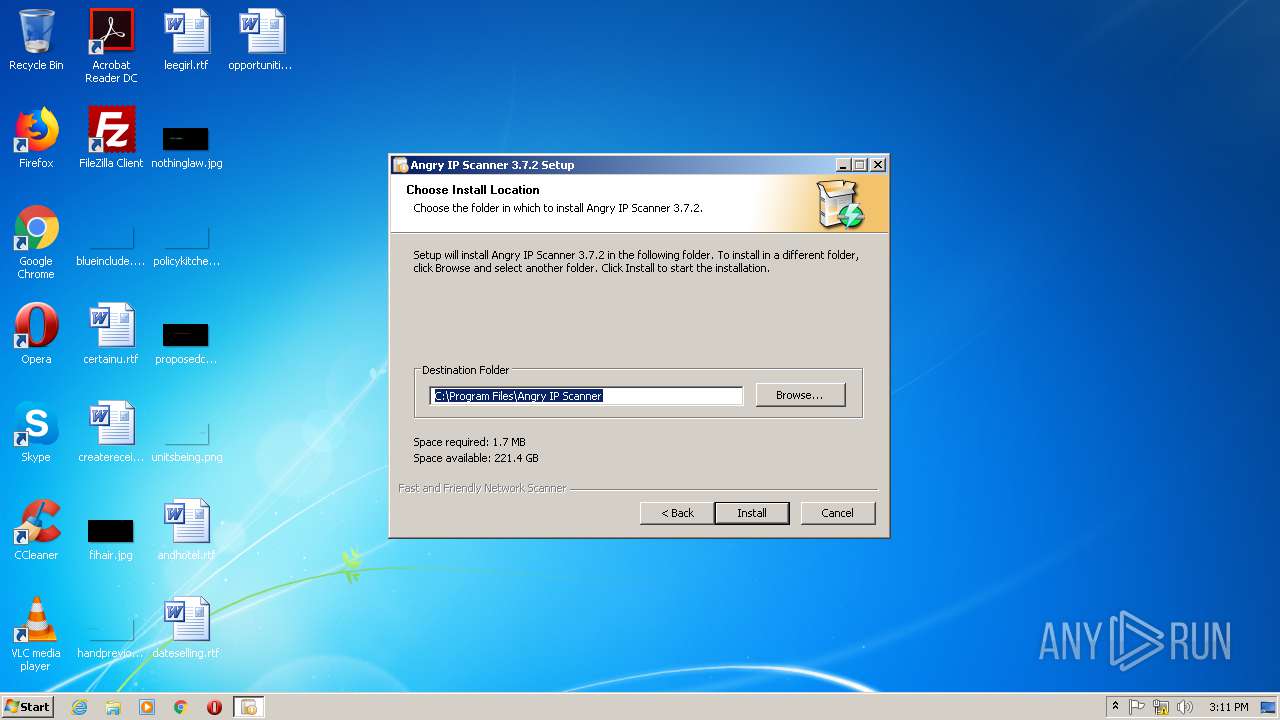
Creates files in the program directory
- ipscan-3.7.2-setup.exe (PID: 3200)
Executable content was dropped or overwritten
- ipscan-3.7.2-setup.exe (PID: 3200)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:16 01:50:50+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3384 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Dec-2019 00:50:50 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Dec-2019 00:50:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000060E4 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41884 |
.rdata | 0x00008000 | 0x0000123E | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.03406 |
.data | 0x0000A000 | 0x0001A838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.21839 |
.ndata | 0x00025000 | 0x00014000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00039000 | 0x0000A688 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.53564 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28847 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.68326 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.94272 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.24037 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 6.50155 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 5.90008 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 6.24662 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.30752 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
43
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1148 | "java" -version | C:\ProgramData\Oracle\Java\javapath\java.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1896 | findstr /I "64-bit" | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2220 | "C:\Users\admin\AppData\Local\Temp\ipscan-3.7.2-setup.exe" | C:\Users\admin\AppData\Local\Temp\ipscan-3.7.2-setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2716 | findstr /I "32-bit|Client VM" | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3104 | "java" -version | C:\ProgramData\Oracle\Java\javapath\java.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3200 | "C:\Users\admin\AppData\Local\Temp\ipscan-3.7.2-setup.exe" | C:\Users\admin\AppData\Local\Temp\ipscan-3.7.2-setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3208 | cmd /c ""C:\Program Files\Angry IP Scanner\detectjvm.cmd"" | C:\Windows\system32\cmd.exe | — | ipscan-3.7.2-setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 32 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
358
Read events
345
Write events
13
Delete events
0
Modification events
| (PID) Process: | (3200) ipscan-3.7.2-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Angry IP Scanner |
| Operation: | write | Name: | |
Value: C:\Program Files\Angry IP Scanner | |||
| (PID) Process: | (3200) ipscan-3.7.2-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Angry IP Scanner |
| Operation: | write | Name: | DisplayName |
Value: Angry IP Scanner | |||
| (PID) Process: | (3200) ipscan-3.7.2-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Angry IP Scanner |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Angry IP Scanner\uninstall.exe" | |||
| (PID) Process: | (3200) ipscan-3.7.2-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Angry IP Scanner |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\Angry IP Scanner\uninstall.exe" /S | |||
| (PID) Process: | (3200) ipscan-3.7.2-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Angry IP Scanner |
| Operation: | write | Name: | InstallLocation |
Value: "C:\Program Files\Angry IP Scanner" | |||
| (PID) Process: | (3200) ipscan-3.7.2-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Angry IP Scanner |
| Operation: | write | Name: | DisplayIcon |
Value: "C:\Program Files\Angry IP Scanner\icon.ico" | |||
| (PID) Process: | (3200) ipscan-3.7.2-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Angry IP Scanner |
| Operation: | write | Name: | Publisher |
Value: Angry IP Scanner | |||
| (PID) Process: | (3200) ipscan-3.7.2-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Angry IP Scanner |
| Operation: | write | Name: | DisplayVersion |
Value: 3.7.2 | |||
| (PID) Process: | (3200) ipscan-3.7.2-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Angry IP Scanner |
| Operation: | write | Name: | VersionMajor |
Value: 3 | |||
| (PID) Process: | (3200) ipscan-3.7.2-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Angry IP Scanner |
| Operation: | write | Name: | VersionMinor |
Value: 5 | |||
Executable files
5
Suspicious files
0
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3200 | ipscan-3.7.2-setup.exe | C:\Users\admin\AppData\Local\Temp\nsdA8D8.tmp | — | |
MD5:— | SHA256:— | |||
| 3200 | ipscan-3.7.2-setup.exe | C:\Program Files\Angry IP Scanner\detectjvm.cmd | text | |
MD5:— | SHA256:— | |||
| 3200 | ipscan-3.7.2-setup.exe | C:\Program Files\Angry IP Scanner\ipscan.exe | executable | |
MD5:— | SHA256:— | |||
| 1148 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3104 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3200 | ipscan-3.7.2-setup.exe | C:\Users\admin\AppData\Local\Temp\nsdA8D9.tmp\nsDialogs.dll | executable | |
MD5:6E64E5D5F9498058A300B26B8741D9D5 | SHA256:8D4B1C275FD1CD0782A265080B56D1AEC8D1C93EDCA5EF3B050D1D20D7B61F33 | |||
| 3200 | ipscan-3.7.2-setup.exe | C:\Program Files\Angry IP Scanner\icon.ico | image | |
MD5:55810E0D26803DC45A5B332F21694494 | SHA256:B006C23D0721D59DF1AB2C3D885DB21A8752BF3AF67F318407E5C4F621B109E0 | |||
| 3200 | ipscan-3.7.2-setup.exe | C:\Users\admin\AppData\Local\Temp\nsdA8D9.tmp\modern-wizard.bmp | image | |
MD5:571986BB6E3EED28C772E9DFA1B2D87E | SHA256:8416E0209E7C1497EF84173F52B623EB38D86BAB59886FE99317D8F557BF66F8 | |||
| 3200 | ipscan-3.7.2-setup.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Angry IP Scanner.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3200 | ipscan-3.7.2-setup.exe | C:\Program Files\Angry IP Scanner\uninstall.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report