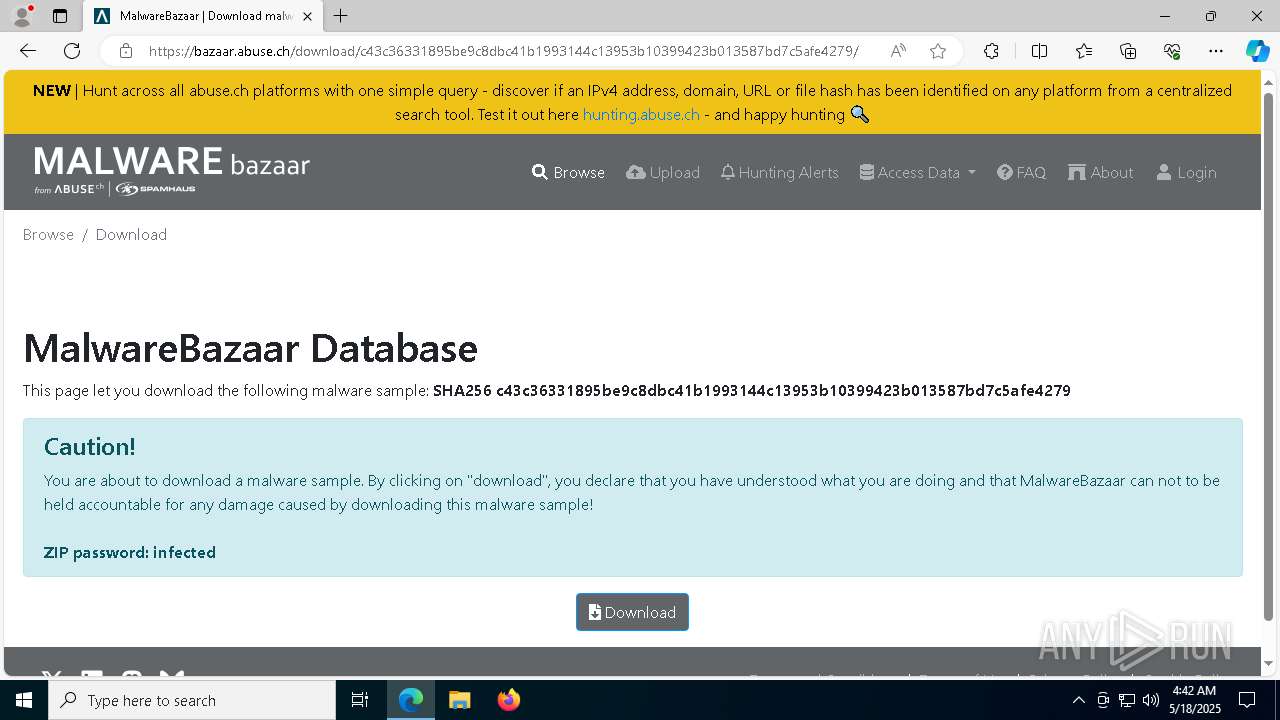
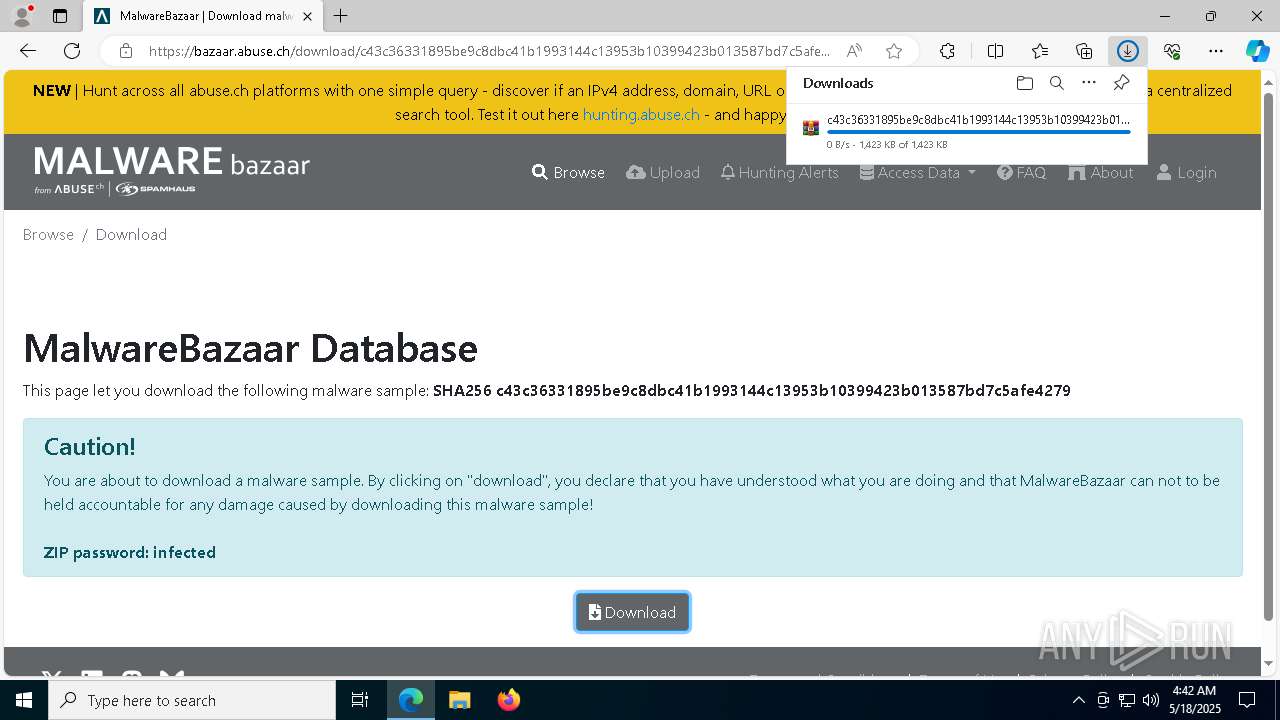
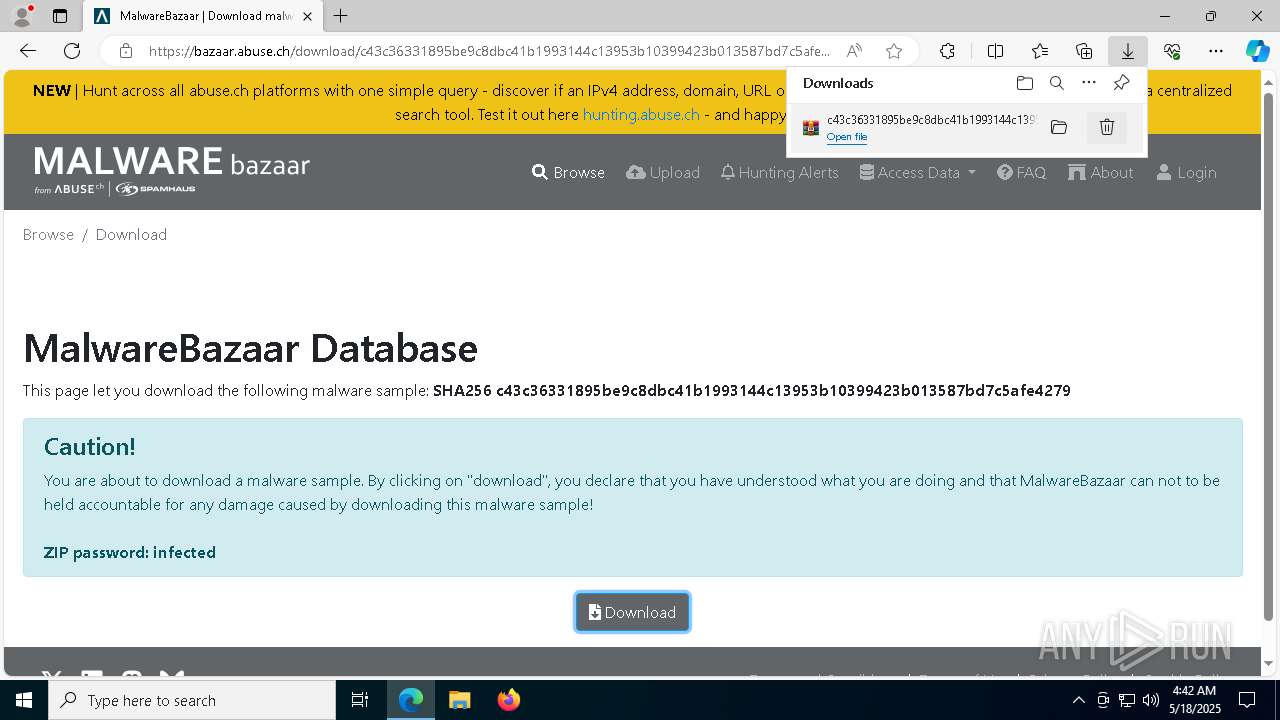
| URL: | https://bazaar.abuse.ch/download/c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279/ |
| Full analysis: | https://app.any.run/tasks/18a29853-07a4-4eff-94cf-6da92de62941 |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | May 18, 2025, 04:41:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8421C2F1E44FFCAFCB6EF4A3EBB0B940 |
| SHA1: | 933718F914DF76CDE98326B9322FBDEBFF37785A |
| SHA256: | 34C3C5886F2E2DDD4E2A8847035A106E175390AC4456039DC11CB3FC90C88F24 |
| SSDEEP: | 3:N8N0uDWB4GWORsHUdDWcQAUowoQHES7:23G0Oe09WcQAUowoSES7 |
MALICIOUS
DCRAT mutex has been found
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
- dwm.exe (PID: 6036)
DARKCRYSTAL has been detected (SURICATA)
- dwm.exe (PID: 6036)
Connects to the CnC server
- dwm.exe (PID: 6036)
SUSPICIOUS
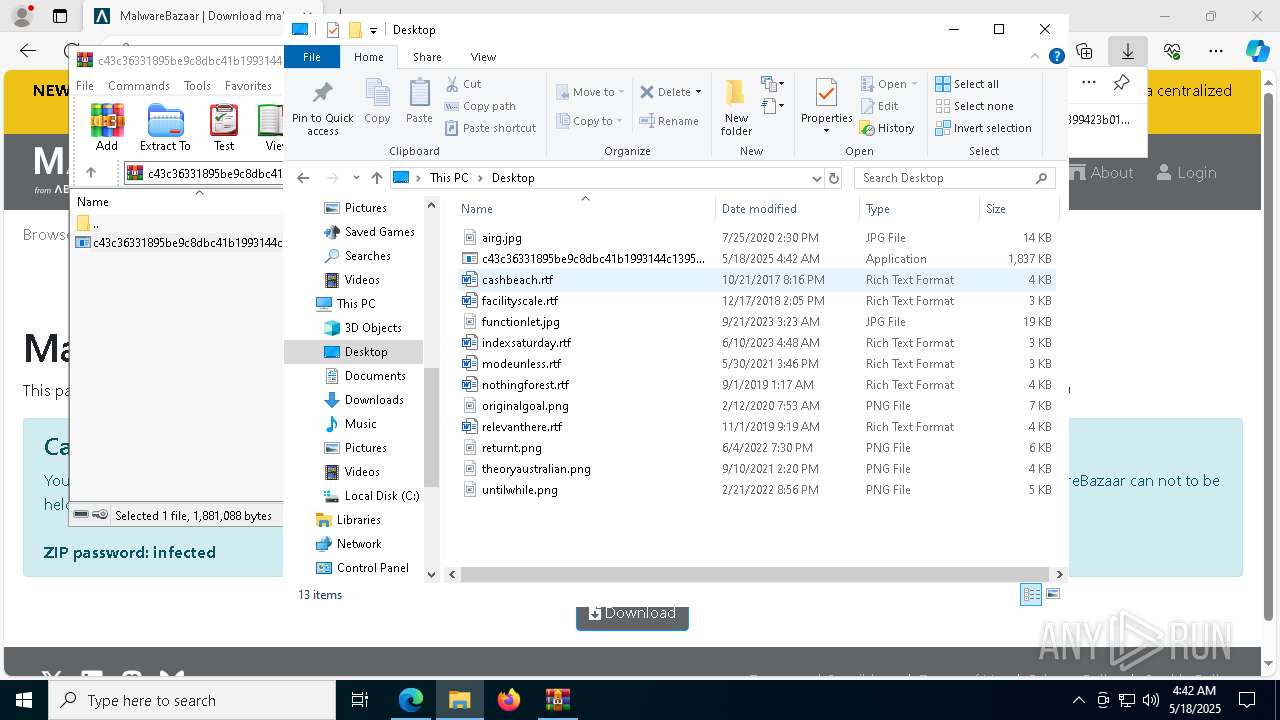
The process creates files with name similar to system file names
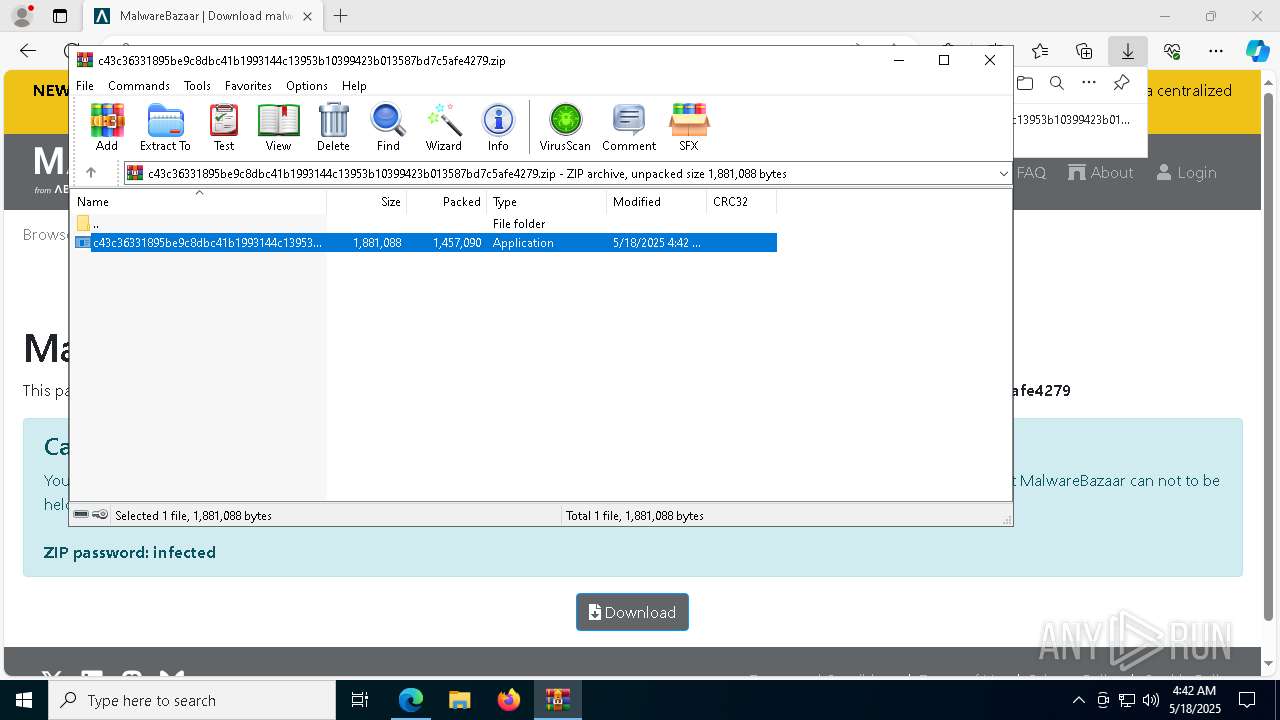
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
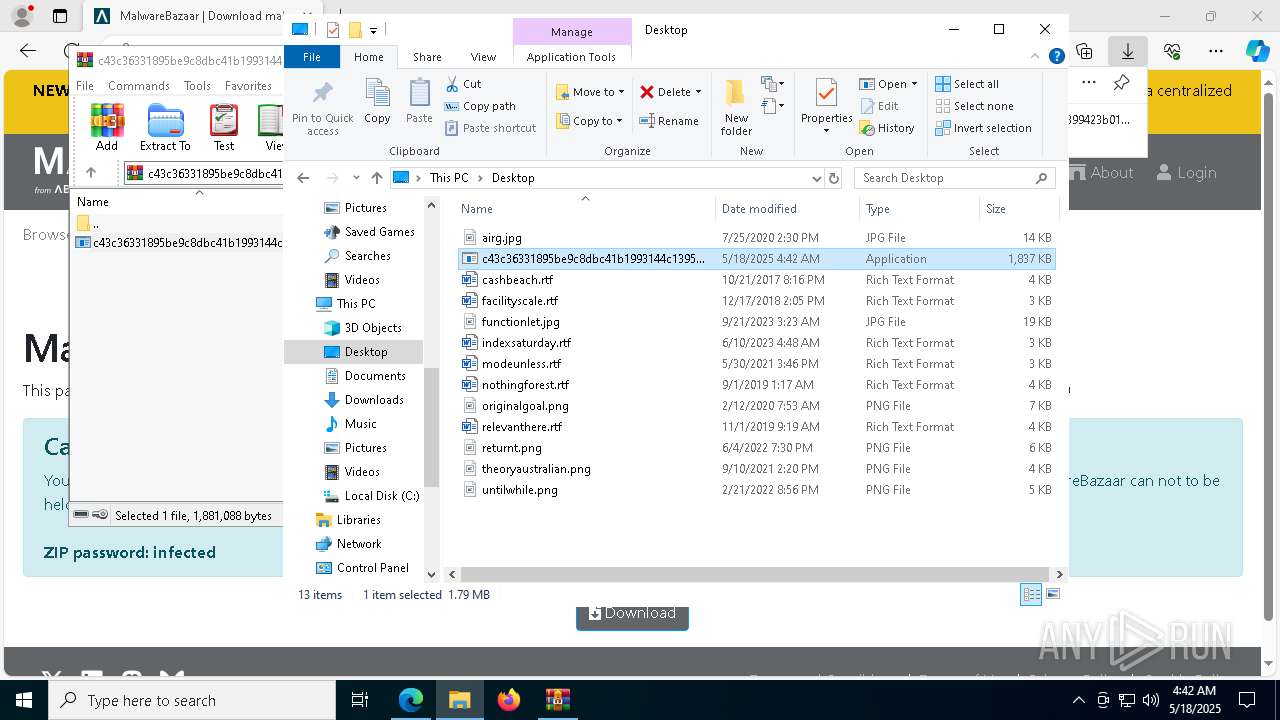
Executable content was dropped or overwritten
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
- dwm.exe (PID: 6036)
Reads the date of Windows installation
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
Reads security settings of Internet Explorer
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
Starts CMD.EXE for commands execution
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
Executing commands from a ".bat" file
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
Starts application with an unusual extension
- cmd.exe (PID: 6940)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 6940)
The executable file from the user directory is run by the CMD process
- dwm.exe (PID: 6036)
INFO
Reads the computer name
- identity_helper.exe (PID: 6768)
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
- dwm.exe (PID: 6036)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2516)
Reads Environment values
- identity_helper.exe (PID: 6768)
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
- dwm.exe (PID: 6036)
Checks supported languages
- identity_helper.exe (PID: 6768)
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
- dwm.exe (PID: 6036)
- chcp.com (PID: 6768)
Application launched itself
- msedge.exe (PID: 2516)
Executable content was dropped or overwritten
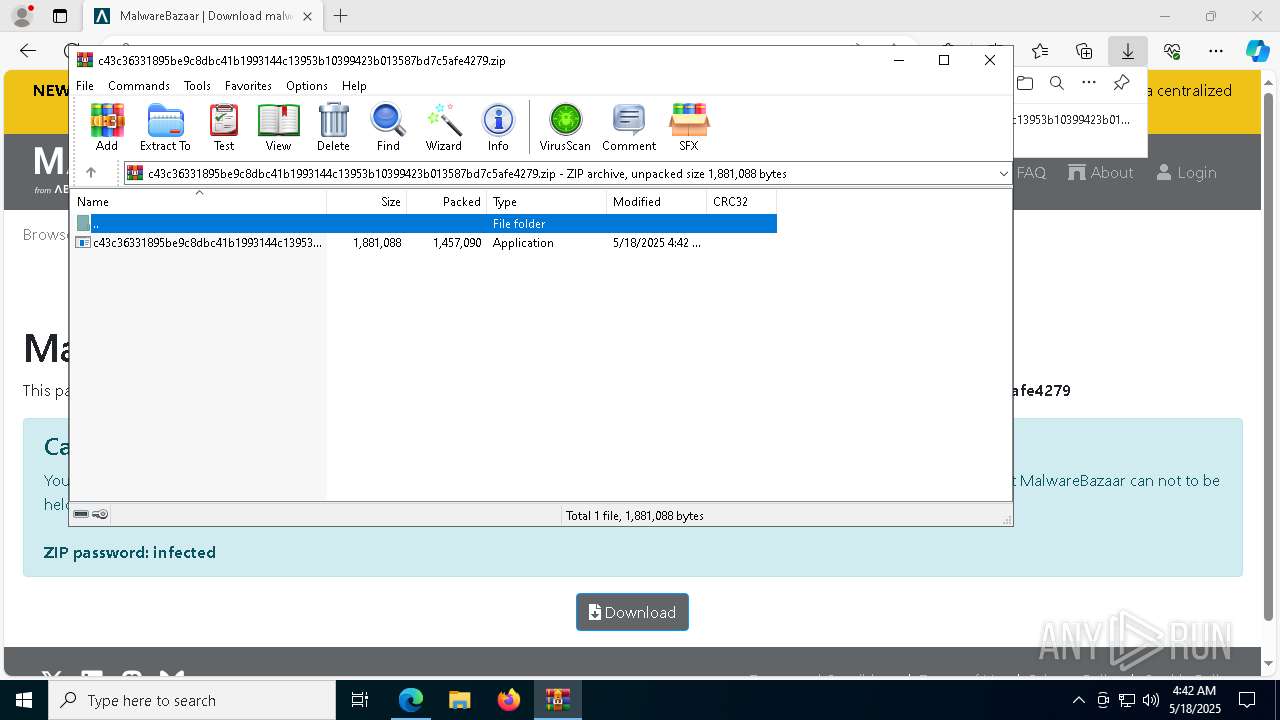
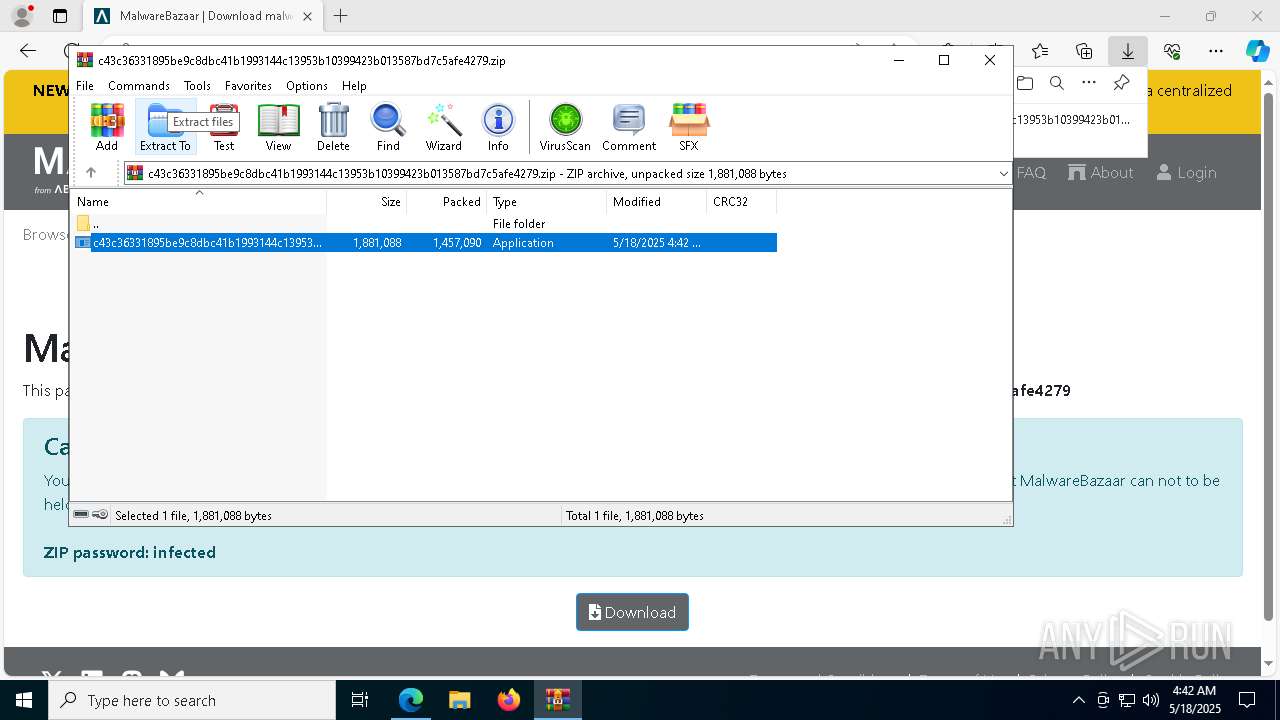
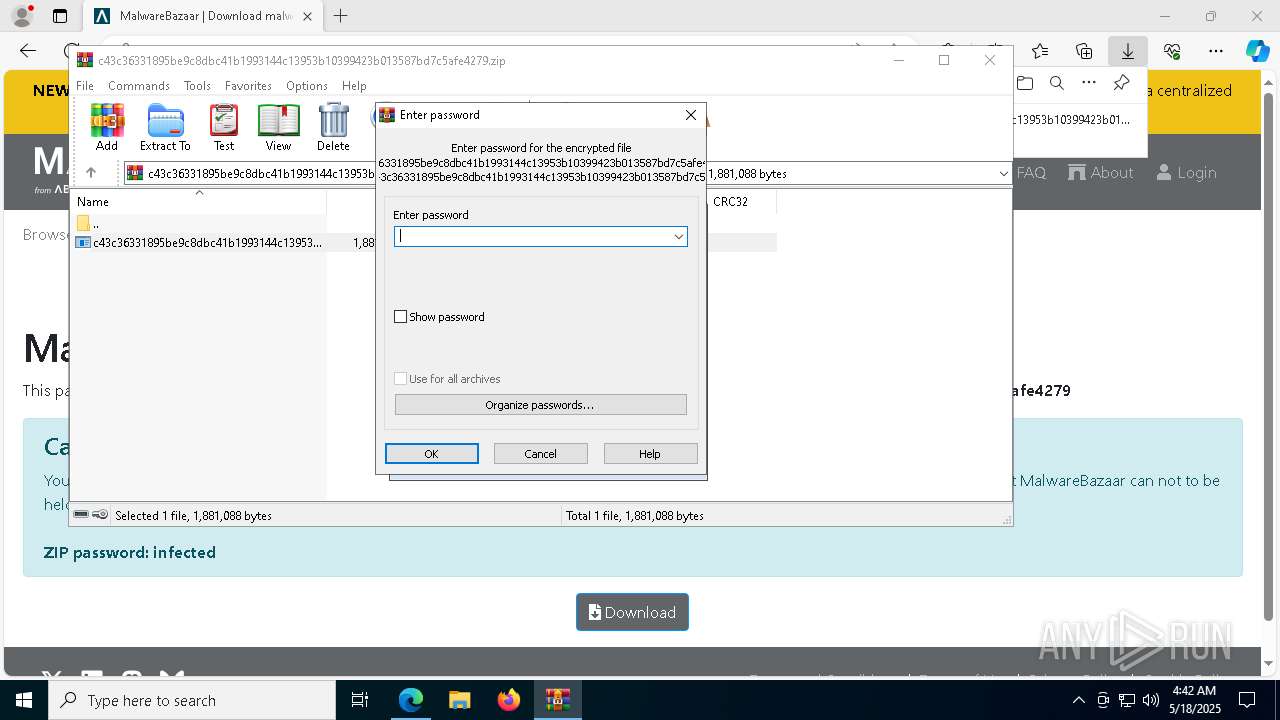
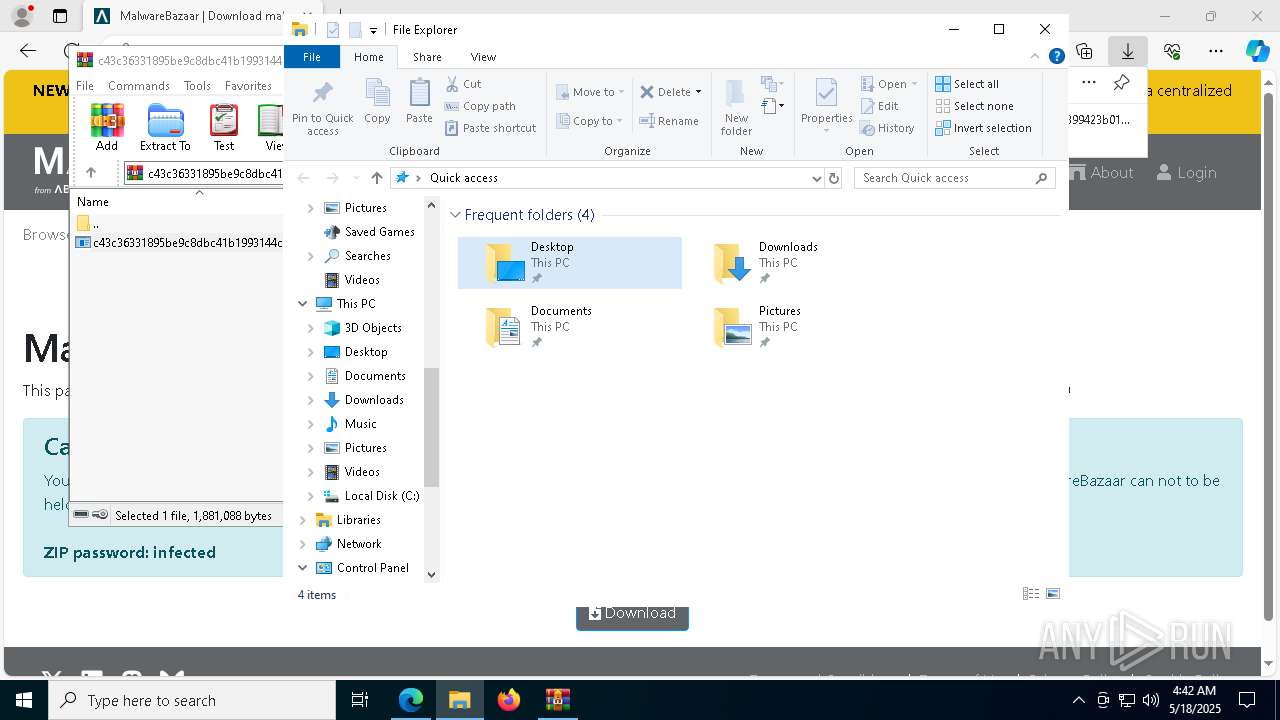
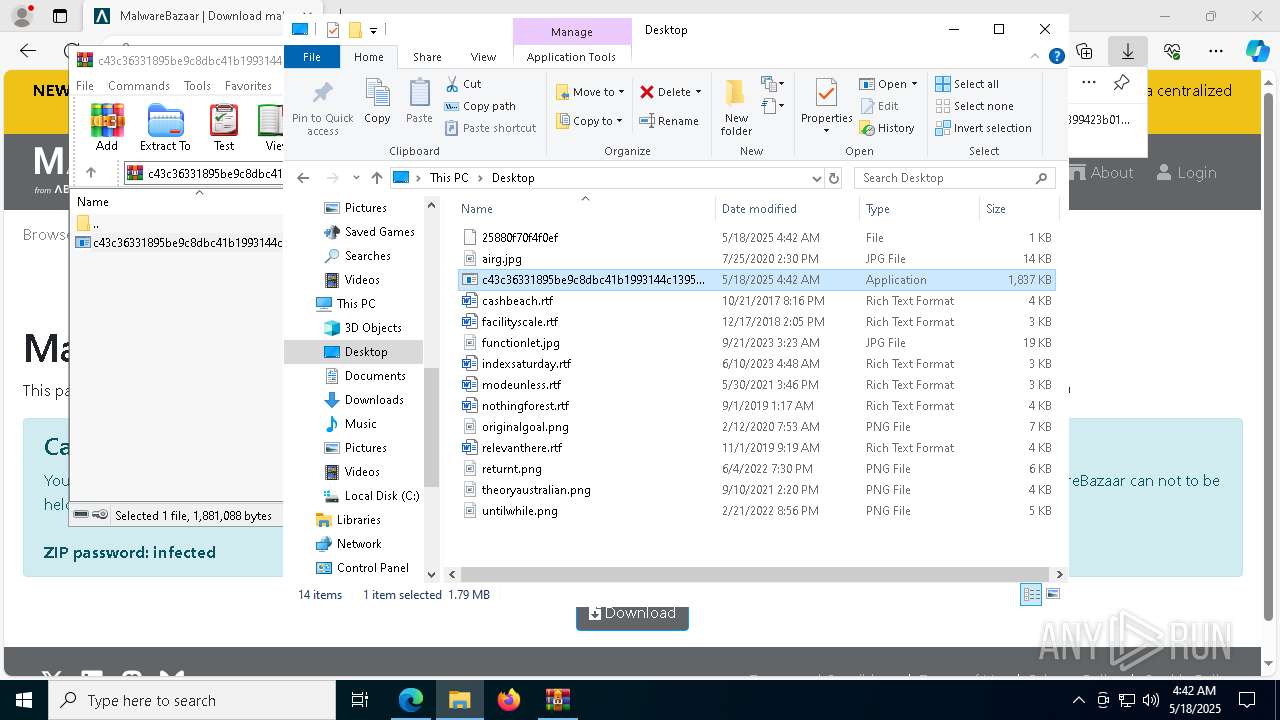
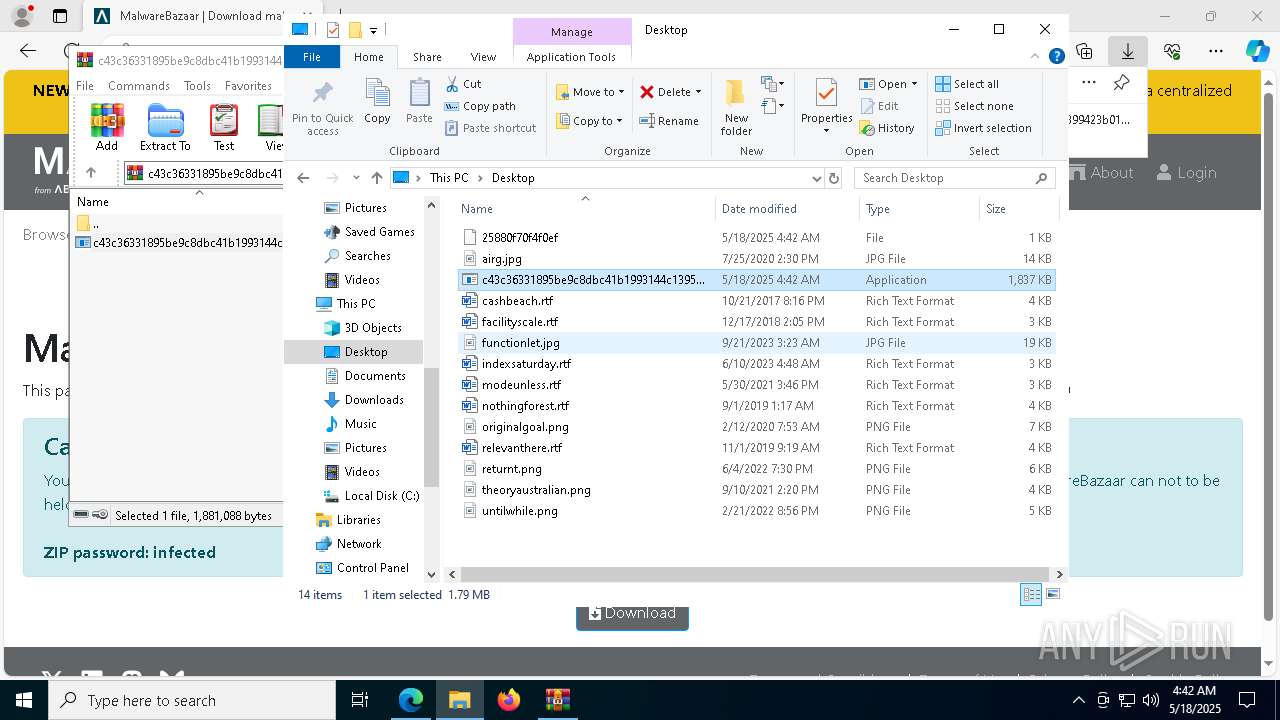
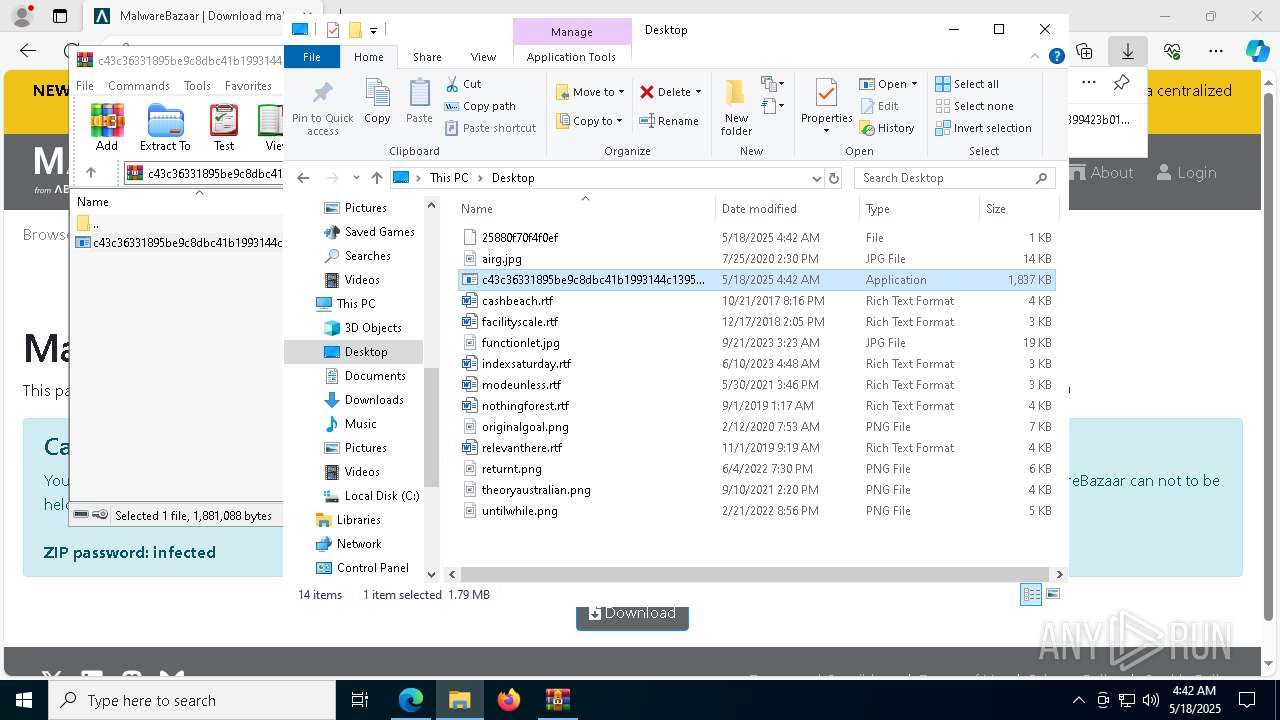
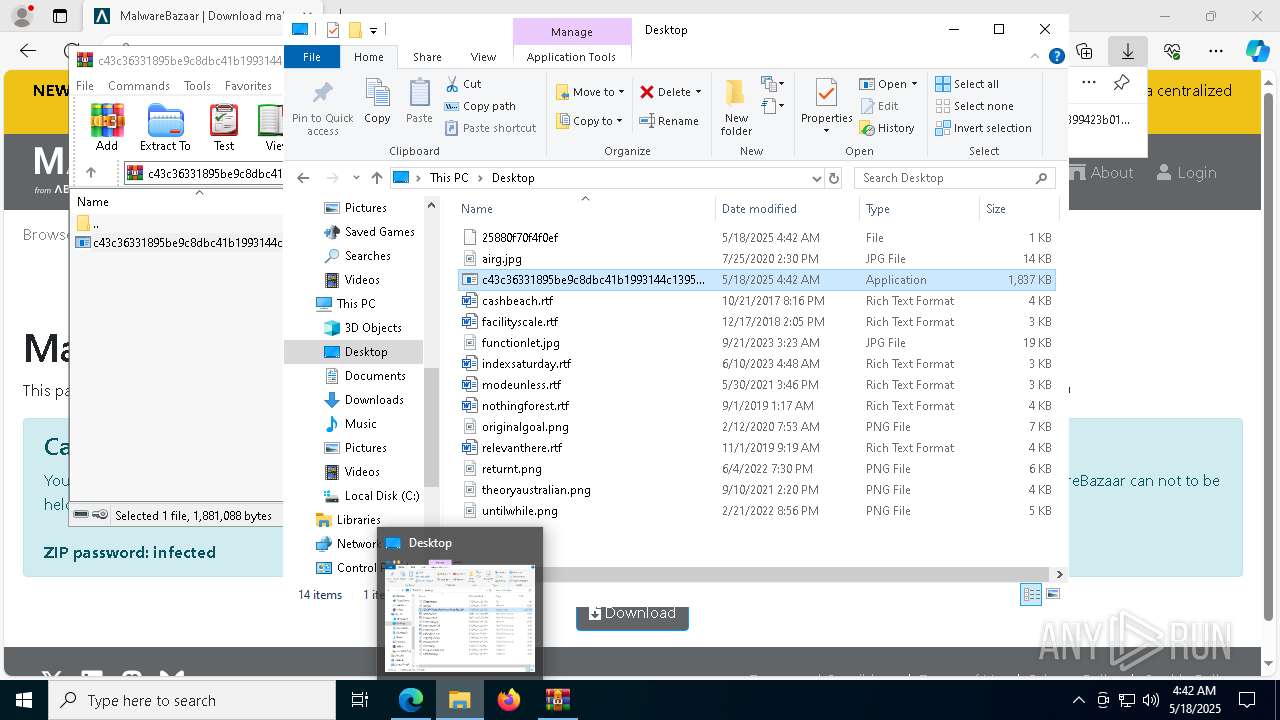
- WinRAR.exe (PID: 4108)
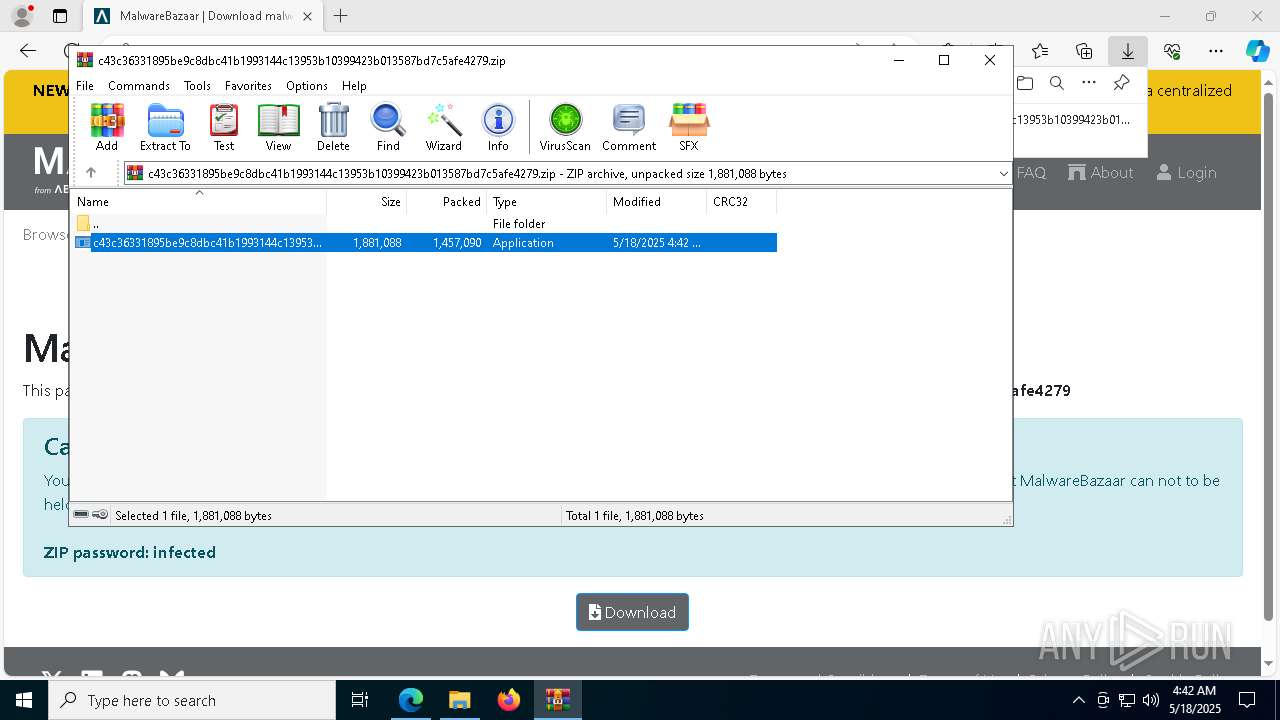
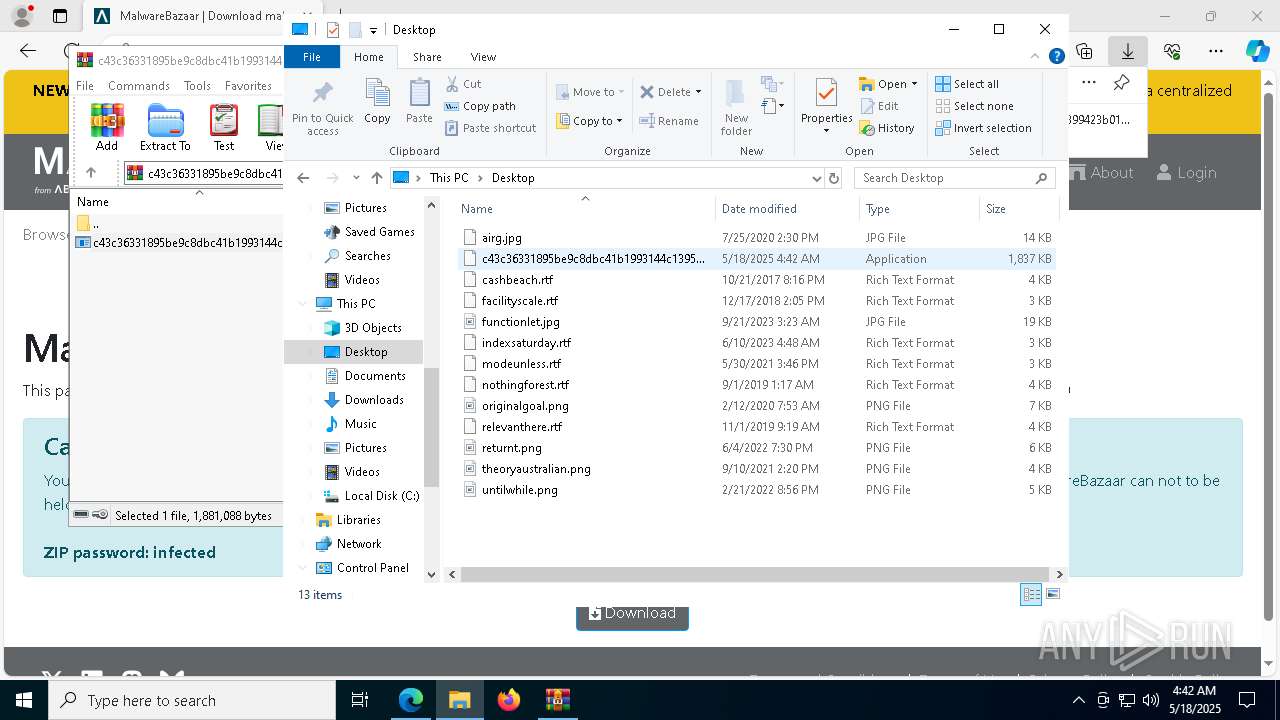
Manual execution by a user
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
Reads the machine GUID from the registry
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
- dwm.exe (PID: 6036)
Creates files in the program directory
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
Failed to create an executable file in Windows directory
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
Create files in a temporary directory
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
Process checks computer location settings
- c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.exe (PID: 8012)
Changes the display of characters in the console
- cmd.exe (PID: 6940)
Disables trace logs
- dwm.exe (PID: 6036)
Checks proxy server information
- dwm.exe (PID: 6036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
177
Monitored processes
47
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6812 --field-trial-handle=2304,i,1890671157583602383,16814172171697314236,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1096 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6484 --field-trial-handle=2304,i,1890671157583602383,16814172171697314236,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=6788 --field-trial-handle=2304,i,1890671157583602383,16814172171697314236,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2344 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://bazaar.abuse.ch/download/c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279/" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2692 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6052 --field-trial-handle=2304,i,1890671157583602383,16814172171697314236,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
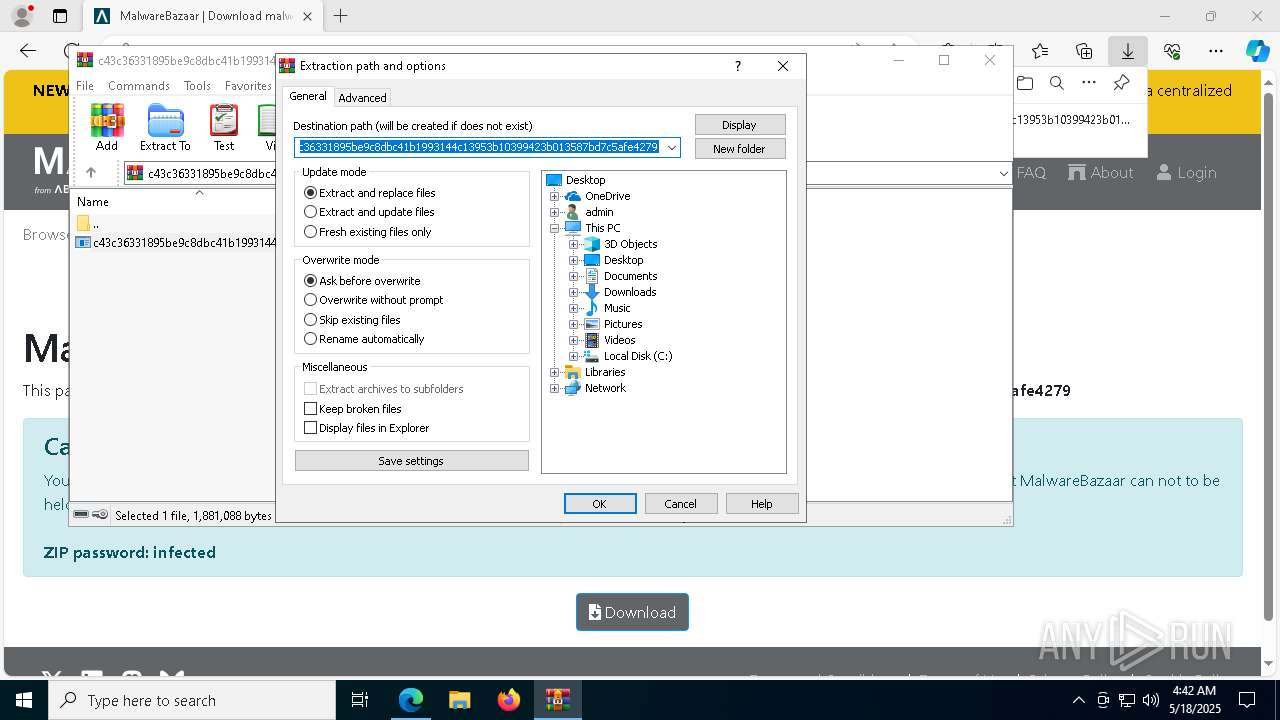
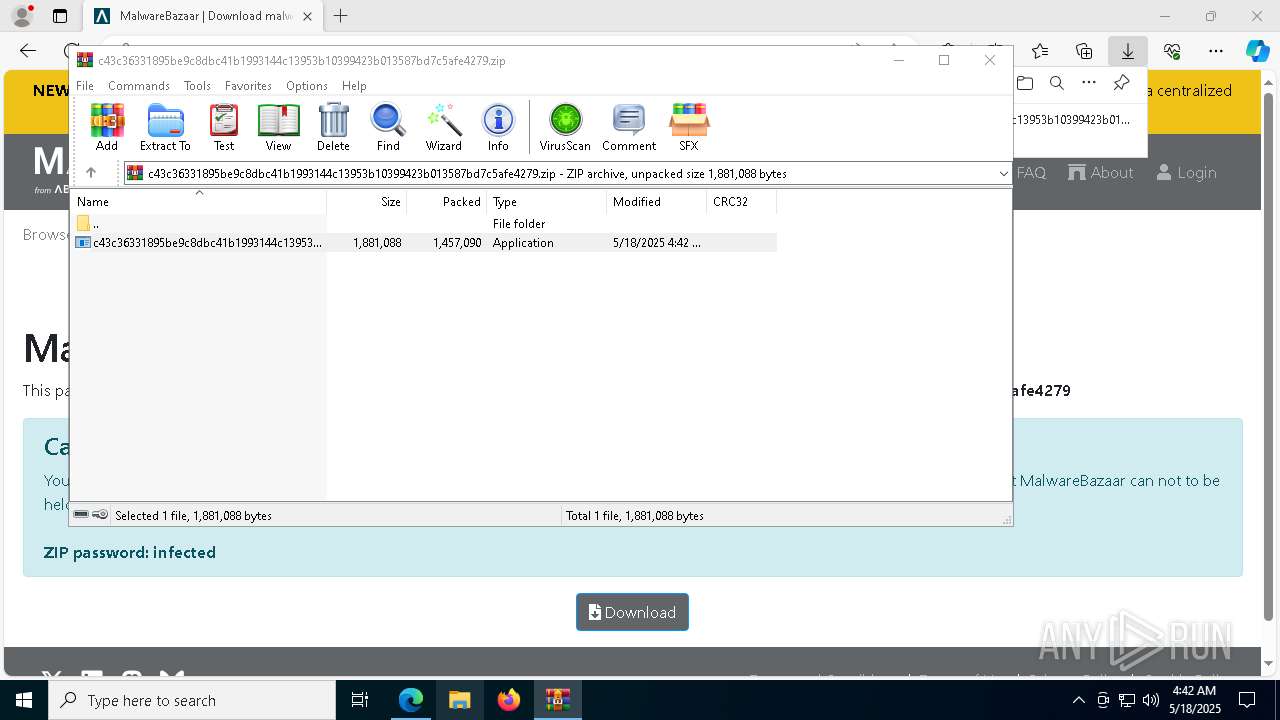
| 4108 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\c43c36331895be9c8dbc41b1993144c13953b10399423b013587bd7c5afe4279.zip" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4756 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffc881c5fd8,0x7ffc881c5fe4,0x7ffc881c5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
10 056
Read events
9 995
Write events
48
Delete events
13
Modification events
| (PID) Process: | (2516) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2516) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F7E777EAF7932F00 | |||
| (PID) Process: | (2516) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1BD882EAF7932F00 | |||
| (PID) Process: | (2516) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2516) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2516) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2516) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E57EF17B-FEB5-45FE-8447-B7C49EE4CEA9} | |||
| (PID) Process: | (2516) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F4F19657-4430-4F32-AC61-894266642225} | |||
| (PID) Process: | (2516) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {93149A84-E2AE-4E7D-8BED-208904DEFF53} | |||
| (PID) Process: | (2516) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0DB93611-E5A1-44F2-9527-618191A749F2} | |||
Executable files
20
Suspicious files
92
Text files
36
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2516 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c083.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c083.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2516 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c083.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2516 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c083.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2516 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c0a2.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2516 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
47
DNS requests
53
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5260 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5260 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6036 | dwm.exe | POST | 200 | 77.222.61.245:80 | http://sagefierce.temp.swtest.ru/pipephpPollupdategeneratortemp.php | unknown | — | — | malicious |
6036 | dwm.exe | POST | 200 | 77.222.61.245:80 | http://sagefierce.temp.swtest.ru/pipephpPollupdategeneratortemp.php | unknown | — | — | malicious |
6036 | dwm.exe | POST | 200 | 77.222.61.245:80 | http://sagefierce.temp.swtest.ru/pipephpPollupdategeneratortemp.php | unknown | — | — | malicious |
6036 | dwm.exe | POST | 200 | 77.222.61.245:80 | http://sagefierce.temp.swtest.ru/pipephpPollupdategeneratortemp.php | unknown | — | — | malicious |
6036 | dwm.exe | POST | 200 | 77.222.61.245:80 | http://sagefierce.temp.swtest.ru/pipephpPollupdategeneratortemp.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2516 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7316 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7316 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7316 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7316 | msedge.exe | 146.75.122.49:443 | bazaar.abuse.ch | FASTLY | US | whitelisted |
7316 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
bazaar.abuse.ch |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7316 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7316 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
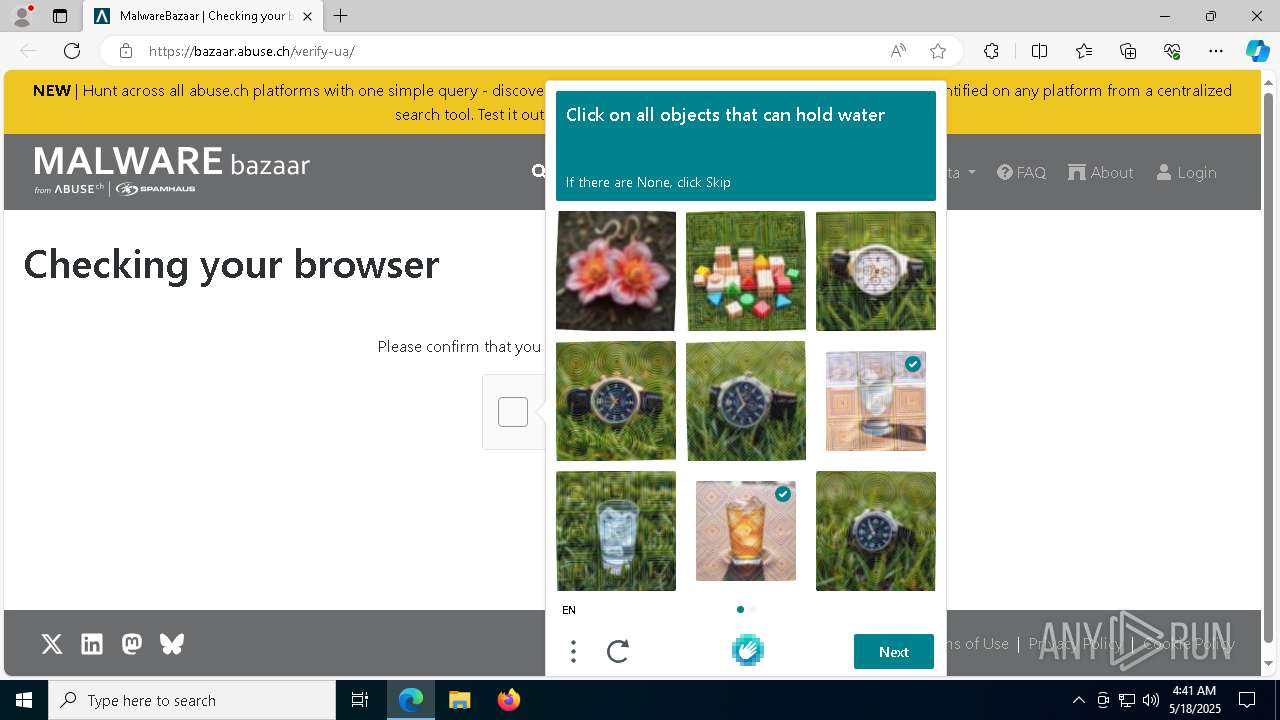
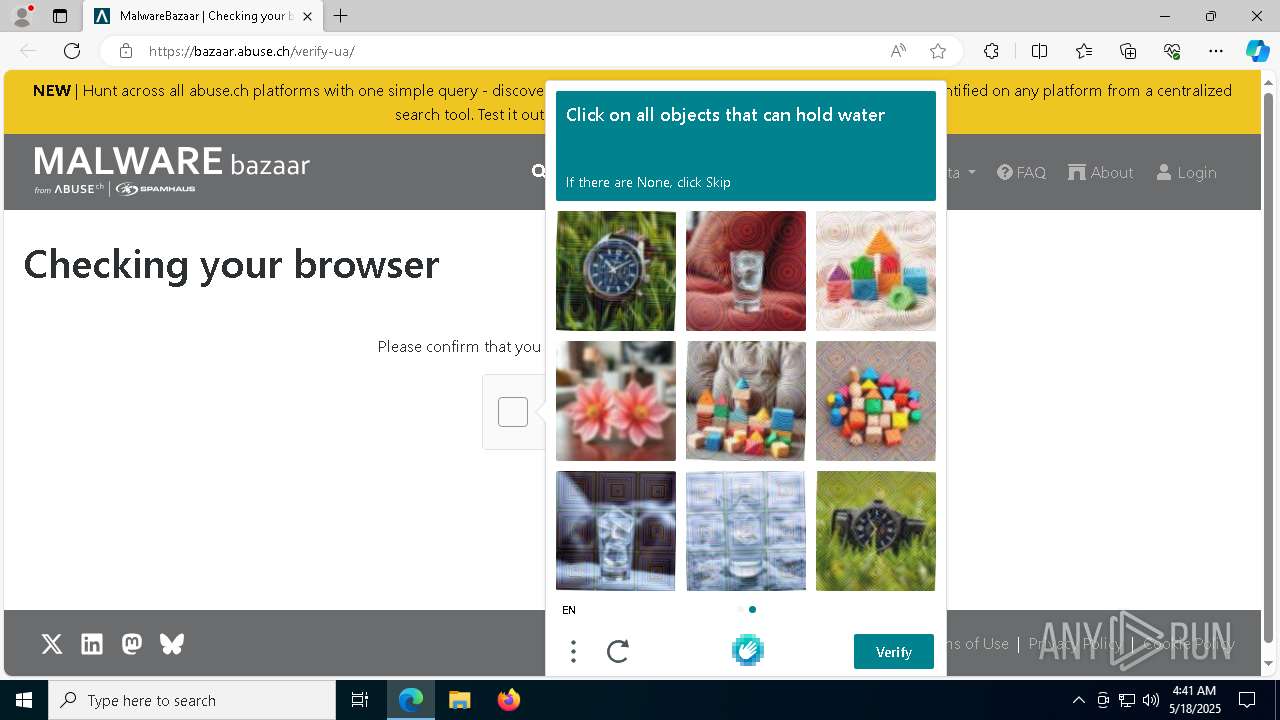
7316 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
7316 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
7316 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7316 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET TA_ABUSED_SERVICES Commonly Abused Domain Service Domain in DNS Lookup (temp .swtest .ru) |
6036 | dwm.exe | A Network Trojan was detected | REMOTE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
6036 | dwm.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Check-in (POST) |