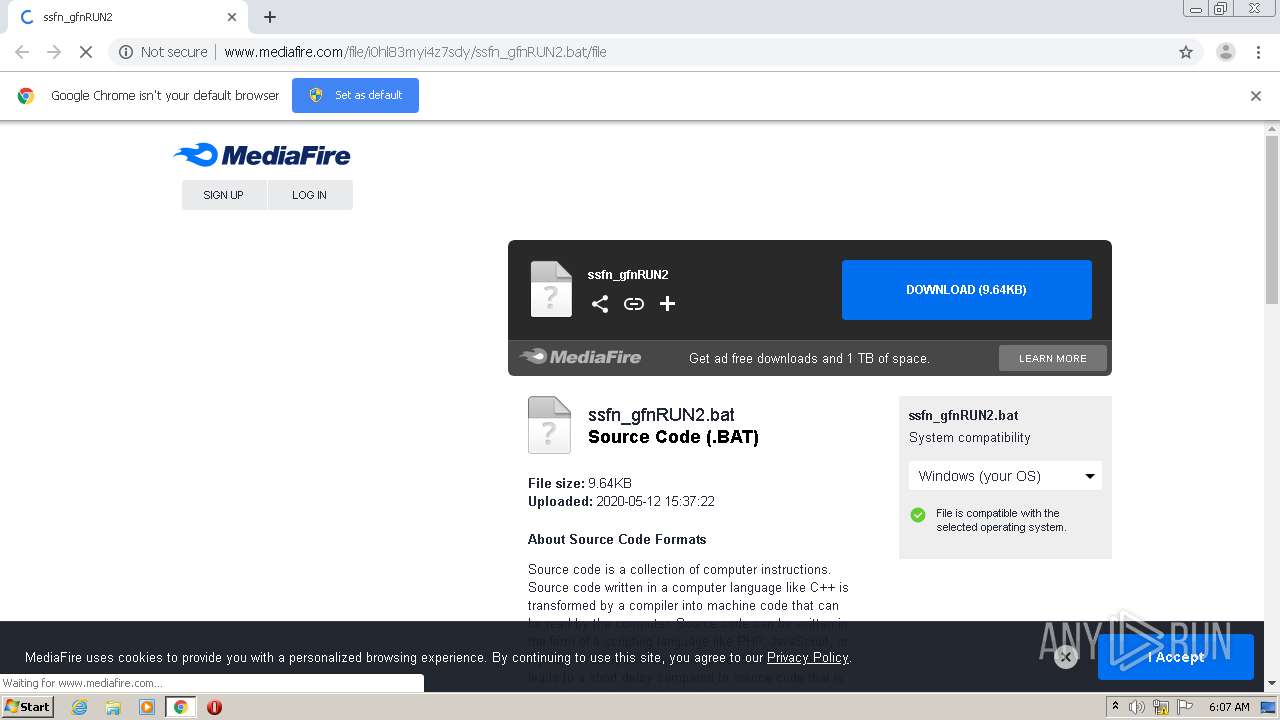
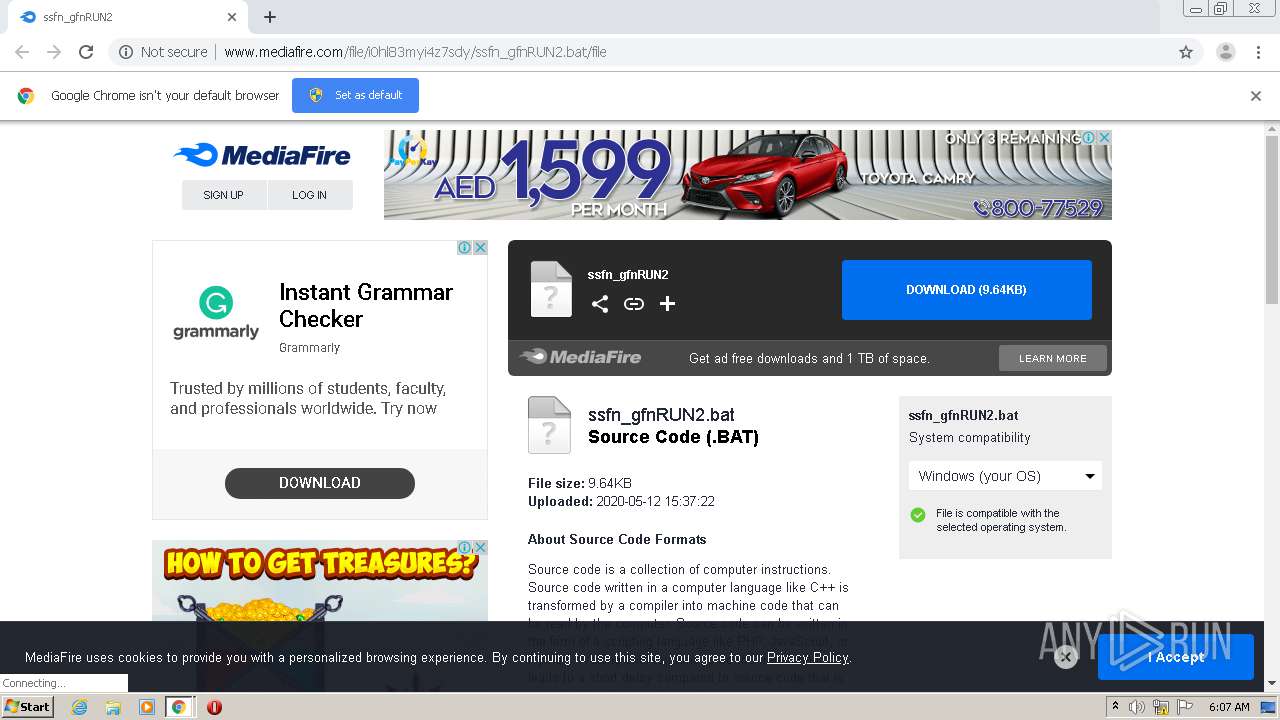
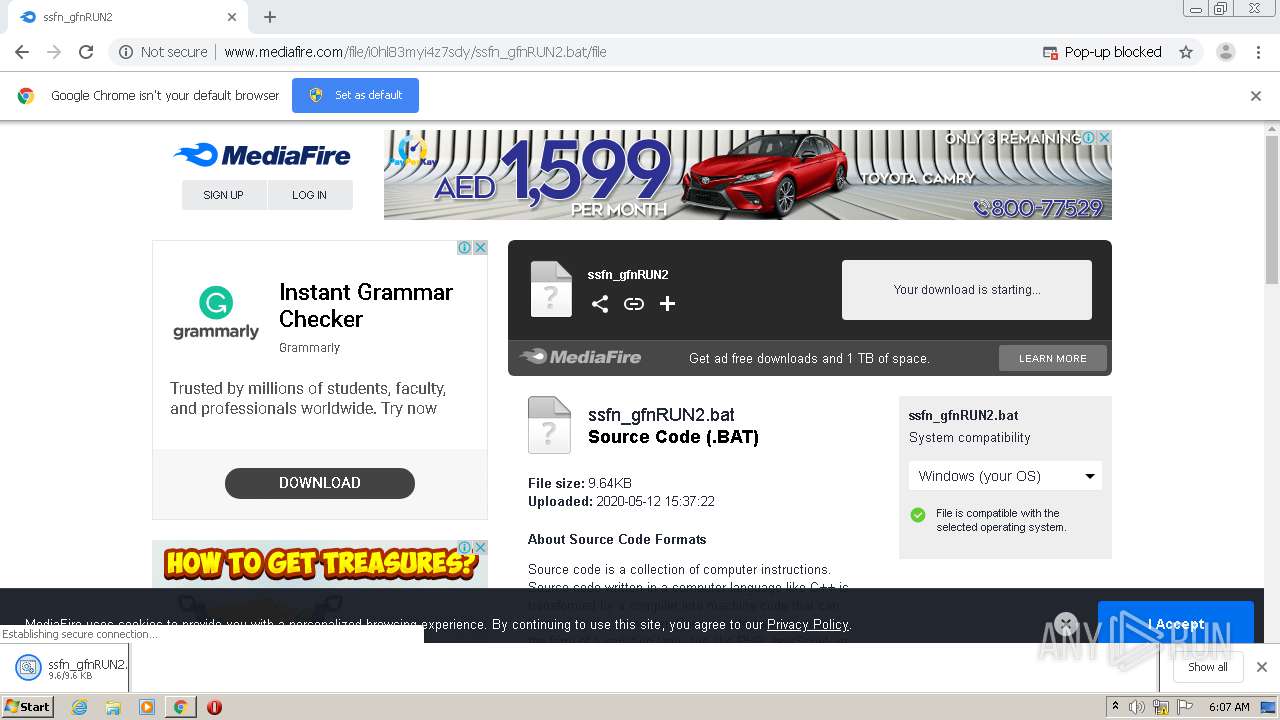
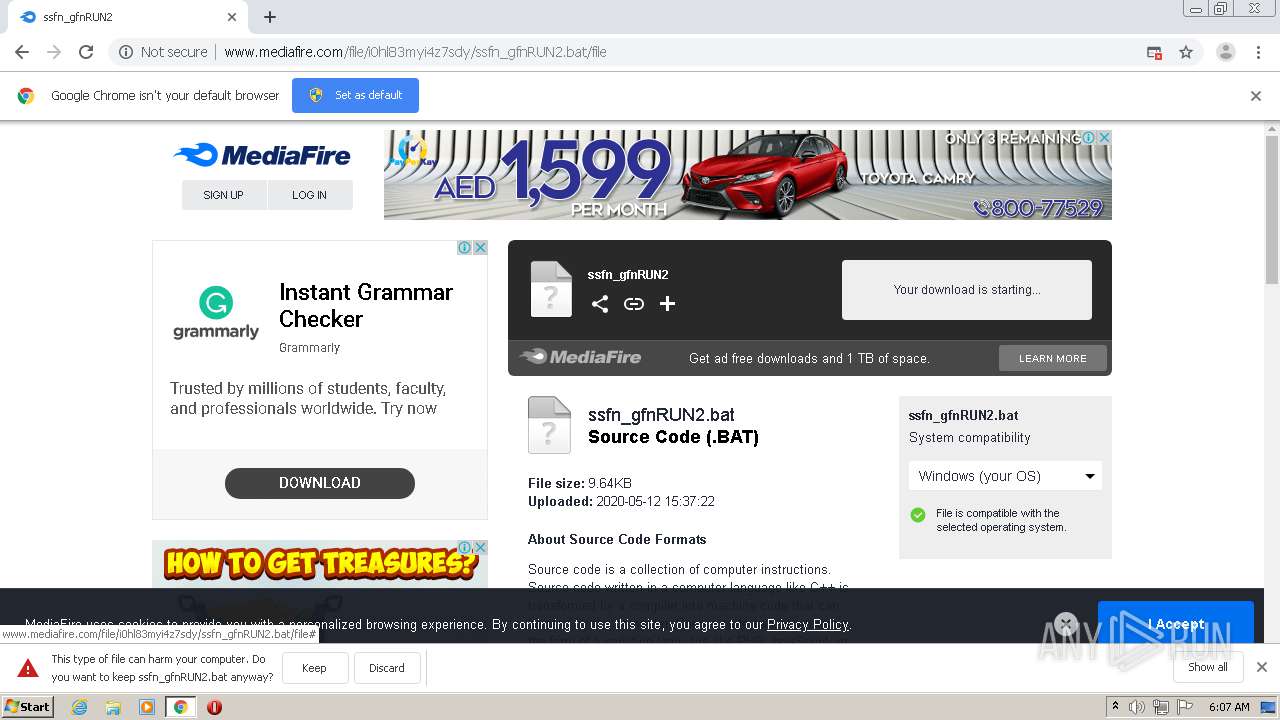
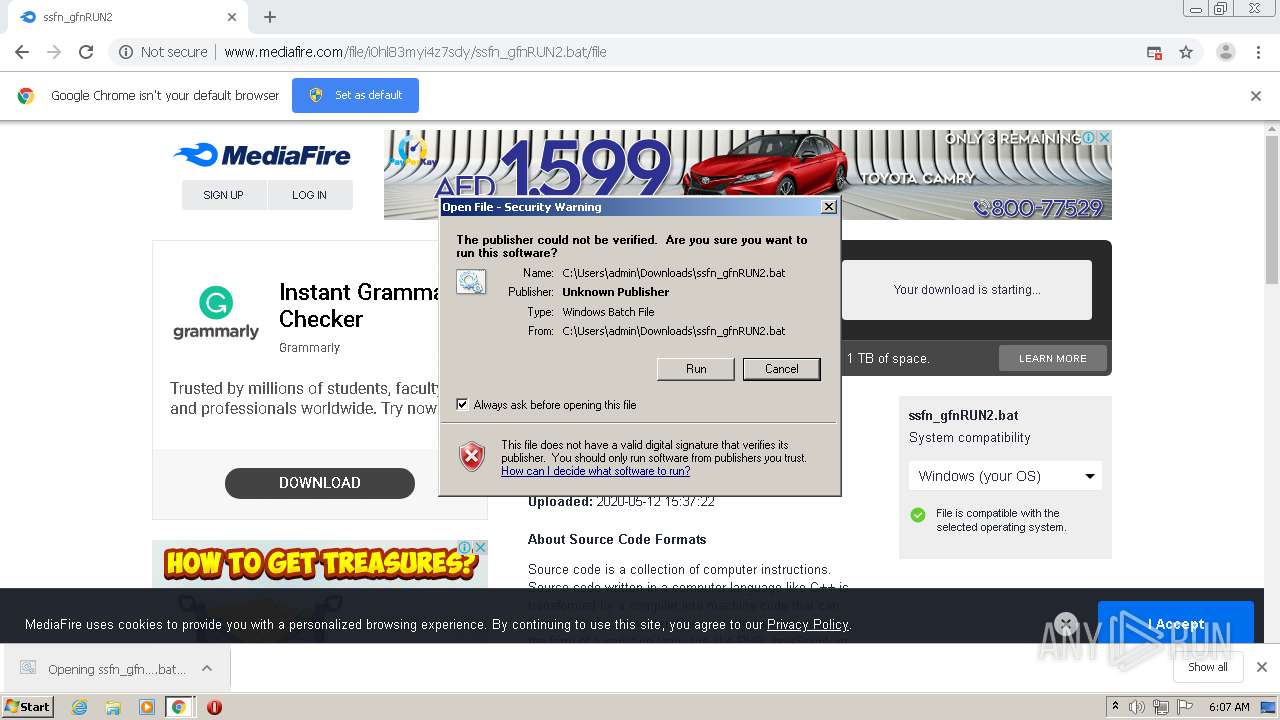
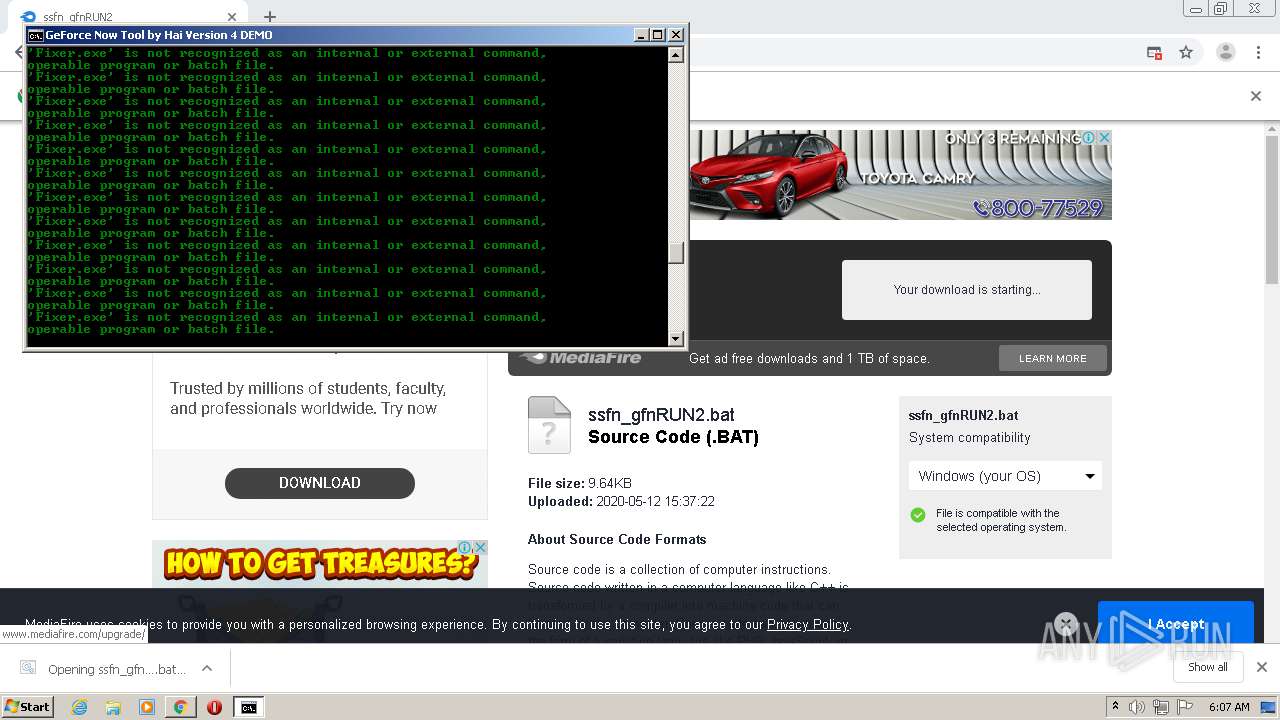
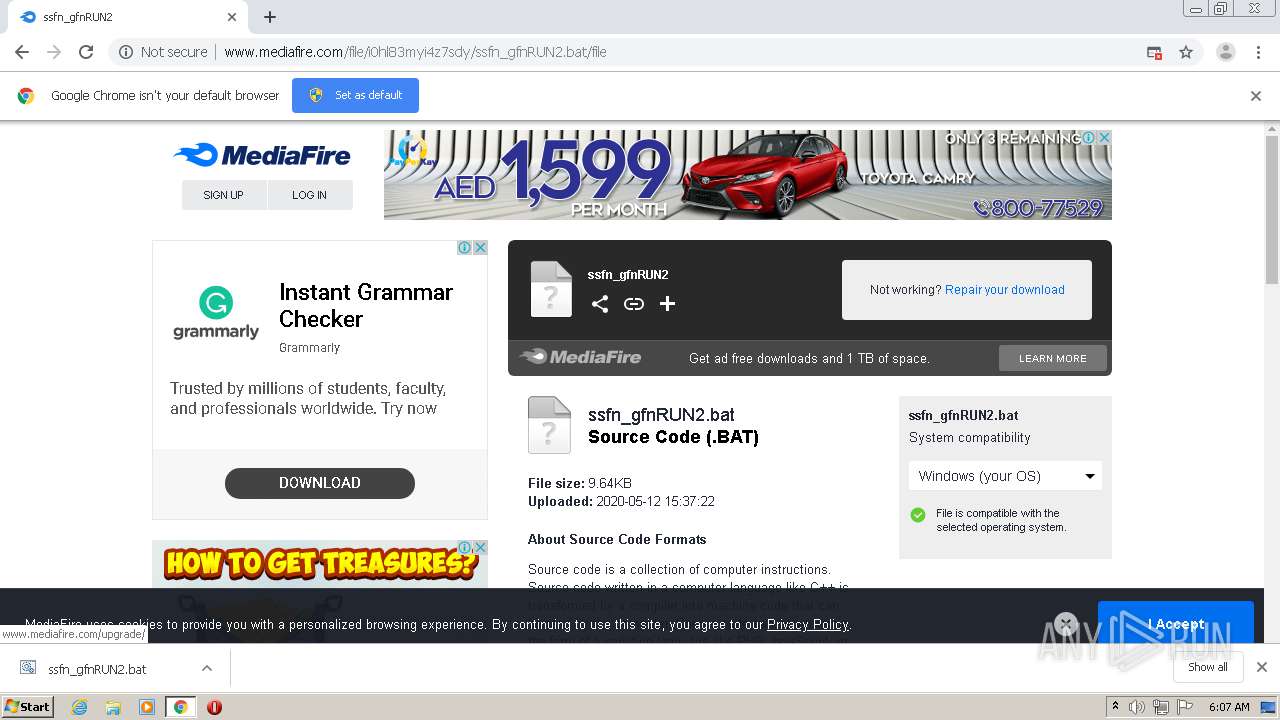
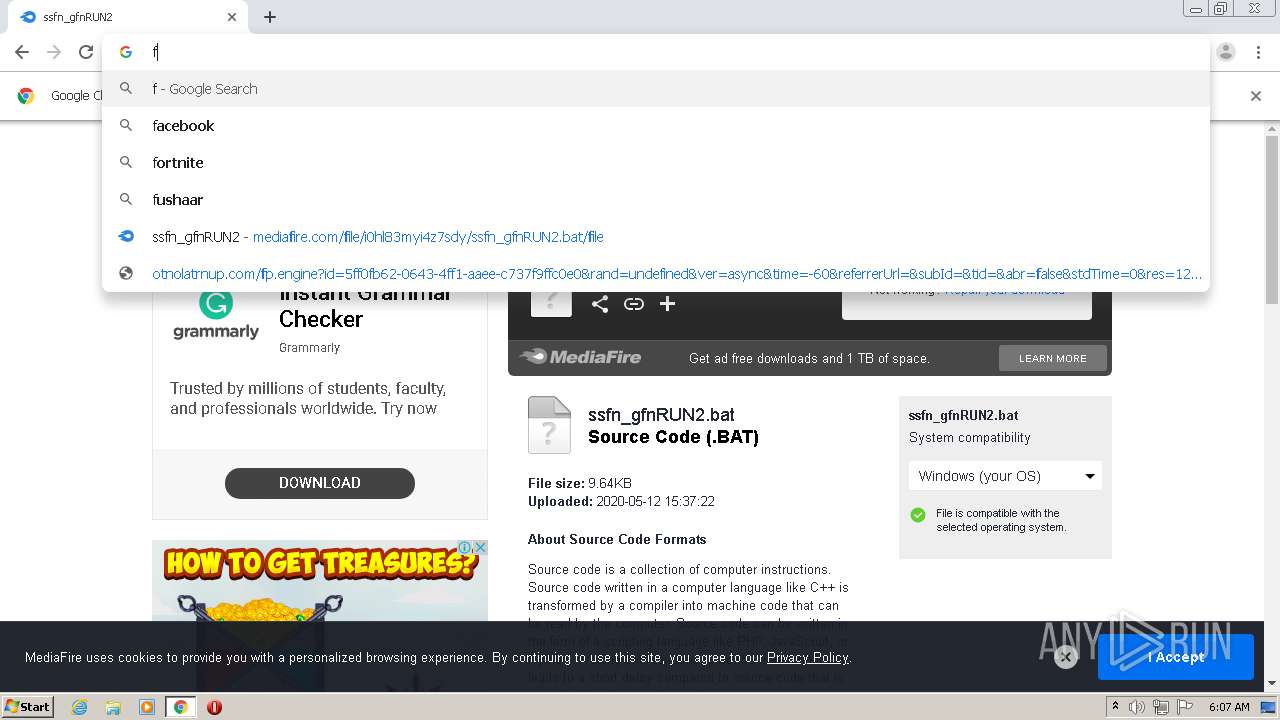
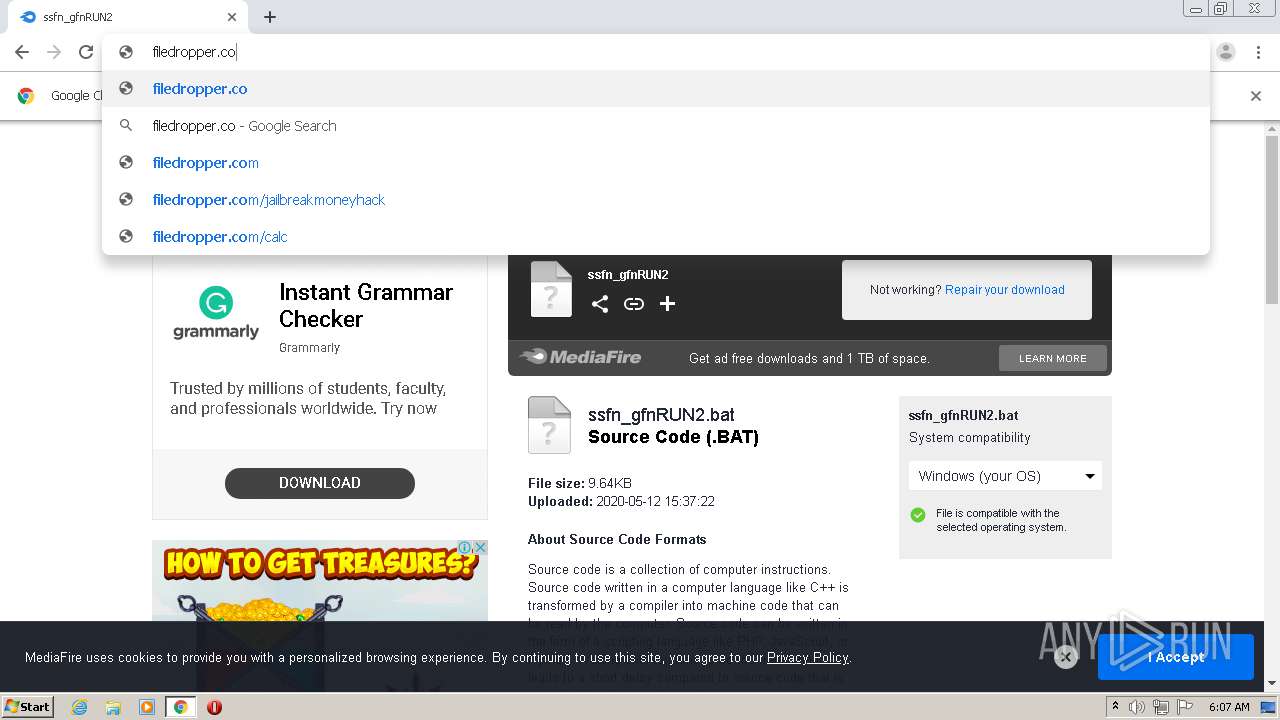
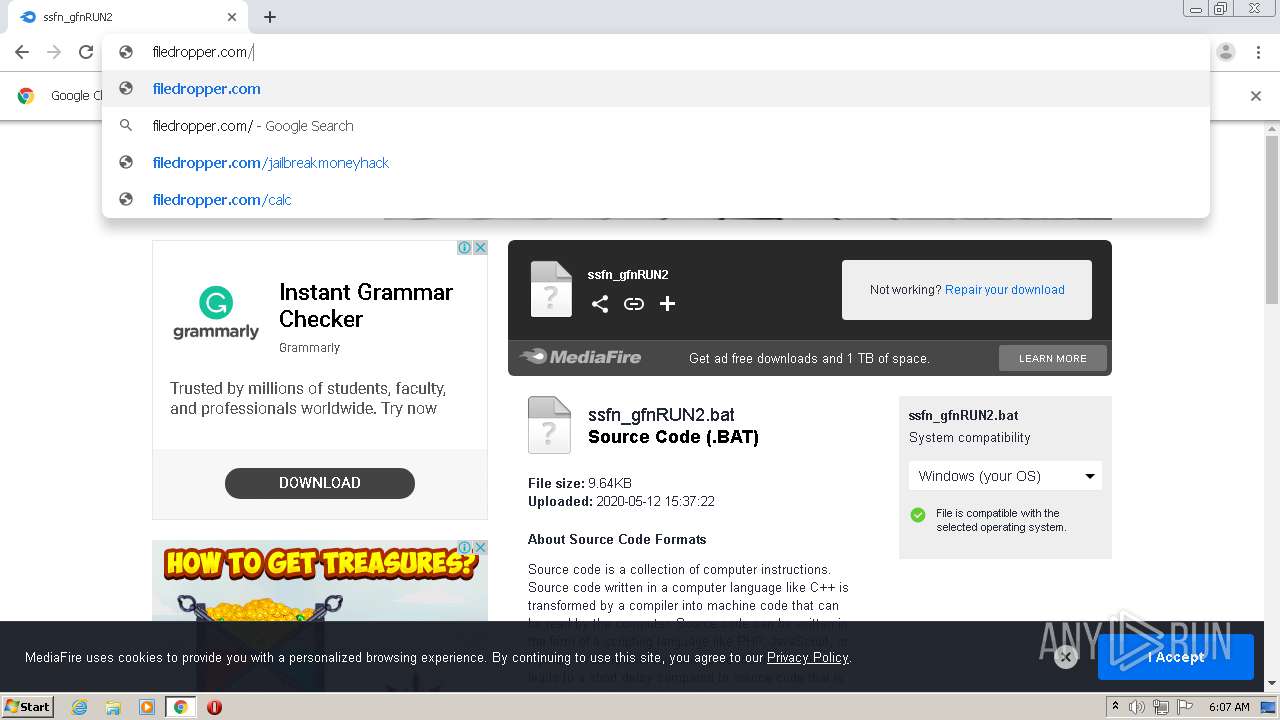
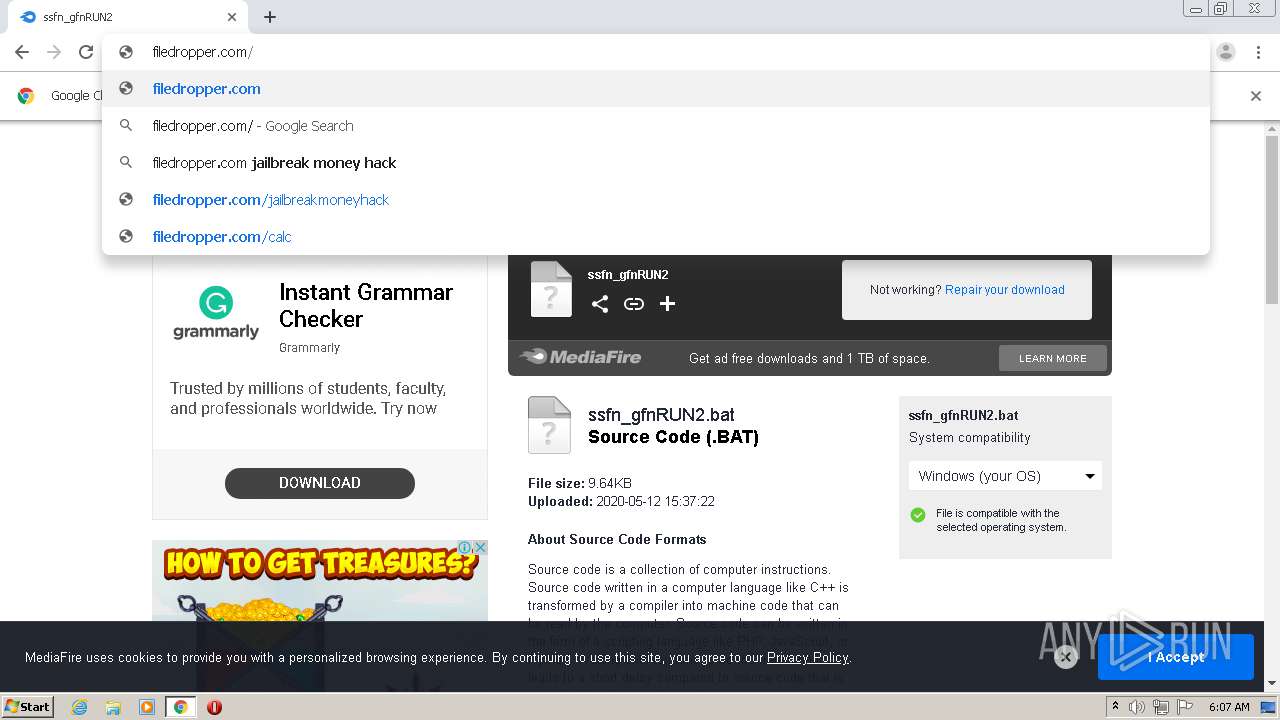
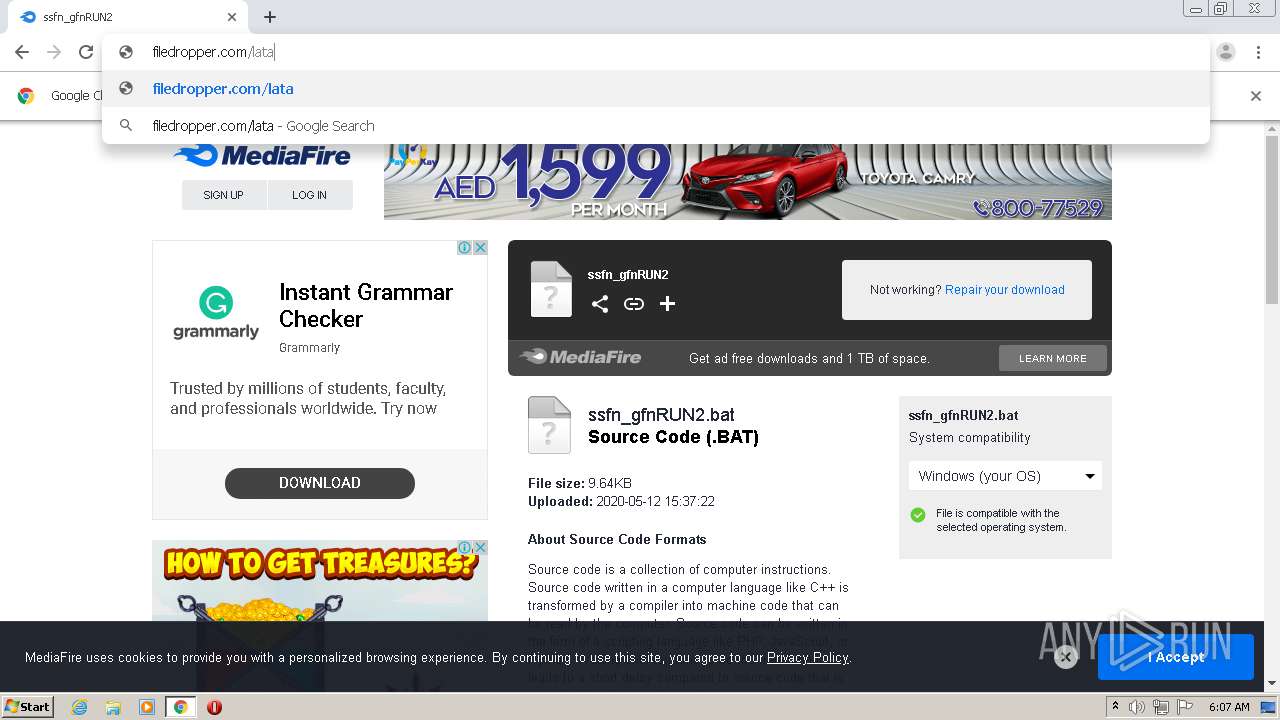
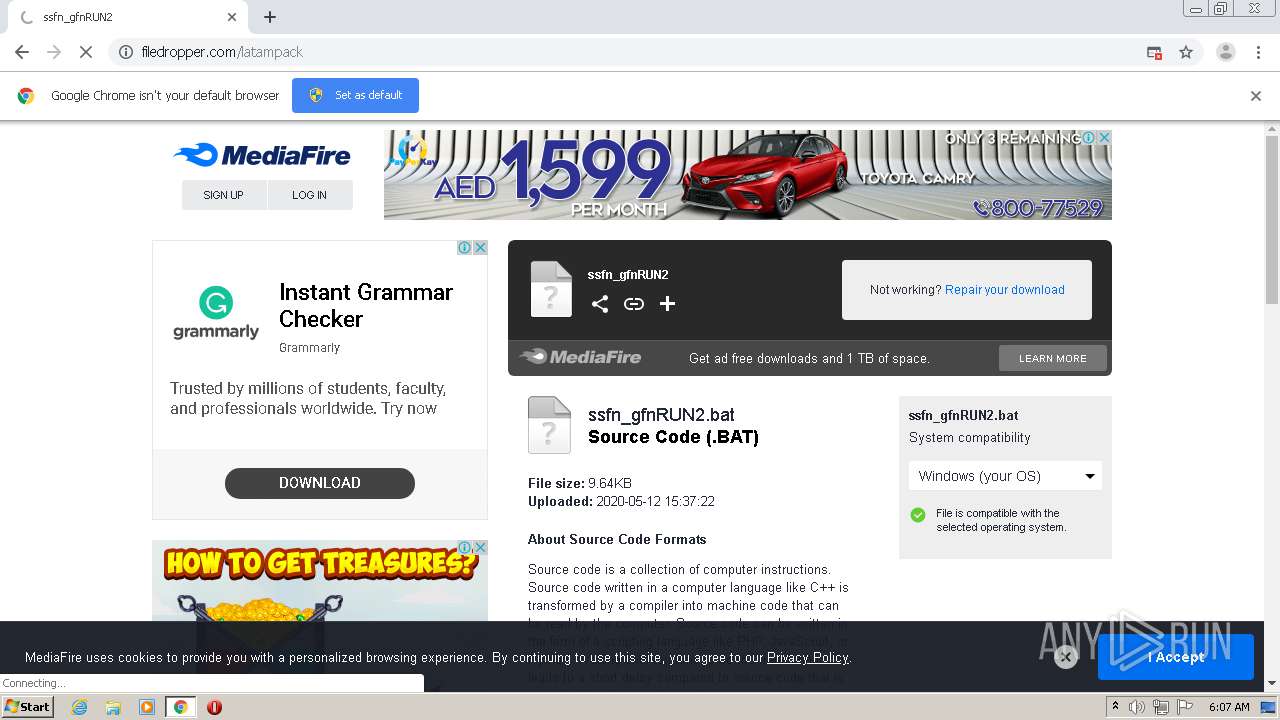
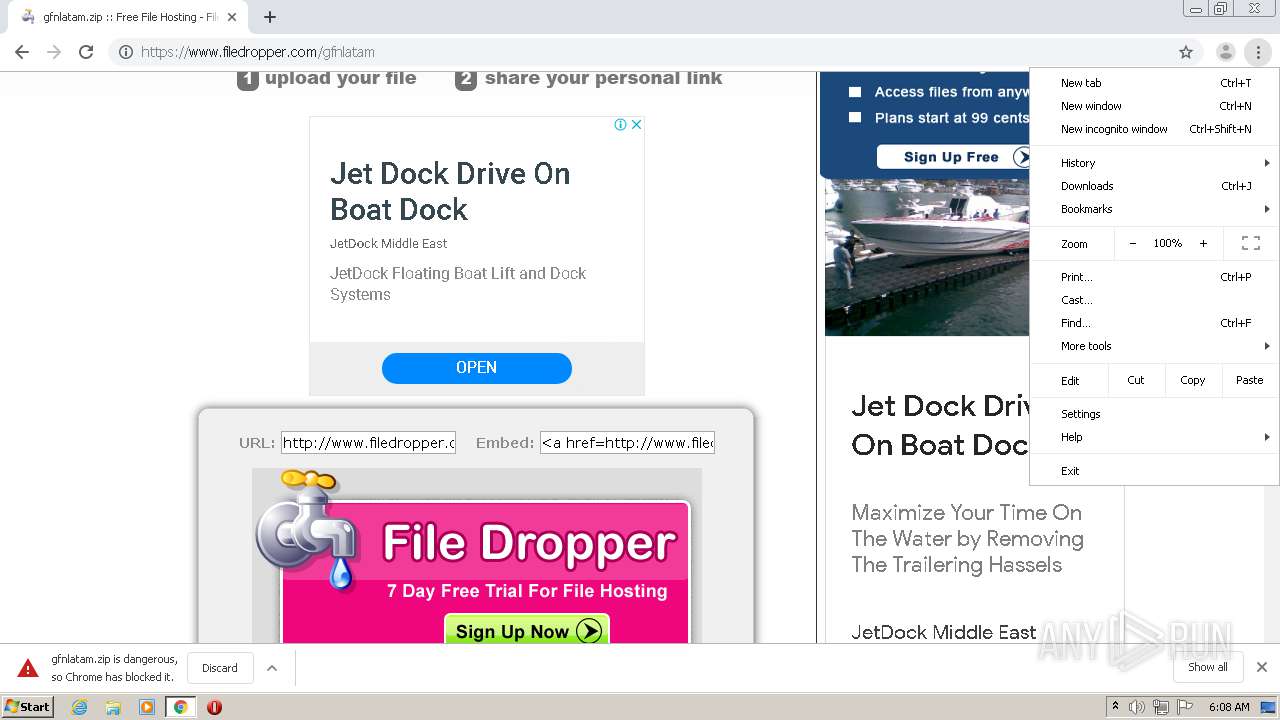
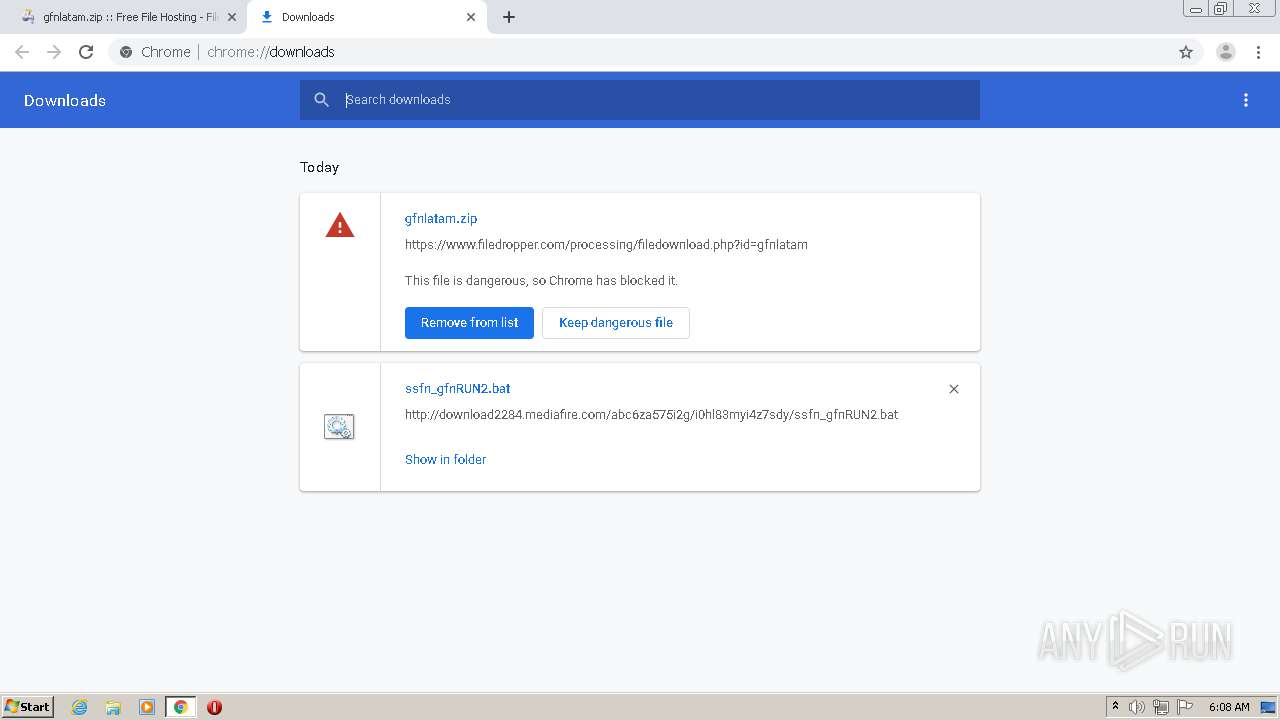
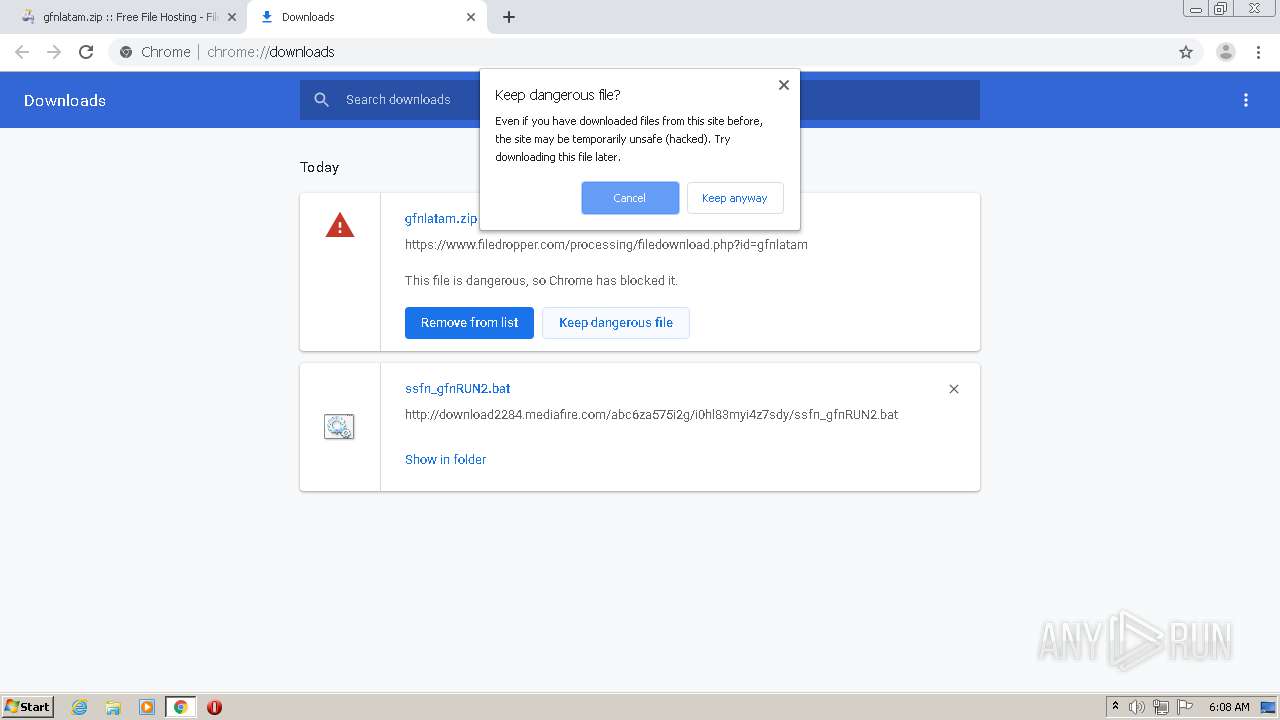
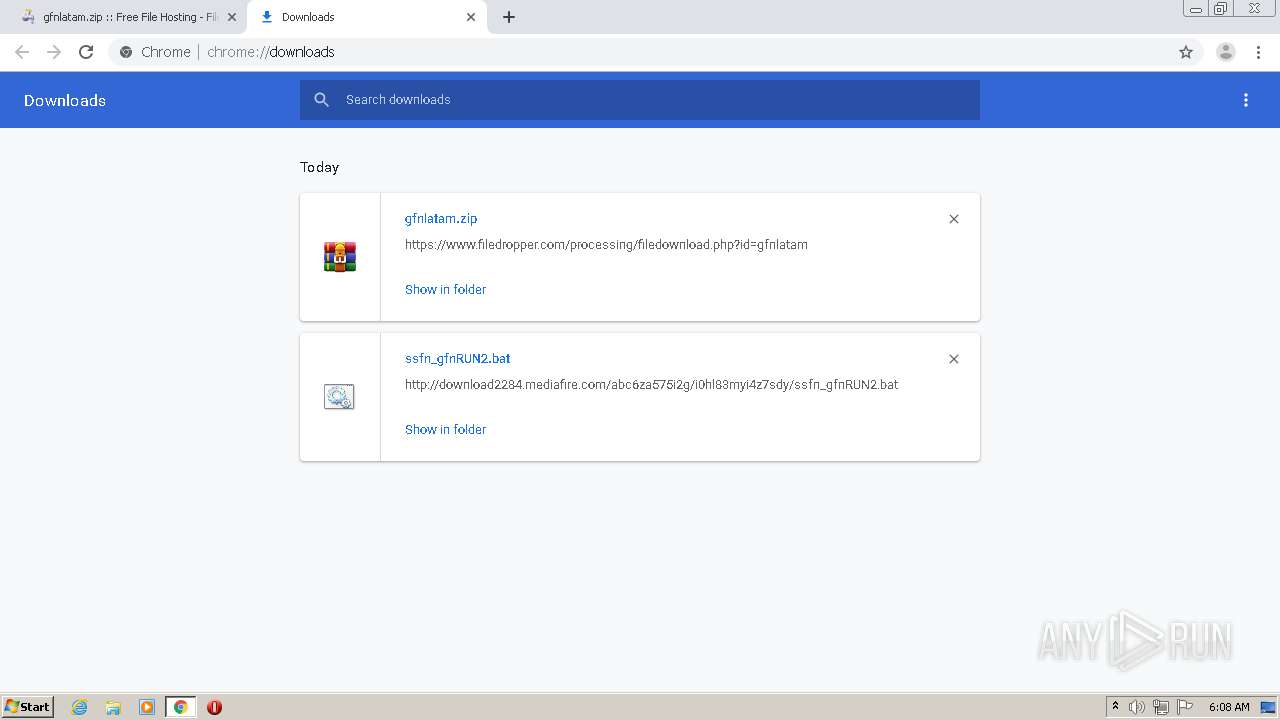
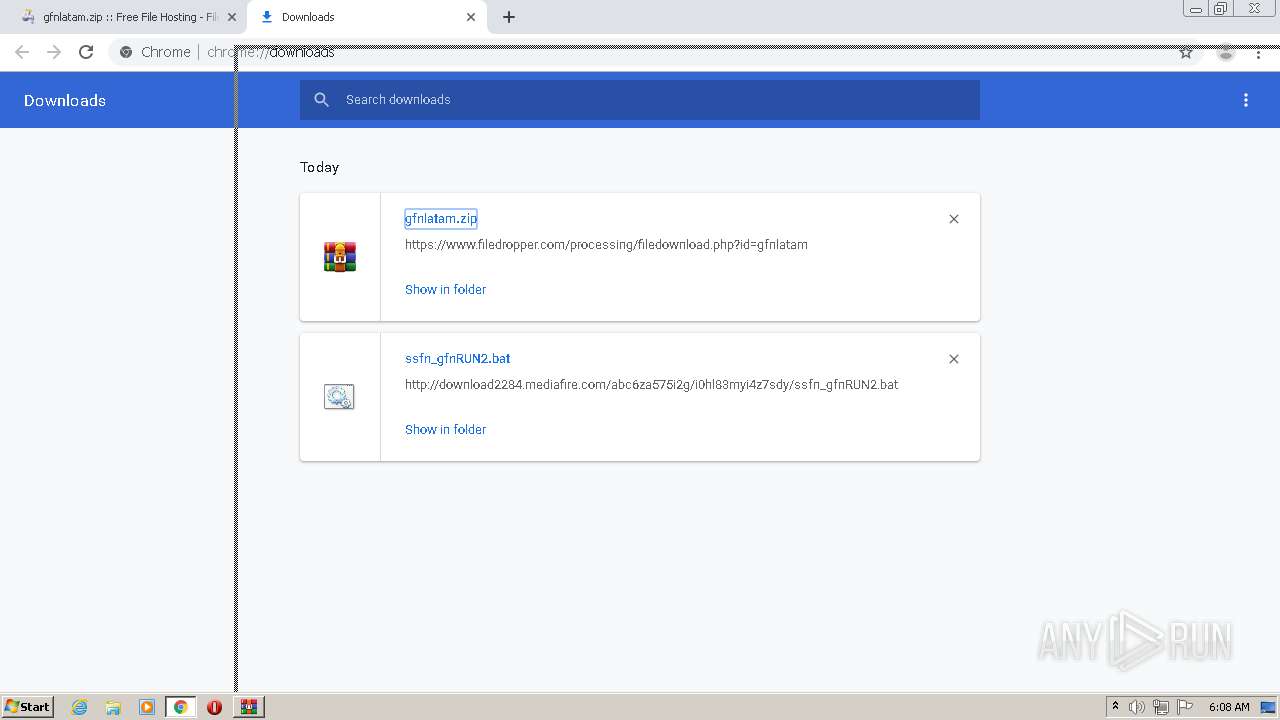
| URL: | http://www.mediafire.com/file/i0hl83myi4z7sdy/ssfn_gfnRUN2.bat/file |
| Full analysis: | https://app.any.run/tasks/86889fba-8701-4fb2-9b1e-b517eb7c6a7f |
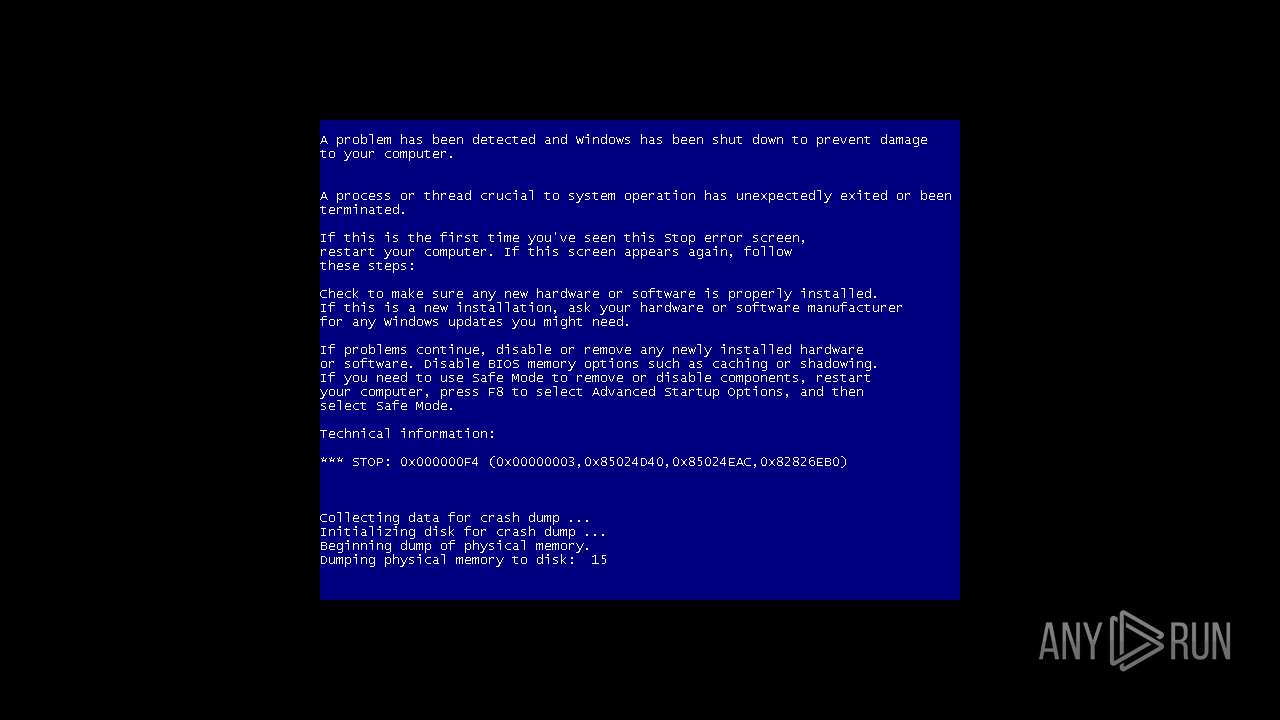
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 05:06:53 |
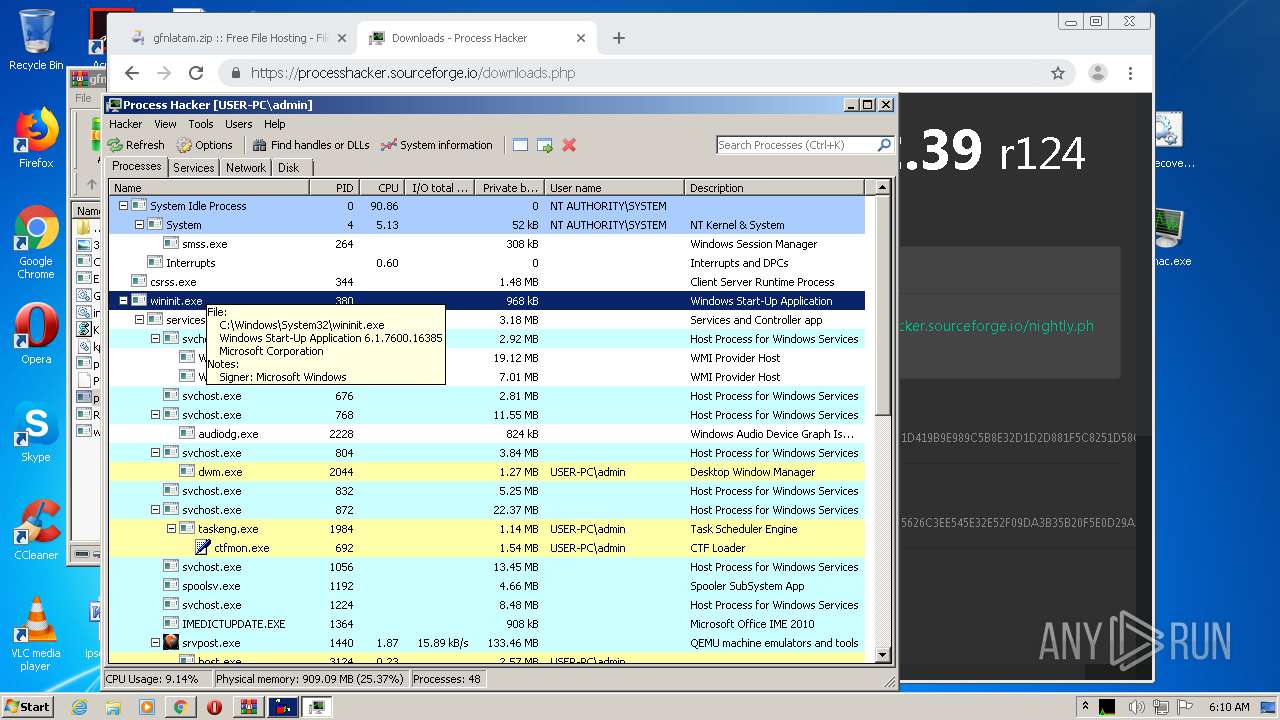
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 60683F38946F87D7D61AC1FE59C1F627 |
| SHA1: | BFD2F793DB30A4ACBCB26ED68875F4E8570060CF |
| SHA256: | 34B49627E7380C51883DCB1166A904FD90720948E1FC17BB40E462056C1A461D |
| SSDEEP: | 3:N1KJS4w3eGUoUIIcQfblqADwrbki9n:Cc4w3eGIy42xn |
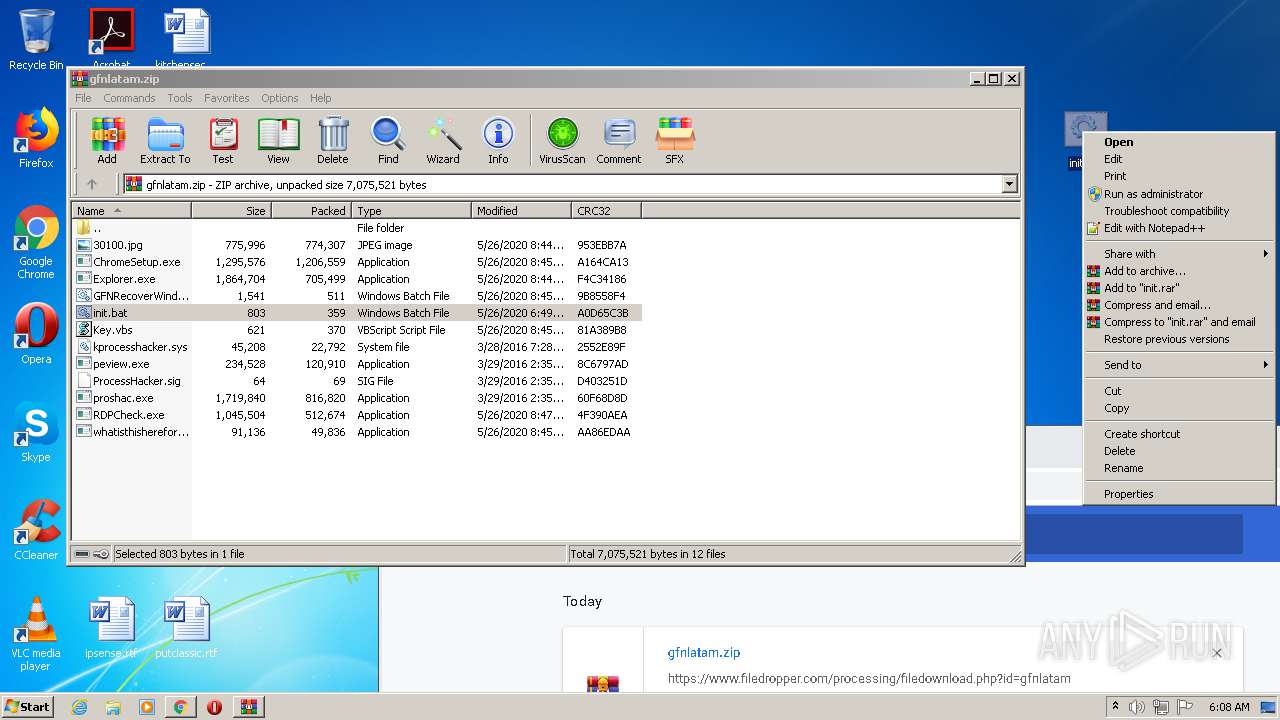
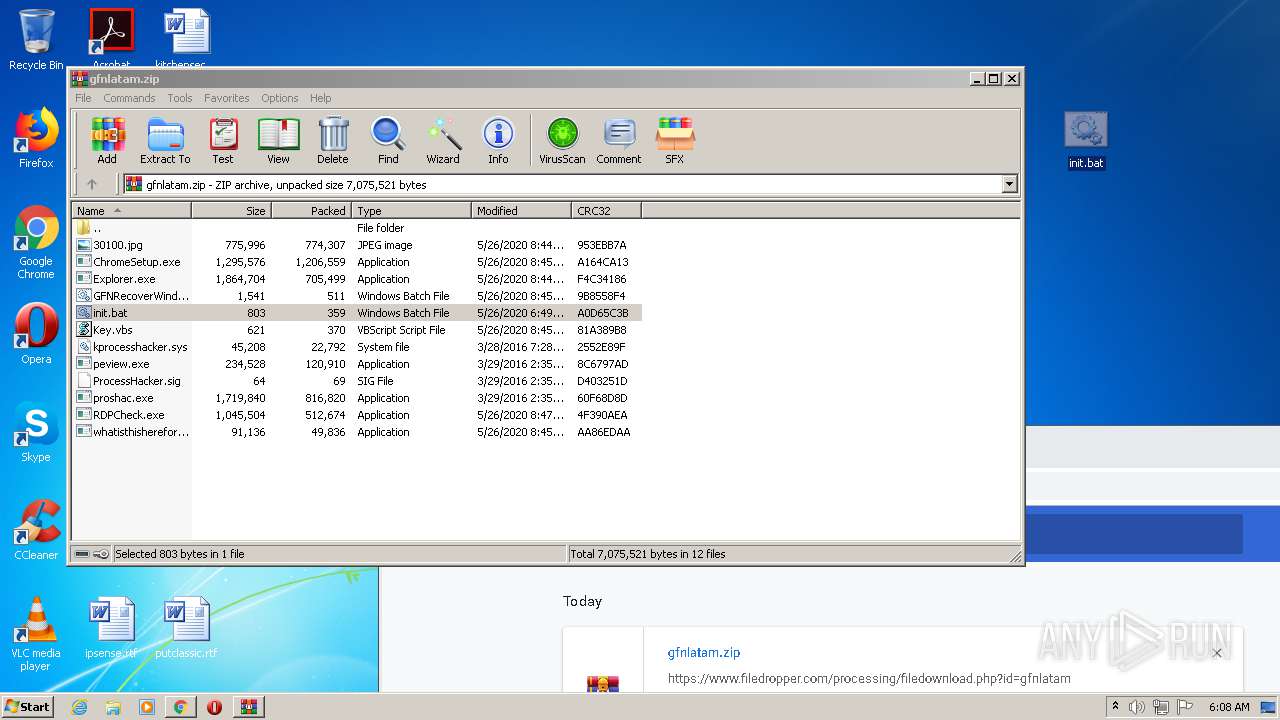
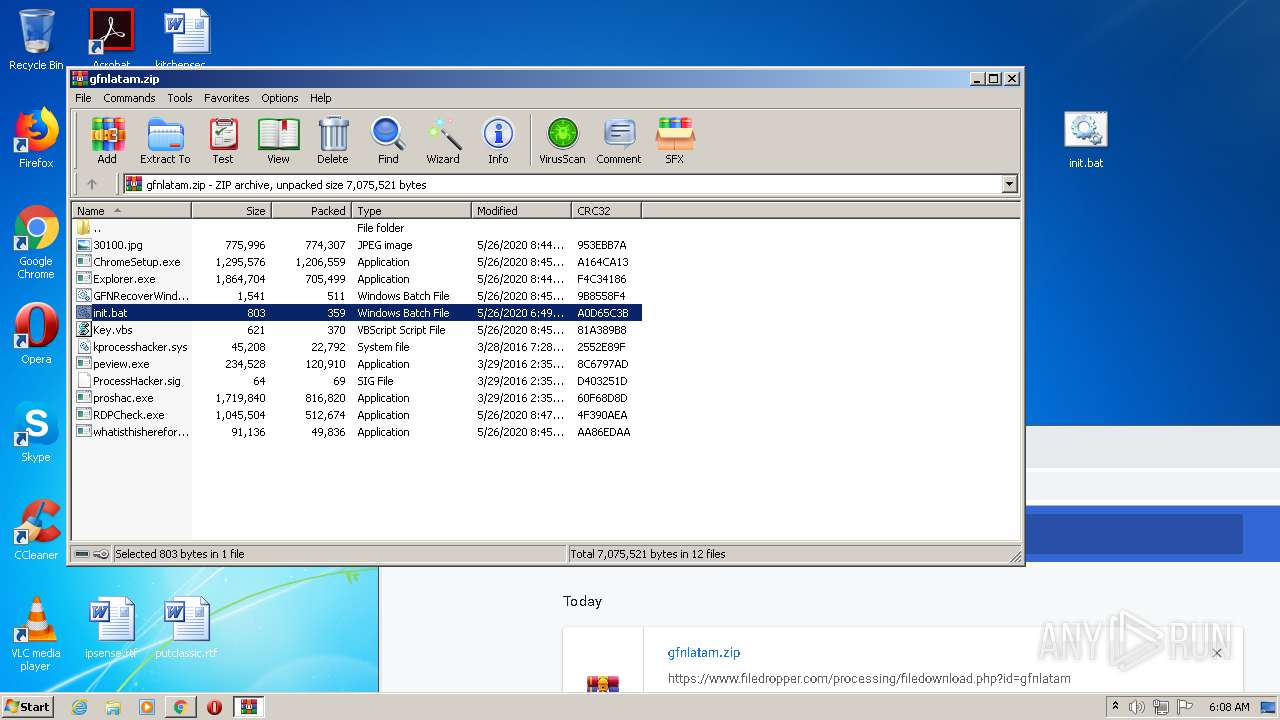
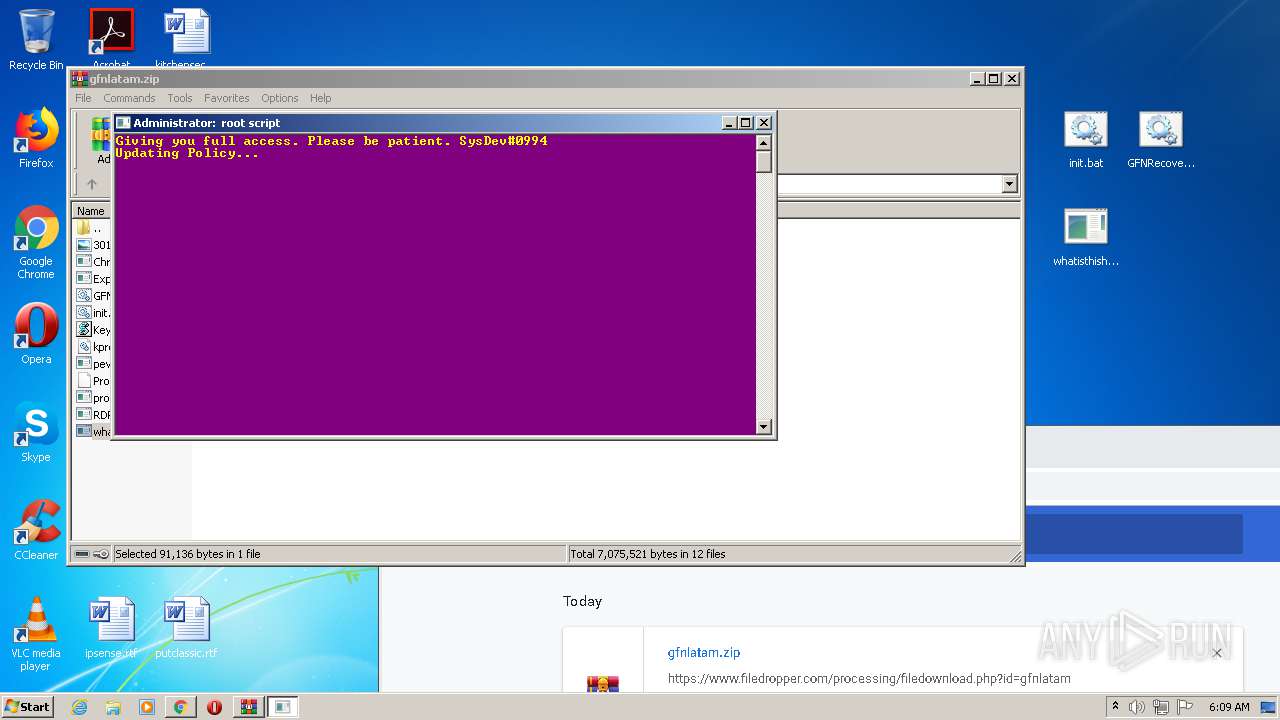
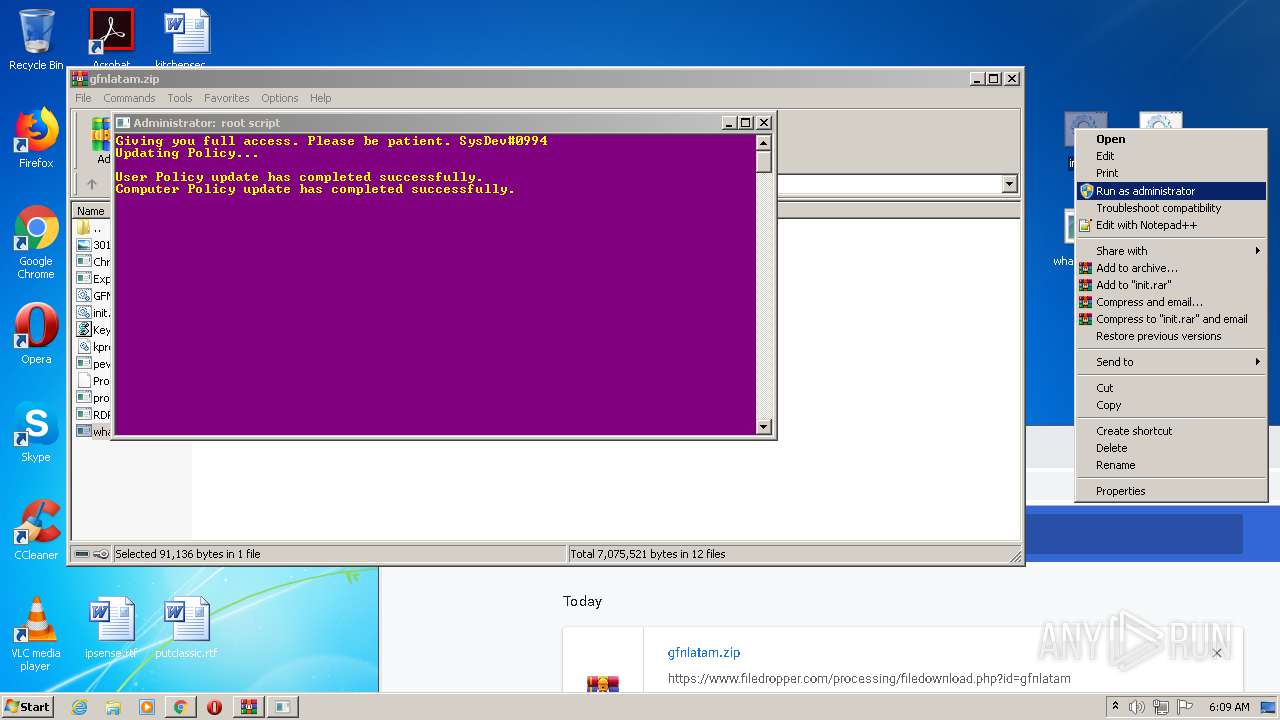
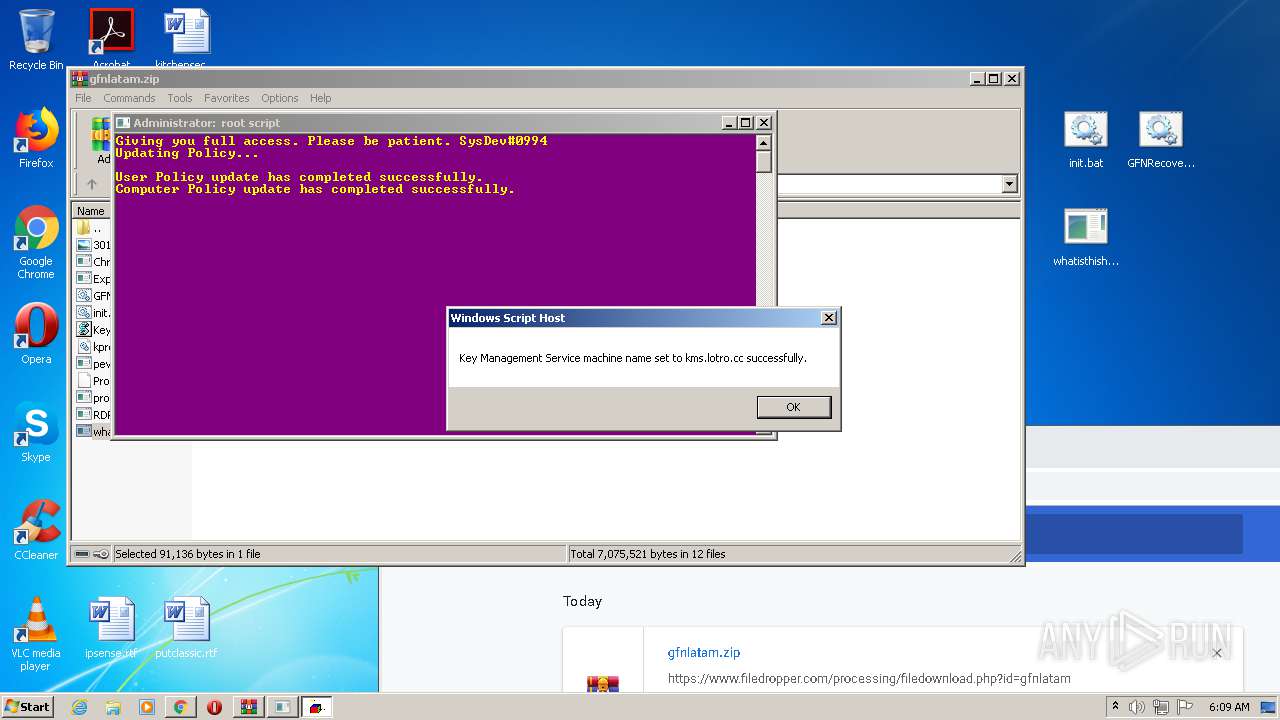
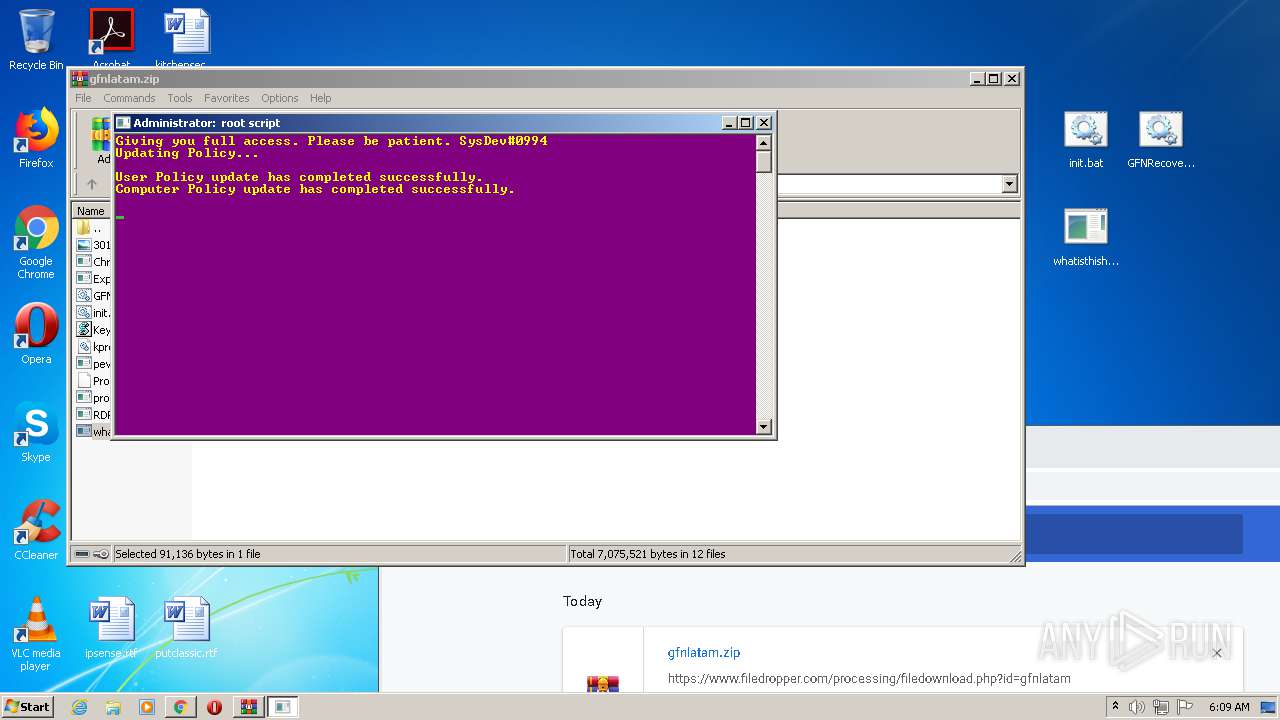
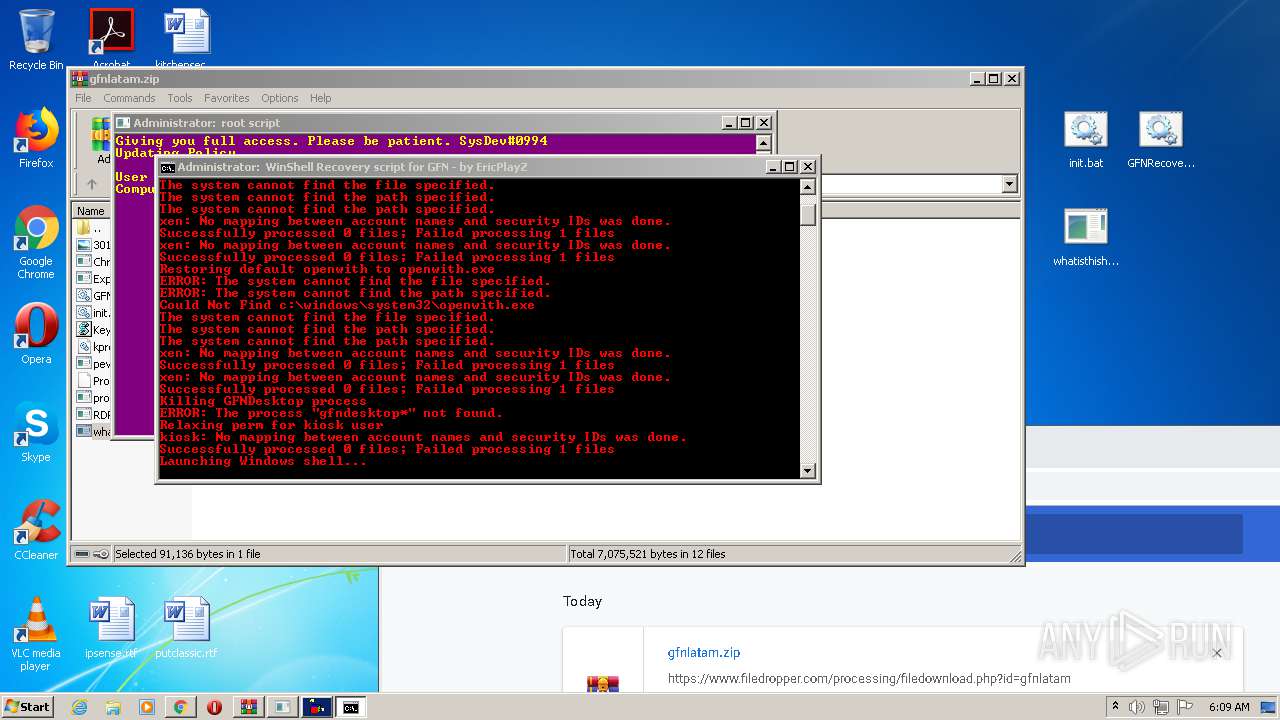
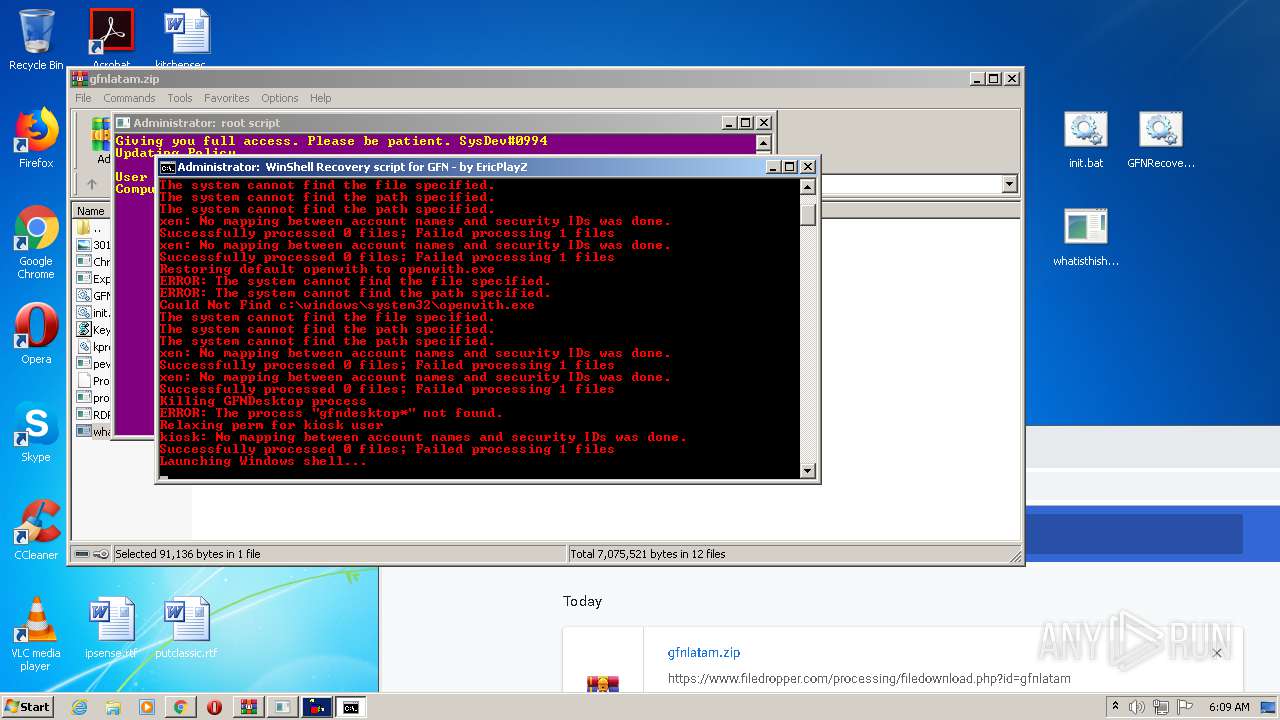
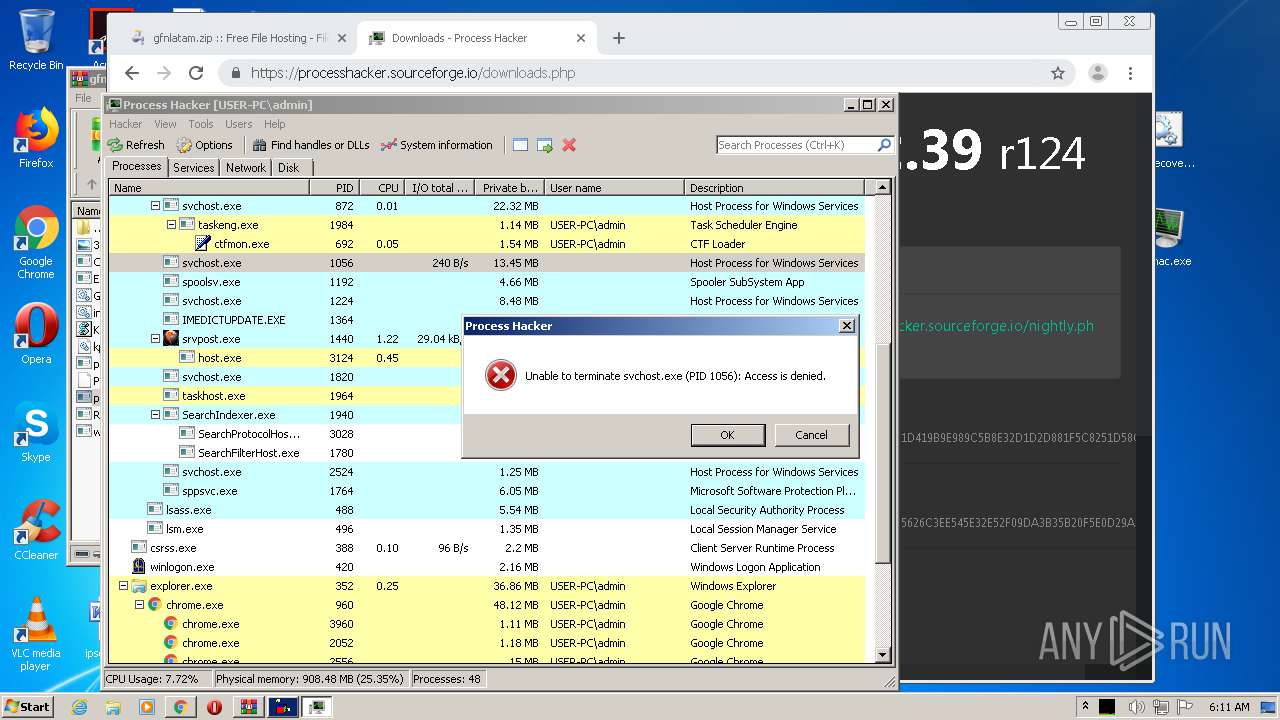
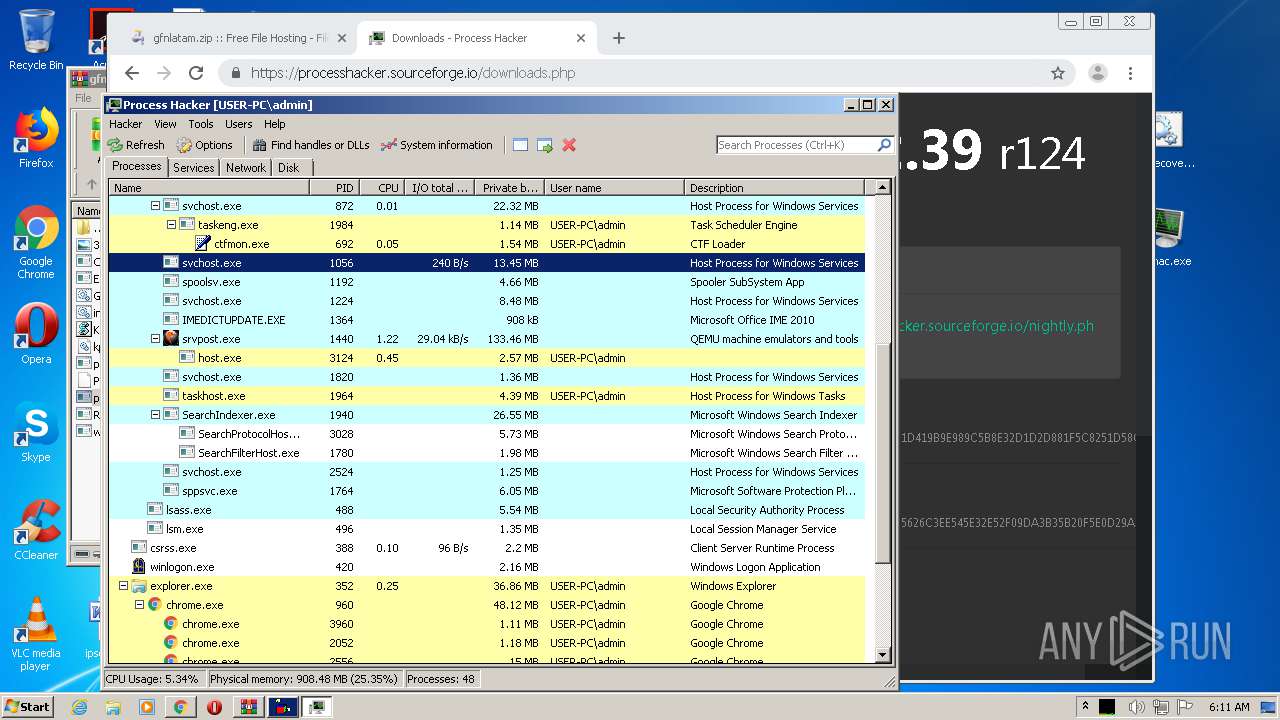
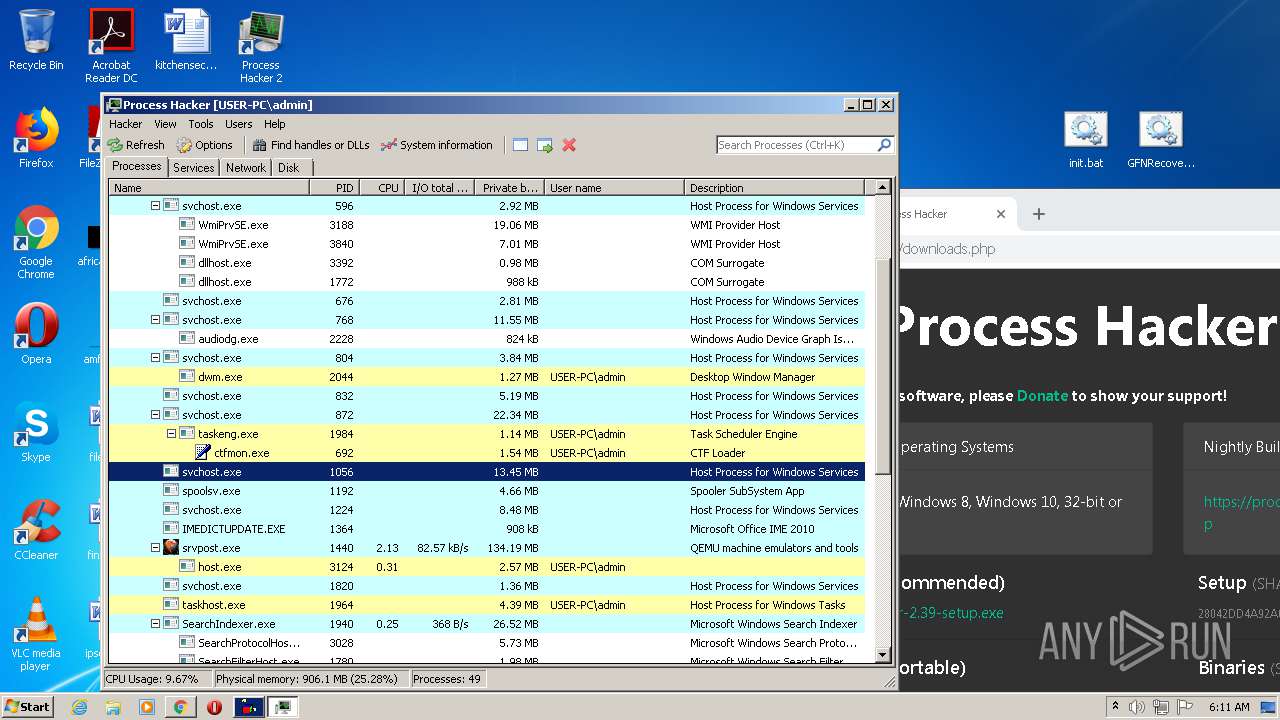
MALICIOUS
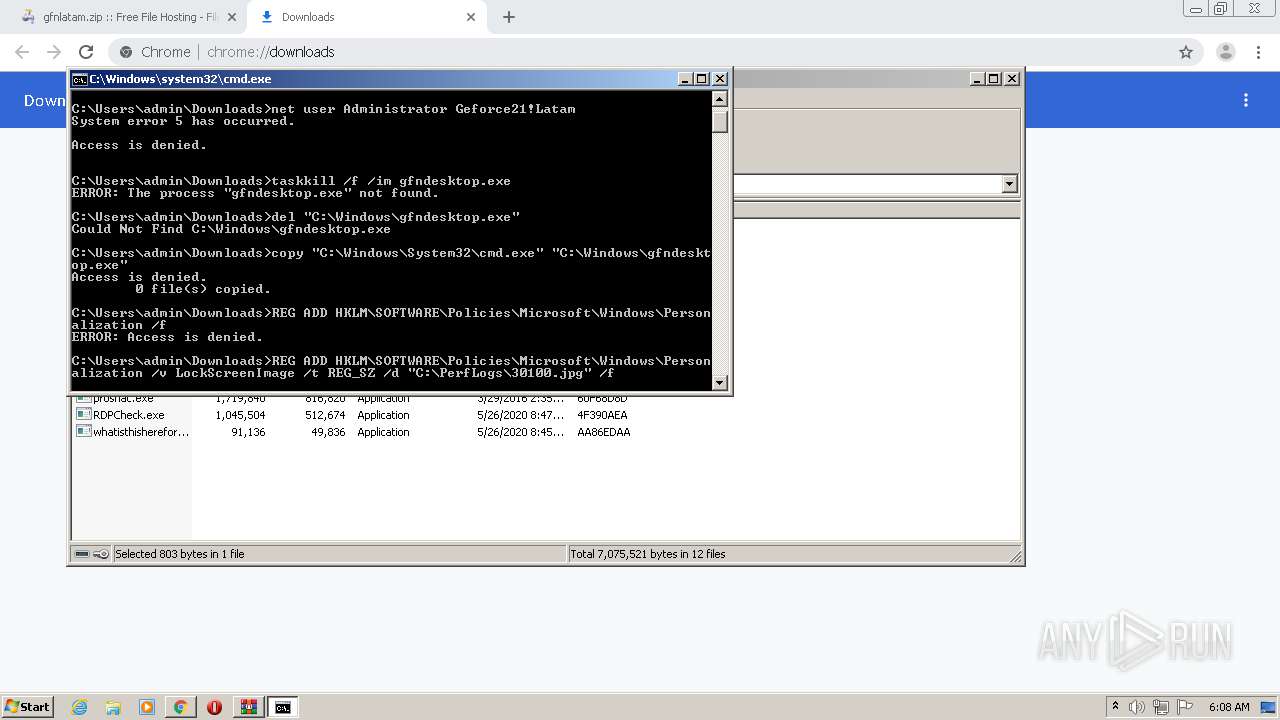
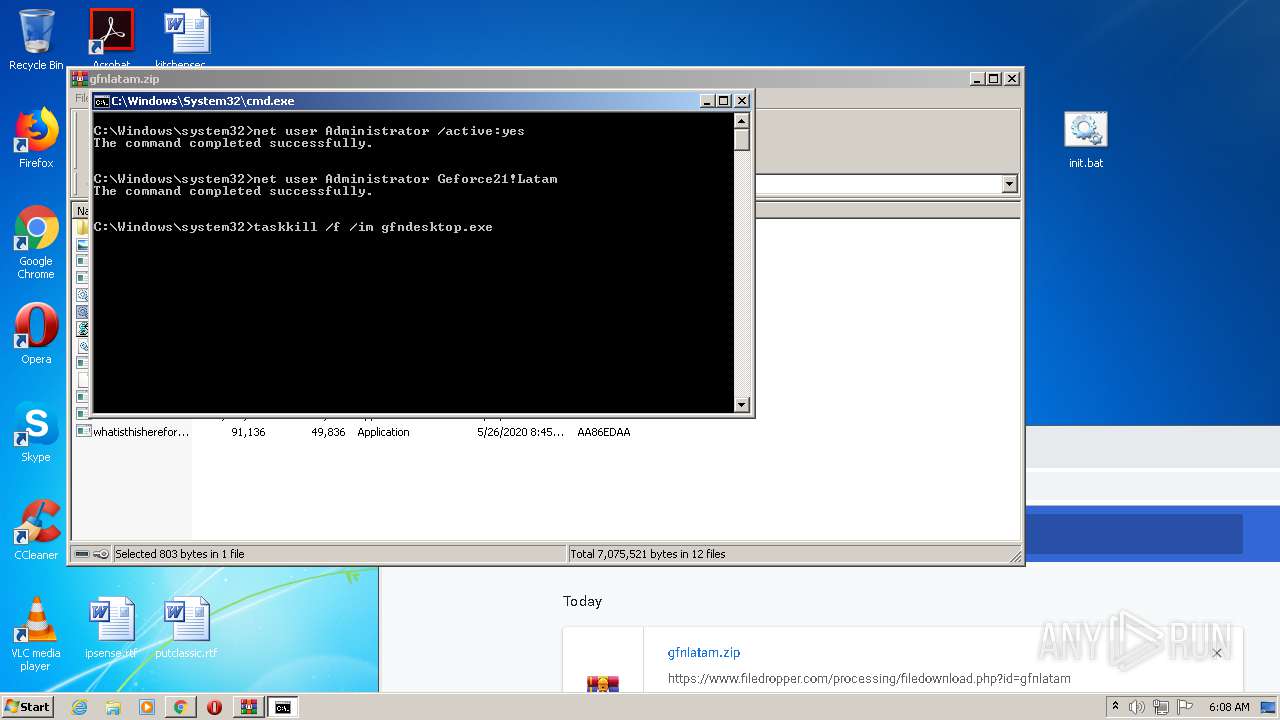
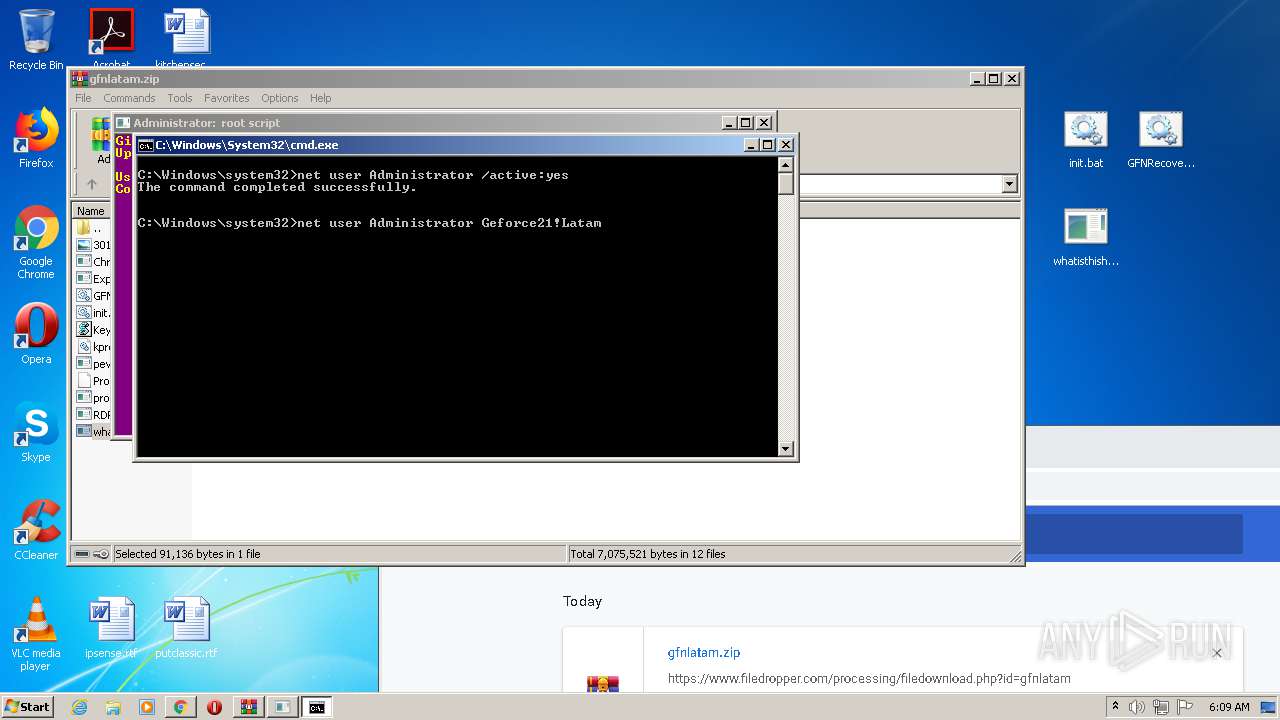
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 2404)
- cmd.exe (PID: 3808)
- cmd.exe (PID: 2028)
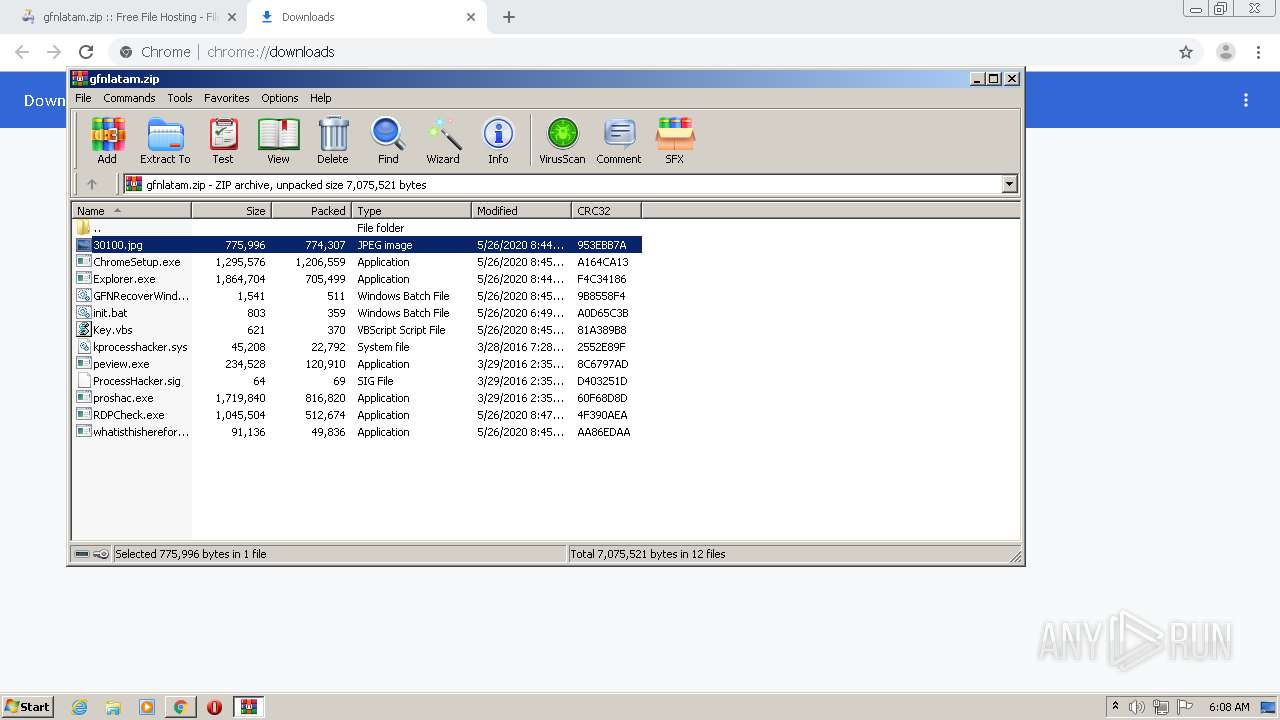
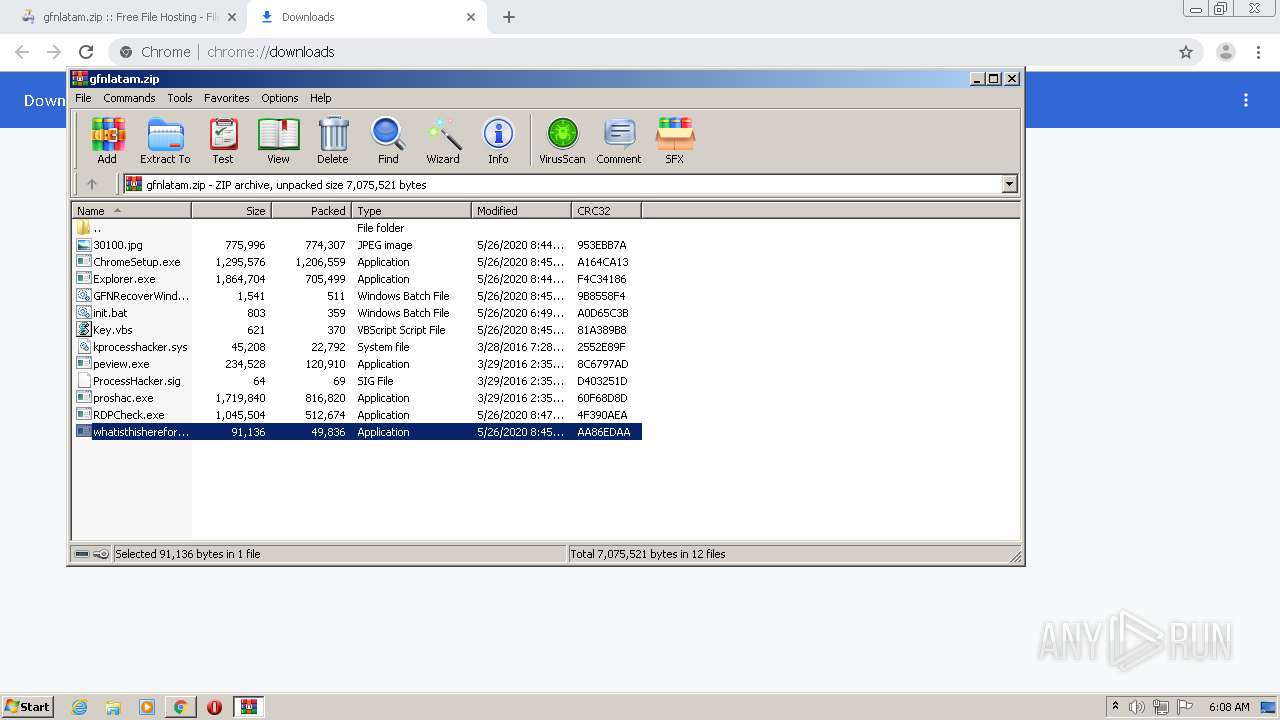
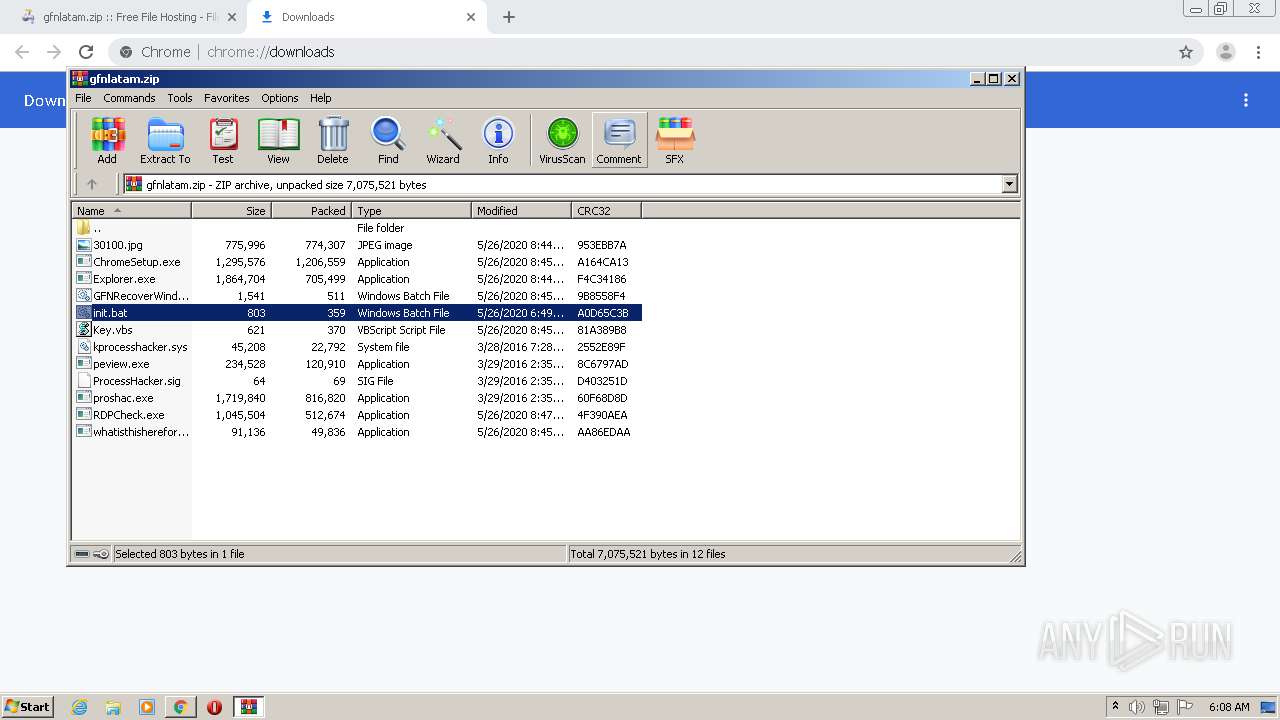
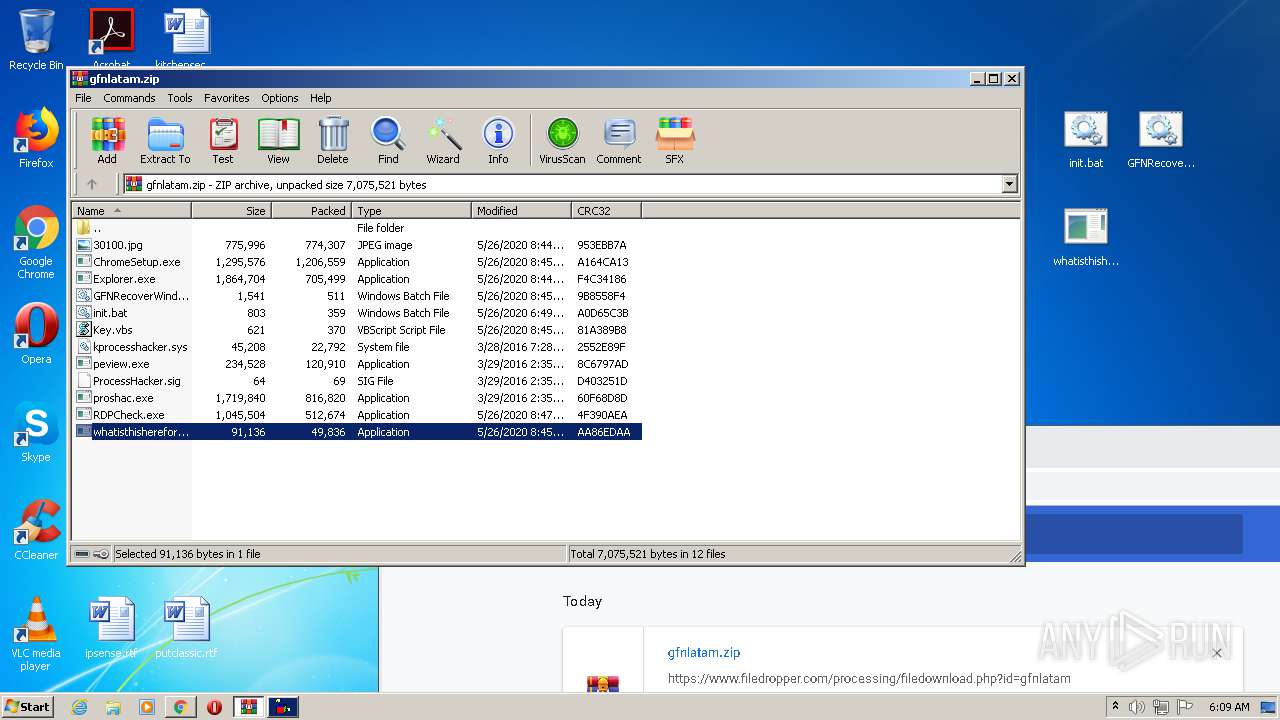
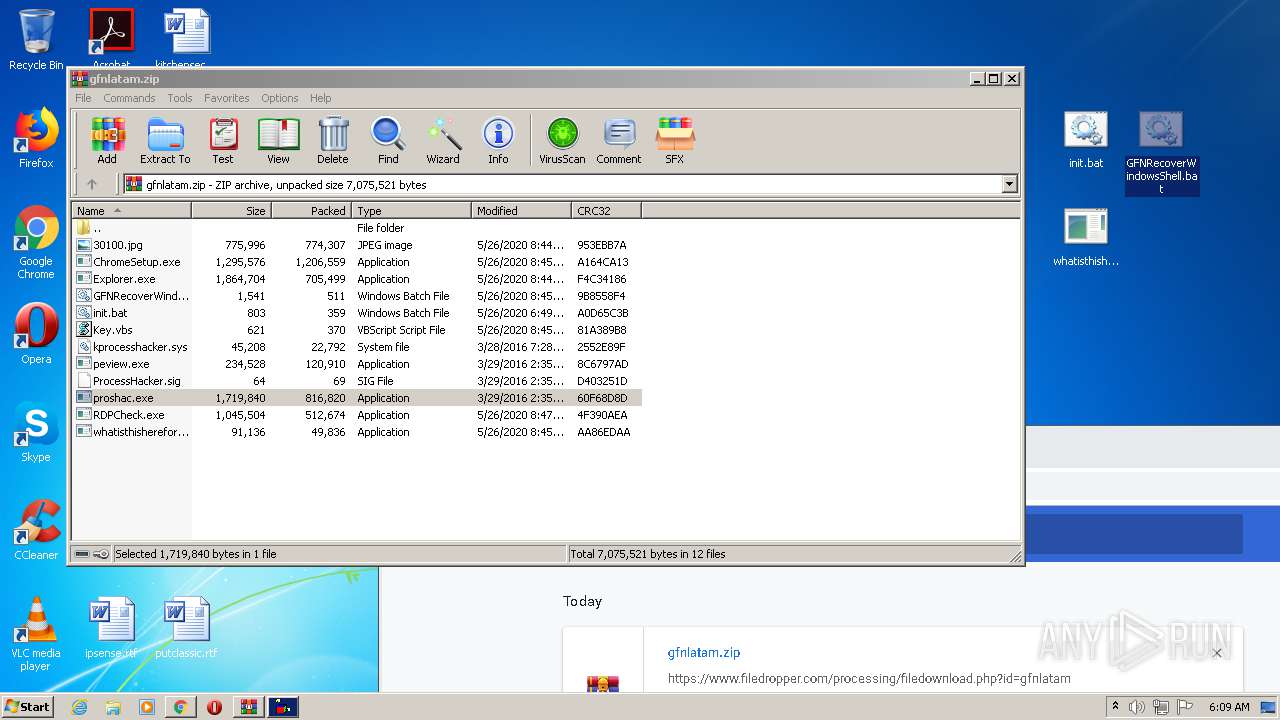
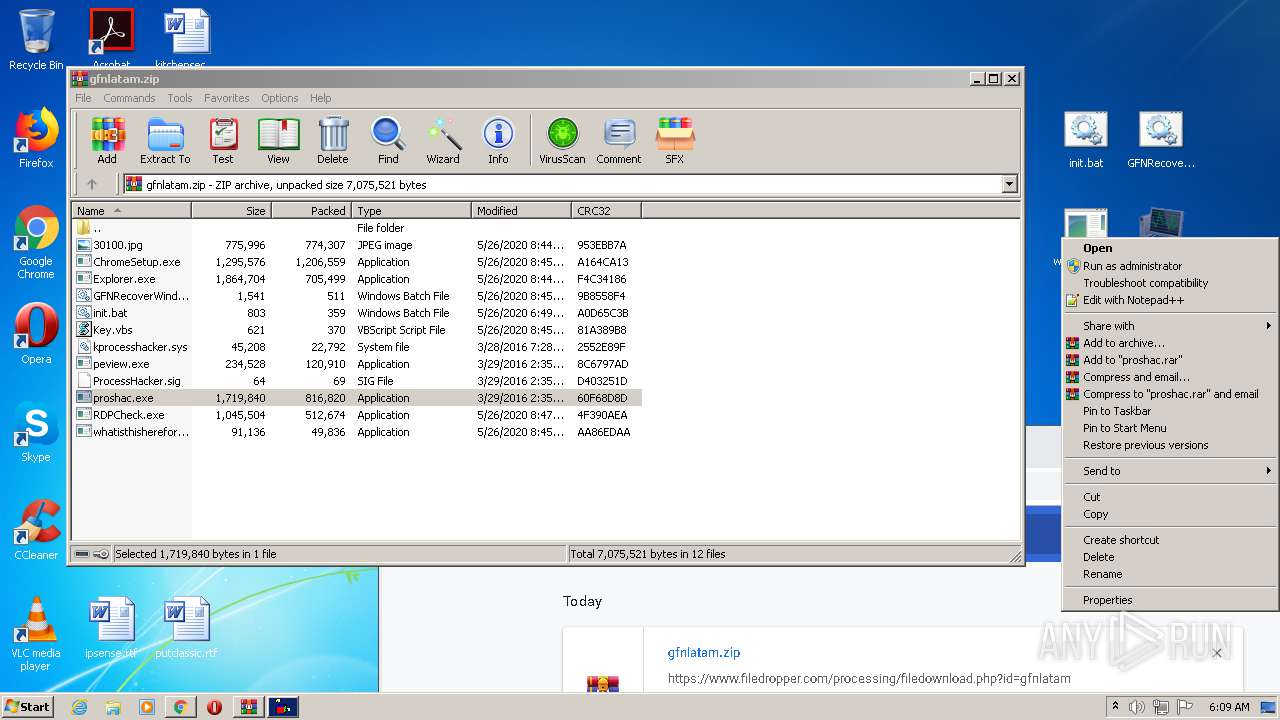
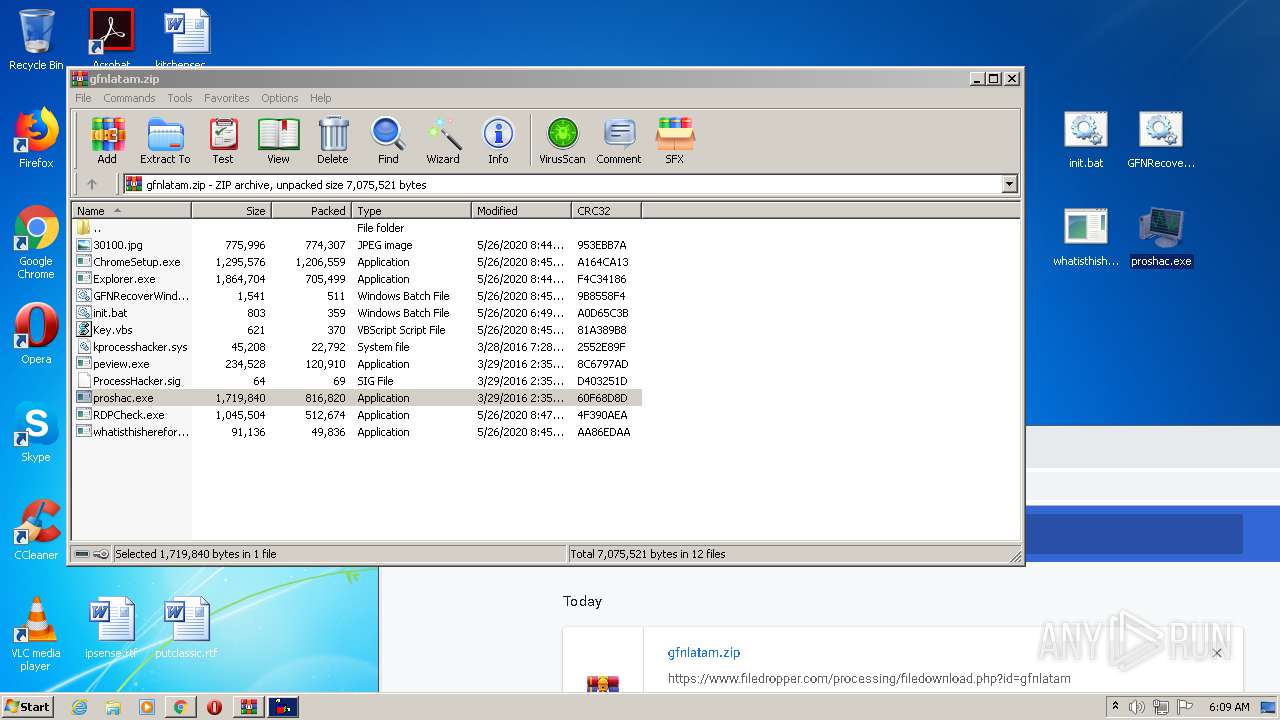
Application was dropped or rewritten from another process
- whatisthisherefor.exe (PID: 1784)
- cmd.exe (PID: 2676)
- cmd.exe (PID: 2760)
- cmd.exe (PID: 2404)
- cmd.exe (PID: 2028)
- cmd.exe (PID: 3808)
- whatisthisherefor.exe (PID: 3644)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 2056)
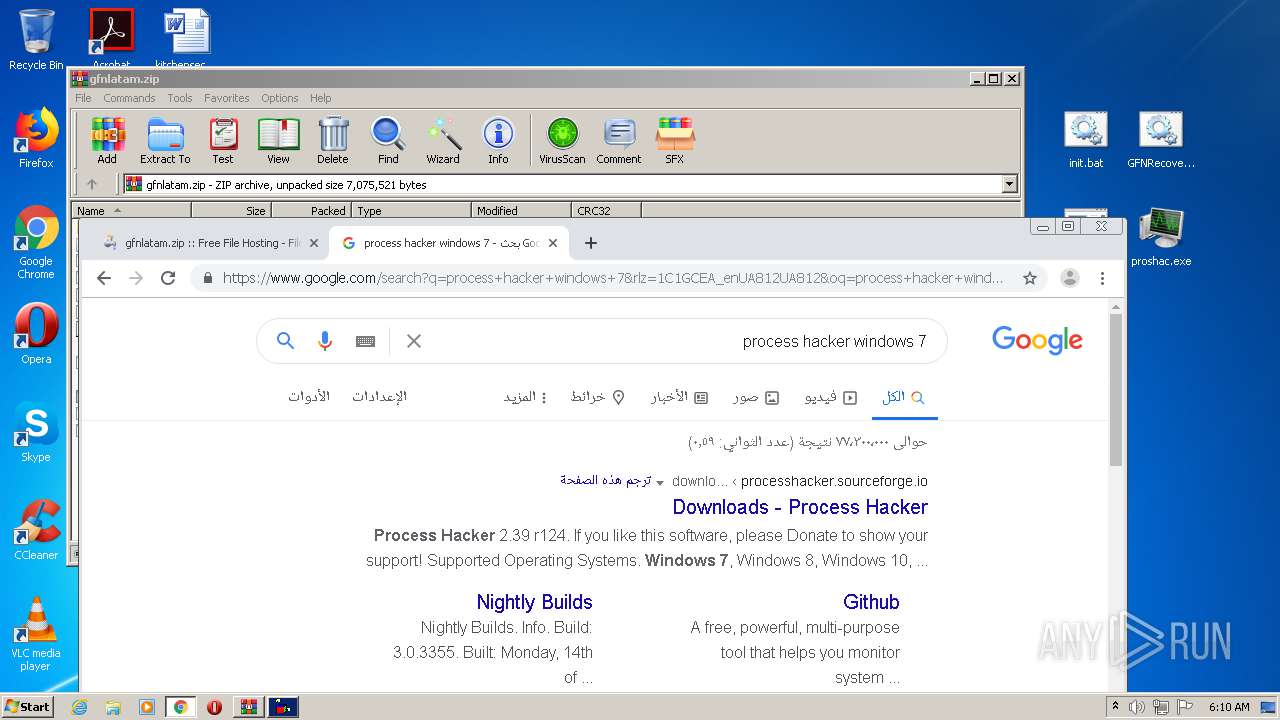
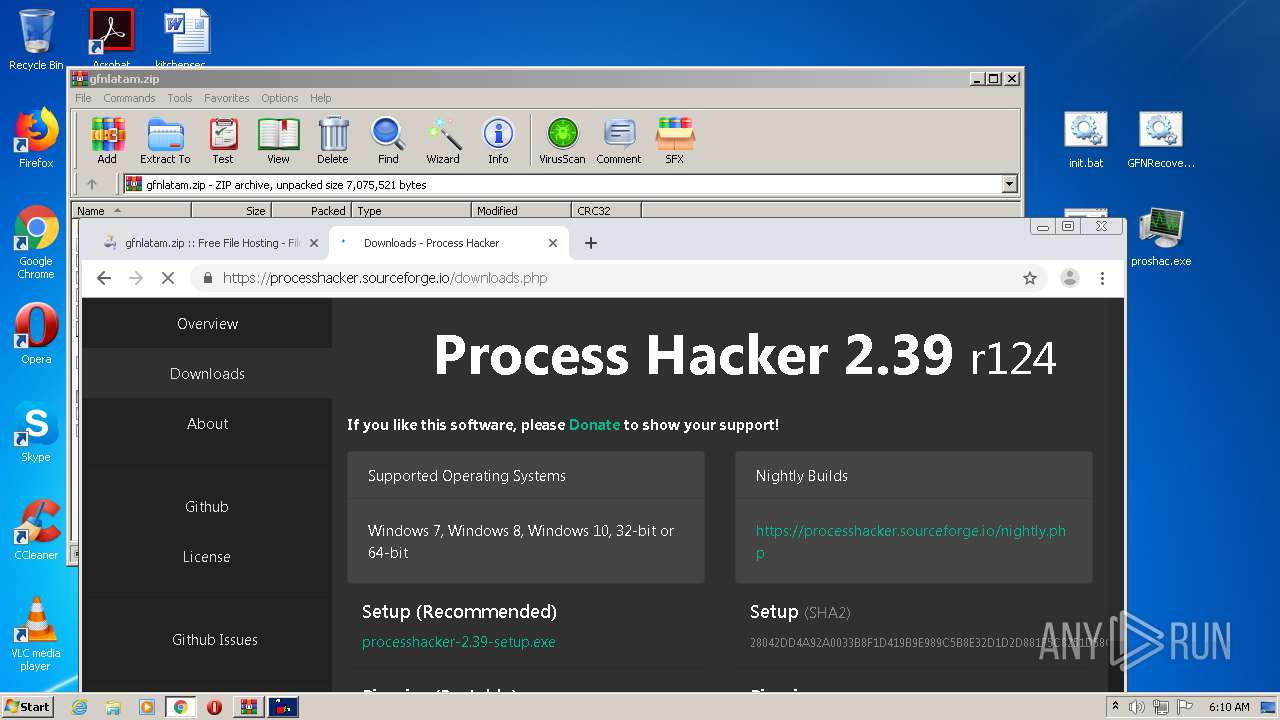
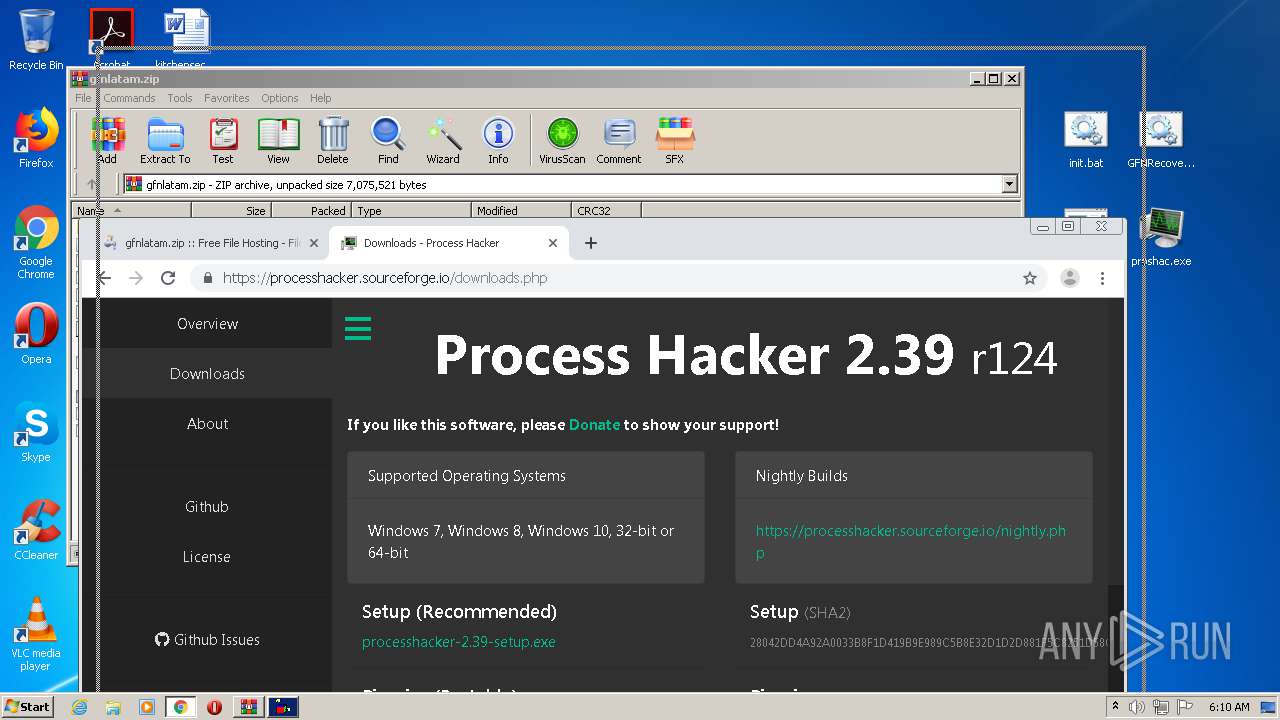
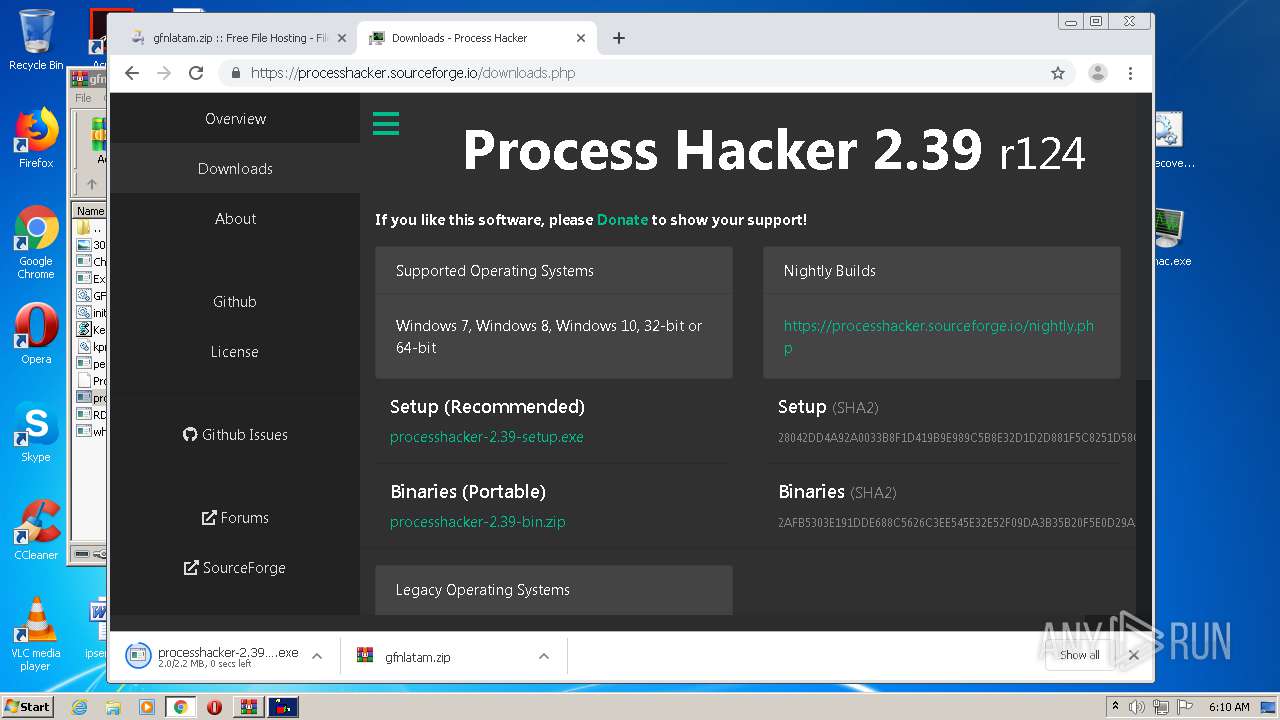
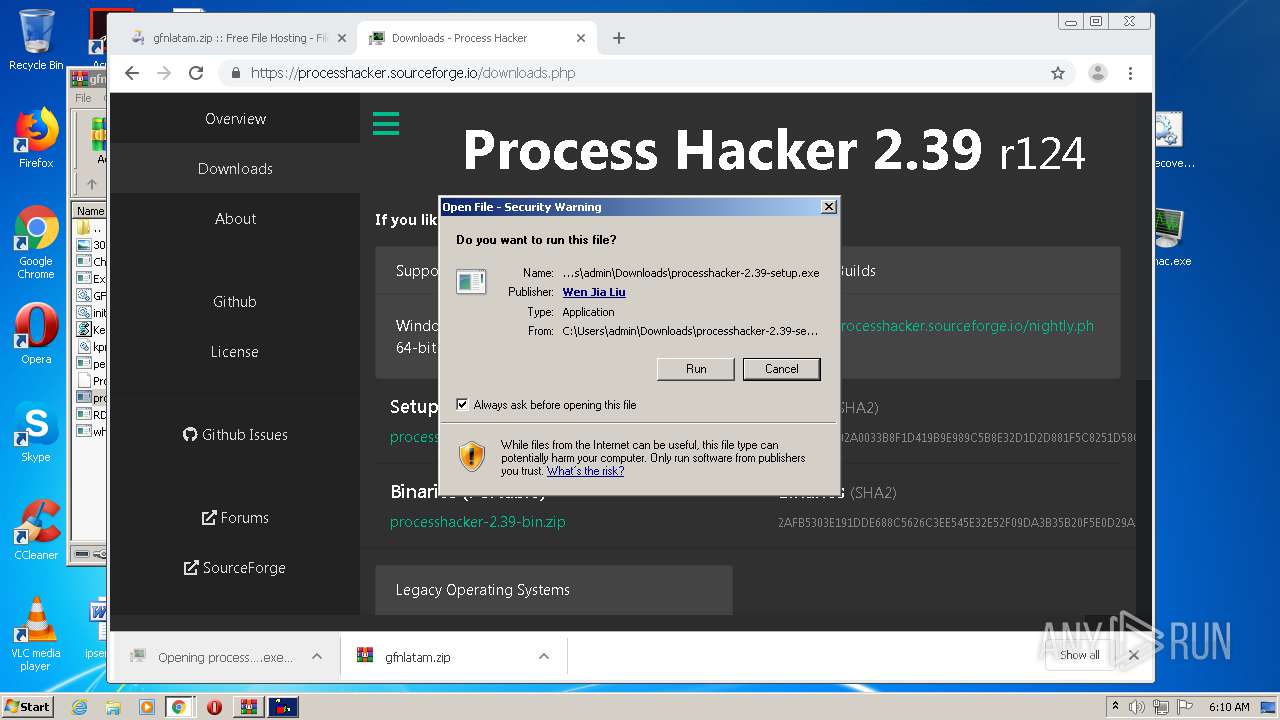
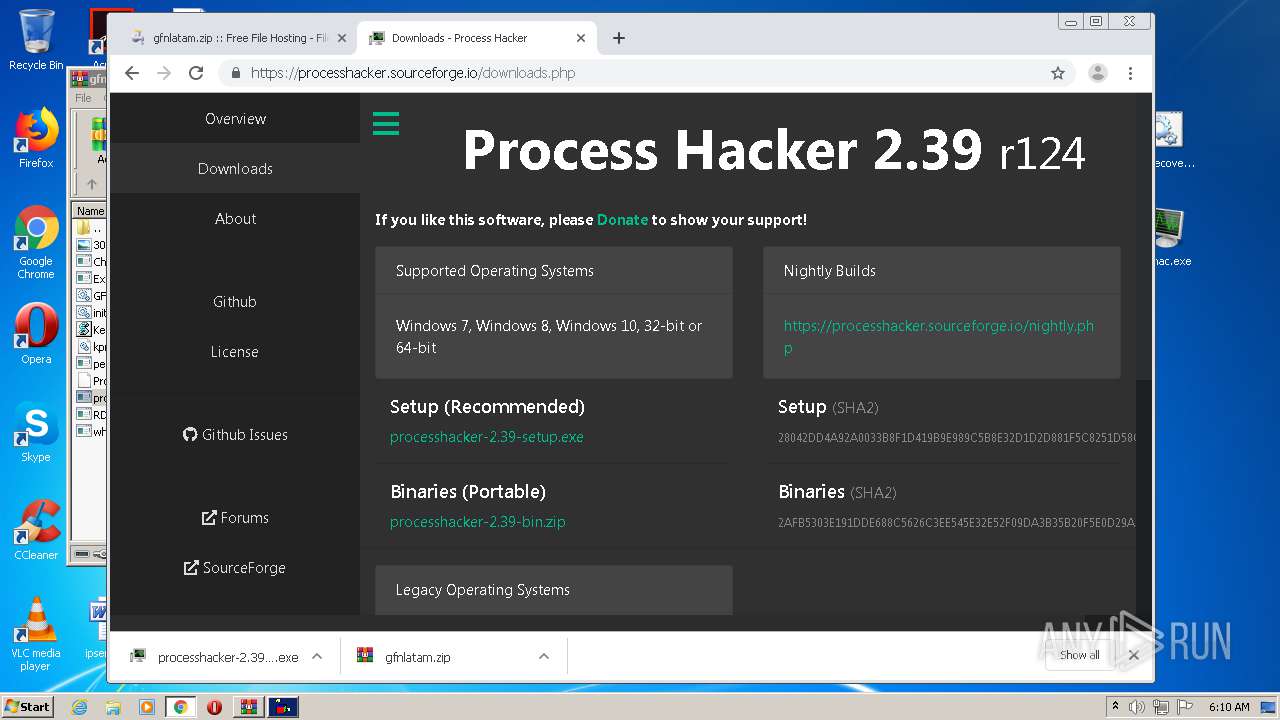
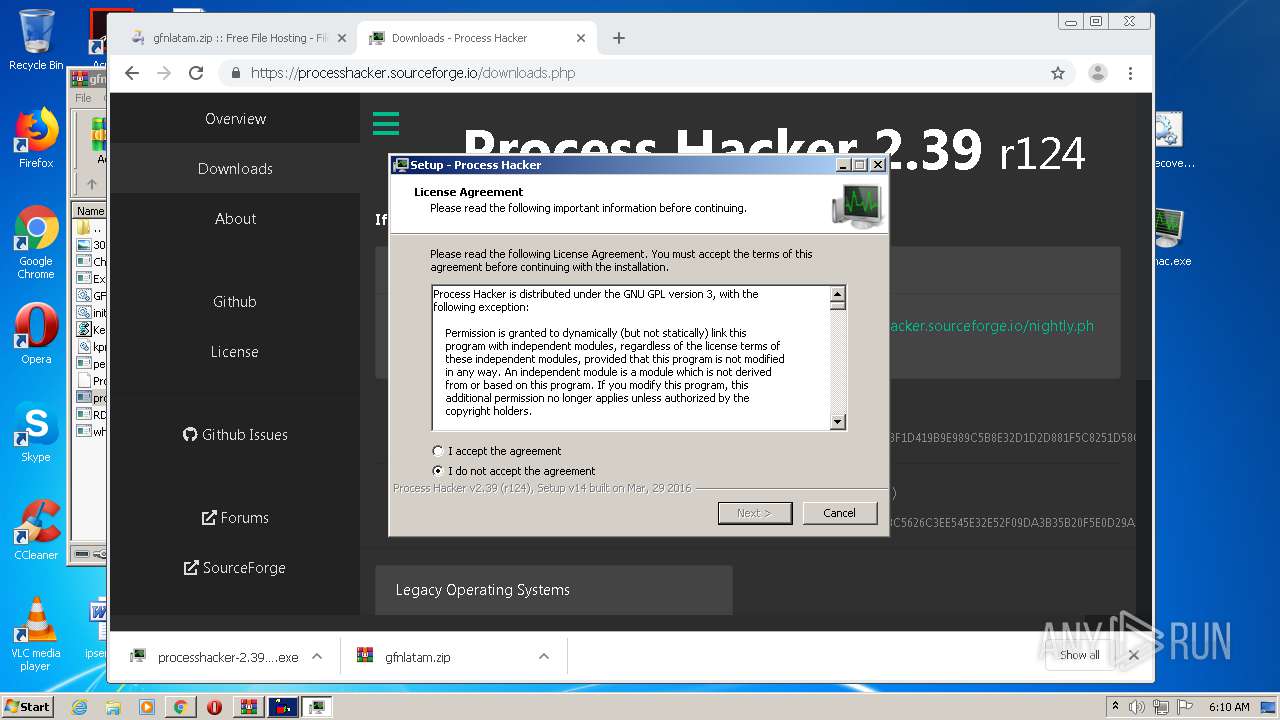
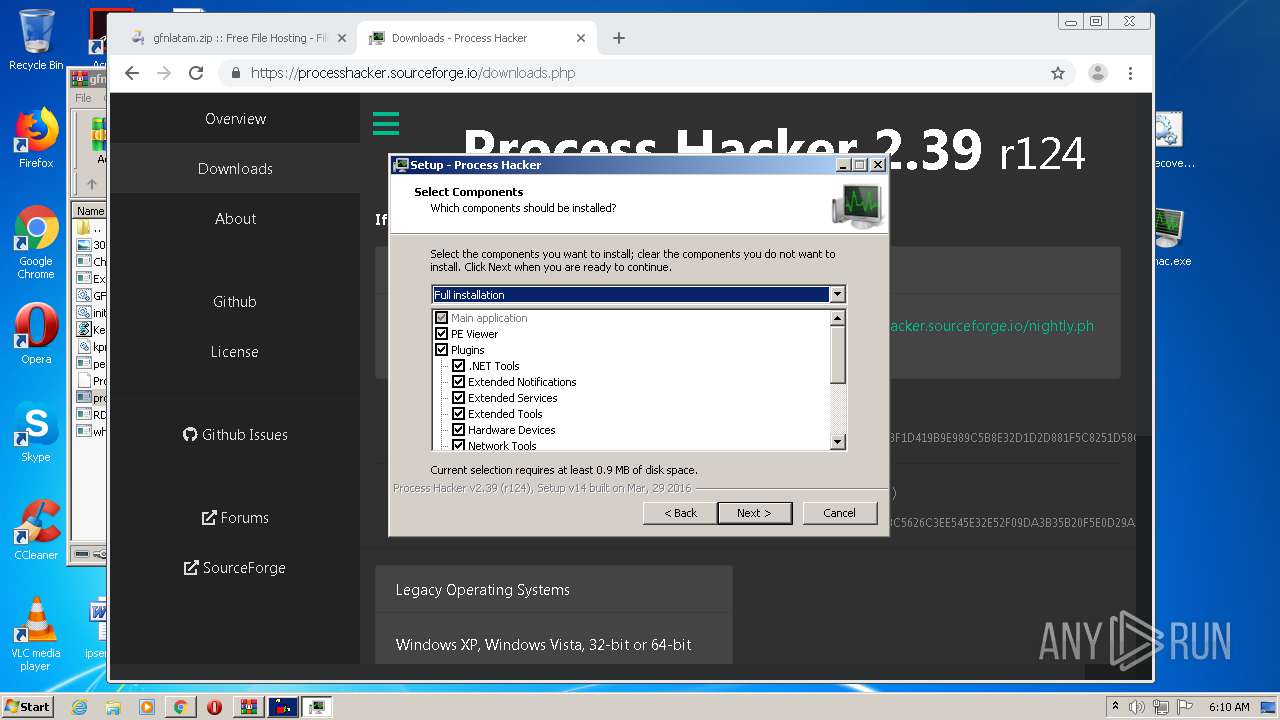
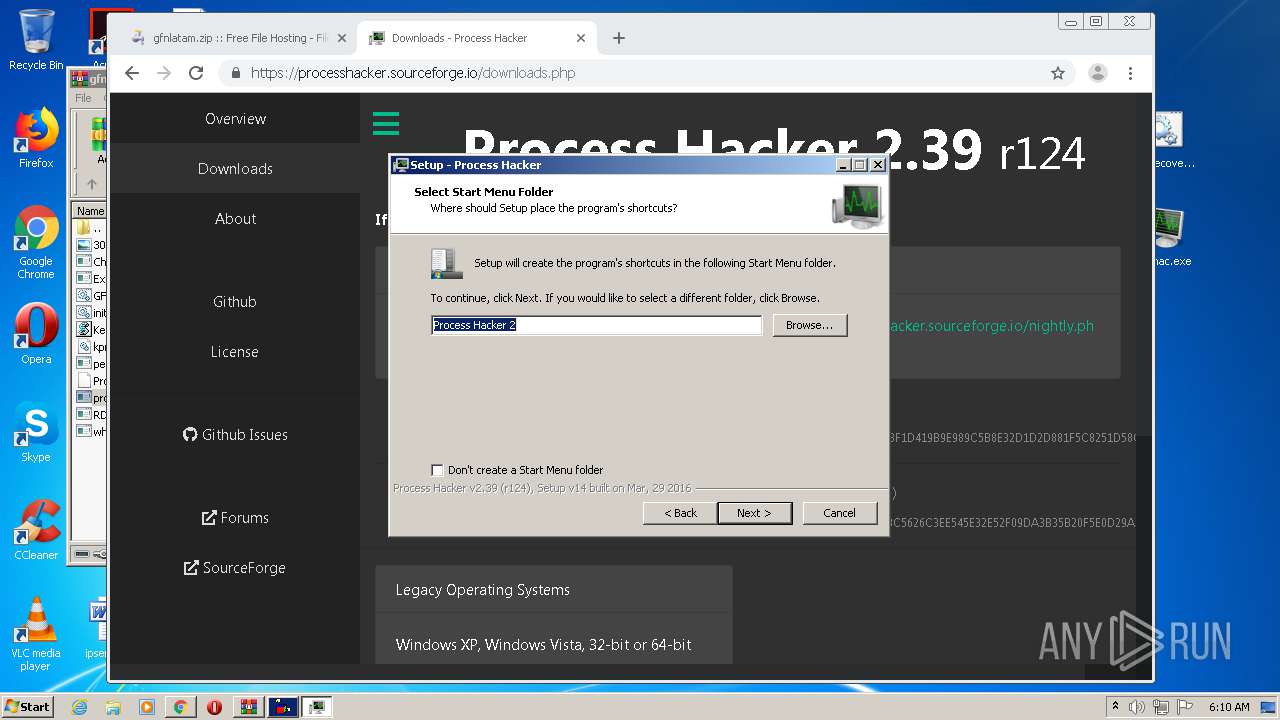
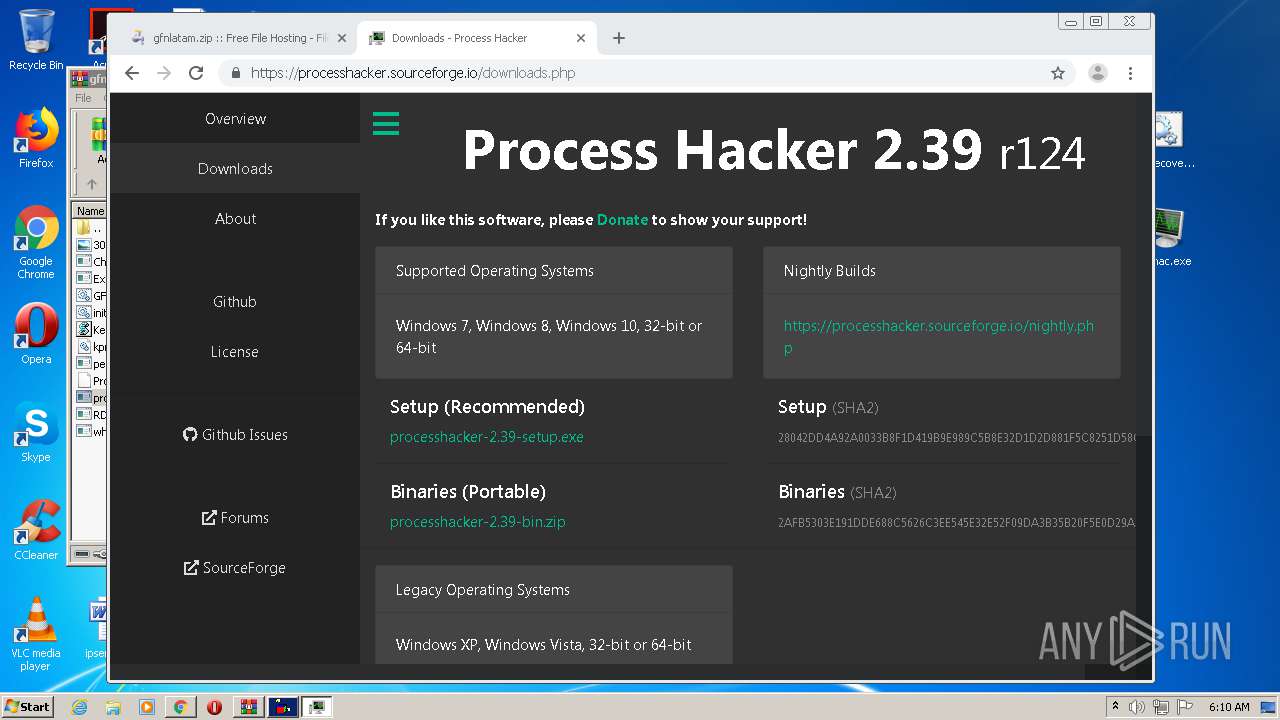
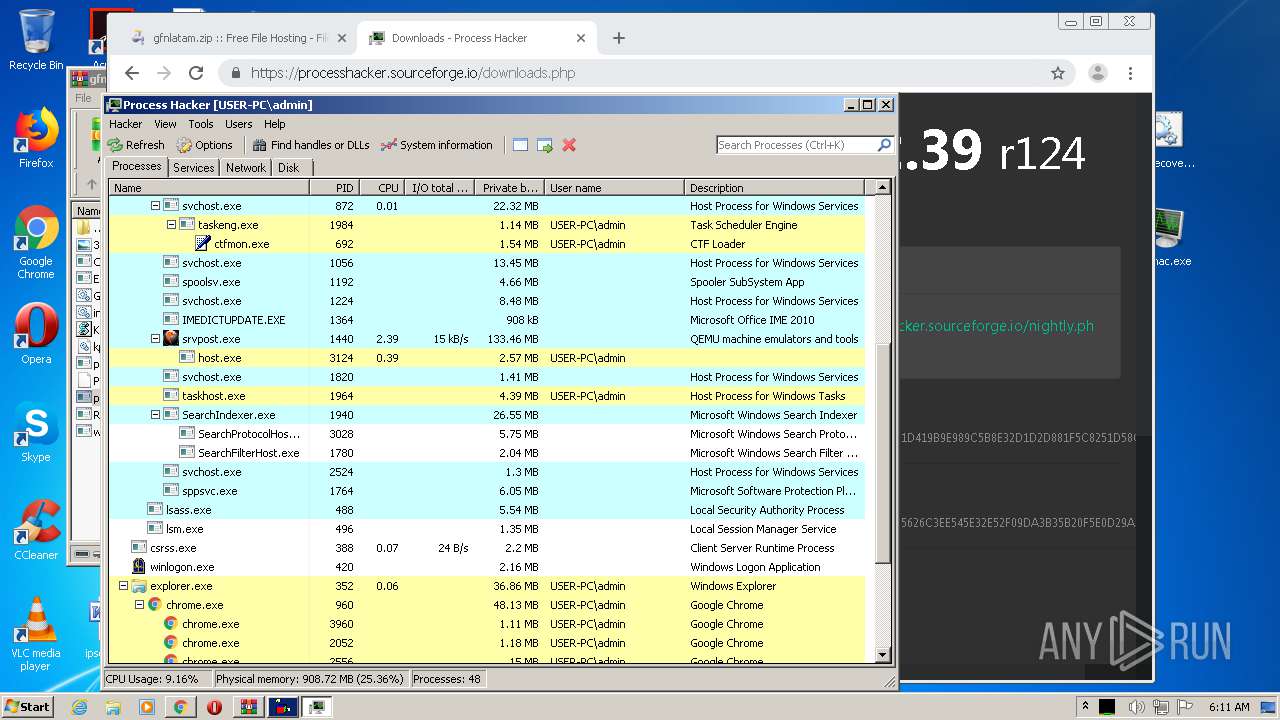
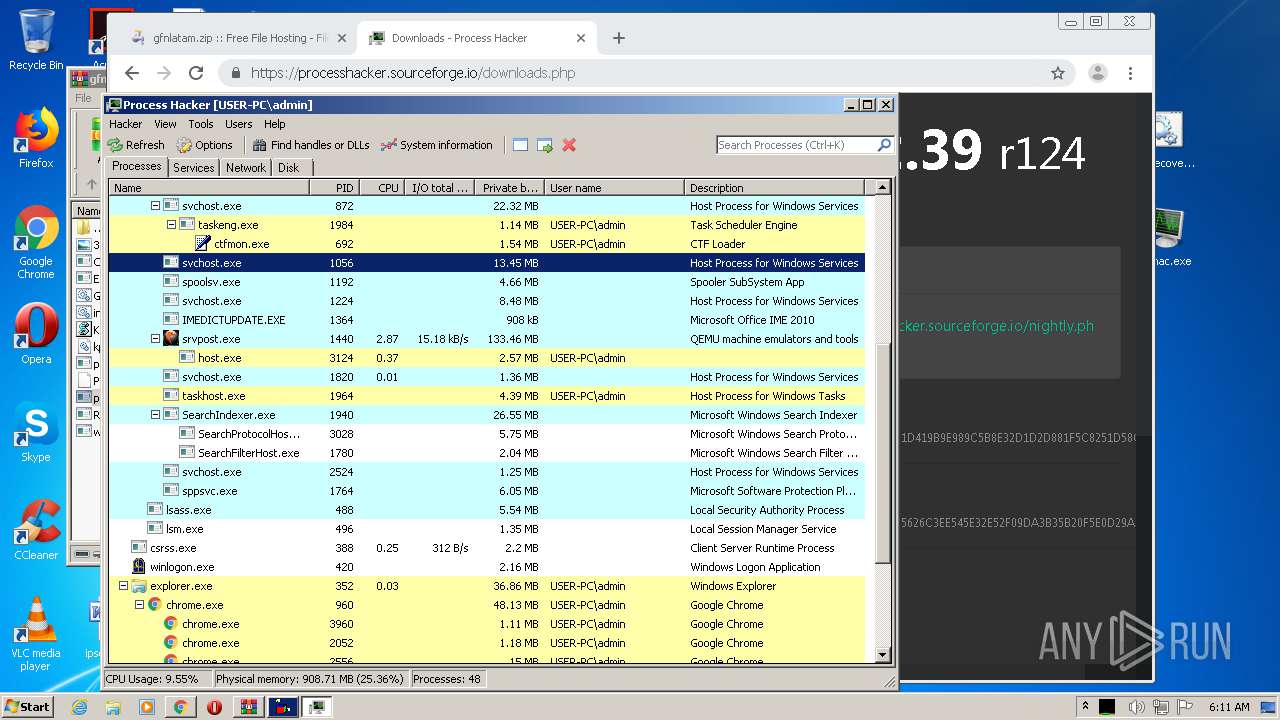
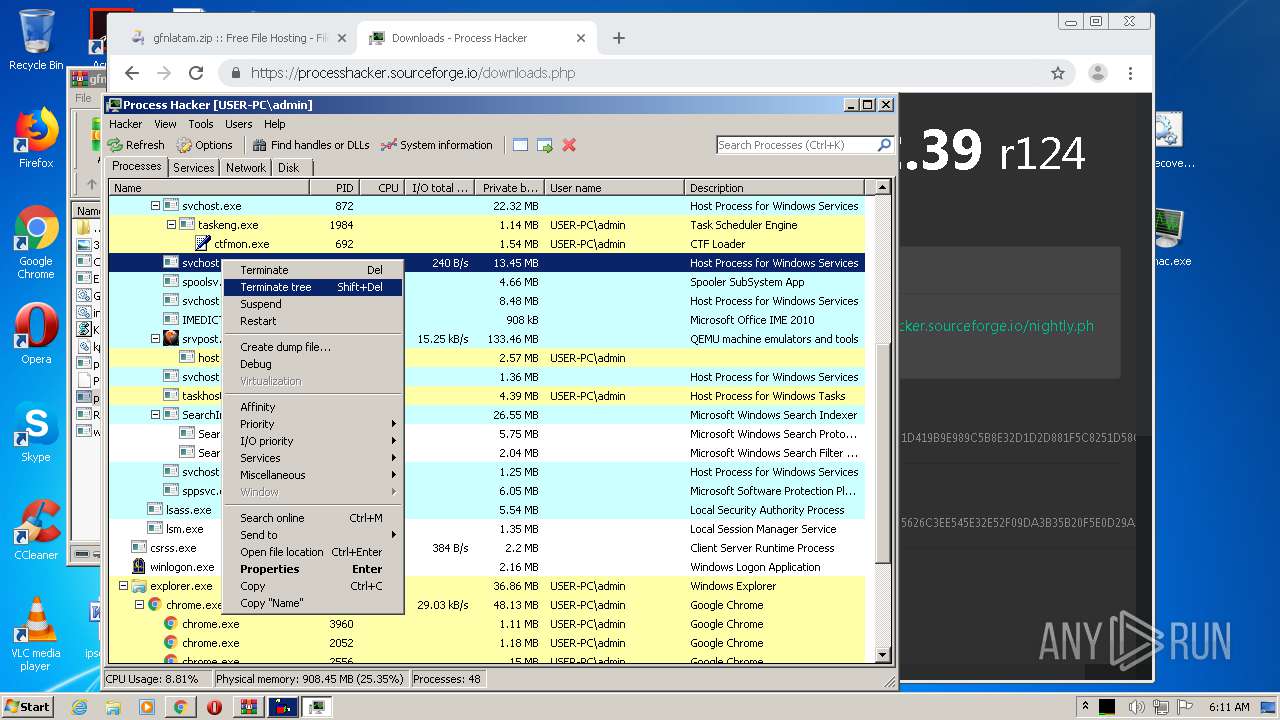
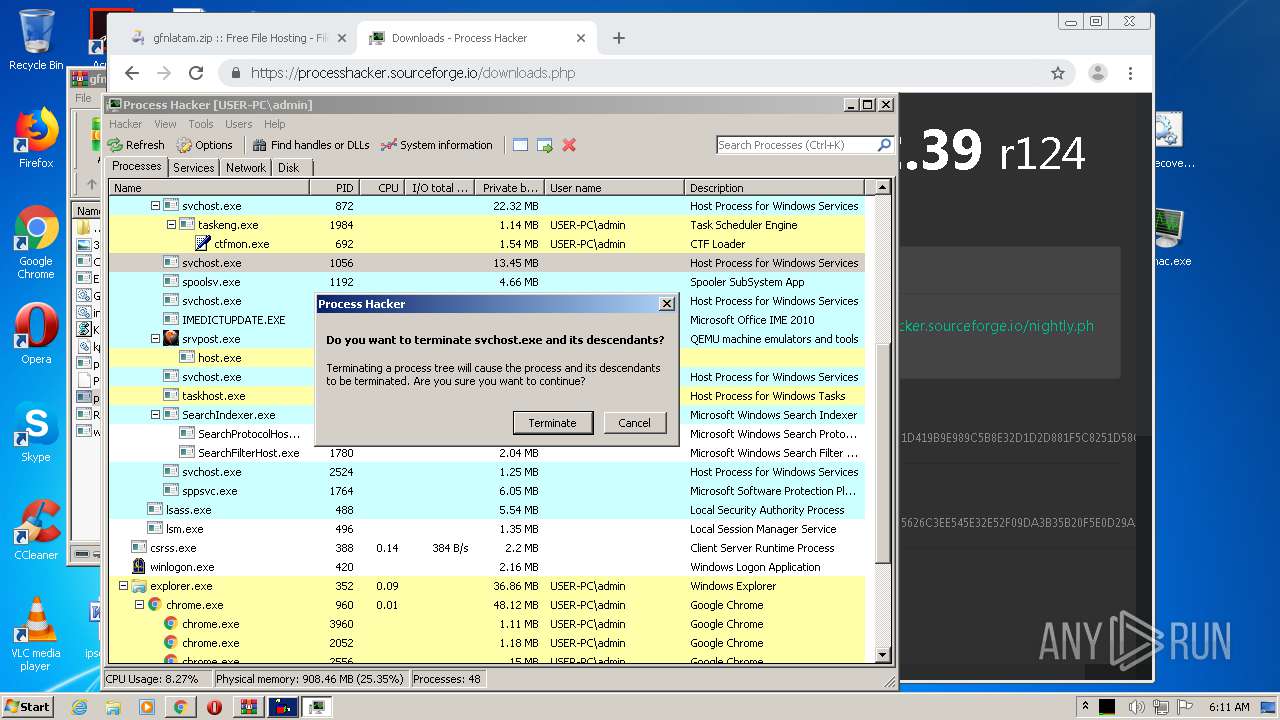
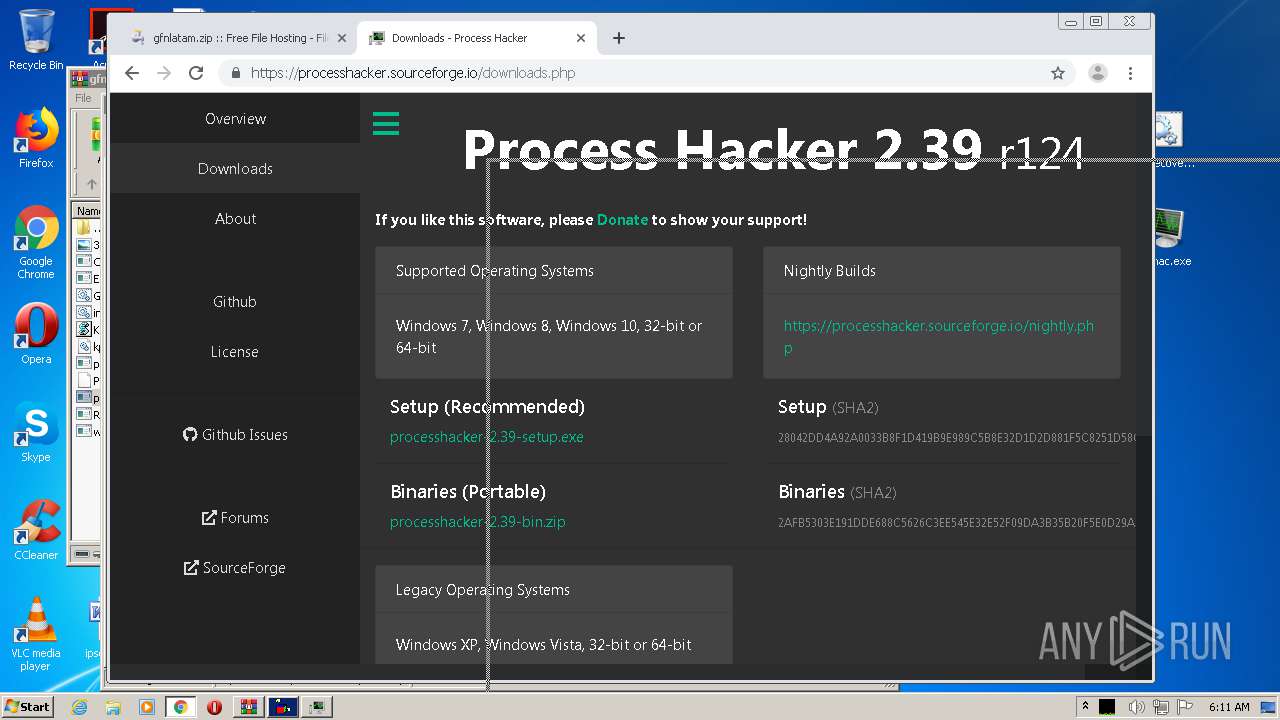
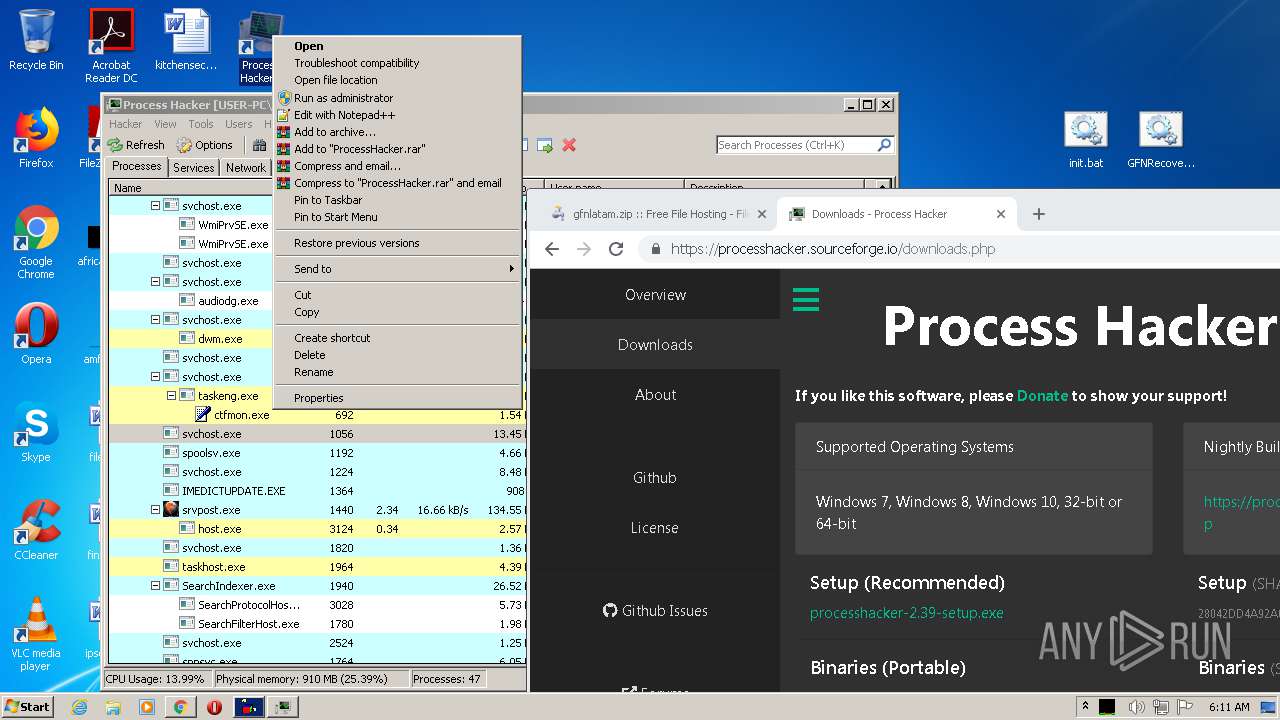
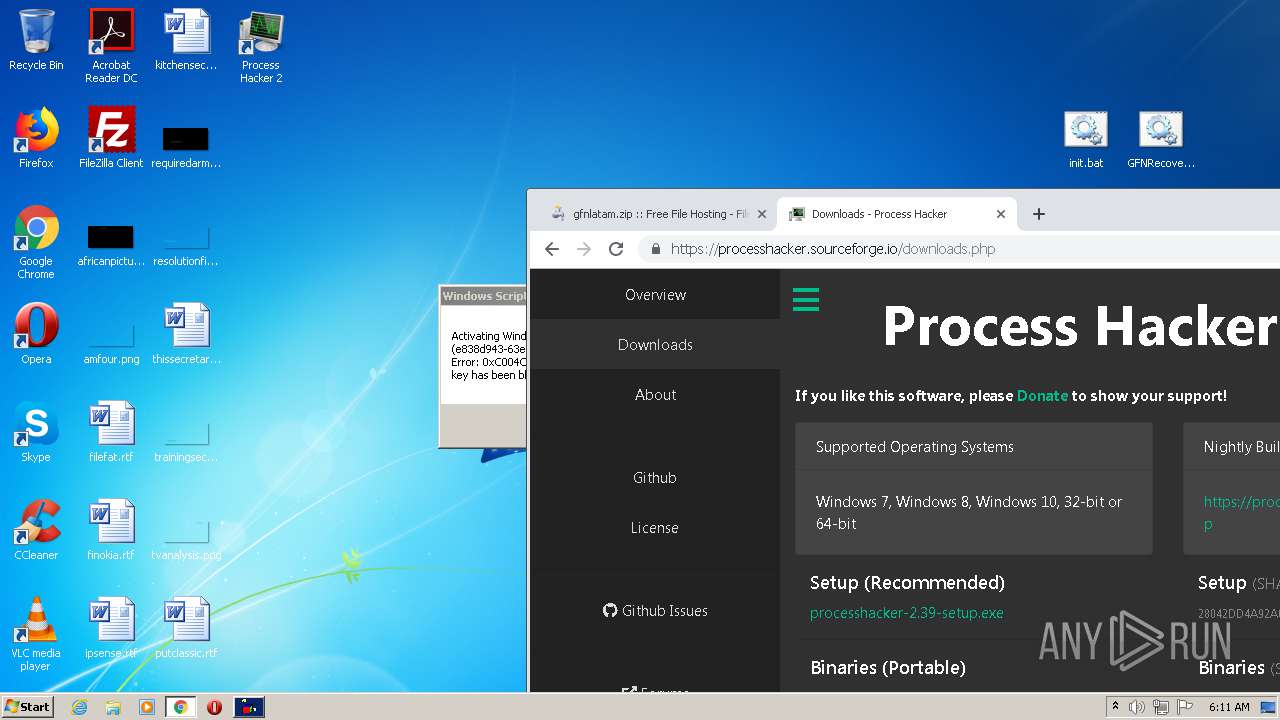
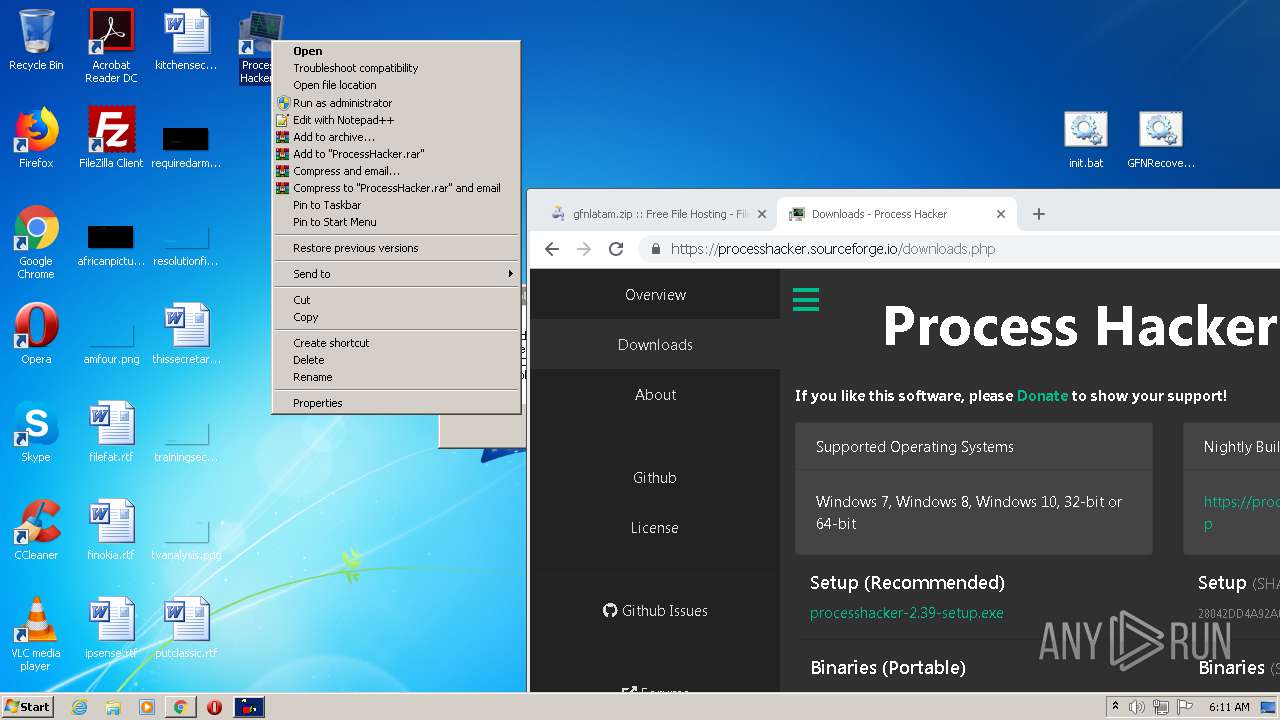
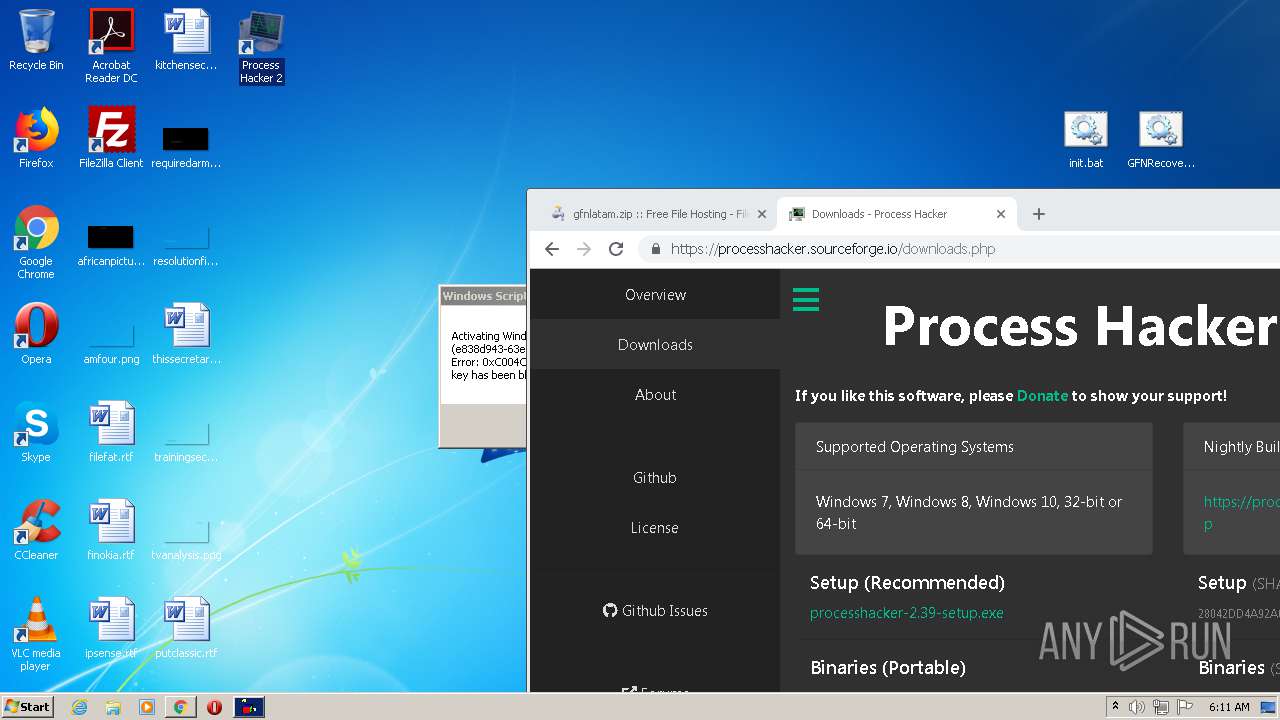
- processhacker-2.39-setup.exe (PID: 1664)
- processhacker-2.39-setup.exe (PID: 992)
- ProcessHacker.exe (PID: 2112)
- ProcessHacker.exe (PID: 3136)
- ProcessHacker.exe (PID: 2260)
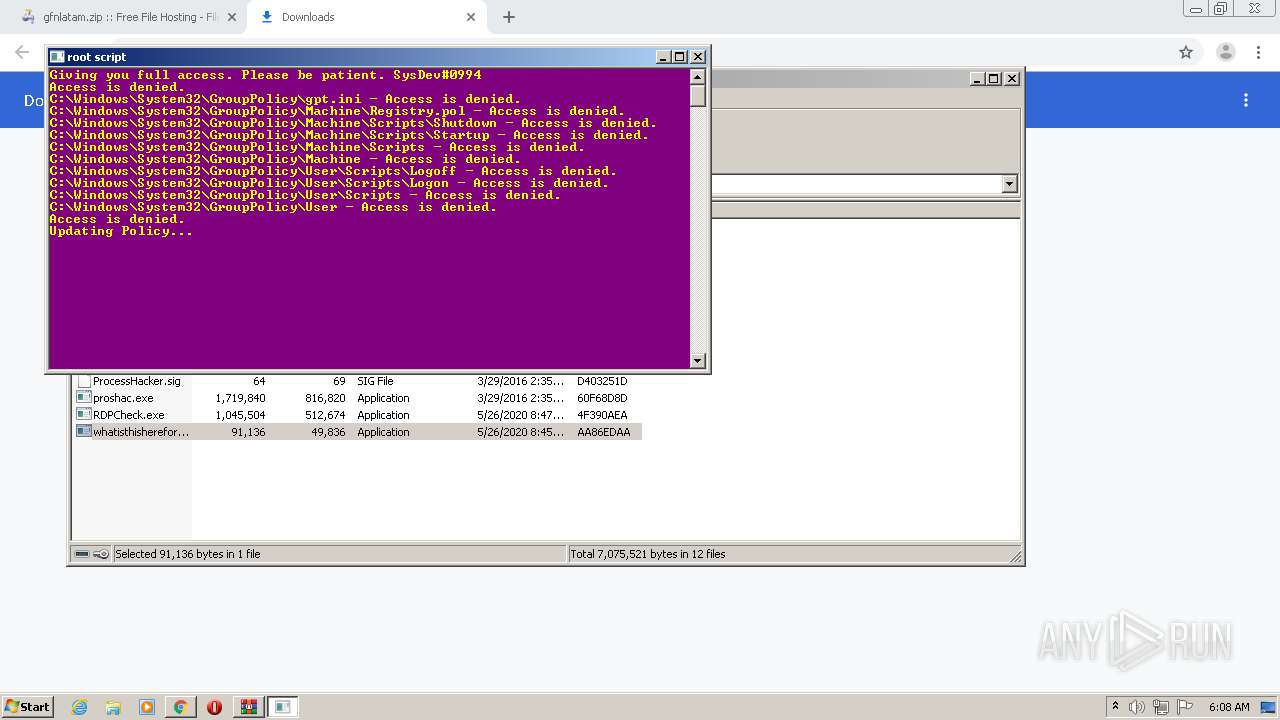
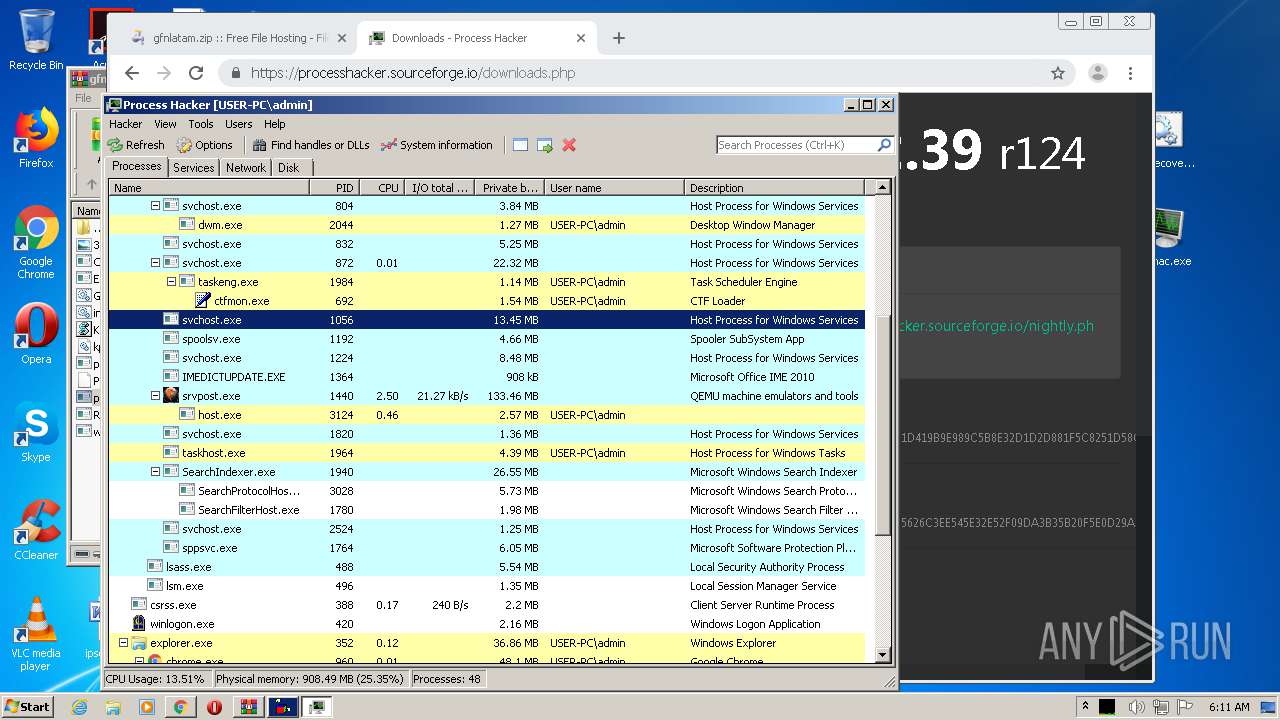
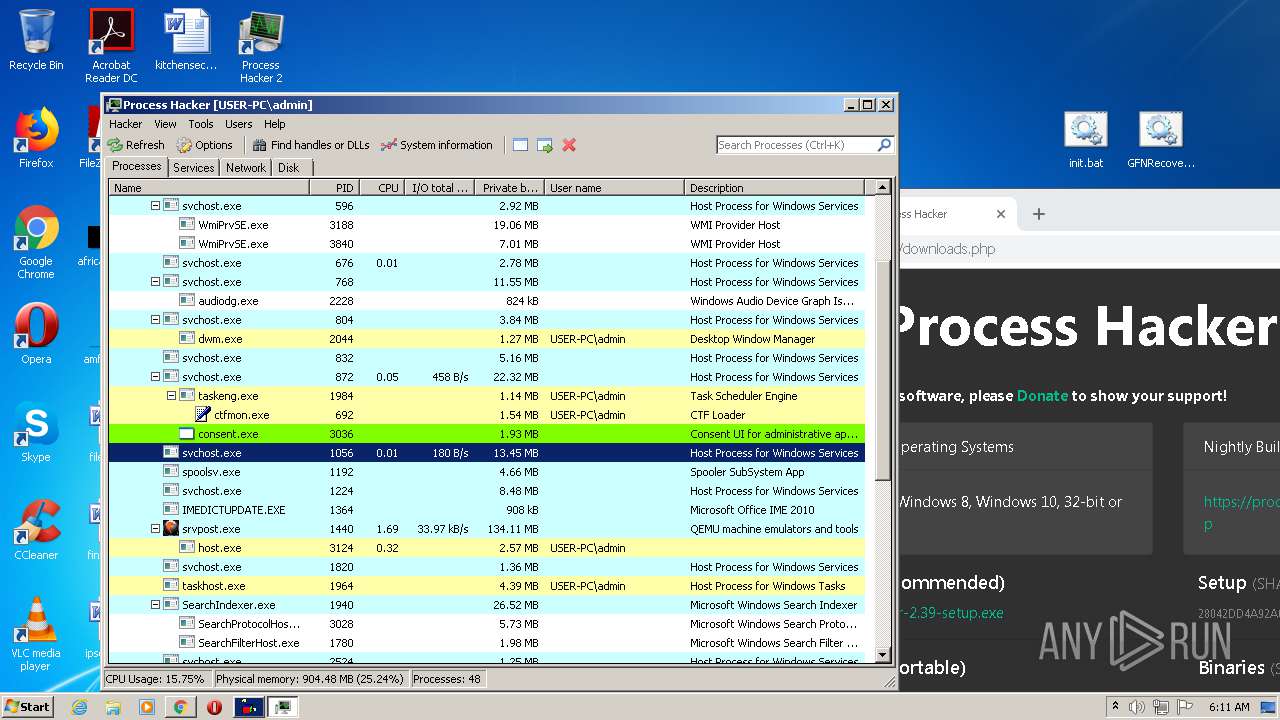
Changes the login/logoff helper path in the registry
- reg.exe (PID: 2852)
- reg.exe (PID: 924)
Loads dropped or rewritten executable
- ProcessHacker.exe (PID: 2112)
- ProcessHacker.exe (PID: 2260)
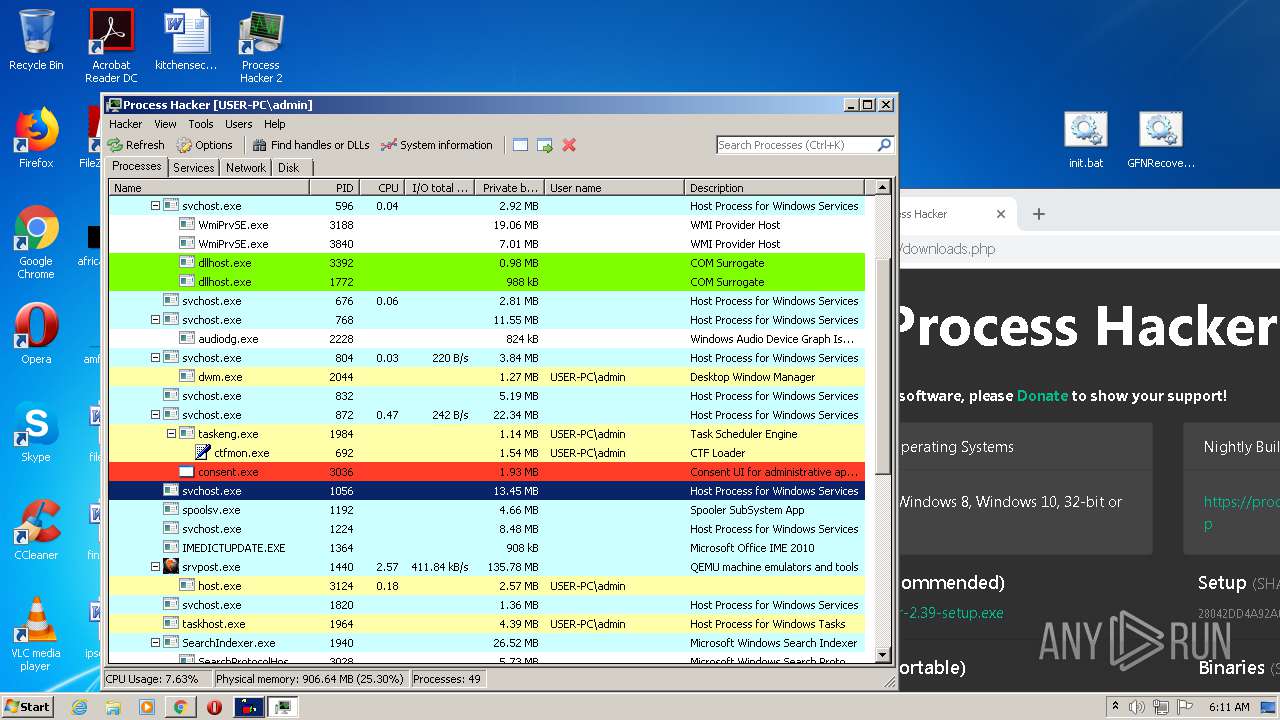
Changes settings of System certificates
- ProcessHacker.exe (PID: 2260)
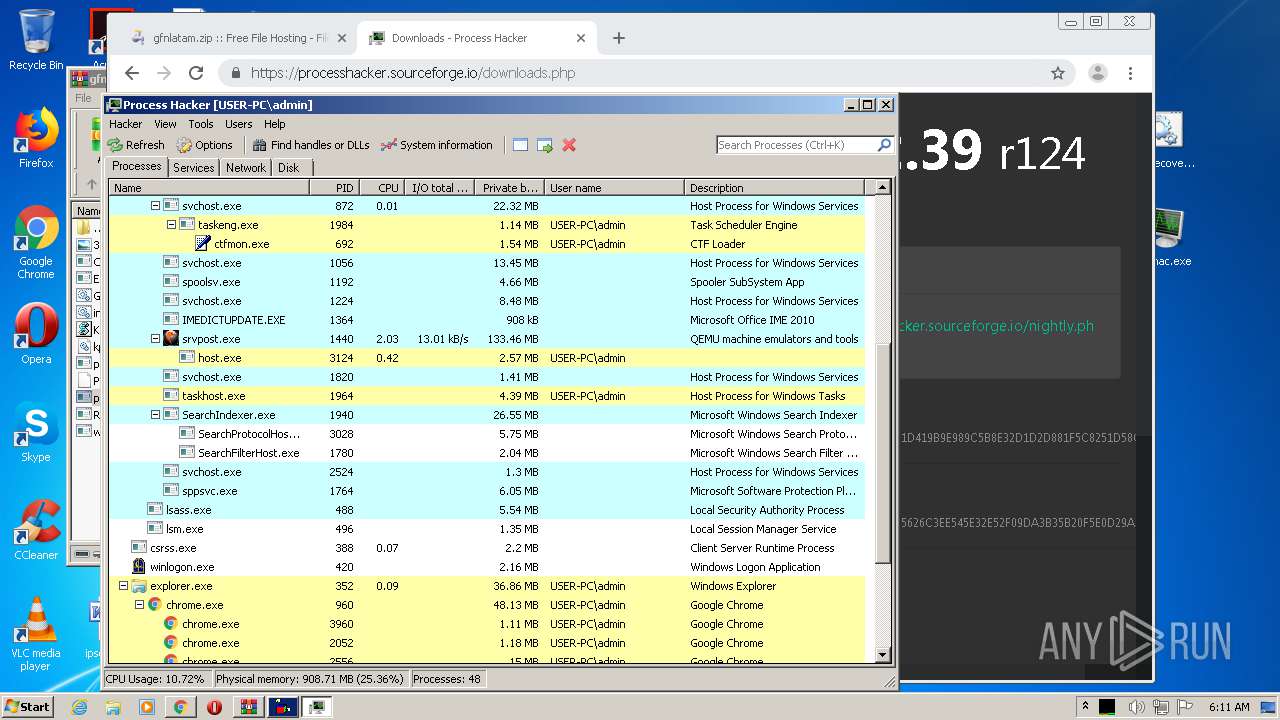
Loads the Task Scheduler COM API
- ProcessHacker.exe (PID: 2260)
SUSPICIOUS
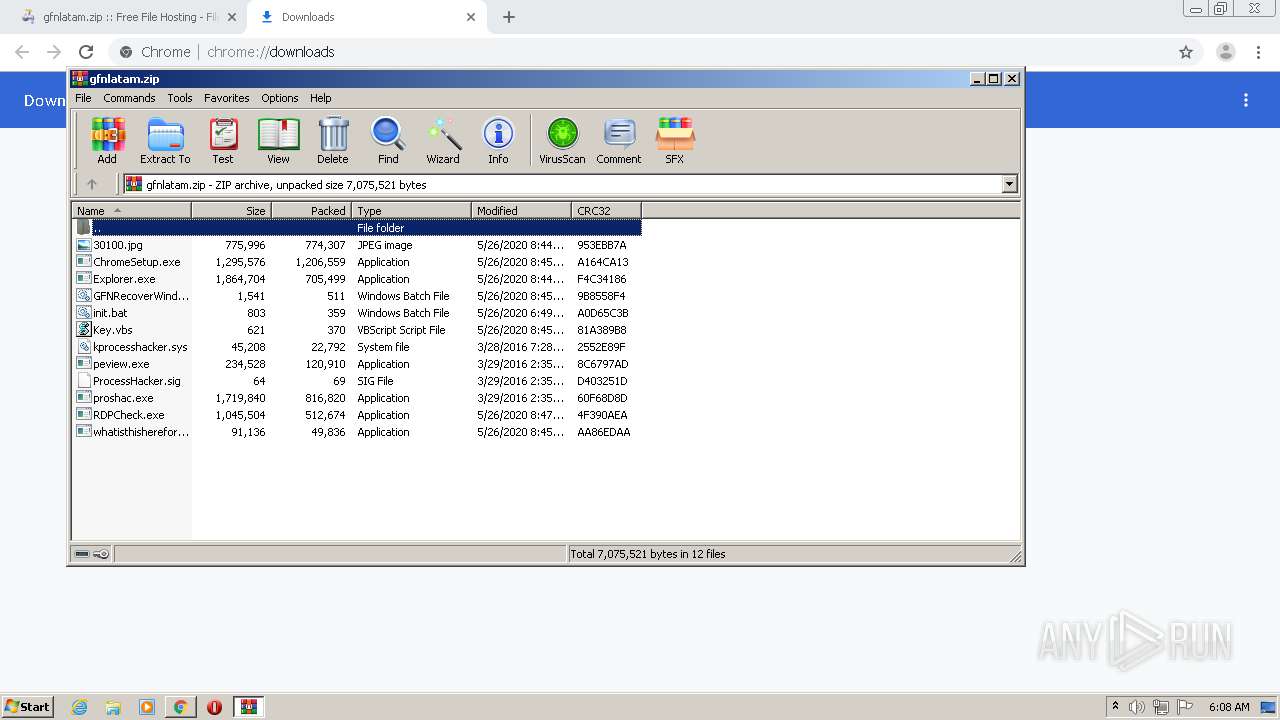
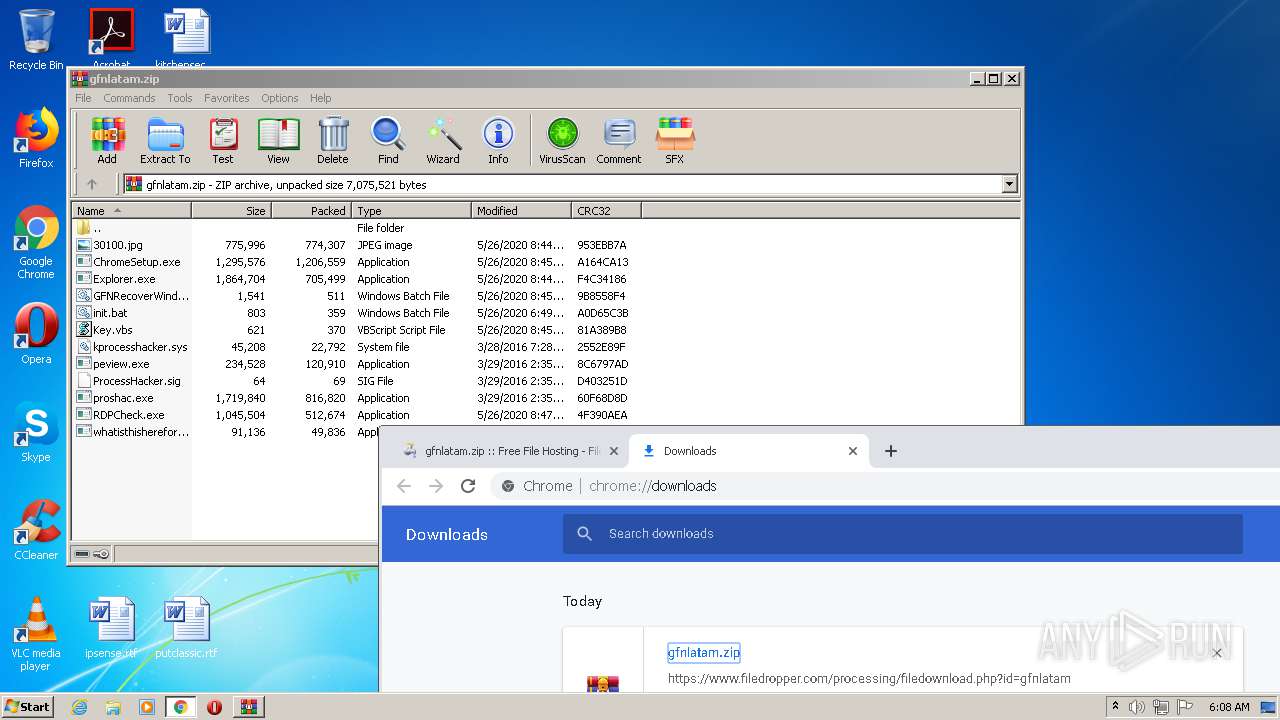
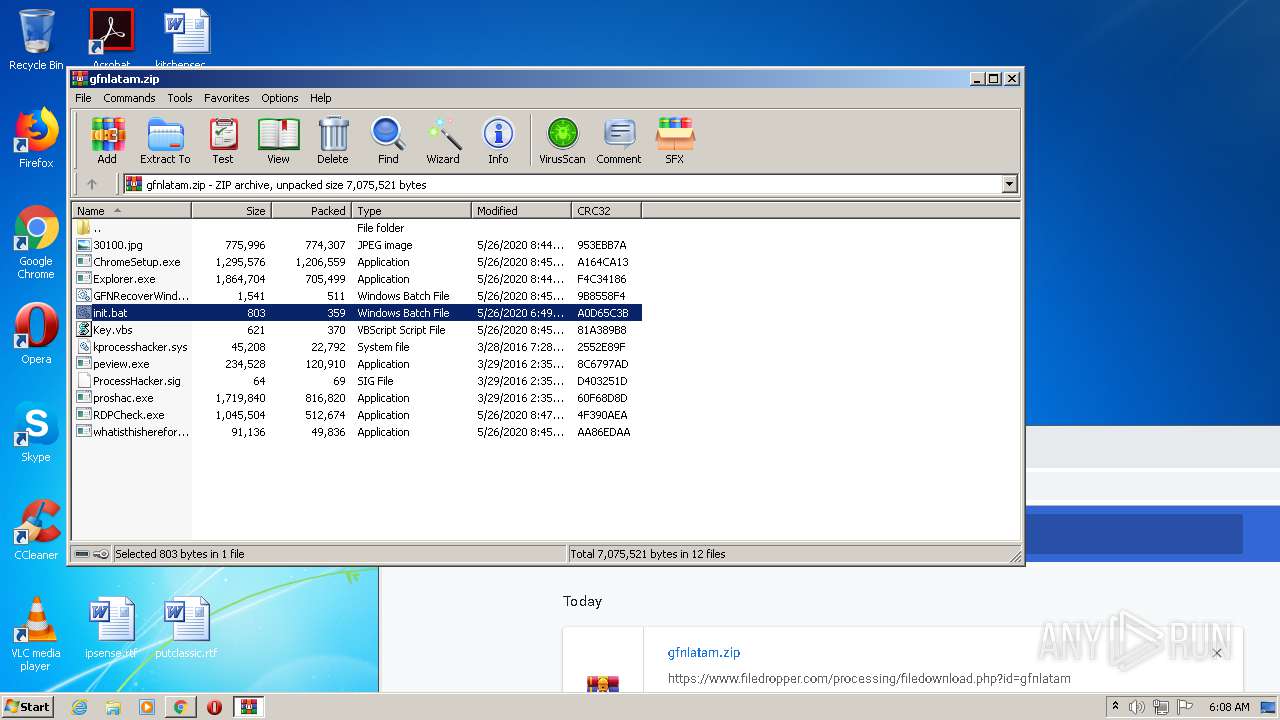
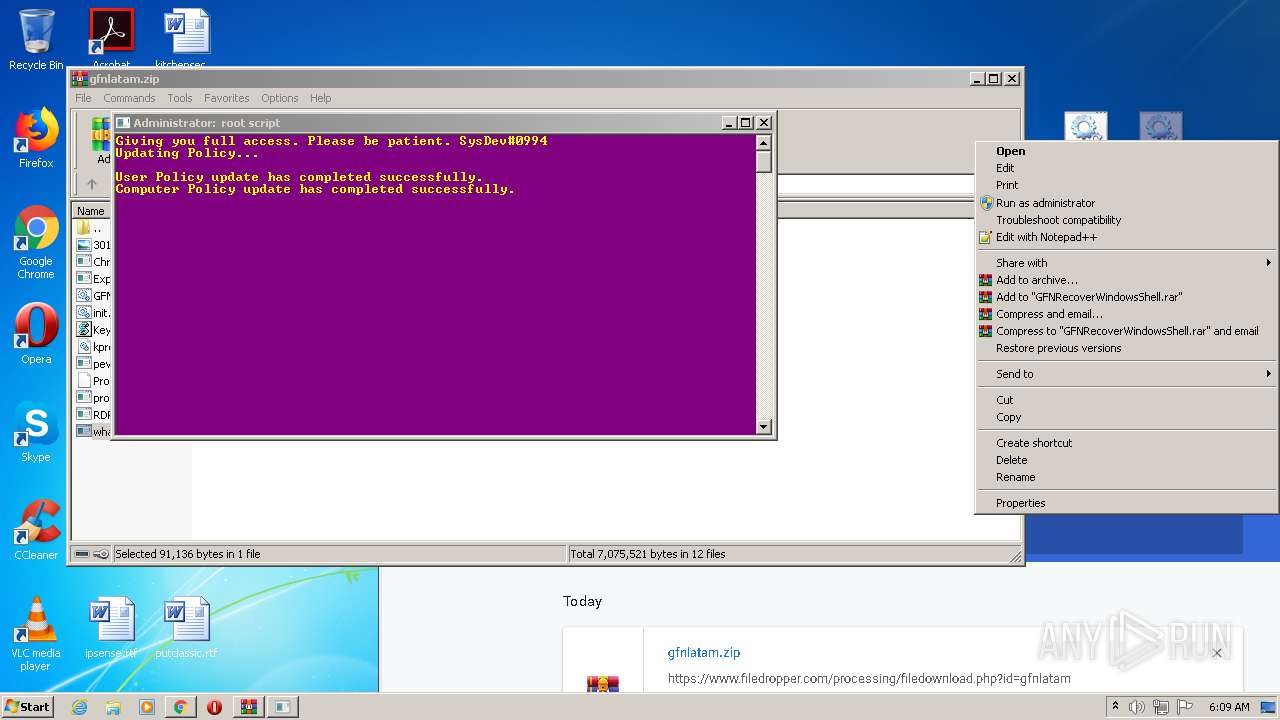
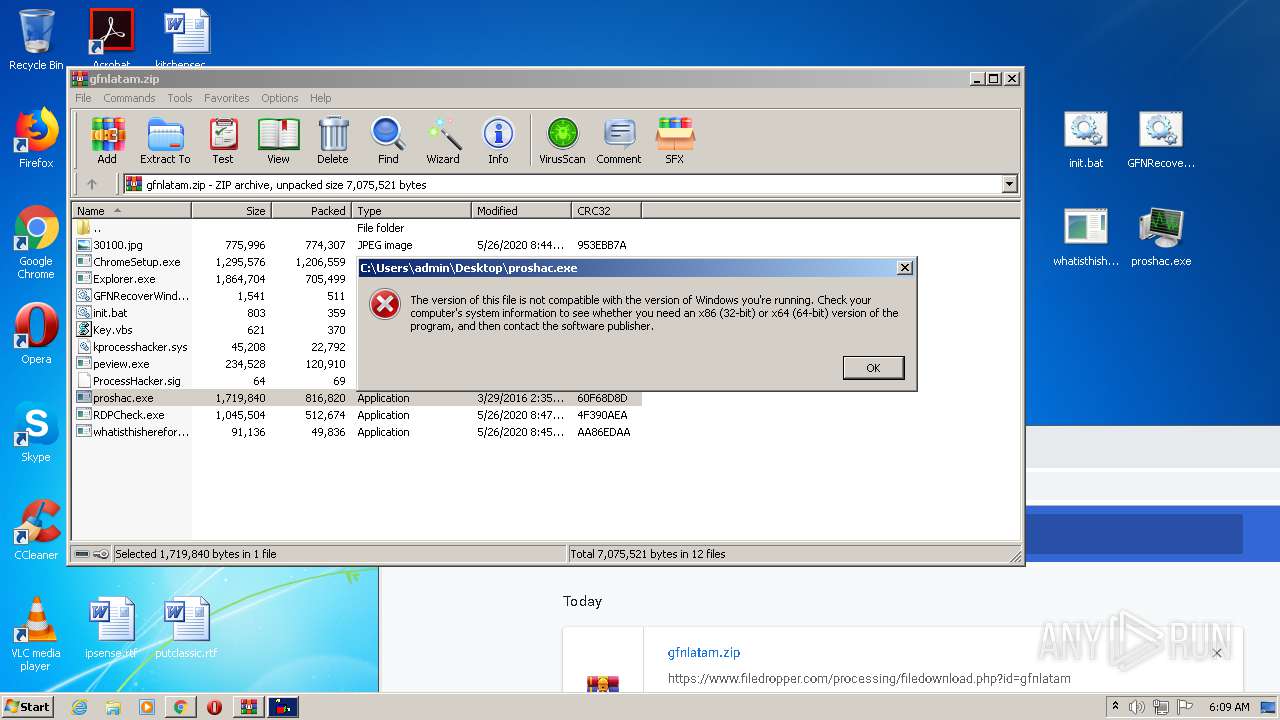
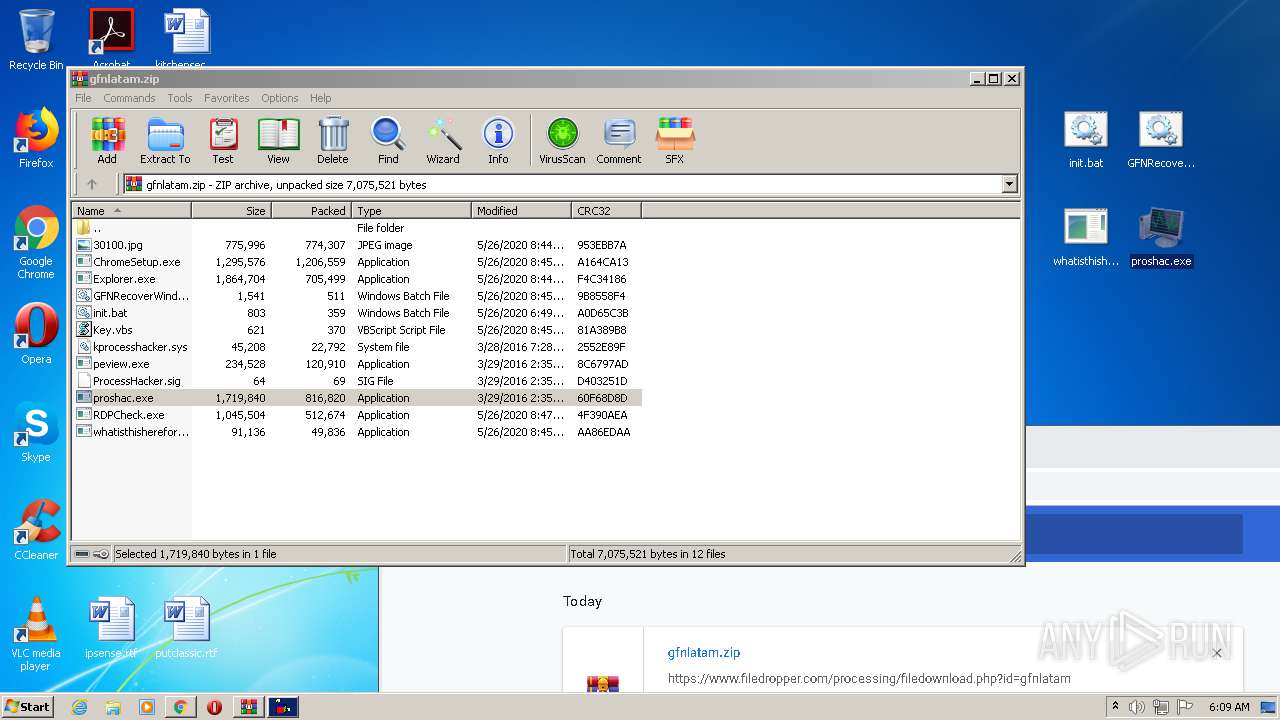
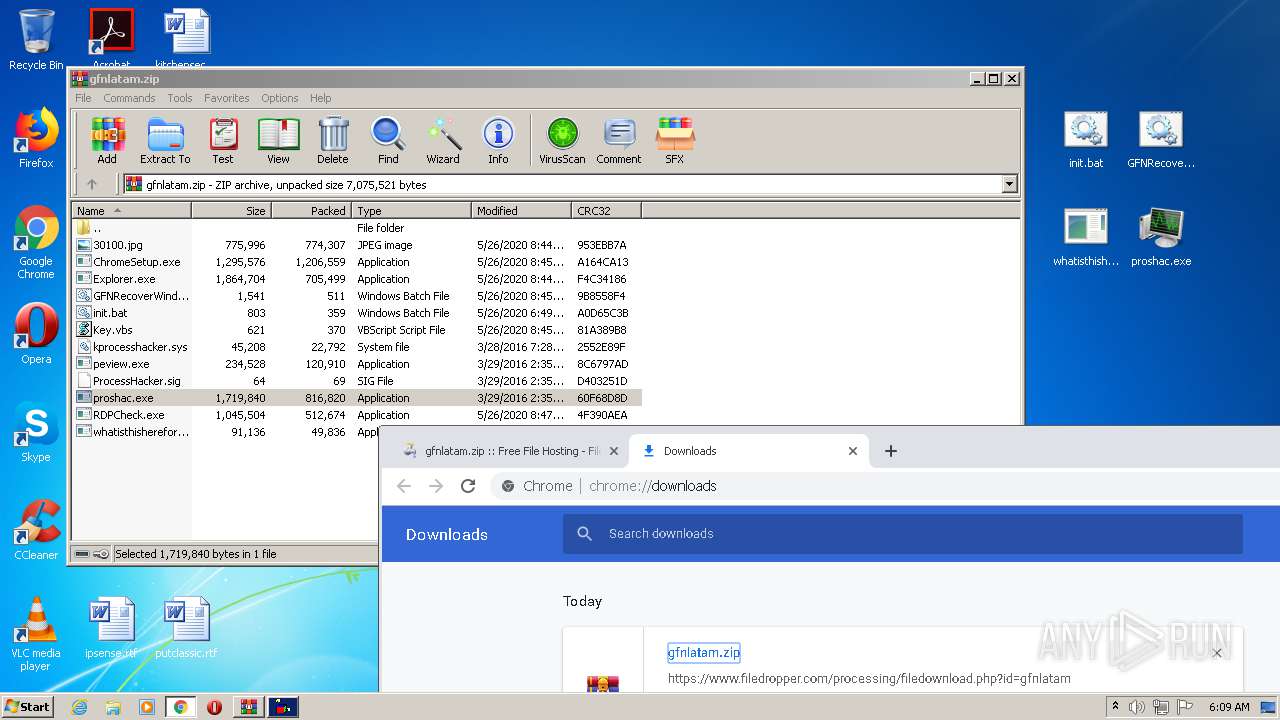
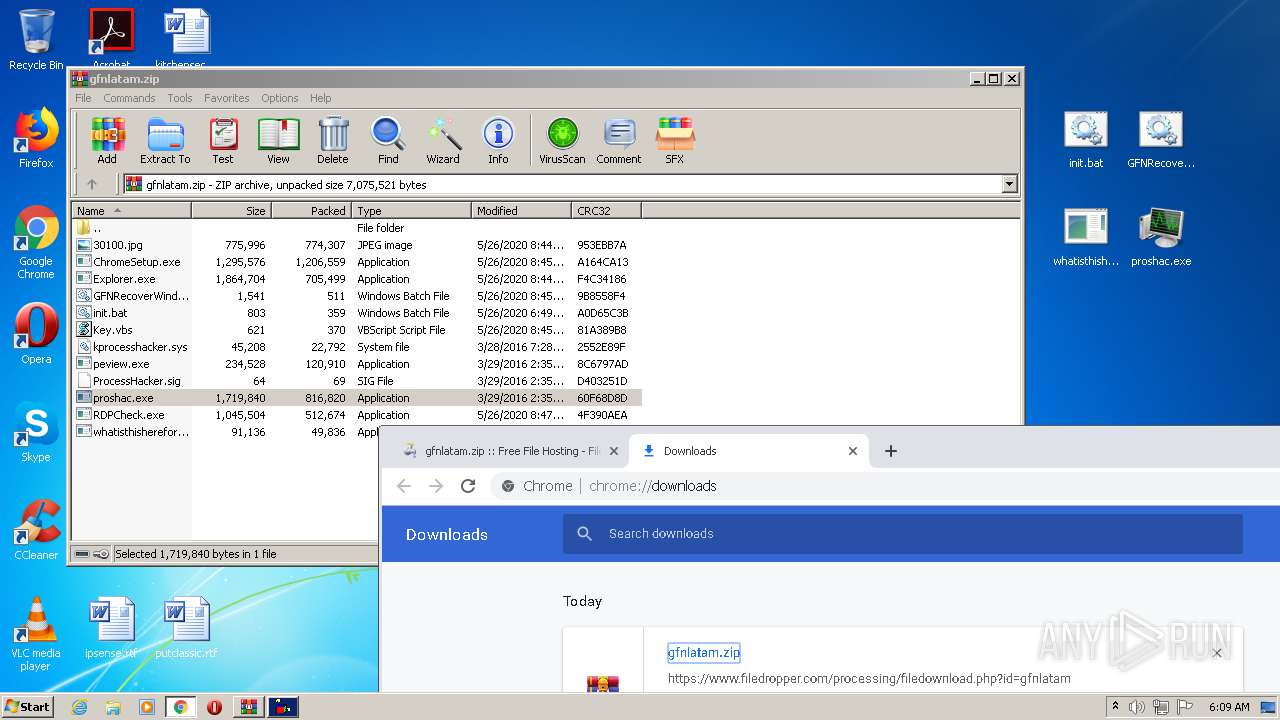
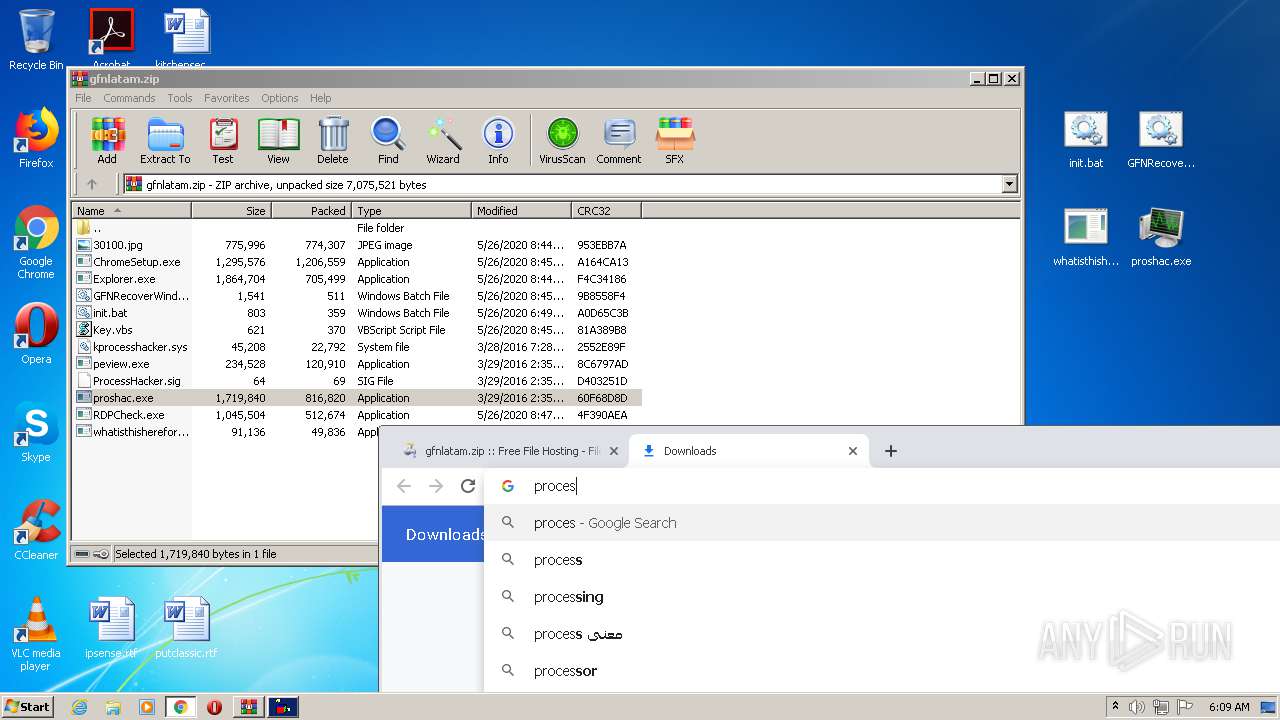
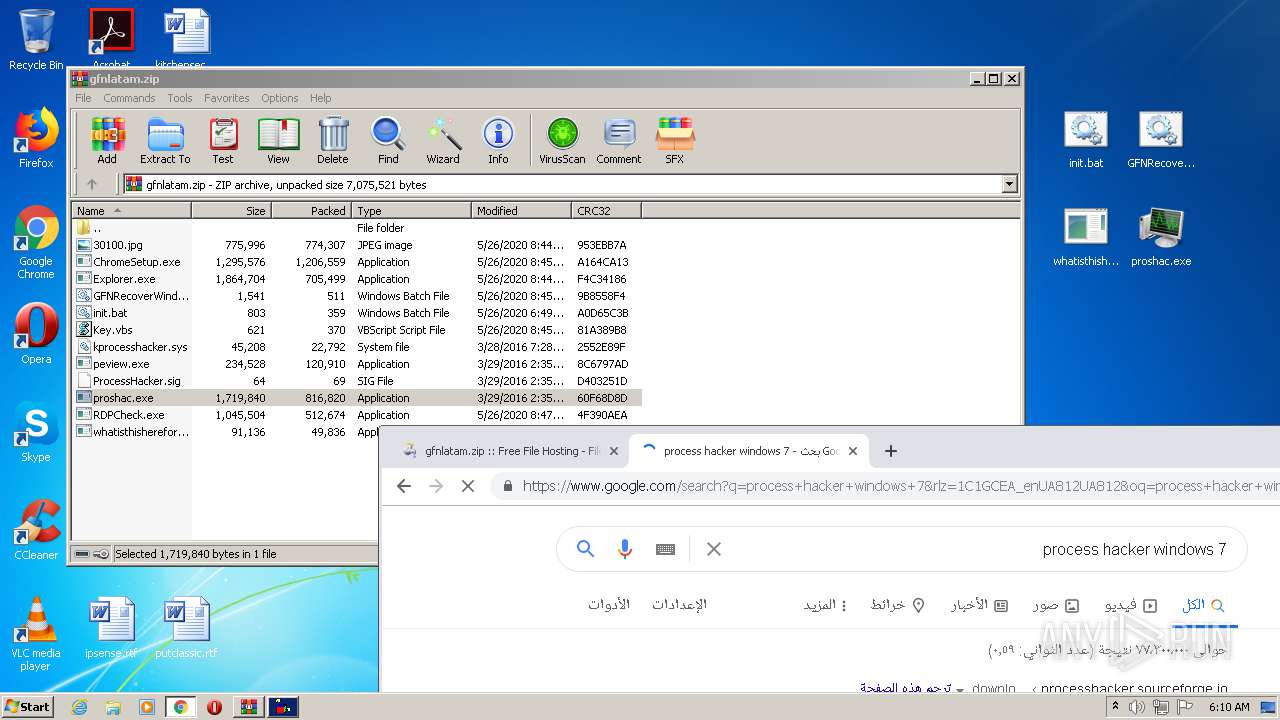
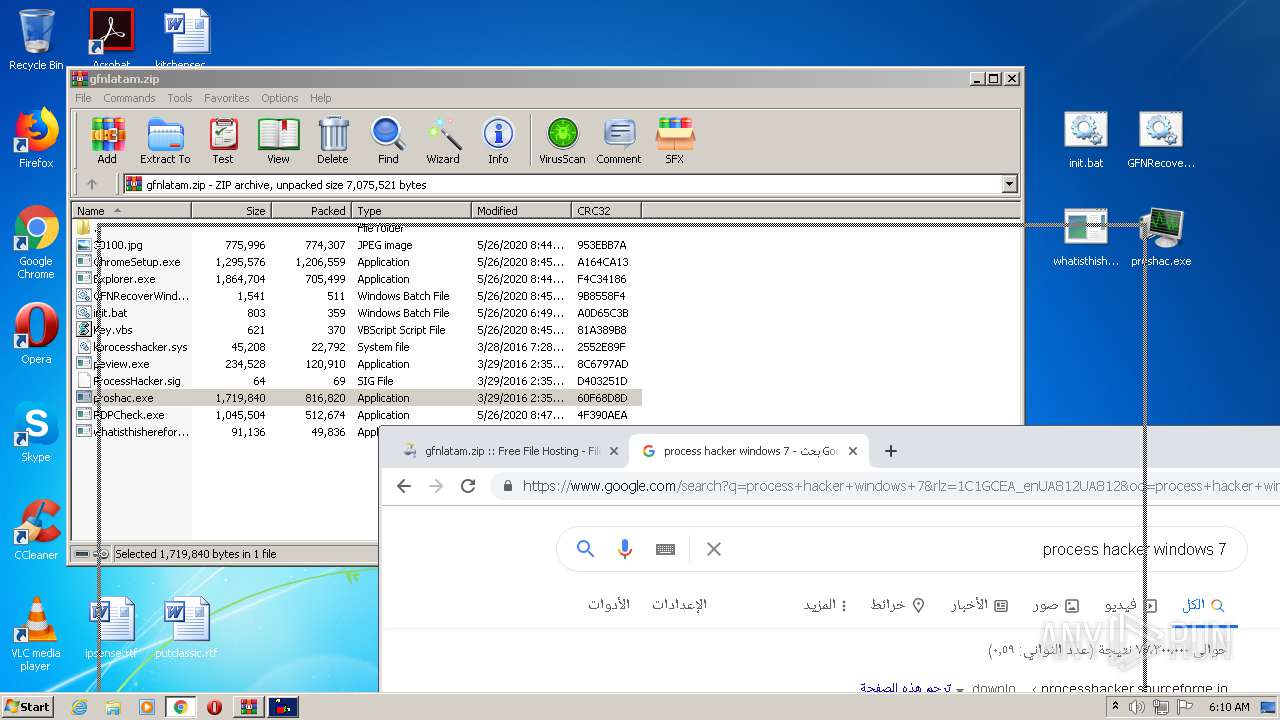
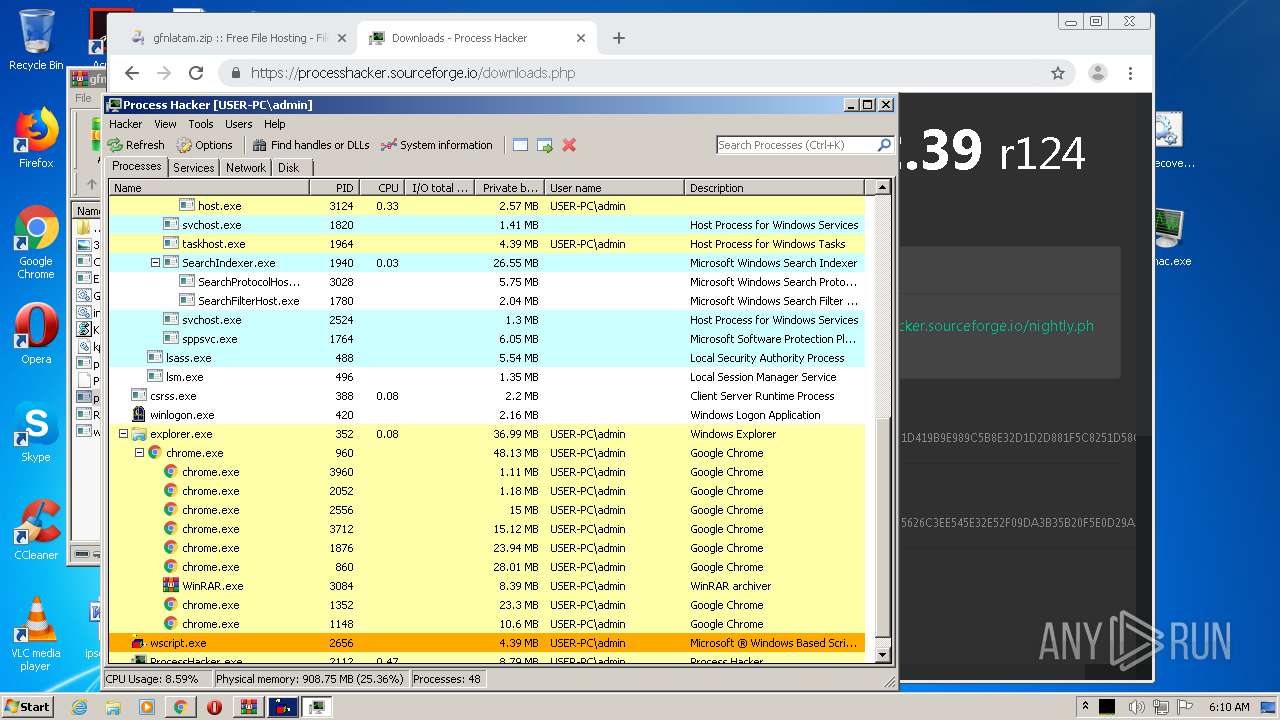
Creates executable files which already exist in Windows
- WinRAR.exe (PID: 3084)
Starts CMD.EXE for commands execution
- chrome.exe (PID: 960)
- whatisthisherefor.exe (PID: 1784)
- WinRAR.exe (PID: 3084)
- whatisthisherefor.exe (PID: 3644)
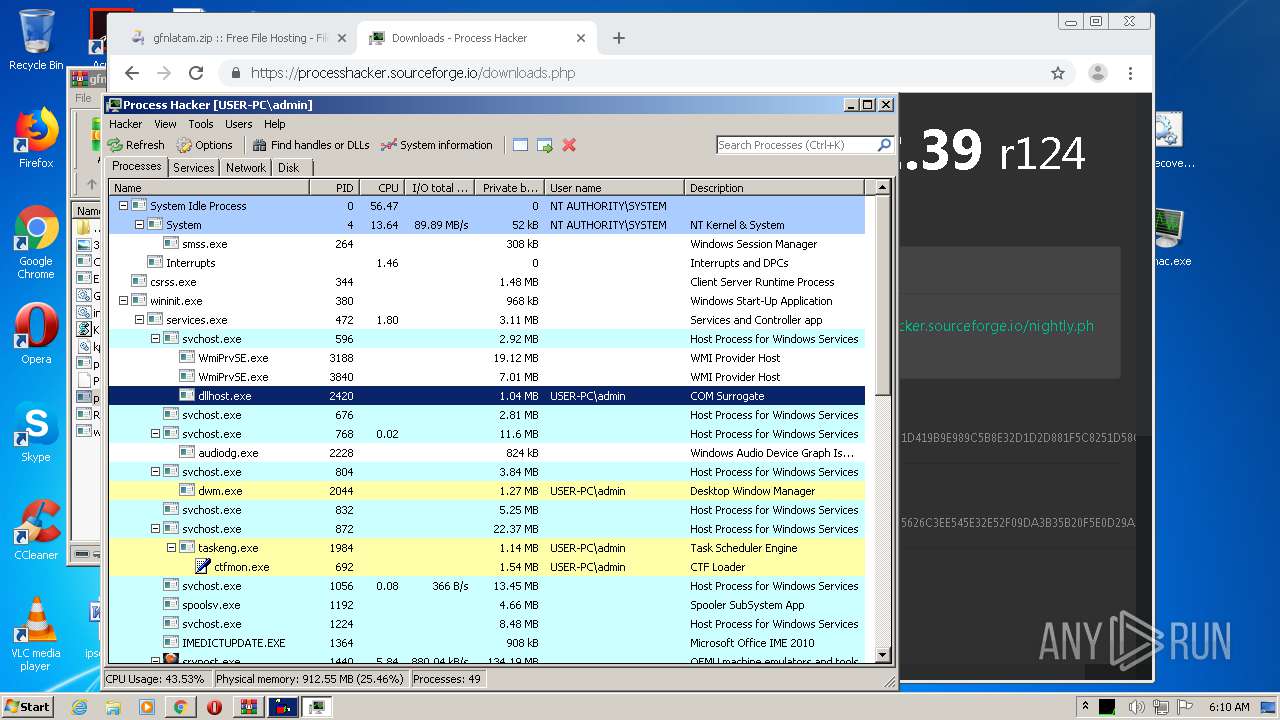
Executed via COM
- DllHost.exe (PID: 2860)
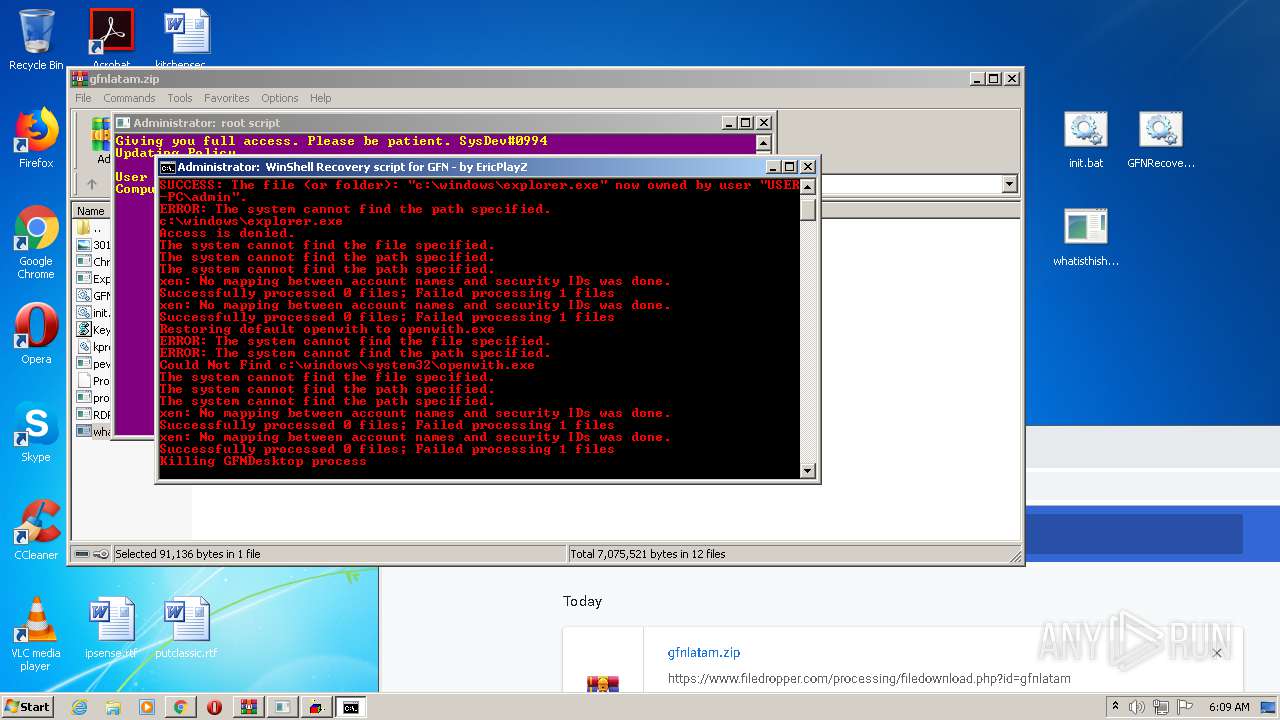
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2404)
- cmd.exe (PID: 3808)
- cmd.exe (PID: 2028)
- cmd.exe (PID: 2056)
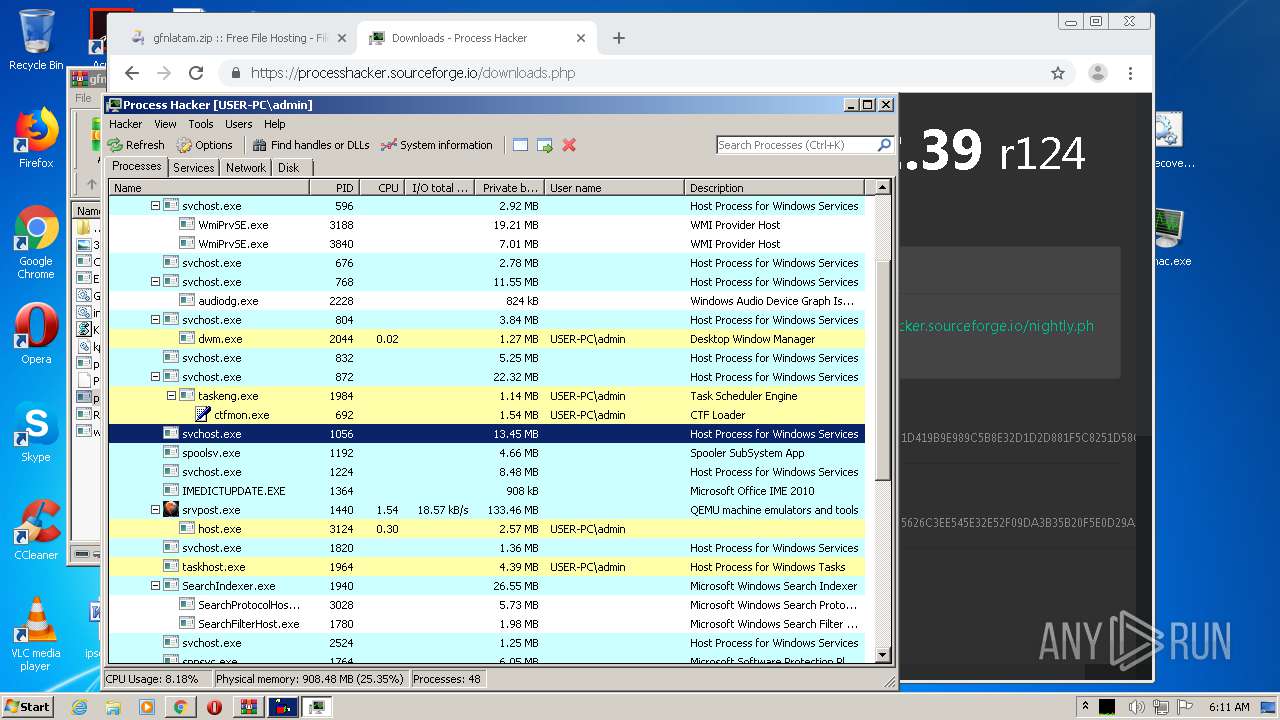
Executable content was dropped or overwritten
- cmd.exe (PID: 3808)
- WinRAR.exe (PID: 3084)
- cmd.exe (PID: 2028)
- chrome.exe (PID: 960)
- chrome.exe (PID: 3712)
- processhacker-2.39-setup.exe (PID: 1664)
- processhacker-2.39-setup.exe (PID: 992)
- processhacker-2.39-setup.tmp (PID: 3396)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2404)
- cmd.exe (PID: 3808)
- cmd.exe (PID: 2028)
- cmd.exe (PID: 2056)
Creates files in the Windows directory
- cmd.exe (PID: 3808)
- cmd.exe (PID: 2028)
Removes files from Windows directory
- cmd.exe (PID: 3900)
- cmd.exe (PID: 2028)
Executes scripts
- cmd.exe (PID: 3900)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 2056)
Creates files in the user directory
- ProcessHacker.exe (PID: 2112)
Adds / modifies Windows certificates
- ProcessHacker.exe (PID: 2260)
INFO
Reads the hosts file
- chrome.exe (PID: 960)
- chrome.exe (PID: 3712)
Reads settings of System Certificates
- chrome.exe (PID: 3712)
- ProcessHacker.exe (PID: 2112)
- ProcessHacker.exe (PID: 2260)
Application launched itself
- chrome.exe (PID: 960)
Reads Internet Cache Settings
- chrome.exe (PID: 960)
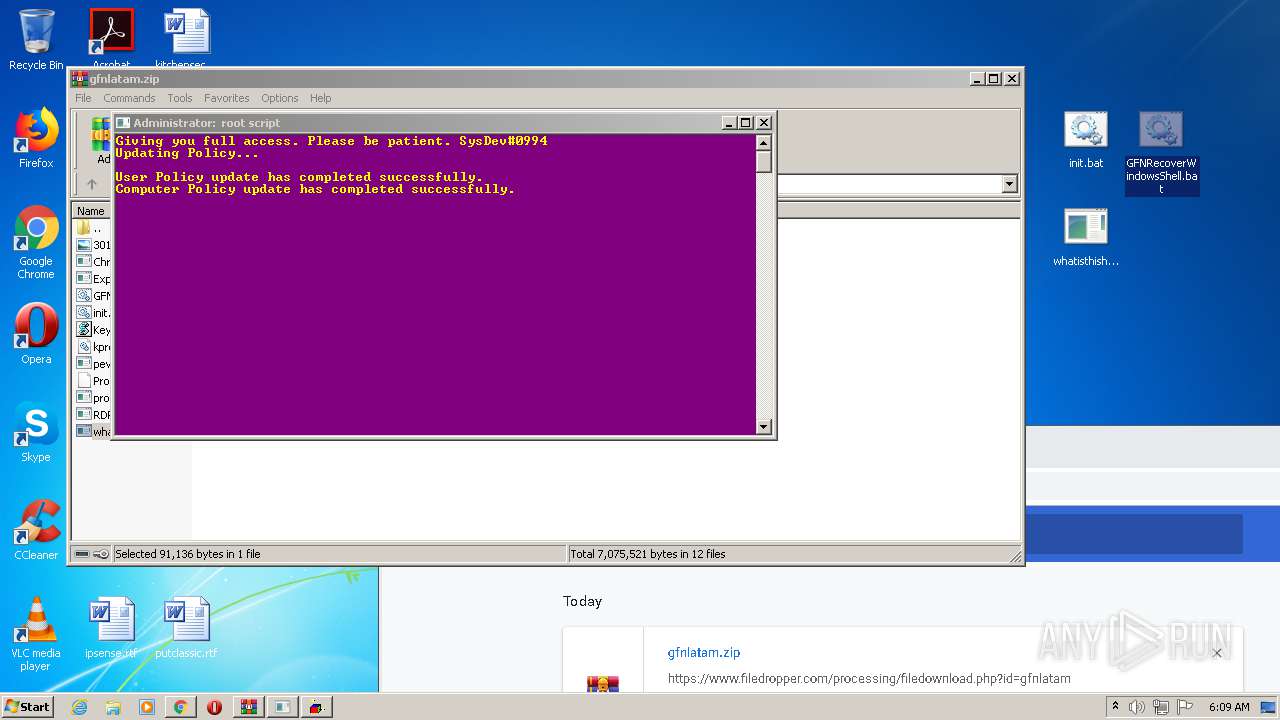
Manual execution by user
- cmd.exe (PID: 3808)
- whatisthisherefor.exe (PID: 3644)
- cmd.exe (PID: 2028)
- cmd.exe (PID: 2056)
- ProcessHacker.exe (PID: 3136)
- ProcessHacker.exe (PID: 2260)
Application was dropped or rewritten from another process
- processhacker-2.39-setup.tmp (PID: 2984)
- processhacker-2.39-setup.tmp (PID: 3396)
Loads dropped or rewritten executable
- processhacker-2.39-setup.tmp (PID: 3396)
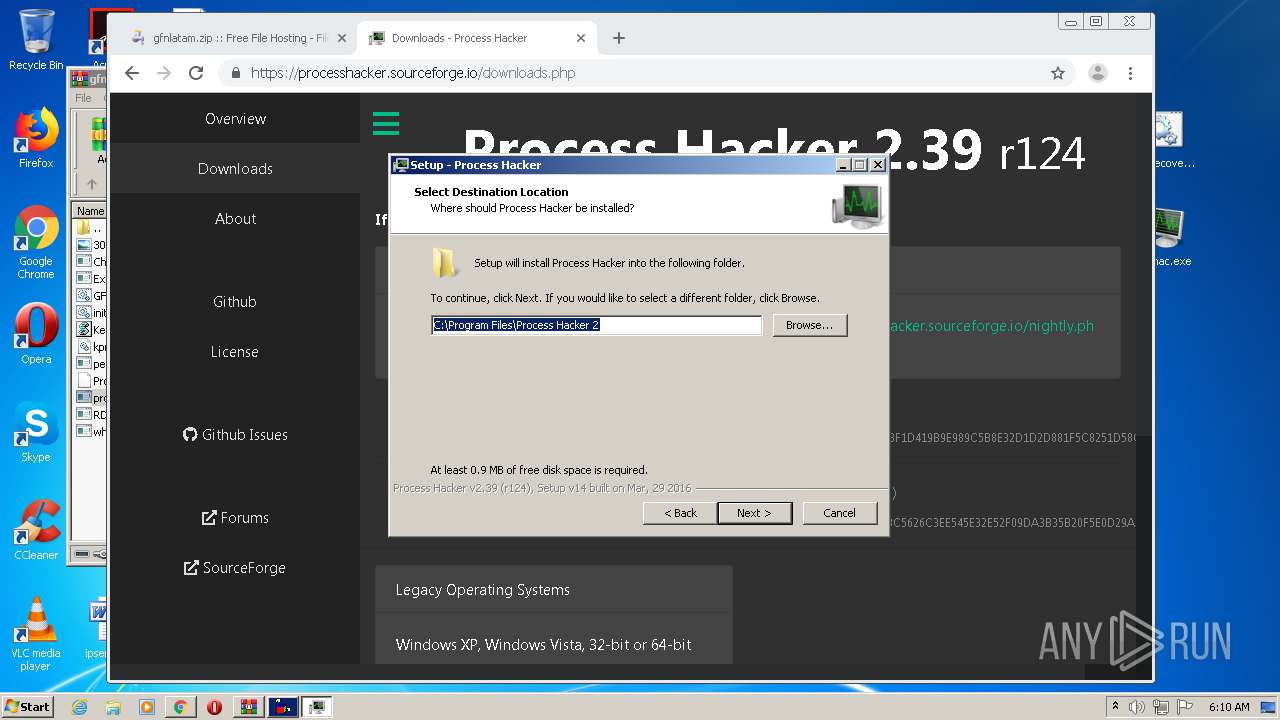
Creates files in the program directory
- processhacker-2.39-setup.tmp (PID: 3396)
Creates a software uninstall entry
- processhacker-2.39-setup.tmp (PID: 3396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
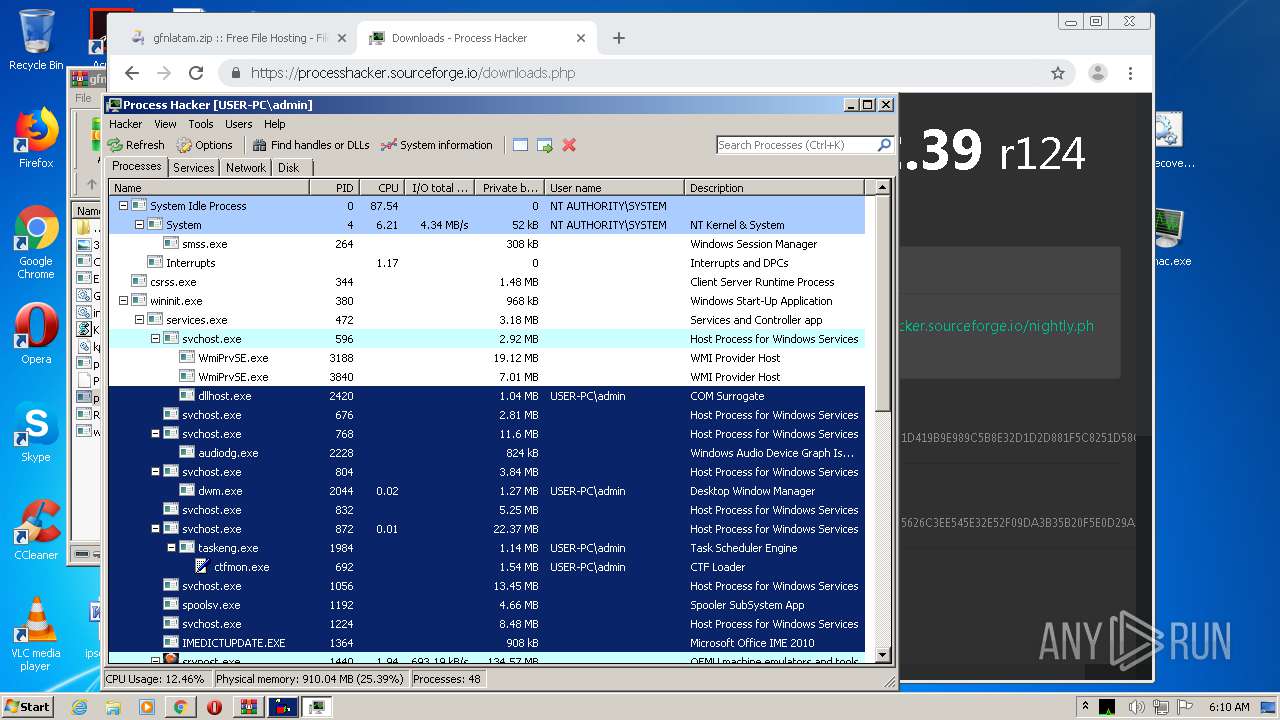
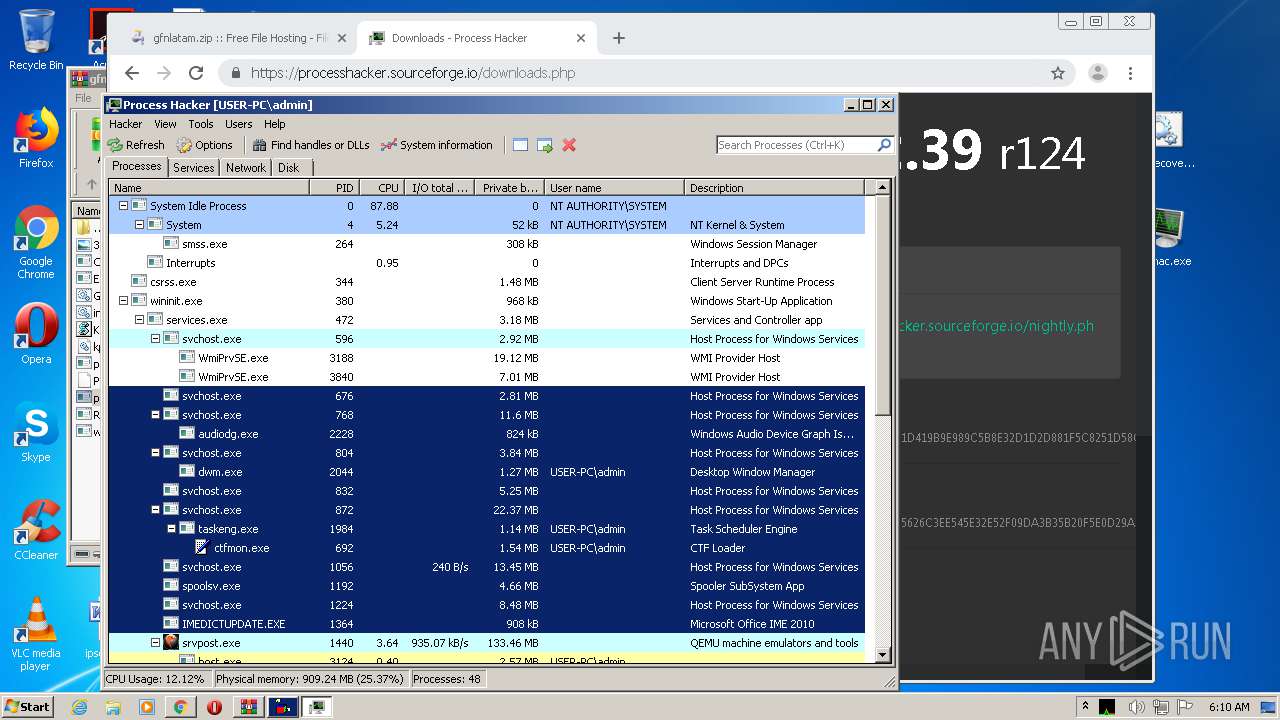
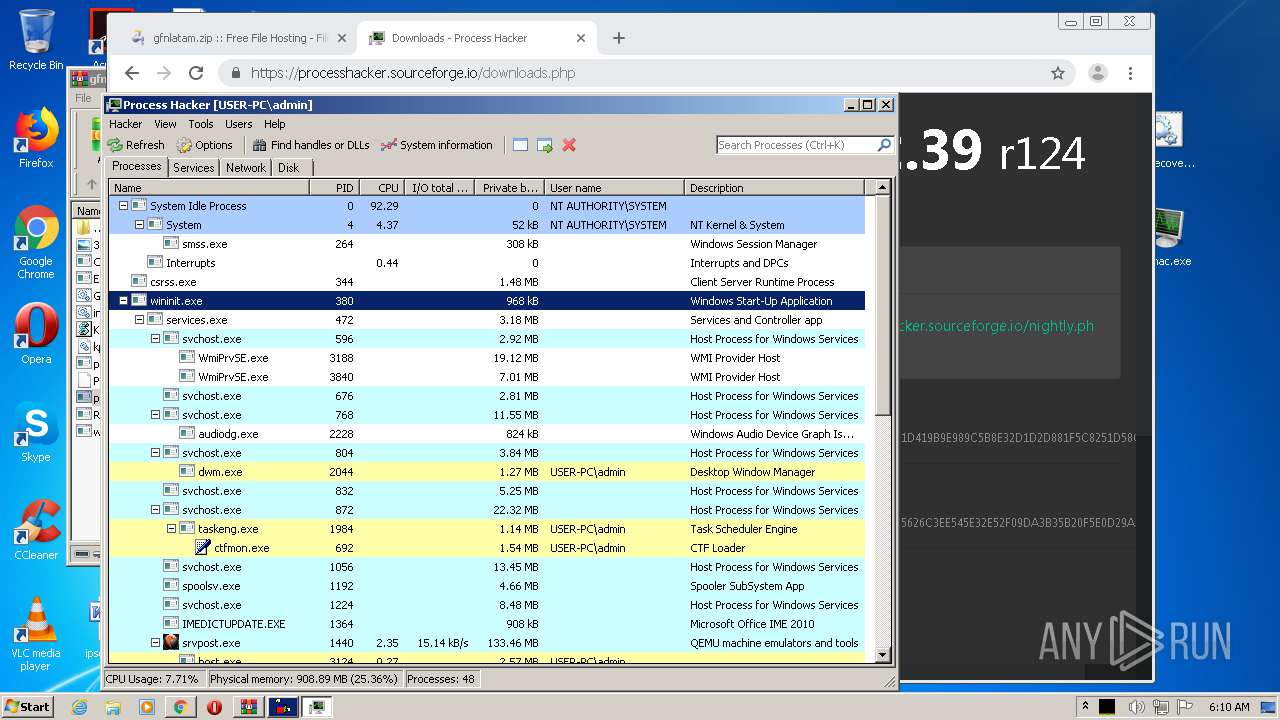
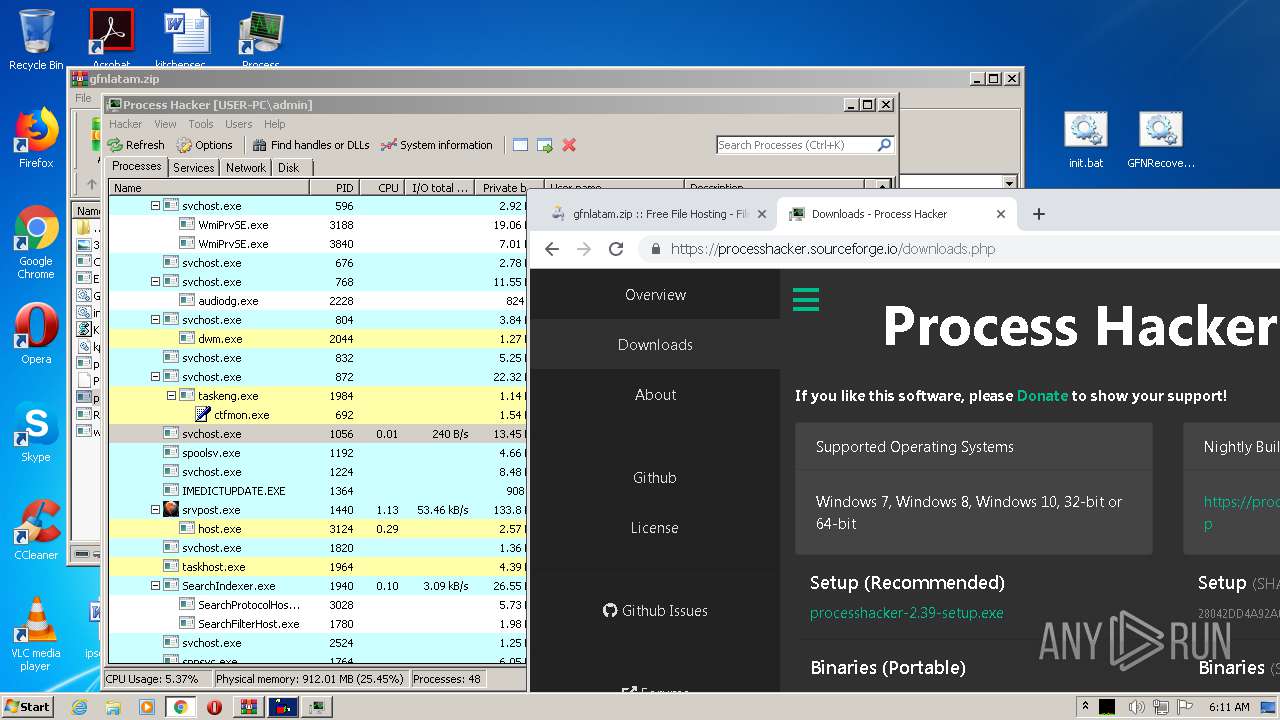
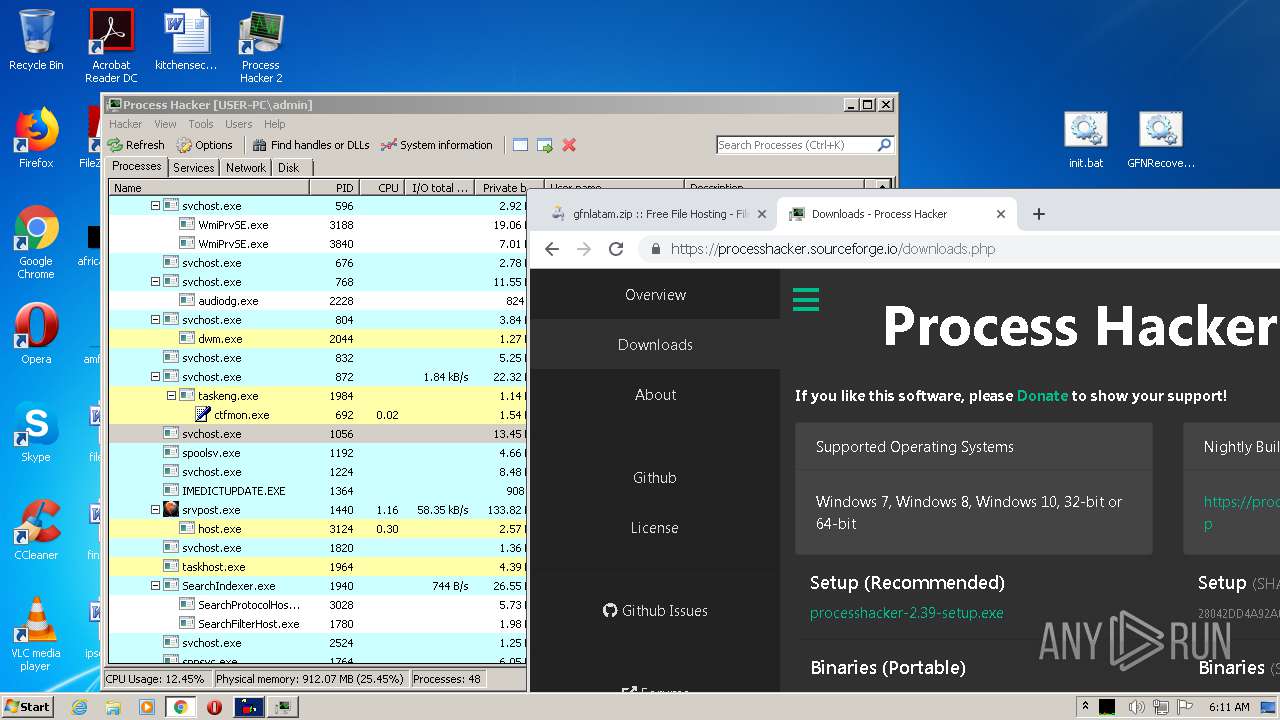
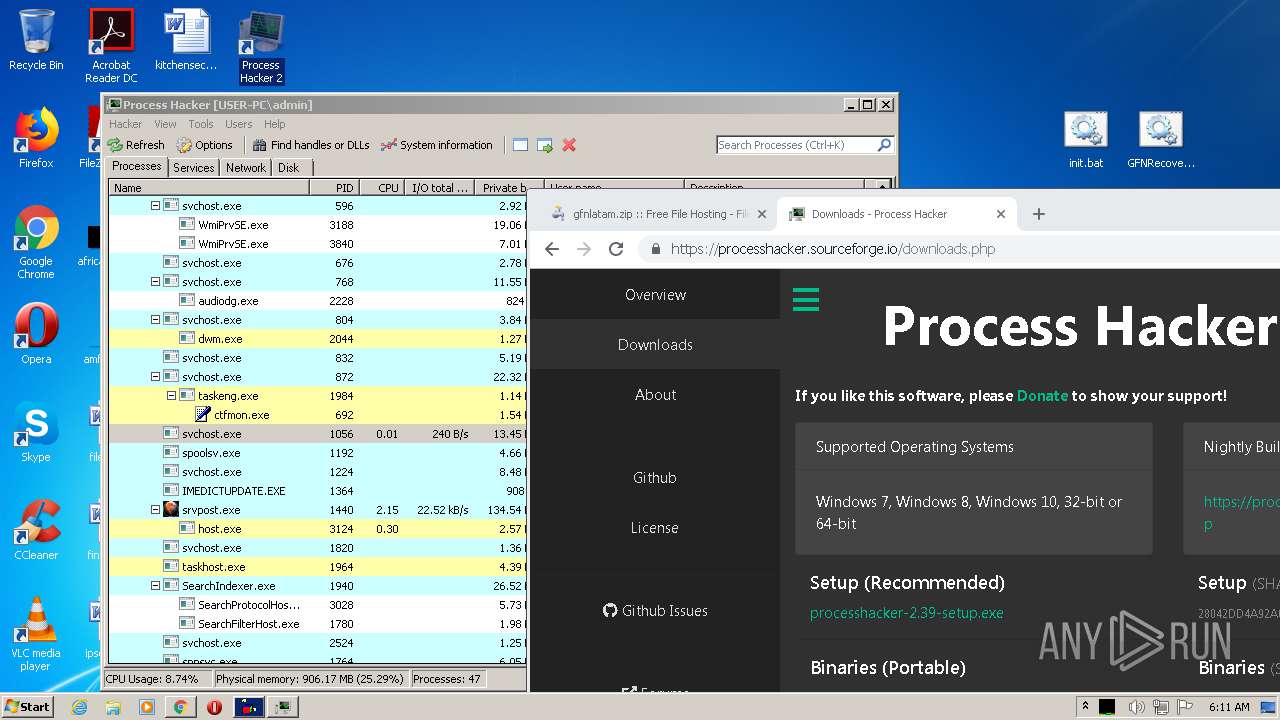
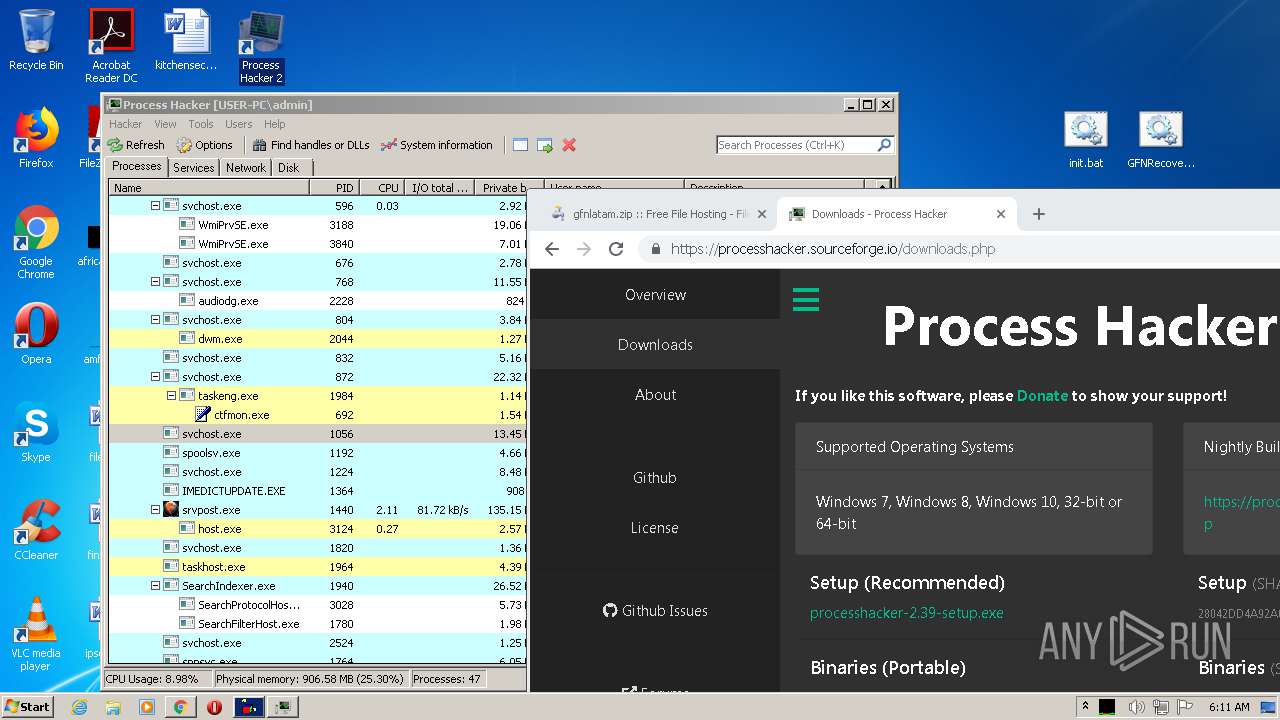
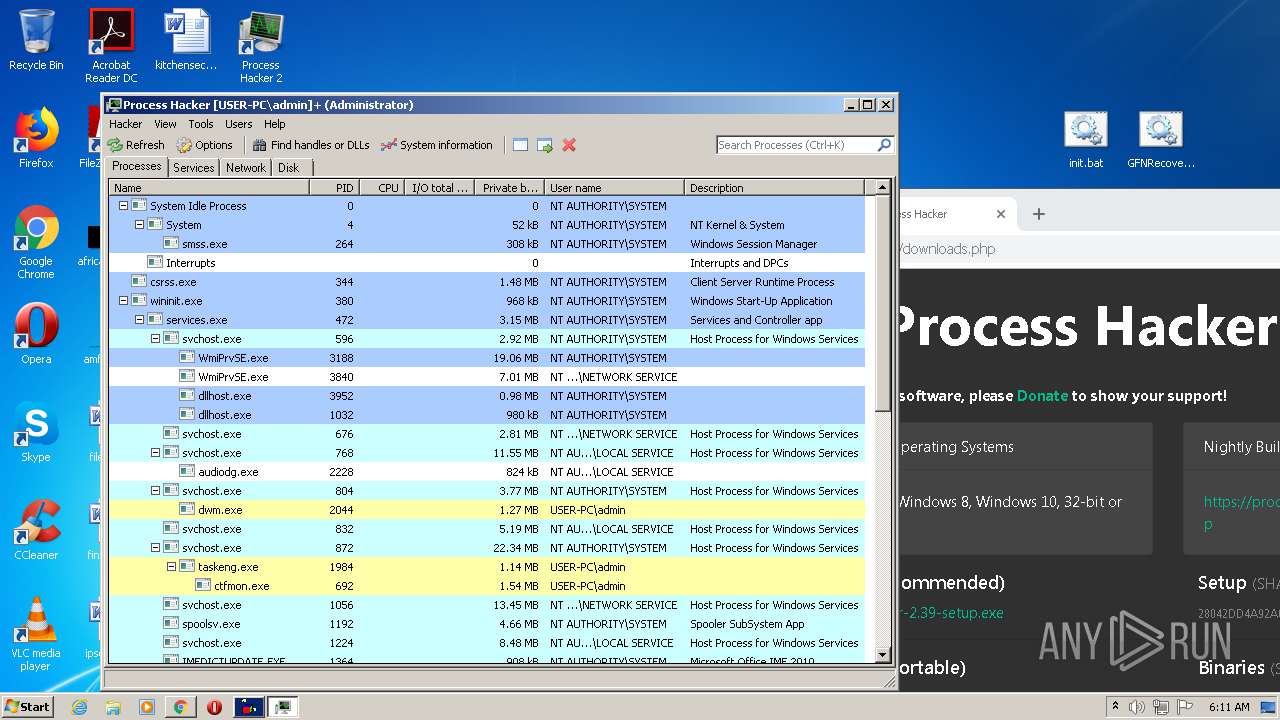
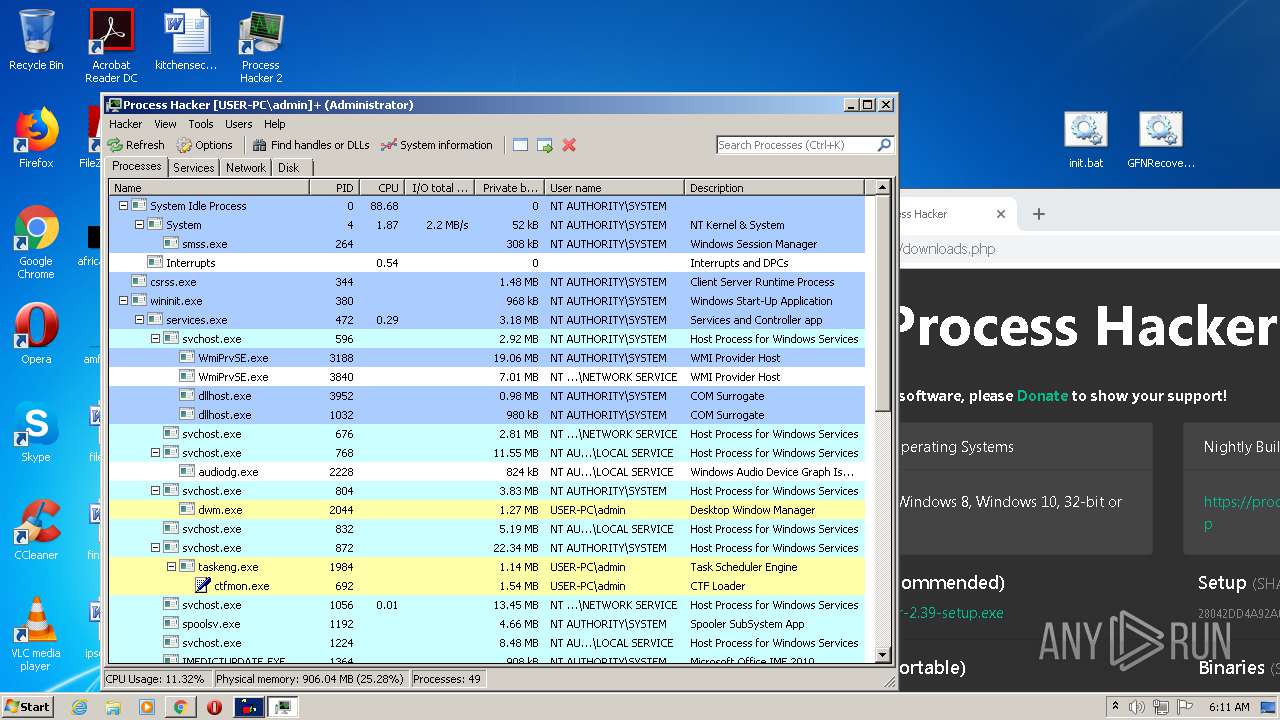
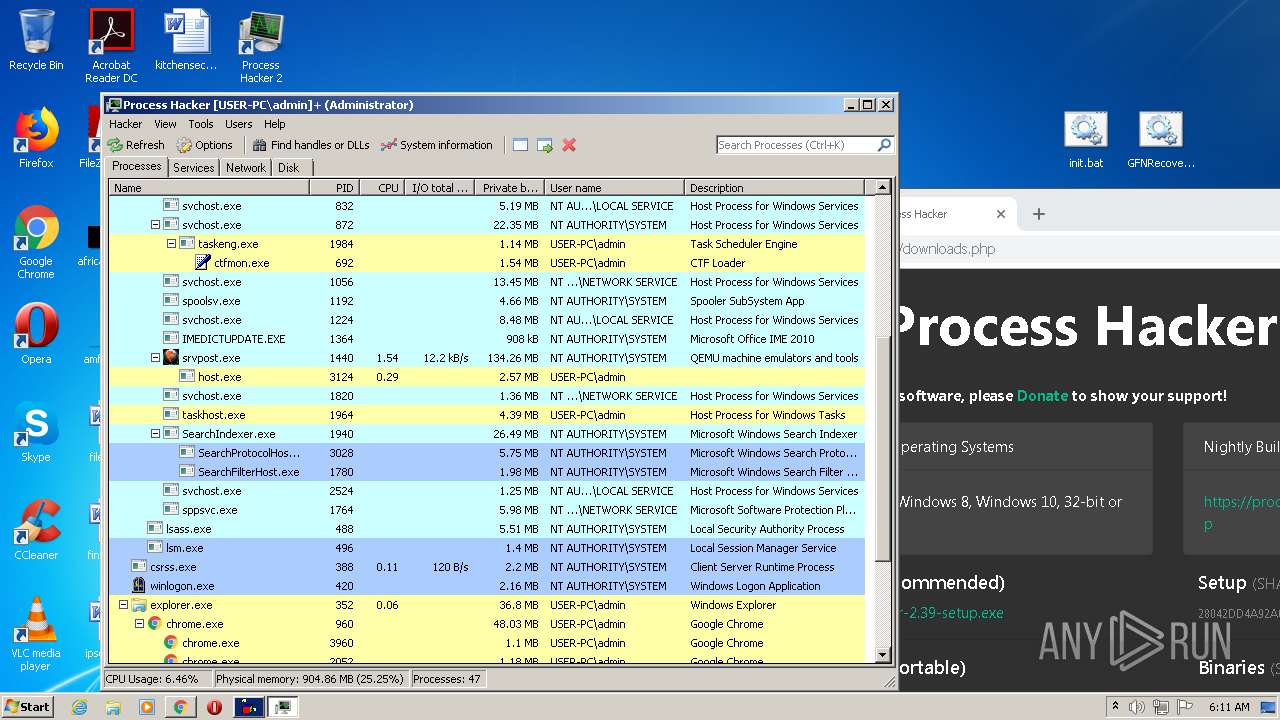
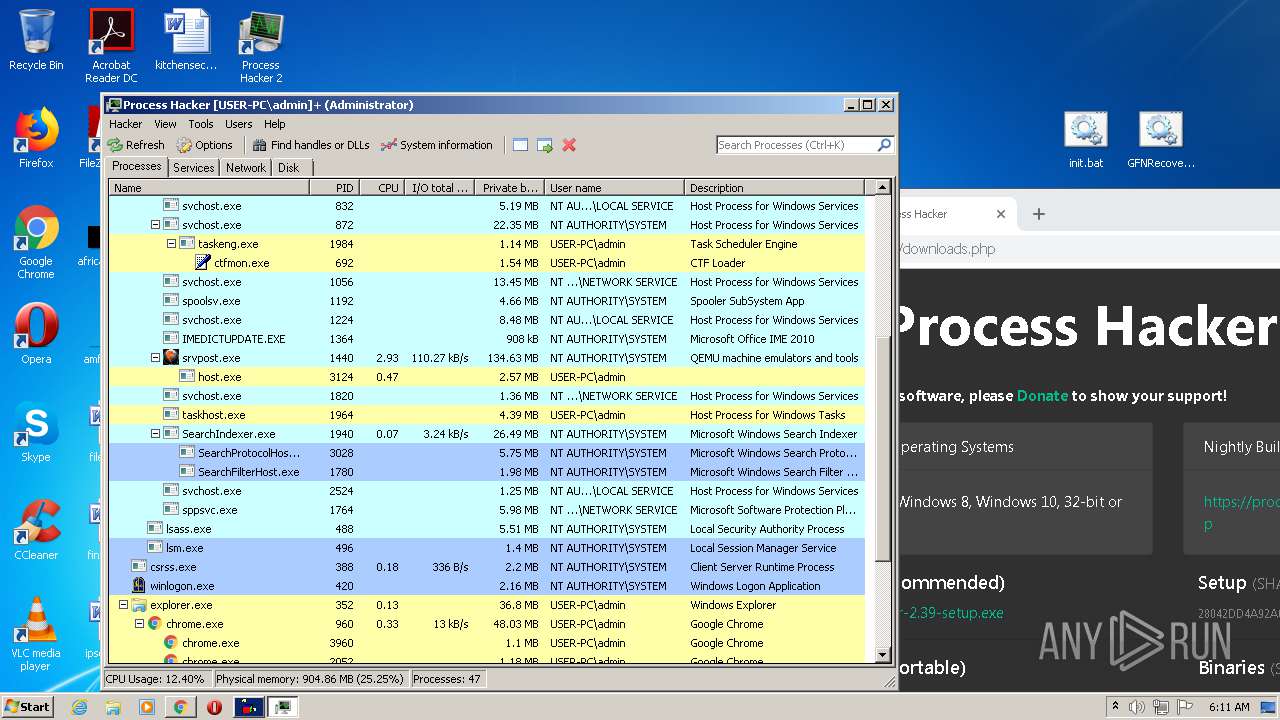
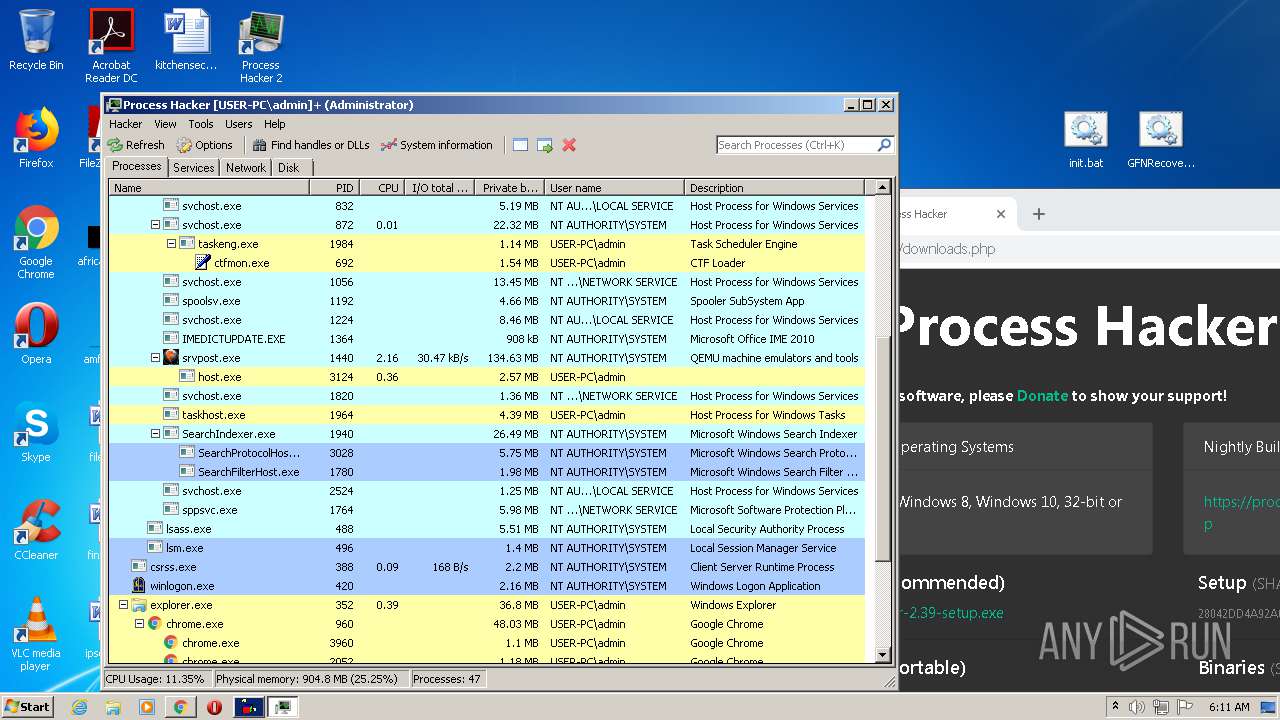
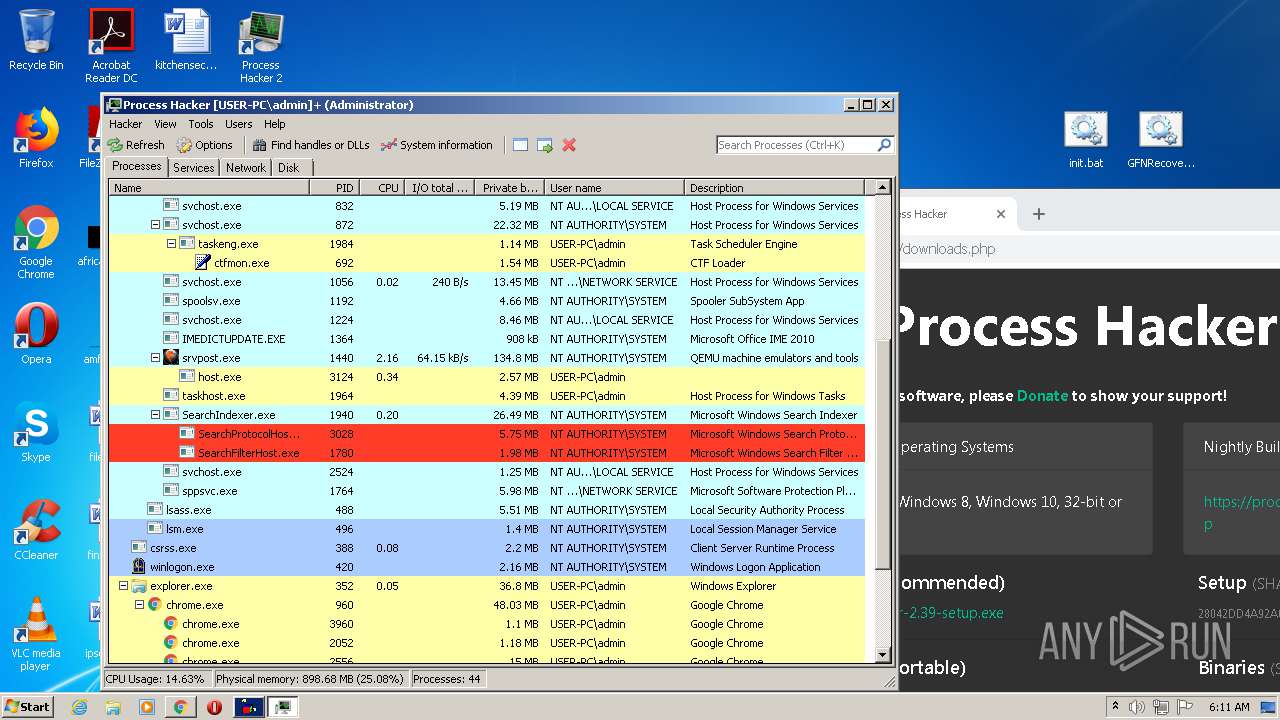
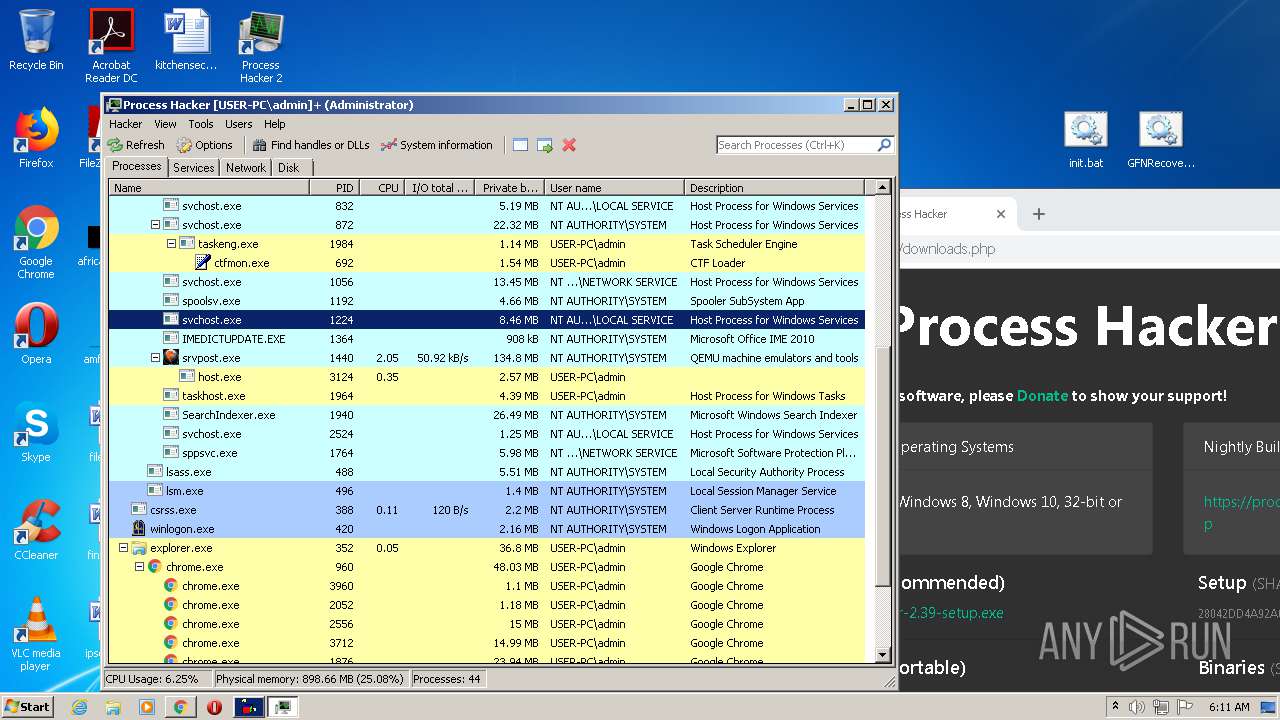
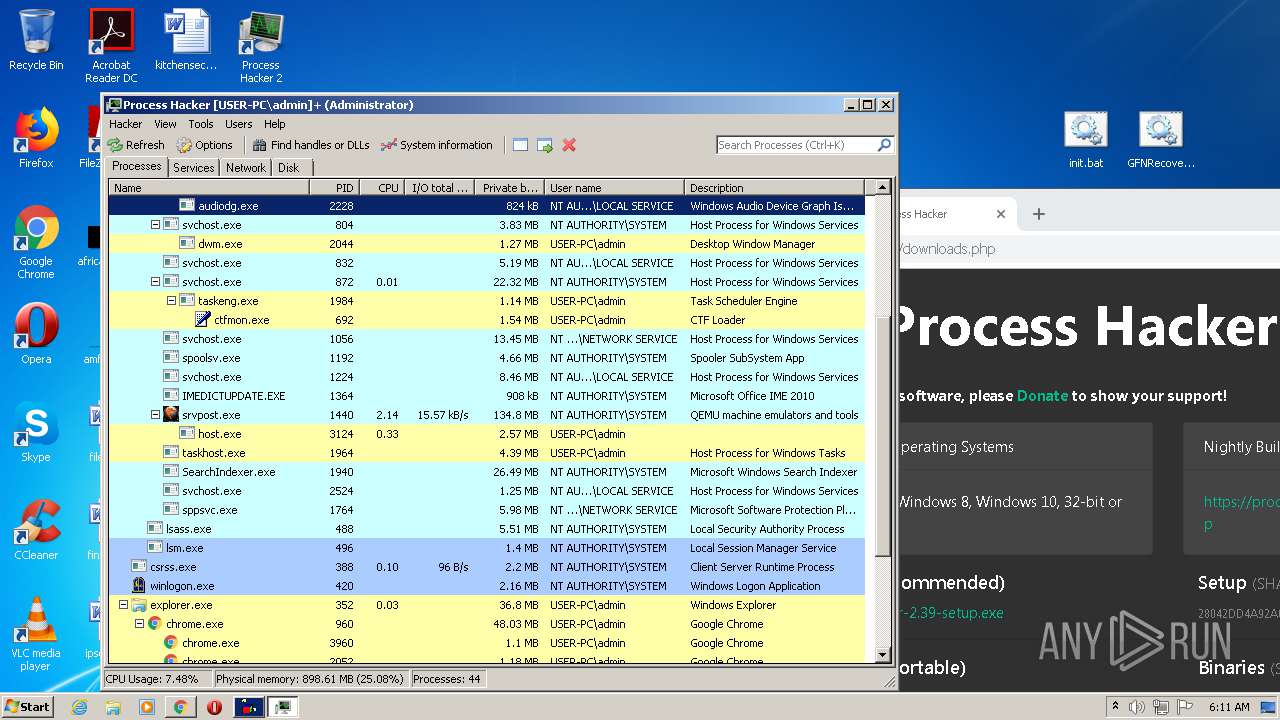
Total processes
174
Monitored processes
99
Malicious processes
13
Suspicious processes
3
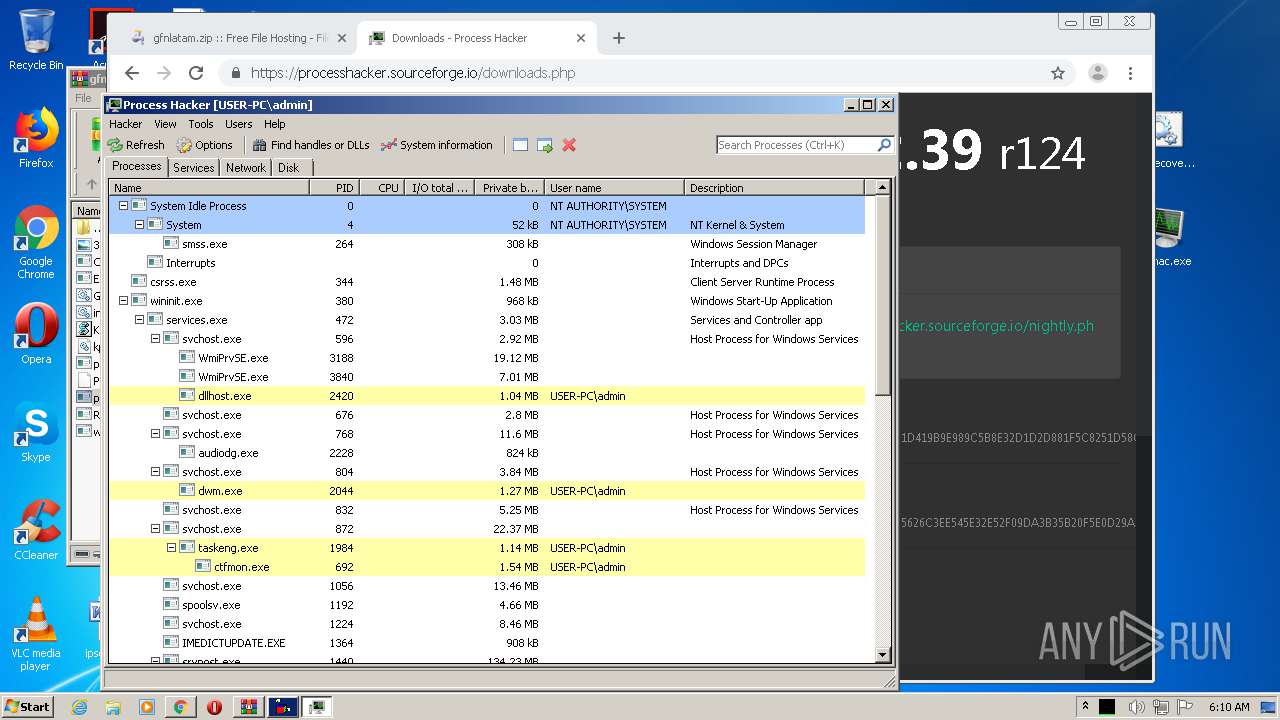
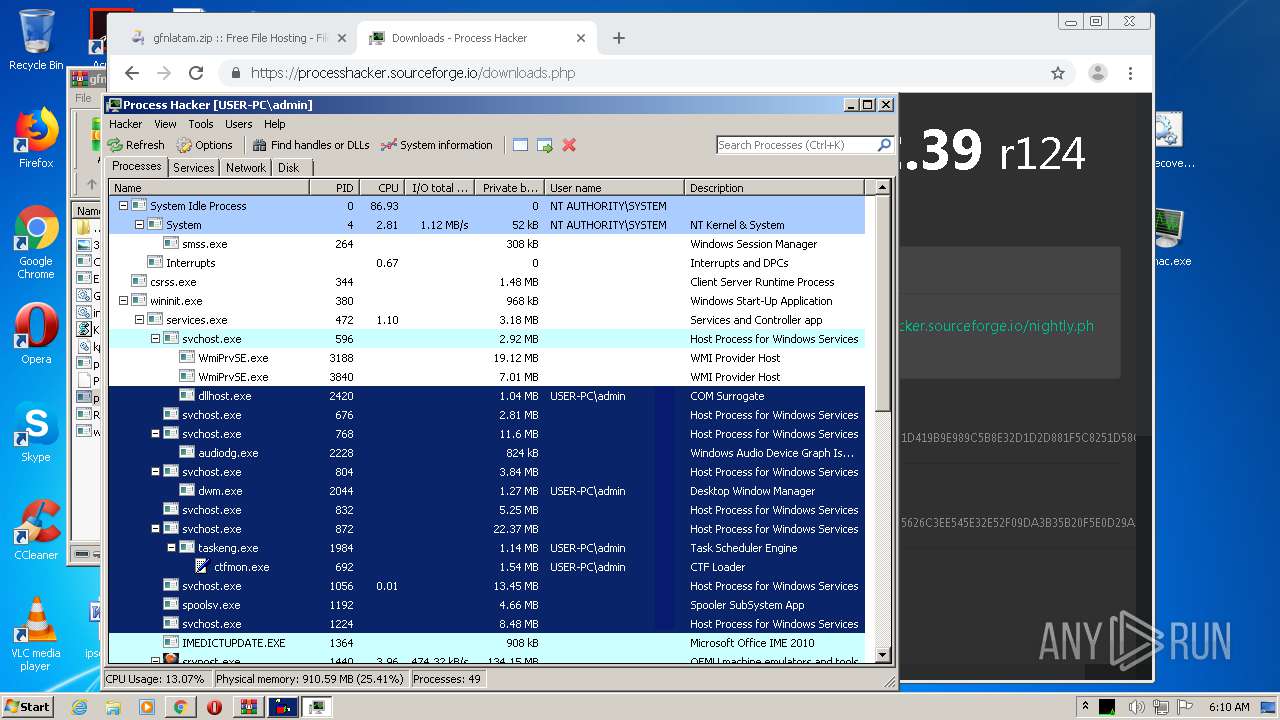
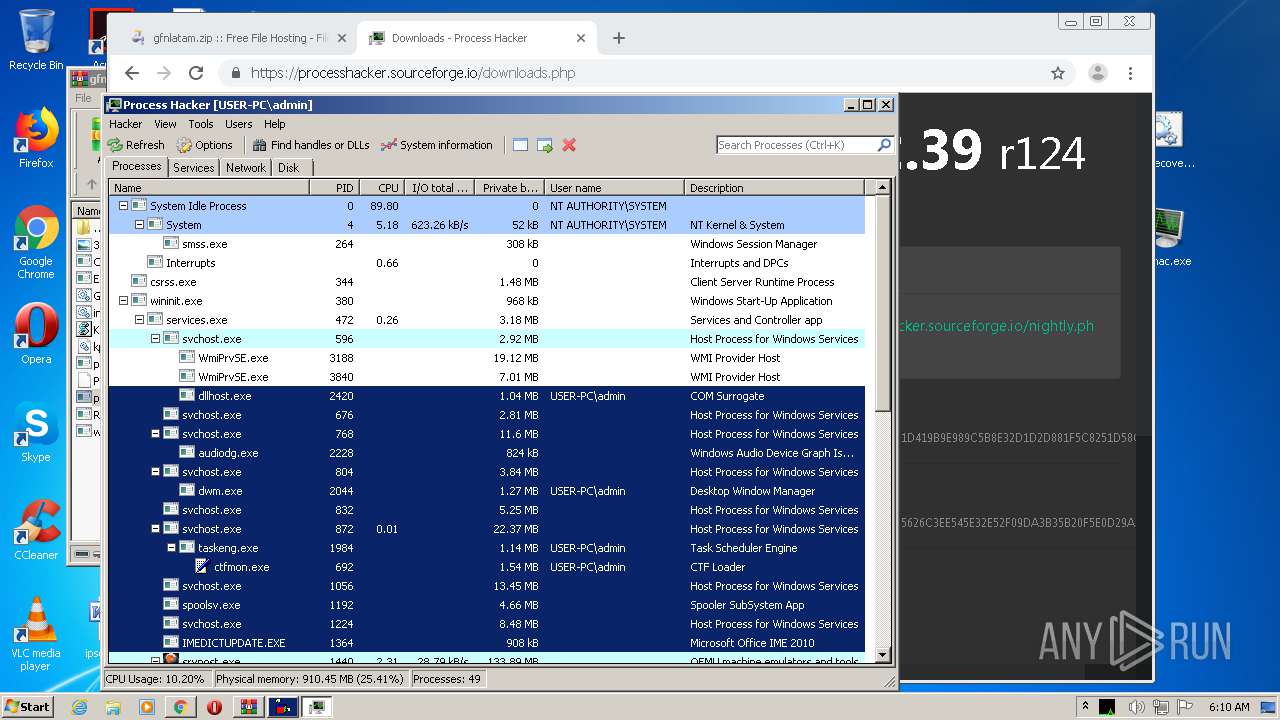
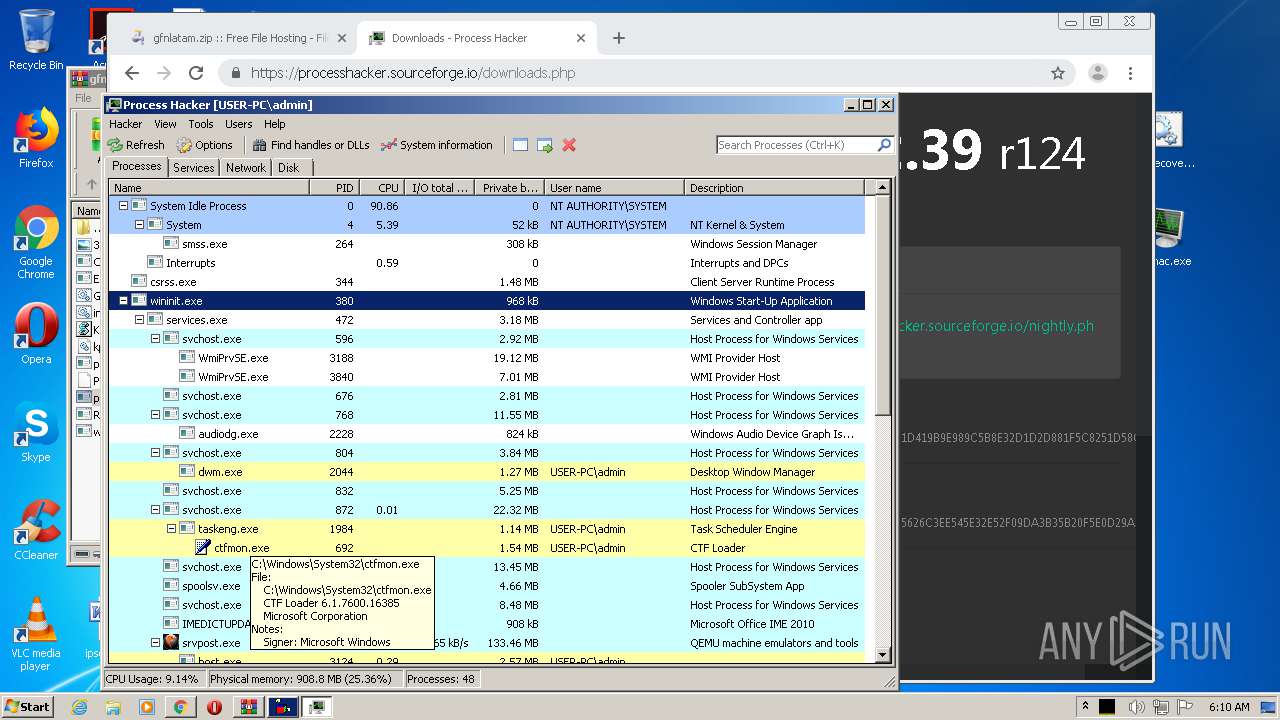
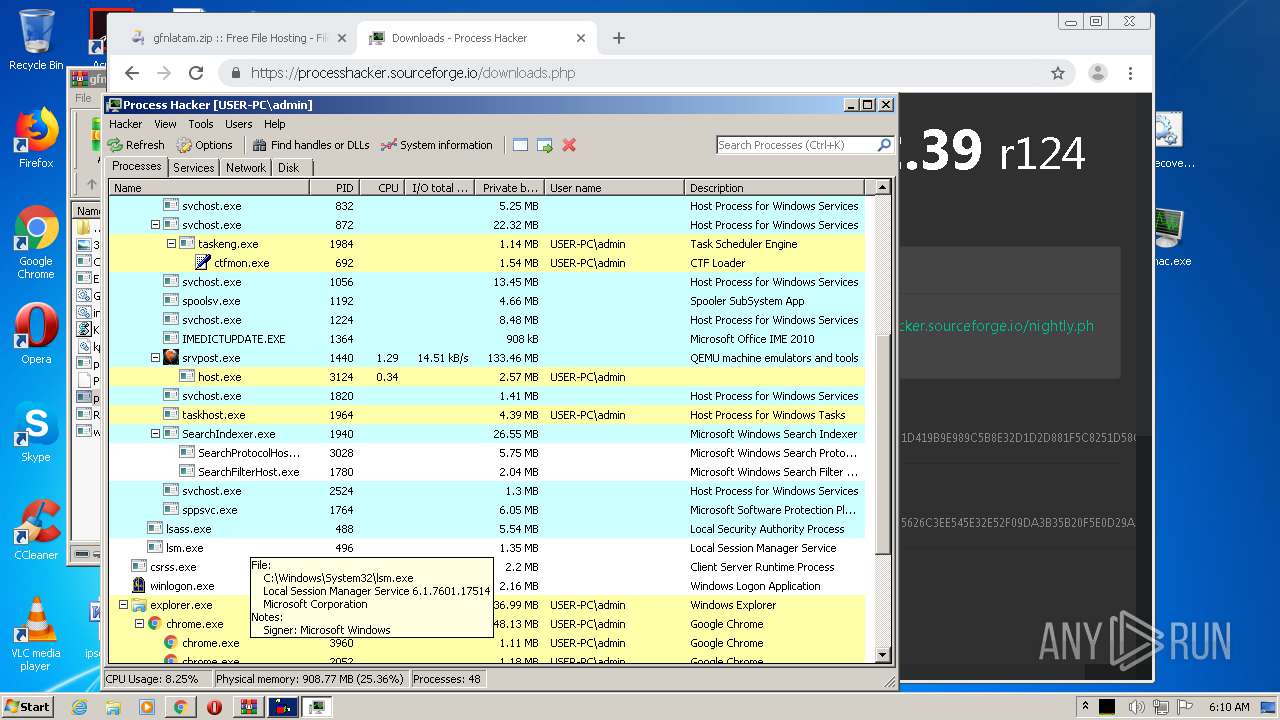
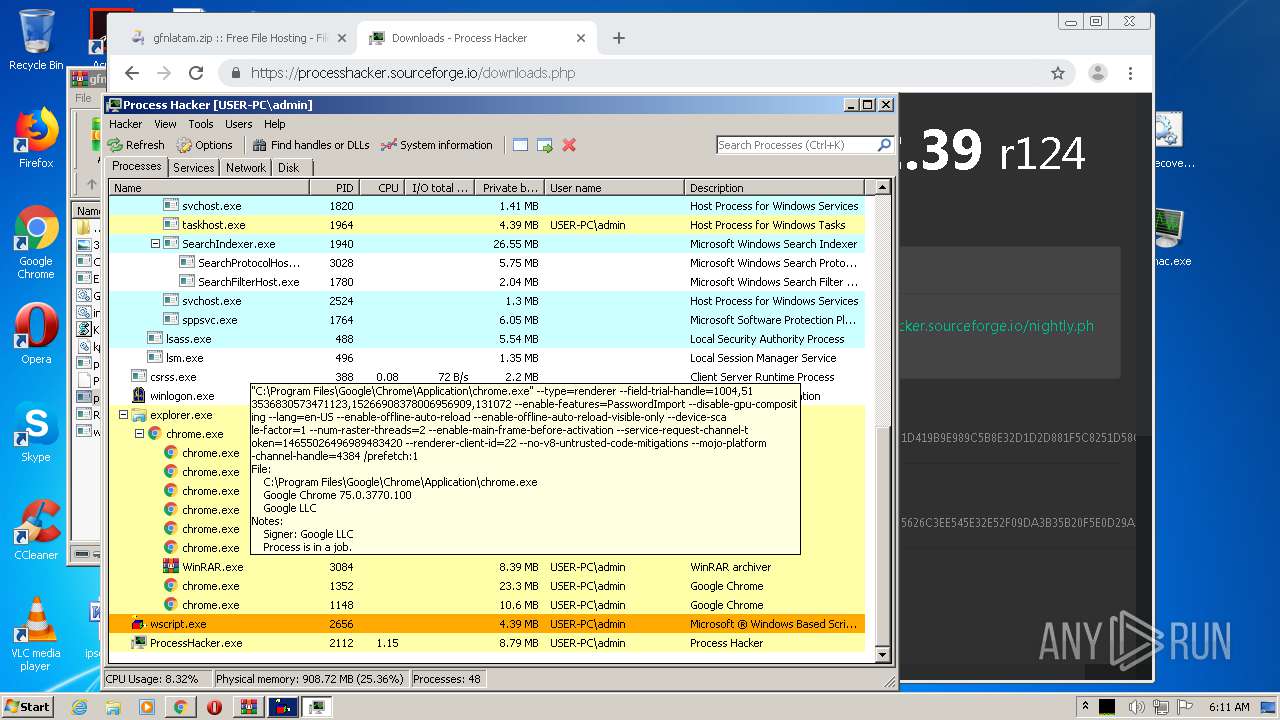
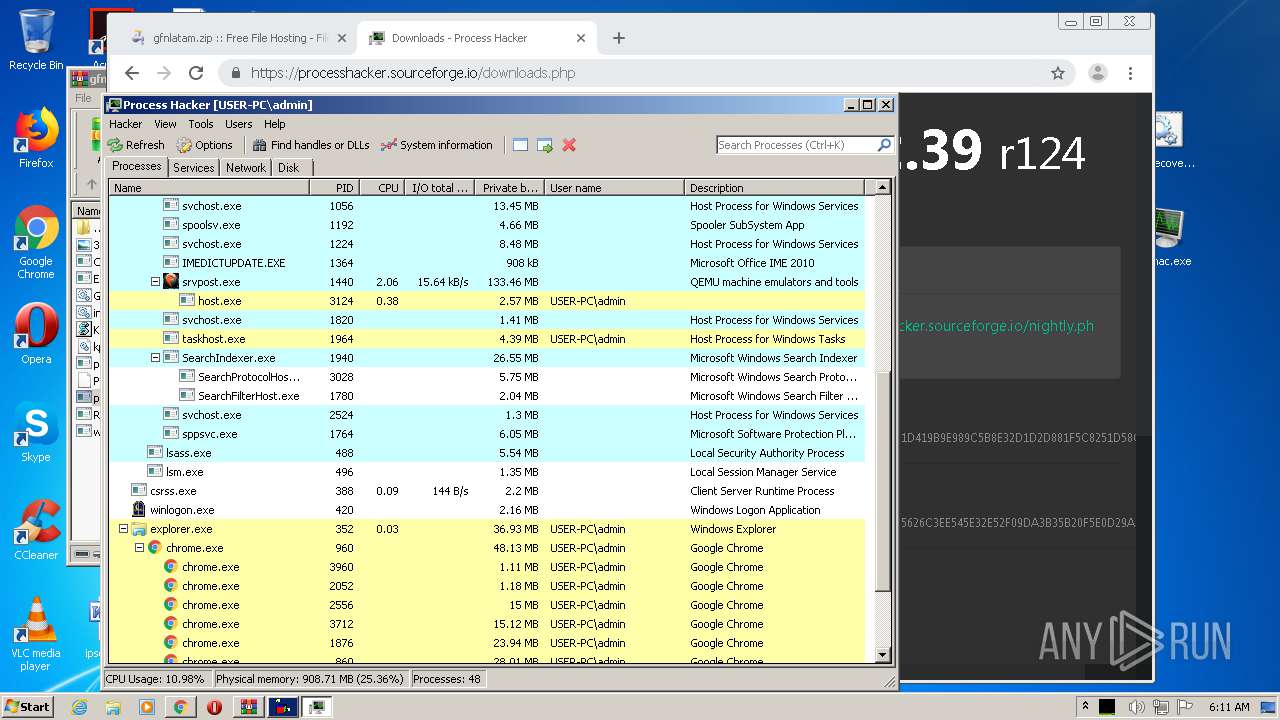
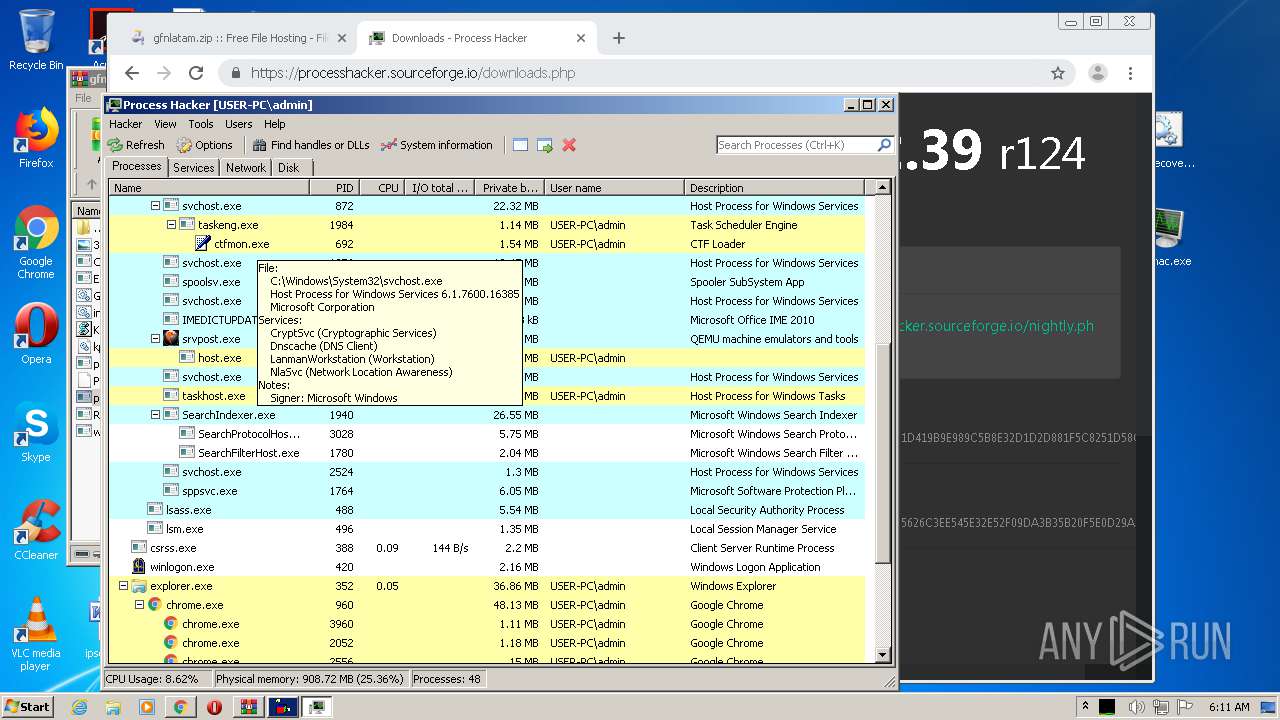
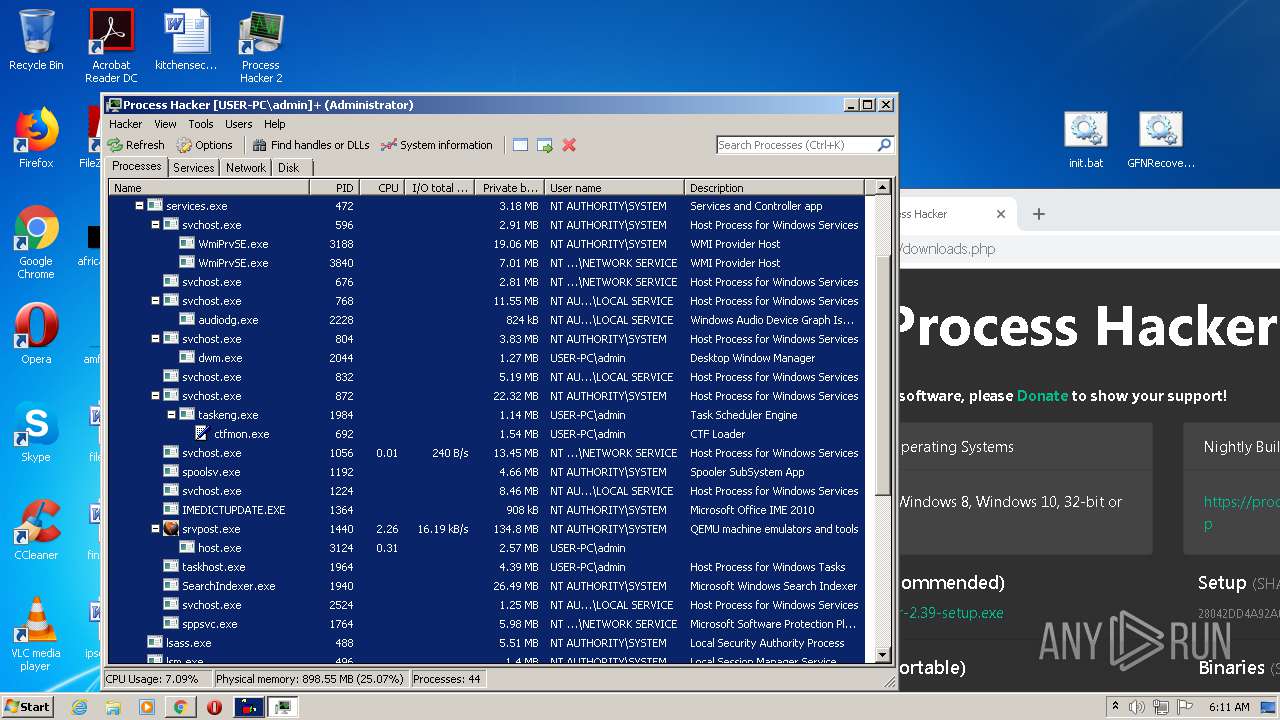
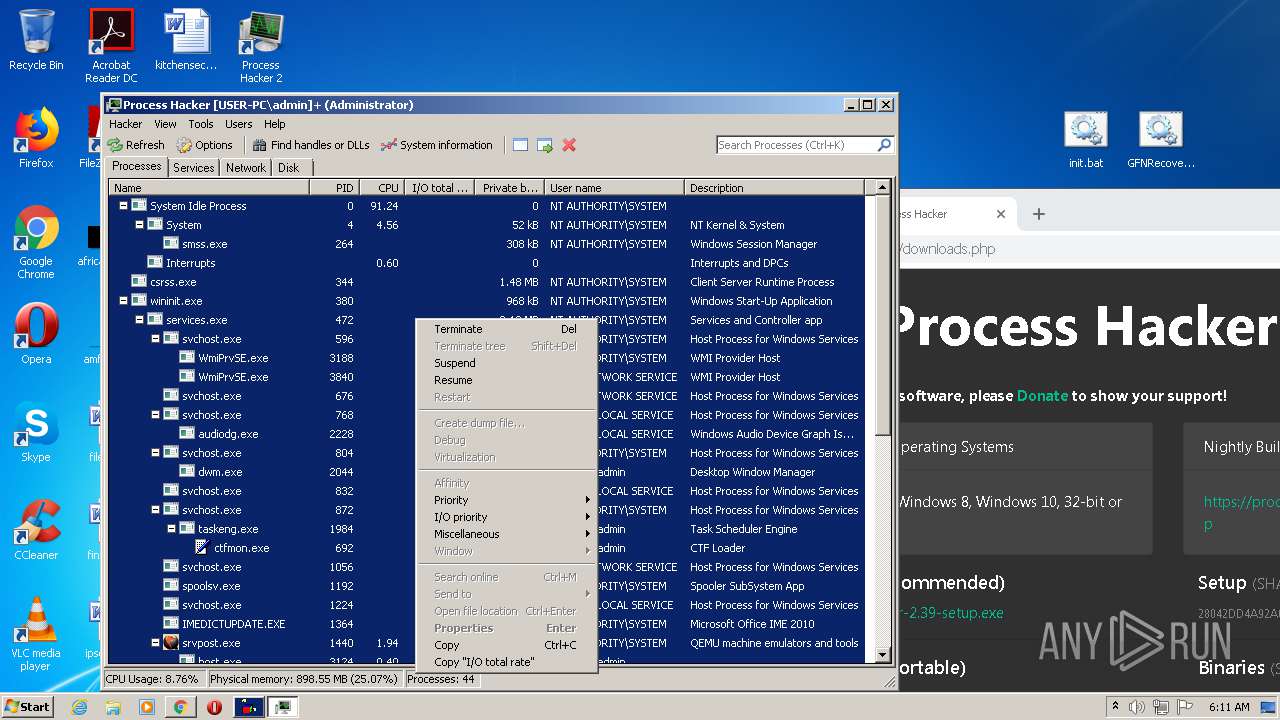
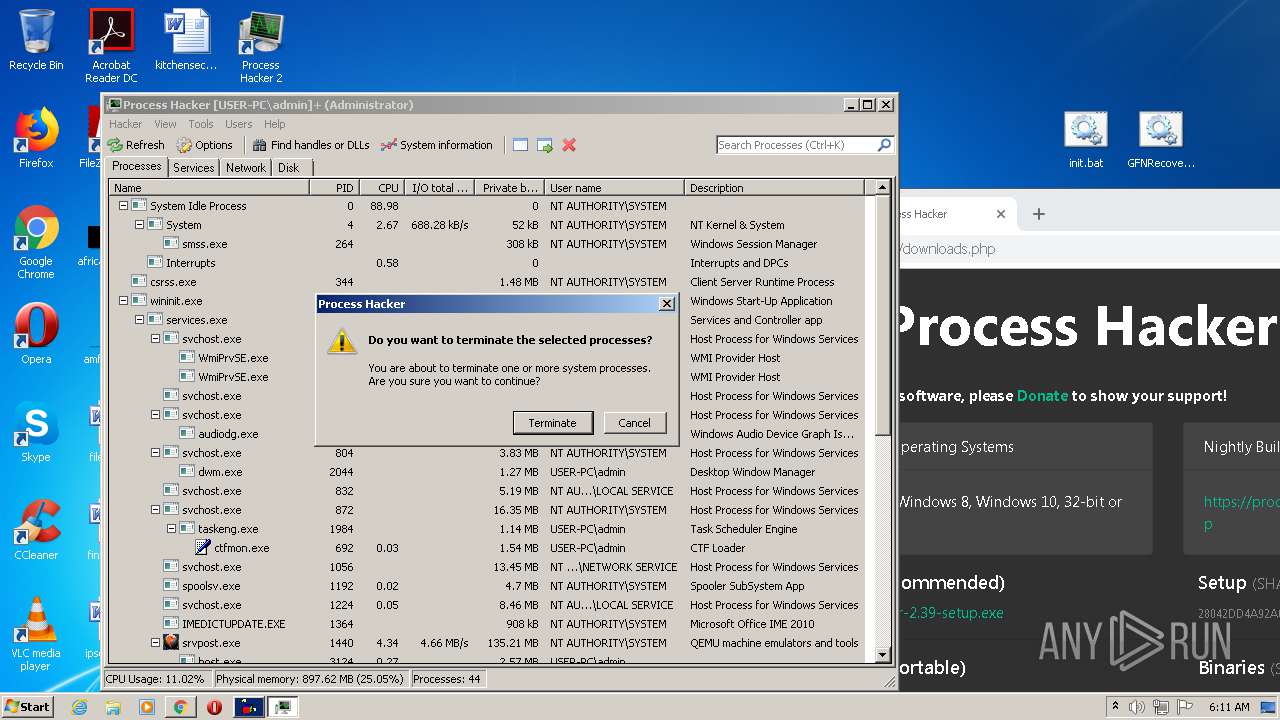
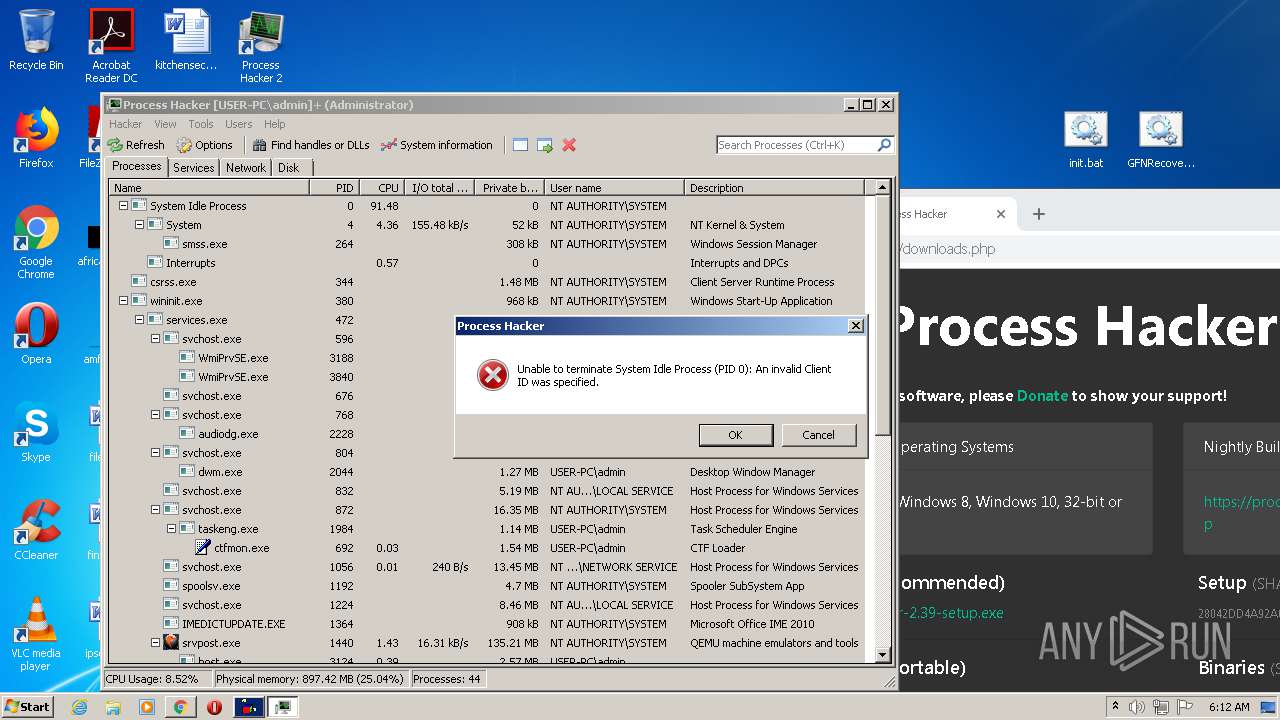
Behavior graph
Click at the process to see the details
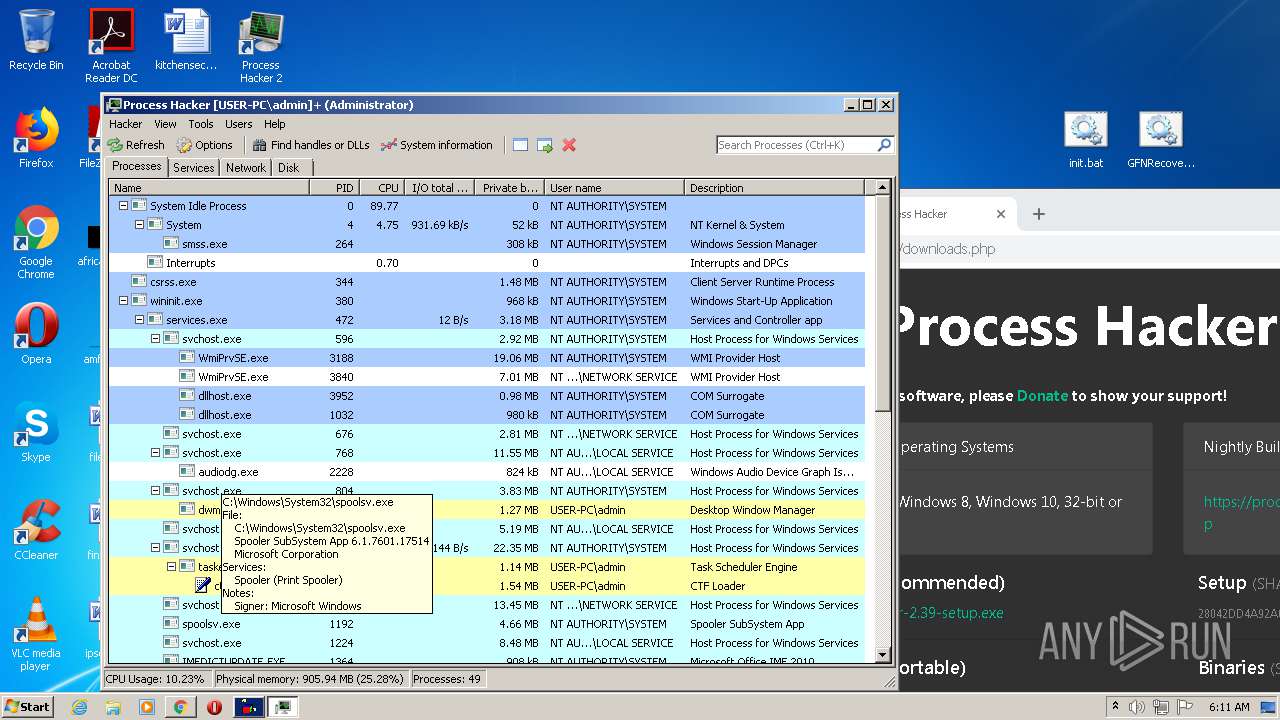
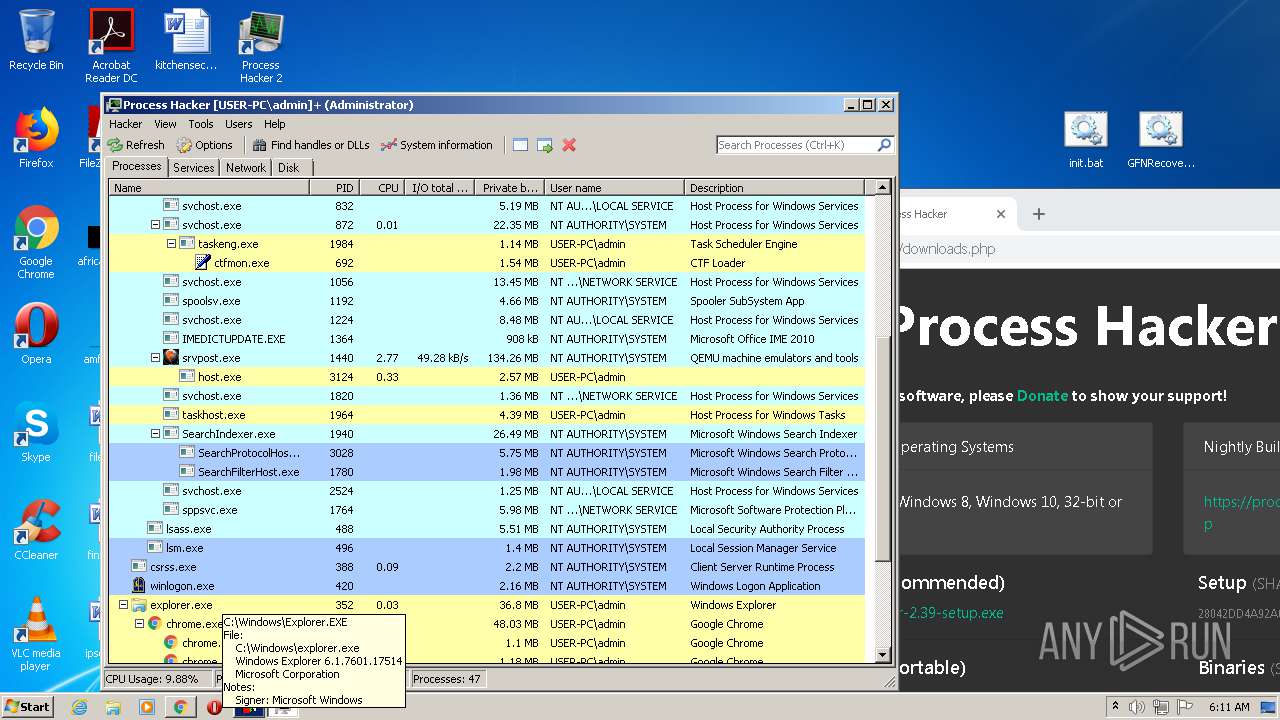
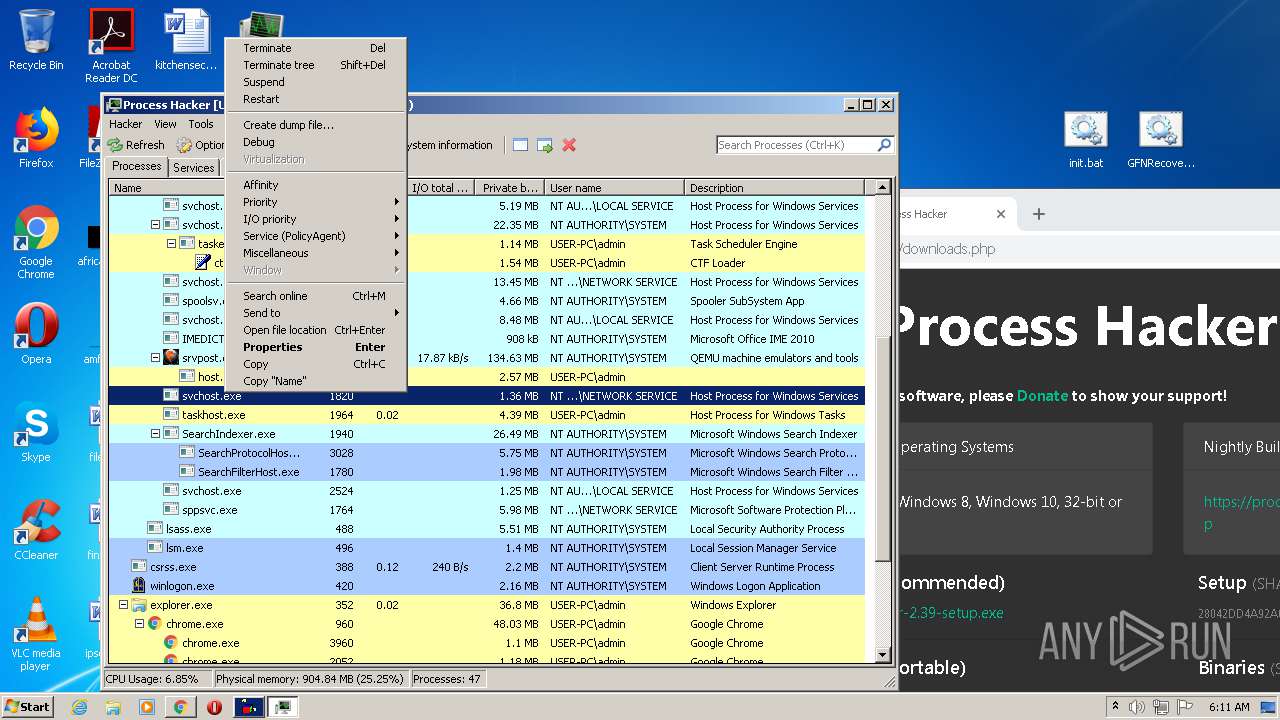
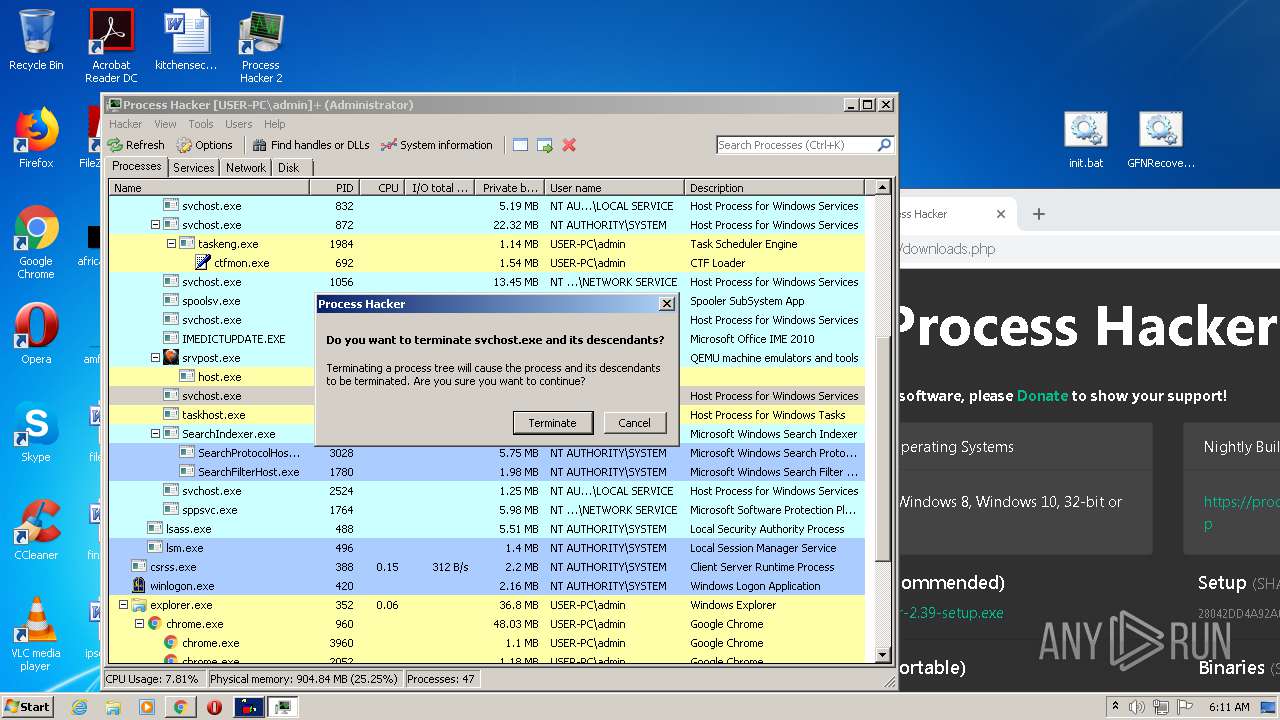
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
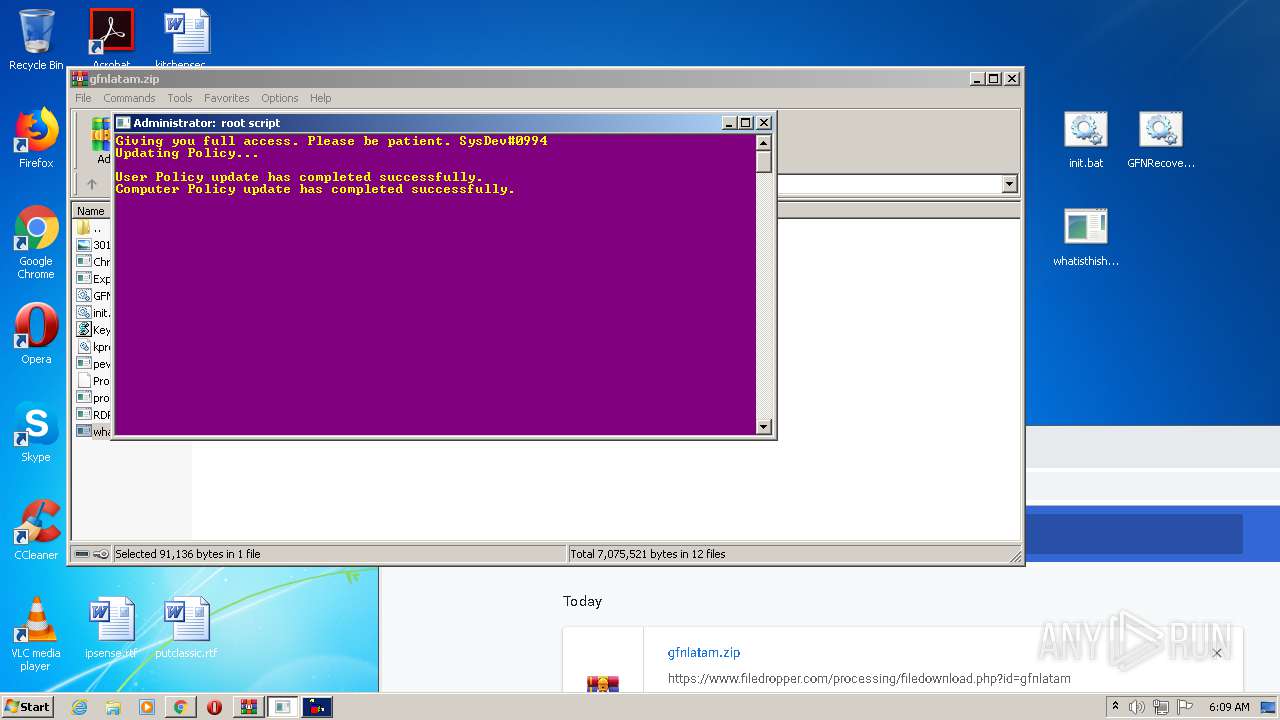
| 308 | gpupdate /force | C:\Windows\system32\gpupdate.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Group Policy Update Utility Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 312 | takeown /f c:\windows\system32\openwith.exe | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 492 | net user Administrator Geforce21!Latam | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
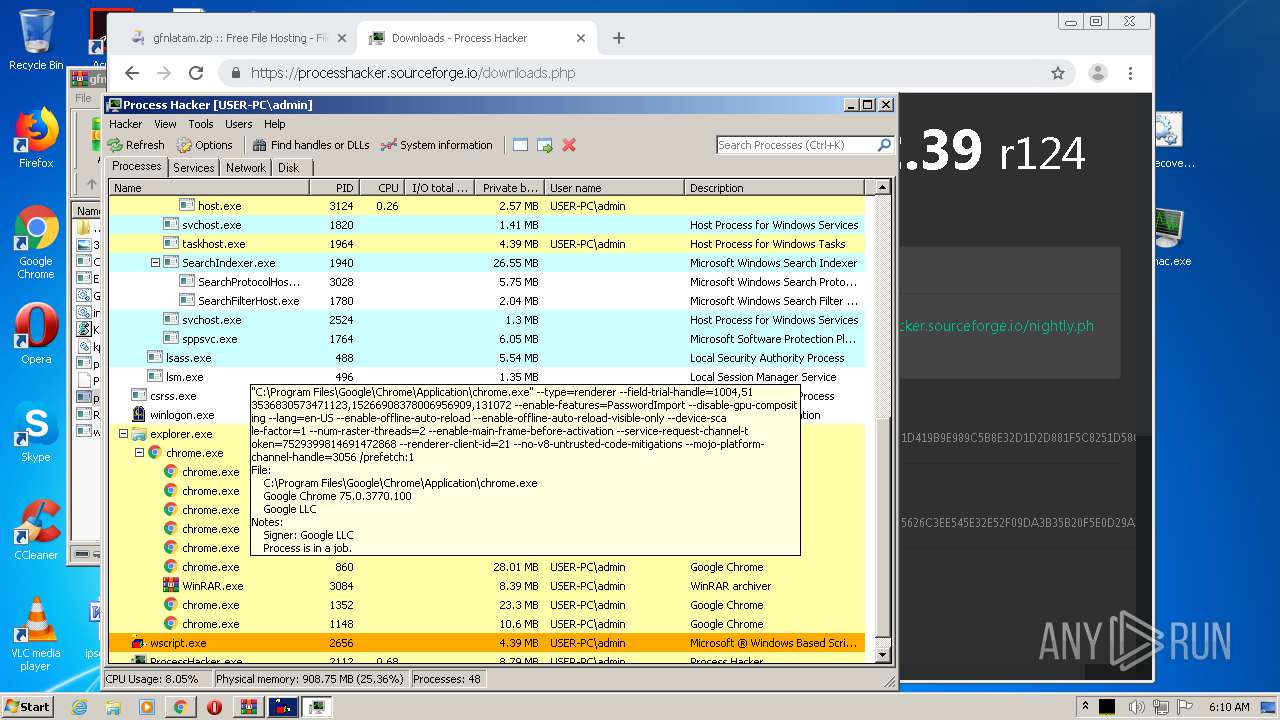
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,513536830573471123,15266908378006956909,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15253073780007500941 --mojo-platform-channel-handle=5420 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,513536830573471123,15266908378006956909,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14655026496989483420 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4384 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | REG ADD "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon" /v Shell /t REG_SZ /d explorer.exe /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 924 | Icacls c:\windows\explorer.exe /grant xen:RX | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 1332 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.mediafire.com/file/i0hl83myi4z7sdy/ssfn_gfnRUN2.bat/file" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Users\admin\Downloads\processhacker-2.39-setup.exe" /SPAWNWND=$1601BA /NOTIFYWND=$1002A4 | C:\Users\admin\Downloads\processhacker-2.39-setup.exe | processhacker-2.39-setup.tmp | ||||||||||||
User: admin Company: wj32 Integrity Level: HIGH Description: Process Hacker Setup Exit code: 0 Version: 2.39 (r124) Modules
| |||||||||||||||
| 1072 | taskkill /f /im gfndesktop.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 424
Read events
3 175
Write events
235
Delete events
14
Modification events
| (PID) Process: | (960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2052) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 960-13245916028869250 |
Value: 259 | |||
| (PID) Process: | (960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (960) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
35
Suspicious files
158
Text files
152
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F74127D-3C0.pma | — | |
MD5:— | SHA256:— | |||
| 960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\39602de1-5510-41ab-ad69-f26c1142c843.tmp | — | |
MD5:— | SHA256:— | |||
| 960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3bbf97.TMP | text | |
MD5:— | SHA256:— | |||
| 960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
137
DNS requests
93
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3712 | chrome.exe | GET | 200 | 104.17.166.186:80 | http://6.adsco.re/ | US | — | — | whitelisted |
3712 | chrome.exe | GET | — | 162.252.214.5:80 | http://adsco.re/p | US | — | — | whitelisted |
3712 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/file/i0hl83myi4z7sdy/ssfn_gfnRUN2.bat/file | US | html | 80.7 Kb | shared |
3712 | chrome.exe | GET | 200 | 216.58.207.46:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 798 b | whitelisted |
3712 | chrome.exe | GET | 200 | 104.17.167.186:80 | http://c.adsco.re/ | US | html | 12.7 Kb | whitelisted |
3712 | chrome.exe | POST | — | 185.33.221.11:80 | http://ib.adnxs.com/ut/v3/prebid | unknown | — | — | whitelisted |
3712 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/images/icons/svg_light/icons_sprite.svg | US | image | 8.42 Kb | shared |
3712 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/js/prebid2.44.1.js | US | text | 52.9 Kb | shared |
3712 | chrome.exe | POST | 200 | 162.252.214.5:80 | http://adsco.re/p | US | text | 133 b | whitelisted |
3712 | chrome.exe | GET | 304 | 104.17.167.186:80 | http://c.adsco.re/ | US | compressed | 12.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3712 | chrome.exe | 185.64.189.112:443 | hbopenbid.pubmatic.com | PubMatic, Inc. | GB | unknown |
3712 | chrome.exe | 142.250.74.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3712 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3712 | chrome.exe | 216.58.212.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3712 | chrome.exe | 216.58.212.136:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3712 | chrome.exe | 216.58.207.34:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
3712 | chrome.exe | 216.58.207.46:443 | fundingchoicesmessages.google.com | Google Inc. | US | whitelisted |
3712 | chrome.exe | 172.217.18.106:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3712 | chrome.exe | 104.17.167.186:443 | c.adsco.re | Cloudflare Inc | US | shared |
3712 | chrome.exe | 104.19.214.37:443 | cdn.otnolatrnup.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
c.aaxads.com |
| whitelisted |
static.mediafire.com |
| shared |
translate.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3712 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3712 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3712 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |