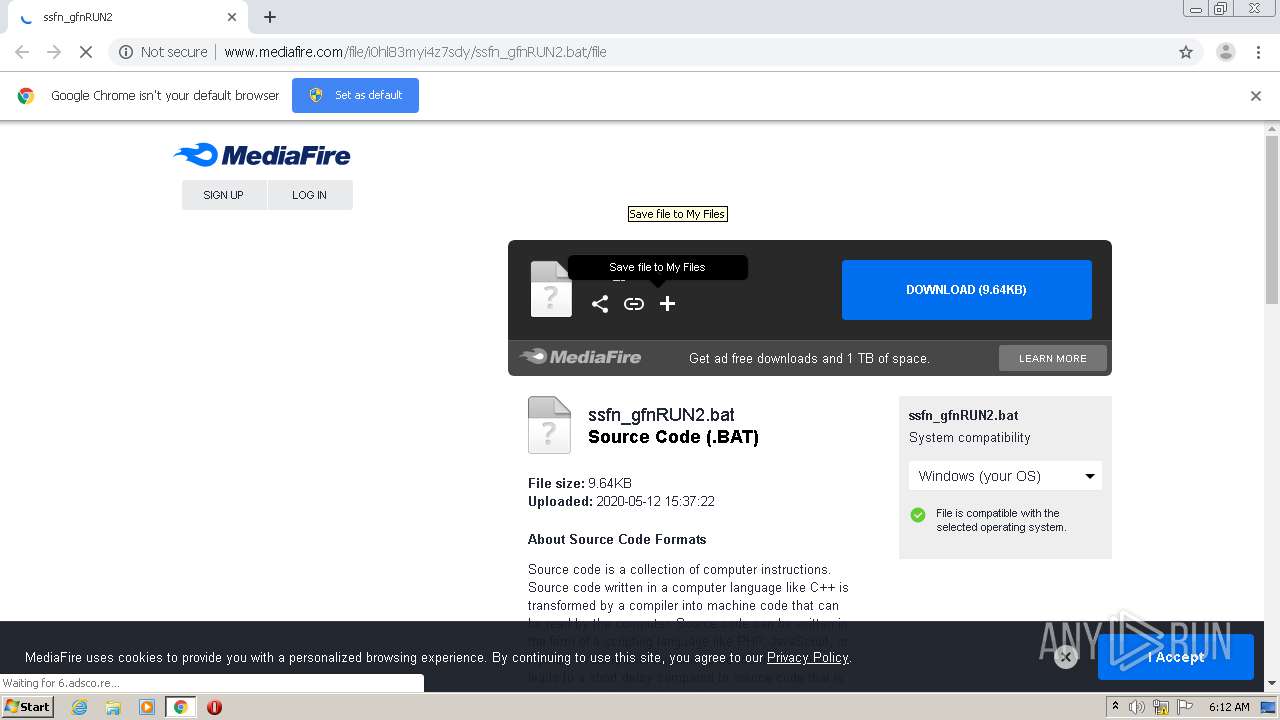
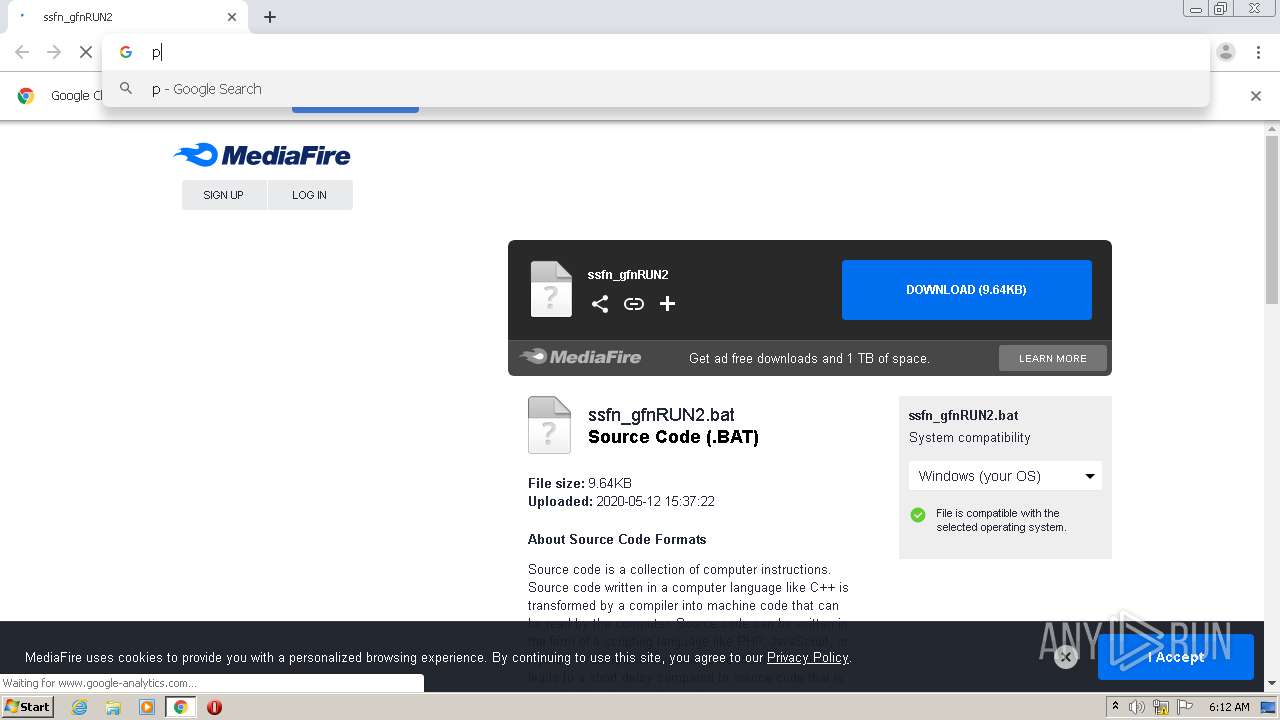
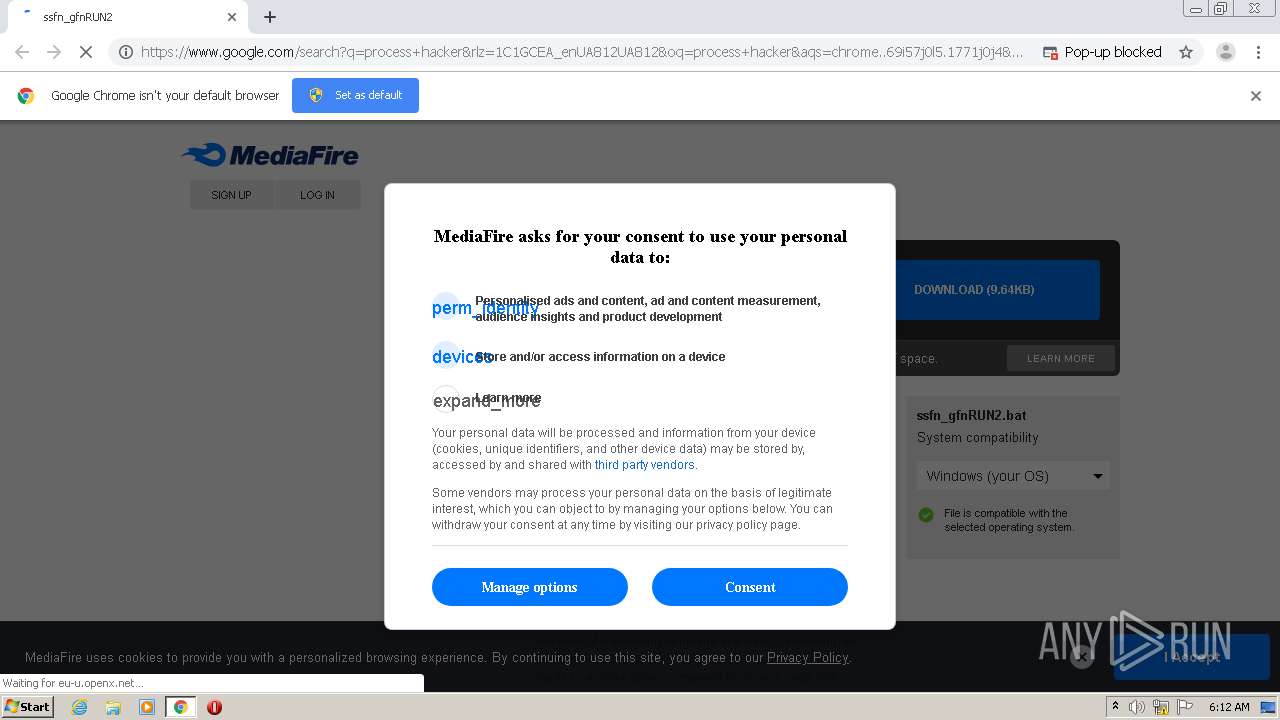
| URL: | http://www.mediafire.com/file/i0hl83myi4z7sdy/ssfn_gfnRUN2.bat/file |
| Full analysis: | https://app.any.run/tasks/1ed82a7d-55b0-4289-a8c9-f9769ed0650e |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 05:12:24 |
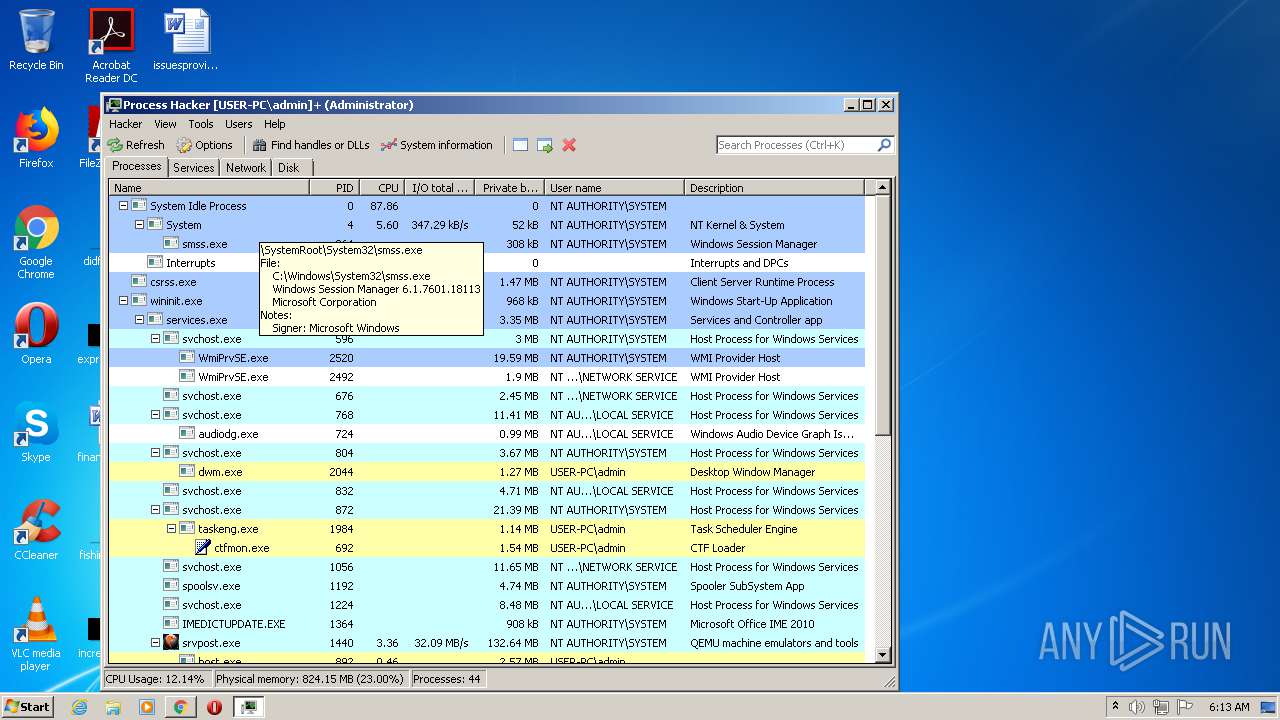
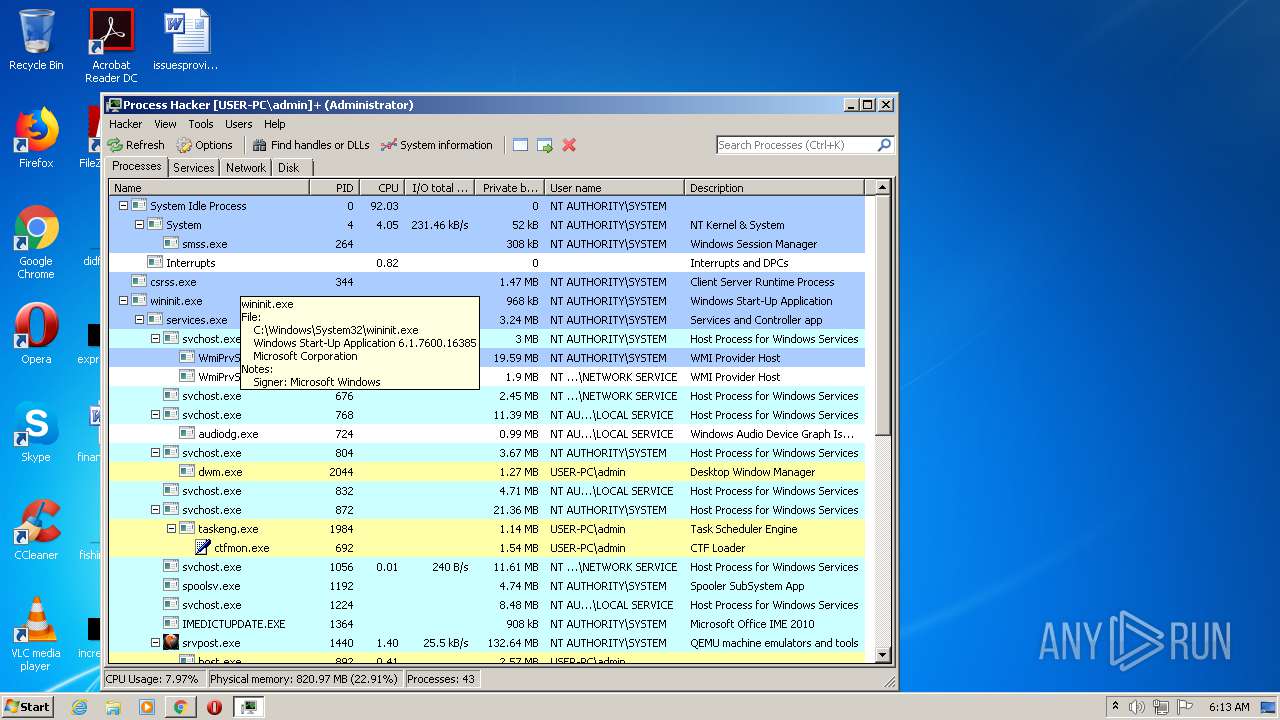
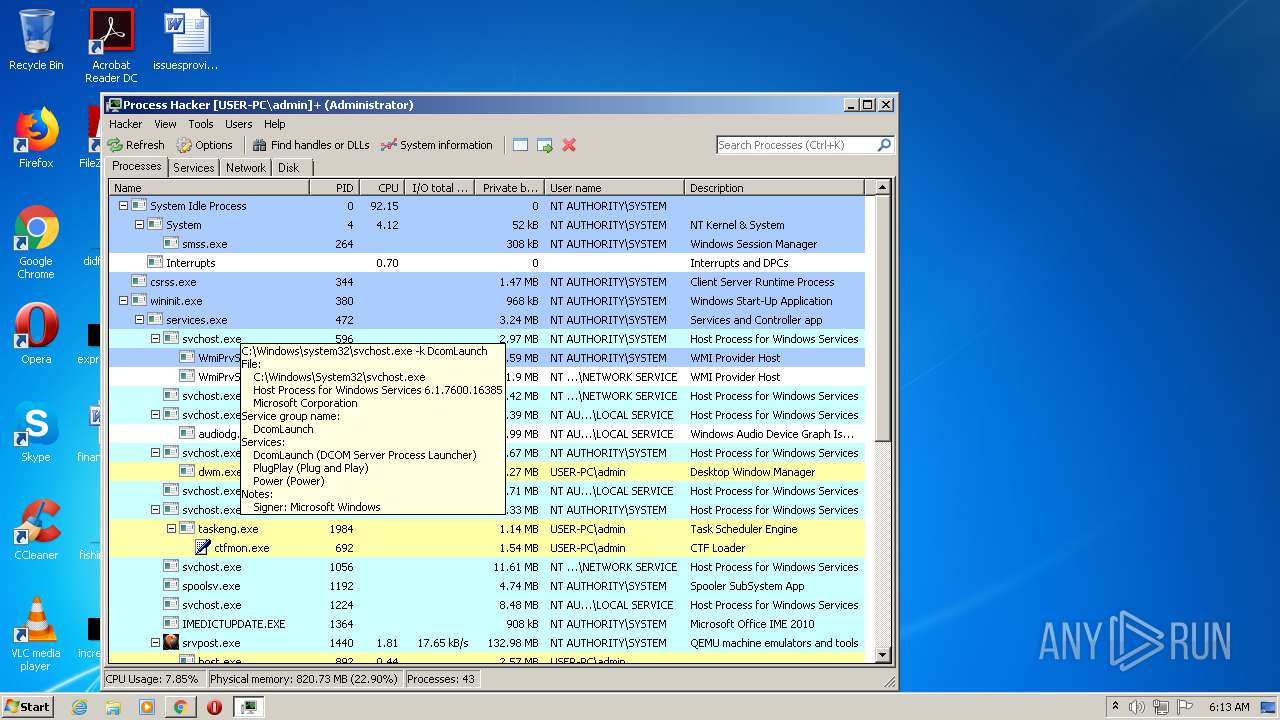
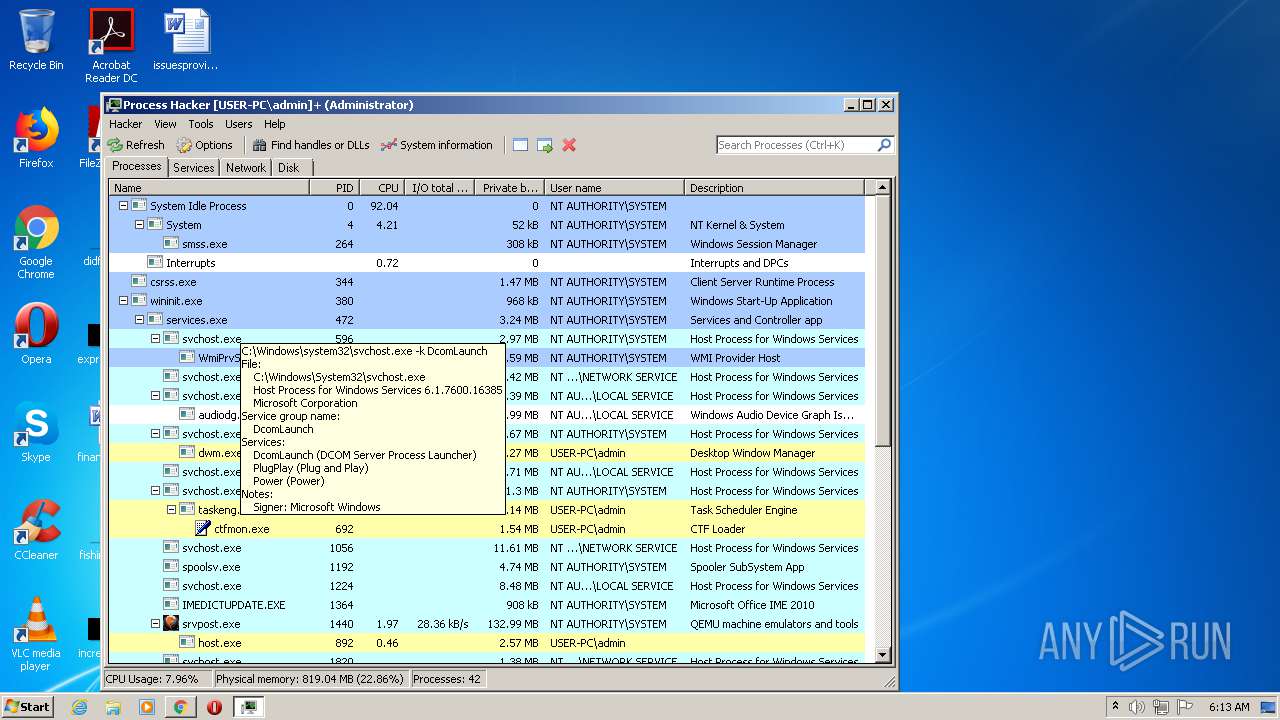
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 60683F38946F87D7D61AC1FE59C1F627 |
| SHA1: | BFD2F793DB30A4ACBCB26ED68875F4E8570060CF |
| SHA256: | 34B49627E7380C51883DCB1166A904FD90720948E1FC17BB40E462056C1A461D |
| SSDEEP: | 3:N1KJS4w3eGUoUIIcQfblqADwrbki9n:Cc4w3eGIy42xn |
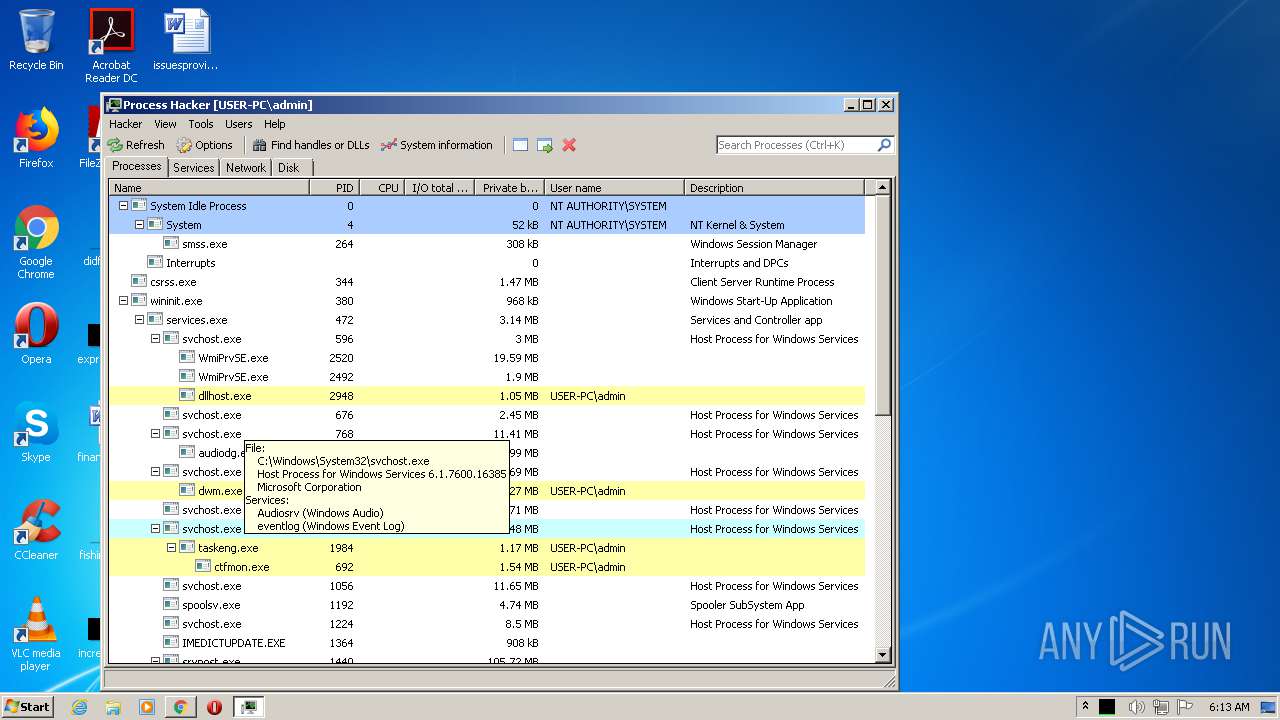
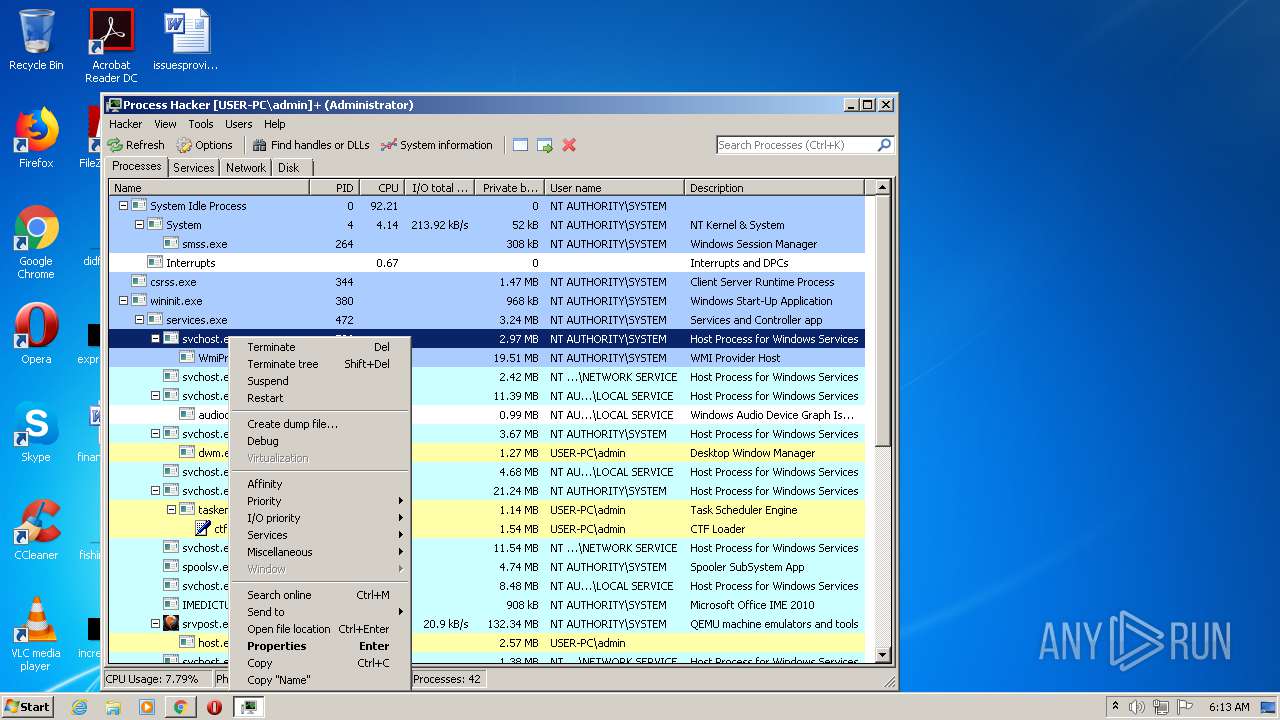
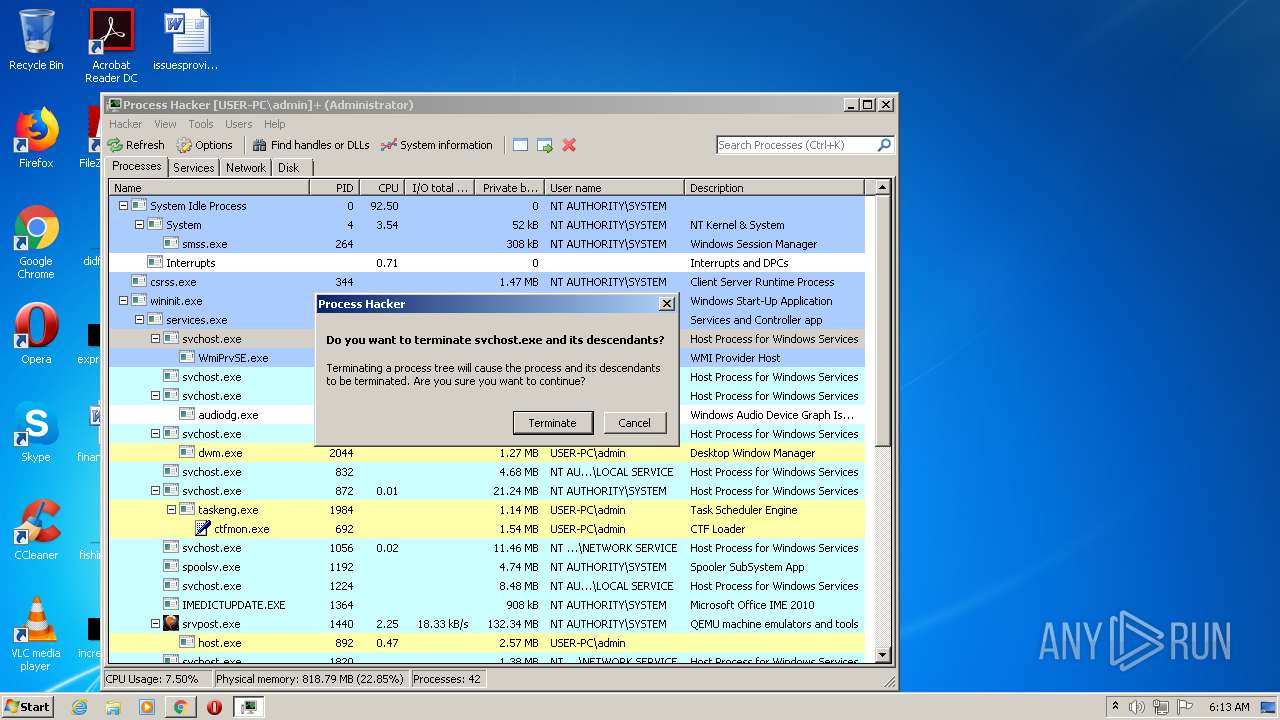
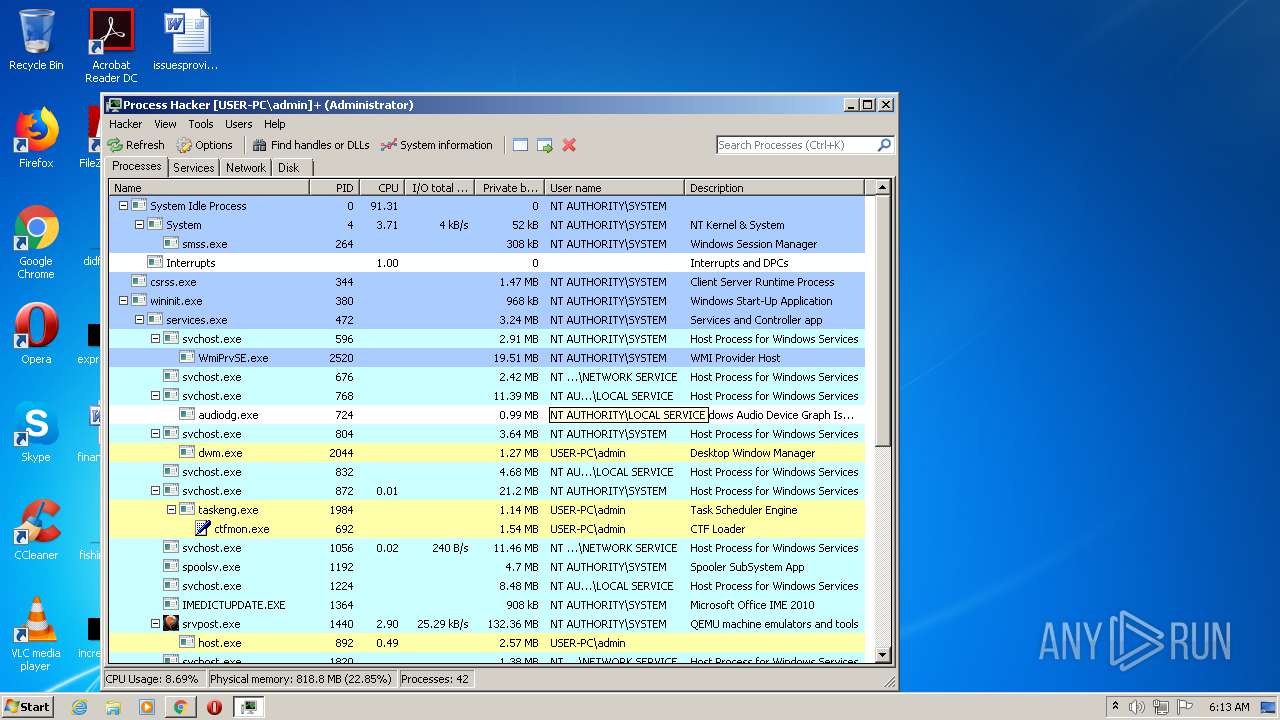
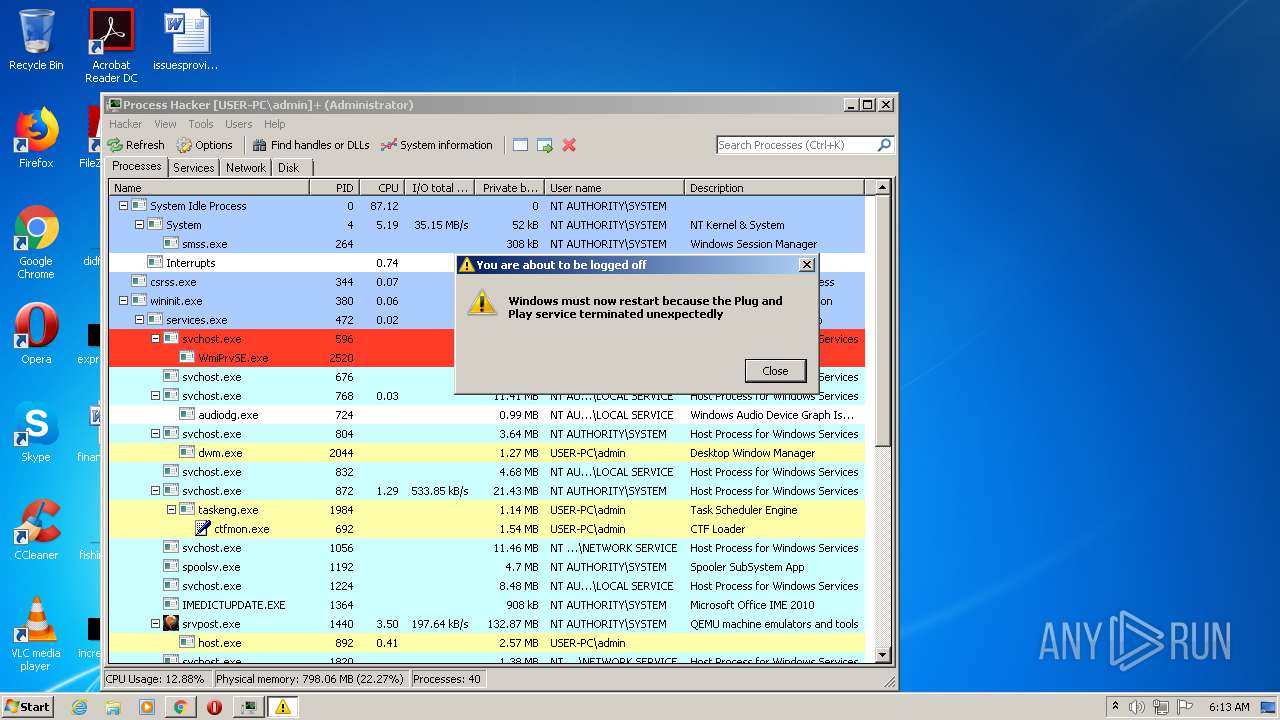
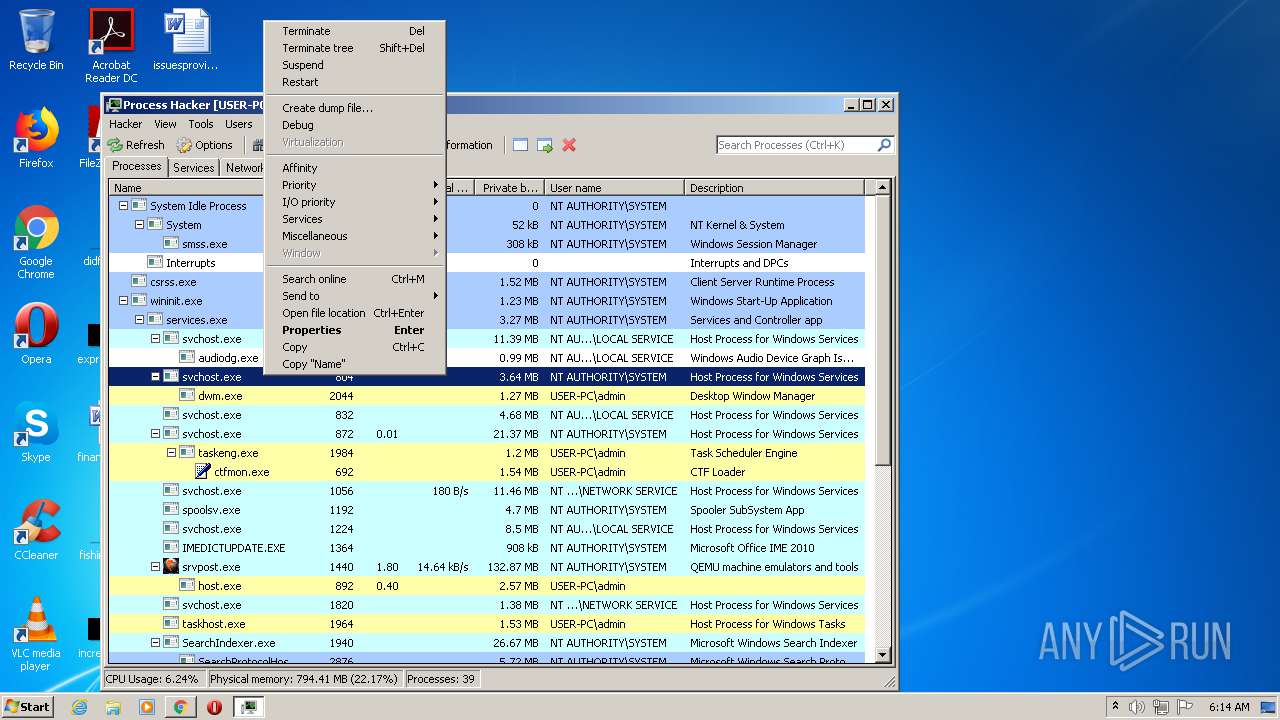
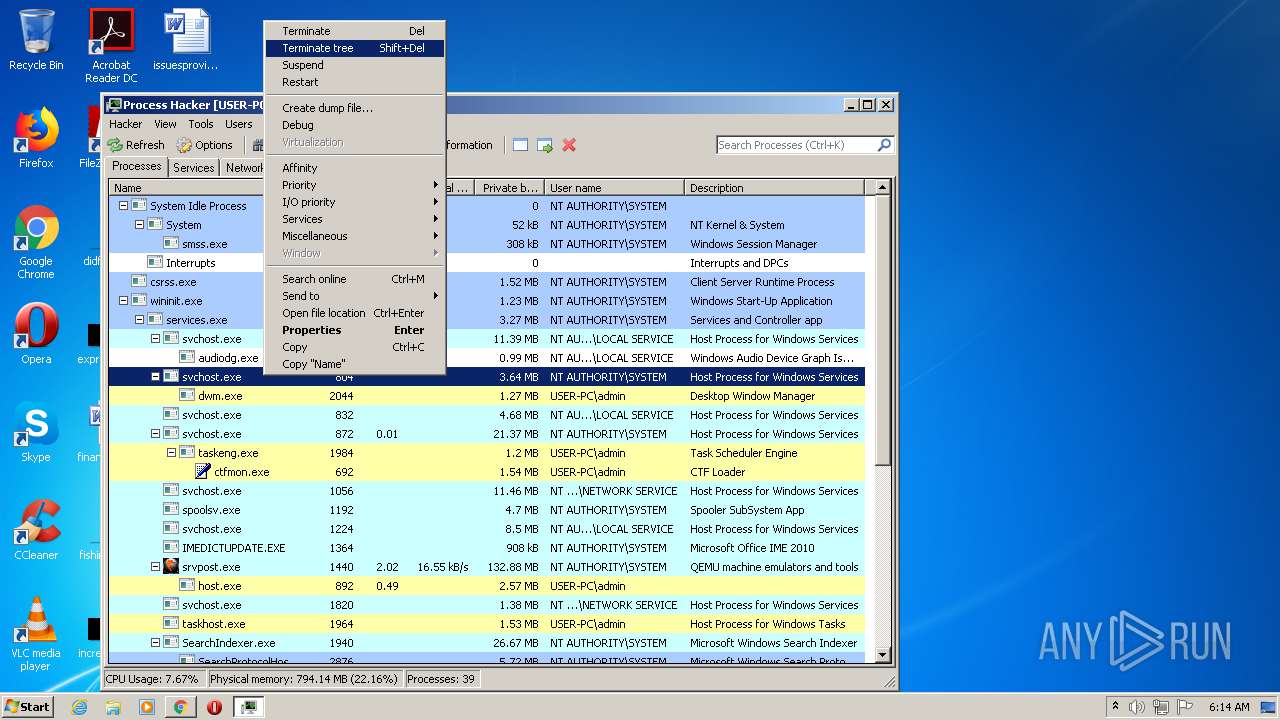
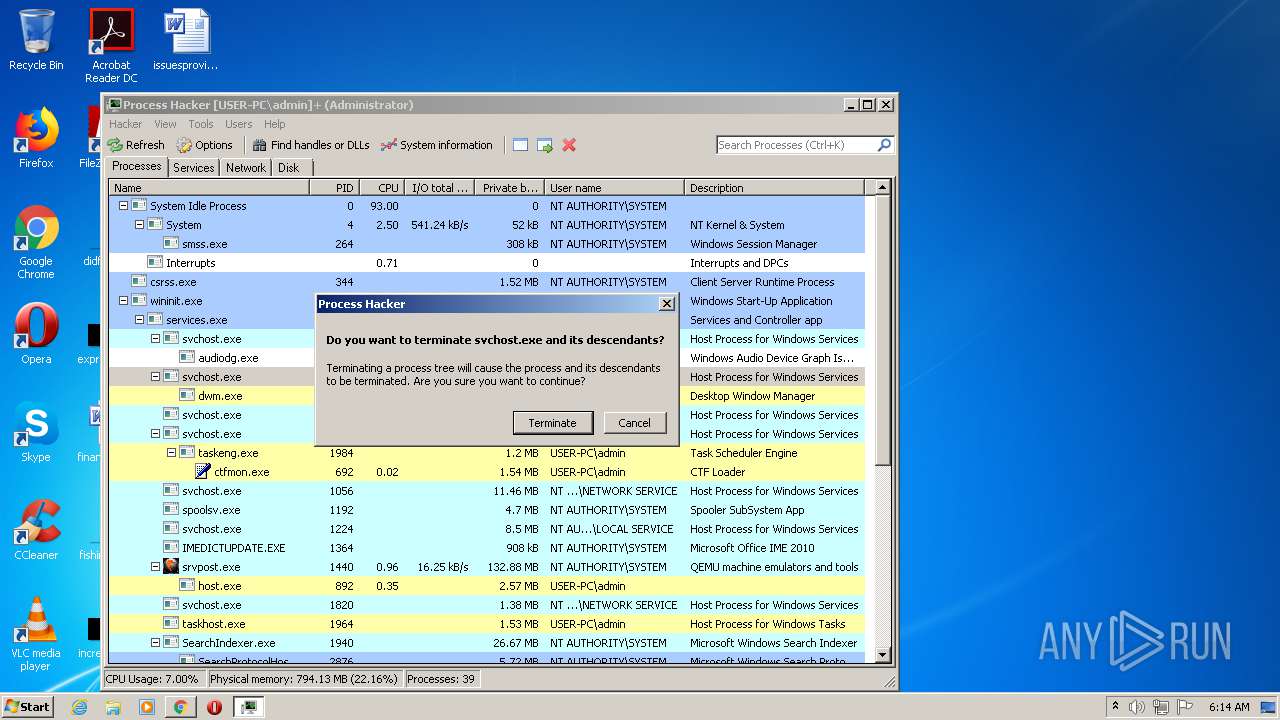
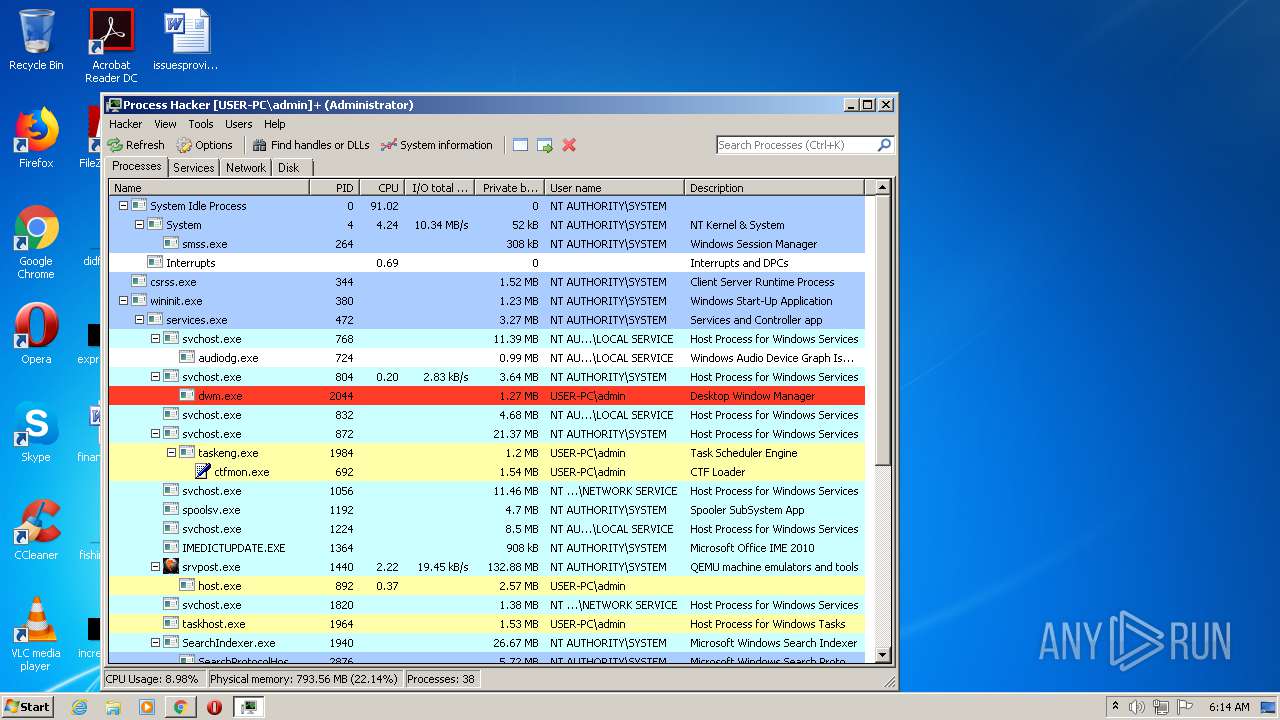
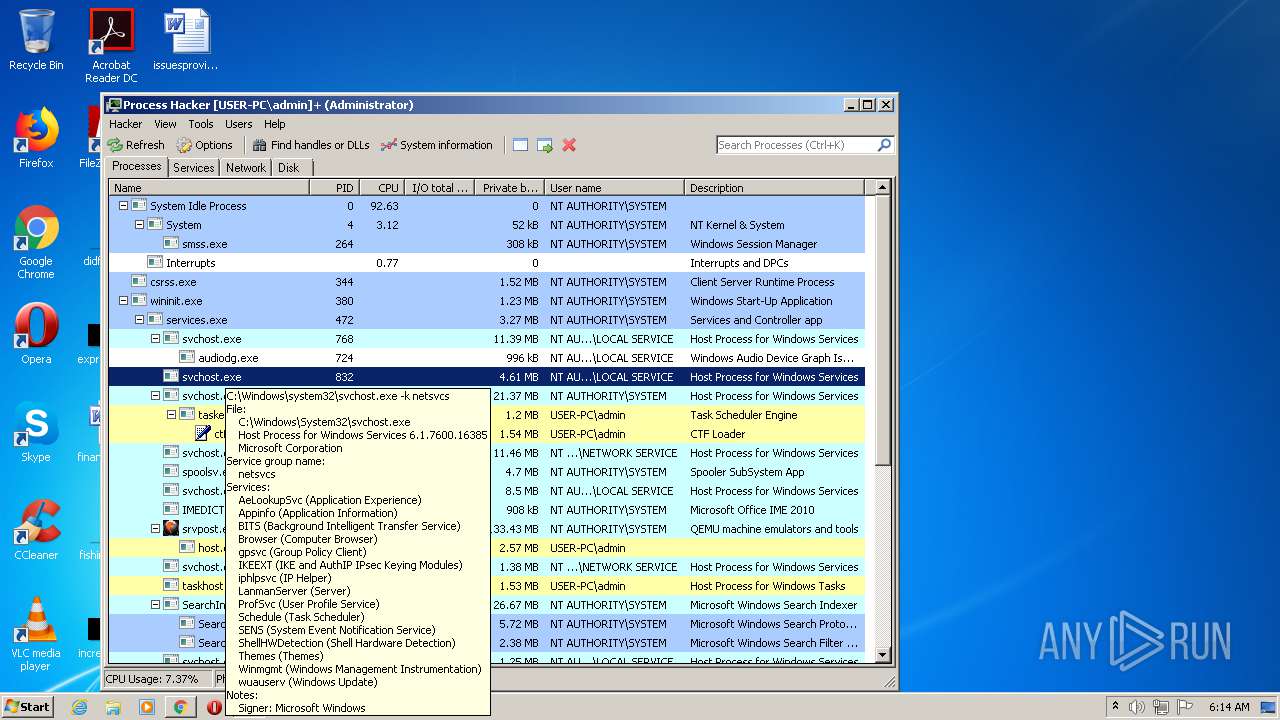
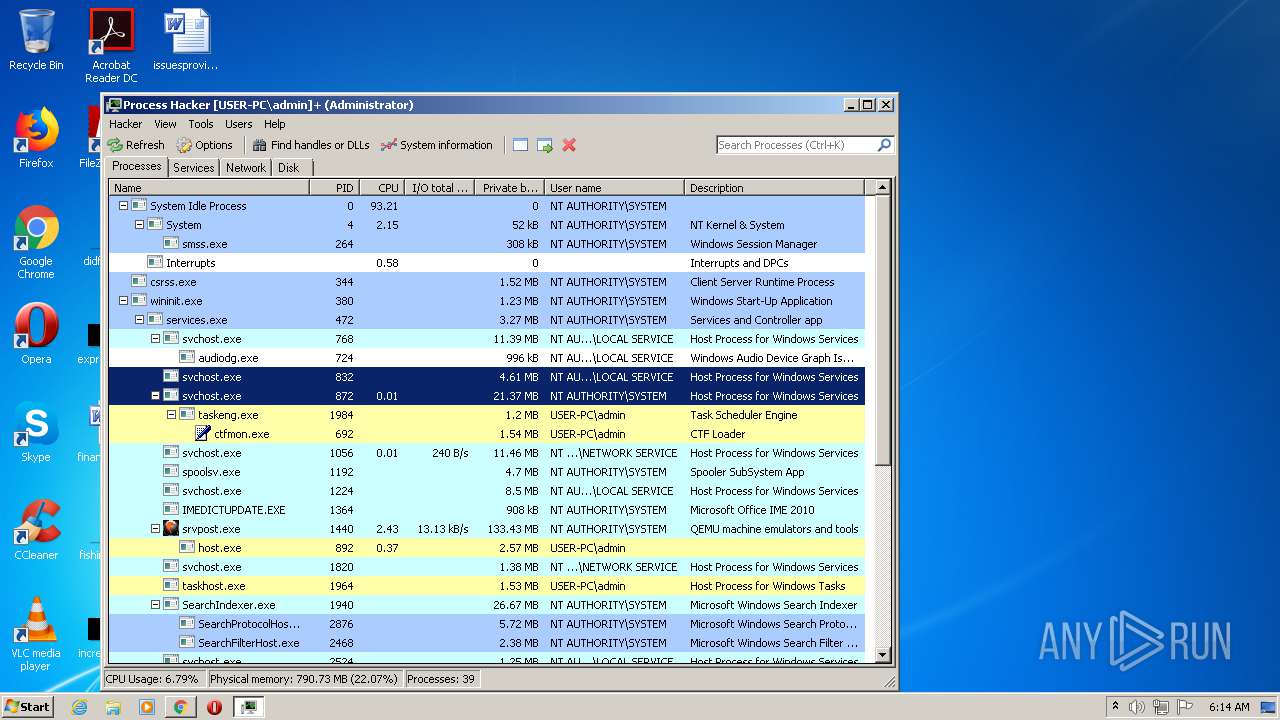
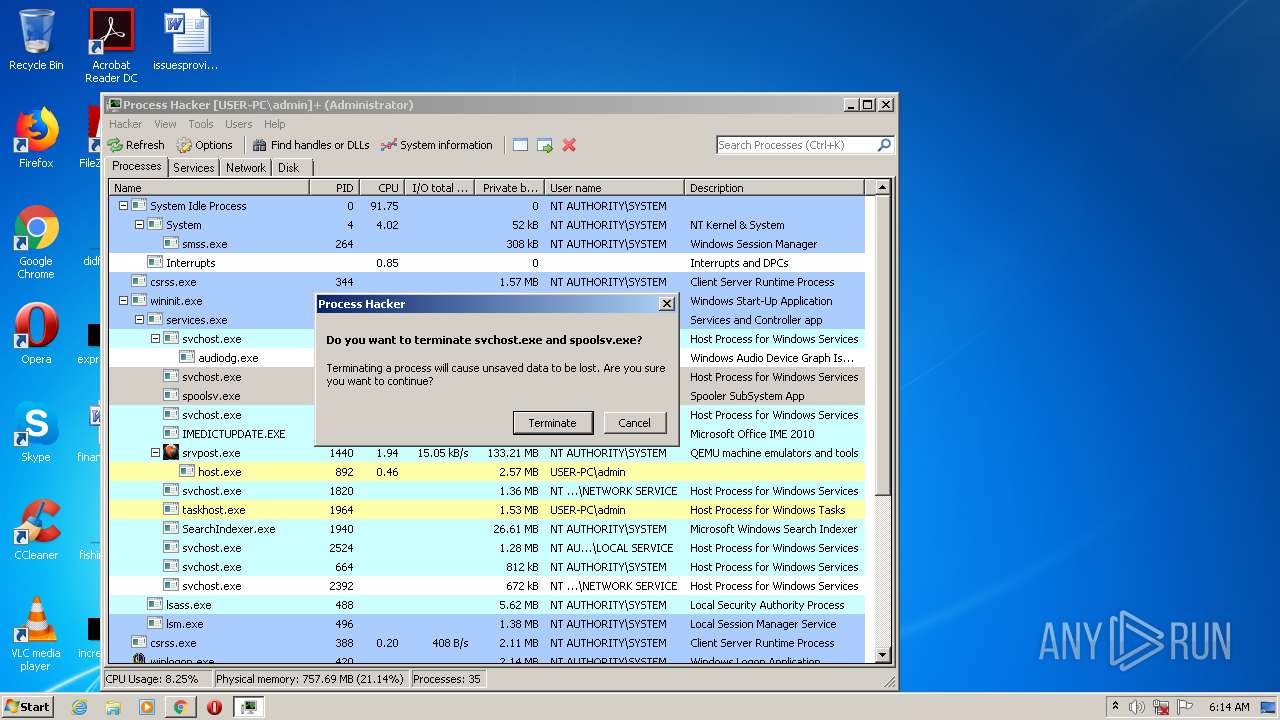
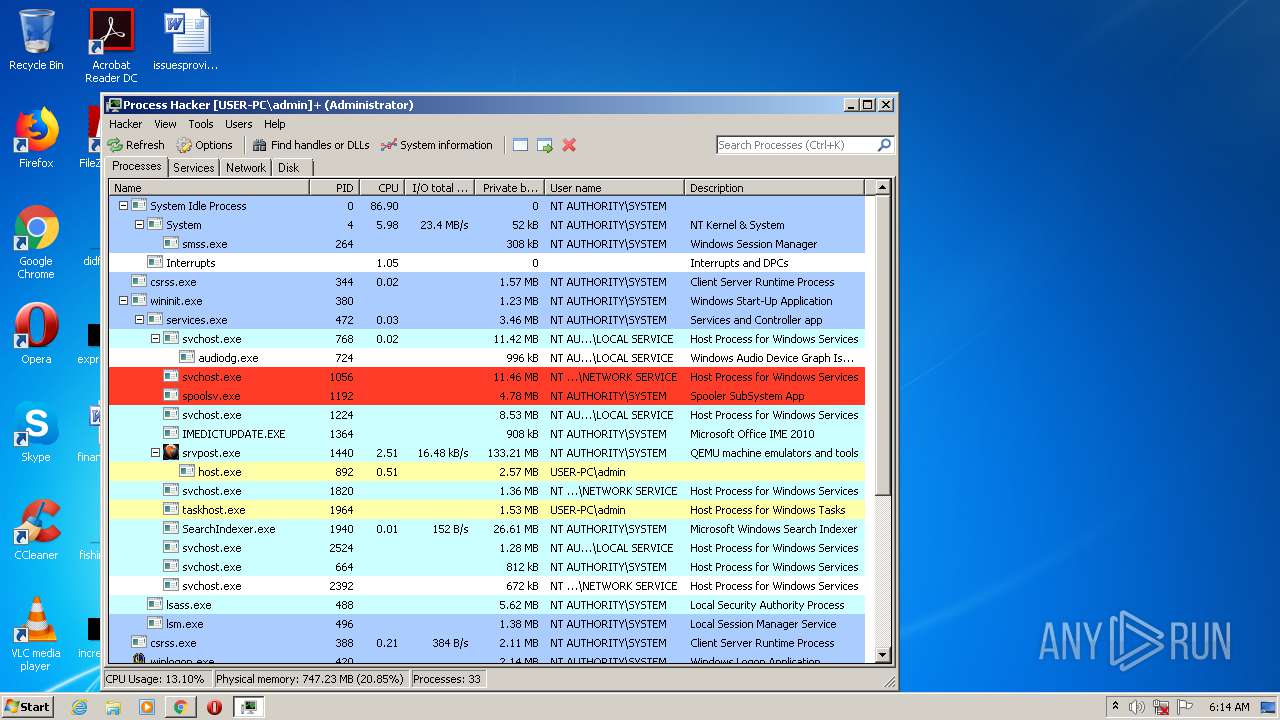
MALICIOUS
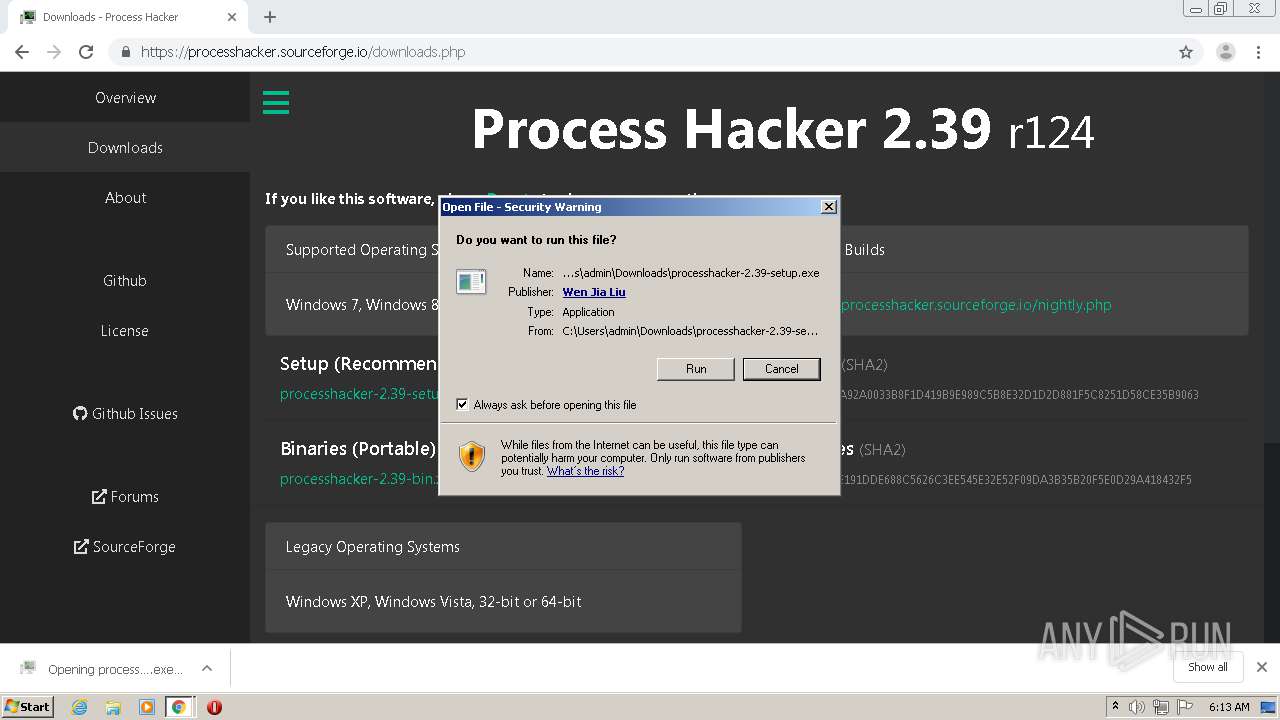
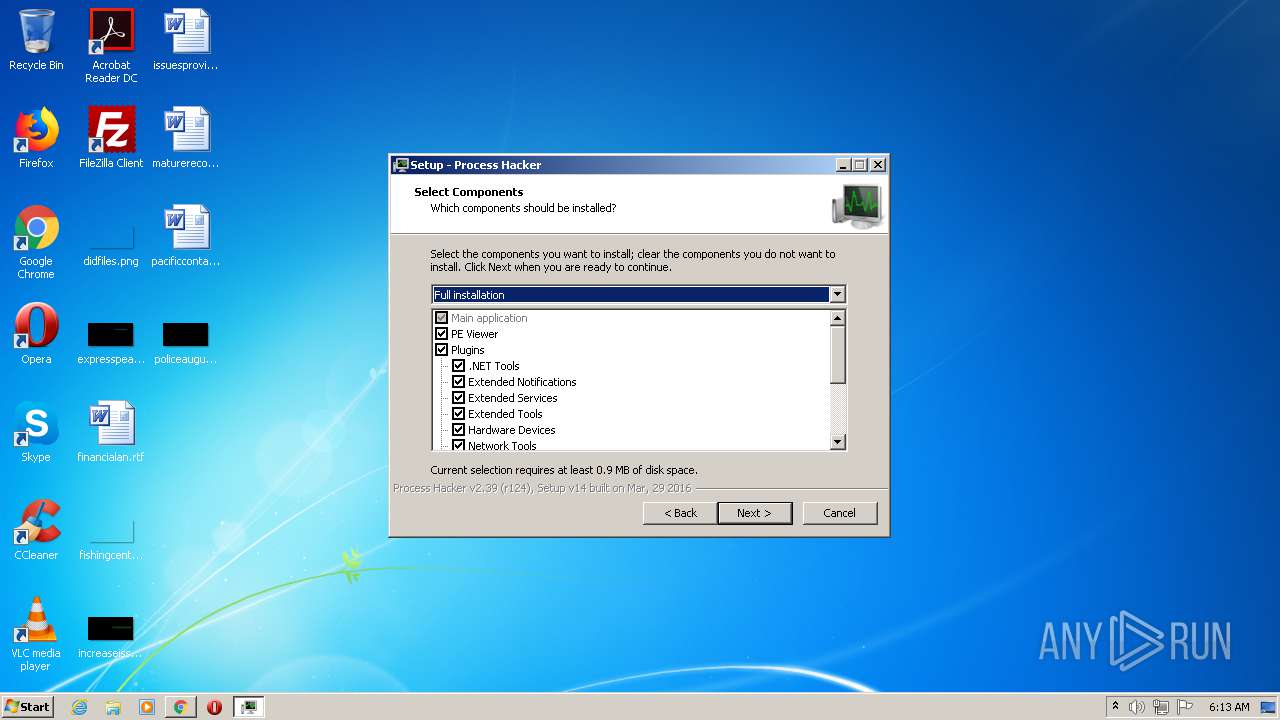
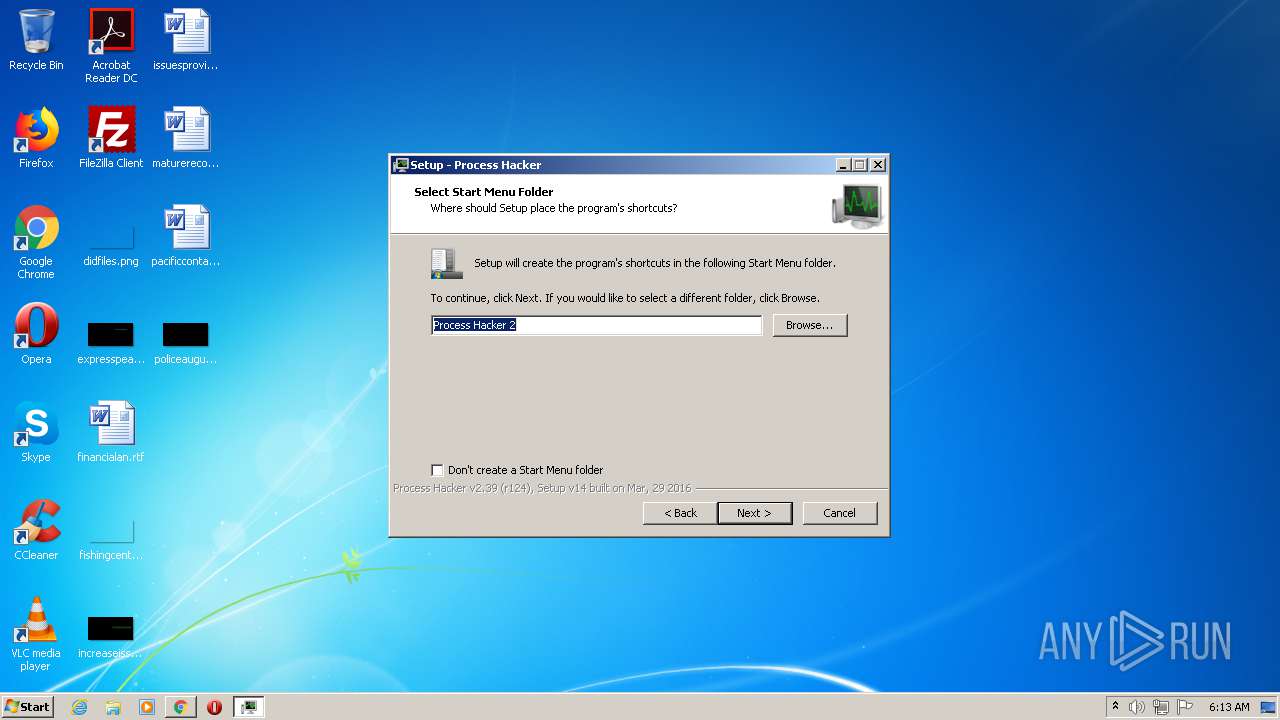
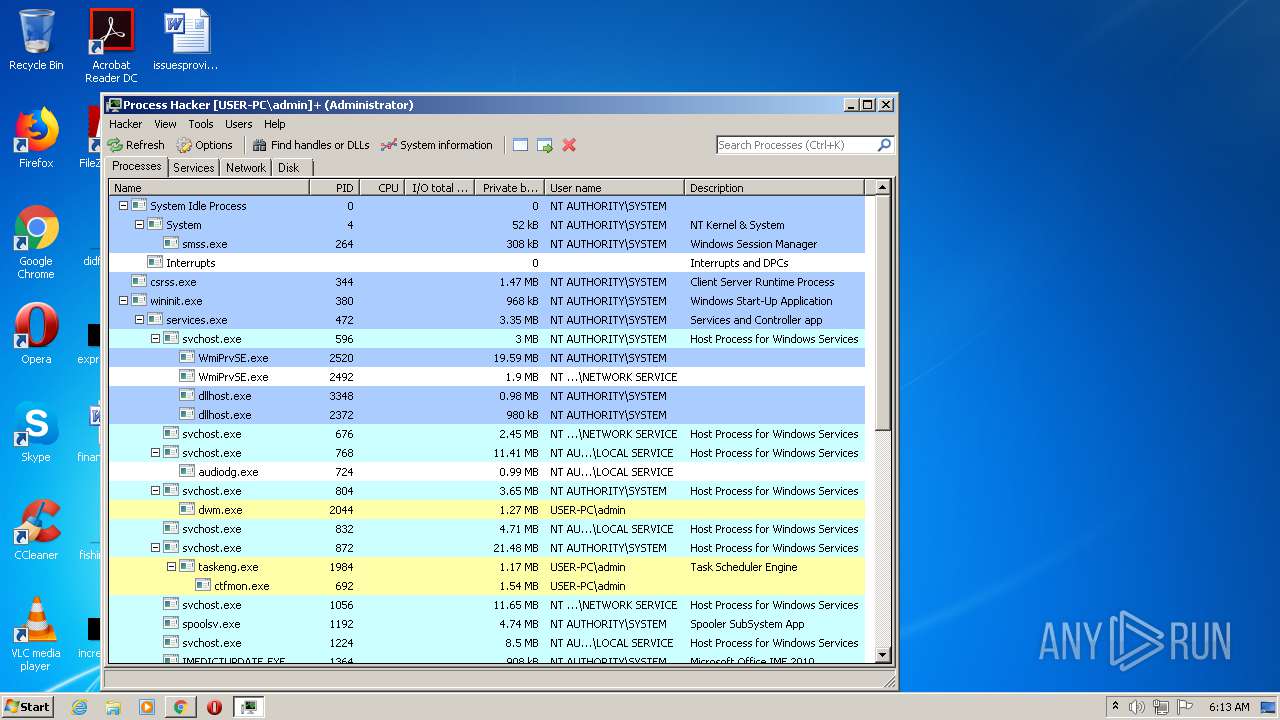
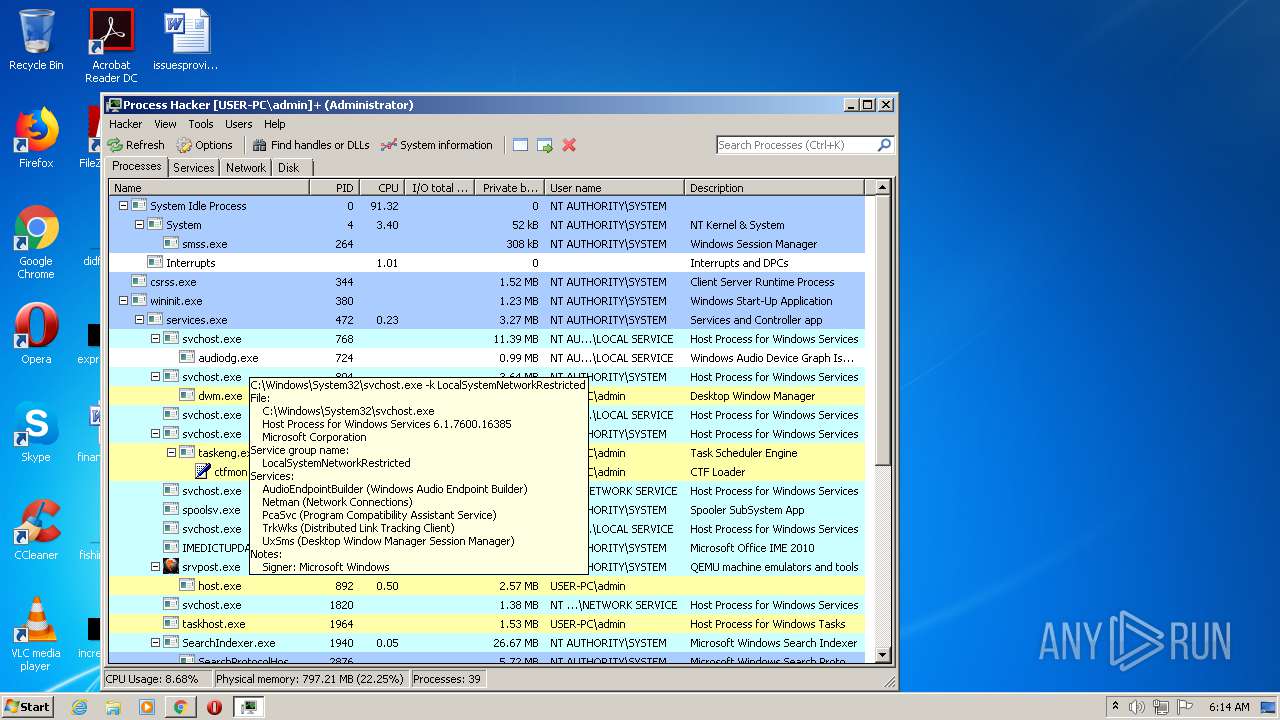
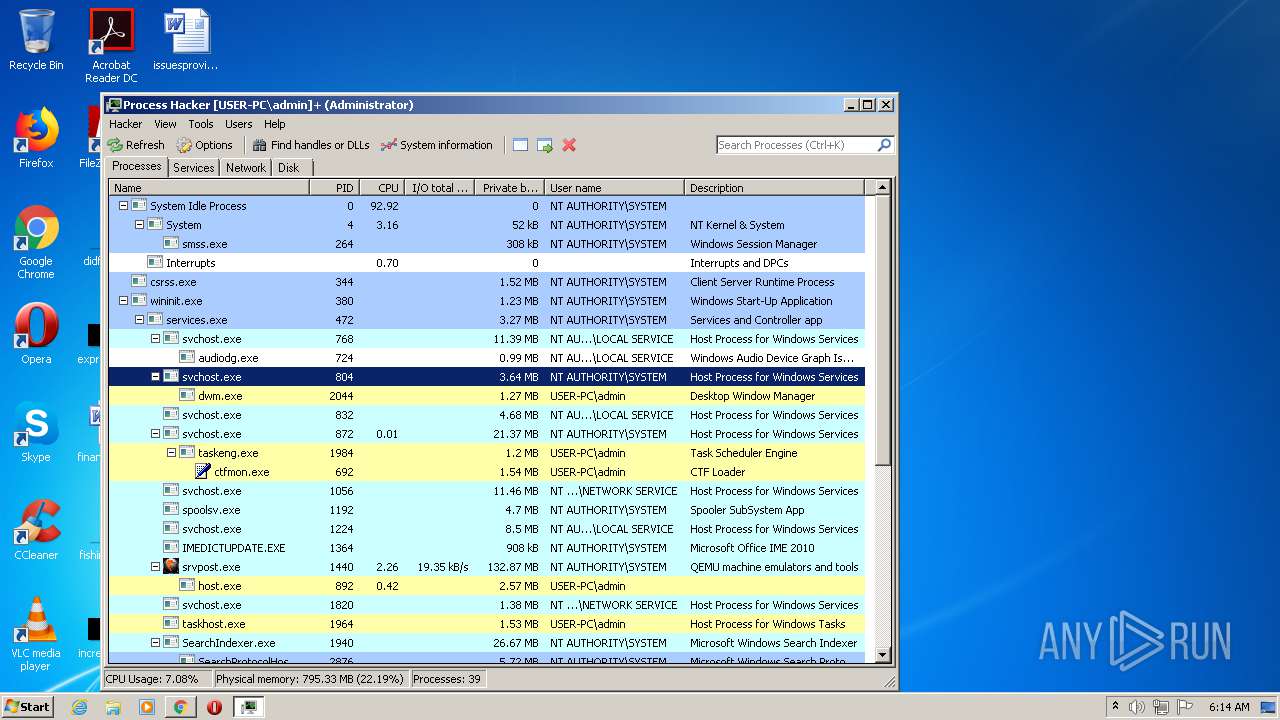
Application was dropped or rewritten from another process
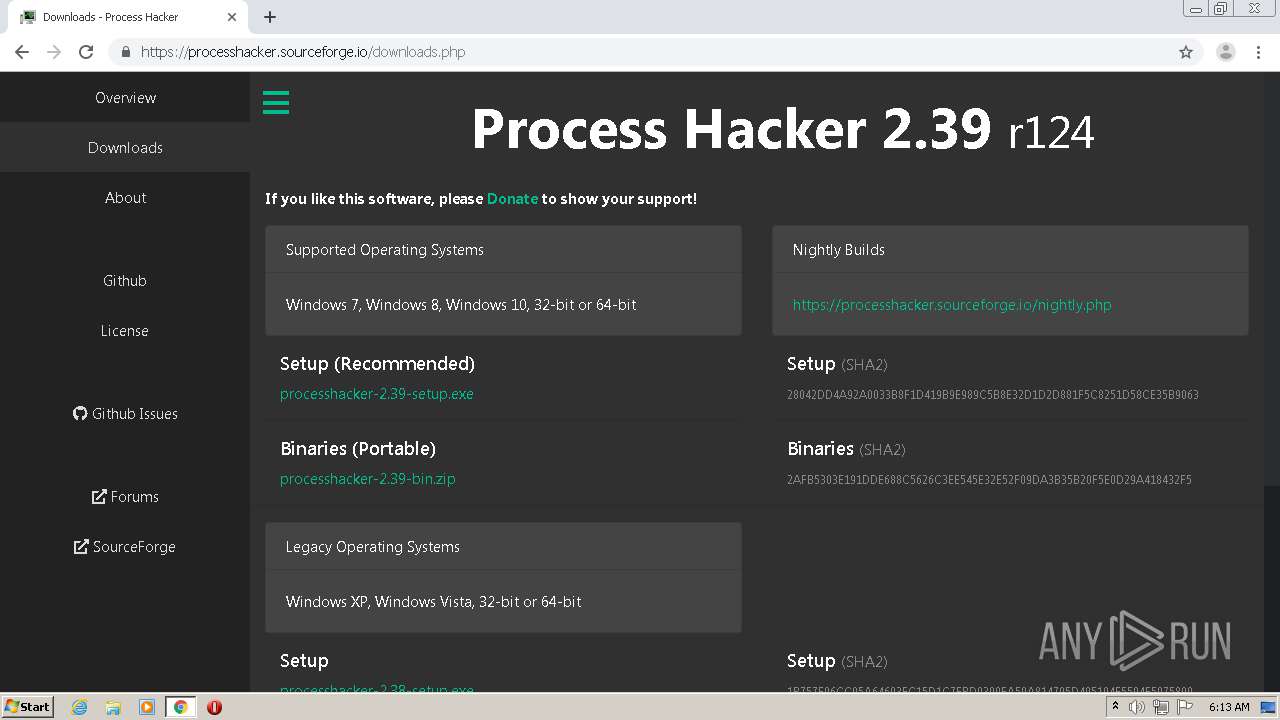
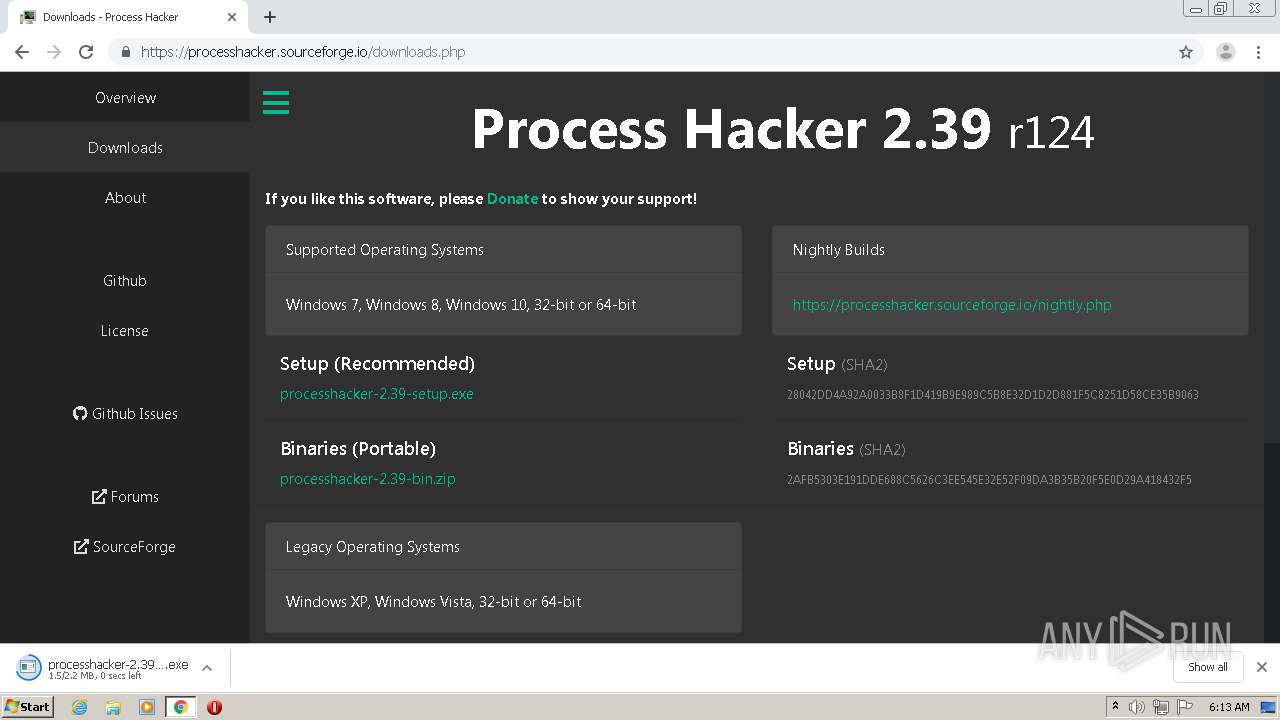
- processhacker-2.39-setup.exe (PID: 3184)
- processhacker-2.39-setup.exe (PID: 312)
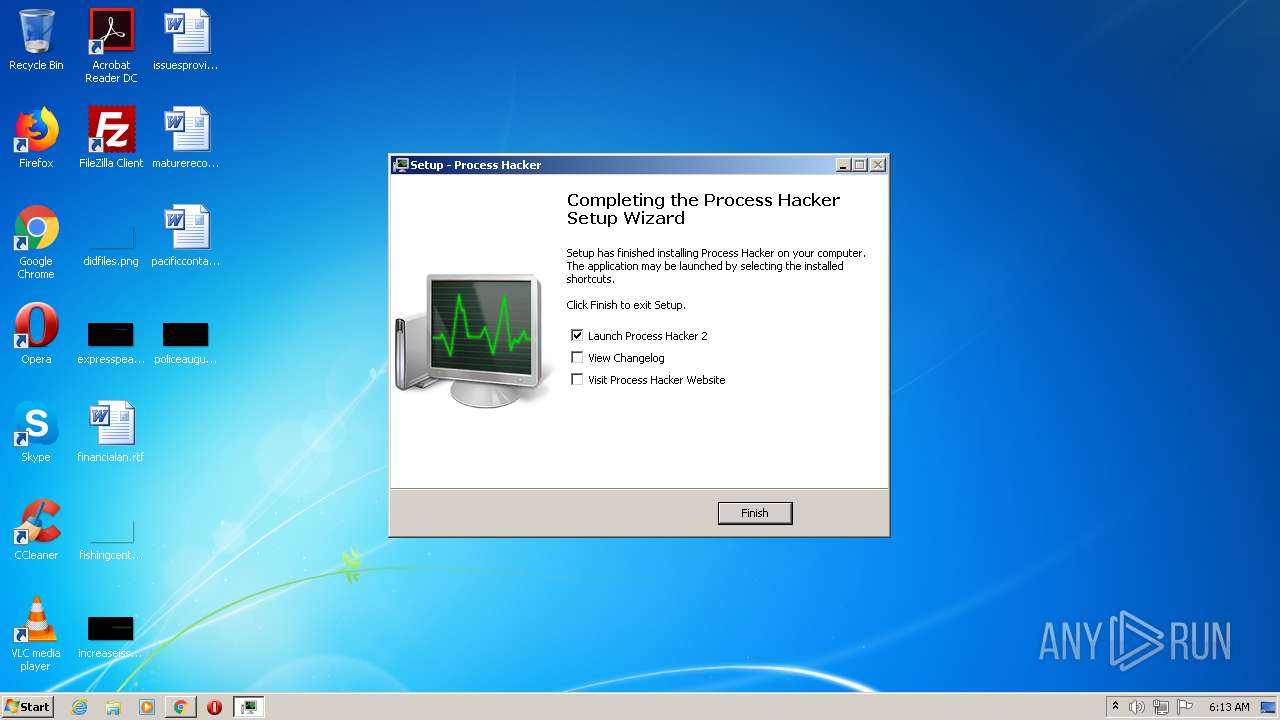
- ProcessHacker.exe (PID: 2080)
- ProcessHacker.exe (PID: 3468)
Loads dropped or rewritten executable
- ProcessHacker.exe (PID: 2080)
- ProcessHacker.exe (PID: 3468)
Changes settings of System certificates
- ProcessHacker.exe (PID: 3468)
SUSPICIOUS
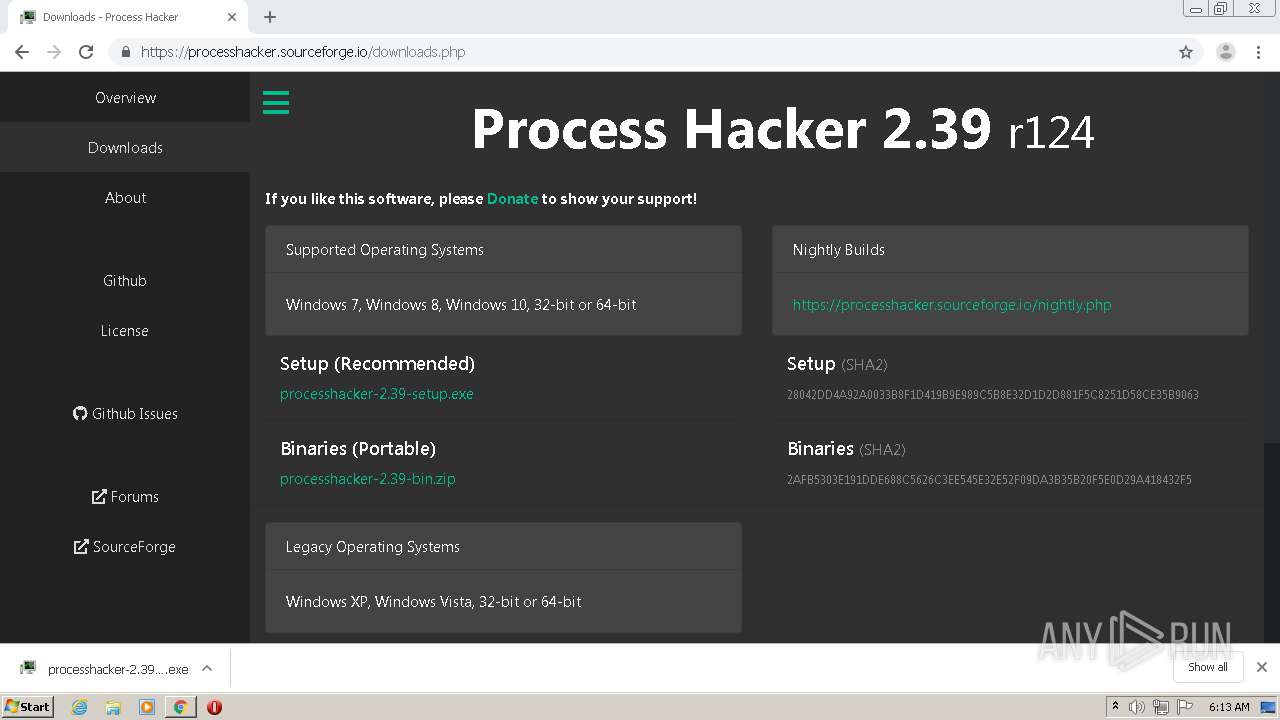
Executable content was dropped or overwritten
- chrome.exe (PID: 3232)
- processhacker-2.39-setup.exe (PID: 3184)
- processhacker-2.39-setup.exe (PID: 312)
- processhacker-2.39-setup.tmp (PID: 1124)
- chrome.exe (PID: 2208)
Creates files in the user directory
- ProcessHacker.exe (PID: 2080)
Adds / modifies Windows certificates
- ProcessHacker.exe (PID: 3468)
INFO
Reads the hosts file
- chrome.exe (PID: 3232)
- chrome.exe (PID: 2208)
Application was dropped or rewritten from another process
- processhacker-2.39-setup.tmp (PID: 4040)
- processhacker-2.39-setup.tmp (PID: 1124)
Application launched itself
- chrome.exe (PID: 2208)
Loads dropped or rewritten executable
- processhacker-2.39-setup.tmp (PID: 1124)
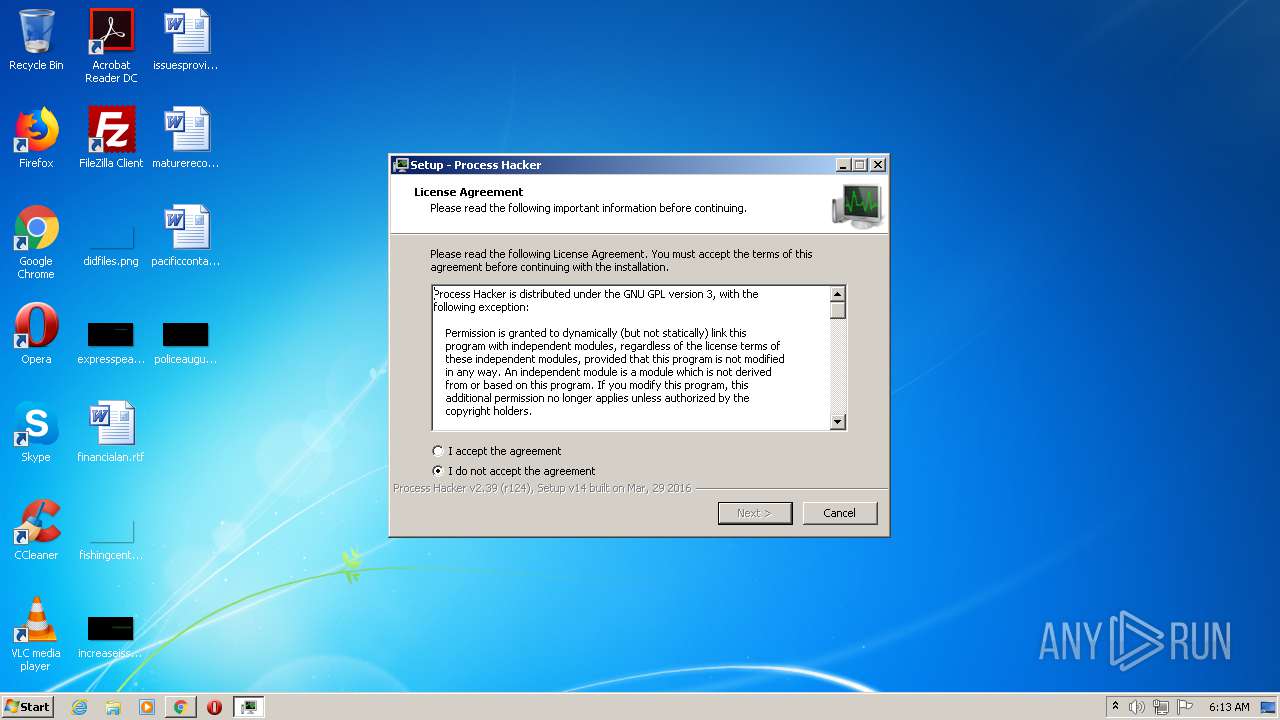
Creates a software uninstall entry
- processhacker-2.39-setup.tmp (PID: 1124)
Reads settings of System Certificates
- ProcessHacker.exe (PID: 2080)
- ProcessHacker.exe (PID: 3468)
Reads Internet Cache Settings
- chrome.exe (PID: 2208)
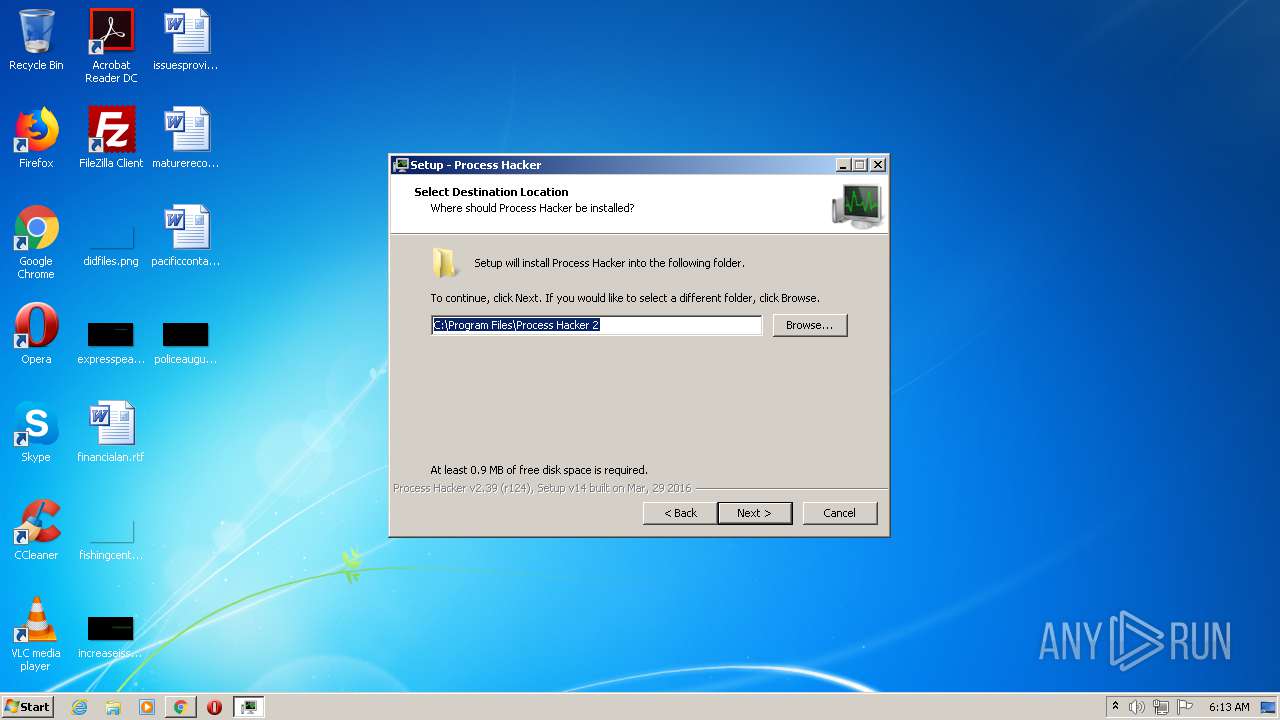
Creates files in the program directory
- processhacker-2.39-setup.tmp (PID: 1124)
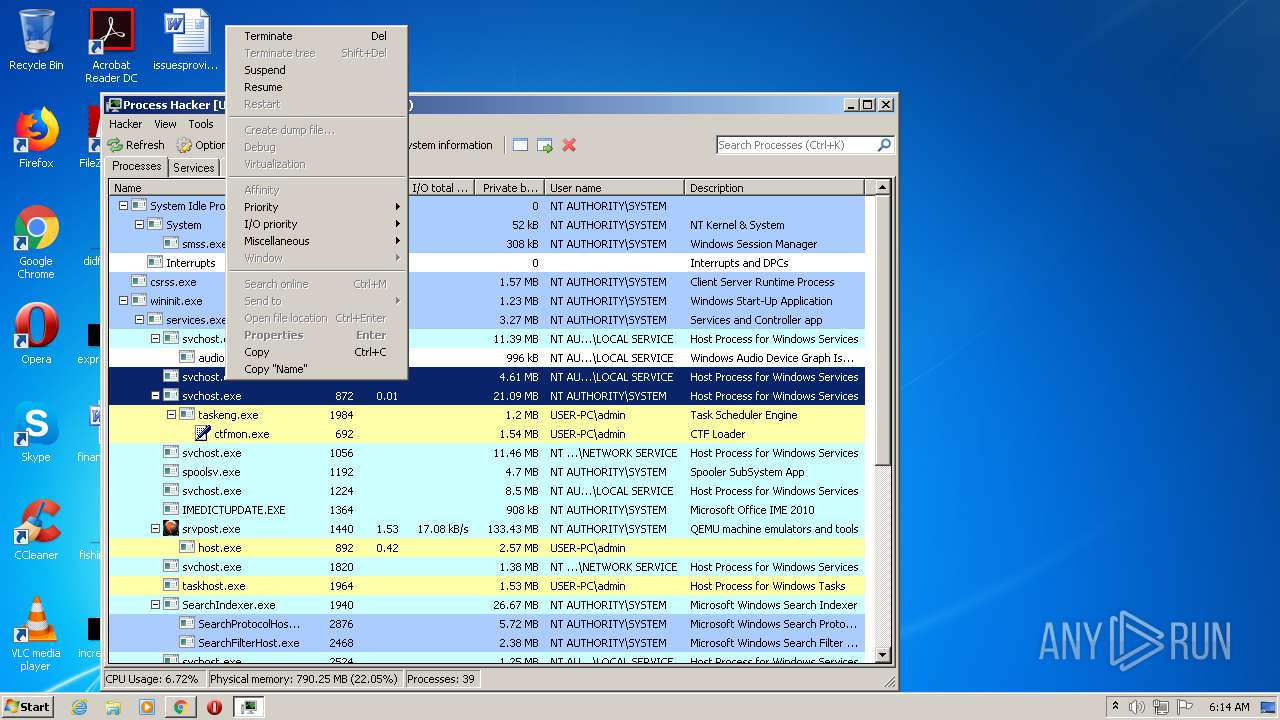
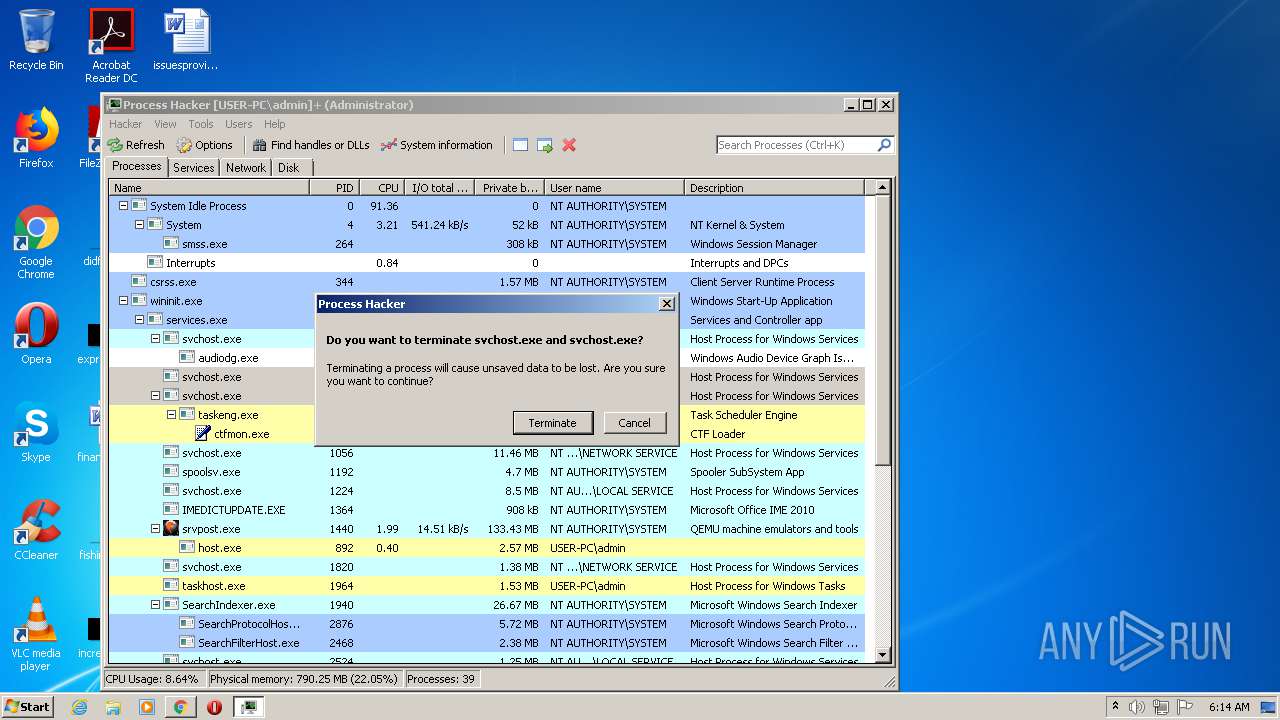
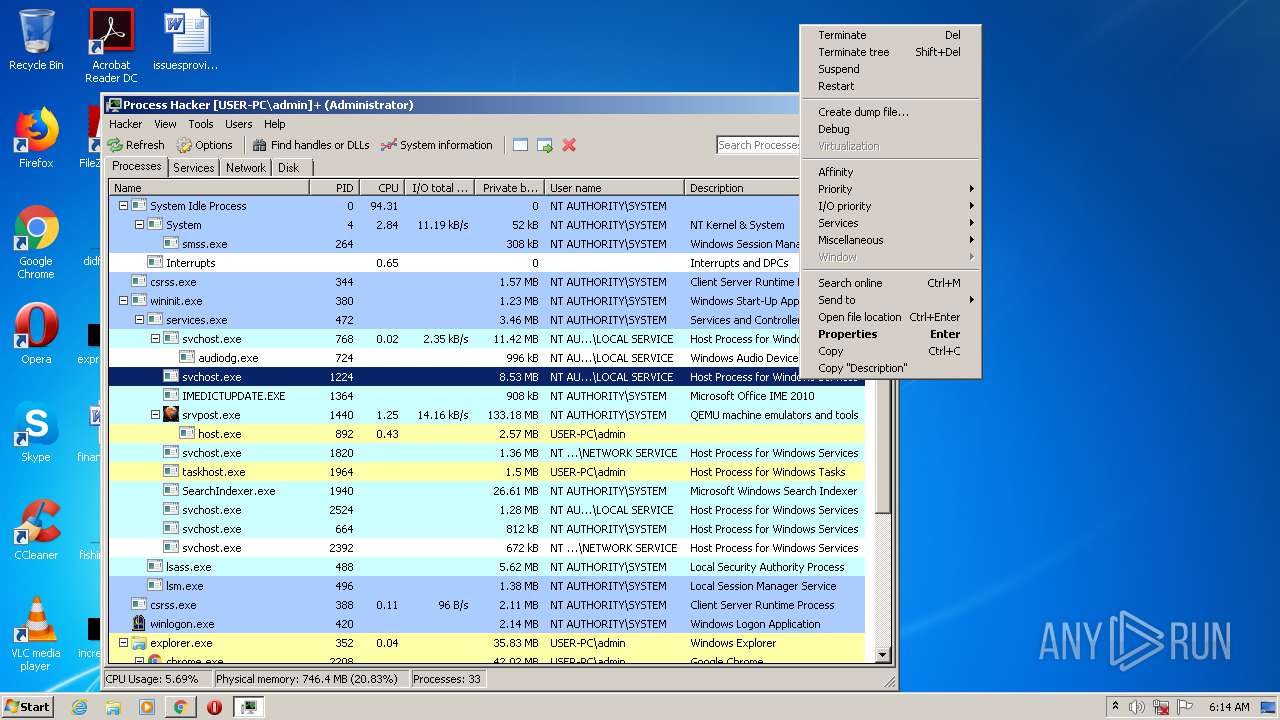
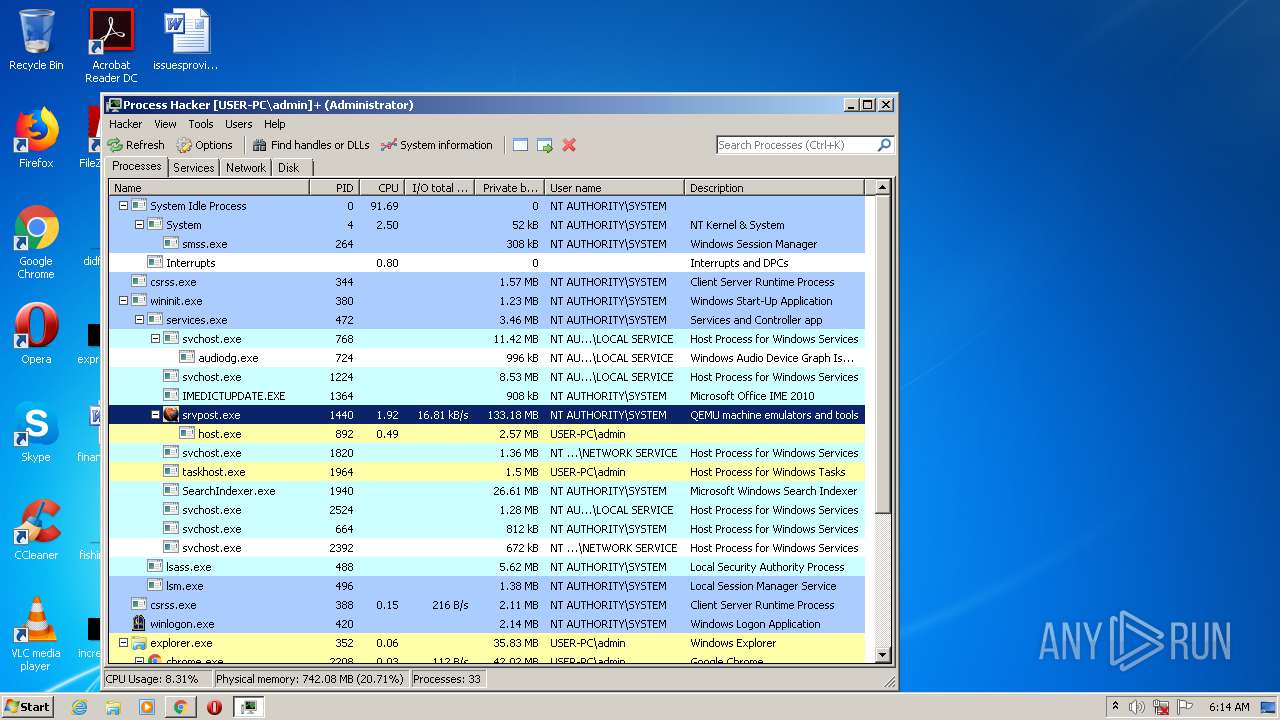
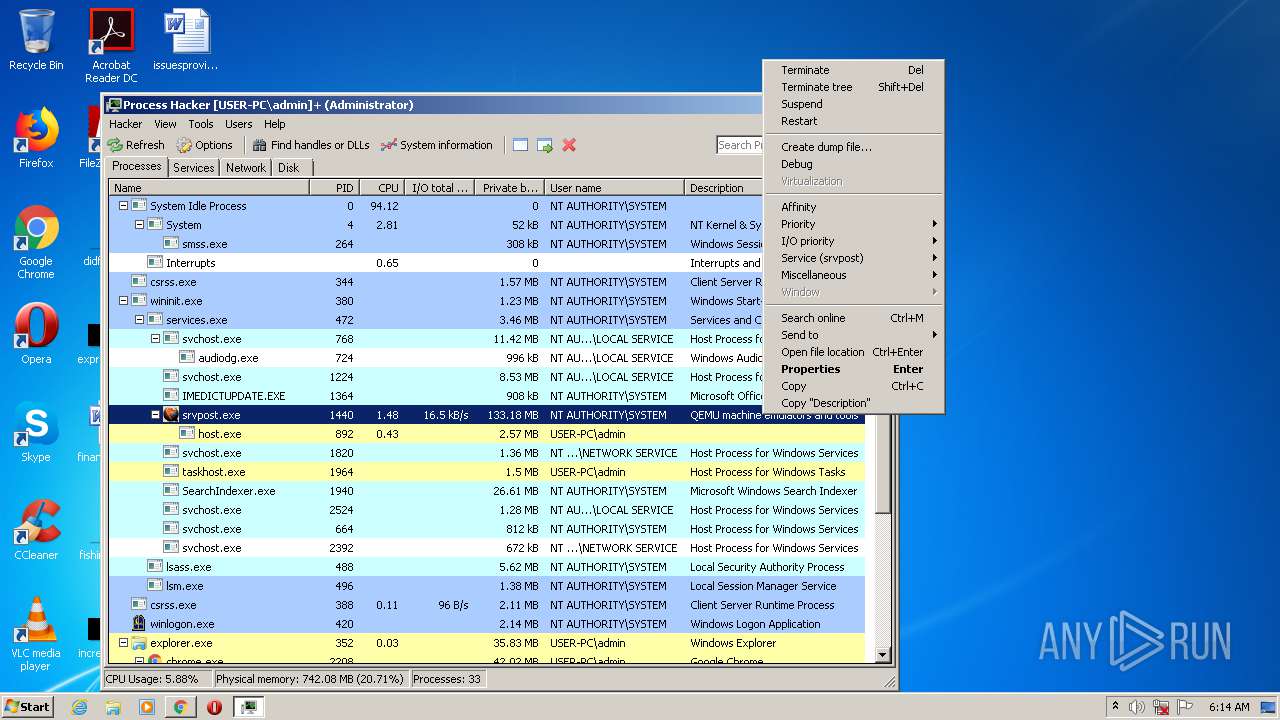
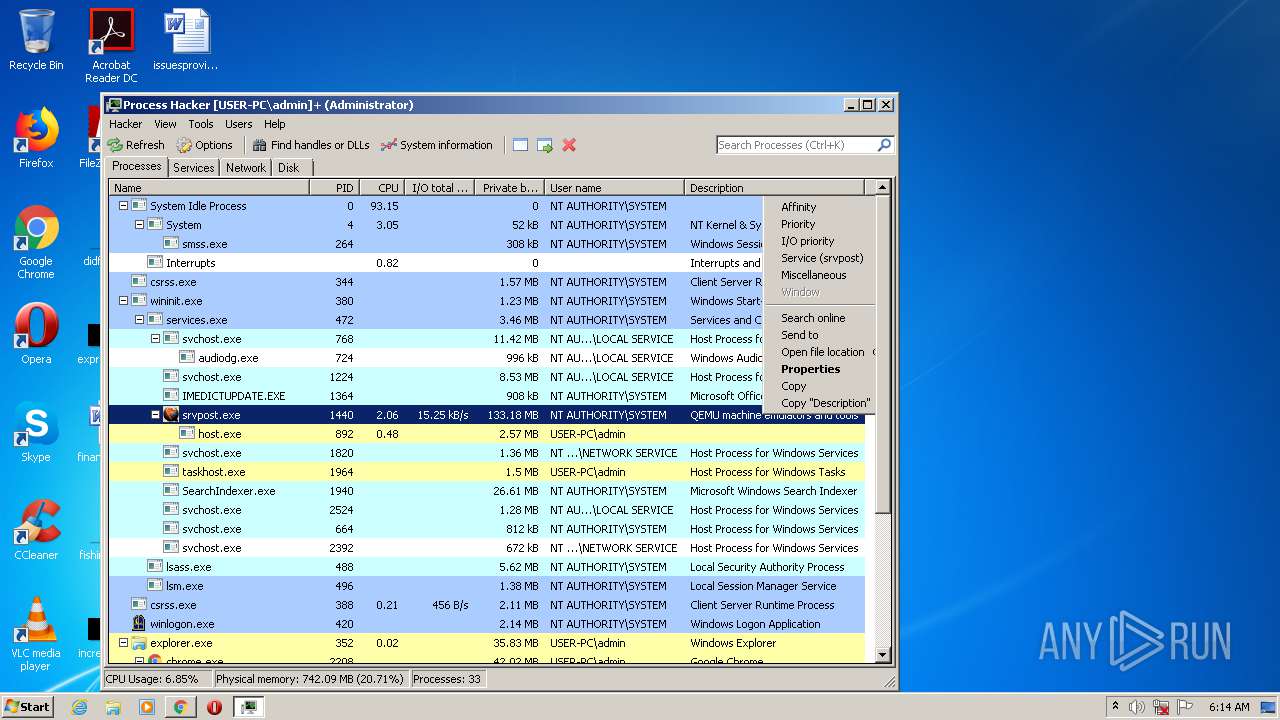
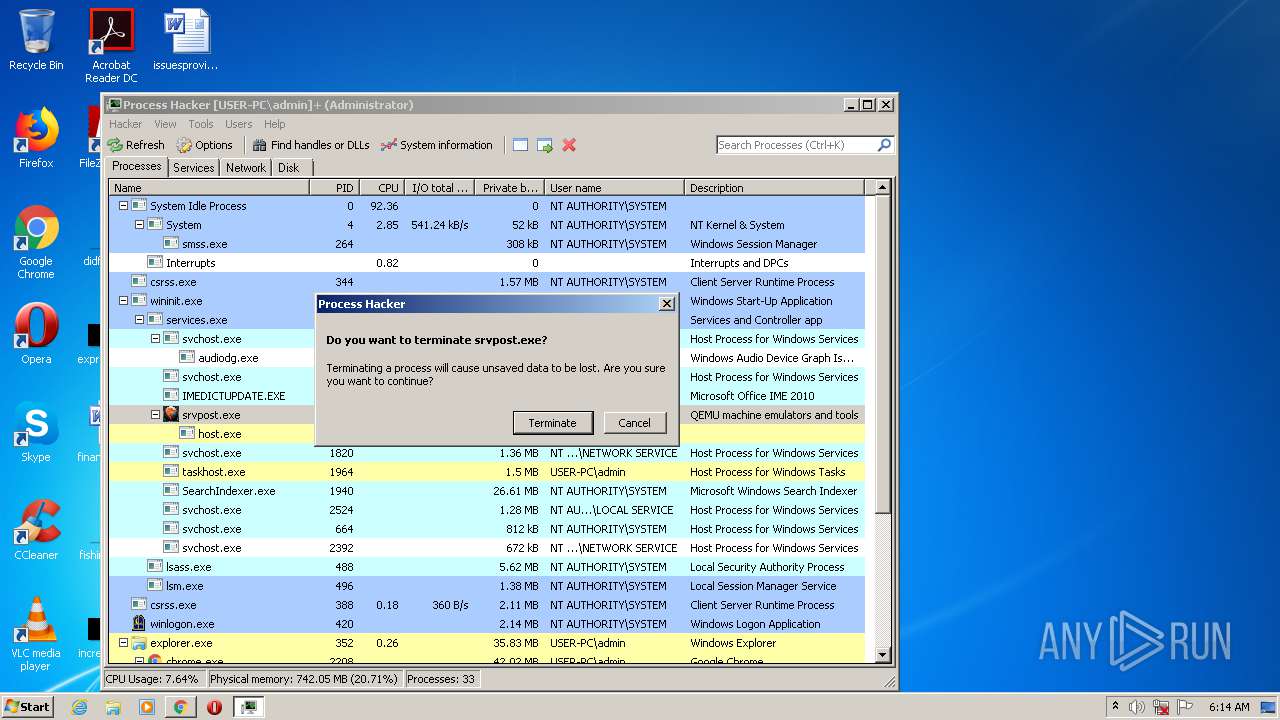
Manual execution by user
- ProcessHacker.exe (PID: 3468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
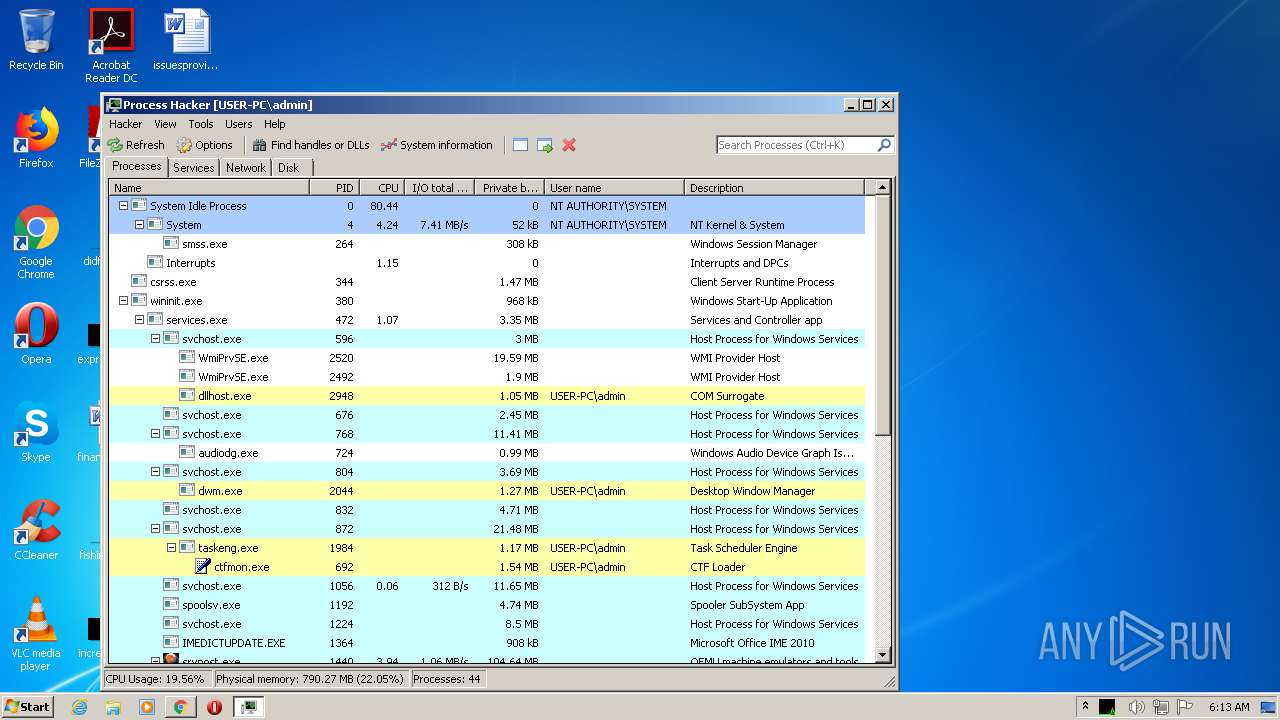
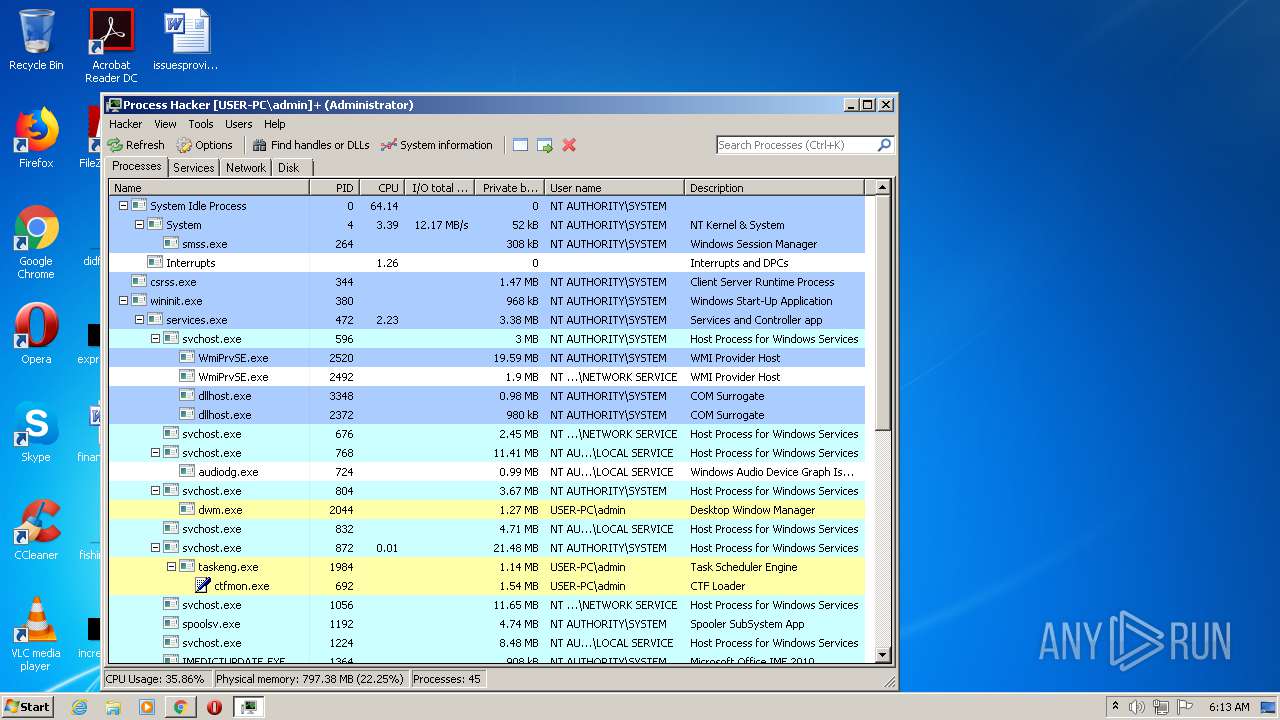
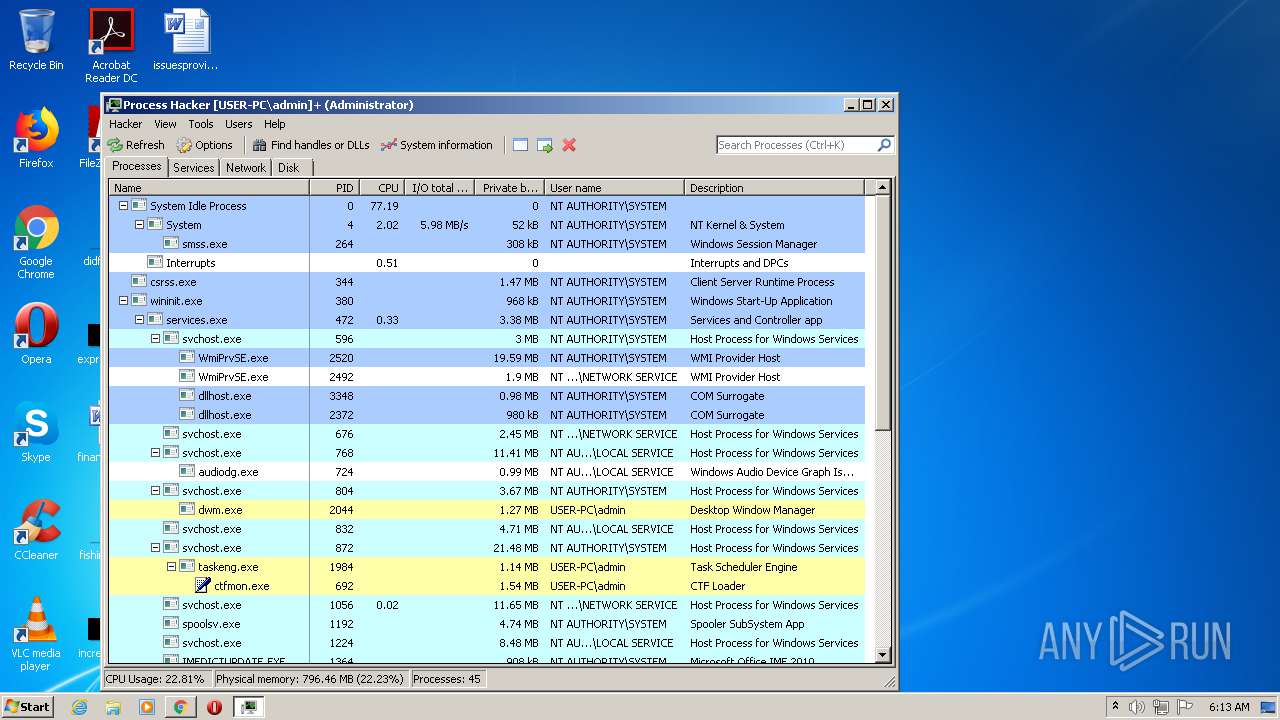
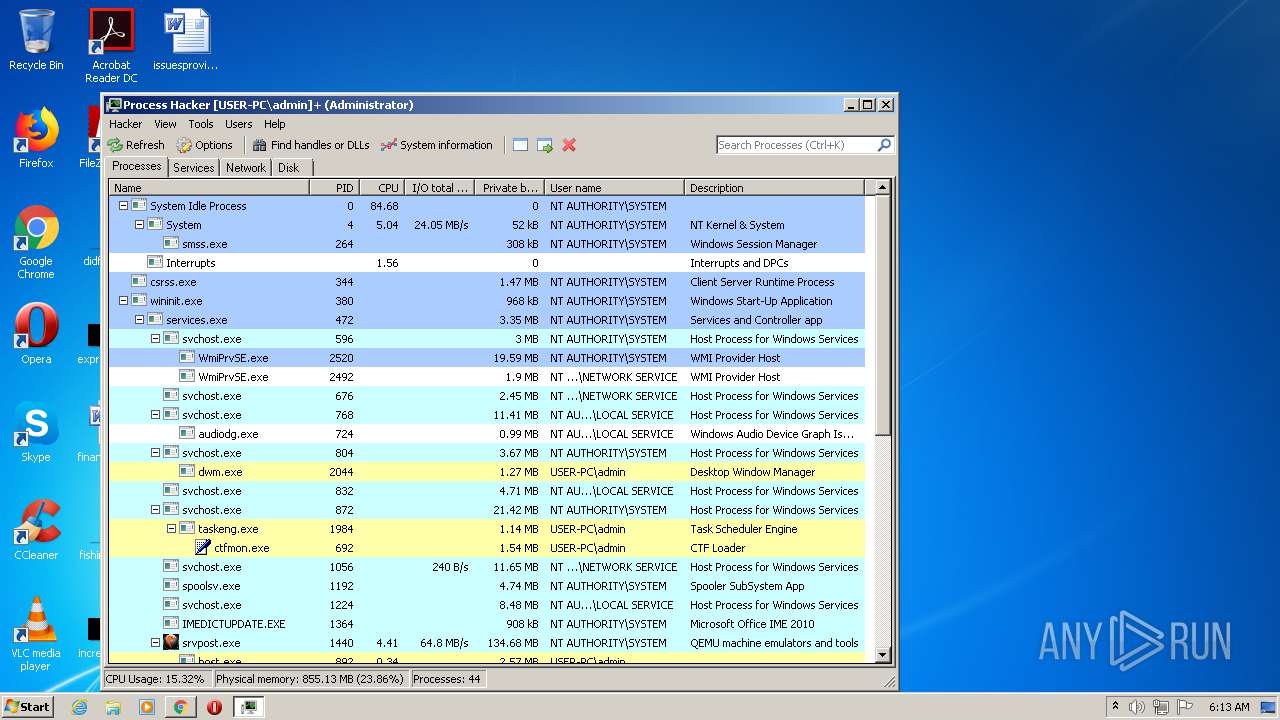
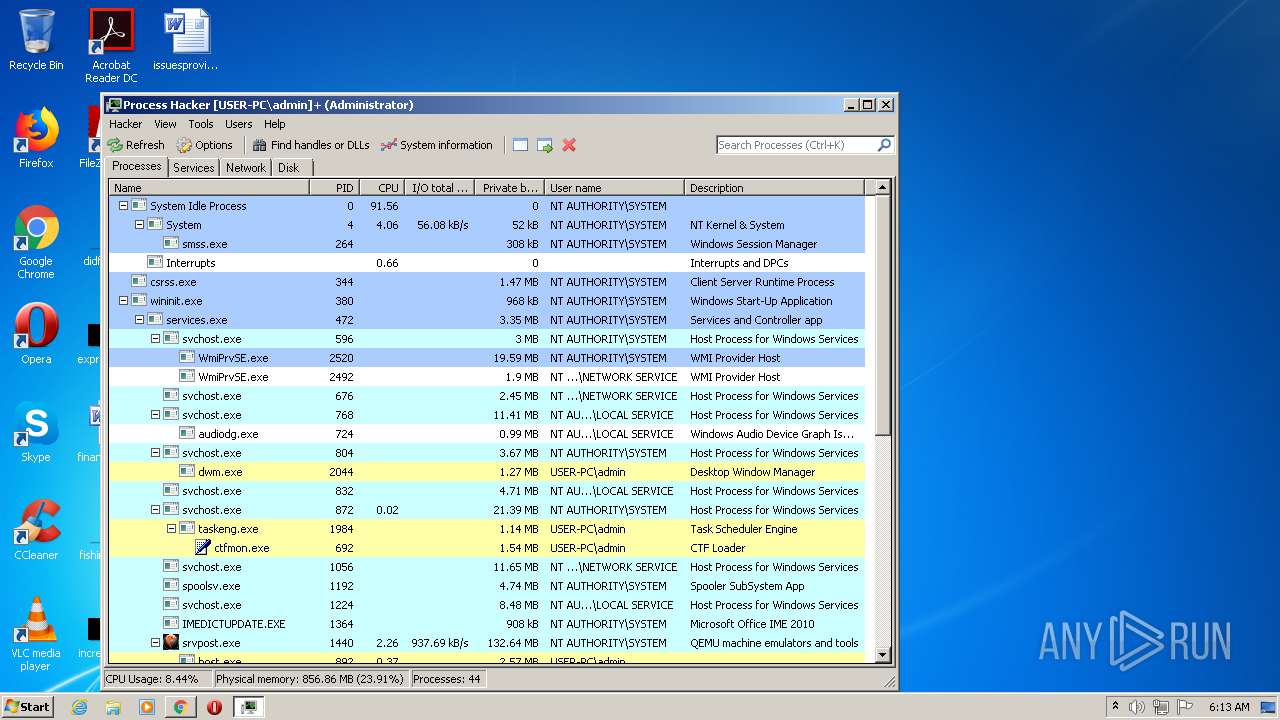
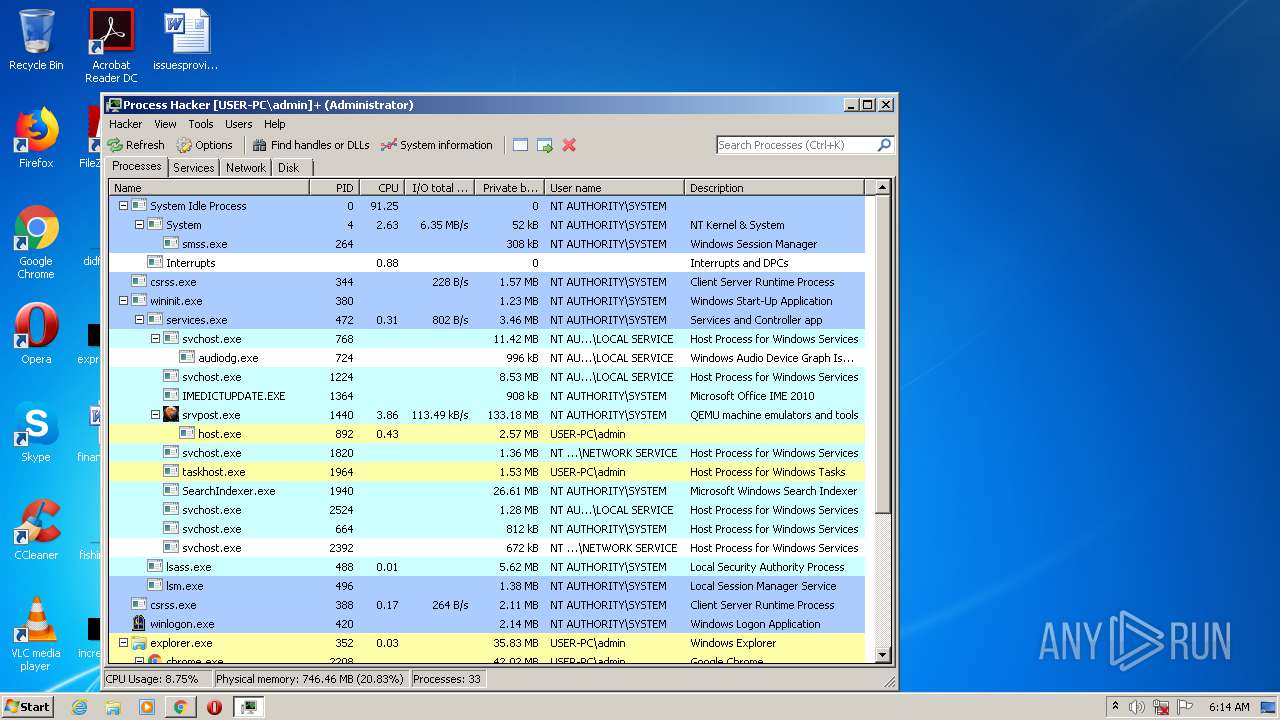
Total processes
84
Monitored processes
33
Malicious processes
3
Suspicious processes
1
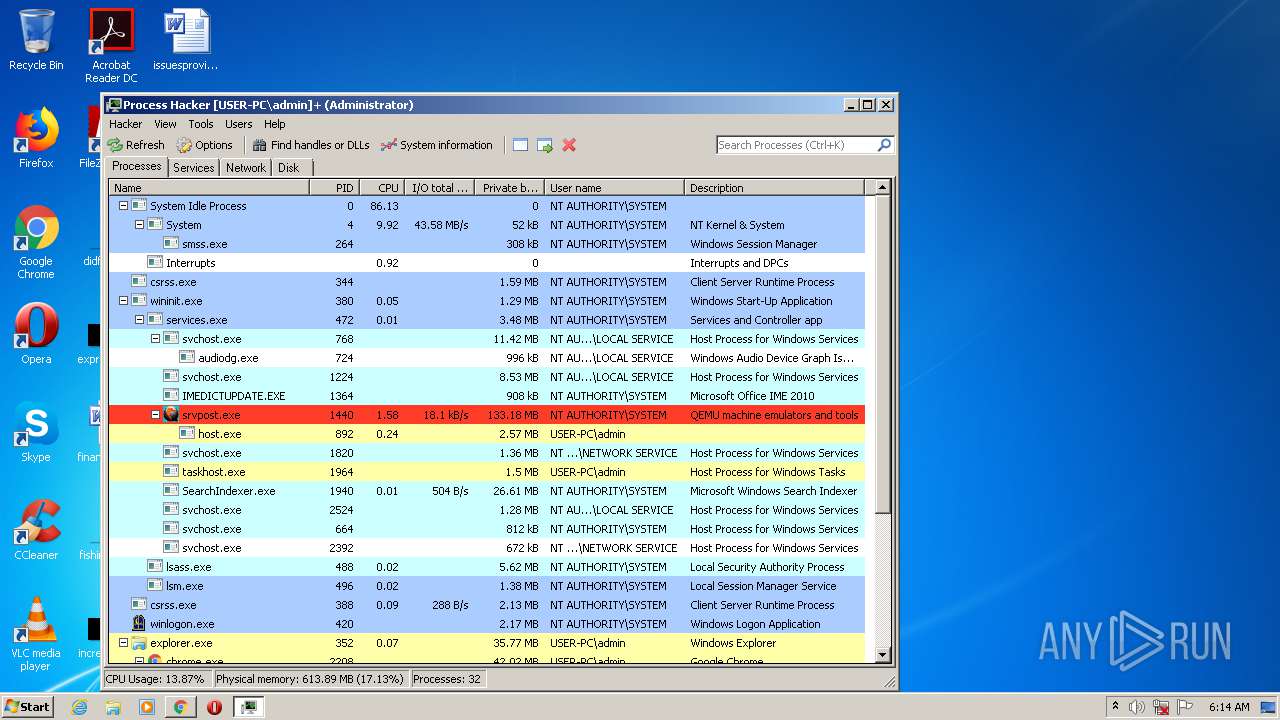
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Users\admin\Downloads\processhacker-2.39-setup.exe" /SPAWNWND=$1C001A /NOTIFYWND=$1E01D4 | C:\Users\admin\Downloads\processhacker-2.39-setup.exe | processhacker-2.39-setup.tmp | ||||||||||||
User: admin Company: wj32 Integrity Level: HIGH Description: Process Hacker Setup Exit code: 0 Version: 2.39 (r124) Modules
| |||||||||||||||
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,5912641843274199931,12169101080813121324,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18005024692453384143 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1364 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,5912641843274199931,12169101080813121324,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7228875689354434954 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,5912641843274199931,12169101080813121324,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1623616693890263722 --mojo-platform-channel-handle=4228 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,5912641843274199931,12169101080813121324,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=18250885008675410321 --mojo-platform-channel-handle=2016 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1124 | "C:\Users\admin\AppData\Local\Temp\is-HHR2C.tmp\processhacker-2.39-setup.tmp" /SL5="$110192,1874675,150016,C:\Users\admin\Downloads\processhacker-2.39-setup.exe" /SPAWNWND=$1C001A /NOTIFYWND=$1E01D4 | C:\Users\admin\AppData\Local\Temp\is-HHR2C.tmp\processhacker-2.39-setup.tmp | processhacker-2.39-setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,5912641843274199931,12169101080813121324,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5649446879418732784 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,5912641843274199931,12169101080813121324,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14518654899374172552 --mojo-platform-channel-handle=984 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,5912641843274199931,12169101080813121324,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12343292219960055423 --mojo-platform-channel-handle=3896 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Process Hacker 2\ProcessHacker.exe" | C:\Program Files\Process Hacker 2\ProcessHacker.exe | processhacker-2.39-setup.tmp | ||||||||||||
User: admin Company: wj32 Integrity Level: MEDIUM Description: Process Hacker Exit code: 0 Version: 2.39.0.124 Modules
| |||||||||||||||
Total events
2 359
Read events
2 155
Write events
194
Delete events
10
Modification events
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2208-13245916359573750 |
Value: 259 | |||
Executable files
24
Suspicious files
79
Text files
102
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F7413C7-8A0.pma | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4f22545f-5661-4e38-a4a0-d6506cfcab08.tmp | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF3b76c7.TMP | text | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF3b7669.TMP | text | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
103
DNS requests
71
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3232 | chrome.exe | GET | 200 | 104.17.167.186:80 | http://6.adsco.re/ | US | — | — | whitelisted |
3232 | chrome.exe | GET | — | 162.252.214.5:80 | http://adsco.re/p | US | — | — | whitelisted |
3232 | chrome.exe | GET | 200 | 216.58.212.174:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 798 b | whitelisted |
3232 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/images/icons/svg_light/icons_sprite.svg | US | image | 8.28 Kb | shared |
3232 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/file/i0hl83myi4z7sdy/ssfn_gfnRUN2.bat/file | US | html | 80.7 Kb | shared |
3232 | chrome.exe | POST | 200 | 37.252.173.38:80 | http://ib.adnxs.com/ut/v3/prebid | unknown | text | 239 b | whitelisted |
3232 | chrome.exe | GET | 200 | 104.17.166.186:80 | http://c.adsco.re/ | US | html | 12.7 Kb | whitelisted |
3232 | chrome.exe | POST | 200 | 37.252.173.38:80 | http://ib.adnxs.com/ut/v3/prebid | unknown | text | 505 b | whitelisted |
3232 | chrome.exe | POST | 200 | 162.252.214.5:80 | http://adsco.re/p | US | text | 132 b | whitelisted |
3232 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/js/prebid2.44.1.js | US | text | 52.9 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3232 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3232 | chrome.exe | 104.16.203.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3232 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3232 | chrome.exe | 216.58.207.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3232 | chrome.exe | 104.111.245.249:443 | c.aaxads.com | Akamai International B.V. | NL | whitelisted |
3232 | chrome.exe | 172.217.16.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3232 | chrome.exe | 172.217.18.162:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
— | — | 216.58.212.174:80 | translate.google.com | Google Inc. | US | whitelisted |
— | — | 104.16.203.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3232 | chrome.exe | 216.58.212.174:443 | translate.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
c.aaxads.com |
| whitelisted |
static.mediafire.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3232 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3232 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |