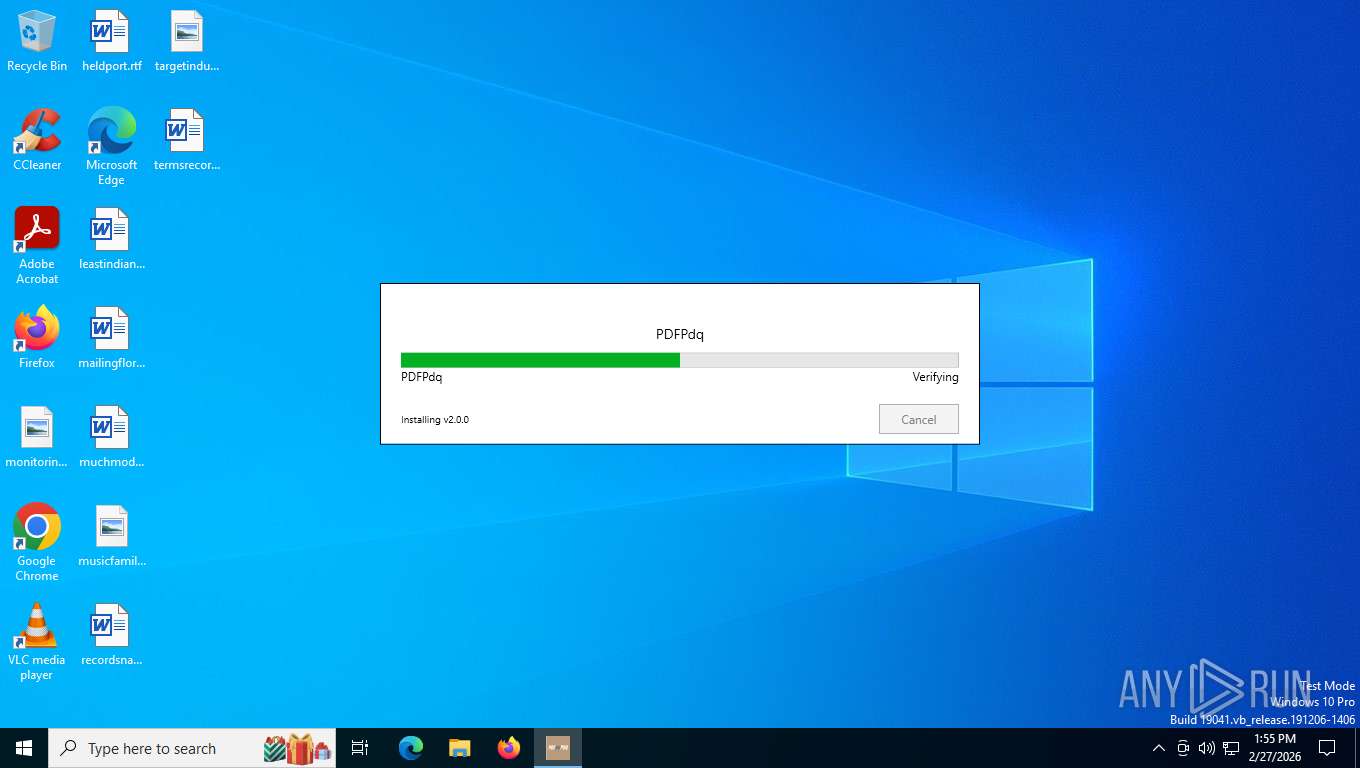
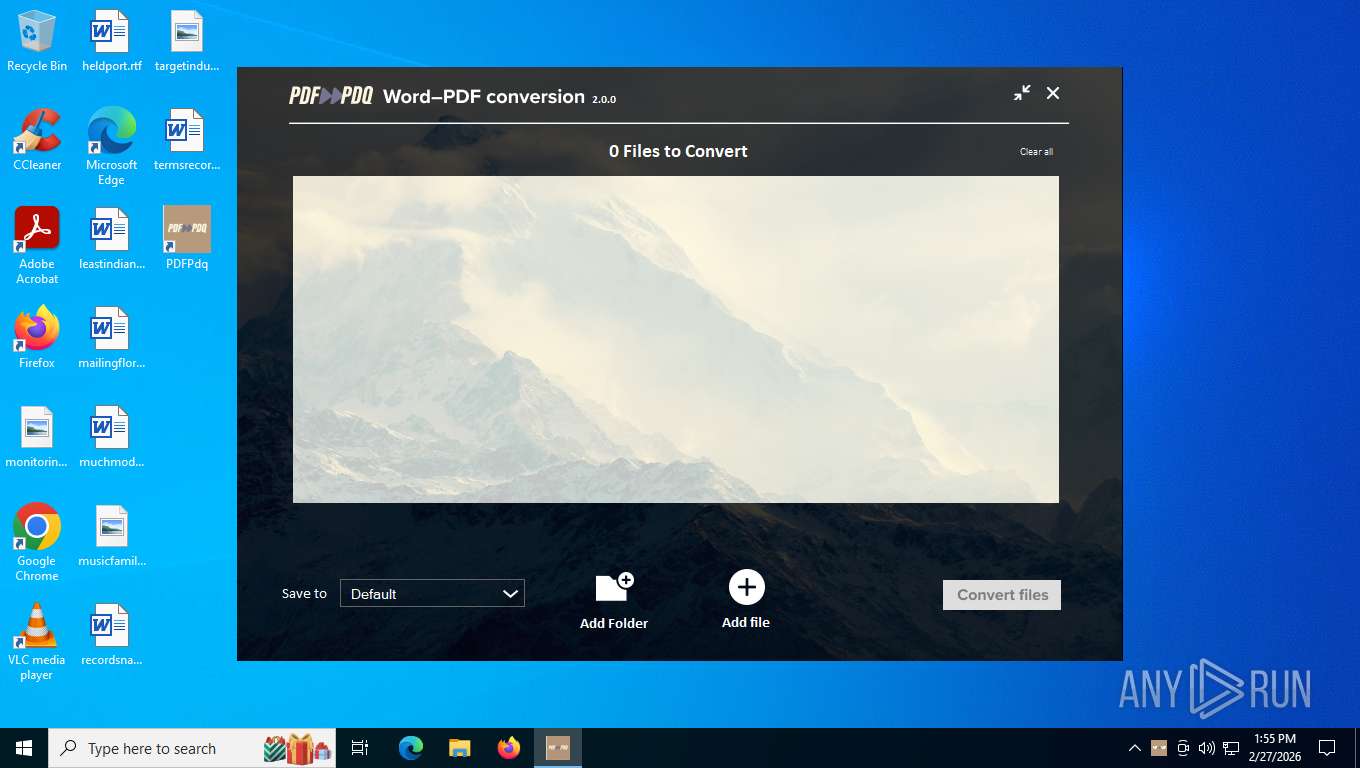
| File name: | PDFPdq.exe |
| Full analysis: | https://app.any.run/tasks/042fac92-668e-457d-a5db-b426d27700cd |
| Verdict: | Malicious activity |
| Analysis date: | February 27, 2026, 18:55:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | 761FC3F5F44FE8E76749EB5A077D0C51 |
| SHA1: | A8F75C022CCFDC5EF0B826F260005993F63A4649 |
| SHA256: | 349B076871225038696D6DDAA30E7F672BE1A92B03256487F1C4CBBAF04131B3 |
| SSDEEP: | 98304:HLycx2D4P+dOTfw9XxdyvU5tqdFMNxU4HcczIYAD0bQ3uvnrs5Nh+9avuPlKCzr3:M22vyLtVKBCz6HTHOSYyKki8 |
MALICIOUS
Executing a file with an untrusted certificate
- PDFPdq.exe (PID: 8060)
- PDFPdq.exe (PID: 1732)
Changes the autorun value in the registry
- PDFPdq.exe (PID: 1732)
SUSPICIOUS
Executable content was dropped or overwritten
- PDFPdq.exe (PID: 8060)
- PDFPdq.exe (PID: 1732)
- rundll32.exe (PID: 2336)
- rundll32.exe (PID: 4624)
- rundll32.exe (PID: 5608)
- rundll32.exe (PID: 5536)
The process creates files with name similar to system file names
- PDFPdq.exe (PID: 1732)
Searches for installed software
- PDFPdq.exe (PID: 1732)
Uses RUNDLL32.EXE to run a file without a DLL extension
- rundll32.exe (PID: 2336)
- rundll32.exe (PID: 4624)
- rundll32.exe (PID: 5608)
- rundll32.exe (PID: 5536)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5752)
INFO
Create files in a temporary directory
- PDFPdq.exe (PID: 8060)
- PDFPdq.exe (PID: 1732)
- rundll32.exe (PID: 4624)
- rundll32.exe (PID: 5608)
- rundll32.exe (PID: 2336)
- rundll32.exe (PID: 5536)
Checks supported languages
- PDFPdq.exe (PID: 8060)
- PDFPdq.exe (PID: 1732)
- msiexec.exe (PID: 5752)
- msiexec.exe (PID: 8732)
- PDFPdq.exe (PID: 6068)
The sample compiled with english language support
- PDFPdq.exe (PID: 8060)
- PDFPdq.exe (PID: 1732)
Reads the computer name
- PDFPdq.exe (PID: 1732)
- msiexec.exe (PID: 8732)
- msiexec.exe (PID: 5752)
- PDFPdq.exe (PID: 6068)
Reads the machine GUID from the registry
- PDFPdq.exe (PID: 1732)
- PDFPdq.exe (PID: 6068)
Reads security settings of Internet Explorer
- PDFPdq.exe (PID: 1732)
- PDFPdq.exe (PID: 6068)
Creates files or folders in the user directory
- PDFPdq.exe (PID: 1732)
- PDFPdq.exe (PID: 6068)
- msiexec.exe (PID: 5752)
Creates a software uninstall entry
- PDFPdq.exe (PID: 1732)
- msiexec.exe (PID: 5752)
Launching a file from a Registry key
- PDFPdq.exe (PID: 1732)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5752)
Disables trace logs
- rundll32.exe (PID: 2336)
- rundll32.exe (PID: 5608)
Checks proxy server information
- rundll32.exe (PID: 2336)
- rundll32.exe (PID: 5608)
- slui.exe (PID: 6200)
Manual execution by a user
- PDFPdq.exe (PID: 6068)
Creates files in the program directory
- PDFPdq.exe (PID: 6068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:22 22:06:13+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.38 |
| CodeSize: | 443392 |
| InitializedDataSize: | 252928 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x48650 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| CompanyName: | PDFPdq |
| FileDescription: | PDFPdq |
| FileVersion: | 2.0.0 |
| InternalName: | burn |
| OriginalFileName: | PDFPdq.exe |
| ProductName: | PDFPdq |
| ProductVersion: | 2.0.0 |
| LegalCopyright: | Copyright (c) PDFPdq. All rights reserved. |
Total processes
159
Monitored processes
10
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1732 | "C:\Users\admin\AppData\Local\Temp\{A36F5A29-3B0F-4F26-A46A-B5FAE258F7FB}\.cr\PDFPdq.exe" -burn.clean.room="C:\Users\admin\Downloads\PDFPdq.exe" -burn.filehandle.attached=656 -burn.filehandle.self=684 | C:\Users\admin\AppData\Local\Temp\{A36F5A29-3B0F-4F26-A46A-B5FAE258F7FB}\.cr\PDFPdq.exe | PDFPdq.exe | ||||||||||||
User: admin Company: PDFPdq Integrity Level: MEDIUM Description: PDFPdq Exit code: 0 Version: 2.0.0 Modules
| |||||||||||||||
| 2336 | rundll32.exe "C:\WINDOWS\Installer\MSI5F06.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1990484 2 RequestSender!RequestSender.CustomActions.Start | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4624 | rundll32.exe "C:\WINDOWS\Installer\MSI62EF.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1991437 6 RequestSender!RequestSender.CustomActions.CreateScheduledTask | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5536 | rundll32.exe "C:\WINDOWS\Installer\MSI694B.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1993062 14 RequestSender!RequestSender.CustomActions.OpenUrl | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5608 | rundll32.exe "C:\WINDOWS\Installer\MSI6487.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1991828 10 RequestSender!RequestSender.CustomActions.Finish | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5752 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6068 | "C:\Users\admin\AppData\Roaming\PDFPdq\PDFPdq.exe" | C:\Users\admin\AppData\Roaming\PDFPdq\PDFPdq.exe | — | explorer.exe | |||||||||||
User: admin Company: PDFPdq Integrity Level: MEDIUM Description: PDFPdq Version: 1.0.0.0 Modules
| |||||||||||||||
| 6200 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8060 | "C:\Users\admin\Downloads\PDFPdq.exe" | C:\Users\admin\Downloads\PDFPdq.exe | explorer.exe | ||||||||||||
User: admin Company: PDFPdq Integrity Level: MEDIUM Description: PDFPdq Exit code: 0 Version: 2.0.0 Modules
| |||||||||||||||
| 8732 | C:\Windows\syswow64\MsiExec.exe -Embedding 28EEA7966910D8D33ECDCA10AD456AB8 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 522
Read events
13 338
Write events
168
Delete events
16
Modification events
| (PID) Process: | (5752) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 78160000E4A01DA11AA8DC01 | |||
| (PID) Process: | (5752) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 7AF1BBA8242BB4454ED7F0917FDC4ED40F2140E77EE5770F7EEA84055D888262 | |||
| (PID) Process: | (5752) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1732) PDFPdq.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{671EE361-7BD3-4D03-9ADC-F5B08C67E7EC} |
| Operation: | write | Name: | BundleCachePath |
Value: C:\Users\admin\AppData\Local\Package Cache\{671EE361-7BD3-4D03-9ADC-F5B08C67E7EC}\PDFPdq.exe | |||
| (PID) Process: | (1732) PDFPdq.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{671EE361-7BD3-4D03-9ADC-F5B08C67E7EC} |
| Operation: | write | Name: | BundleUpgradeCode |
Value: {3E193566-79CA-40D6-B31D-A1DF54C146B6} | |||
| (PID) Process: | (1732) PDFPdq.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{671EE361-7BD3-4D03-9ADC-F5B08C67E7EC} |
| Operation: | write | Name: | BundleAddonCode |
Value: | |||
| (PID) Process: | (1732) PDFPdq.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{671EE361-7BD3-4D03-9ADC-F5B08C67E7EC} |
| Operation: | write | Name: | BundleDetectCode |
Value: | |||
| (PID) Process: | (1732) PDFPdq.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{671EE361-7BD3-4D03-9ADC-F5B08C67E7EC} |
| Operation: | write | Name: | BundlePatchCode |
Value: | |||
| (PID) Process: | (1732) PDFPdq.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{671EE361-7BD3-4D03-9ADC-F5B08C67E7EC} |
| Operation: | write | Name: | BundleVersion |
Value: 2.0.0 | |||
| (PID) Process: | (1732) PDFPdq.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{671EE361-7BD3-4D03-9ADC-F5B08C67E7EC} |
| Operation: | write | Name: | VersionMajor |
Value: 2 | |||
Executable files
51
Suspicious files
20
Text files
40
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8060 | PDFPdq.exe | C:\Users\admin\AppData\Local\Temp\{A36F5A29-3B0F-4F26-A46A-B5FAE258F7FB}\.cr\PDFPdq.exe | executable | |
MD5:B45961E54553910AB1102E78153F33D6 | SHA256:9B8CD8E321470C92C71AC98FD6280D9253A2829E7BD9903608E23A0C37A503E4 | |||
| 1732 | PDFPdq.exe | C:\Users\admin\AppData\Local\Temp\{79B03F2E-0193-476D-8679-CC9E63B28F22}\.ba\mbanative.dll | executable | |
MD5:5441EC98C2136783BB902259B6CDD647 | SHA256:659FF12D11D77A18962D25292FED64CDC94A1BD99470F7E17111CE57EFCCA83E | |||
| 1732 | PDFPdq.exe | C:\Users\admin\AppData\Local\Temp\{79B03F2E-0193-476D-8679-CC9E63B28F22}\.ba\mbapreq.wxl | text | |
MD5:065D124A9E34C797DC659A9E45112C28 | SHA256:F93E649641239FFACEBC76258F1686730931091D6488F4316F9A2358D8C9B29C | |||
| 1732 | PDFPdq.exe | C:\Users\admin\AppData\Local\Temp\{79B03F2E-0193-476D-8679-CC9E63B28F22}\.ba\1030\mbapreq.wxl | text | |
MD5:51D7E4F9374FC66C4BF16B603126A574 | SHA256:580567035D7993F1CD9874A6199A1E842D0F29A7A935BDC402AF5EDAC6F37A55 | |||
| 1732 | PDFPdq.exe | C:\Users\admin\AppData\Local\Temp\{79B03F2E-0193-476D-8679-CC9E63B28F22}\.ba\1028\mbapreq.wxl | text | |
MD5:6CFA1150F69B6815C7E20052C29093FE | SHA256:623D6CB1067C3340326579A2DC7456BB09F894259E029E3DC4D880CC032B3FED | |||
| 1732 | PDFPdq.exe | C:\Users\admin\AppData\Local\Temp\{79B03F2E-0193-476D-8679-CC9E63B28F22}\.ba\1035\mbapreq.wxl | text | |
MD5:6A4F5B0316A2290E5BBE4ADAF53D19F3 | SHA256:78DB48FB9835E4557D47915D7AF57A56F6CA62074612867A2BA8DD7BC7834331 | |||
| 1732 | PDFPdq.exe | C:\Users\admin\AppData\Local\Temp\{79B03F2E-0193-476D-8679-CC9E63B28F22}\.ba\Bootstrapper.dll | executable | |
MD5:7ED402760E9BCCA43A7C00D217824B9E | SHA256:9D19E14E83FAC5D65061E37D4F08A10567C3CE7FD067F065362DC214BD455CBE | |||
| 1732 | PDFPdq.exe | C:\Users\admin\AppData\Local\Temp\{79B03F2E-0193-476D-8679-CC9E63B28F22}\.ba\mbahost.dll | executable | |
MD5:013033CFFC1F318DF1D5048BA40A31DF | SHA256:B43F1B674894E2997AAE9DB0C5B5C95D2A14010E9AB95F63E2908E381768A148 | |||
| 1732 | PDFPdq.exe | C:\Users\admin\AppData\Local\Temp\{79B03F2E-0193-476D-8679-CC9E63B28F22}\.ba\WixToolset.Mba.Core.dll | executable | |
MD5:EC393B51456EE6AE6C3FA9BD840EC783 | SHA256:2FDFD86CA4BA705AAE263E59CEF29A0FA8D251E4B288E5713EADD2E1D2681812 | |||
| 1732 | PDFPdq.exe | C:\Users\admin\AppData\Local\Temp\{79B03F2E-0193-476D-8679-CC9E63B28F22}\.ba\mbapreq.thm | xml | |
MD5:CC80C7B334DEE4C354BFC3F1B55206C6 | SHA256:6A5201727416260B662F8AEEA2D98EF111AED66C1838A44CE5E0E86334BAAFE0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
34
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2336 | rundll32.exe | GET | 200 | 185.111.111.158:443 | https://c.pdf-pdq.com/start | GB | — | — | unknown |
5608 | rundll32.exe | GET | 200 | 185.111.111.158:443 | https://c.pdf-pdq.com/finish | GB | — | — | unknown |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
6320 | svchost.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
8548 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
8548 | SIHClient.exe | GET | 200 | 74.179.77.164:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
8548 | SIHClient.exe | GET | 200 | 135.232.92.137:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
8548 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
8548 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | US | binary | 419 b | whitelisted |
3292 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7304 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6320 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
2336 | rundll32.exe | 185.111.111.158:443 | c.pdf-pdq.com | CDNEXT | GB | whitelisted |
5608 | rundll32.exe | 185.111.111.158:443 | c.pdf-pdq.com | CDNEXT | GB | whitelisted |
356 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
356 | svchost.exe | 172.66.2.5:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
c.pdf-pdq.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |