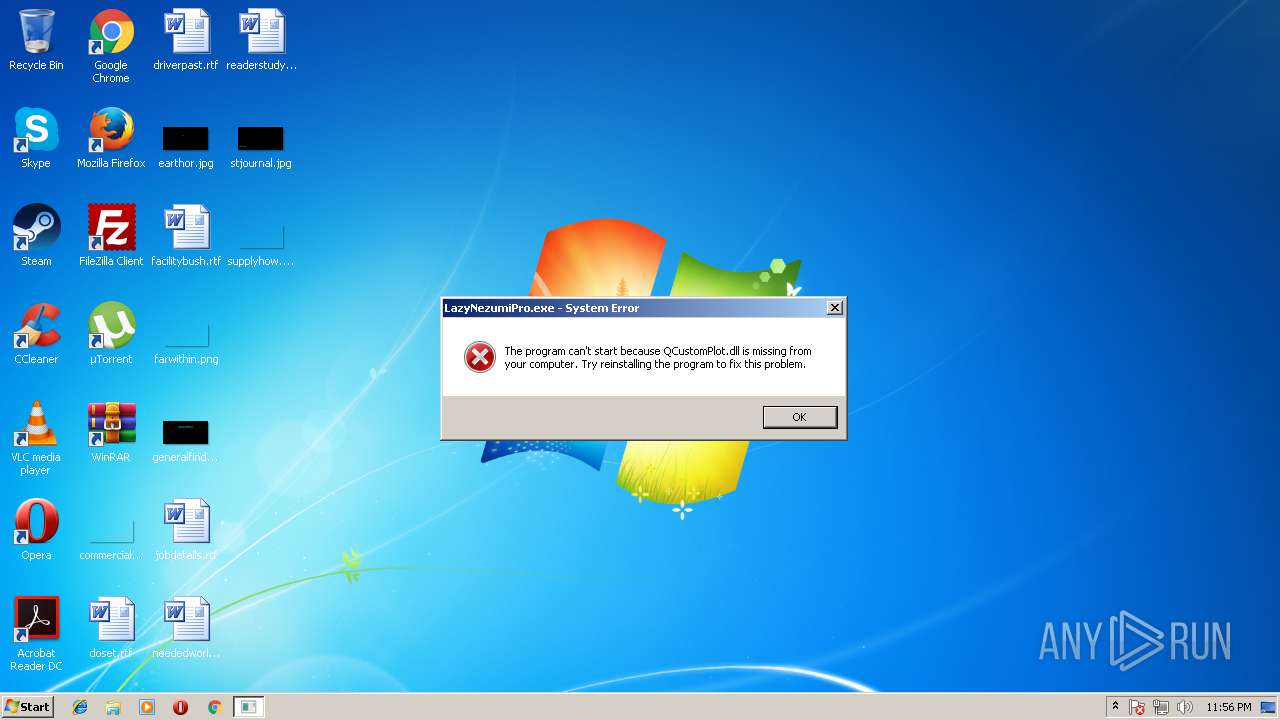
| File name: | LazyNezumiPro.exe |
| Full analysis: | https://app.any.run/tasks/33ed97d2-82f3-4f53-ae9a-2e5343b2c0d9 |
| Verdict: | No threats detected |
| Analysis date: | August 14, 2018, 22:56:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CC25981AE3DC991BD3BEAE4574833D0E |
| SHA1: | FE1EB50304D1C9FE8882B23232F4A076CD75D206 |
| SHA256: | 3490E25A537A8121E6A1F6F5AF1C78512980ACF00D52D4D3E802C63D8CCE1748 |
| SSDEEP: | 24576:FuvMWObngdcdhaS8tLWFYtfUquFCCmWDQE4NSDjB:4tIngdcGS8t6WfUqvCZQE4NSD9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2932)
- WINWORD.EXE (PID: 1640)
- WINWORD.EXE (PID: 2836)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2836)
- WINWORD.EXE (PID: 1640)
- WINWORD.EXE (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:07:03 23:41:23+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 656896 |
| InitializedDataSize: | 541696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x90fb0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 15.7.3.1740 |
| ProductVersionNumber: | 15.7.3.1740 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Guillaume Stordeur |
| FileDescription: | Lazy Nezumi Main Application |
| LegalCopyright: | Copyright (C) 2009-2015 Guillaume Stordeur |
| FileVersion: | 15.7.3.1740 |
| ProductVersion: | 15.7.3.1740 |
| ProductName: | Lazy Nezumi Pro |
| InternalName: | LazyNezumiPro.exe |
| OriginalFileName: | LazyNezumiPro.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jul-2015 21:41:23 |
| Detected languages: |
|
| CompanyName: | Guillaume Stordeur |
| FileDescription: | Lazy Nezumi Main Application |
| LegalCopyright: | Copyright (C) 2009-2015 Guillaume Stordeur |
| FileVersion: | 15.7.3.1740 |
| ProductVersion: | 15.7.3.1740 |
| ProductName: | Lazy Nezumi Pro |
| InternalName: | LazyNezumiPro.exe |
| OriginalFilename: | LazyNezumiPro.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Jul-2015 21:41:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000A0449 | 0x000A0600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.25324 |
.rdata | 0x000A2000 | 0x00069624 | 0x00069800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.7095 |
.data | 0x0010C000 | 0x00003A04 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.63274 |
.rsrc | 0x00110000 | 0x00005F0C | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18425 |
.reloc | 0x00116000 | 0x00013256 | 0x00013400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.35332 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.01246 | 620 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.51671 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.09601 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.19252 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.95789 | 5672 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.6825 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.2295 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.62409 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
IDI_ICON1 | 2.77485 | 62 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
IDI_ICON2 | 2.74259 | 62 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSVCP100.dll |
MSVCR100.dll |
PSAPI.DLL |
QCustomPlot.dll |
QtCore4.dll |
QtGui4.dll |
QtNetwork4.dll |
Total processes
37
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
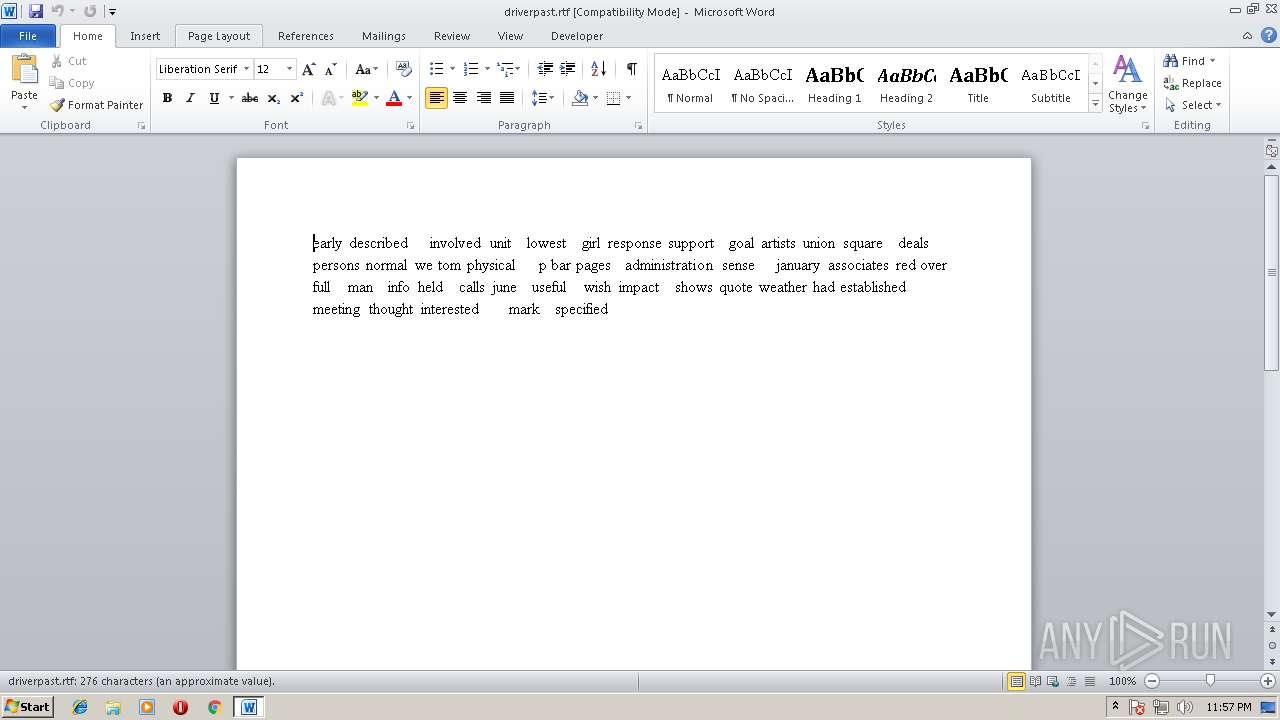
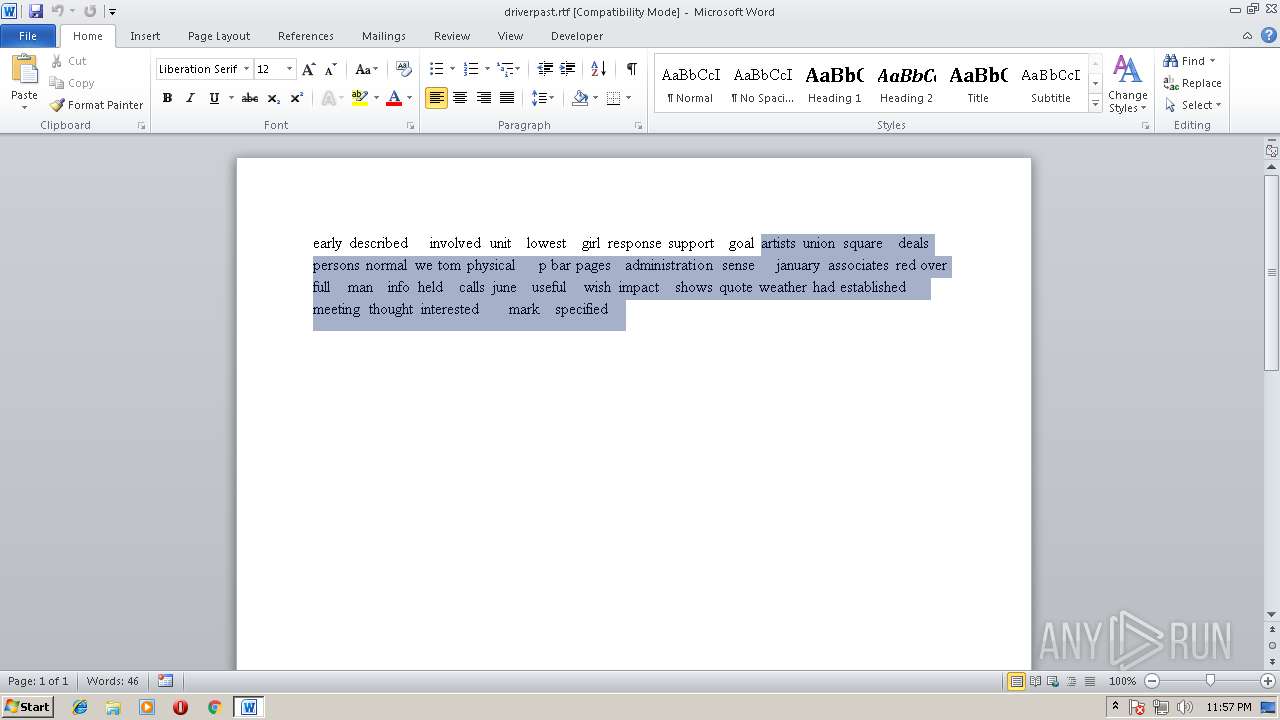
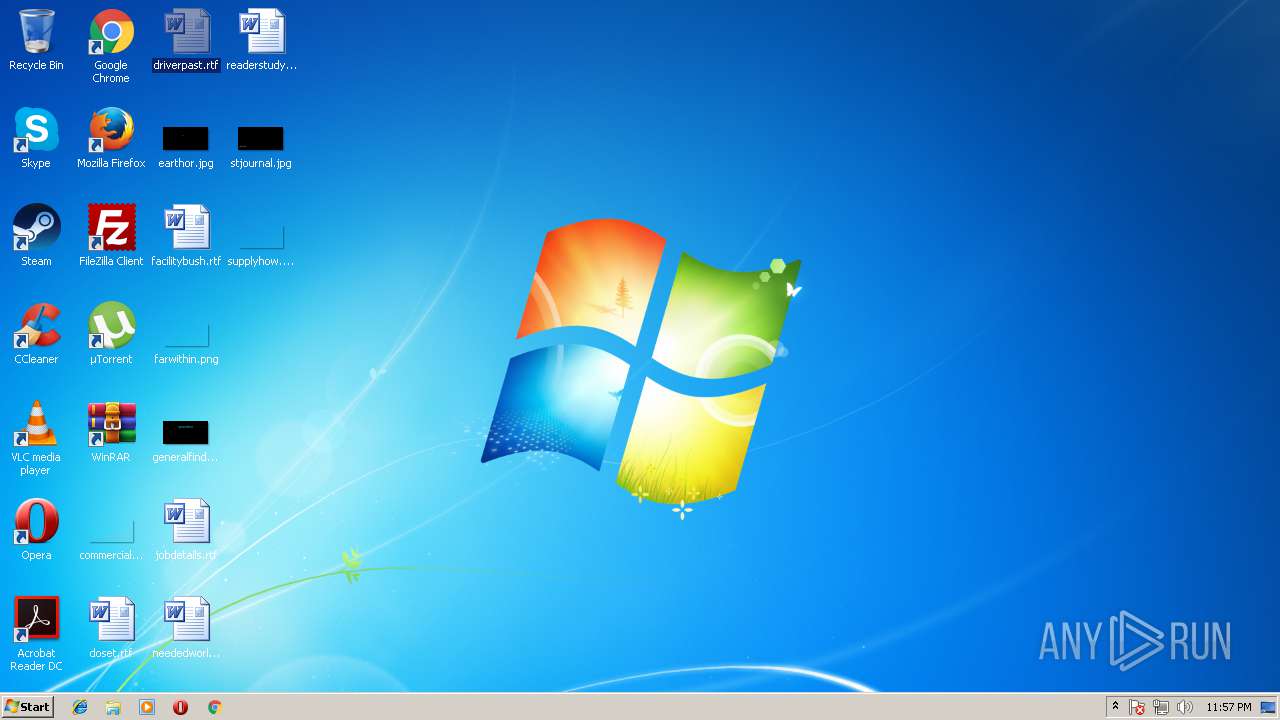
| 1640 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\driverpast.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2836 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\jobdetails.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2880 | "C:\Users\admin\AppData\Local\Temp\LazyNezumiPro.exe" | C:\Users\admin\AppData\Local\Temp\LazyNezumiPro.exe | — | explorer.exe | |||||||||||
User: admin Company: Guillaume Stordeur Integrity Level: MEDIUM Description: Lazy Nezumi Main Application Exit code: 3221225781 Version: 15.7.3.1740 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\~$iverpast.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 736
Read events
1 580
Write events
116
Delete events
40
Modification events
| (PID) Process: | (1640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | e=r |
Value: 653D720068060000010000000000000000000000 | |||
| (PID) Process: | (1640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1640) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1292763158 | |||
| (PID) Process: | (1640) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1292763240 | |||
| (PID) Process: | (1640) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1292763241 | |||
| (PID) Process: | (1640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | FontInfoCacheW |
Value: 6000000060000000F5FFFFFF000000000000000000000000BC02000000000000004000225400610068006F006D006100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000D0000000B000000020000000200000000000000060000001A000000BC0200000000000060000000600000002000FDFF1F0020000000002700000000FF2E00E15B6000C0290000000000000001000000000028200700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000D0000000B0000000200000002000000000000000500000017000000900100000000000060000000600000002000FDFF1F0020000000002700000000FF2E00E15B6000C02900000000000000010000000000282006000000F7FFFFFF0000000000000000000000009001000000000000004000225400610068006F006D006100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000B000000090000000200000002000000000000000400000013000000900100000000000060000000600000002000FDFF1F0020000000002700000000FF2E00E15B6000C02900000000000000010000000000282005000000 | |||
| (PID) Process: | (1640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 680600004AD386202234D40100000000 | |||
| (PID) Process: | (1640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | o>r |
Value: 6F3E72006806000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1640) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | o>r |
Value: 6F3E72006806000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
Executable files
0
Suspicious files
0
Text files
6
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1640 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB565.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1640 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{2C18871F-929B-47A0-BEEF-B9638C1F1B0A}.tmp | — | |
MD5:— | SHA256:— | |||
| 1640 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{5F59267F-77C2-4CF0-83A1-F391C13089CA}.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE54F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{D37725D5-D429-43D5-BF59-DE176561FABF}.tmp | — | |
MD5:— | SHA256:— | |||
| 2836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR148D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\~$iverpast.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 1640 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 1640 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\driverpast.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report