| File name: | rtcomlite.exe |
| Full analysis: | https://app.any.run/tasks/6e550c9b-3c77-4287-a2ef-c797a701dd88 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2021, 06:18:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E22801B4D476FCEE8A5C678392CFE81C |
| SHA1: | 85F72A373555AE6179EDF7DA62983ABF24CA27BF |
| SHA256: | 348F010FA5A6C89CCE724B32DE934B14D46C603FDAD5104CCE4DAFA598BE9E80 |
| SSDEEP: | 12288:ygvK6+eUwLR25hfG08sdu/JJk/843cG7mJ3DwdSry43khnyyG:LKEUwk7fdu/JJljJTI0y43my3 |
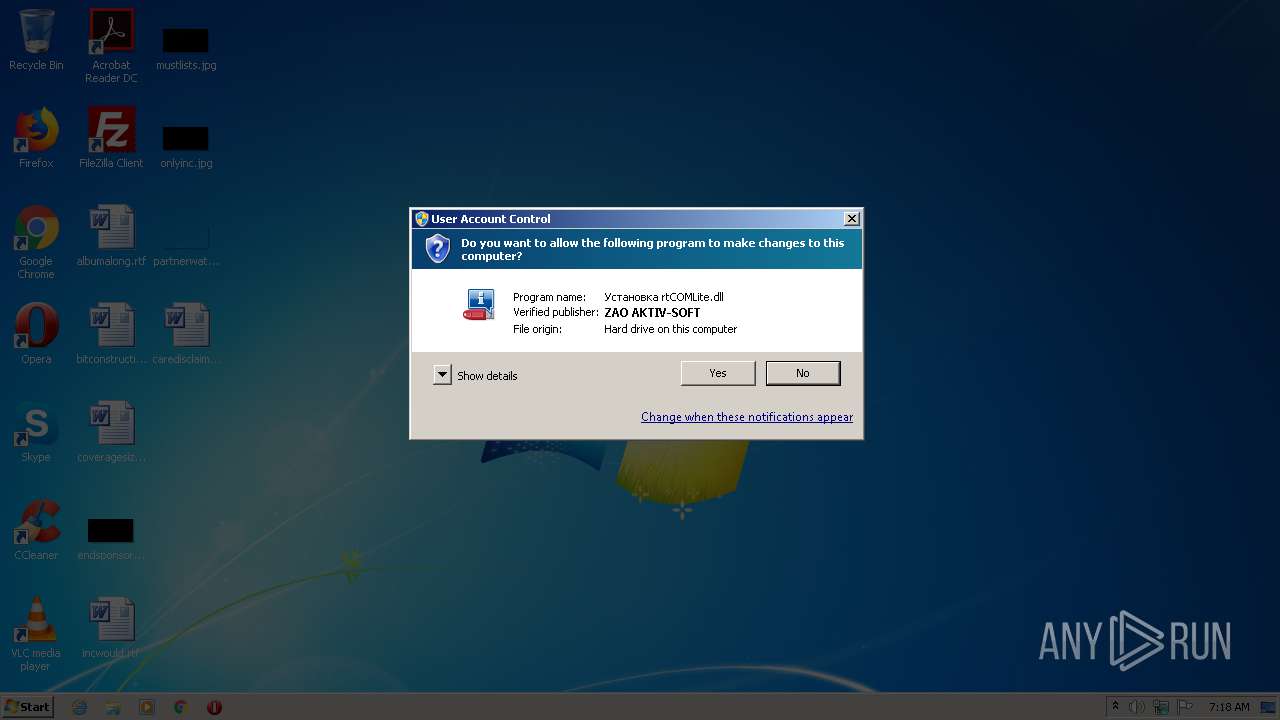
MALICIOUS
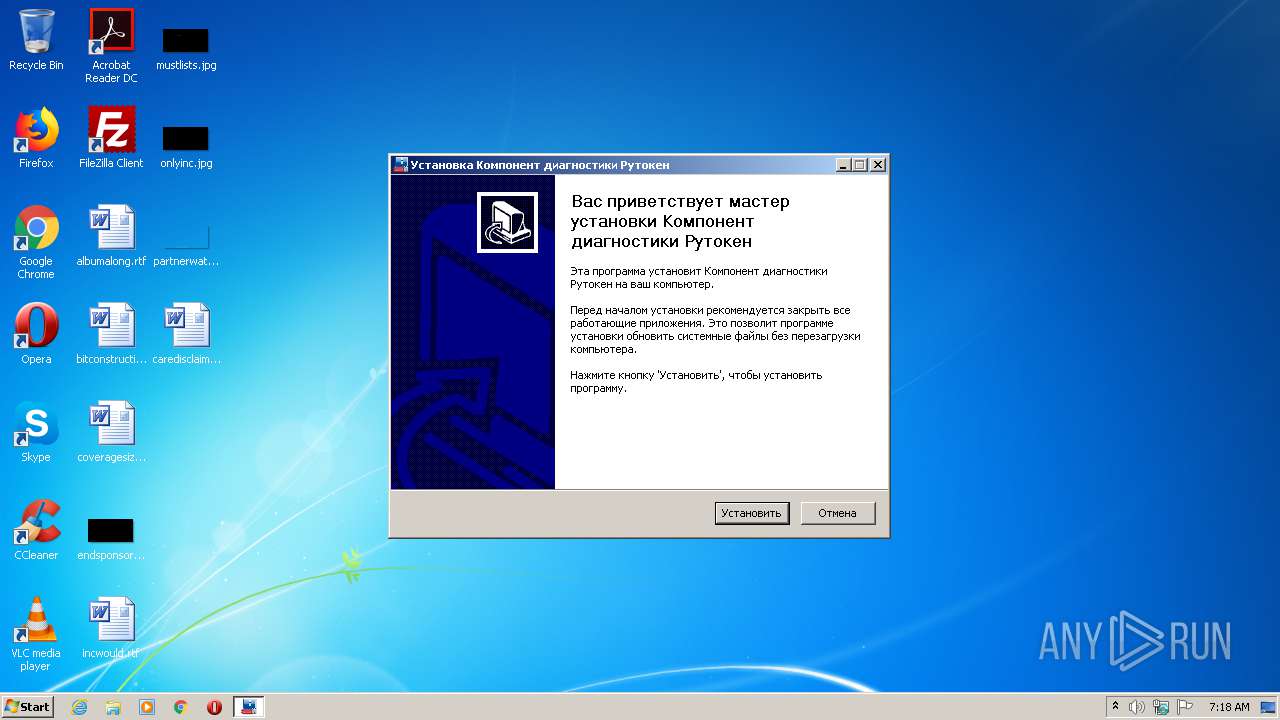
Loads dropped or rewritten executable
- rtcomlite.exe (PID: 3668)
- regsvr32.exe (PID: 2372)
Drops executable file immediately after starts
- rtcomlite.exe (PID: 3668)
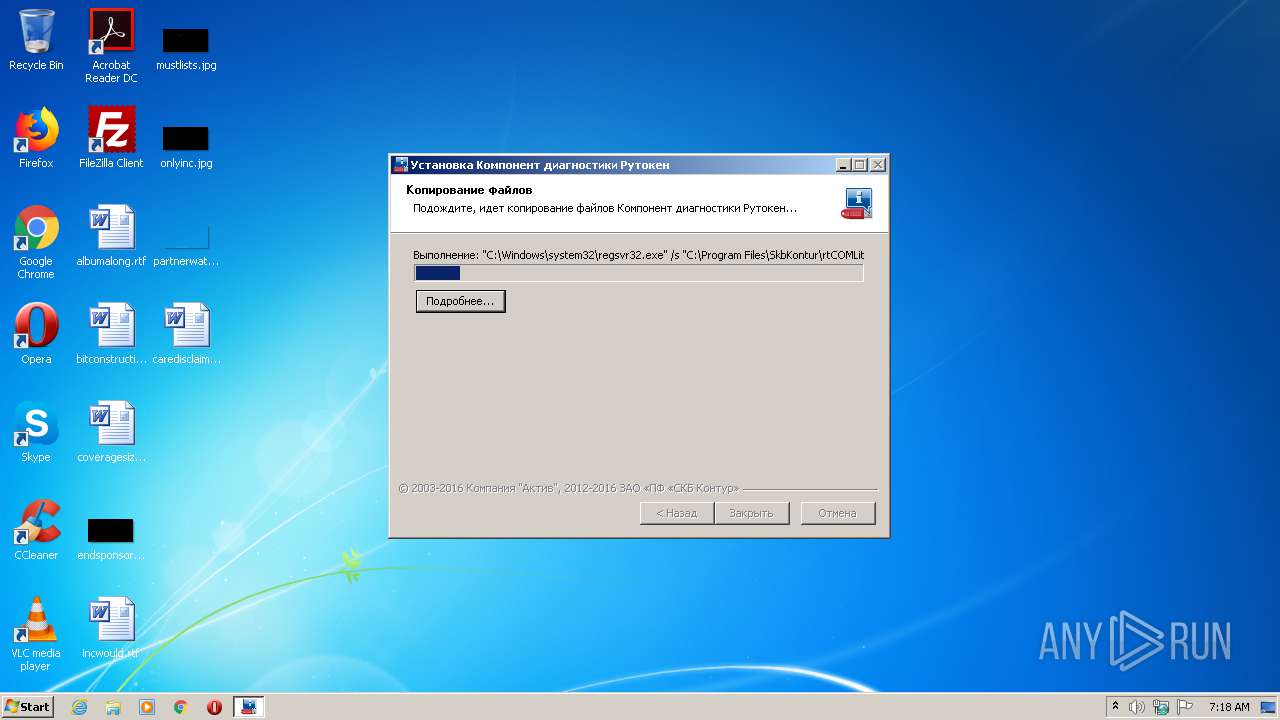
Registers / Runs the DLL via REGSVR32.EXE
- rtcomlite.exe (PID: 3668)
SUSPICIOUS
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2372)
Executable content was dropped or overwritten
- rtcomlite.exe (PID: 3668)
Creates a directory in Program Files
- rtcomlite.exe (PID: 3668)
Creates files in the program directory
- rtcomlite.exe (PID: 3668)
Creates a software uninstall entry
- rtcomlite.exe (PID: 3668)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:25 02:55:51+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 14848 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x33b6 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.3.1 |
| ProductVersionNumber: | 1.0.3.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Russian |
| CharacterSet: | Windows, Cyrillic |
| CompanyName: | Компания "Актив", ЗАО «ПФ «СКБ Контур» |
| CompanyWebsite: | https://kontur.ru/ |
| FileDescription: | - |
| FileVersion: | 1.0.3.1 |
| LegalCopyright: | © 2003-2016 Компания "Актив", 2012-2016 ЗАО «ПФ «СКБ Контур» |
| ProductName: | rtCOMLite Installer |
| ProductVersion: | 1.0.3.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jul-2016 00:55:51 |
| Detected languages: |
|
| CompanyName: | Компания "Актив", ЗАО «ПФ «СКБ Контур» |
| CompanyWebsite: | https://kontur.ru/ |
| FileDescription: | - |
| FileVersion: | 1.0.3.1 |
| LegalCopyright: | © 2003-2016 Компания "Актив", 2012-2016 ЗАО «ПФ «СКБ Контур» |
| ProductName: | rtCOMLite Installer |
| ProductVersion: | 1.0.3.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Jul-2016 00:55:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000615D | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45023 |
.rdata | 0x00008000 | 0x000013A4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.163 |
.data | 0x0000A000 | 0x00020338 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.9824 |
.ndata | 0x0002B000 | 0x00015000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00040000 | 0x00001E40 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.61959 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26716 | 1197 | Latin 1 / Western European | English - United States | RT_MANIFEST |
103 | 1.7815 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | Latin 1 / Western European | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | Latin 1 / Western European | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
43
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2372 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\SkbKontur\rtCOMLite\rtCOMLite.dll" | C:\Windows\system32\regsvr32.exe | — | rtcomlite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2404 | "C:\Users\admin\AppData\Local\Temp\rtcomlite.exe" | C:\Users\admin\AppData\Local\Temp\rtcomlite.exe | — | explorer.exe | |||||||||||
User: admin Company: Компания "Актив", ЗАО «ПФ «СКБ Контур» Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.0.3.1 Modules
| |||||||||||||||
| 3668 | "C:\Users\admin\AppData\Local\Temp\rtcomlite.exe" | C:\Users\admin\AppData\Local\Temp\rtcomlite.exe | explorer.exe | ||||||||||||
User: admin Company: Компания "Актив", ЗАО «ПФ «СКБ Контур» Integrity Level: HIGH Exit code: 0 Version: 1.0.3.1 Modules
| |||||||||||||||
Total events
416
Read events
340
Write events
76
Delete events
0
Modification events
| (PID) Process: | (2372) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{E6BC1EBE-8048-4BB0-9939-DD5582EB01DC} |
| Operation: | write | Name: | (default) |
Value: rtCOMLite | |||
| (PID) Process: | (2372) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{E6BC1EBE-8048-4BB0-9939-DD5582EB01DC} |
| Operation: | write | Name: | DllSurrogate |
Value: | |||
| (PID) Process: | (2372) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\rtCOMLite.DLL |
| Operation: | write | Name: | AppID |
Value: {E6BC1EBE-8048-4BB0-9939-DD5582EB01DC} | |||
| (PID) Process: | (2372) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\rtCOMLite.rtContext.1 |
| Operation: | write | Name: | (default) |
Value: rtContext Class | |||
| (PID) Process: | (2372) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\rtCOMLite.rtContext.1\CLSID |
| Operation: | write | Name: | (default) |
Value: {0ACACF07-54A6-4230-8FA2-6CBBE9B87BB9} | |||
| (PID) Process: | (2372) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\rtCOMLite.rtContext |
| Operation: | write | Name: | (default) |
Value: rtContext Class | |||
| (PID) Process: | (2372) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\rtCOMLite.rtContext\CLSID |
| Operation: | write | Name: | (default) |
Value: {0ACACF07-54A6-4230-8FA2-6CBBE9B87BB9} | |||
| (PID) Process: | (2372) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\rtCOMLite.rtContext\CurVer |
| Operation: | write | Name: | (default) |
Value: rtCOMLite.rtContext.1 | |||
| (PID) Process: | (2372) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{0ACACF07-54A6-4230-8FA2-6CBBE9B87BB9} |
| Operation: | write | Name: | (default) |
Value: rtContext Class | |||
| (PID) Process: | (2372) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{0ACACF07-54A6-4230-8FA2-6CBBE9B87BB9} |
| Operation: | write | Name: | AppID |
Value: {E6BC1EBE-8048-4BB0-9939-DD5582EB01DC} | |||
Executable files
6
Suspicious files
0
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3668 | rtcomlite.exe | C:\Users\admin\AppData\Local\Temp\nseAD05.tmp | — | |
MD5:— | SHA256:— | |||
| 3668 | rtcomlite.exe | C:\Users\admin\AppData\Local\Temp\nseAD06.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3668 | rtcomlite.exe | C:\Users\admin\AppData\Local\Temp\nseAD06.tmp\System.dll | executable | |
MD5:A4DD044BCD94E9B3370CCF095B31F896 | SHA256:2E226715419A5882E2E14278940EE8EF0AA648A3EF7AF5B3DC252674111962BC | |||
| 3668 | rtcomlite.exe | C:\Users\admin\AppData\Local\Temp\nseAD06.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3668 | rtcomlite.exe | C:\Users\admin\AppData\Local\Temp\nseAD06.tmp\AccessControl.dll | executable | |
MD5:F447D1CF69F64202DEBFB0BFAB148E8F | SHA256:E77DE58BA1DB34D49FF089A83A3AED68CBFF30EA54591990A60AEBD34EAB09CC | |||
| 3668 | rtcomlite.exe | C:\Users\admin\AppData\Local\Temp\nseAD06.tmp\UserInfo.dll | executable | |
MD5:B98F45A83C1D09132E1E4ADA1387A6F8 | SHA256:23661A4B1F3D6744FCDD1B2379E5E602E6CF6BD5950B2D19B844527B2F626E99 | |||
| 3668 | rtcomlite.exe | C:\Users\admin\AppData\Local\Temp\nseAD06.tmp\InstallOptions.dll | executable | |
MD5:5B3EDB39FE9C026322CAF37EA10F6733 | SHA256:A96B1C95F51B088ED5EC476485A6AA562CBE68A88D0261CE88BCB3DCA1F1C8B0 | |||
| 3668 | rtcomlite.exe | C:\Program Files\SkbKontur\rtCOMLite\rtCOMLite.dll | executable | |
MD5:21330AC3D791934A6BEBA85F794517D3 | SHA256:DE1DD54E78C2F6FA2FA872C8D3D0B74D398975FEF03EF789DE891CC8562D59E0 | |||
| 3668 | rtcomlite.exe | C:\Program Files\SkbKontur\rtCOMLite\uninstall.exe | executable | |
MD5:FD849C4B62DBCBB9C3297A9917FDEE5F | SHA256:AFC332FDEF71F4BFB770CB175B9AE39D2CF9A4107E030BF7A96577E957F28D0C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report