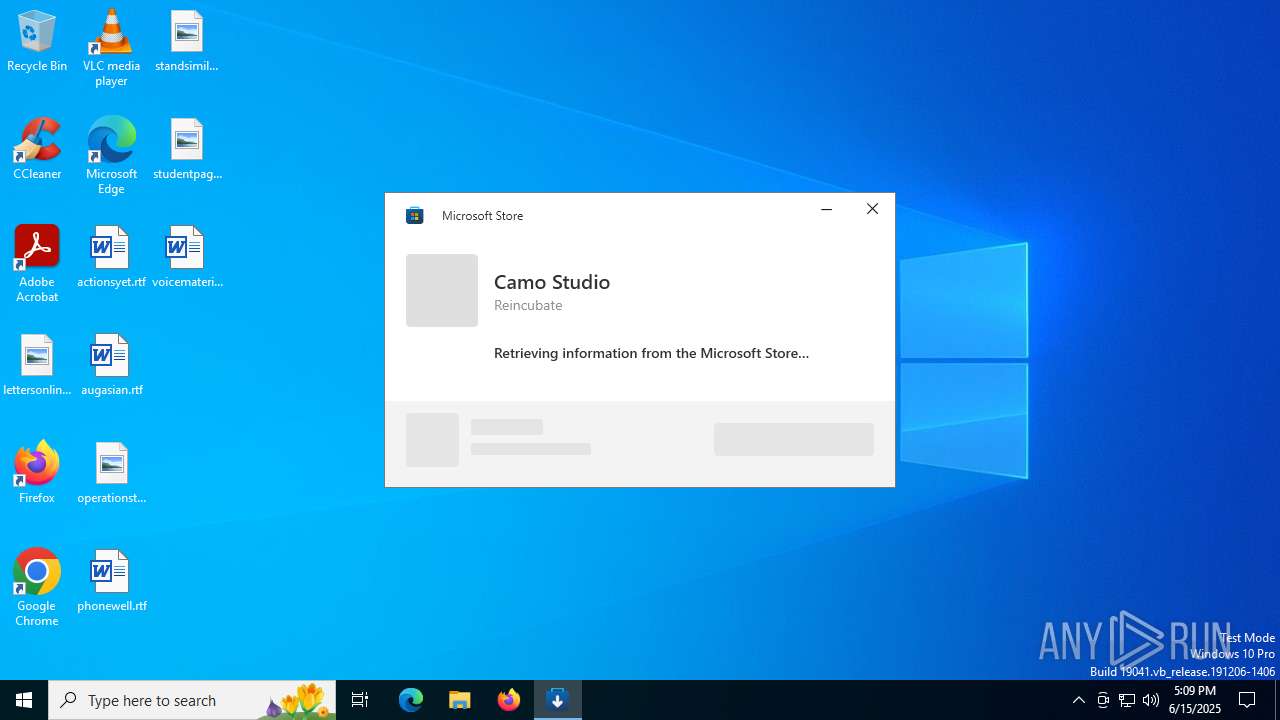
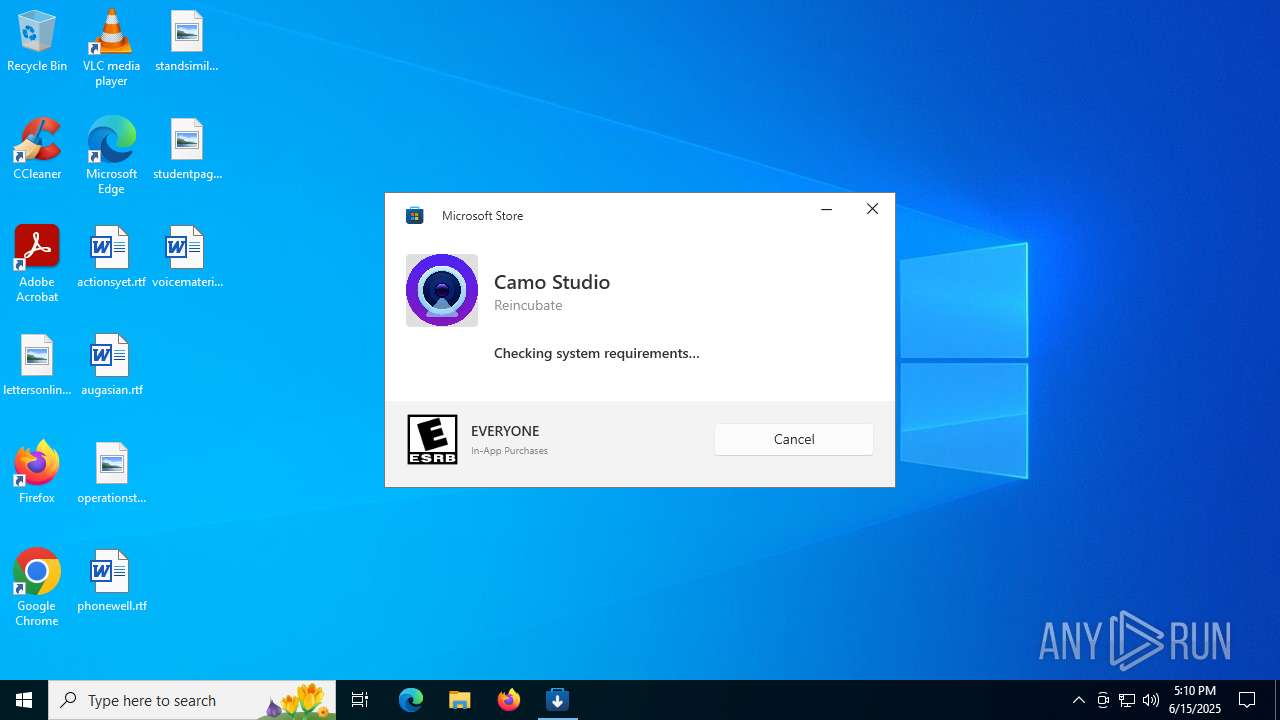
| File name: | Camo Studio Installer.exe |
| Full analysis: | https://app.any.run/tasks/209bb0e3-6e30-4d5f-8a39-5be70ff6fe5c |
| Verdict: | Malicious activity |
| Analysis date: | June 15, 2025, 17:09:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | ABA7AC2F2071724133D42076E58A393F |
| SHA1: | 3852776D8B58CF676533B2598CEBF76533990986 |
| SHA256: | 348C9446C808308435D02CDA37000067EE63360B6229EEABF0BB623B9A2BE640 |
| SSDEEP: | 12288:c2KjjWCNdtwTKtwKMpvSriaTLxAetD7lu38PKtwMVspl:xSjWCNdtw+twKM5SriaTR3hCtwMVspl |
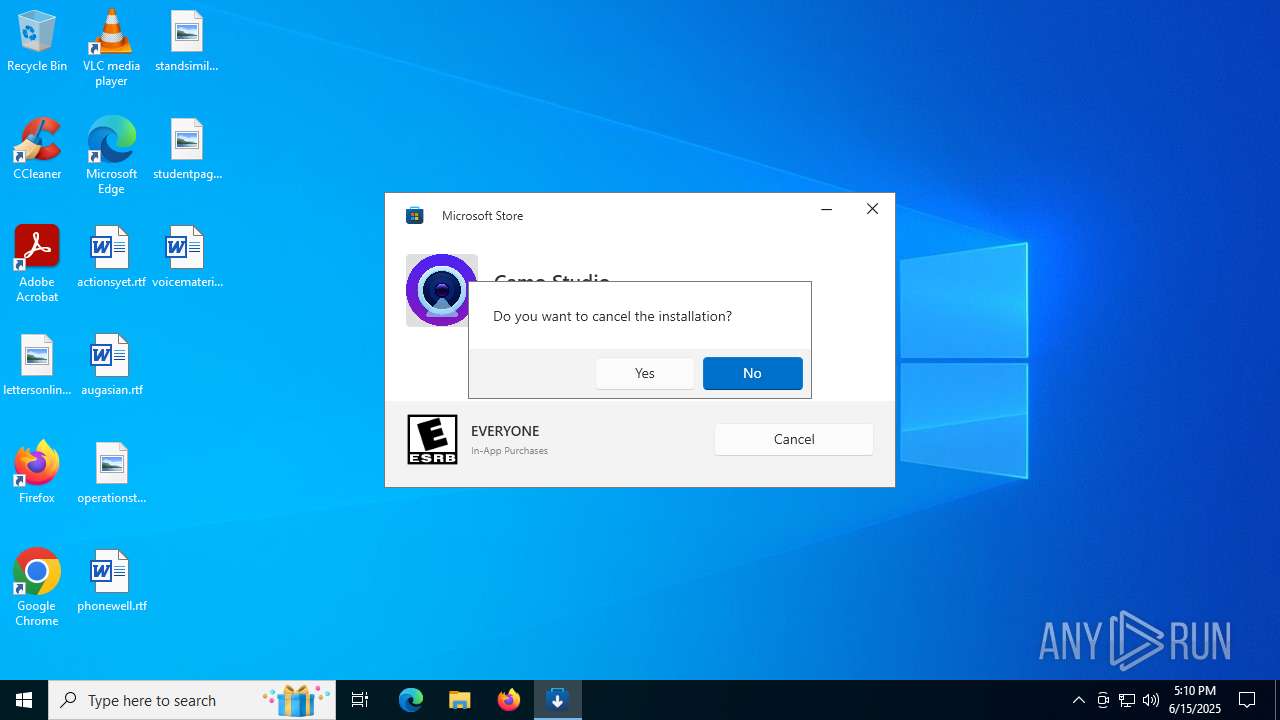
MALICIOUS
No malicious indicators.SUSPICIOUS
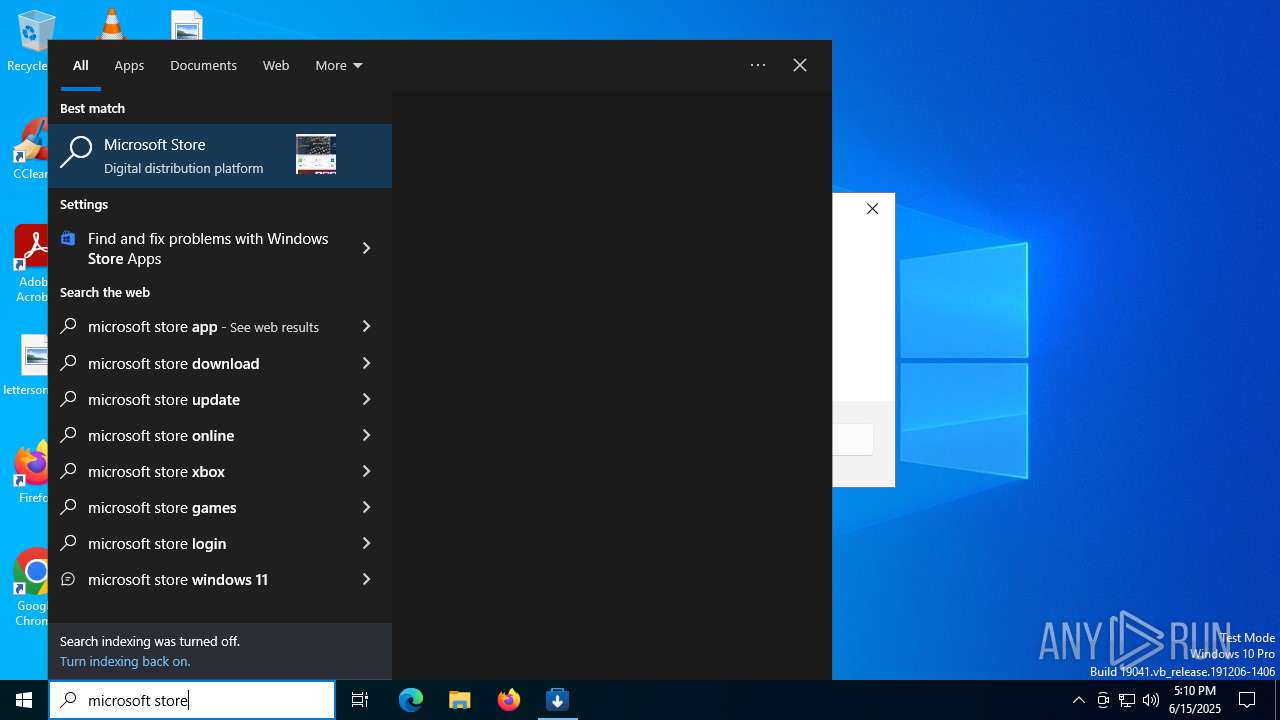
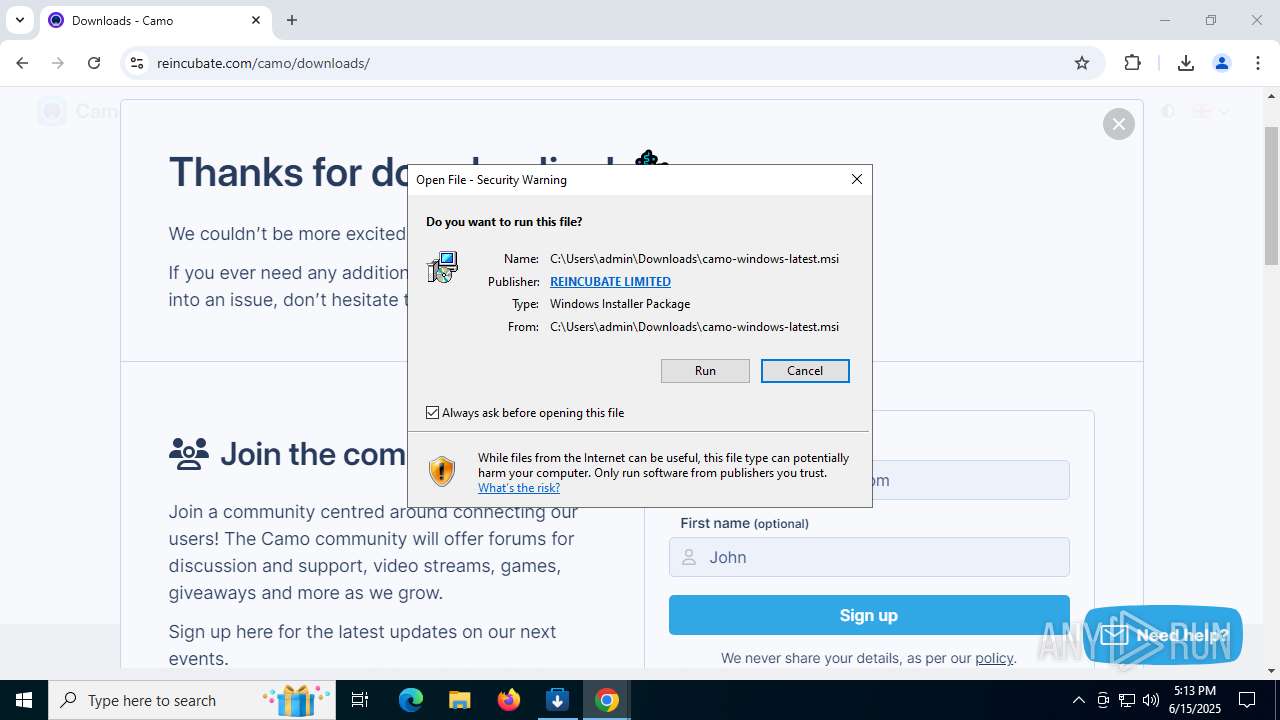
Starts a Microsoft application from unusual location
- Camo Studio Installer.exe (PID: 316)
Process drops legitimate windows executable
- Camo Studio Installer.exe (PID: 316)
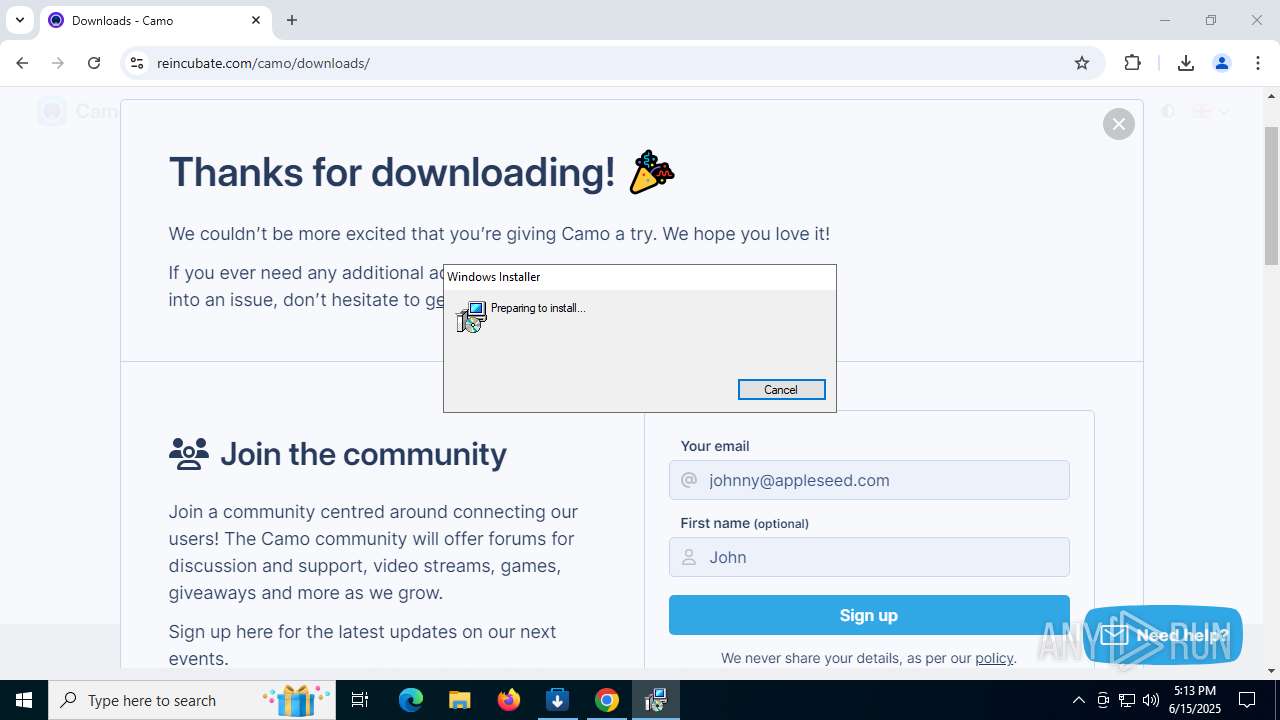
- msiexec.exe (PID: 3100)
Application launched itself
- msiexec.exe (PID: 3100)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 3100)
- drvinst.exe (PID: 6124)
- drvinst.exe (PID: 3880)
- drvinst.exe (PID: 8180)
Reads security settings of Internet Explorer
- Camo Studio Installer.exe (PID: 316)
Executable content was dropped or overwritten
- rundll32.exe (PID: 6756)
- rundll32.exe (PID: 7836)
- rundll32.exe (PID: 724)
- drvinst.exe (PID: 6124)
- drvinst.exe (PID: 3880)
- rundll32.exe (PID: 8076)
- drvinst.exe (PID: 8180)
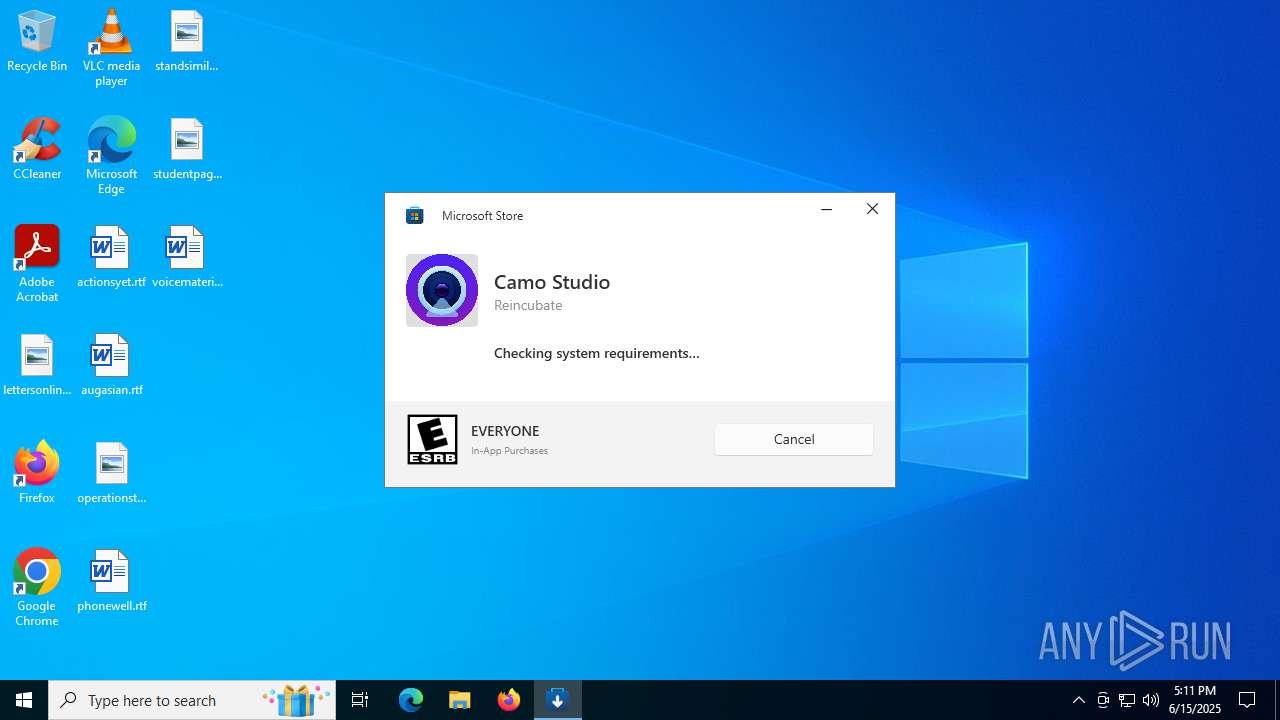
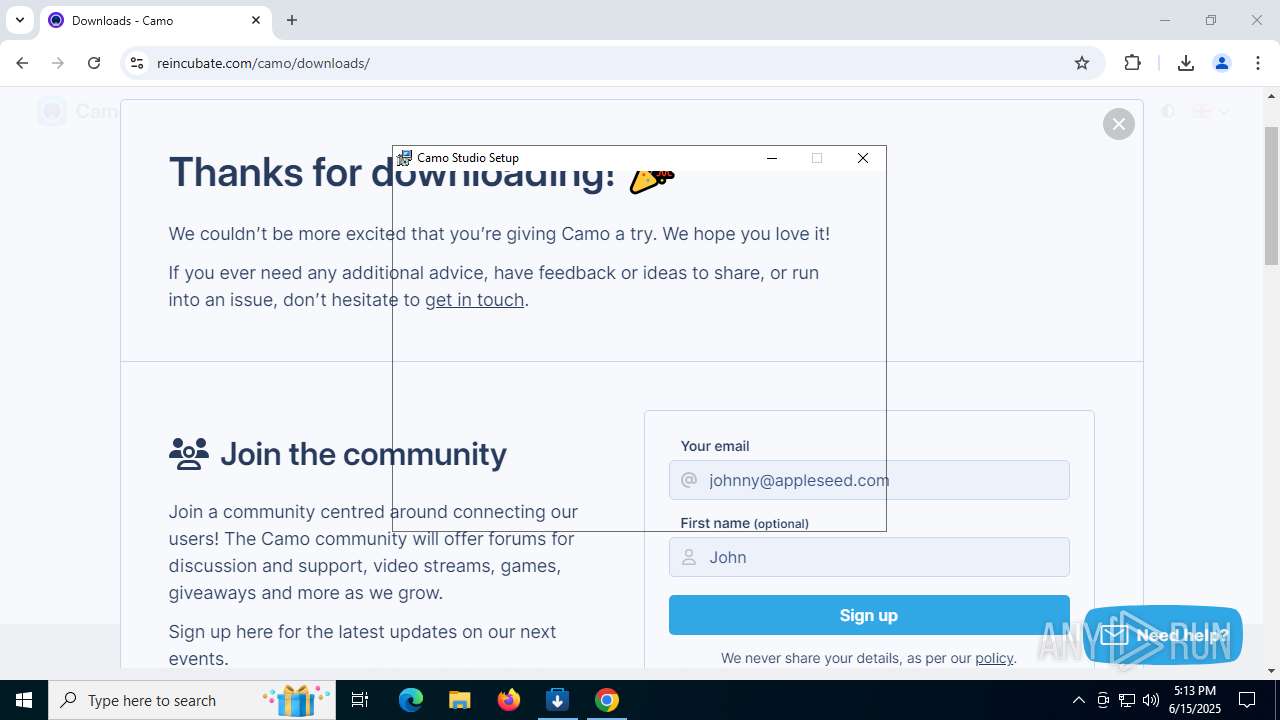
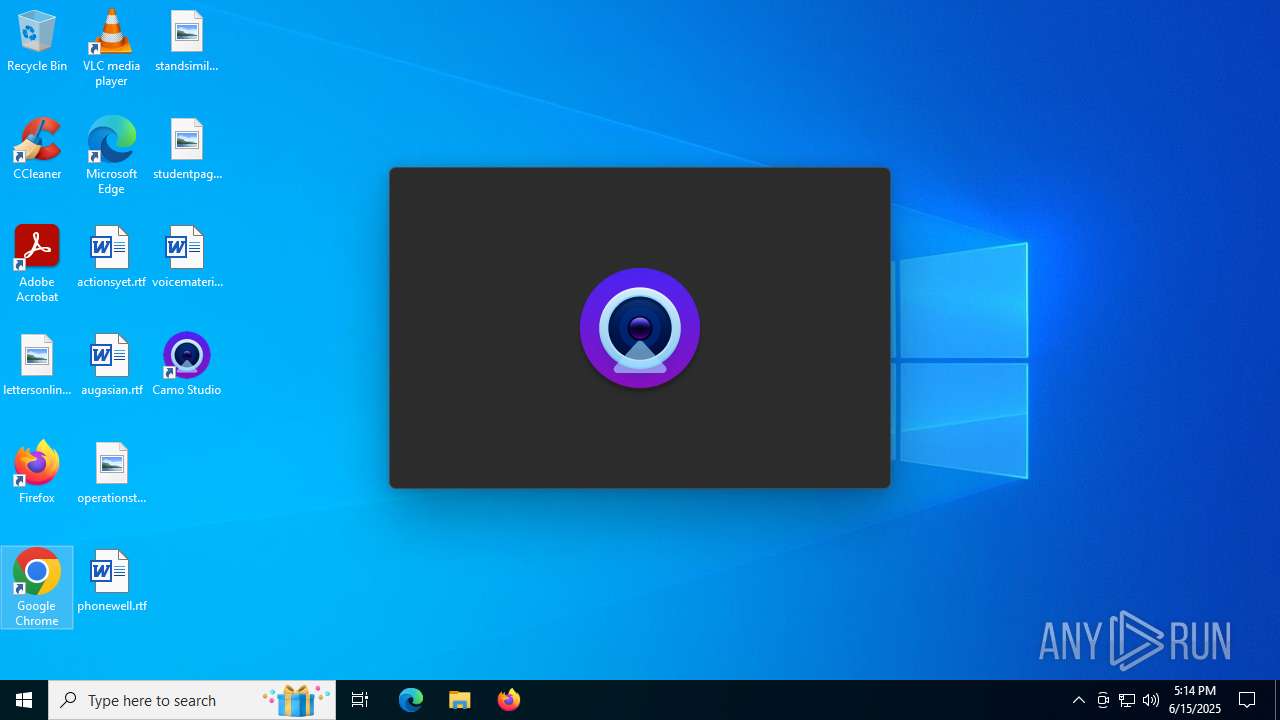
Executes as Windows Service
- VSSVC.exe (PID: 2140)
- CamoService.exe (PID: 2168)
Executes application which crashes
- Camo Studio Installer.exe (PID: 316)
The process drops C-runtime libraries
- msiexec.exe (PID: 3100)
INFO
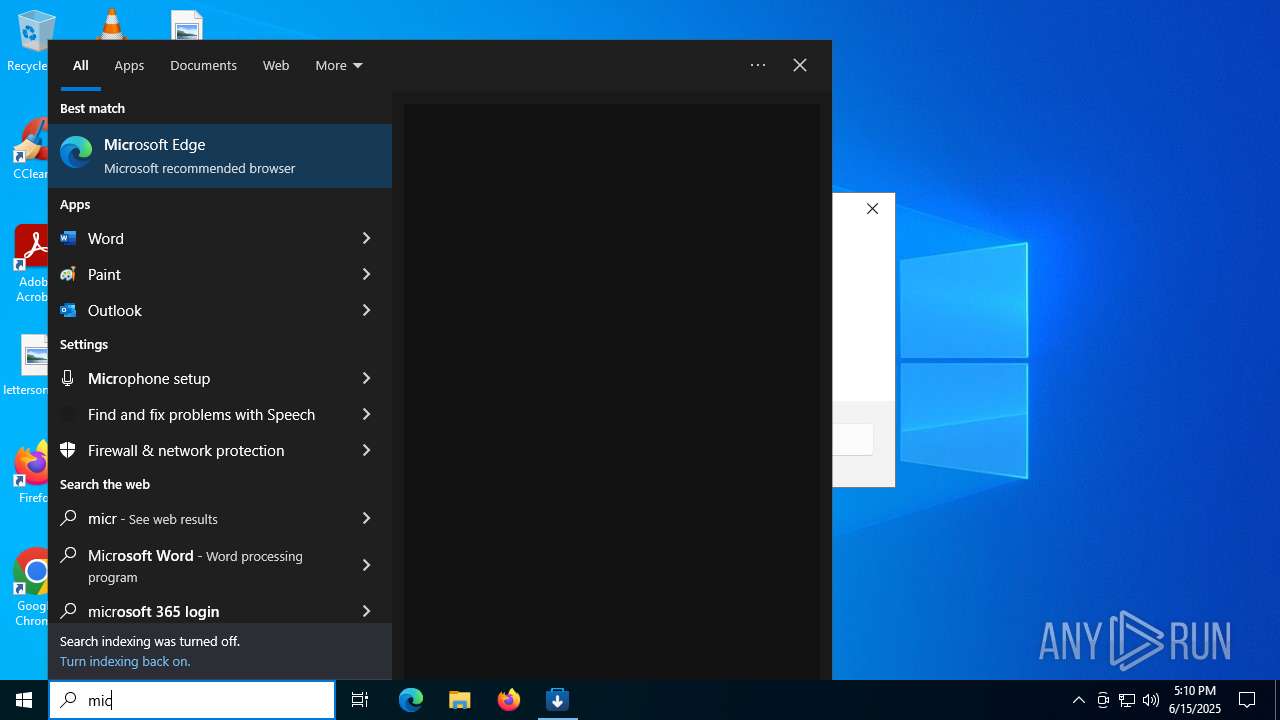
Reads the computer name
- Camo Studio Installer.exe (PID: 316)
Reads the machine GUID from the registry
- Camo Studio Installer.exe (PID: 316)
Checks supported languages
- Camo Studio Installer.exe (PID: 316)
Disables trace logs
- Camo Studio Installer.exe (PID: 316)
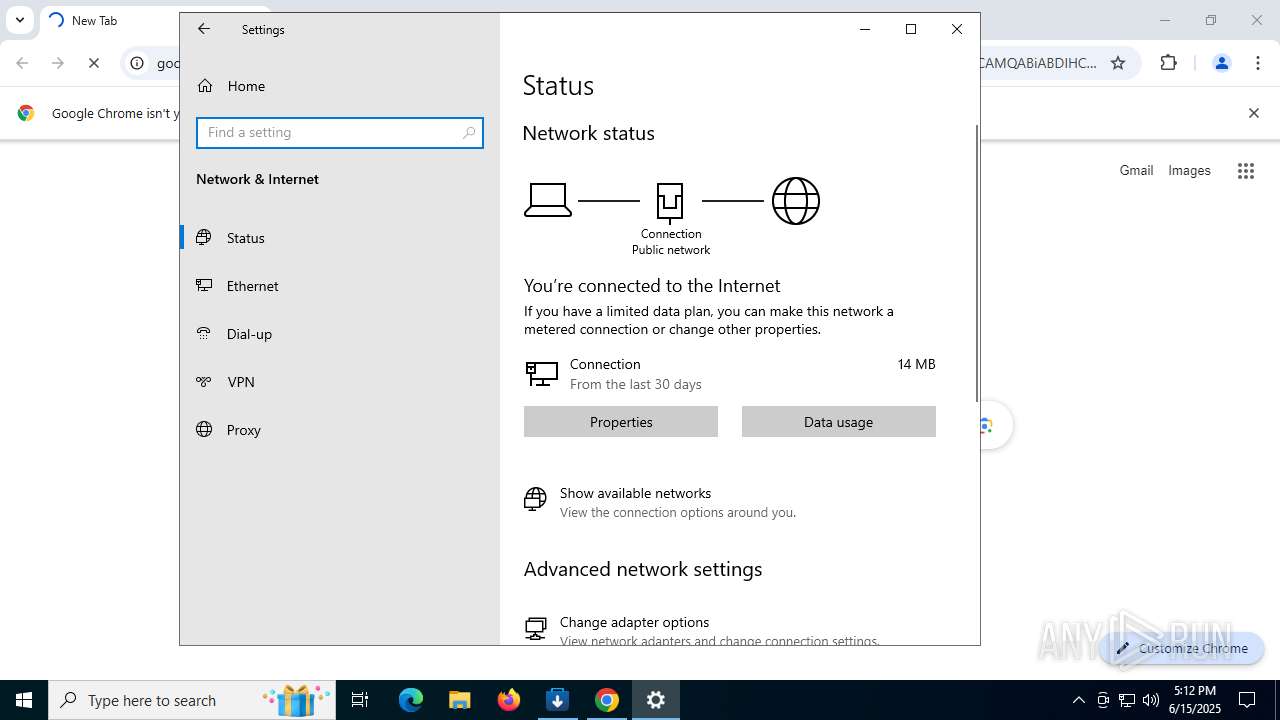
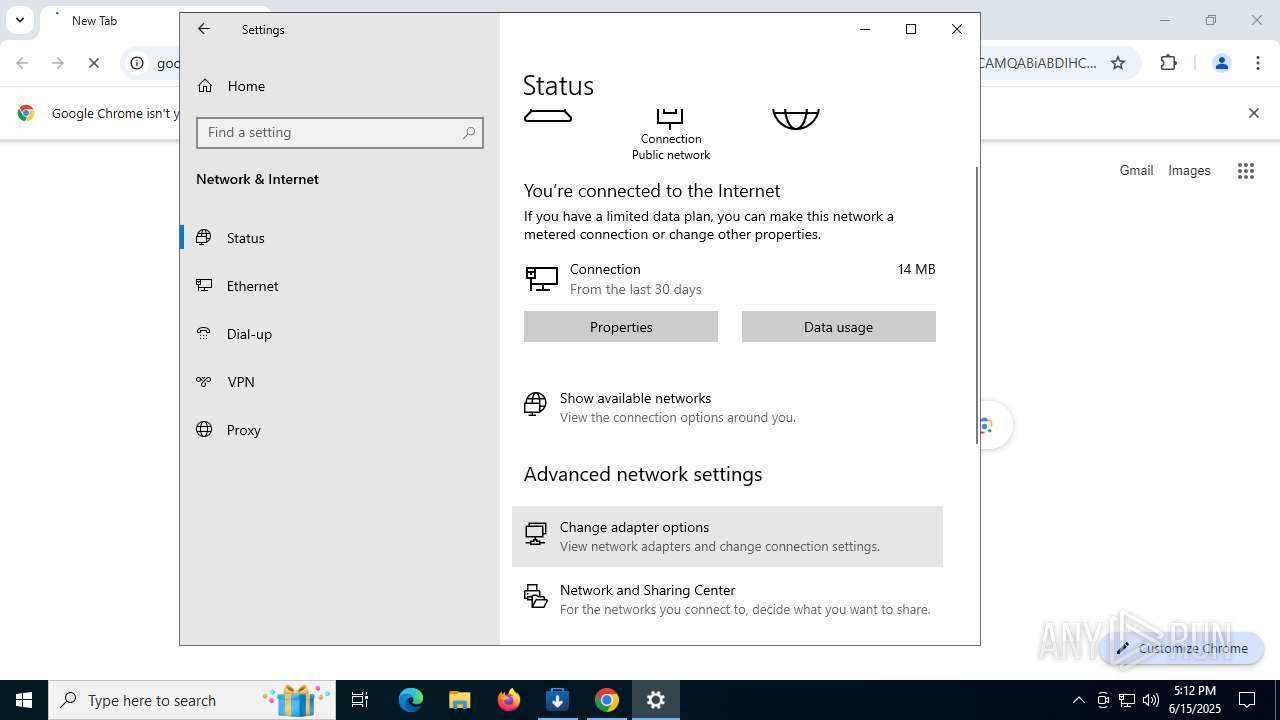
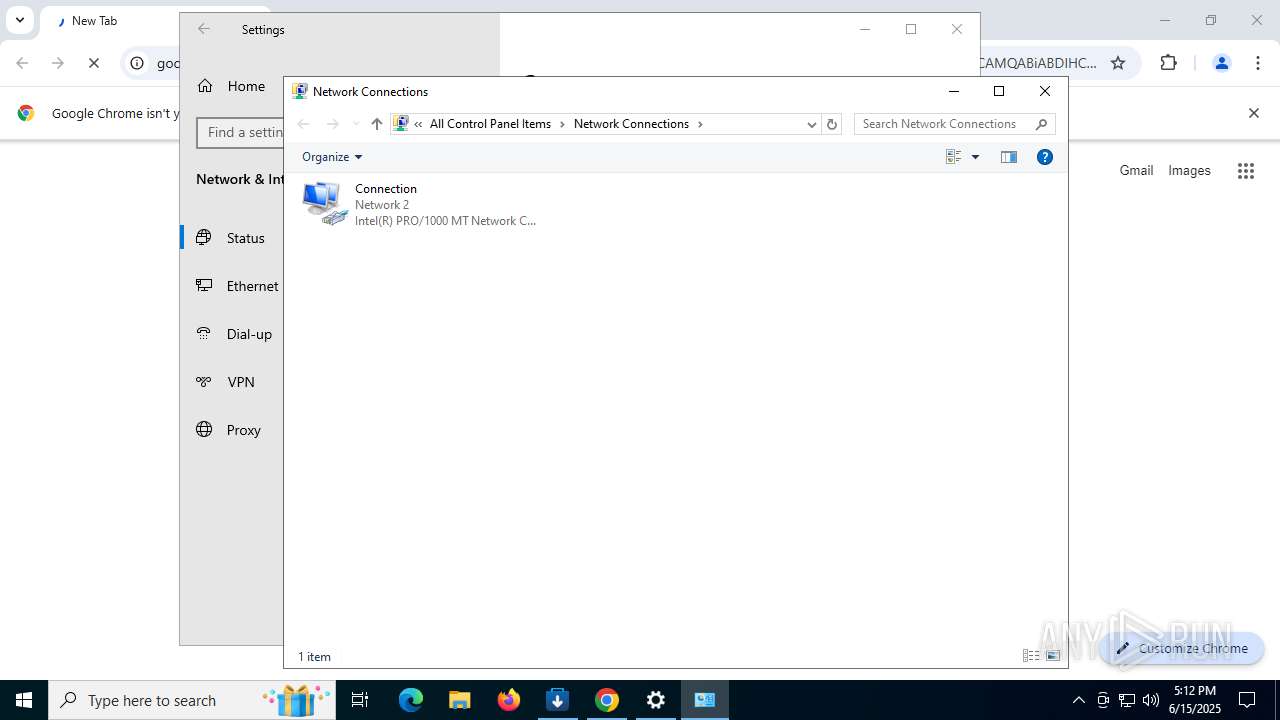
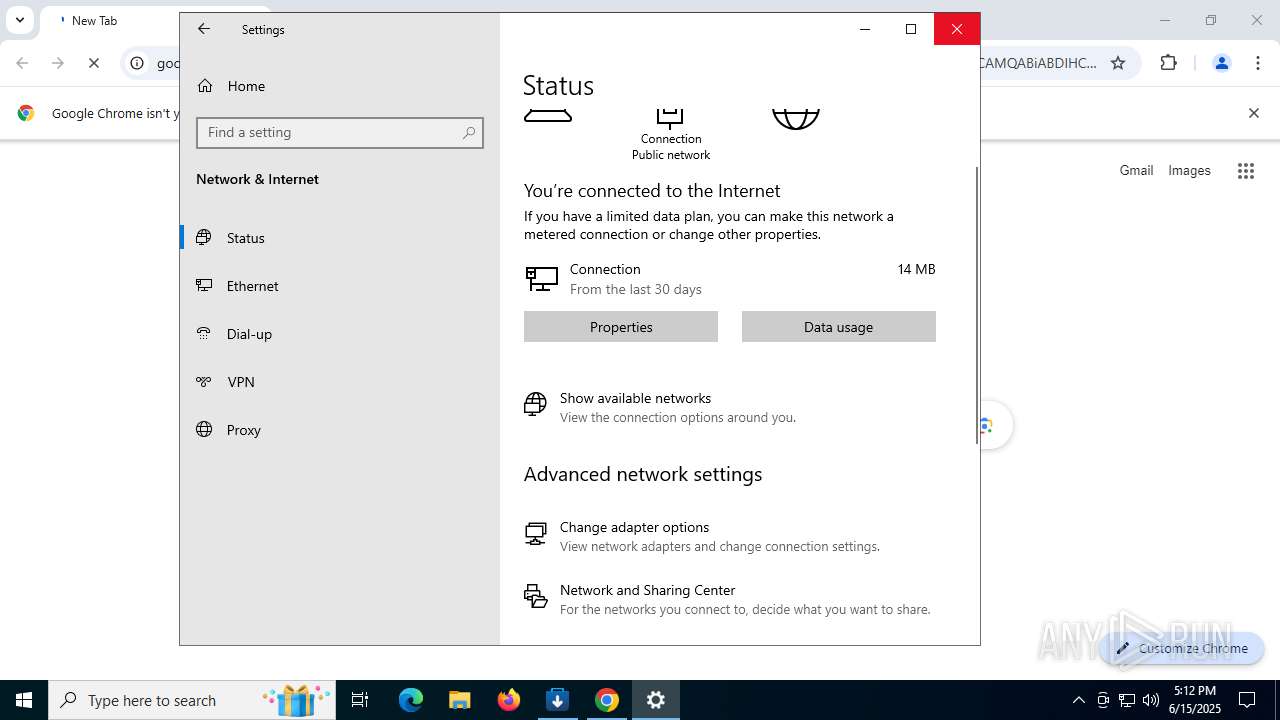
Checks proxy server information
- Camo Studio Installer.exe (PID: 316)
- slui.exe (PID: 760)
Reads Environment values
- Camo Studio Installer.exe (PID: 316)
Process checks computer location settings
- Camo Studio Installer.exe (PID: 316)
Reads the software policy settings
- Camo Studio Installer.exe (PID: 316)
- slui.exe (PID: 760)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3100)
- msiexec.exe (PID: 1984)
The sample compiled with english language support
- msiexec.exe (PID: 3100)
- drvinst.exe (PID: 8180)
- drvinst.exe (PID: 6124)
- drvinst.exe (PID: 3880)
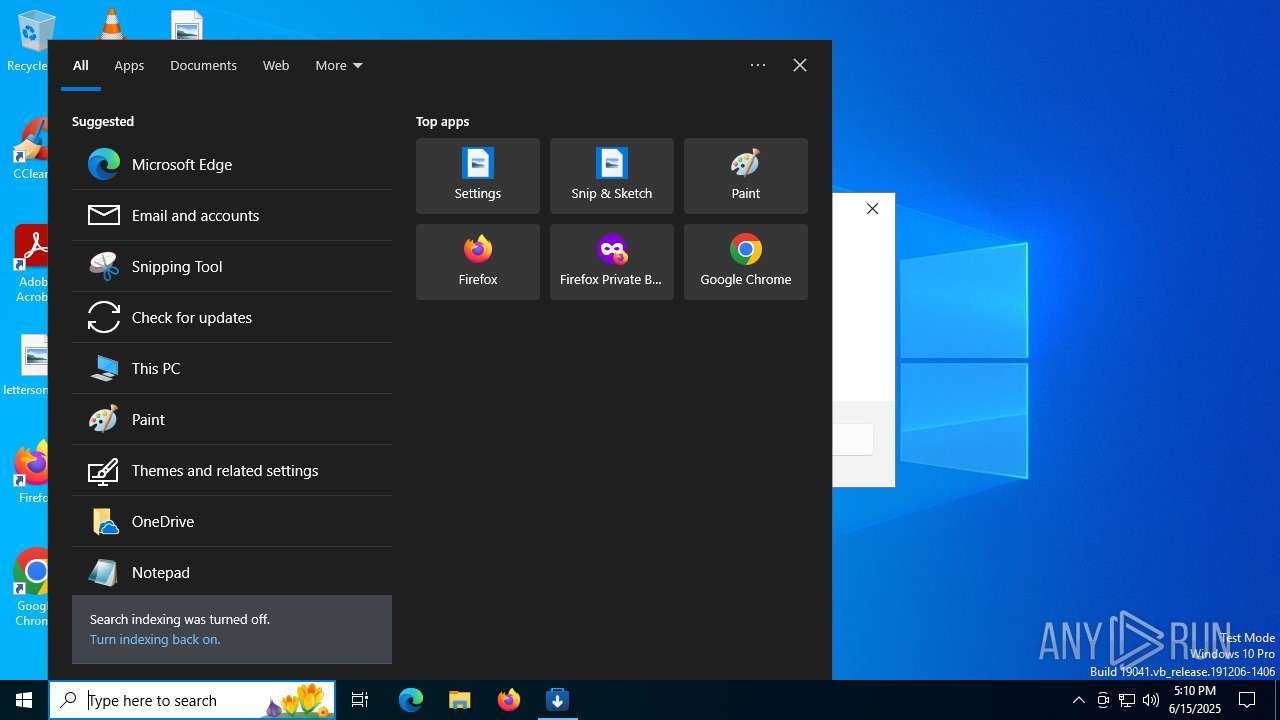
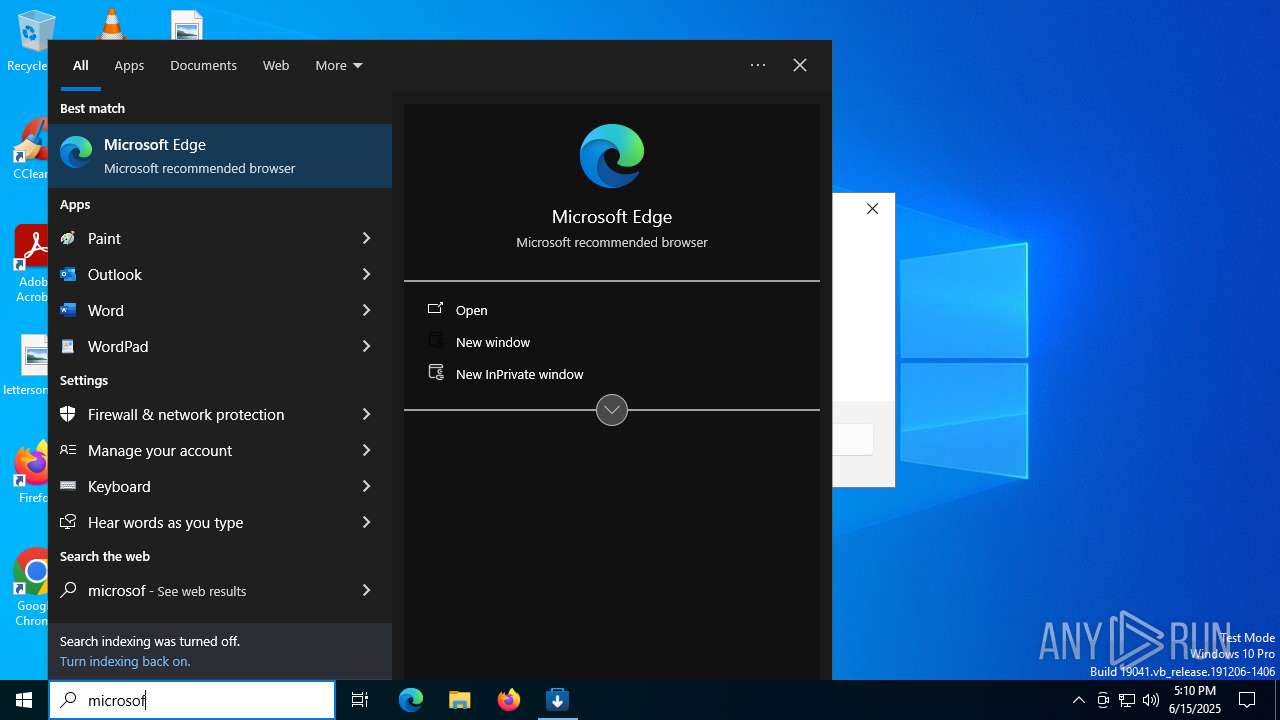
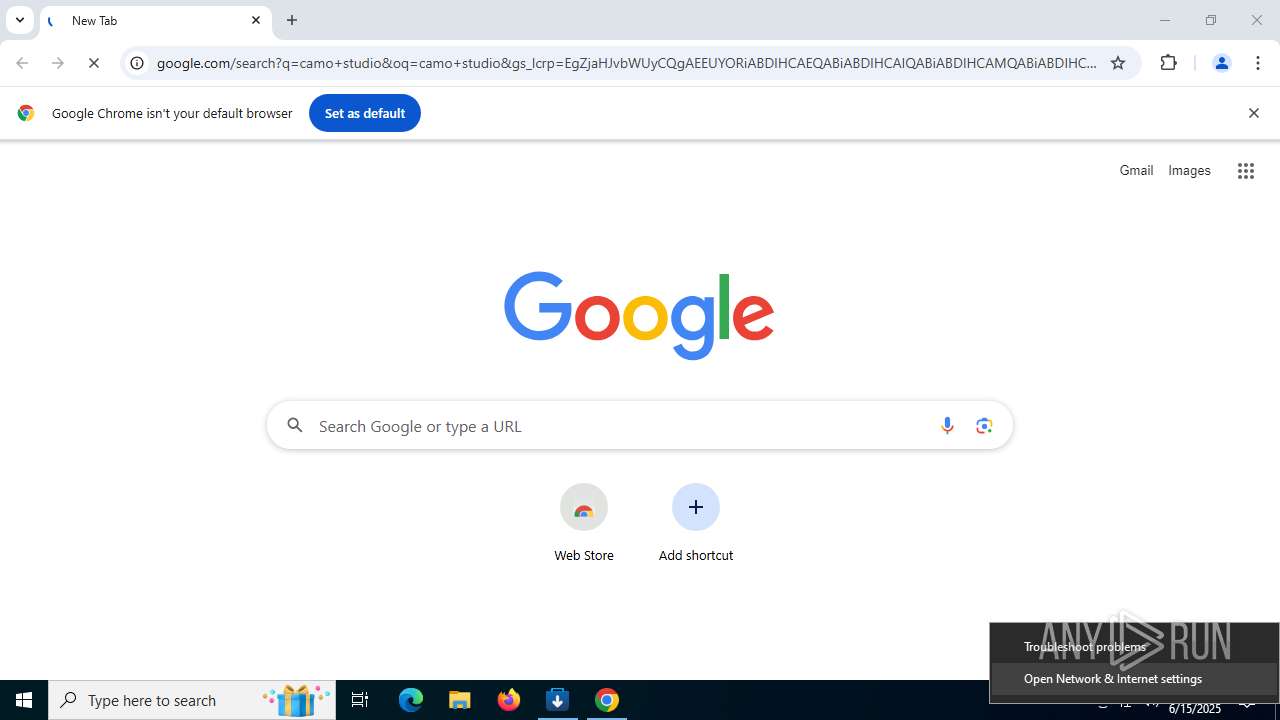
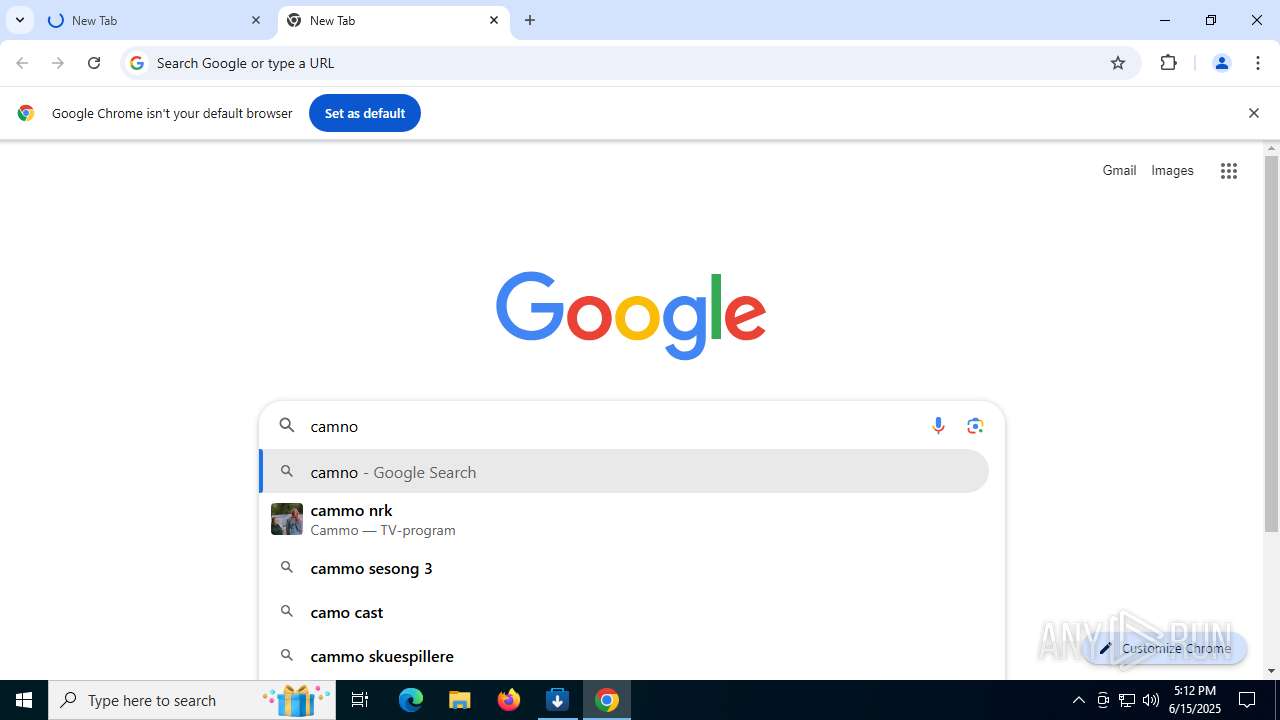
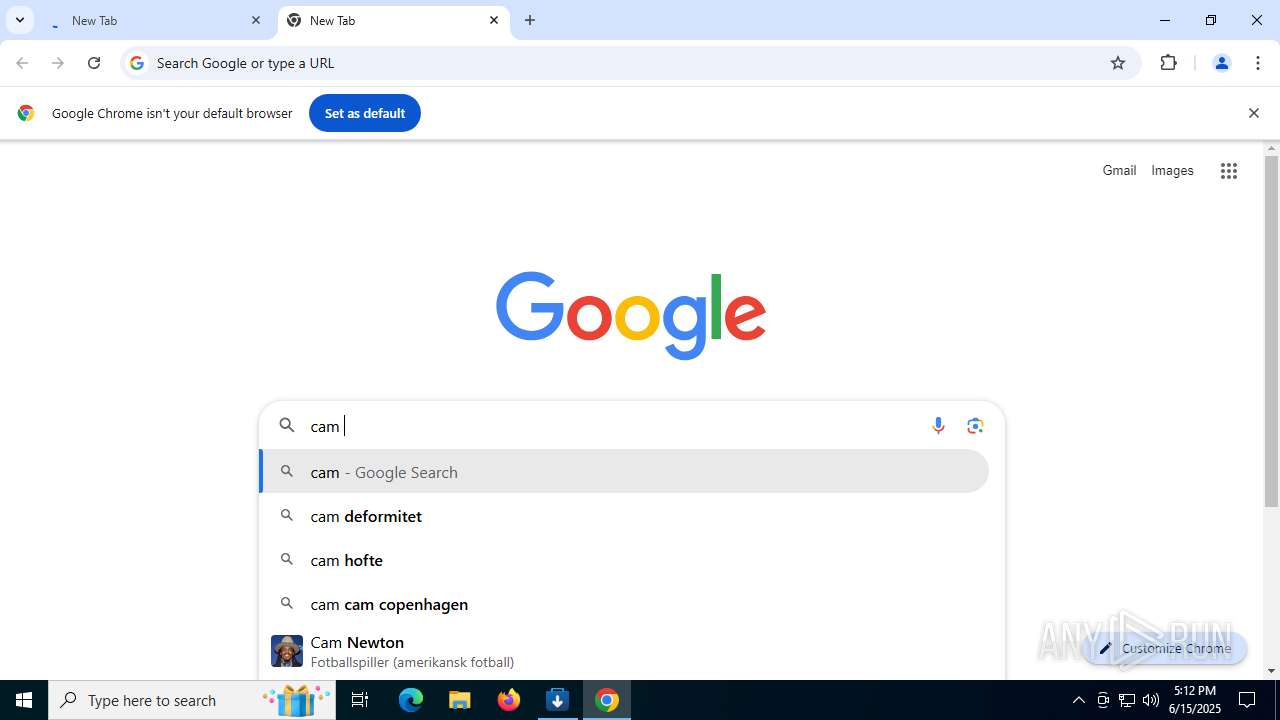
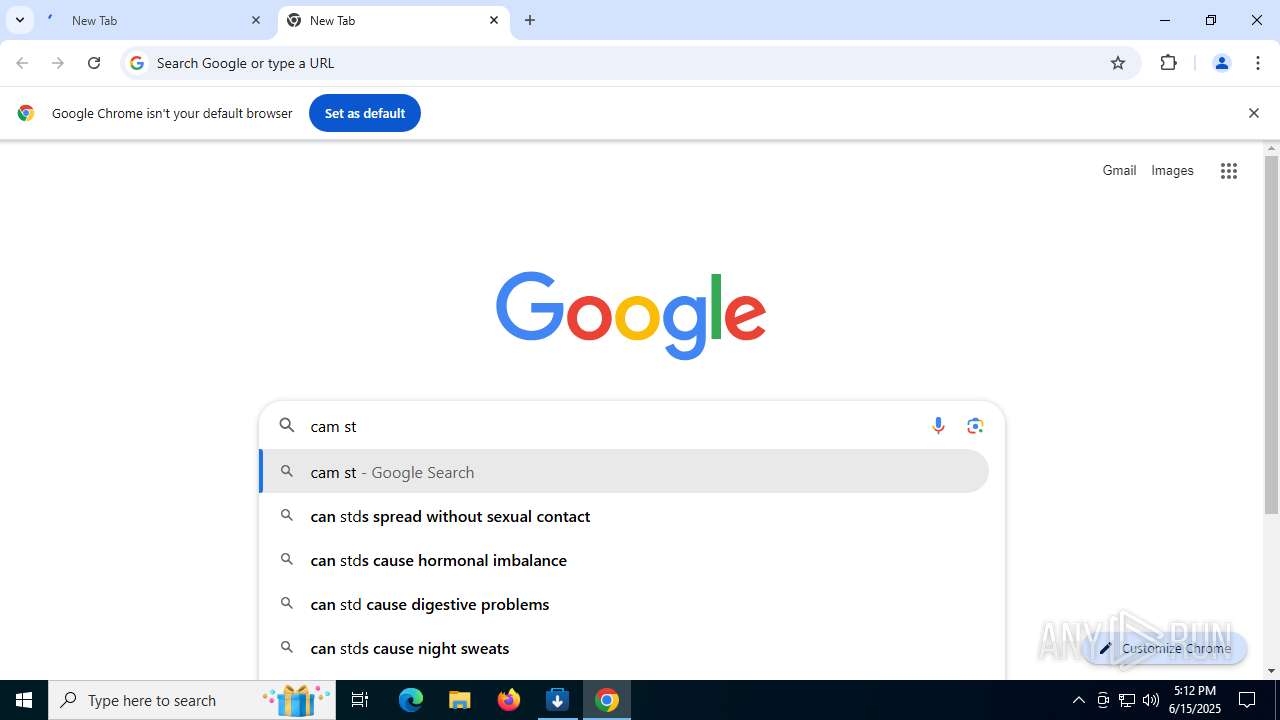
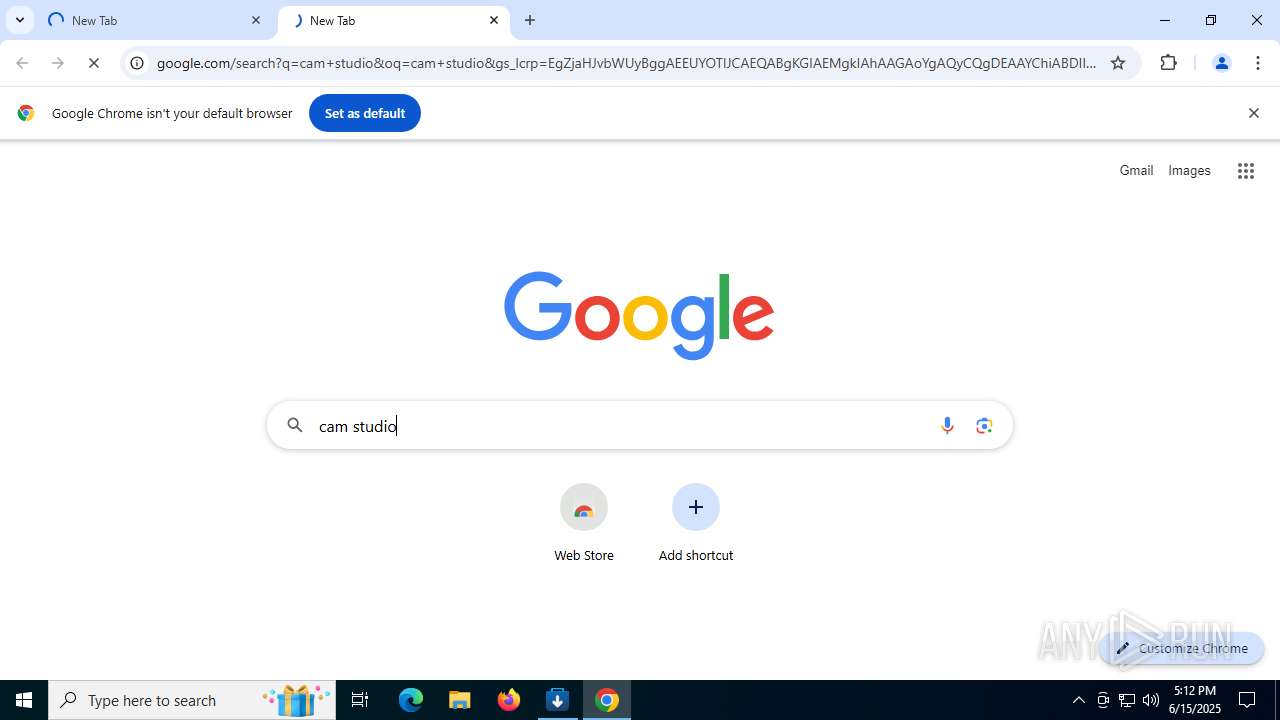
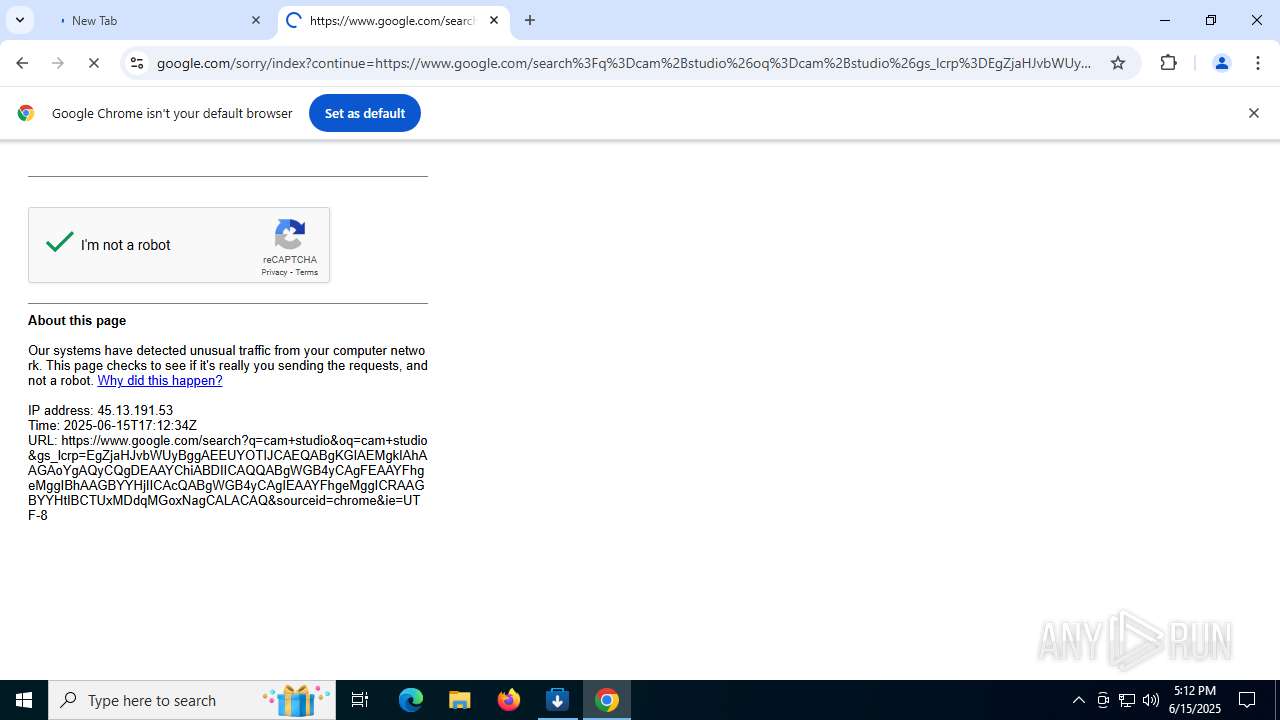
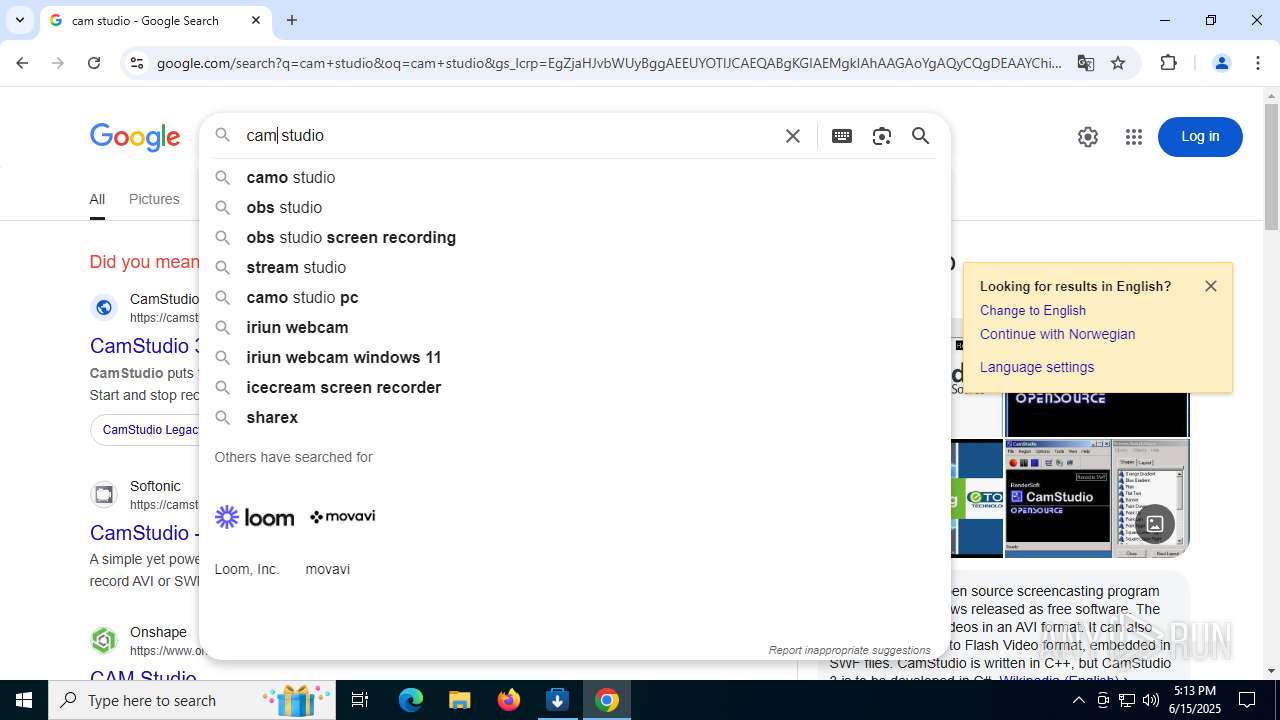
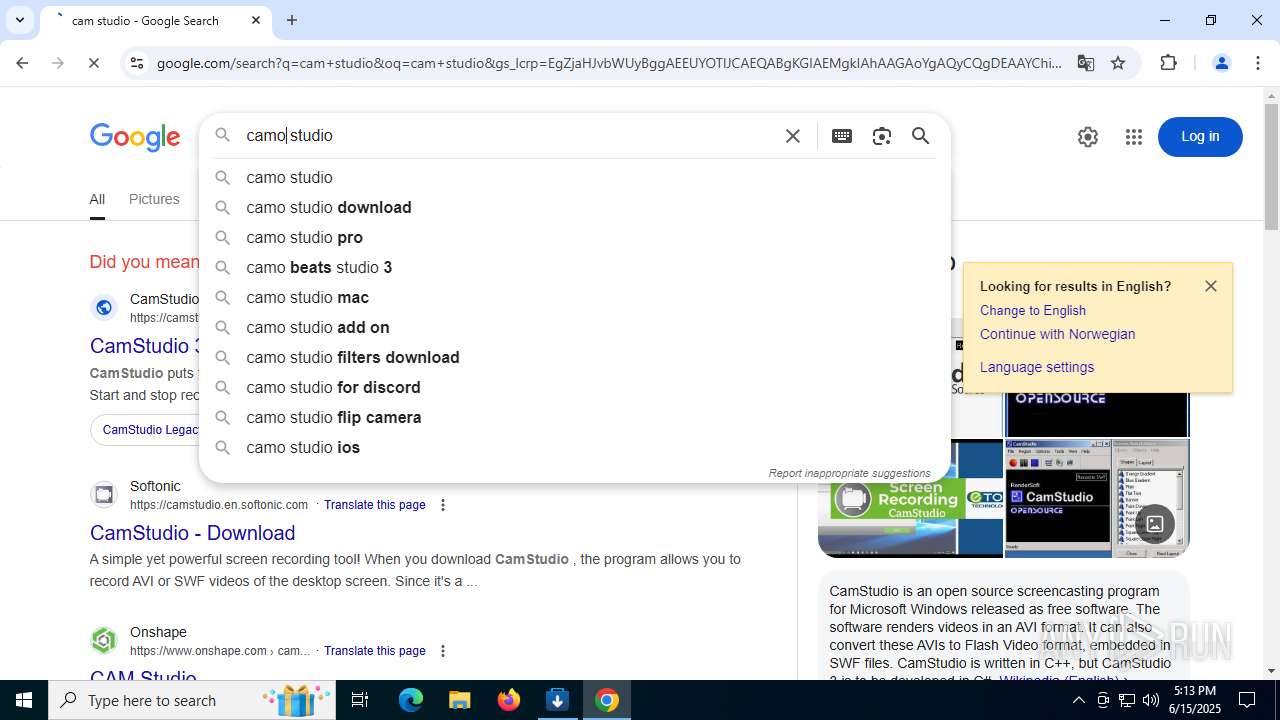
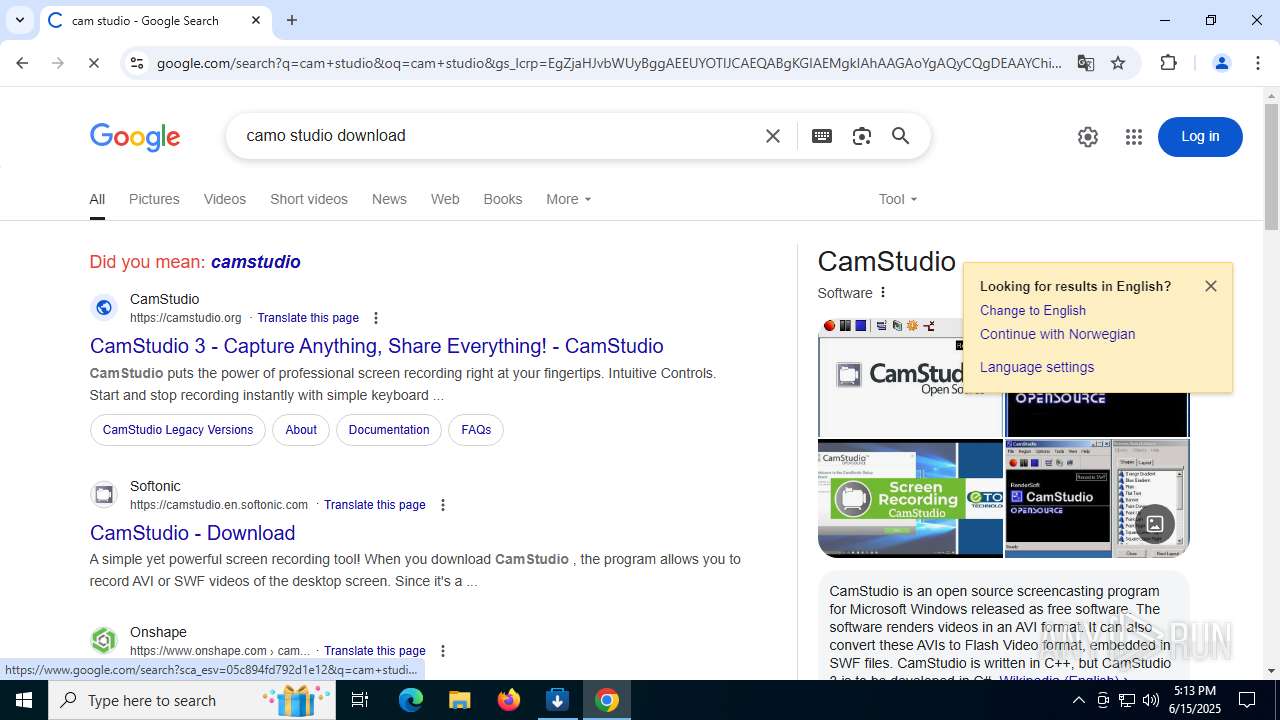
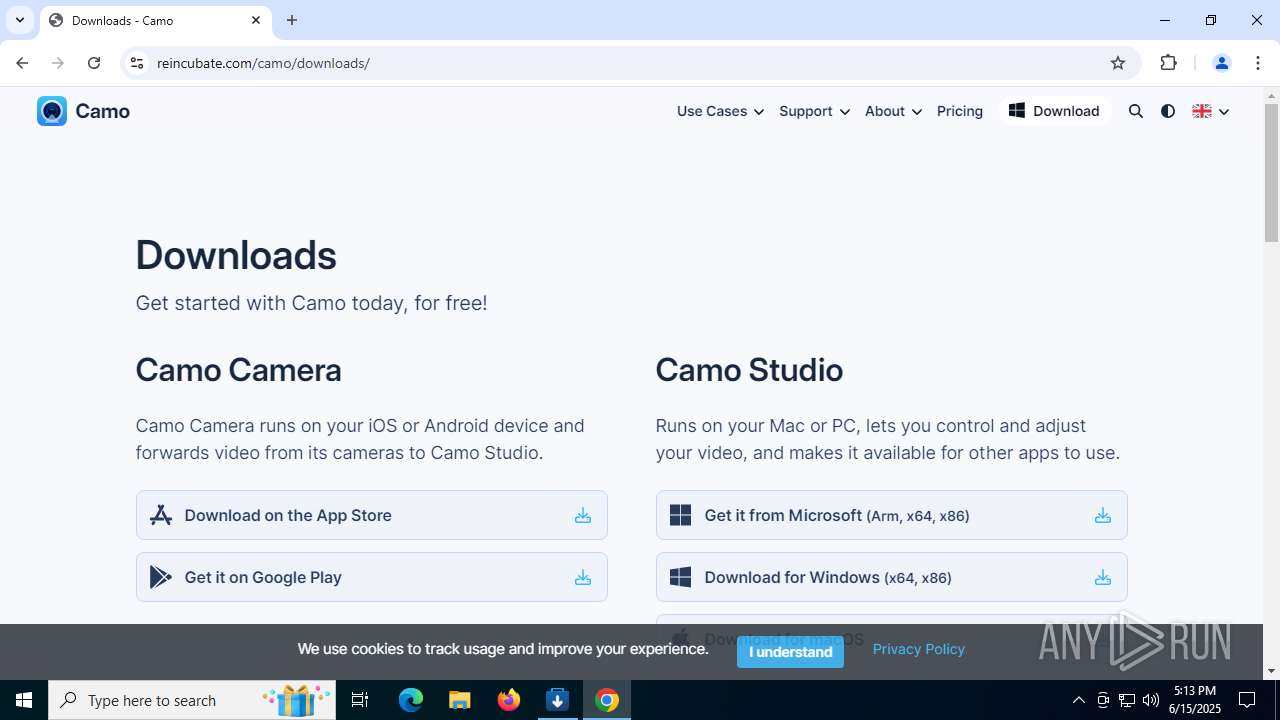
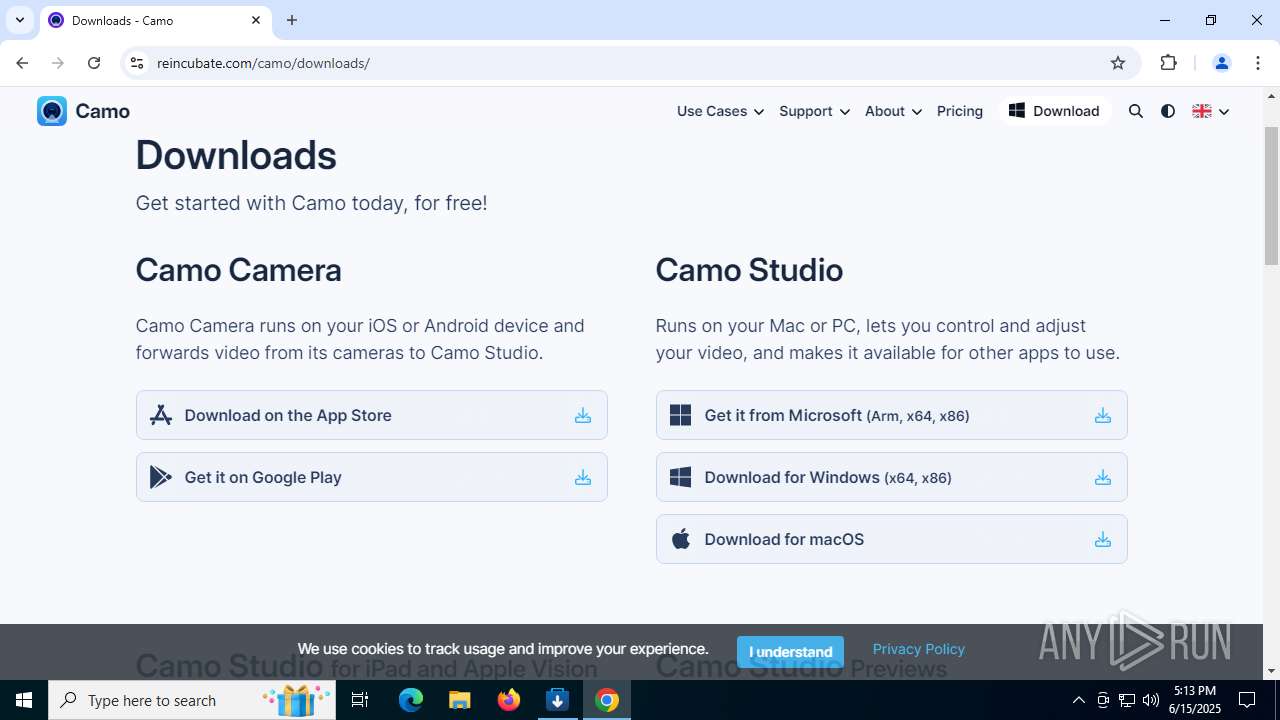
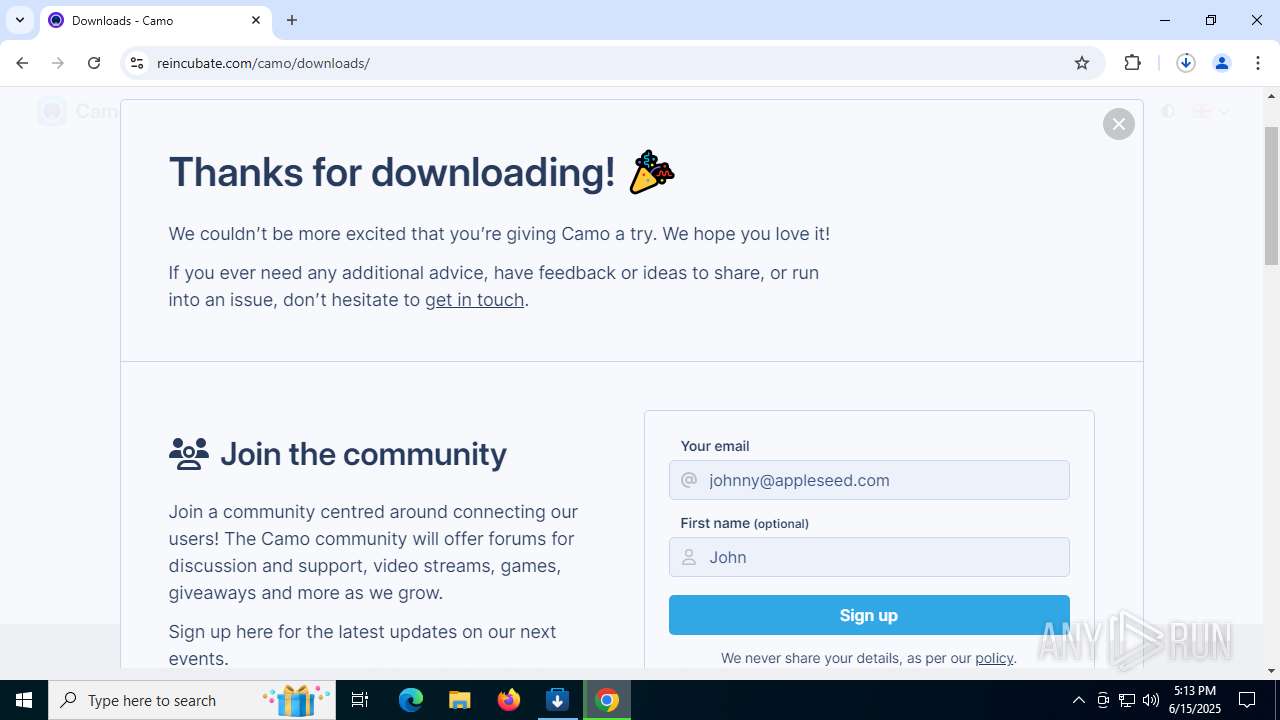
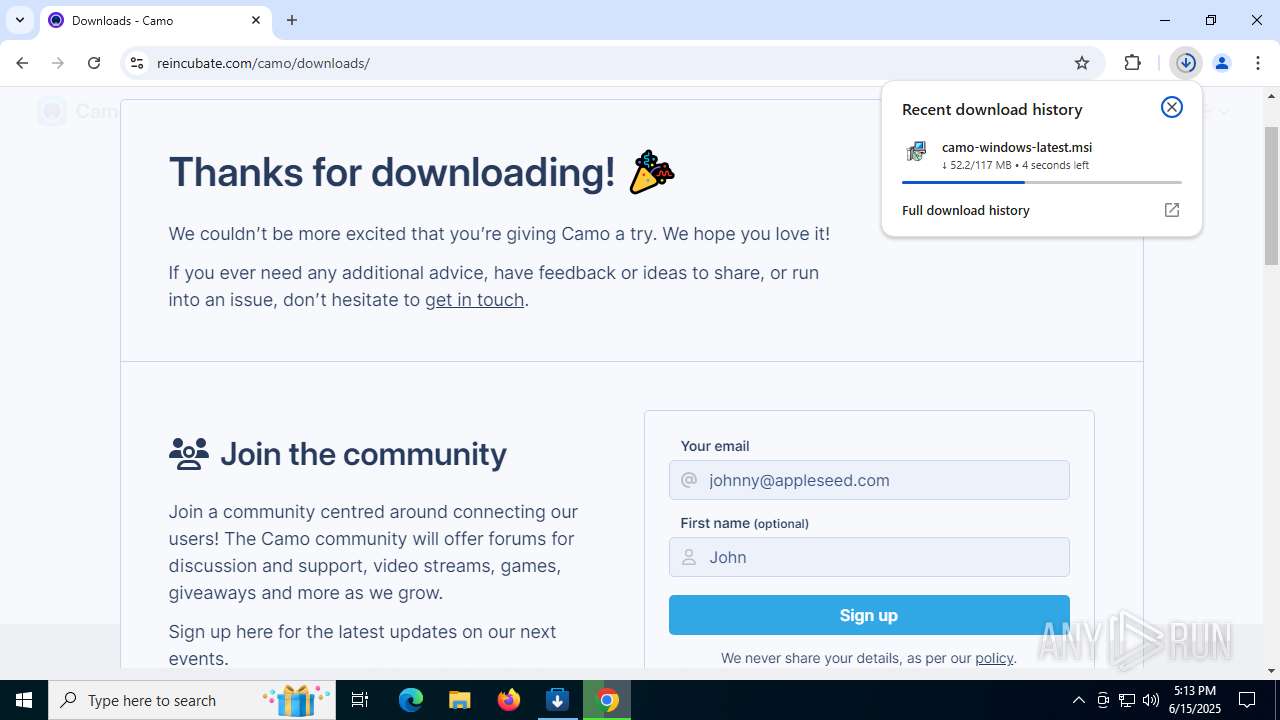
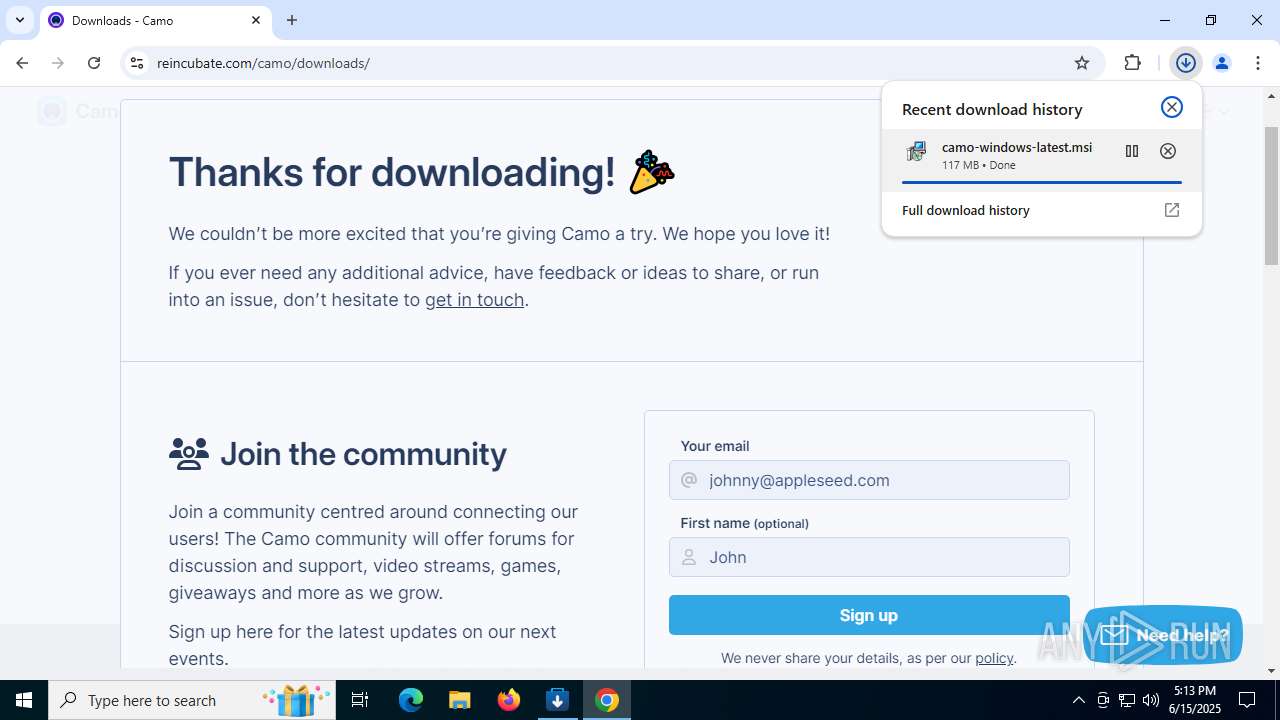
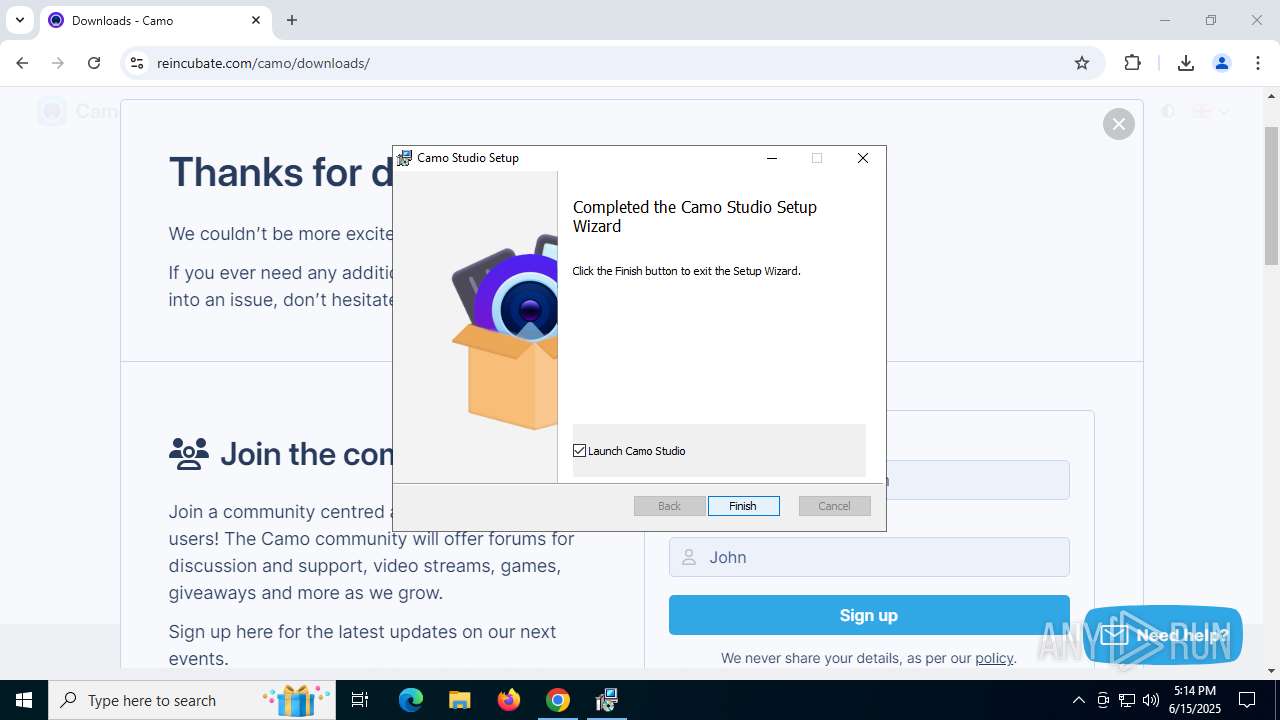
Manual execution by a user
- chrome.exe (PID: 1644)
Application launched itself
- chrome.exe (PID: 1644)
Manages system restore points
- SrTasks.exe (PID: 7320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2061:03:23 21:25:22+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 998912 |
| InitializedDataSize: | 75776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf5d12 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 22504.418.1.0 |
| ProductVersionNumber: | 22504.418.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Store Installer |
| FileVersion: | 22504.418.1.0 |
| InternalName: | StoreInstaller.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | StoreInstaller.exe |
| ProductName: | Store Installer |
| ProductVersion: | 22504.0418.01.0+88d4431a5e7625ea51830218ca1a0e0aa192321d |
| AssemblyVersion: | 22504.418.1.0 |
Total processes
218
Monitored processes
54
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Users\admin\AppData\Local\Temp\Camo Studio Installer.exe" | C:\Users\admin\AppData\Local\Temp\Camo Studio Installer.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Store Installer Exit code: 3762504530 Version: 22504.418.1.0 Modules
| |||||||||||||||
| 436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=2004,i,4580889344129535457,1950765304360320435,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1984 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 724 | rundll32.exe "C:\WINDOWS\Installer\MSIC5D5.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1820125 77 CamoStudio.Setup.CustomActions!CamoStudio.Setup.CustomActions.CustomActions.InstallAudioDriver | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 760 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=6884,i,4580889344129535457,1950765304360320435,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6984 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1080 | DrvInst.exe "2" "211" "ROOT\CAMERA\0000" "C:\WINDOWS\INF\oem1.inf" "oem1.inf:c14ce8840bd02e1d:camodriver:13.17.28.365:camodriver," "4de0271f3" "0000000000000170" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2244,i,4580889344129535457,1950765304360320435,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2256 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=6944,i,4580889344129535457,1950765304360320435,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6904 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1496 | "C:\Program Files (x86)\Camo Studio\vac\CamoAudioDriverInstaller.exe" -q -l -m -h "Root\{e070661c-ac3f-4aae-aa3f-7d4e8ded5142}\0000" -i "Camo_e070661c-ac3f-4aae-aa3f-7d4e8ded5142" "C:\Program Files (x86)\Camo Studio\vac\vacrnckd.inf" | C:\Program Files (x86)\Camo Studio\vac\CamoAudioDriverInstaller.exe | — | rundll32.exe | |||||||||||
User: SYSTEM Company: Reincubate Integrity Level: SYSTEM Description: Camo Audio Driver Installer Exit code: 0 Version: 1.14.0.1 Modules
| |||||||||||||||
| 1632 | C:\Windows\syswow64\MsiExec.exe -Embedding C455C6483AEB61E1B9CF83B1D09694FC C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
47 536
Read events
45 700
Write events
1 798
Delete events
38
Modification events
| (PID) Process: | (316) Camo Studio Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (316) Camo Studio Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (316) Camo Studio Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (316) Camo Studio Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Camo Studio Installer_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (316) Camo Studio Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Camo Studio Installer_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (316) Camo Studio Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Camo Studio Installer_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (316) Camo Studio Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Camo Studio Installer_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (316) Camo Studio Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Camo Studio Installer_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (316) Camo Studio Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Camo Studio Installer_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (316) Camo Studio Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Camo Studio Installer_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
177
Suspicious files
309
Text files
84
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF197092.TMP | — | |
MD5:— | SHA256:— | |||
| 1644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1970a2.TMP | — | |
MD5:— | SHA256:— | |||
| 1644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1970b2.TMP | — | |
MD5:— | SHA256:— | |||
| 1644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF1970b2.TMP | — | |
MD5:— | SHA256:— | |||
| 1644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1970b2.TMP | — | |
MD5:— | SHA256:— | |||
| 1644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
179
DNS requests
198
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2520 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6388 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6388 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1128 | chrome.exe | GET | 200 | 172.217.18.14:80 | http://clients2.google.com/time/1/current?cup2key=8:XXPCGGKb40YDU2aTb2nav1wVsRP8hyoFZkWWxrzcgAY&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1128 | chrome.exe | GET | 204 | 172.217.16.195:80 | http://www.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2324 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acwmiglbaq6quecjufmamfsqupsa_2025.5.21.0/niikhdgajlphfehepabhhblakbdgeefj_2025.05.21.00_all_msqewqxesfaohilvaerhlfagai.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1136 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
316 | Camo Studio Installer.exe | 23.35.237.194:443 | storesdk.dsx.mp.microsoft.com | AKAMAI-AS | DE | whitelisted |
316 | Camo Studio Installer.exe | 23.35.229.133:443 | store-images.s-microsoft.com | AKAMAI-AS | DE | unknown |
316 | Camo Studio Installer.exe | 20.82.228.9:443 | displaycatalog.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
316 | Camo Studio Installer.exe | 23.35.237.133:443 | store-images.microsoft.com | AKAMAI-AS | DE | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
storesdk.dsx.mp.microsoft.com |
| whitelisted |
store-images.s-microsoft.com |
| whitelisted |
displaycatalog.mp.microsoft.com |
| whitelisted |
store-images.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1128 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
1128 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
1128 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1128 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1128 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
1128 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
1128 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1128 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1128 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1128 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |