| File name: | 2.rar |
| Full analysis: | https://app.any.run/tasks/4878fa54-3609-4d28-8e3e-608aeb0e8388 |
| Verdict: | Malicious activity |
| Analysis date: | July 24, 2020, 17:33:31 |
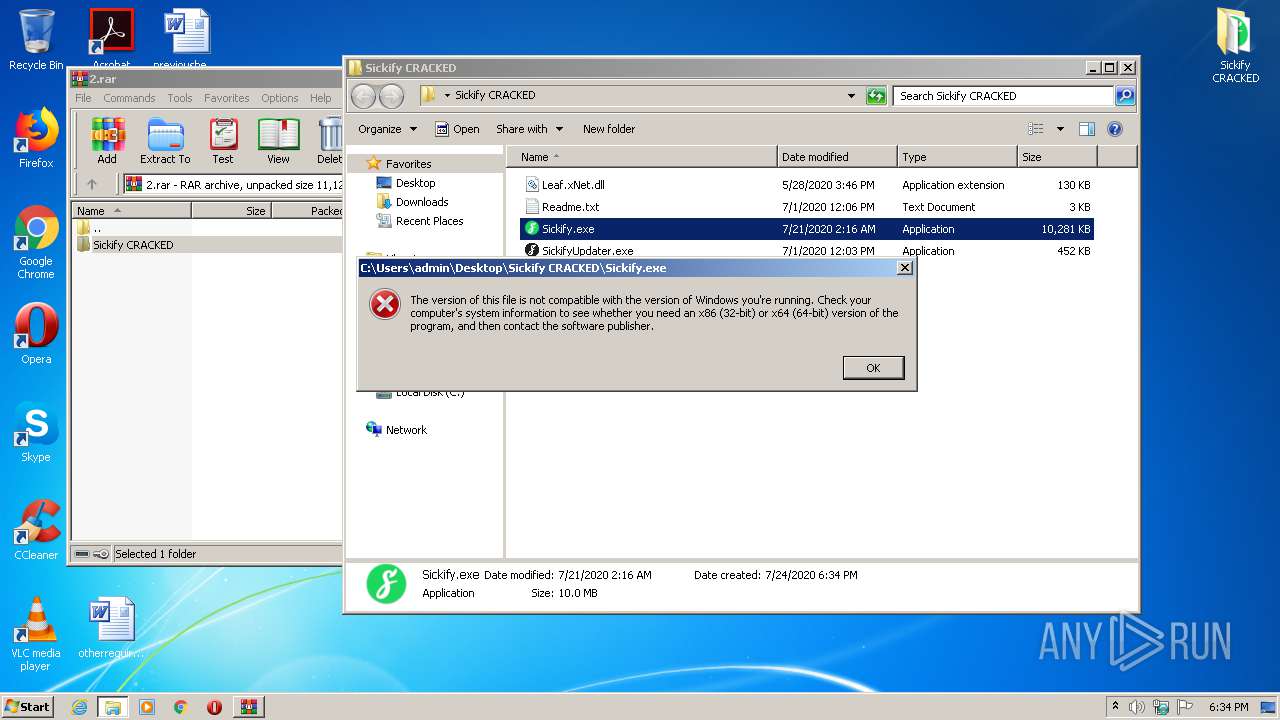
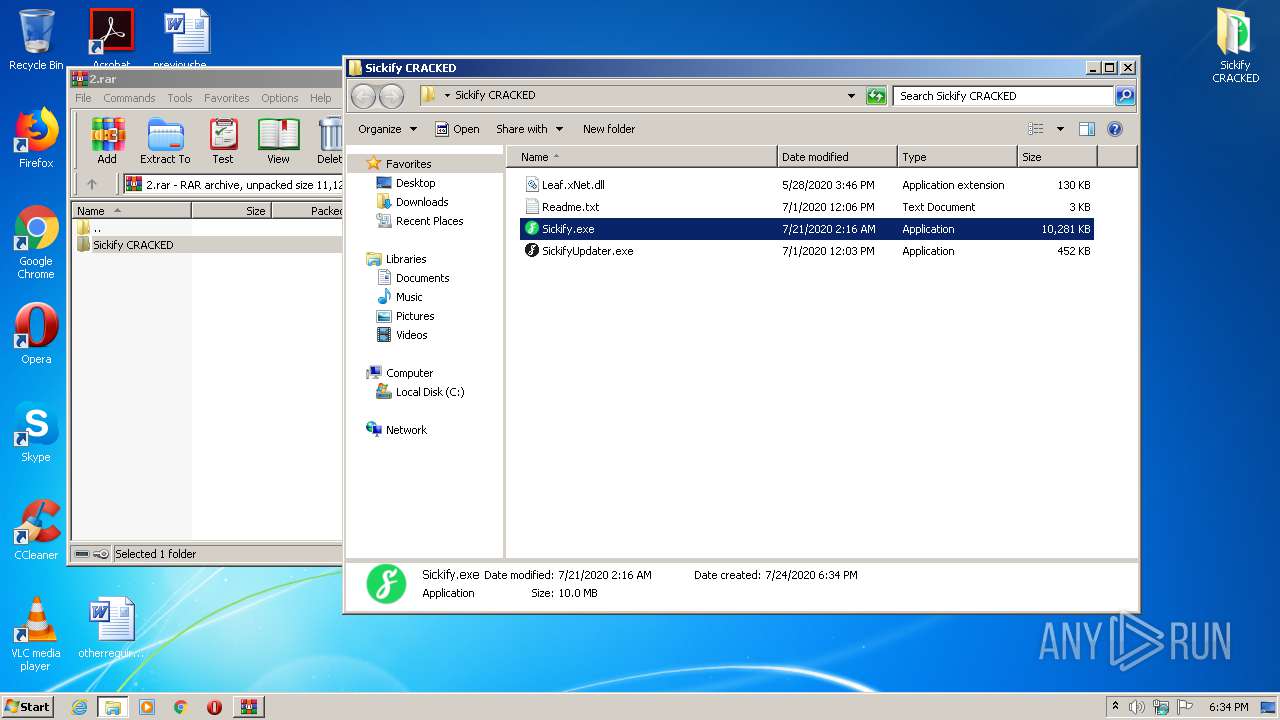
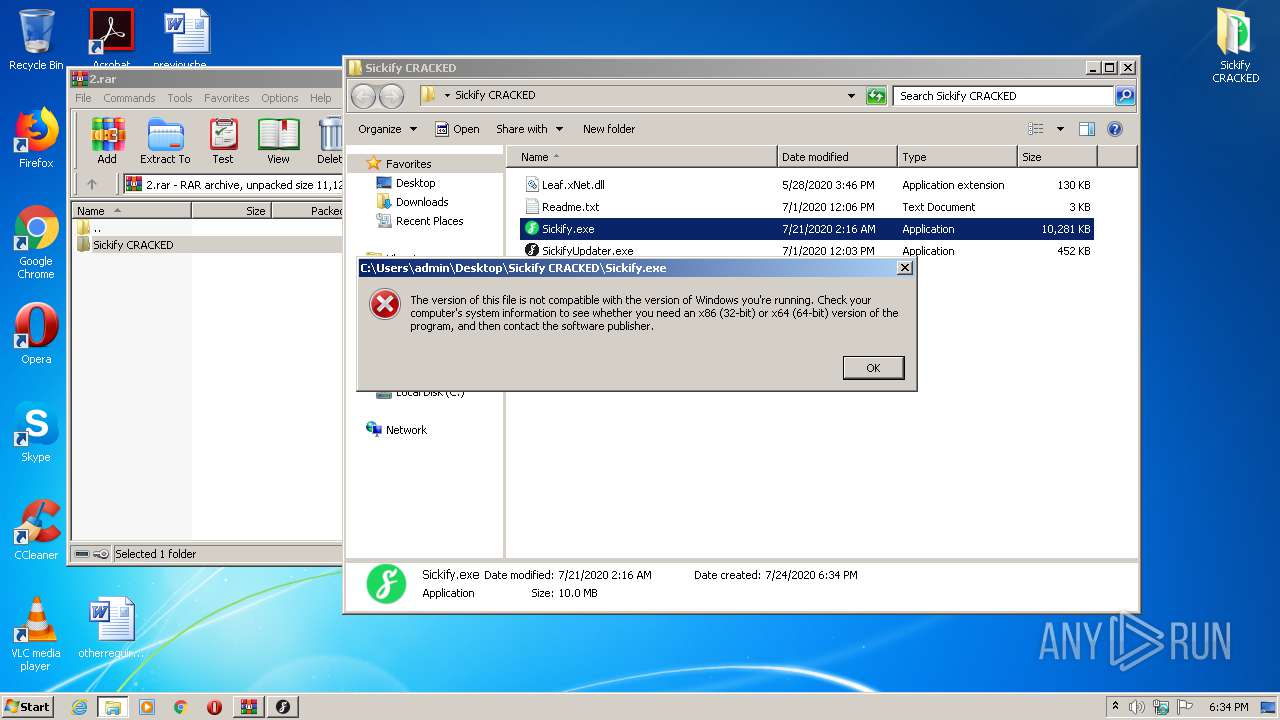
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
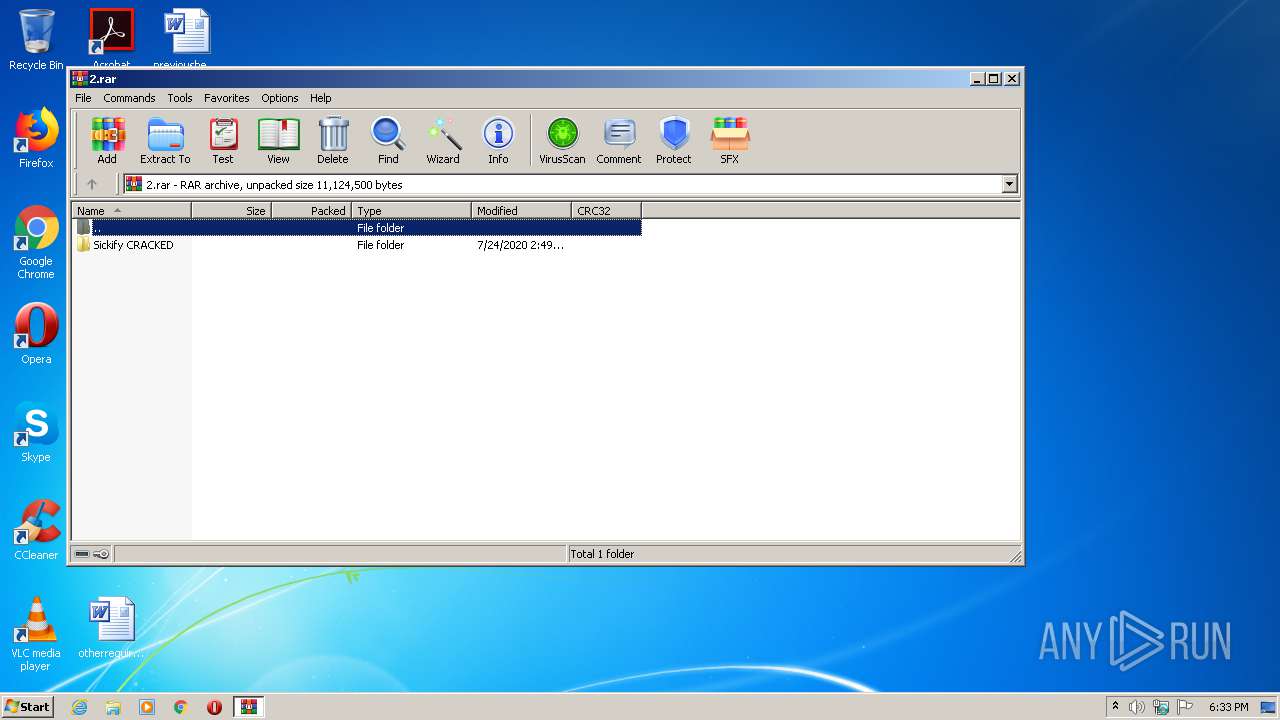
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 394E9A78E017DA5F7F739AB3E605E087 |
| SHA1: | 9A94C0B6D515FC137F688446A4234A36306CC94E |
| SHA256: | 345EB2E6FCE85EA25995415794FB47D75666DAD3E5C00ADCDA407F4A0FB99FD9 |
| SSDEEP: | 196608:6UaUAKMRhqSgXphjf8Zy1iepWP9JffI35YF18M2rkbAUzdIX:Jbphjf82pWjmGIM3ziX |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3564)
- SickifyUpdater.exe (PID: 2664)
Changes settings of System certificates
- SickifyUpdater.exe (PID: 2664)
Application was dropped or rewritten from another process
- SickifyUpdater.exe (PID: 2664)
SUSPICIOUS
Executable content was dropped or overwritten
- SickifyUpdater.exe (PID: 2664)
- WinRAR.exe (PID: 2336)
INFO
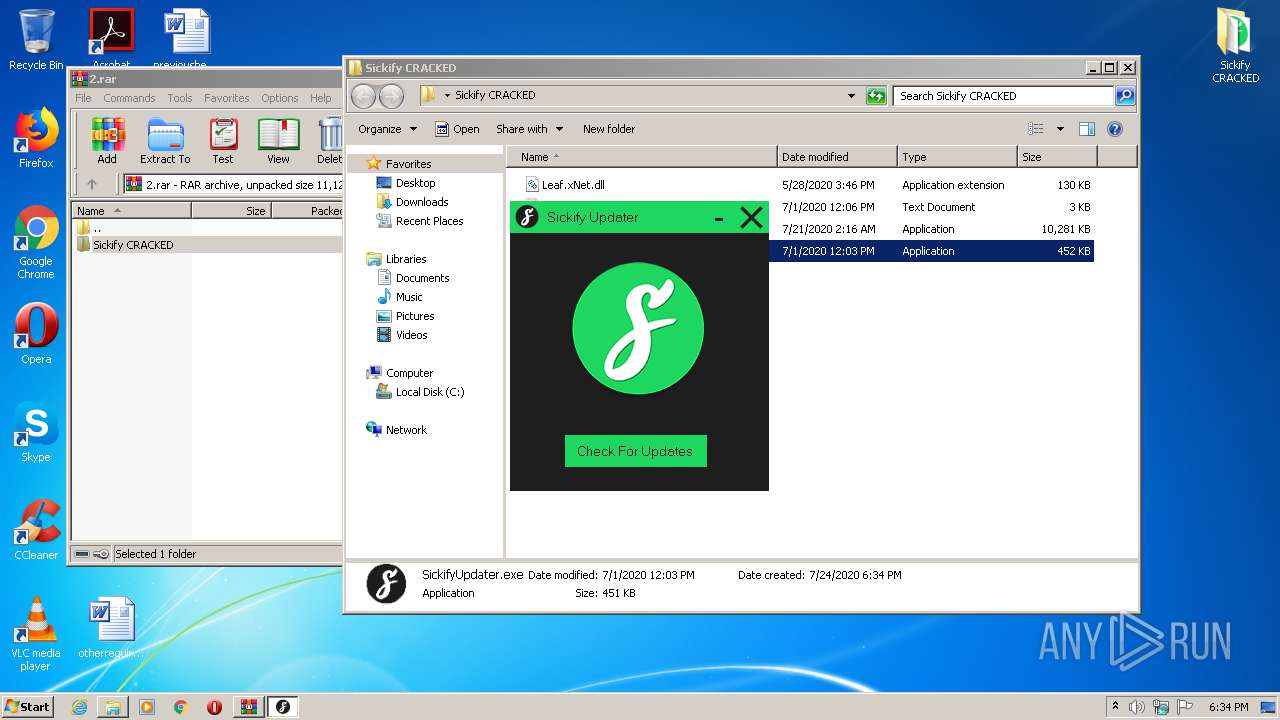
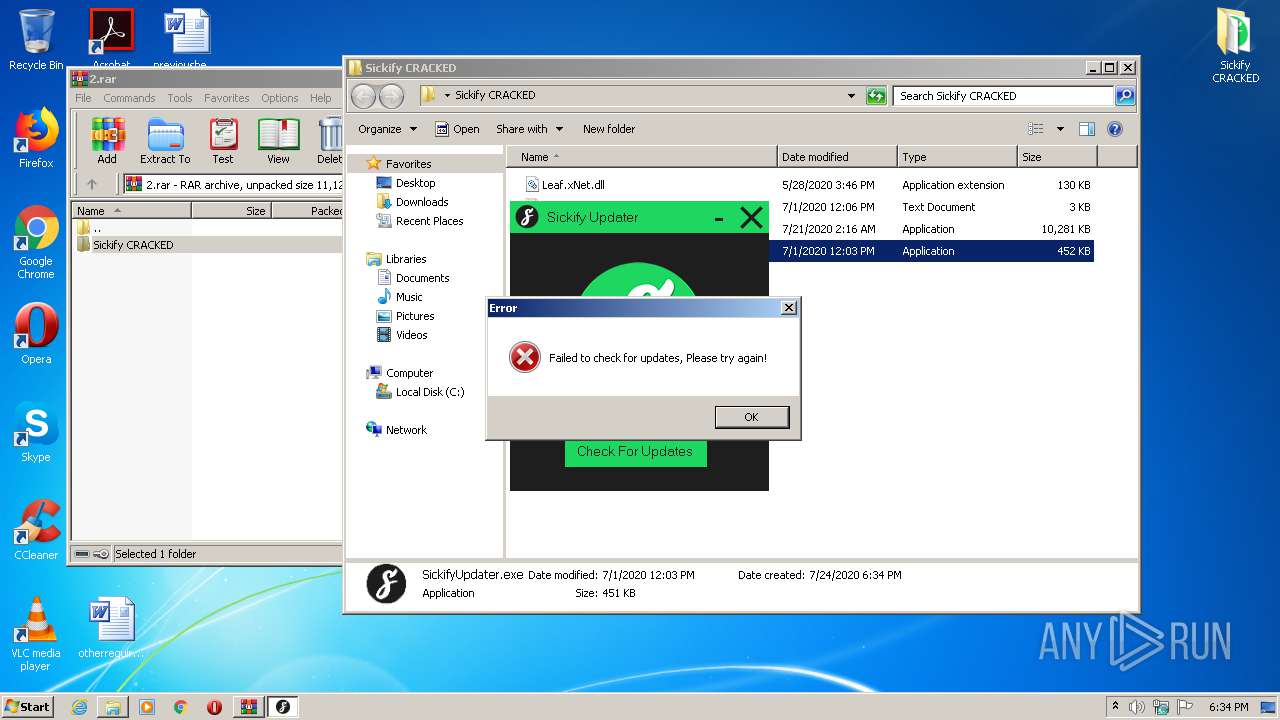
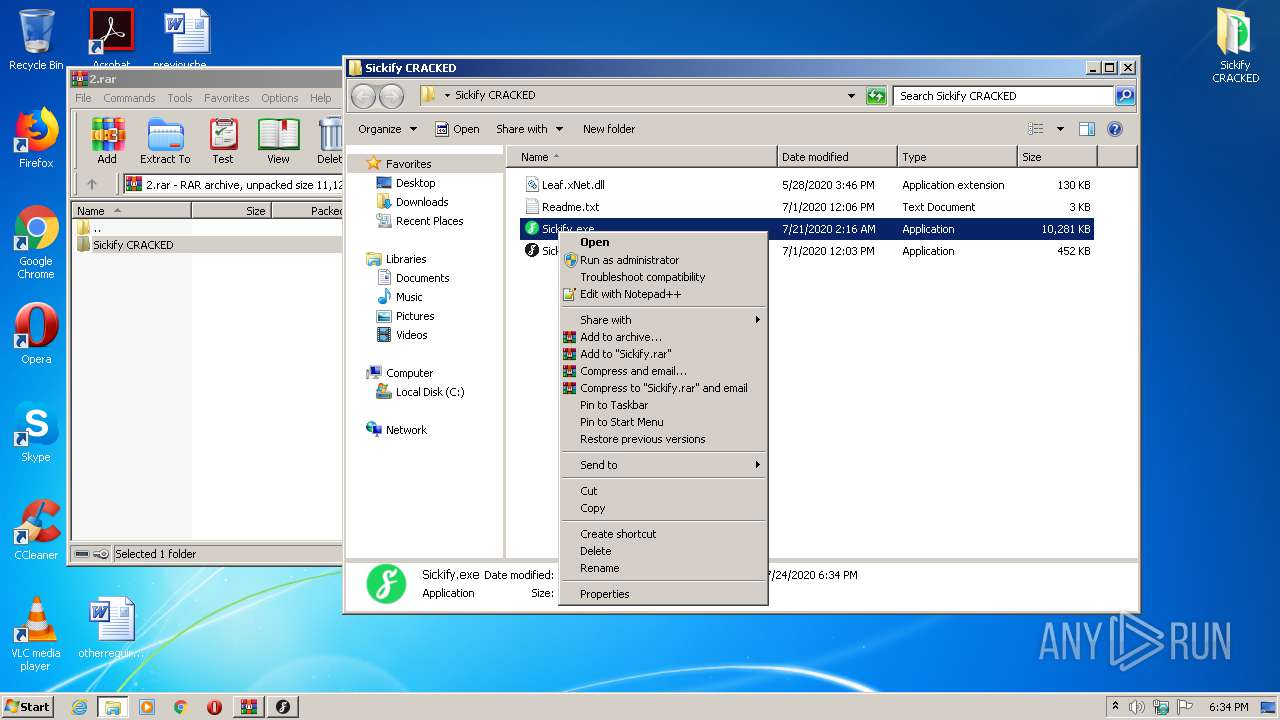
Manual execution by user
- SickifyUpdater.exe (PID: 2664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
40
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
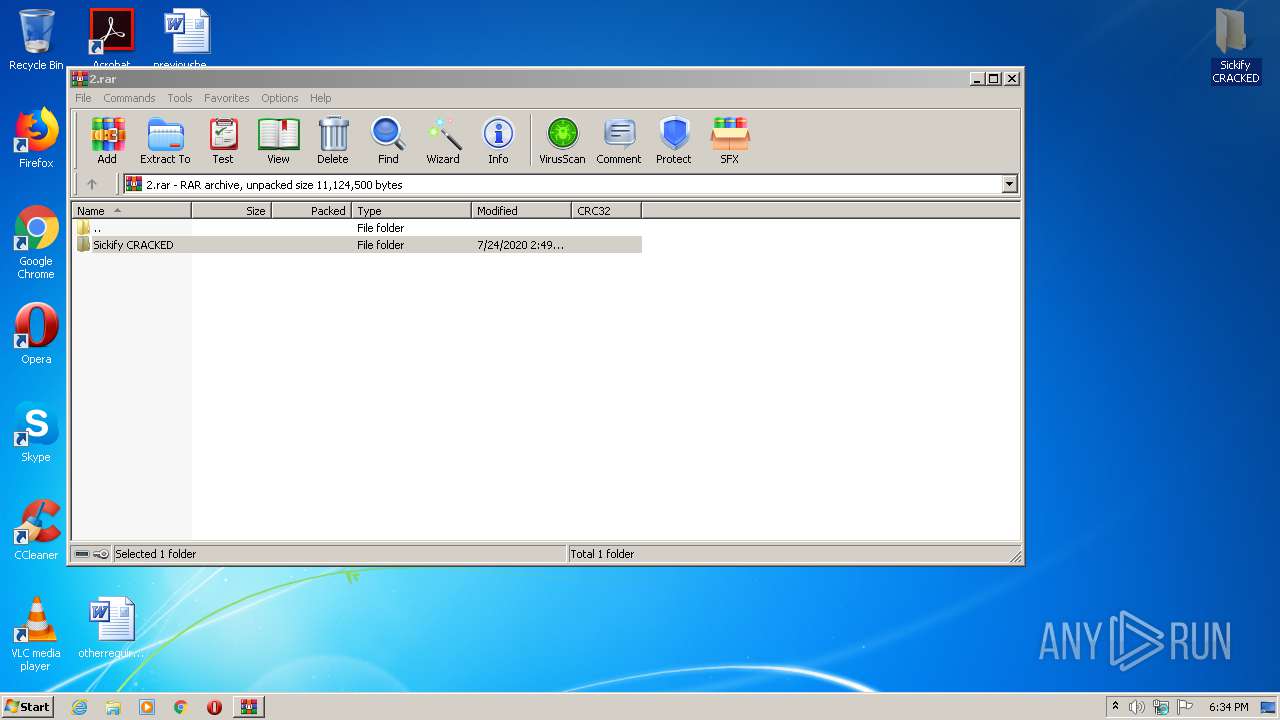
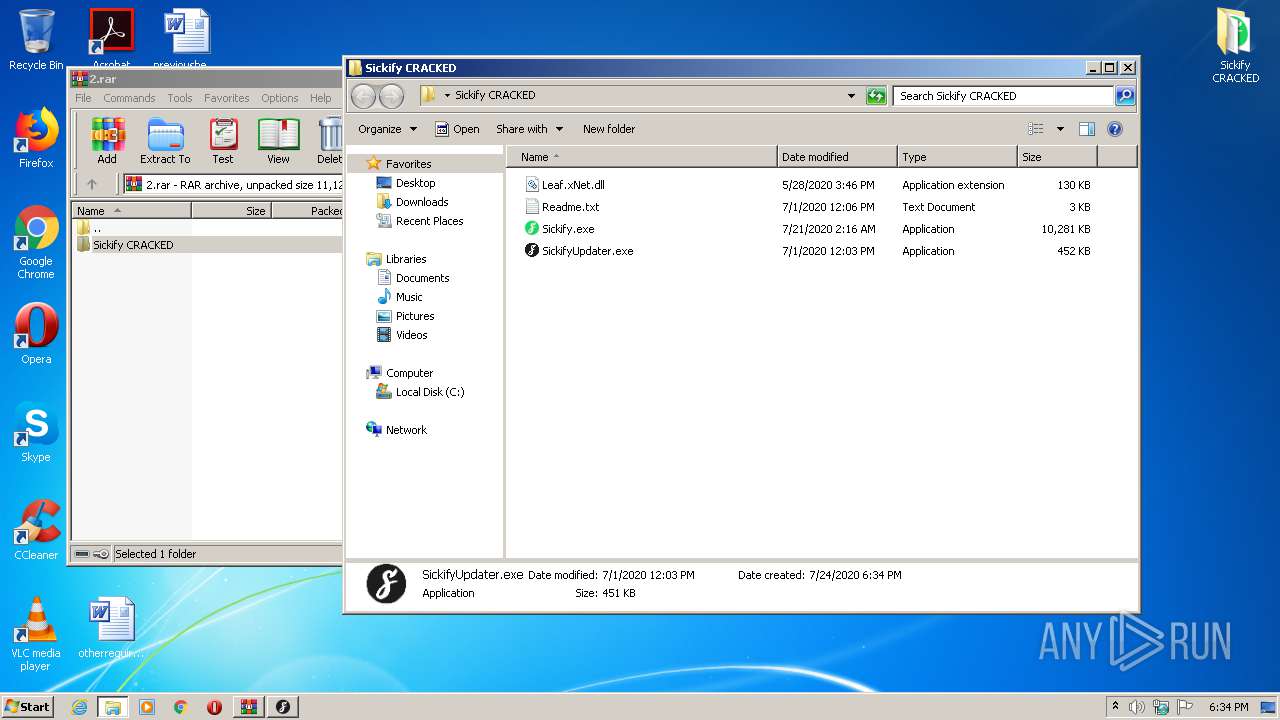
| 2336 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\2.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
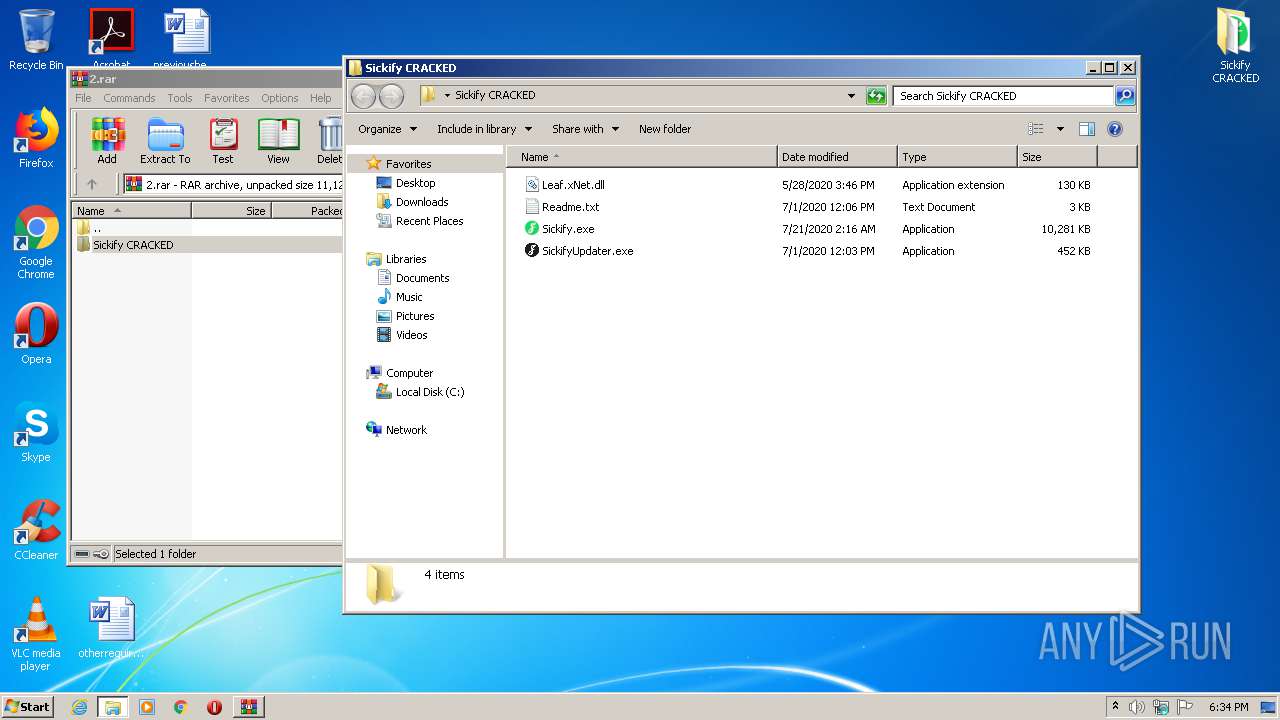
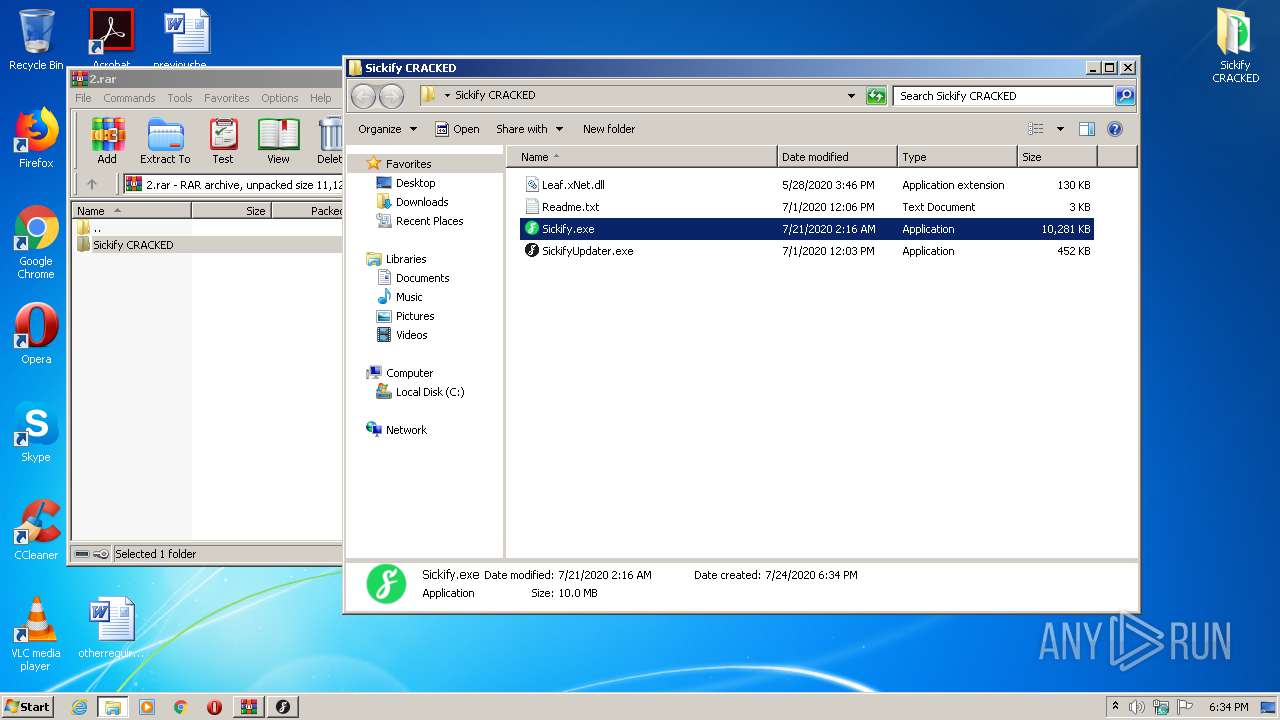
| 2664 | "C:\Users\admin\Desktop\Sickify CRACKED\SickifyUpdater.exe" | C:\Users\admin\Desktop\Sickify CRACKED\SickifyUpdater.exe | explorer.exe | ||||||||||||
User: admin Company: DJR Integrity Level: MEDIUM Description: SickifyUpdater Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 3564 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
817
Read events
784
Write events
33
Delete events
0
Modification events
| (PID) Process: | (2336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2336) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\2.rar | |||
| (PID) Process: | (2336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3564) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3564) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
4
Suspicious files
5
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | SickifyUpdater.exe | C:\Users\admin\AppData\Local\Temp\CabBA29.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | SickifyUpdater.exe | C:\Users\admin\AppData\Local\Temp\TarBA2A.tmp | — | |
MD5:— | SHA256:— | |||
| 2336 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2336.36962\Sickify CRACKED\Readme.txt | text | |
MD5:— | SHA256:— | |||
| 2336 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2336.36962\Sickify CRACKED\SickifyUpdater.exe | executable | |
MD5:— | SHA256:— | |||
| 2664 | SickifyUpdater.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 2664 | SickifyUpdater.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\03B1086BEACE1B21AE277E4081D01594 | der | |
MD5:— | SHA256:— | |||
| 2664 | SickifyUpdater.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\03B1086BEACE1B21AE277E4081D01594 | binary | |
MD5:— | SHA256:— | |||
| 2336 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2336.36962\Sickify CRACKED\Sickify.exe | executable | |
MD5:— | SHA256:— | |||
| 2664 | SickifyUpdater.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A2ECA083537A02B6158458FF1752C63F | binary | |
MD5:— | SHA256:— | |||
| 2664 | SickifyUpdater.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2664 | SickifyUpdater.exe | GET | 200 | 2.16.107.114:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgTs1EUYAvt5l0HL5rVTkJCVGQ%3D%3D | unknown | der | 527 b | whitelisted |
2664 | SickifyUpdater.exe | GET | 200 | 2.16.107.80:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
2664 | SickifyUpdater.exe | GET | 200 | 23.37.41.57:80 | http://cert.int-x3.letsencrypt.org/ | NL | der | 1.15 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2664 | SickifyUpdater.exe | 45.87.80.99:443 | idkwhere.cf | — | — | suspicious |
2664 | SickifyUpdater.exe | 23.37.41.57:80 | cert.int-x3.letsencrypt.org | Akamai Technologies, Inc. | NL | suspicious |
2664 | SickifyUpdater.exe | 2.16.107.80:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | suspicious |
2664 | SickifyUpdater.exe | 2.16.107.114:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
idkwhere.cf |
| suspicious |
cert.int-x3.letsencrypt.org |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .cf Domain |
2664 | SickifyUpdater.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.cf) in TLS SNI |
2664 | SickifyUpdater.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.cf) |
2664 | SickifyUpdater.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.cf) |