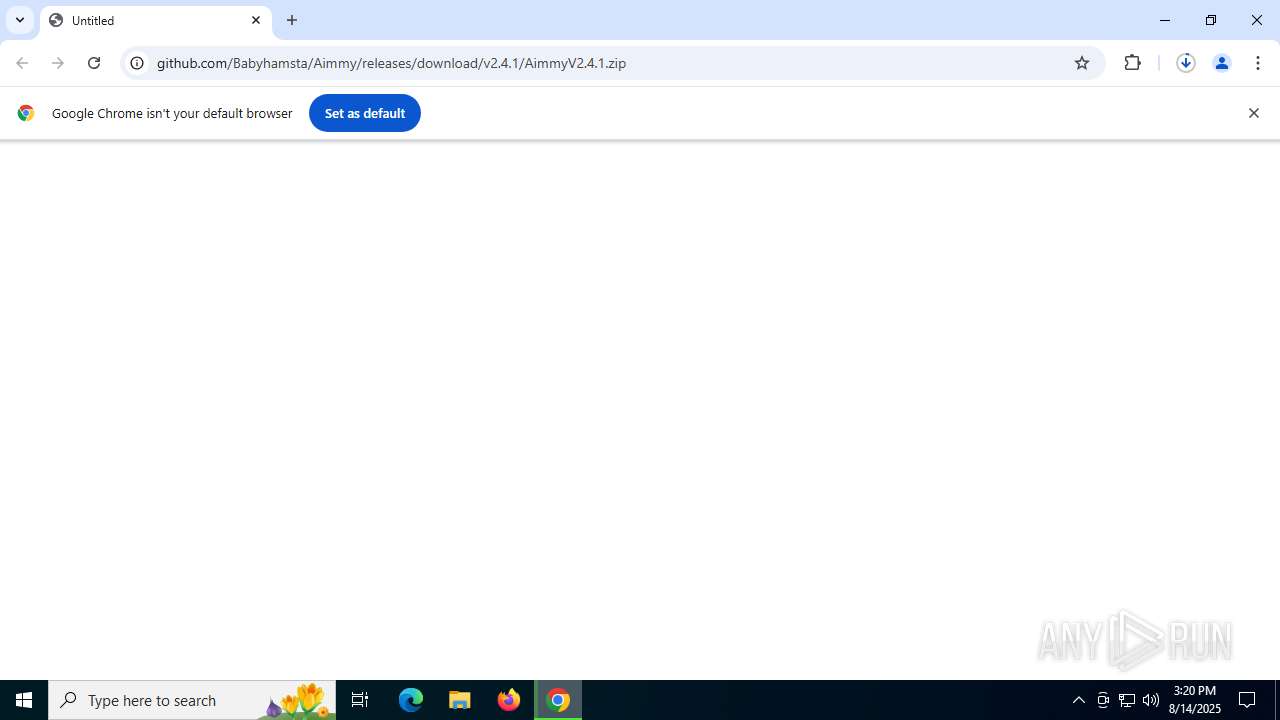
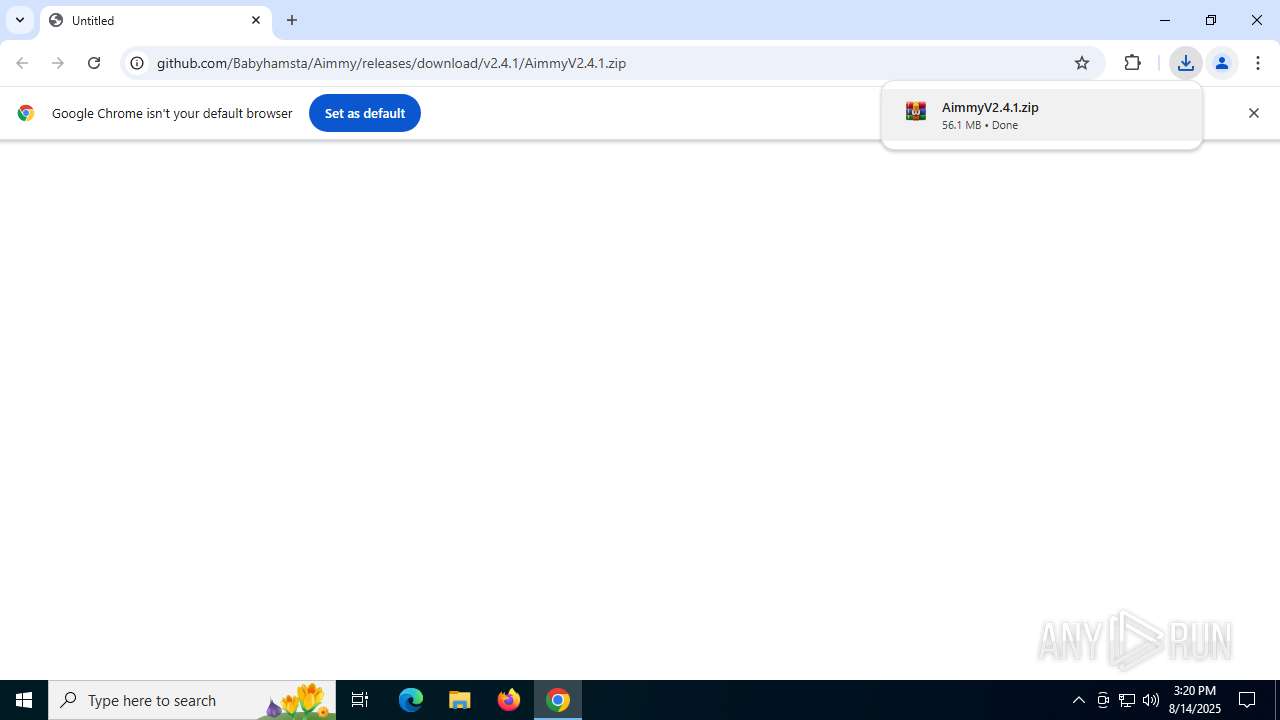
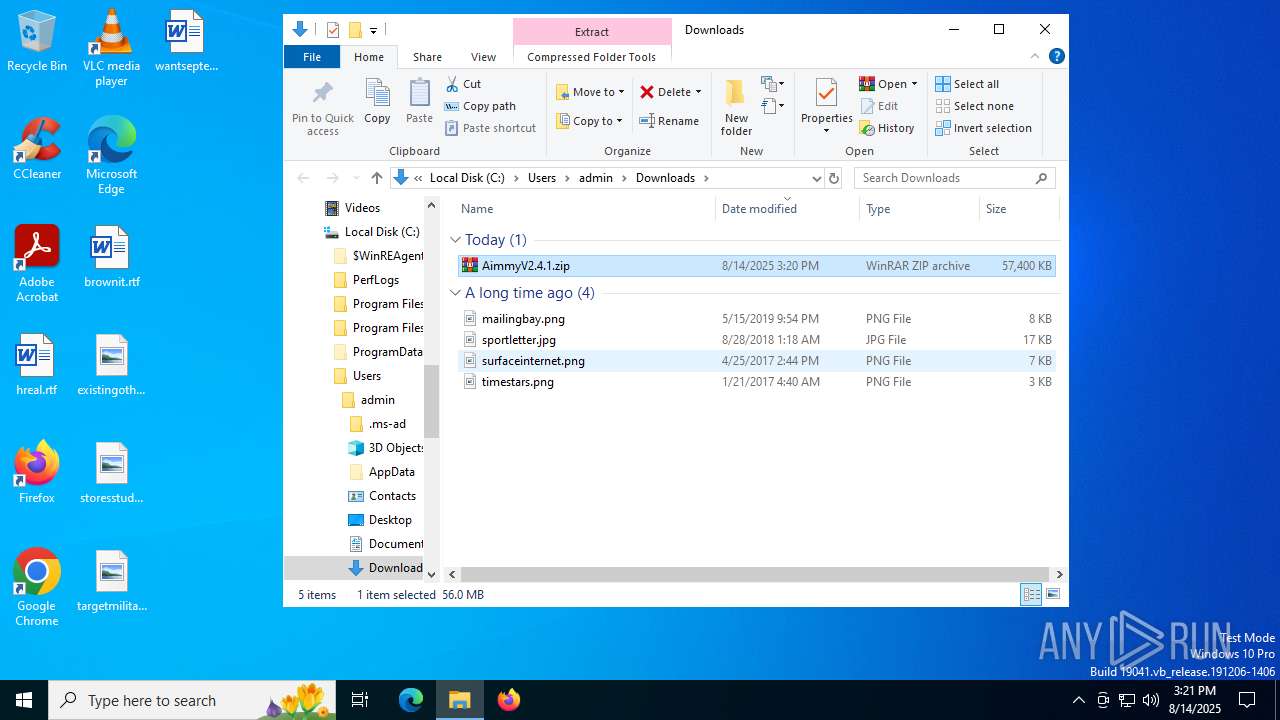
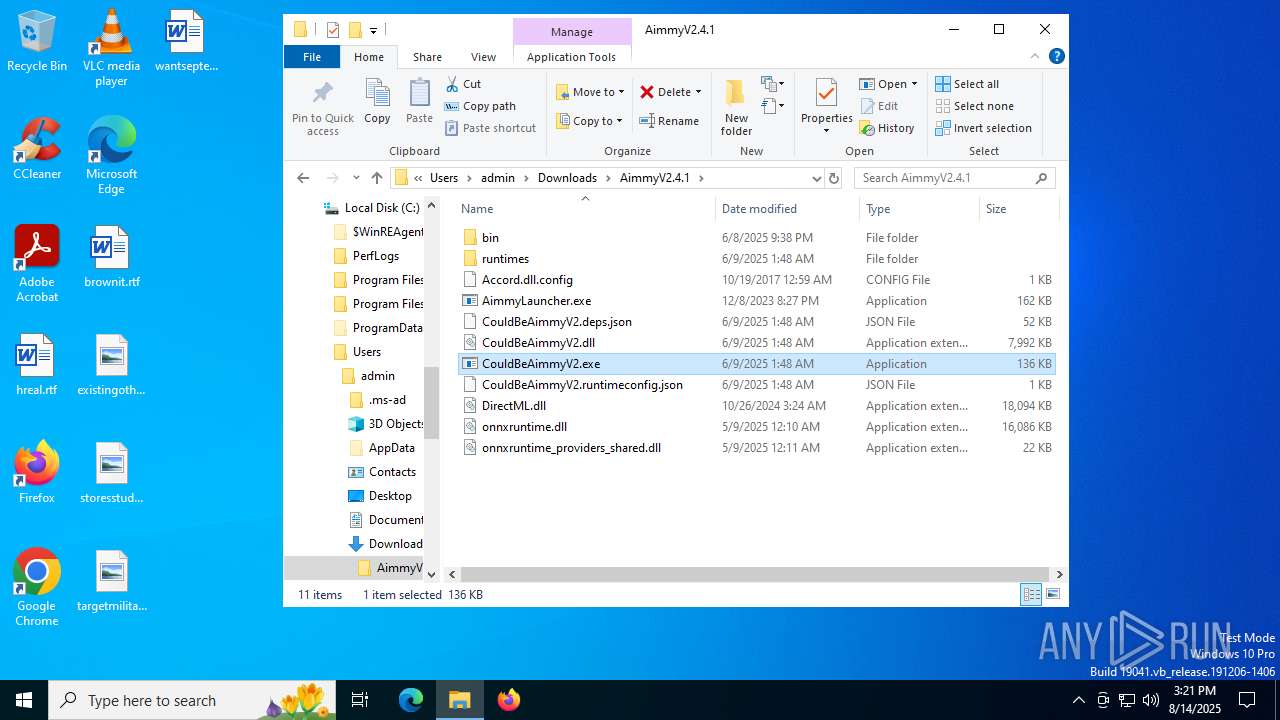
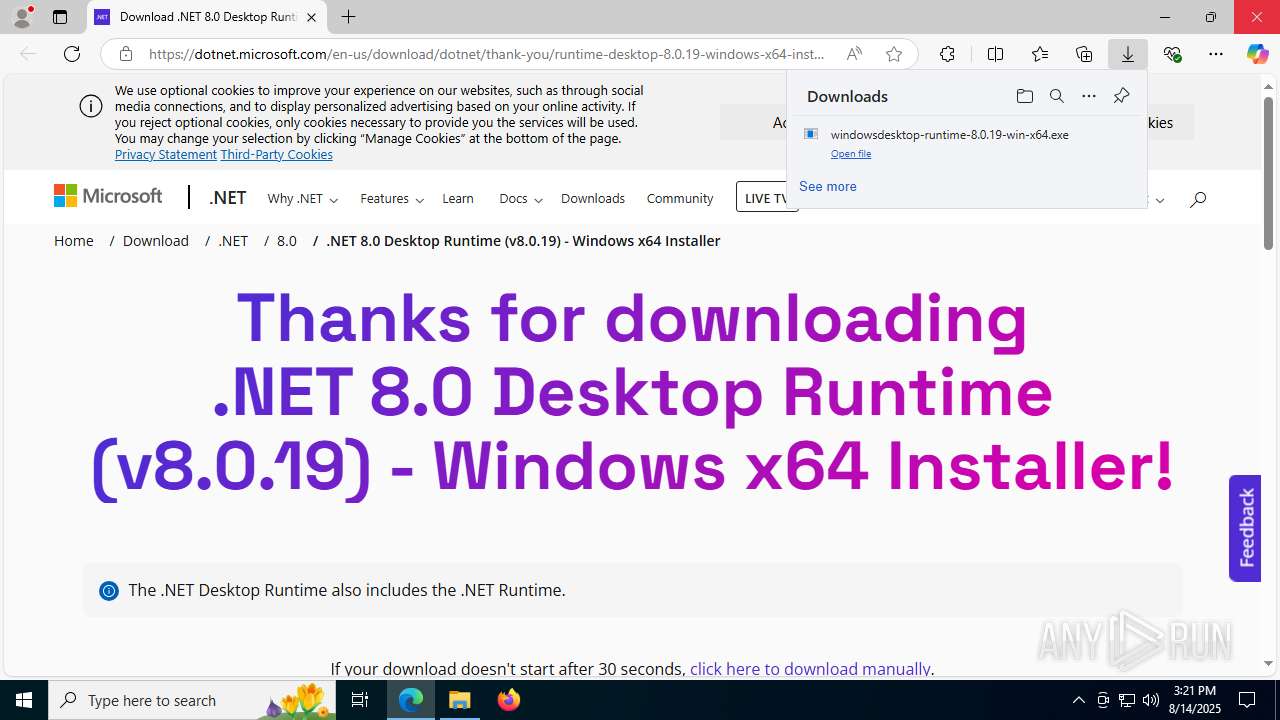
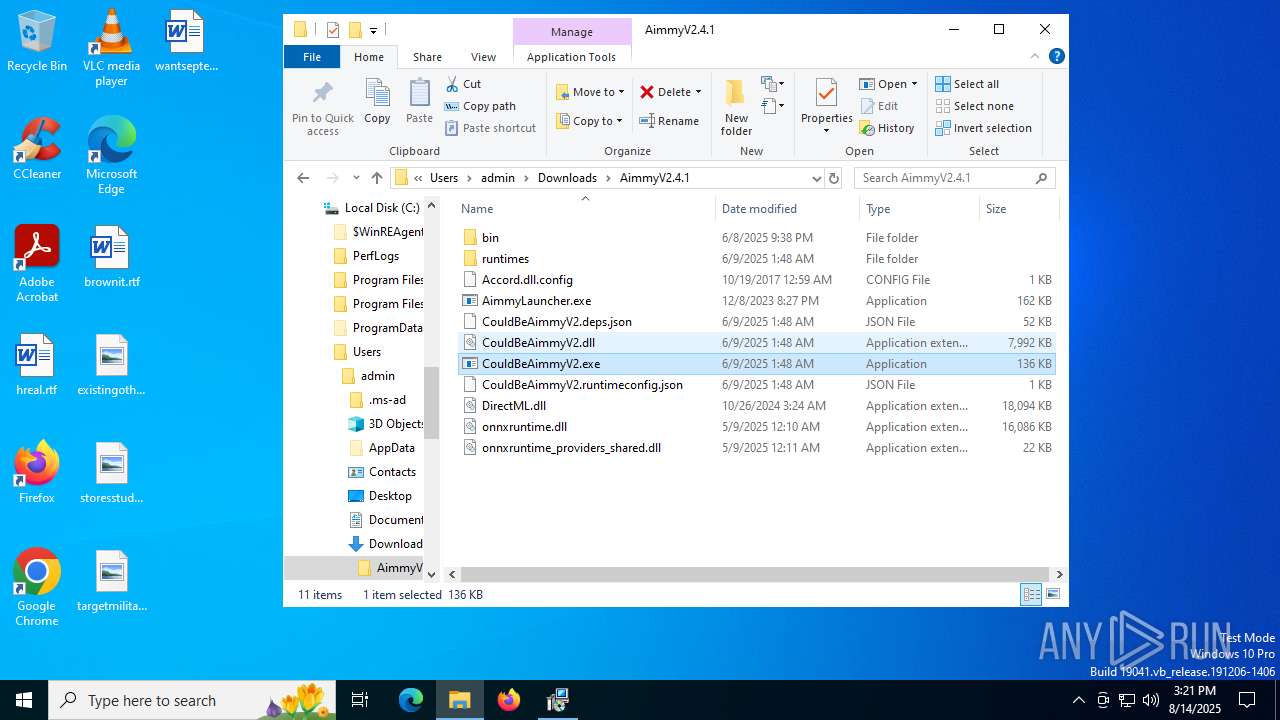
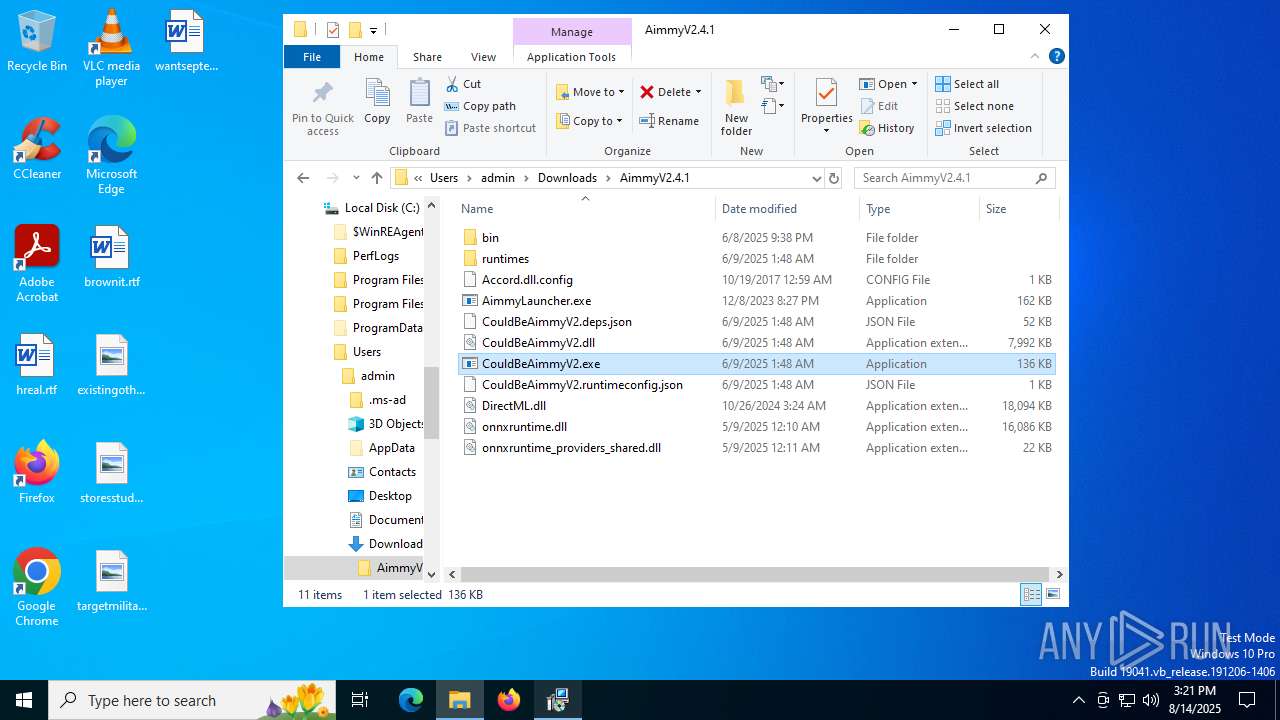
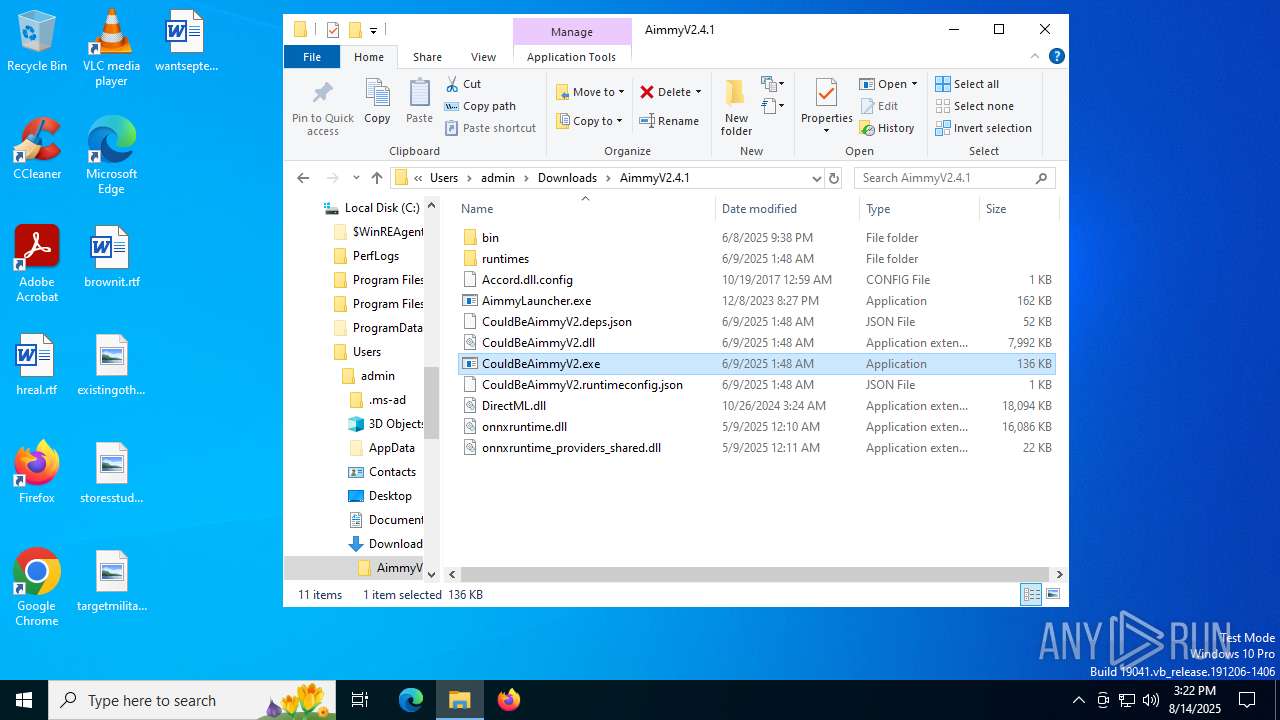
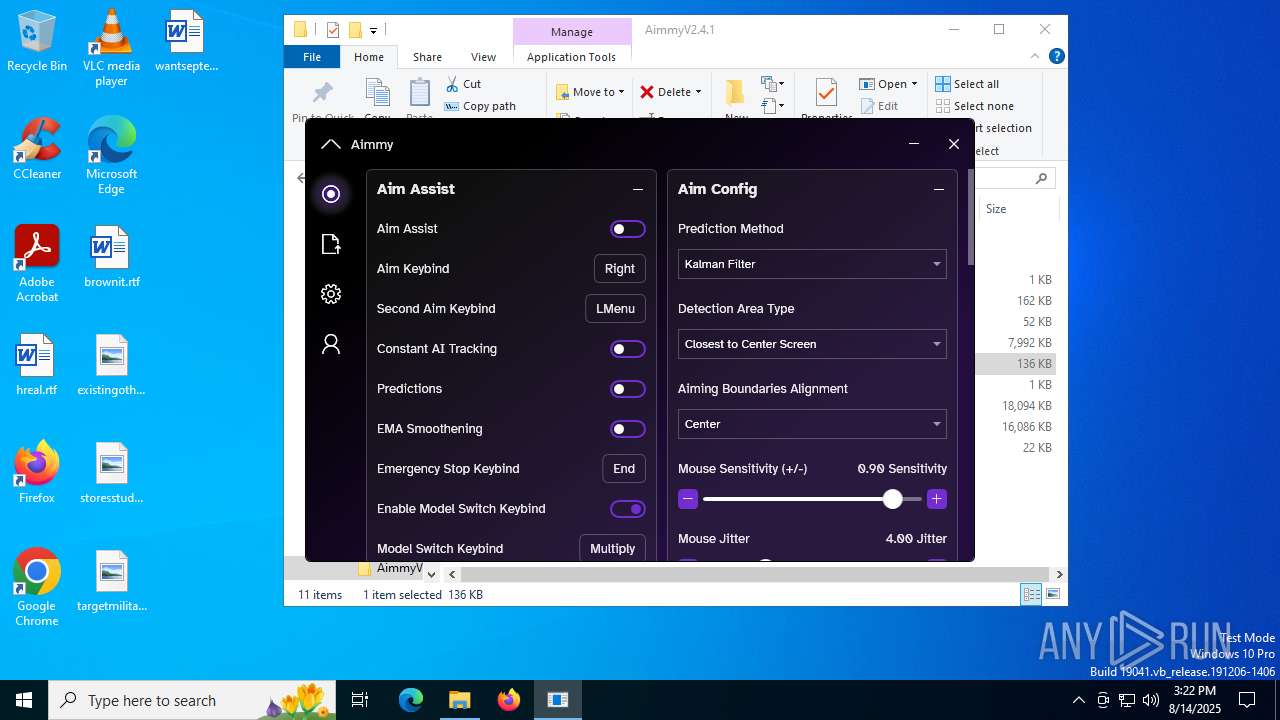
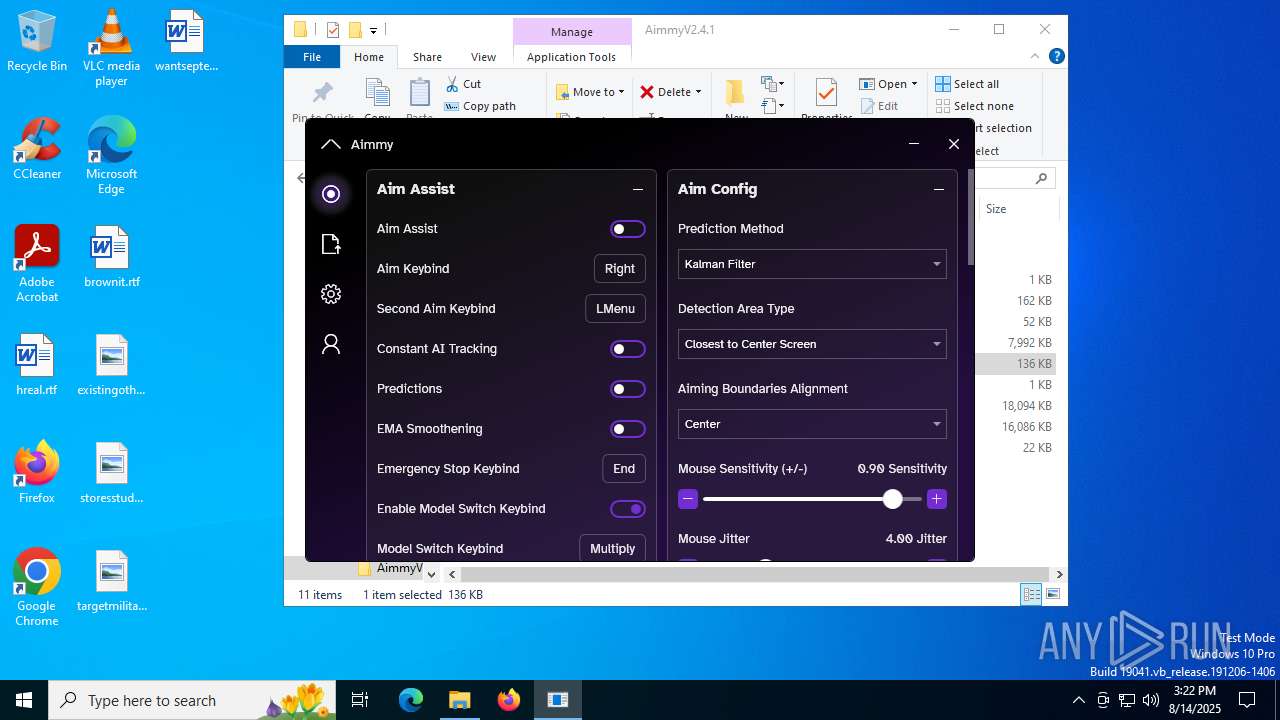
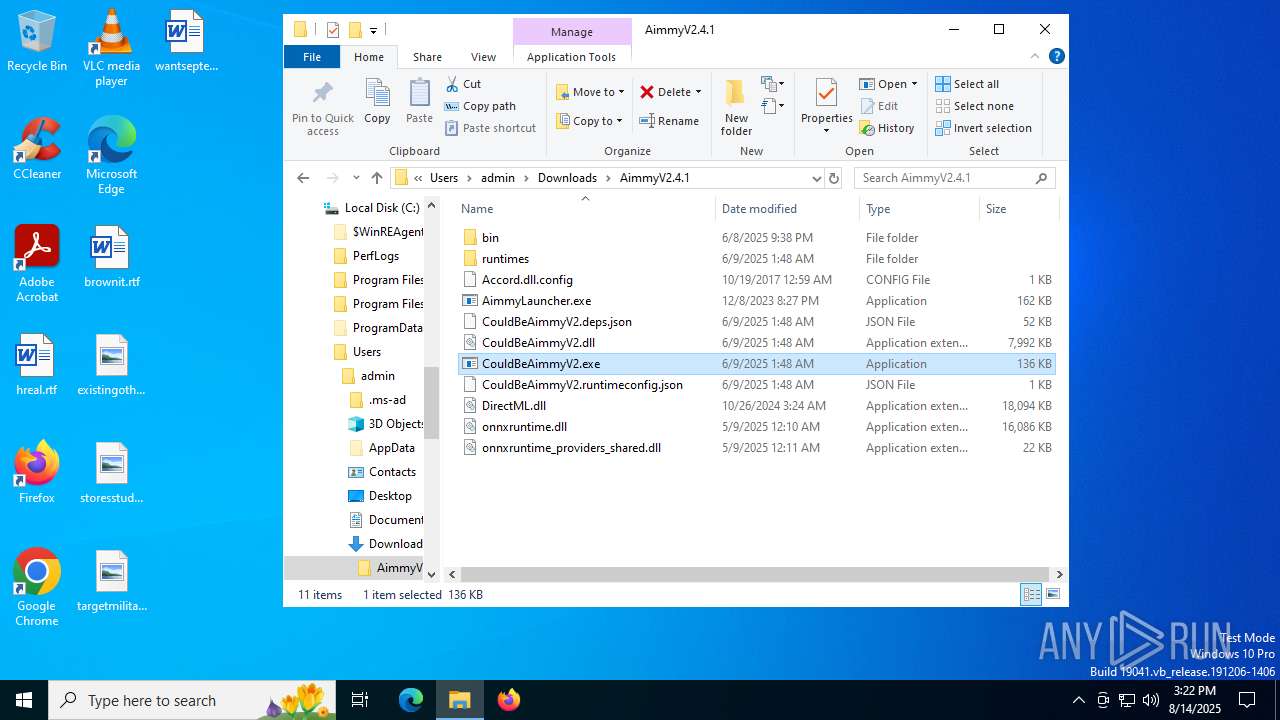
| URL: | https://github.com/Babyhamsta/Aimmy/releases/download/v2.4.1/AimmyV2.4.1.zip |
| Full analysis: | https://app.any.run/tasks/1a8199bb-b10c-4171-9c67-6204233edaa8 |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2025, 15:20:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E955B5CDF95A173F64BDCE8206EBA27E |
| SHA1: | 256A6F2AD80994C851D8C9EF723D196FDA0E6D9B |
| SHA256: | 3454593E61F281DCE2BC1D6D5B1951C2E8CAC73149BBC50A7C4742B3DABDEA3B |
| SSDEEP: | 3:N8tEdU8N7hKcMkCFTkMWpwU:2uyc75MLR4L |
MALICIOUS
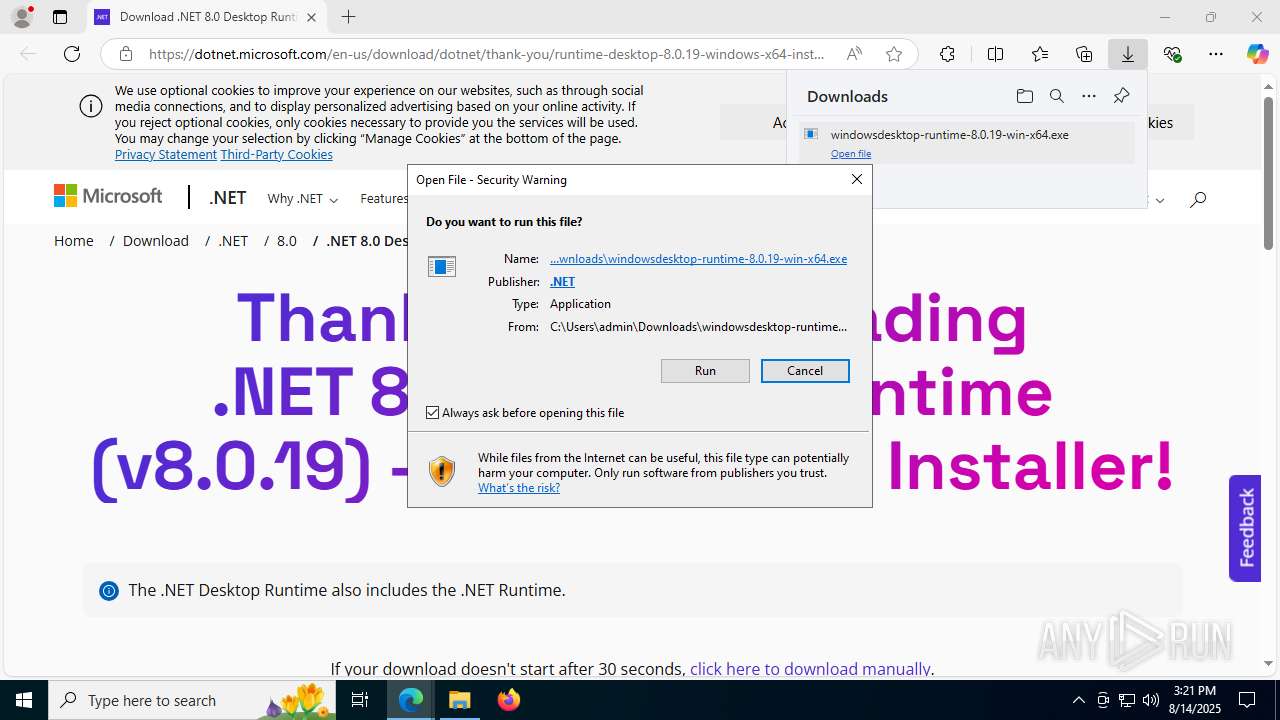
Changes the autorun value in the registry
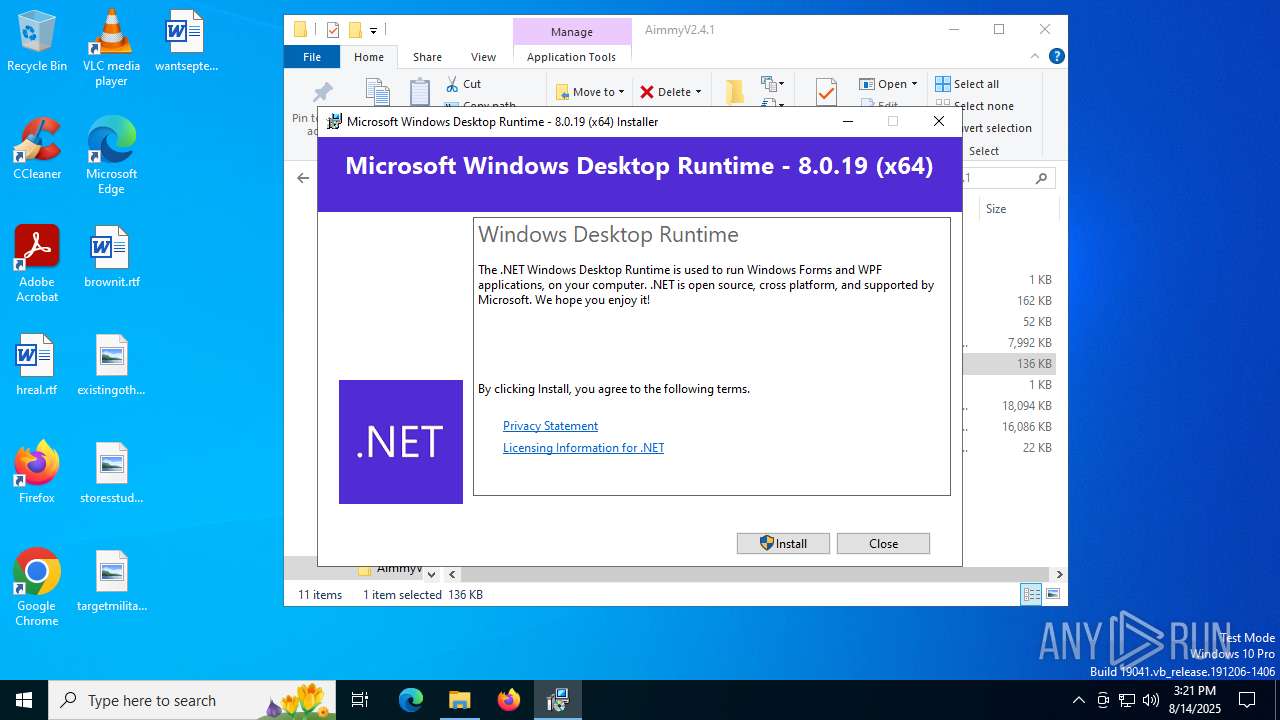
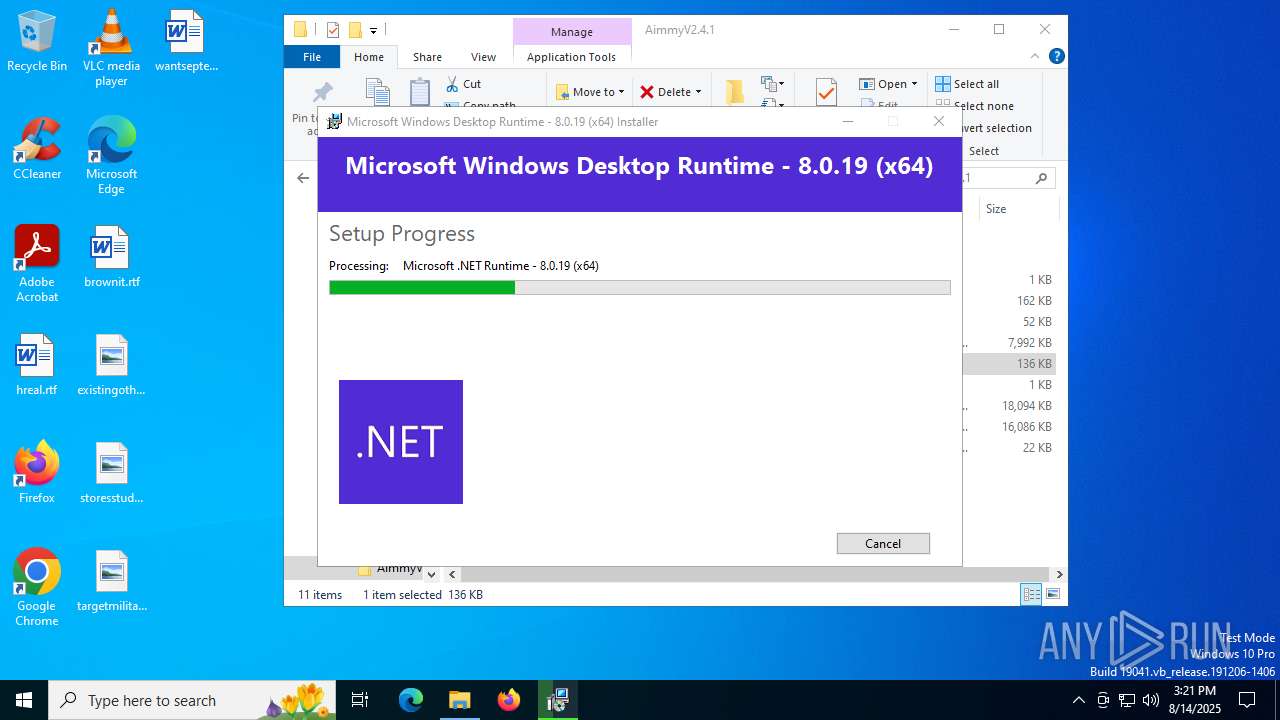
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 4888)
SUSPICIOUS
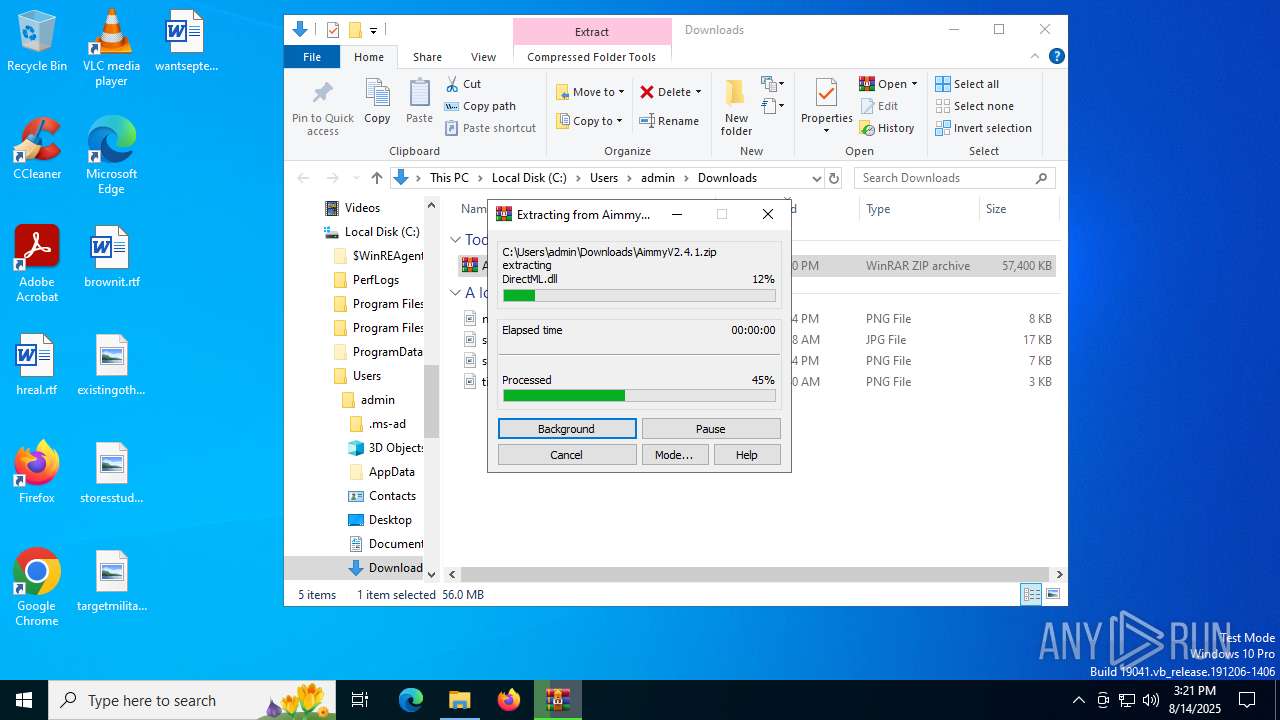
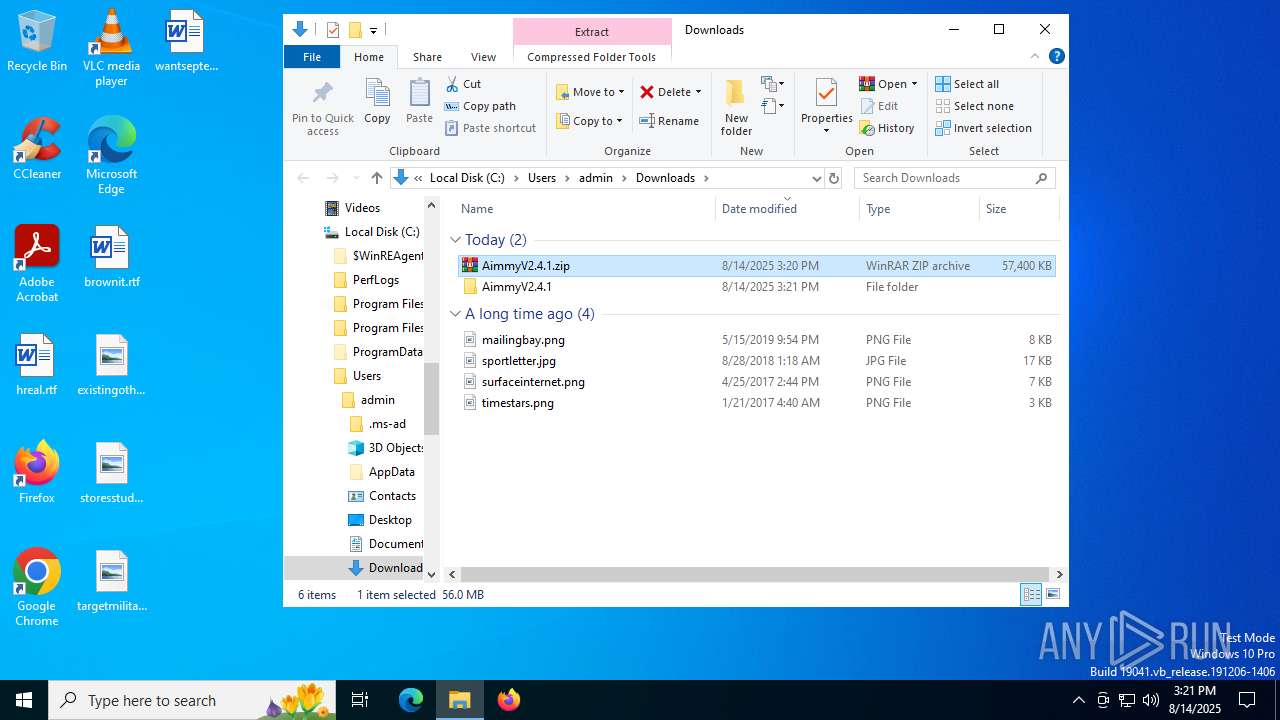
Process drops legitimate windows executable
- WinRAR.exe (PID: 7624)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 7840)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 5244)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 4888)
- msiexec.exe (PID: 4160)
Reads security settings of Internet Explorer
- CouldBeAimmyV2.exe (PID: 7864)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 5244)
- CouldBeAimmyV2.exe (PID: 8116)
Starts a Microsoft application from unusual location
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 5244)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 4888)
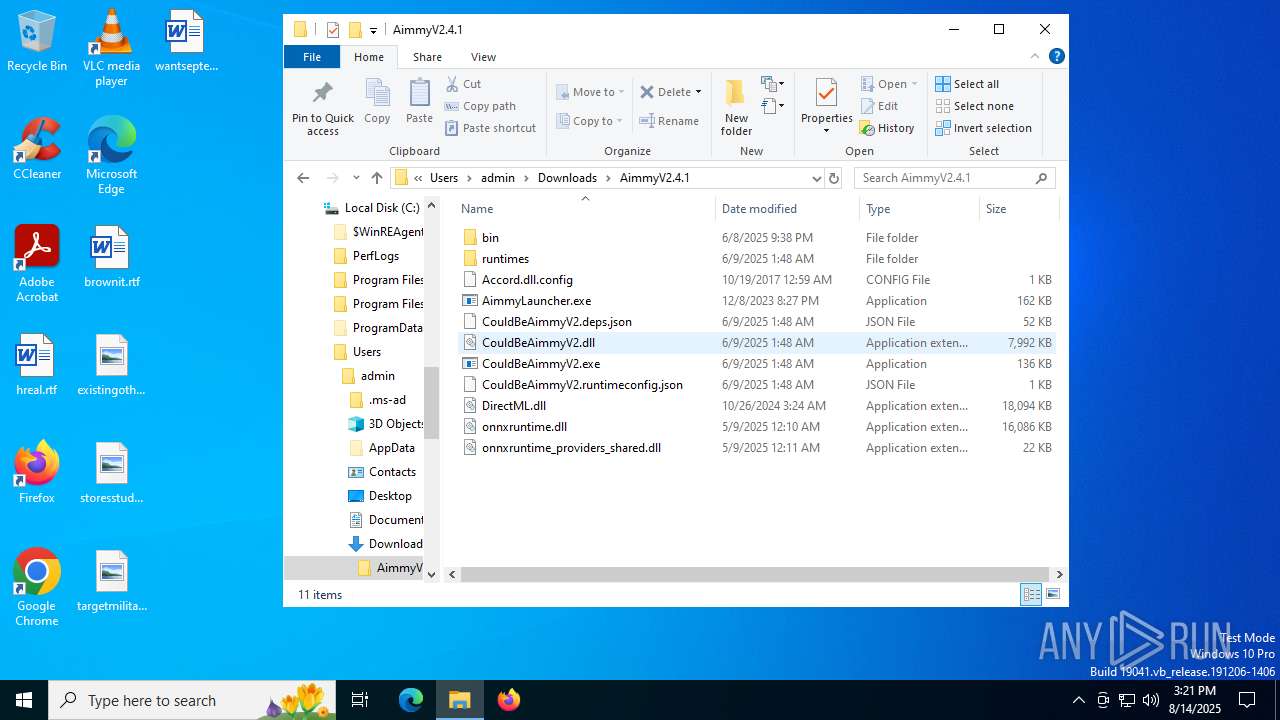
Executable content was dropped or overwritten
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 7840)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 4888)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 5244)
Searches for installed software
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 5244)
Starts itself from another location
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 5244)
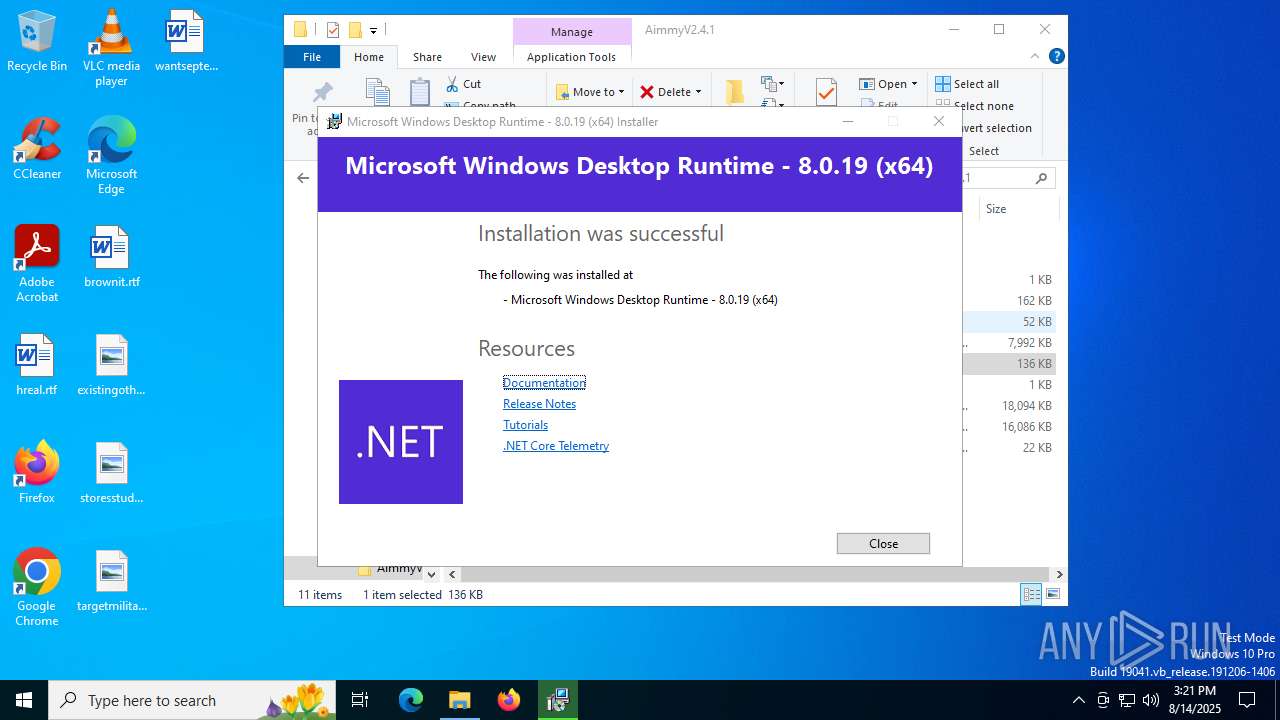
Creates a software uninstall entry
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 4888)
The process creates files with name similar to system file names
- msiexec.exe (PID: 4160)
The process drops C-runtime libraries
- msiexec.exe (PID: 4160)
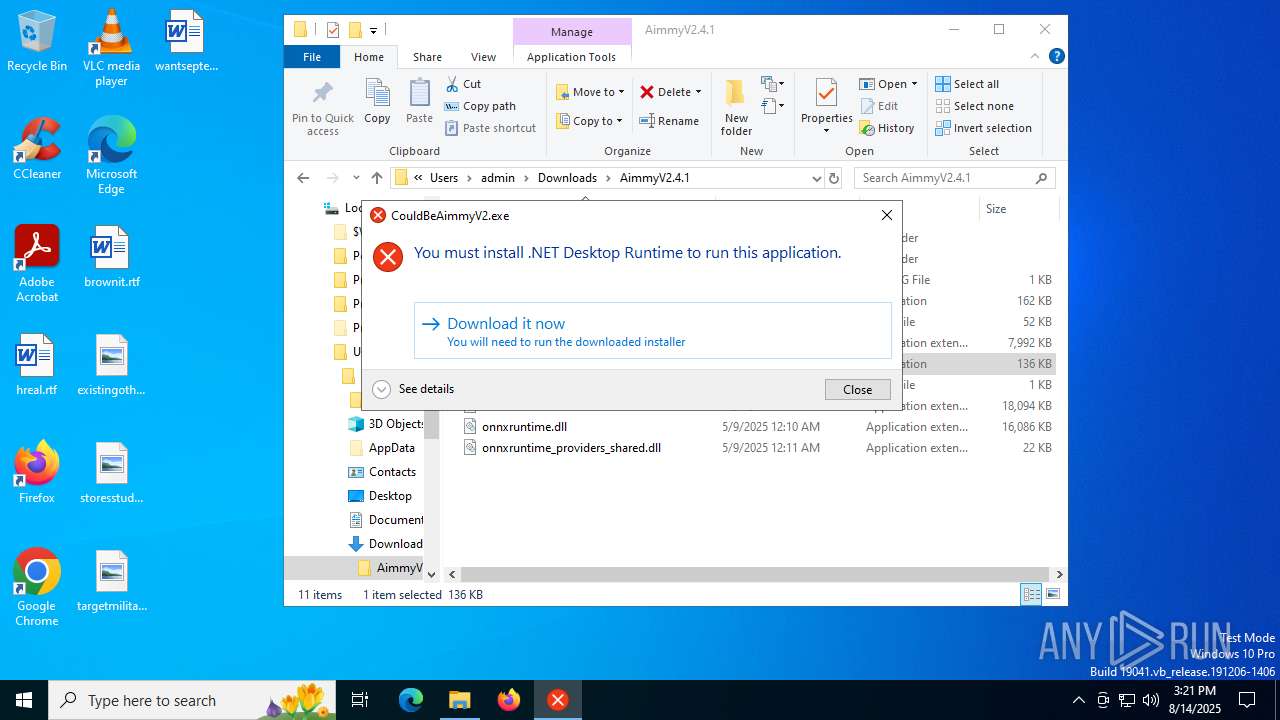
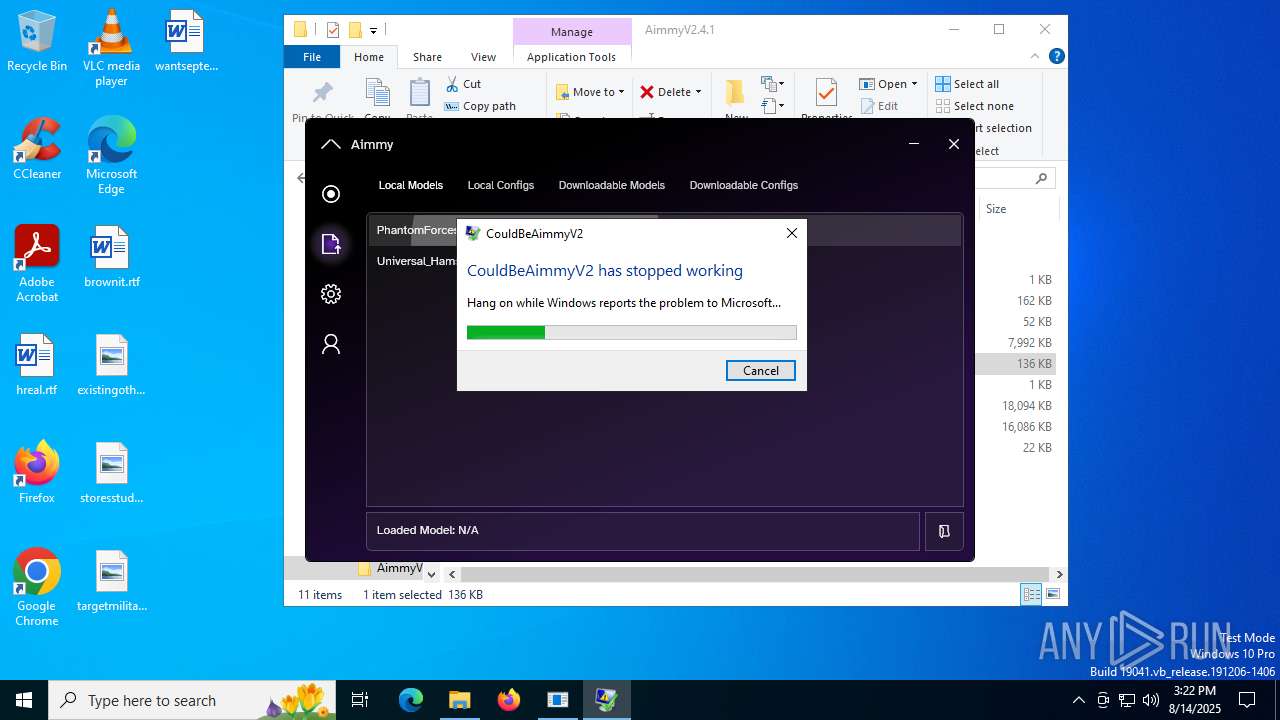
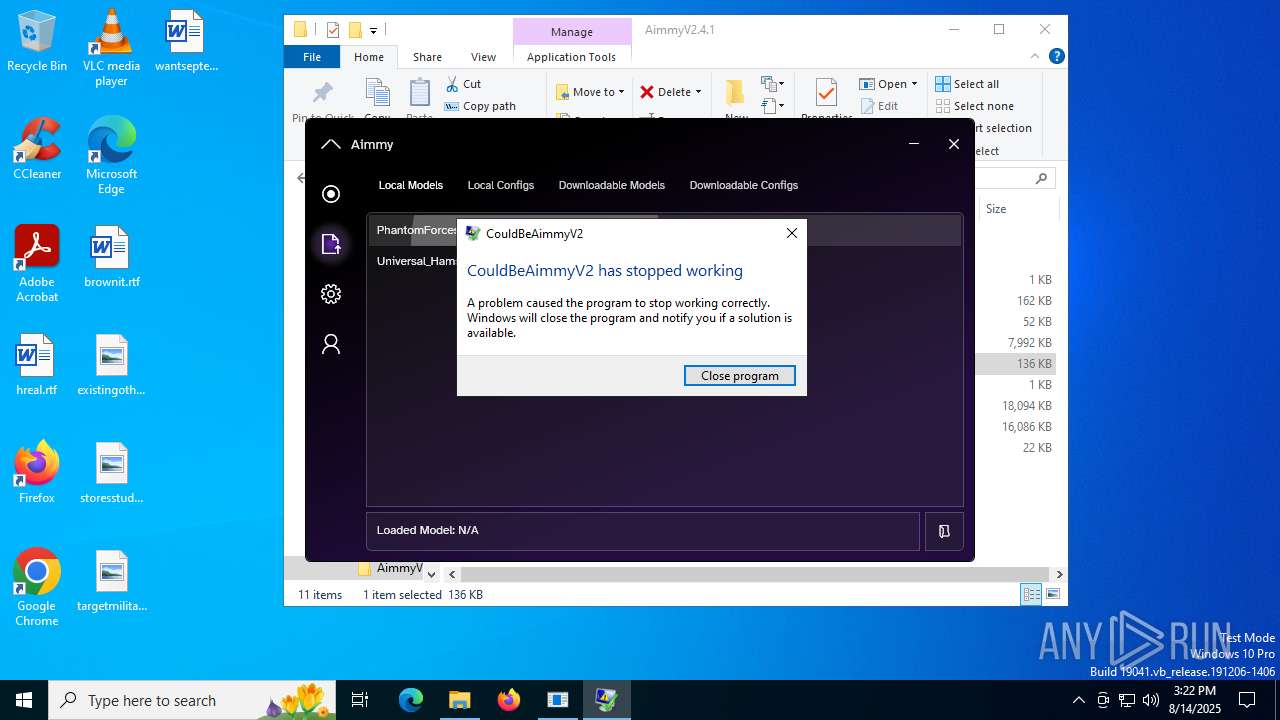
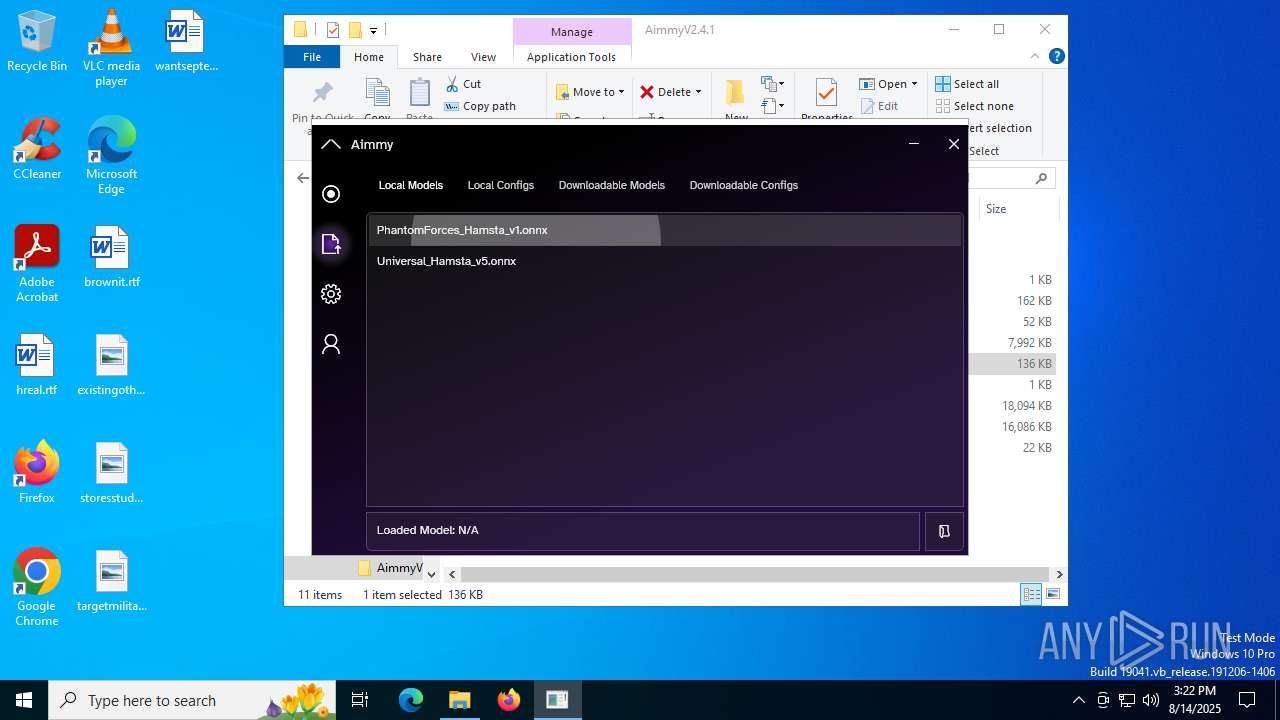
Executes application which crashes
- CouldBeAimmyV2.exe (PID: 8116)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4160)
INFO
Application launched itself
- chrome.exe (PID: 2972)
- msedge.exe (PID: 7948)
- msedge.exe (PID: 7972)
- msedge.exe (PID: 7984)
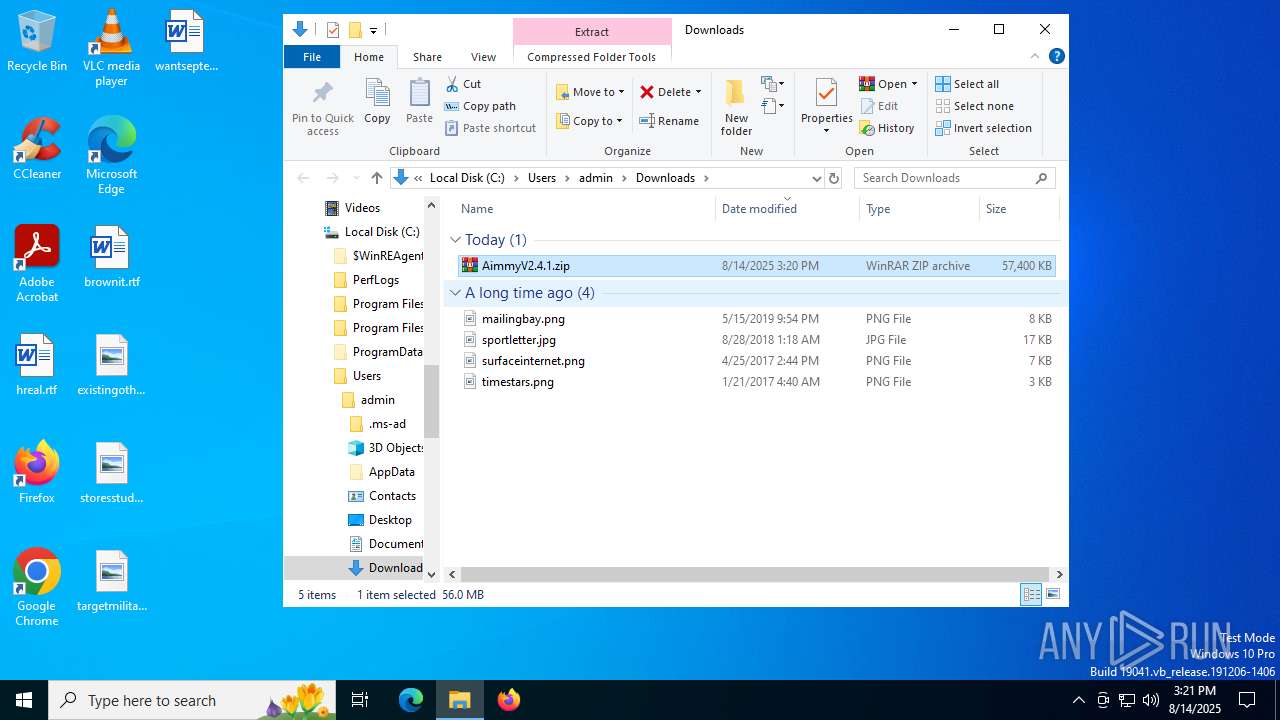
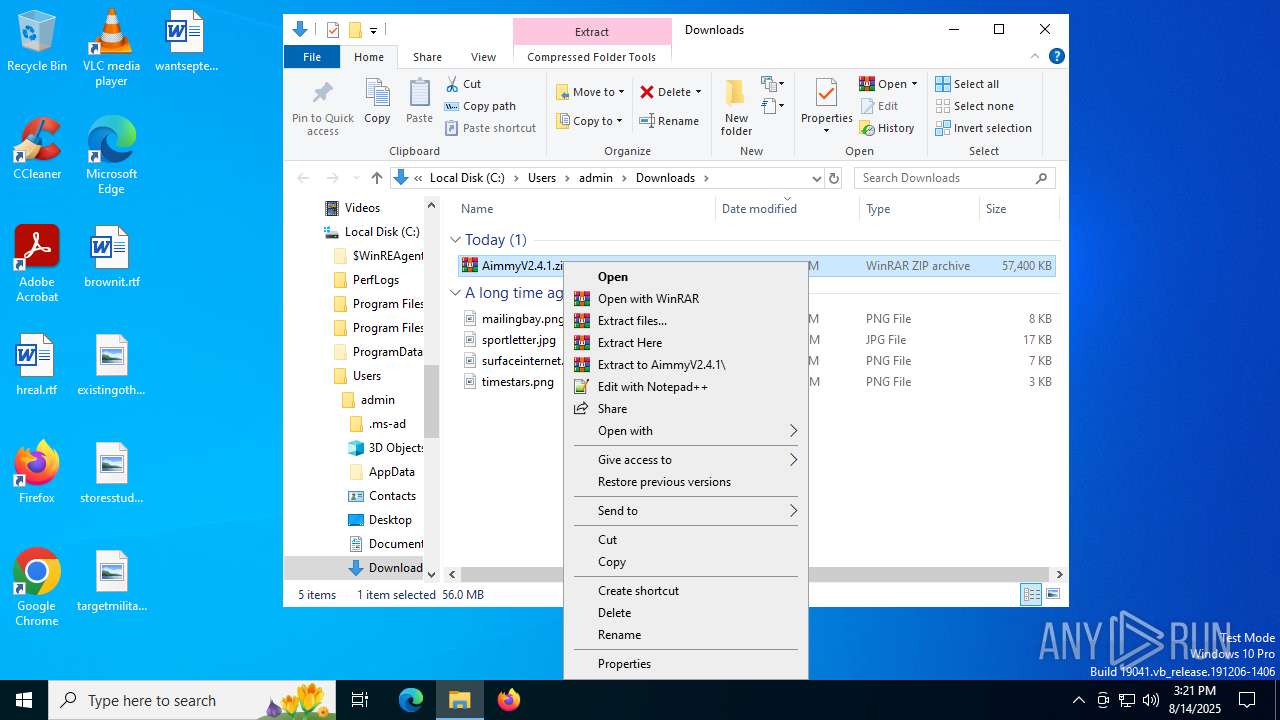
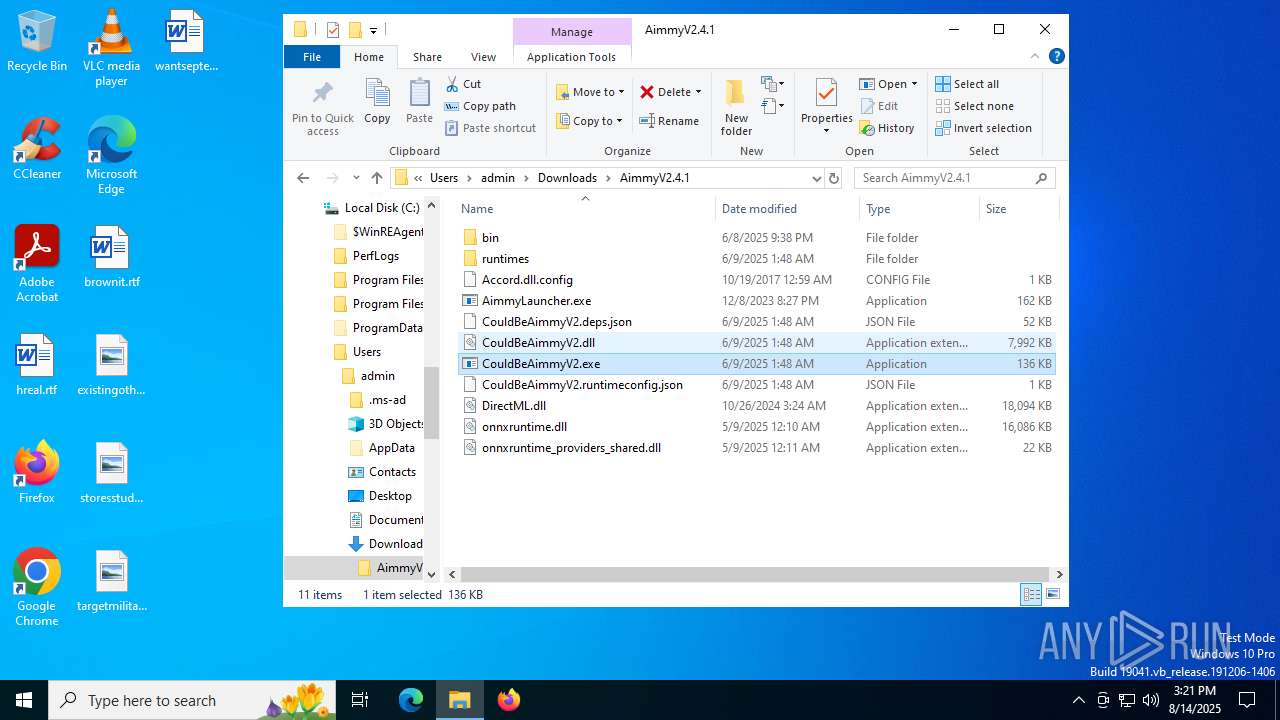
Manual execution by a user
- WinRAR.exe (PID: 7624)
- CouldBeAimmyV2.exe (PID: 7864)
- CouldBeAimmyV2.exe (PID: 8116)
Checks supported languages
- CouldBeAimmyV2.exe (PID: 7864)
- identity_helper.exe (PID: 5184)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 5244)
- identity_helper.exe (PID: 7000)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 4888)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 7840)
- msiexec.exe (PID: 4160)
- msiexec.exe (PID: 6796)
- msiexec.exe (PID: 6412)
- msiexec.exe (PID: 7572)
- msiexec.exe (PID: 7328)
- CouldBeAimmyV2.exe (PID: 8116)
Reads the computer name
- identity_helper.exe (PID: 5184)
- CouldBeAimmyV2.exe (PID: 7864)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 5244)
- identity_helper.exe (PID: 7000)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 4888)
- msiexec.exe (PID: 4160)
- msiexec.exe (PID: 6796)
- msiexec.exe (PID: 7572)
- msiexec.exe (PID: 6412)
- CouldBeAimmyV2.exe (PID: 8116)
- msiexec.exe (PID: 7328)
Create files in a temporary directory
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 7840)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 4888)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 5244)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7624)
- msedge.exe (PID: 7972)
- msiexec.exe (PID: 4160)
The sample compiled with english language support
- WinRAR.exe (PID: 7624)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 7840)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 5244)
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 4888)
- msiexec.exe (PID: 4160)
Reads Environment values
- identity_helper.exe (PID: 7000)
- identity_helper.exe (PID: 5184)
Process checks computer location settings
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 5244)
Creates files in the program directory
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 4888)
- CouldBeAimmyV2.exe (PID: 8116)
Launching a file from a Registry key
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 4888)
Reads the machine GUID from the registry
- windowsdesktop-runtime-8.0.19-win-x64.exe (PID: 4888)
- msiexec.exe (PID: 4160)
Reads the software policy settings
- msiexec.exe (PID: 4160)
- CouldBeAimmyV2.exe (PID: 8116)
- slui.exe (PID: 5476)
- WerFault.exe (PID: 7568)
Creates a software uninstall entry
- msiexec.exe (PID: 4160)
Checks proxy server information
- CouldBeAimmyV2.exe (PID: 8116)
- WerFault.exe (PID: 7568)
- slui.exe (PID: 5476)
Creates files or folders in the user directory
- WerFault.exe (PID: 5084)
- WerFault.exe (PID: 6748)
- WerFault.exe (PID: 4512)
- WerFault.exe (PID: 7500)
- WerFault.exe (PID: 7568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
211
Monitored processes
63
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3656,i,16317148926618602966,6691611779727543624,262144 --variations-seed-version --mojo-platform-channel-handle=5200 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2148,i,16317148926618602966,6691611779727543624,262144 --variations-seed-version --mojo-platform-channel-handle=2556 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1100 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5796,i,6995268885153859653,12932094514183201427,262144 --variations-seed-version --mojo-platform-channel-handle=5752 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6712,i,6995268885153859653,12932094514183201427,262144 --variations-seed-version --mojo-platform-channel-handle=7364 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5156,i,16317148926618602966,6691611779727543624,262144 --variations-seed-version --mojo-platform-channel-handle=4932 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffc4424fff8,0x7ffc44250004,0x7ffc44250010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2464 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2248,i,6995268885153859653,12932094514183201427,262144 --variations-seed-version --mojo-platform-channel-handle=2988 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://github.com/Babyhamsta/Aimmy/releases/download/v2.4.1/AimmyV2.4.1.zip" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3460 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3668,i,6995268885153859653,12932094514183201427,262144 --variations-seed-version --mojo-platform-channel-handle=3712 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2748,i,16317148926618602966,6691611779727543624,262144 --variations-seed-version --mojo-platform-channel-handle=2592 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
36 994
Read events
36 035
Write events
912
Delete events
47
Modification events
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (7624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
500
Suspicious files
352
Text files
163
Unknown types
100
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF18d4b0.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF18d4cf.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF18d4cf.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF18d4cf.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF18d4cf.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
99
DNS requests
110
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.26:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6620 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5744 | chrome.exe | GET | 200 | 172.217.18.14:80 | http://clients2.google.com/time/1/current?cup2key=8:FwZt2x5a4o5sNPRvY6B818RvtSwGvtoZnNRDFB6wH4g&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4664 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:OaM_CjxoUr8O3lUnljSIC3riWPXM637K01huhqTiCb0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
6620 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7972 | msedge.exe | GET | 200 | 23.216.77.31:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7972 | msedge.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
6236 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1755363214&P2=404&P3=2&P4=QKSg9EE4OjncxBvC4l5NbqP0RkmLNCKHYPx7BPhlvLq8i%2bA2%2f9TNPT6Mx3QTgrgTGxEDHkEsFbNNpZ7AjI6pTA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6764 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5744 | chrome.exe | 172.217.18.14:80 | clients2.google.com | GOOGLE | US | whitelisted |
5744 | chrome.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
5744 | chrome.exe | 142.250.185.202:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
5744 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5744 | chrome.exe | 185.199.110.133:443 | release-assets.githubusercontent.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
github.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
release-assets.githubusercontent.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5744 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
Process | Message |
|---|---|
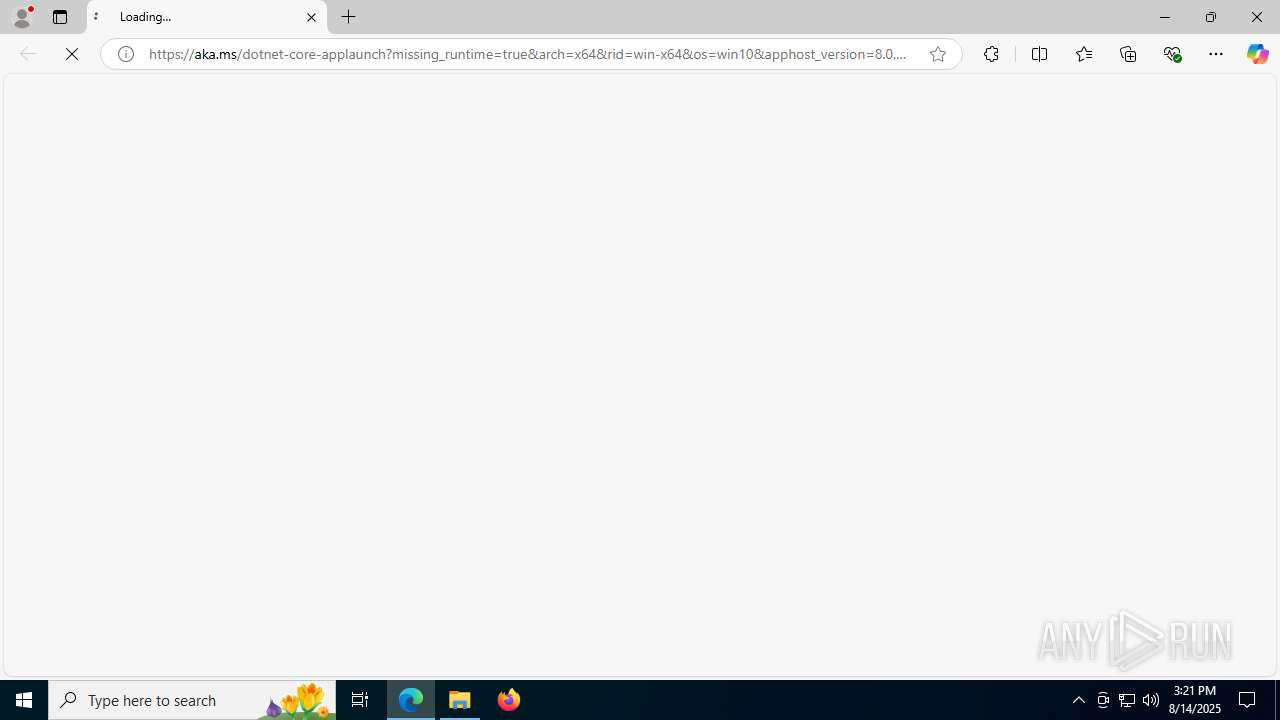
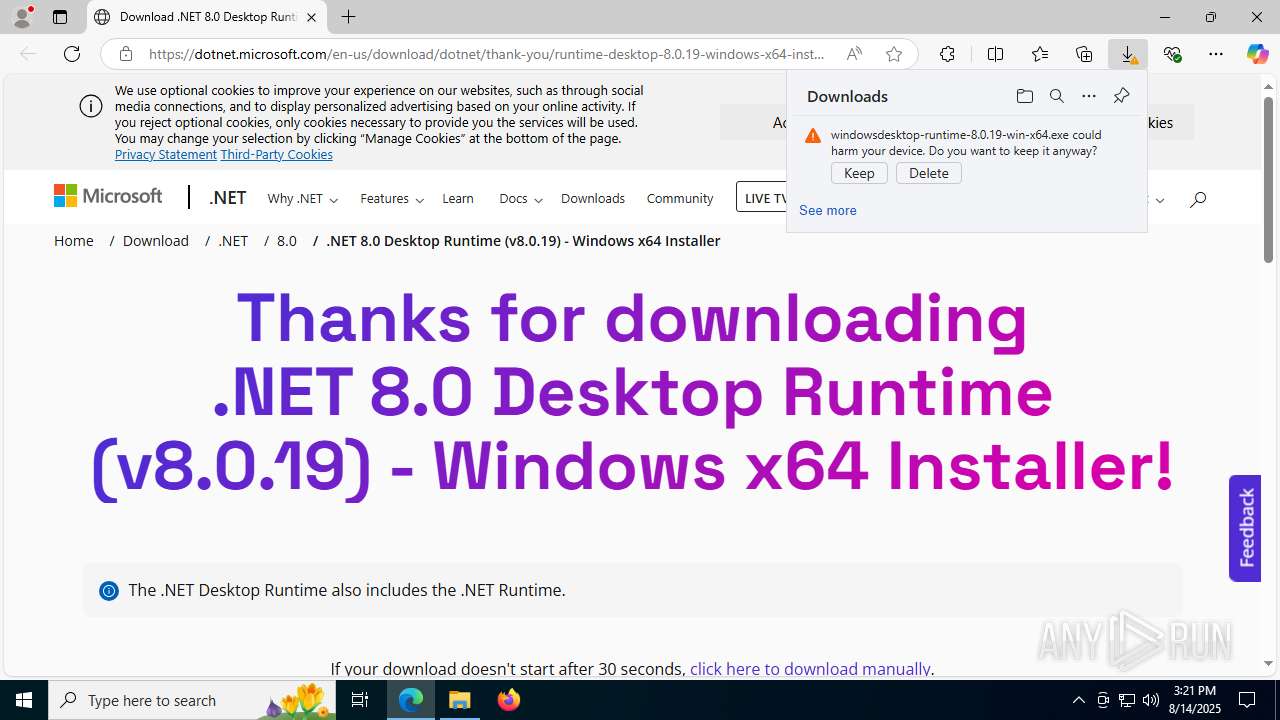
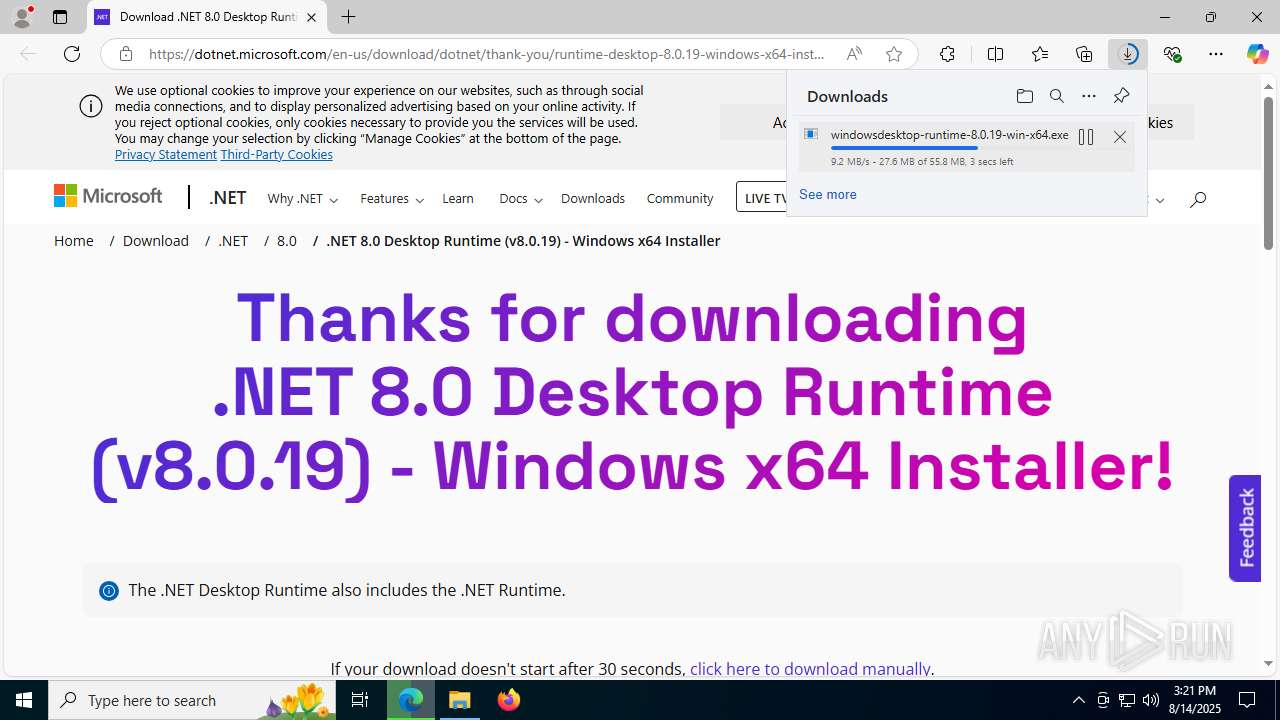
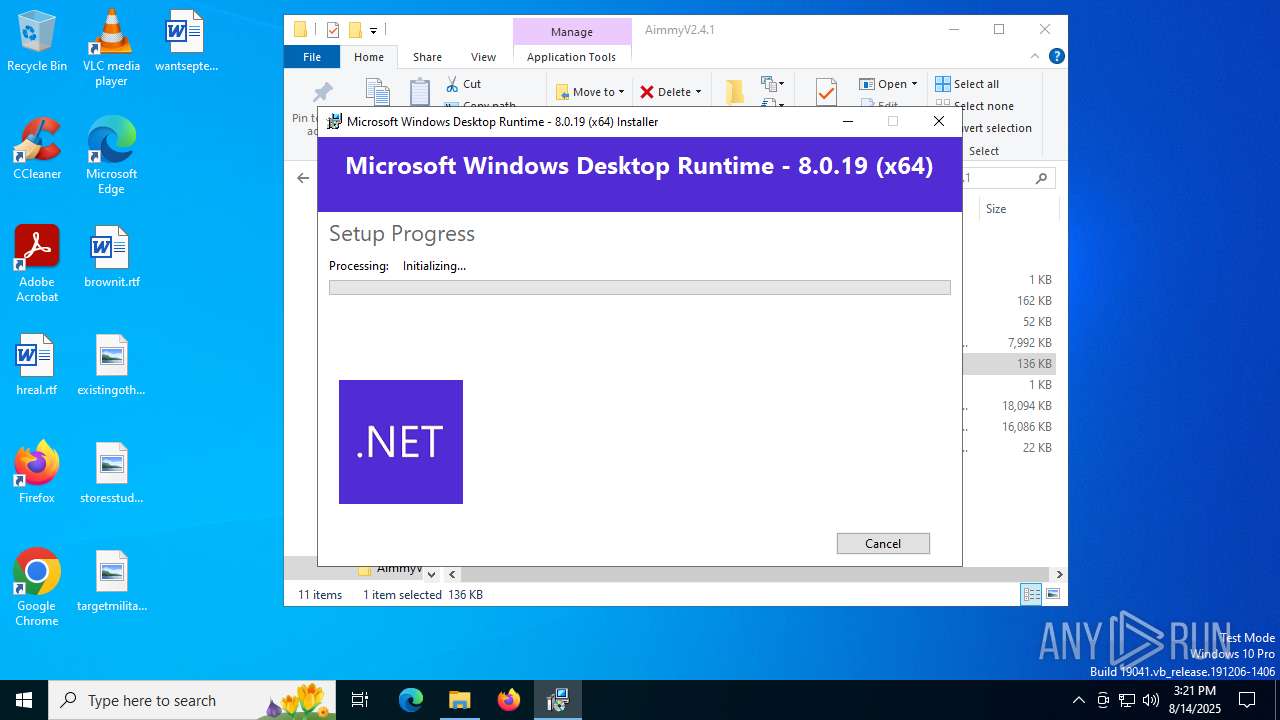
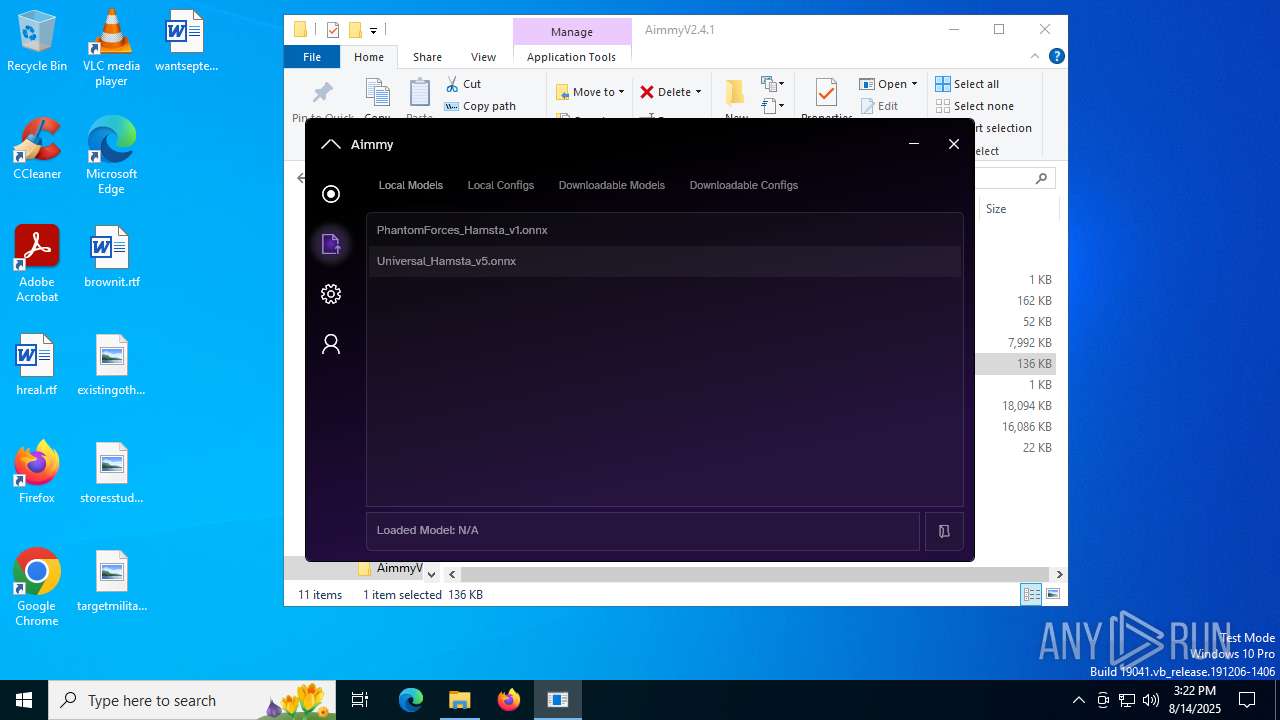
CouldBeAimmyV2.exe | You must install .NET to run this application.
App: C:\Users\admin\Downloads\AimmyV2.4.1\CouldBeAimmyV2.exe
Architecture: x64
App host version: 8.0.16
.NET location: Not found
Learn more:
https://aka.ms/dotnet/app-launch-failed
Download the .NET runtime:
https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x64&rid=win-x64&os=win10&apphost_version=8.0.16 |