| File name: | inetinfo.exe |
| Full analysis: | https://app.any.run/tasks/6c5f975d-186f-4a19-a87c-615b994a49f4 |
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2024, 01:21:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 692B741EDC1EA534702CBF6EA9103421 |
| SHA1: | 8406F17E33912132DDD98B7C420D1F2E0B63A390 |
| SHA256: | 344C8E2F72037C47B74AF28C546CB508067A39E590B147A491BD449D0604AF04 |
| SSDEEP: | 98304:h4U/N8hOSzRZLaMEDUGOooPliS7cFkdHLEe7TA3TT70lJJ1ECJVoqzWrHf354GJT:yELwM/syh4UqvR+Mm4coM9zD8 |
MALICIOUS
Drops the executable file immediately after the start
- inetinfo.exe (PID: 3980)
- inetinfo.exe (PID: 2092)
Changes the autorun value in the registry
- inetinfo.exe (PID: 3980)
Actions looks like stealing of personal data
- Rar.exe (PID: 560)
SUSPICIOUS
Reads the BIOS version
- inetinfo.exe (PID: 3980)
- inetinfo.exe (PID: 2092)
Executable content was dropped or overwritten
- inetinfo.exe (PID: 3980)
- inetinfo.exe (PID: 2092)
Starts itself from another location
- inetinfo.exe (PID: 3980)
INFO
Checks supported languages
- inetinfo.exe (PID: 3980)
- inetinfo.exe (PID: 2092)
- Rar.exe (PID: 560)
- kis.exe (PID: 2700)
Reads the computer name
- inetinfo.exe (PID: 3980)
- inetinfo.exe (PID: 2092)
- Rar.exe (PID: 560)
Create files in a temporary directory
- inetinfo.exe (PID: 3980)
- inetinfo.exe (PID: 2092)
Creates files in the program directory
- inetinfo.exe (PID: 3980)
Manual execution by a user
- WINWORD.EXE (PID: 588)
- WINWORD.EXE (PID: 1024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:07:07 07:39:59+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 36864 |
| InitializedDataSize: | 4911104 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xef8000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
47
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Program Files\winrar\rar.exe" a -apC -r -ed -tk -m5 -dh -tl -hpThis0nePiece -ta20240516 C:\PROGRA~2\DOCUME~1\Media\15F6949E.ldf C:\*.doc C:\*.DOCX | C:\Program Files\WinRAR\Rar.exe | inetinfo.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: Command line RAR Exit code: 6 Version: 5.91.0 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\overgarden.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\belowadded.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2092 | "C:\ProgramData\Application Data\inetinfo.exe" | C:\ProgramData\inetinfo.exe | inetinfo.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2700 | C:\Users\admin\AppData\Local\Temp\kis.exe | C:\Users\admin\AppData\Local\Temp\kis.exe | inetinfo.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 3980 | "C:\Users\admin\inetinfo.exe" | C:\Users\admin\inetinfo.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
21 462
Read events
18 366
Write events
1 137
Delete events
1 959
Modification events
| (PID) Process: | (1024) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 375 |
Value: 3337350000040000010000000000000000000000 | |||
| (PID) Process: | (1024) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1024) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1024) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1024) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1024) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1024) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1024) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1024) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1024) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
22
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1024 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8723.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3D54.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 588 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\overgarden.rtf.LNK | — | |
MD5:— | SHA256:— | |||
| 588 | WINWORD.EXE | C:\Users\admin\Documents\~WRL0001.tmp | — | |
MD5:— | SHA256:— | |||
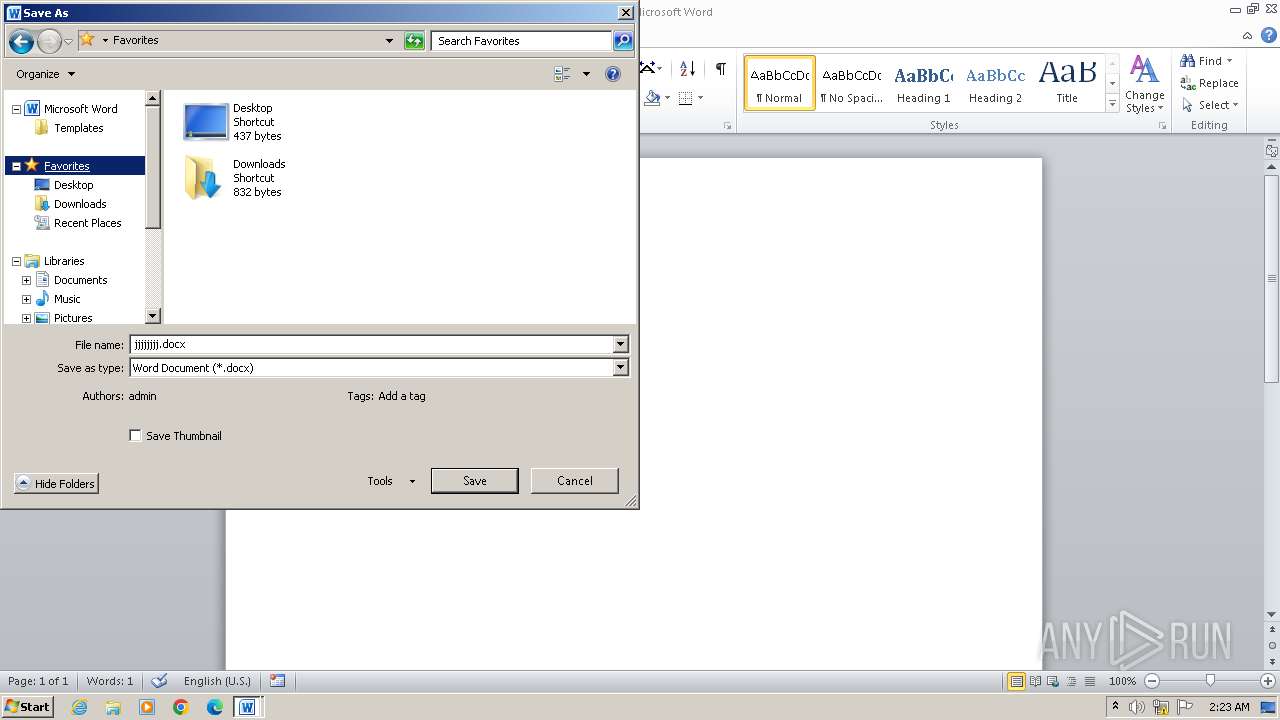
| 588 | WINWORD.EXE | C:\Users\admin\Documents\jjjjjjjj.docx | — | |
MD5:— | SHA256:— | |||
| 1024 | WINWORD.EXE | C:\Users\admin\Desktop\~$lowadded.rtf | binary | |
MD5:2FFC47ABEF532B939ED7B3897CB40142 | SHA256:A833496D93EF0DE87B10592C29970FAE9C69254AC51DA78A5D0C500C9033FD5C | |||
| 1024 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\belowadded.rtf.LNK | lnk | |
MD5:0601C3057BBFF3F94628010BE9F82839 | SHA256:00D552B0B0813E1300C7E49237D355F701B047A9BCD42AEC5130741BB173009A | |||
| 1024 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0409.lex | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 588 | WINWORD.EXE | C:\Users\admin\Desktop\~WRD0002.tmp | — | |
MD5:— | SHA256:— | |||
| 588 | WINWORD.EXE | C:\Users\admin\Desktop\~WRL0003.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Threats
Process | Message |
|---|---|
inetinfo.exe |
%s------------------------------------------------
--- WinLicense Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
inetinfo.exe |
%s------------------------------------------------
--- WinLicense Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|