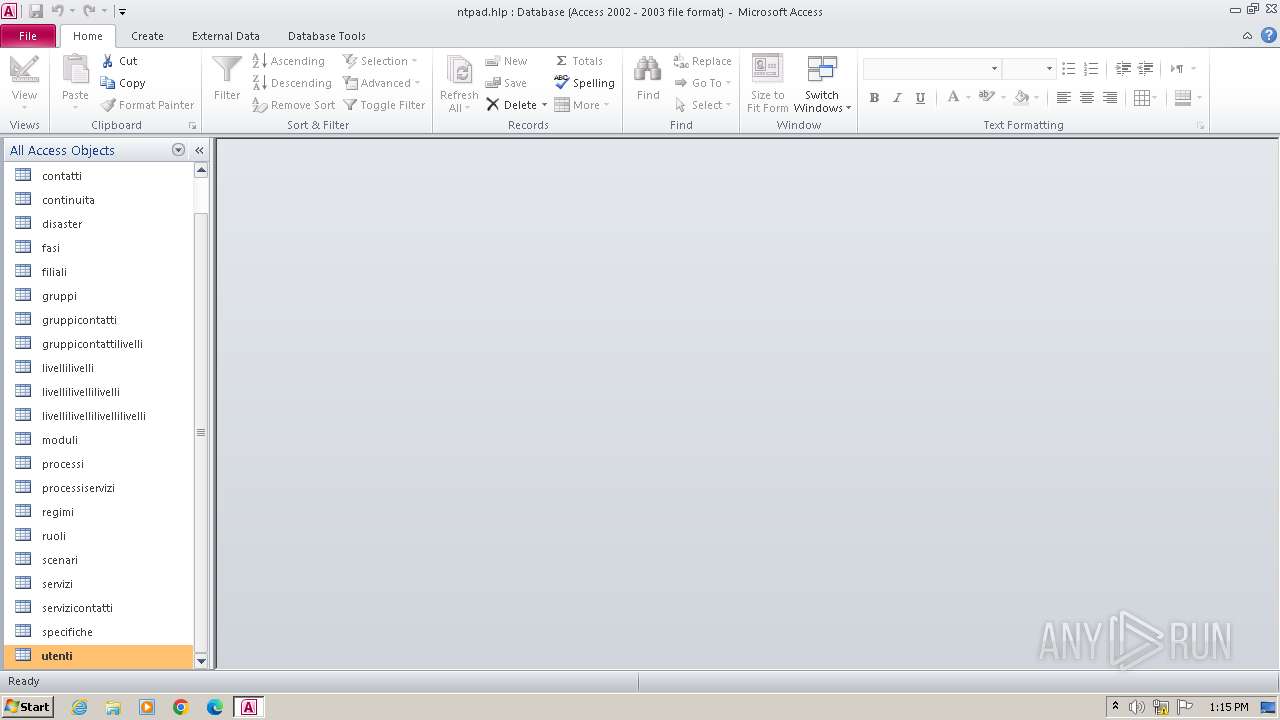
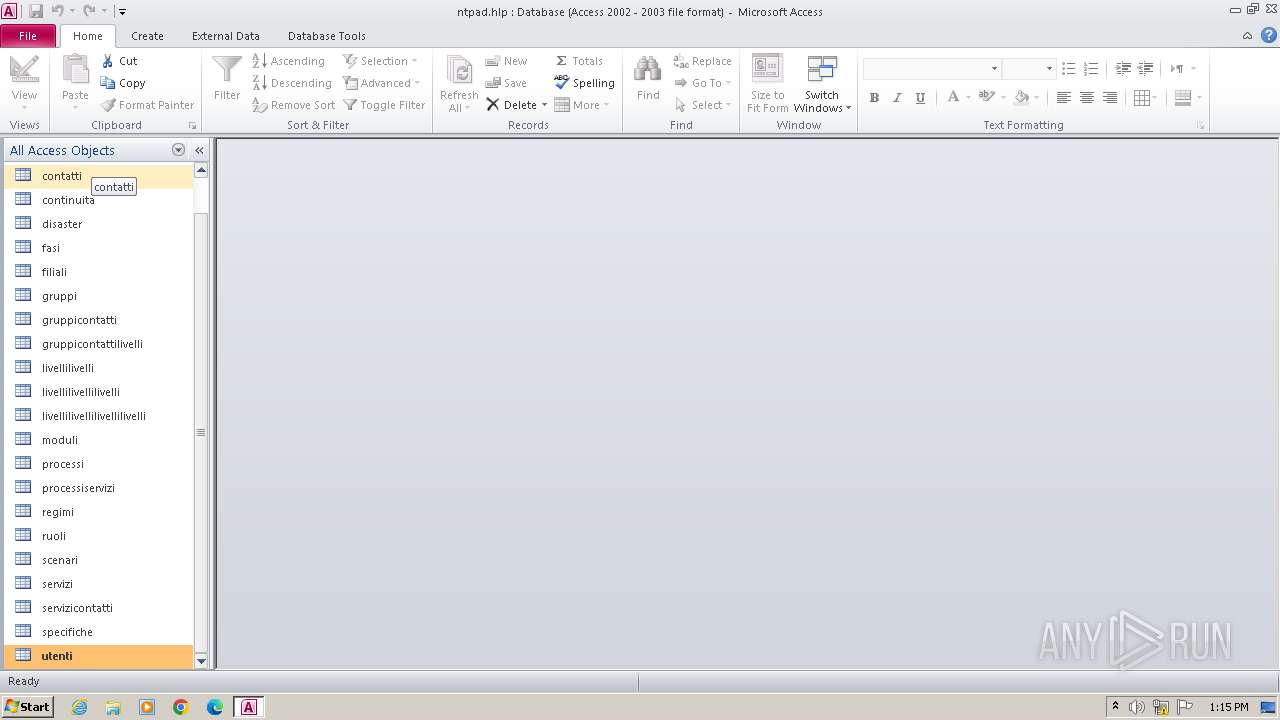
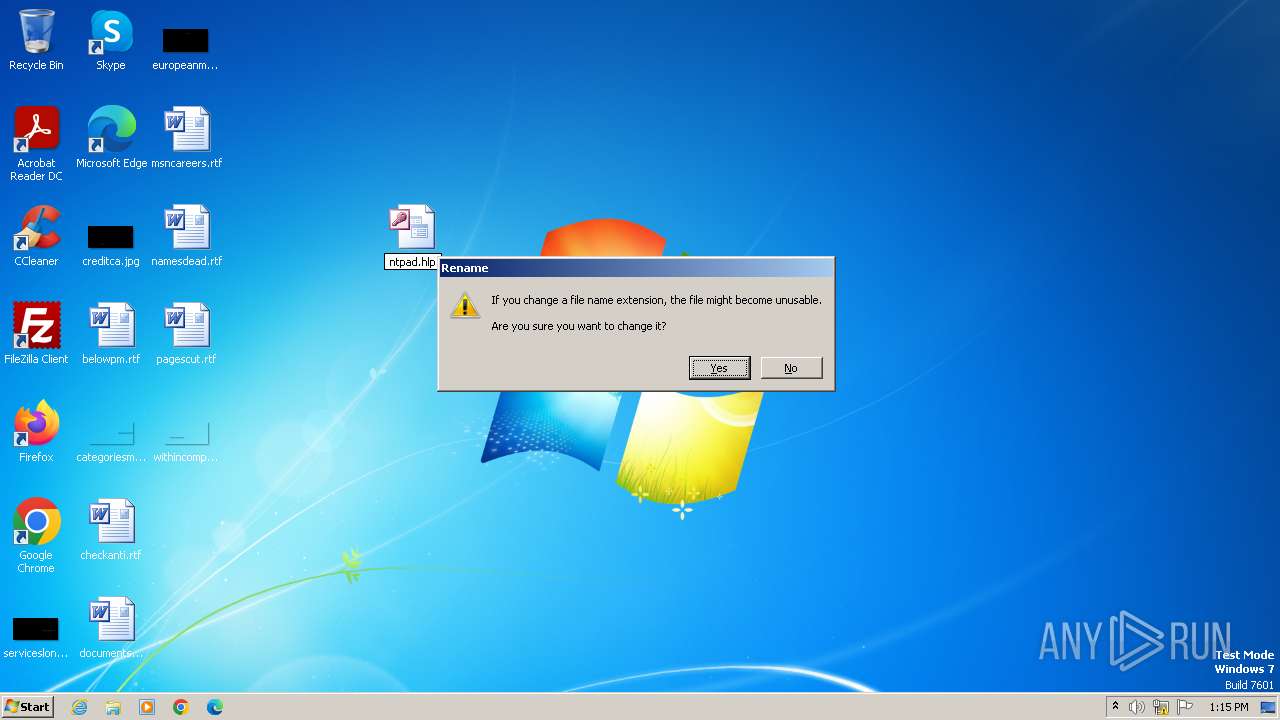
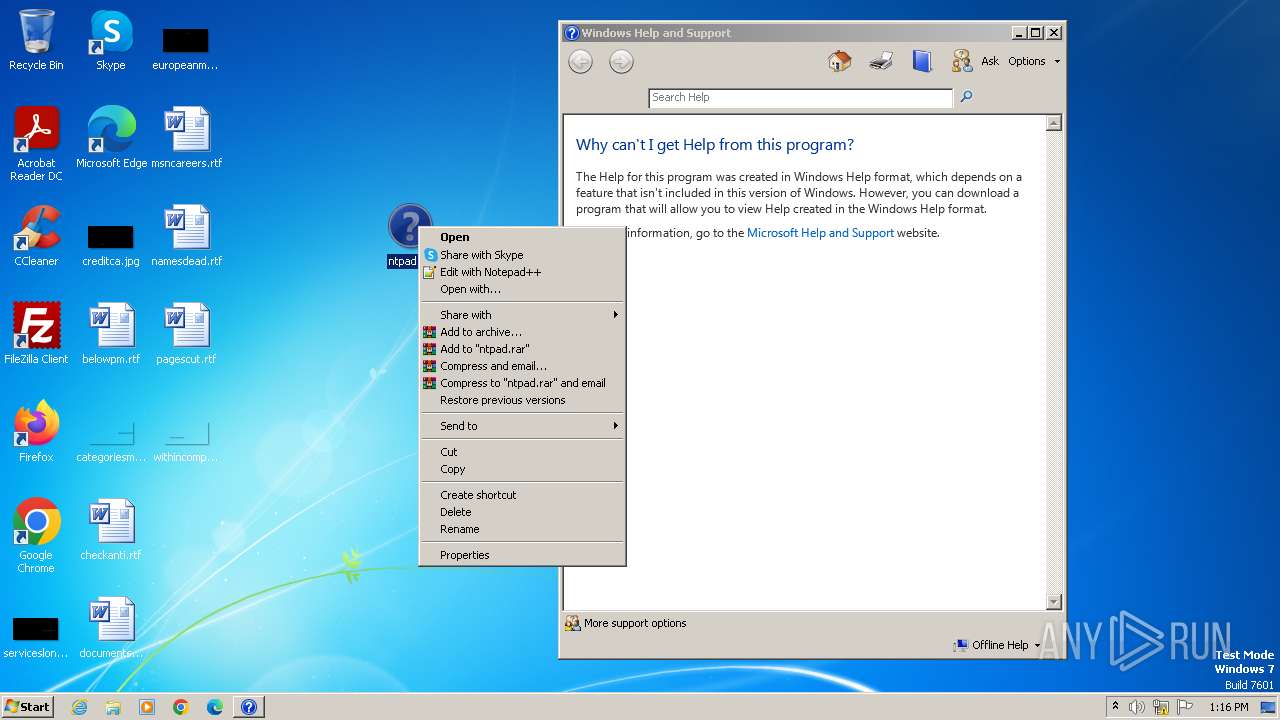
| File name: | ntpad.hlp |
| Full analysis: | https://app.any.run/tasks/c3e1a381-a29b-447a-8fcd-5bd616b93097 |
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2024, 12:15:05 |
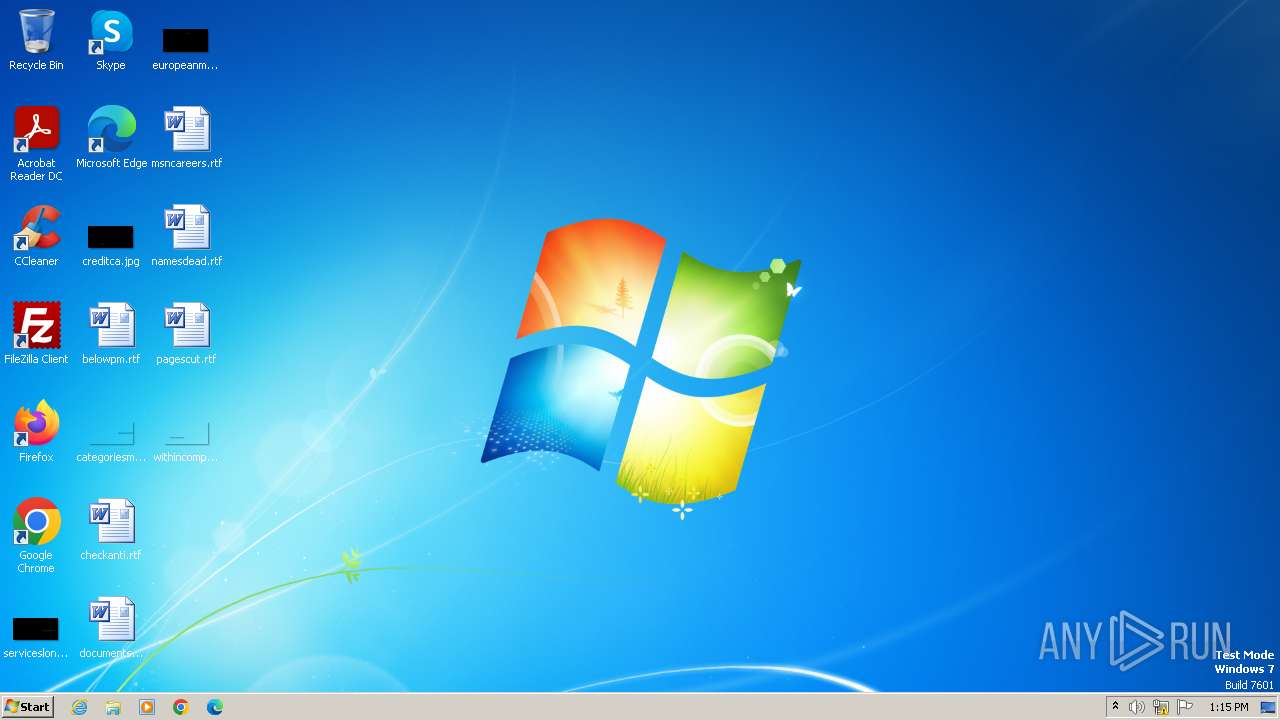
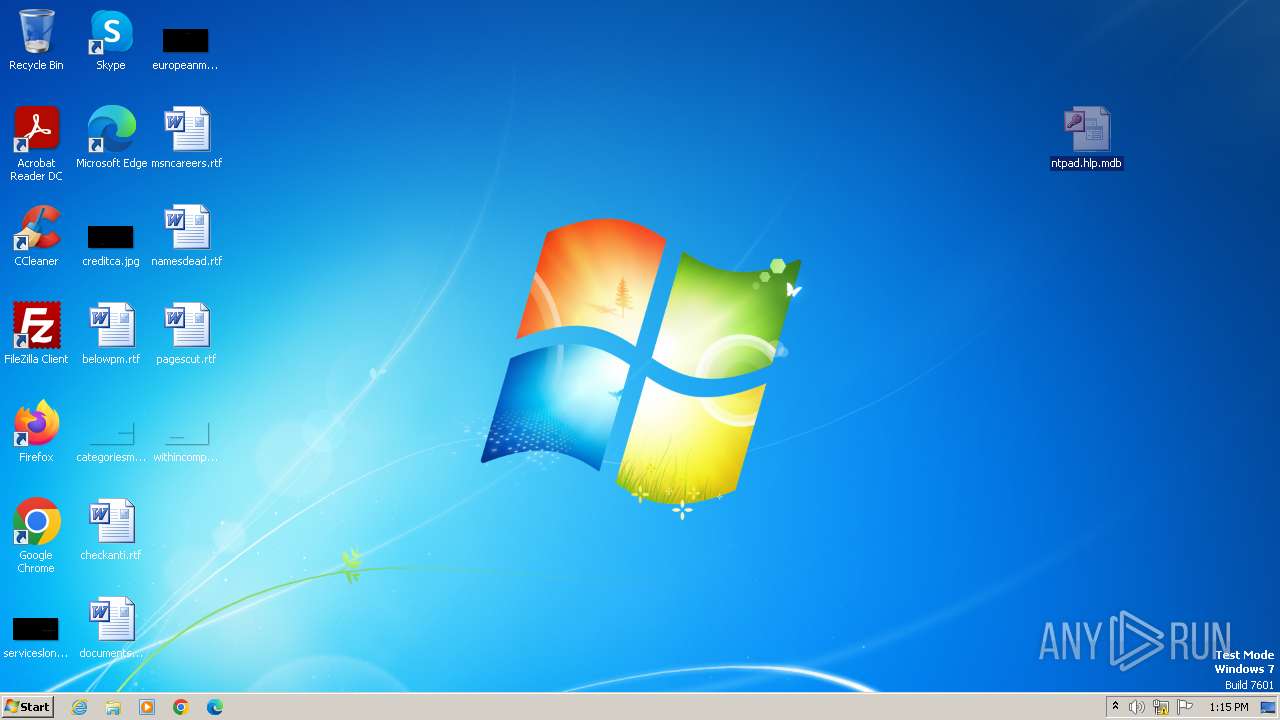
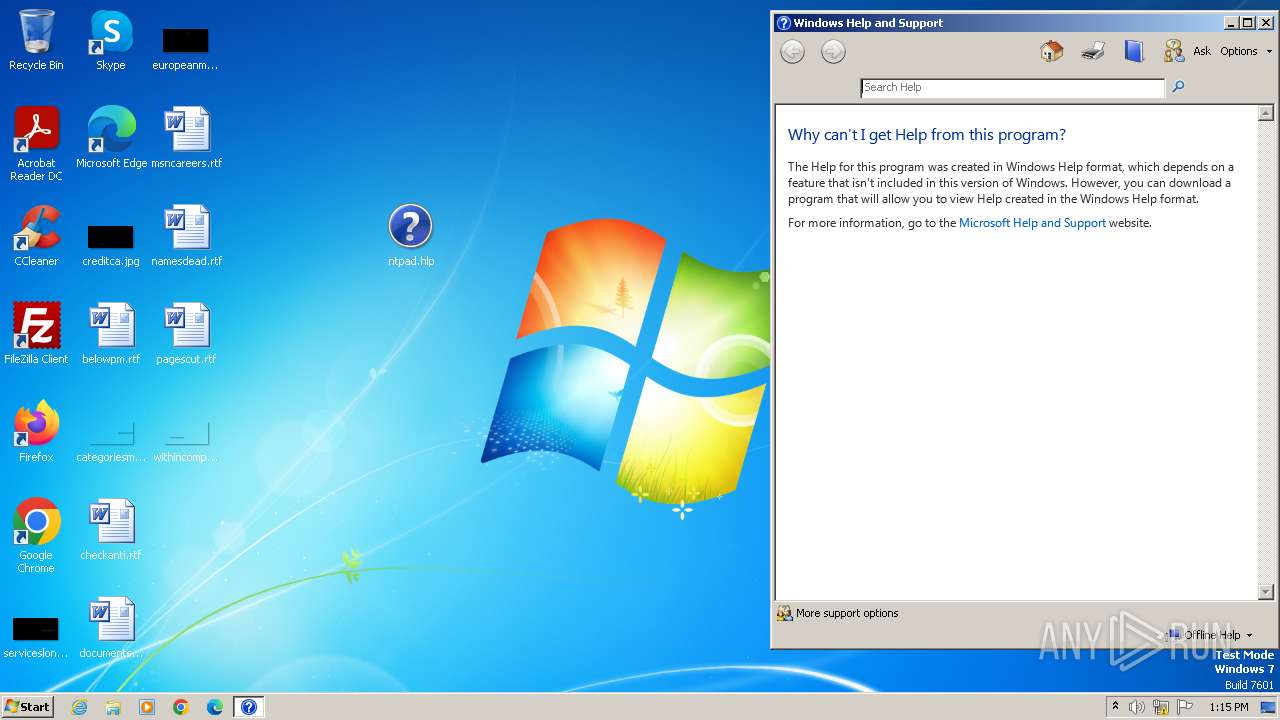
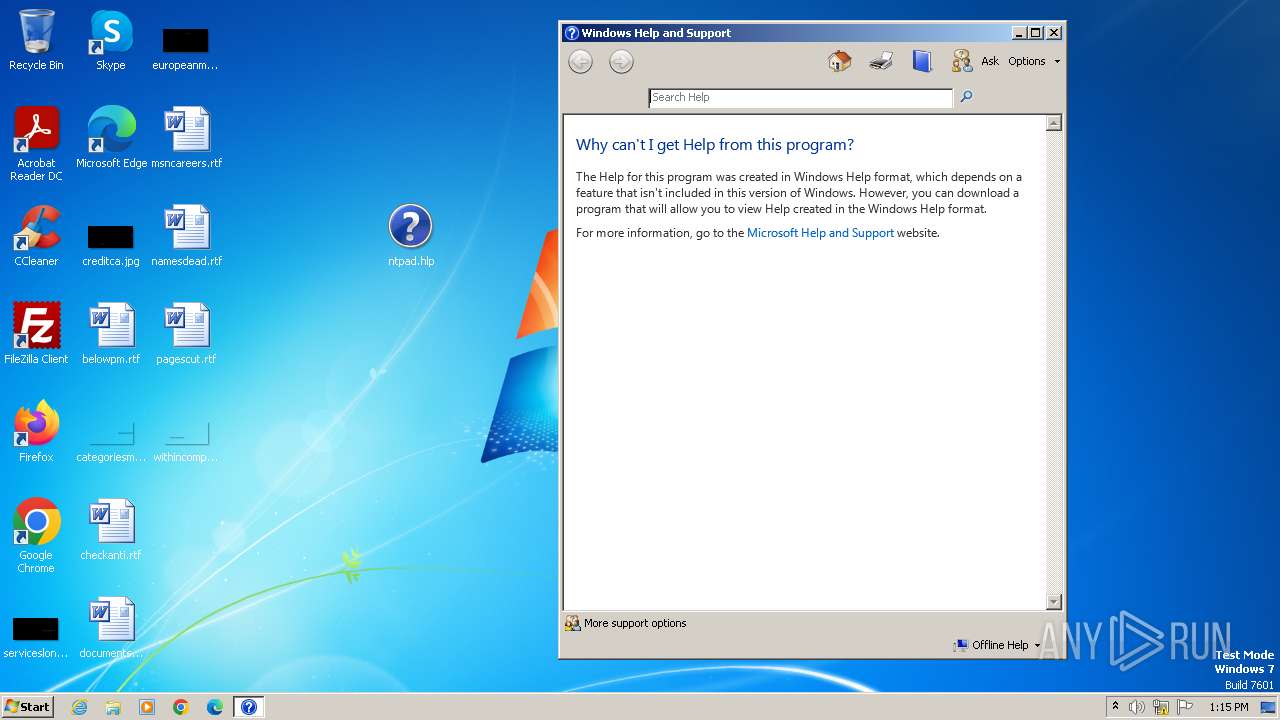
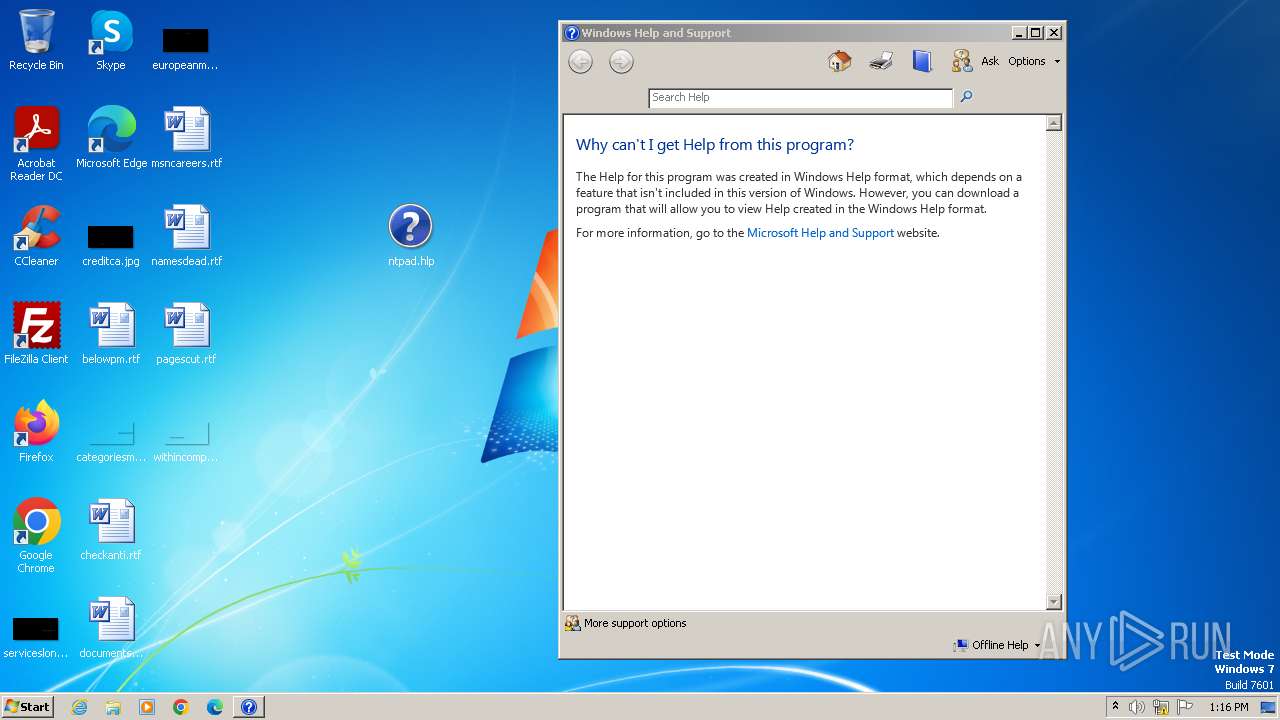
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msaccess |
| File info: | Microsoft Access Database |
| MD5: | F73BAE1B76573AEDF74BE961F6FED404 |
| SHA1: | AB1459C6D4BB3E85234868A5ABAD14F245BB58FB |
| SHA256: | 344356966D3A077B2C3916B8057B3DABD1FDC73471FCA158720F3B9A7E96BF15 |
| SSDEEP: | 3072:T63lNhmM3SQME8Che7R8Wf+0elBMLA6eE:cNhv3jMEZhH0elBML5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- HelpPane.exe (PID: 1664)
Reads Internet Explorer settings
- HelpPane.exe (PID: 1664)
Searches for installed software
- MSACCESS.EXE (PID: 3980)
Reads the Internet Settings
- HelpPane.exe (PID: 1664)
INFO
Checks supported languages
- MSACCESS.EXE (PID: 3980)
Reads Environment values
- MSACCESS.EXE (PID: 3980)
Reads Microsoft Office registry keys
- MSACCESS.EXE (PID: 3980)
Reads the computer name
- MSACCESS.EXE (PID: 3980)
Process checks computer location settings
- MSACCESS.EXE (PID: 3980)
Reads the machine GUID from the registry
- MSACCESS.EXE (PID: 3980)
- HelpPane.exe (PID: 1664)
- winhlp32.exe (PID: 1856)
Creates files or folders in the user directory
- MSACCESS.EXE (PID: 3980)
Reads security settings of Internet Explorer
- HelpPane.exe (PID: 1664)
Manual execution by a user
- winhlp32.exe (PID: 1856)
- verclsid.exe (PID: 116)
Checks proxy server information
- HelpPane.exe (PID: 1664)
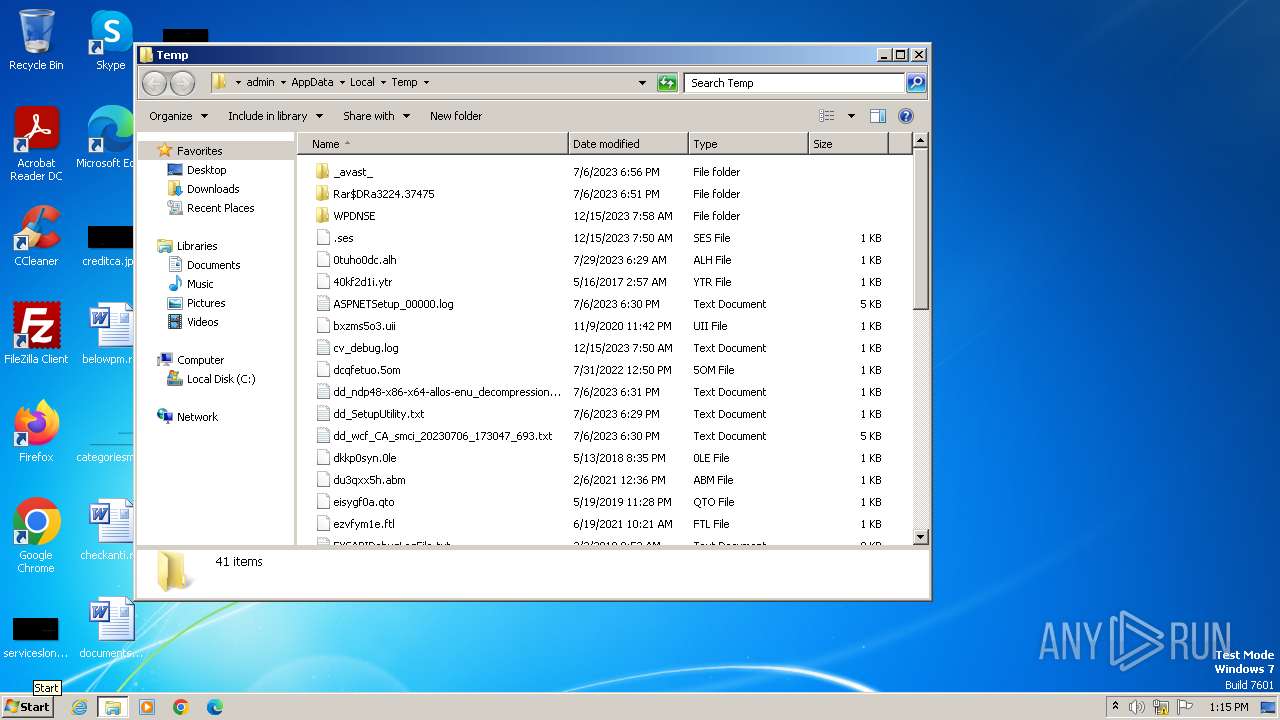
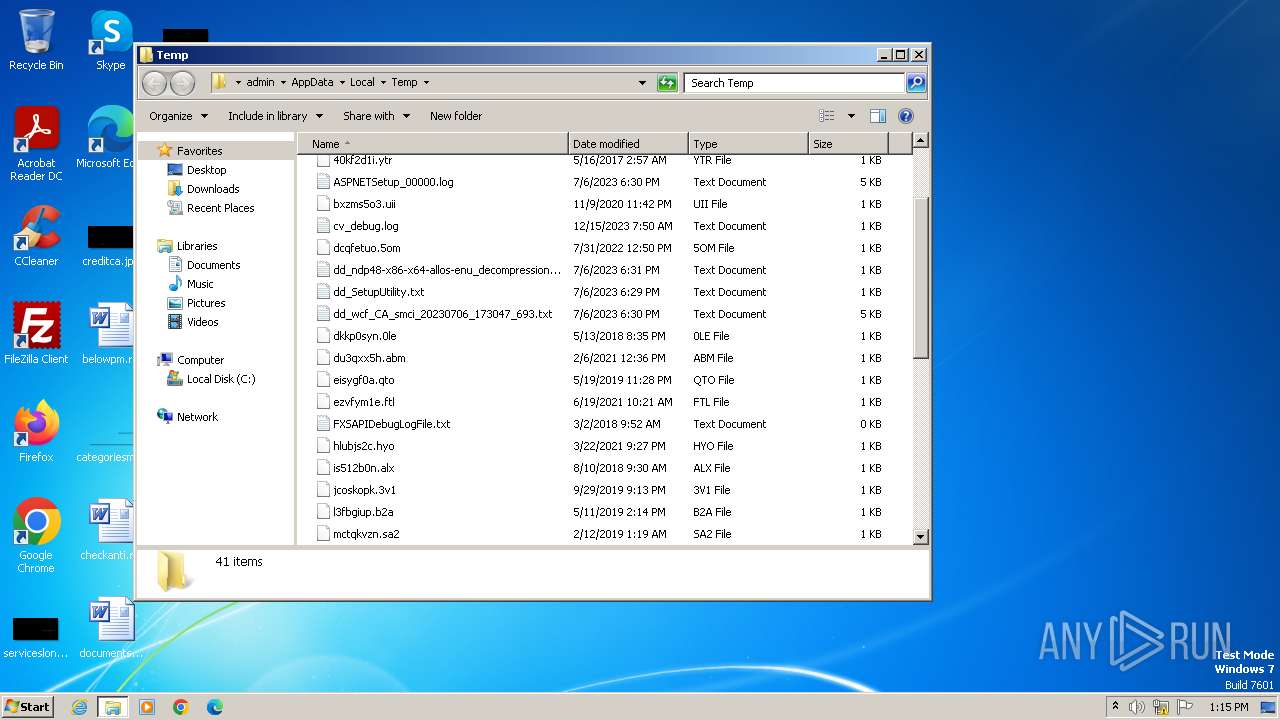
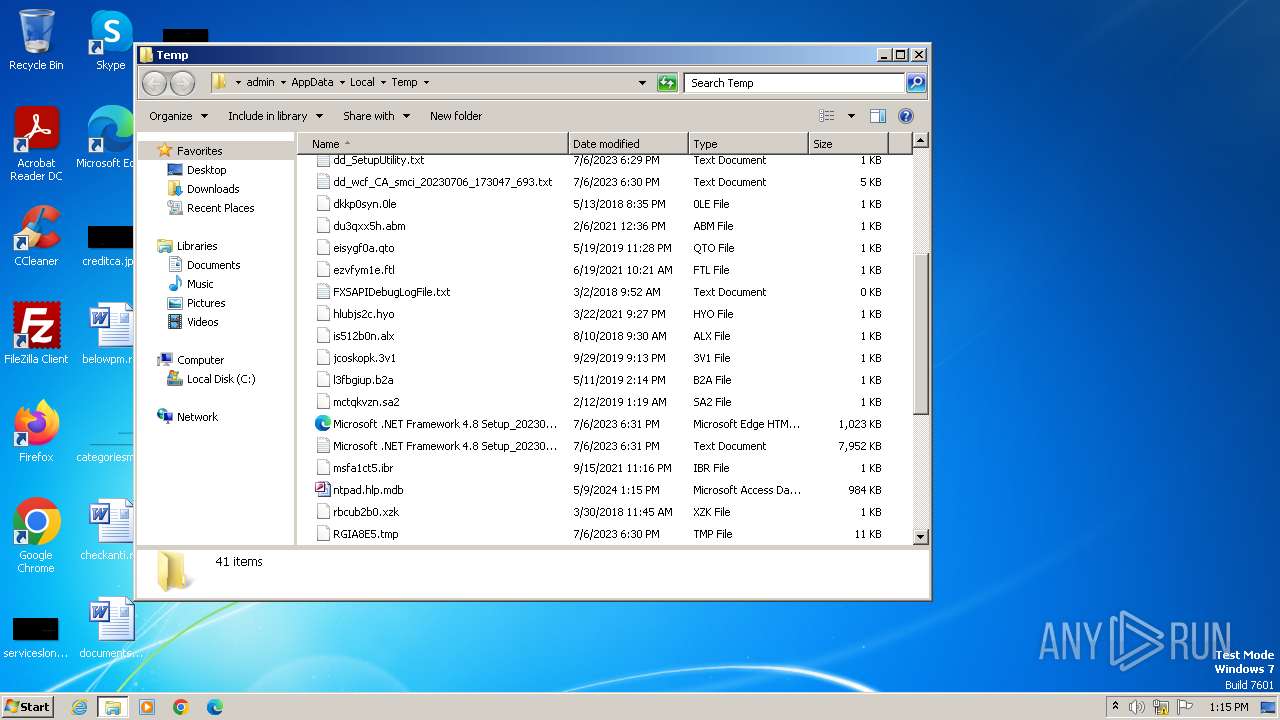
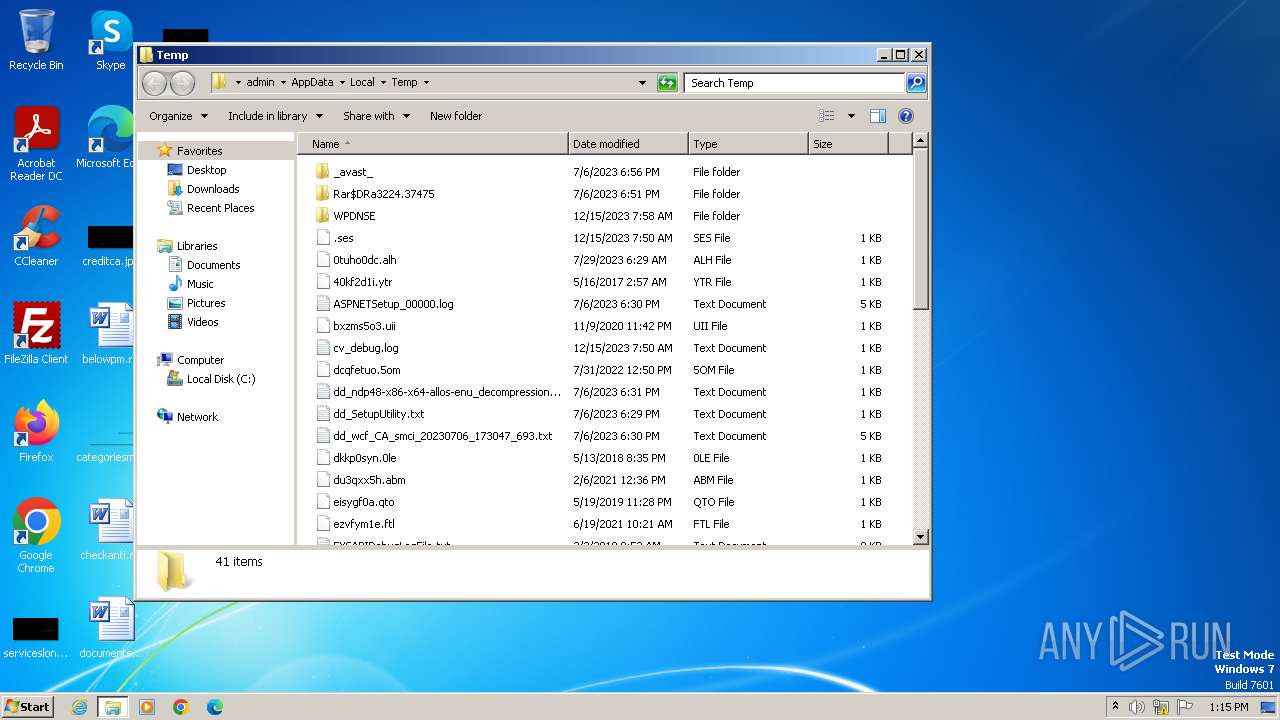
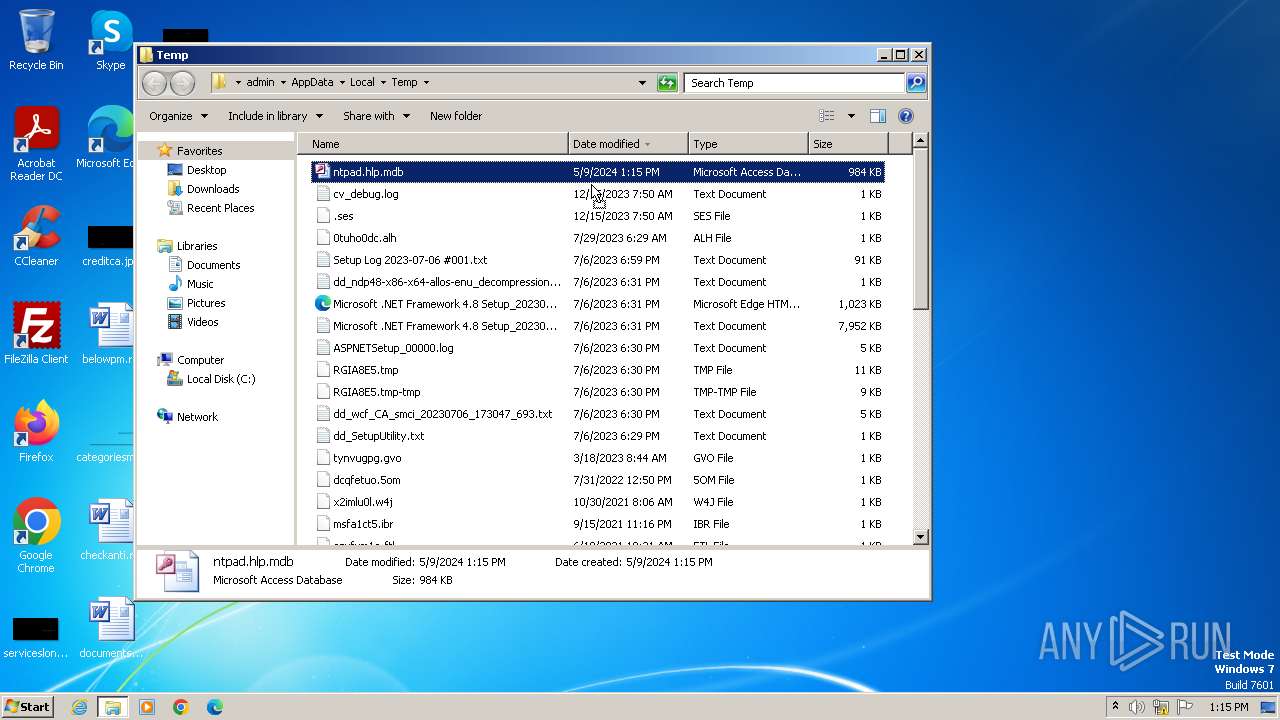
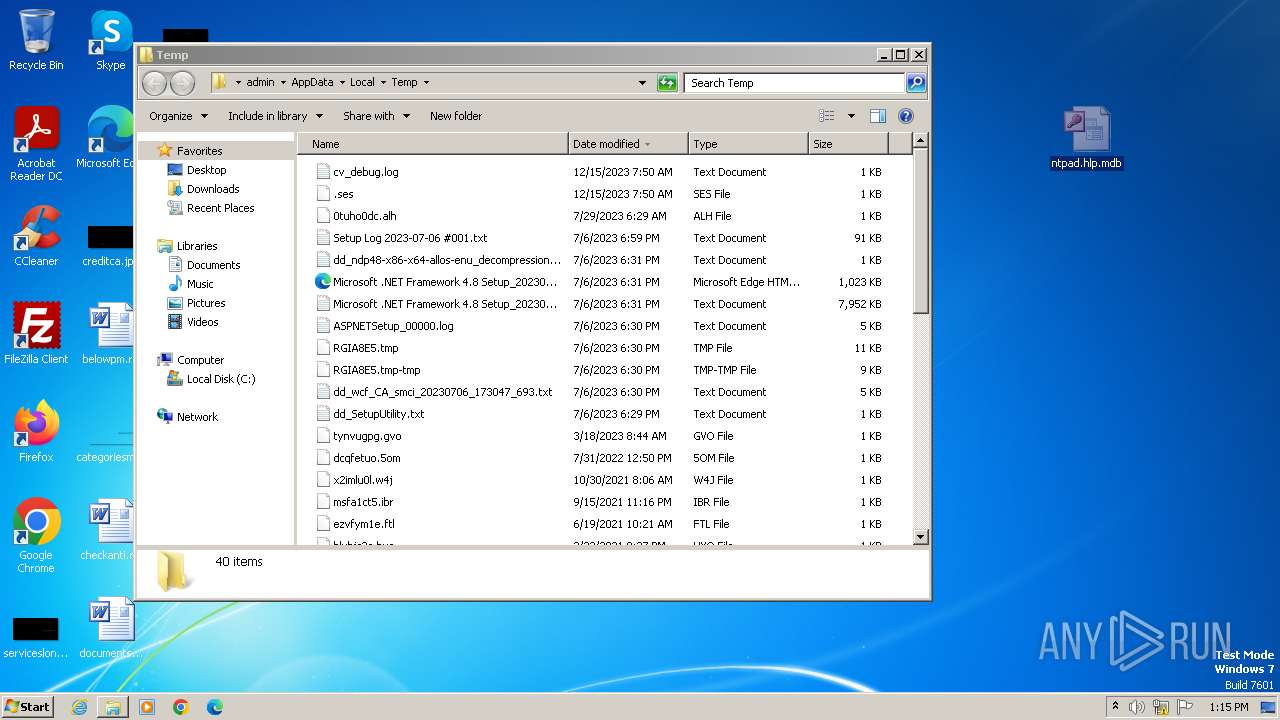
Create files in a temporary directory
- MSACCESS.EXE (PID: 3980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .mdb | | | Microsoft Jet DB (90.9) |
|---|---|---|
| .pi2 | | | DEGAS med-res bitmap (9) |
Total processes
38
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\System32\verclsid.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1664 | C:\Windows\helppane.exe -Embedding | C:\Windows\HelpPane.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Help and Support Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
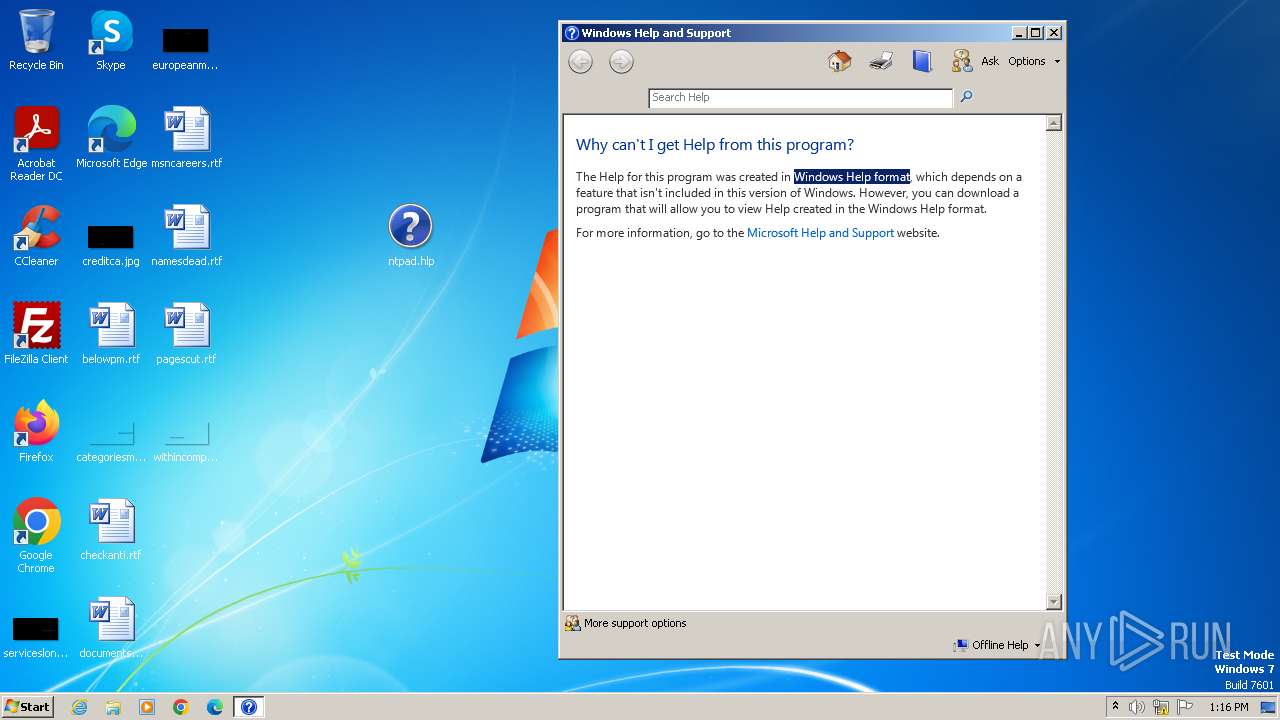
| 1856 | "C:\Windows\winhlp32.exe" C:\Users\admin\Desktop\ntpad.hlp | C:\Windows\winhlp32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Winhlp32 Stub Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3980 | "C:\Program Files\Microsoft Office\Office14\MSACCESS.EXE" /NOSTARTUP C:\Users\admin\AppData\Local\Temp\ntpad.hlp.mdb %2 %3 %4 %5 %6 %7 %8 %9 | C:\Program Files\Microsoft Office\Office14\MSACCESS.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Access Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
5 736
Read events
5 647
Write events
54
Delete events
35
Modification events
| (PID) Process: | (3980) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Access\Resiliency\StartupItems |
| Operation: | write | Name: | 'm? |
Value: 276D3F008C0F0000010000000000000000000000 | |||
| (PID) Process: | (3980) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3980) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3980) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3980) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3980) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3980) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3980) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3980) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3980) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3980 | MSACCESS.EXE | C:\Users\admin\AppData\Local\Temp\CVR3D97.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3980 | MSACCESS.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Access\System.mdw | binary | |
MD5:E7C71E1B54F6D38F3C49EA4A48316A9B | SHA256:9294401E28C3B3793E3DD7CE628B2C6633F273900A5DAFEB78F42293AF3E46BE | |||
| 3980 | MSACCESS.EXE | C:\Users\admin\AppData\Local\Temp\ntpad.hlp.mdb | mdb | |
MD5:006D9B1FAF60592276393AABC2D61CF6 | SHA256:CFFA6D8B2ED08F4BA296647E0874B6BAD6C76C65E1295E79CCA888165F17A594 | |||
| 3980 | MSACCESS.EXE | C:\Users\admin\AppData\Local\Temp\ntpad.hlp.ldb | binary | |
MD5:60440F32EA16D34DE13F285E51EBE6CD | SHA256:C431A46E8660FA7BF21517D0656A2DD0F20AAF272A1734267AC393D97FB3E9F0 | |||
| 3980 | MSACCESS.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Access\System.ldb | binary | |
MD5:60440F32EA16D34DE13F285E51EBE6CD | SHA256:C431A46E8660FA7BF21517D0656A2DD0F20AAF272A1734267AC393D97FB3E9F0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Threats
Process | Message |
|---|---|
MSACCESS.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Access\System.mdw |