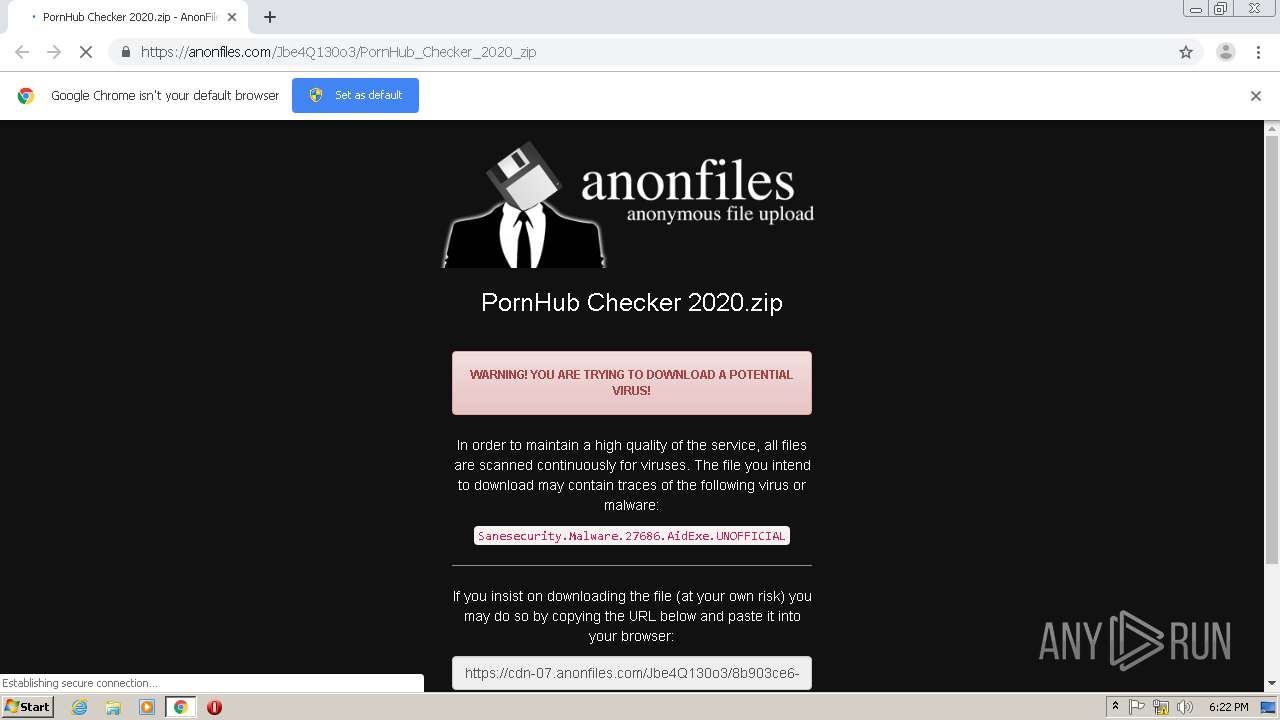
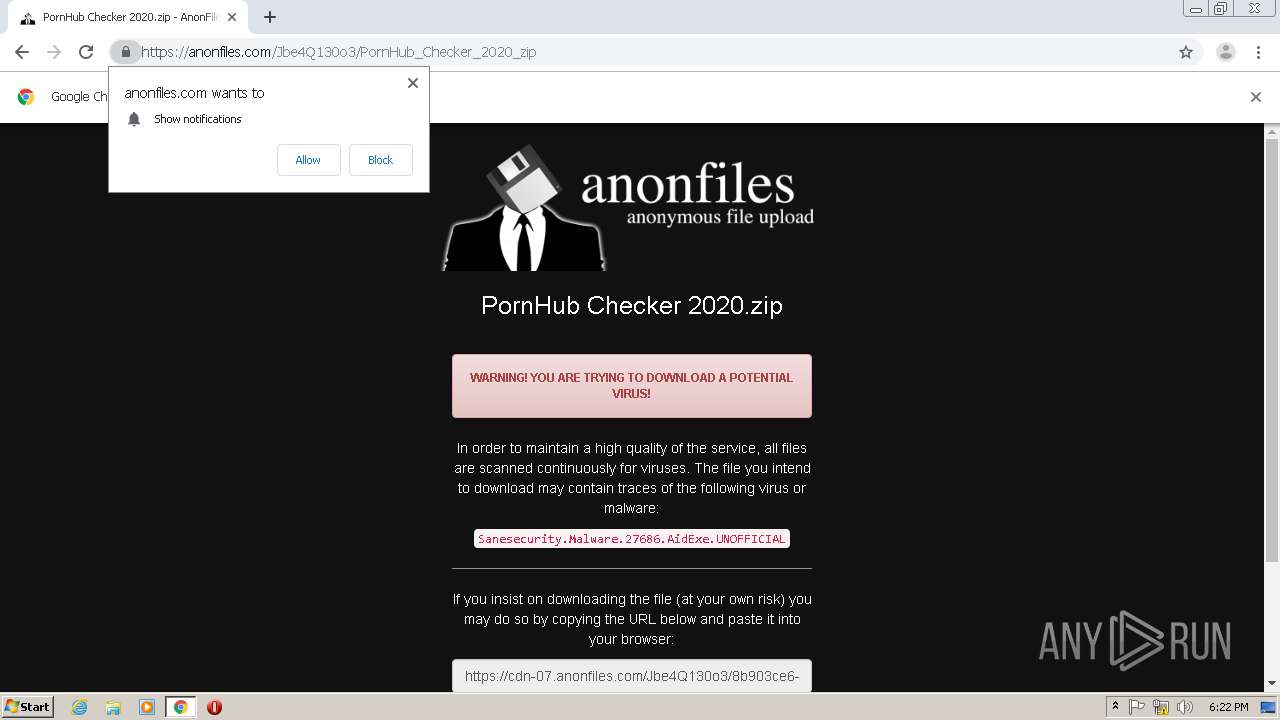
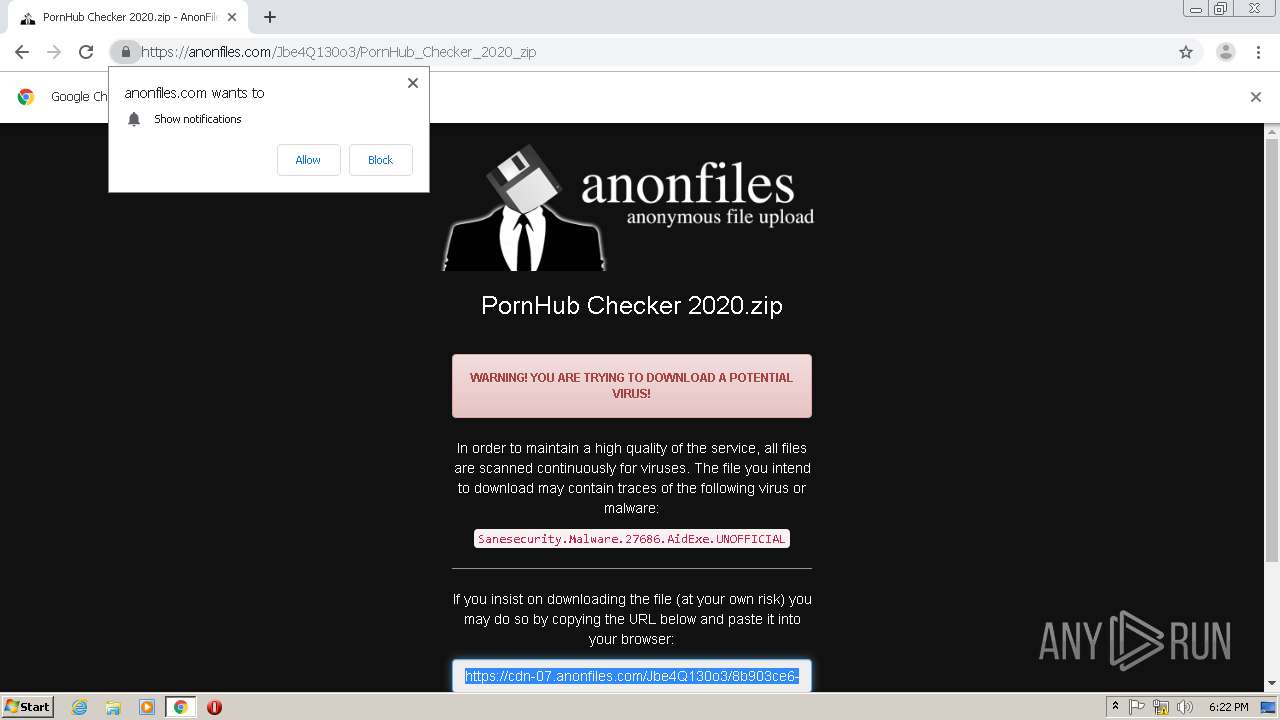
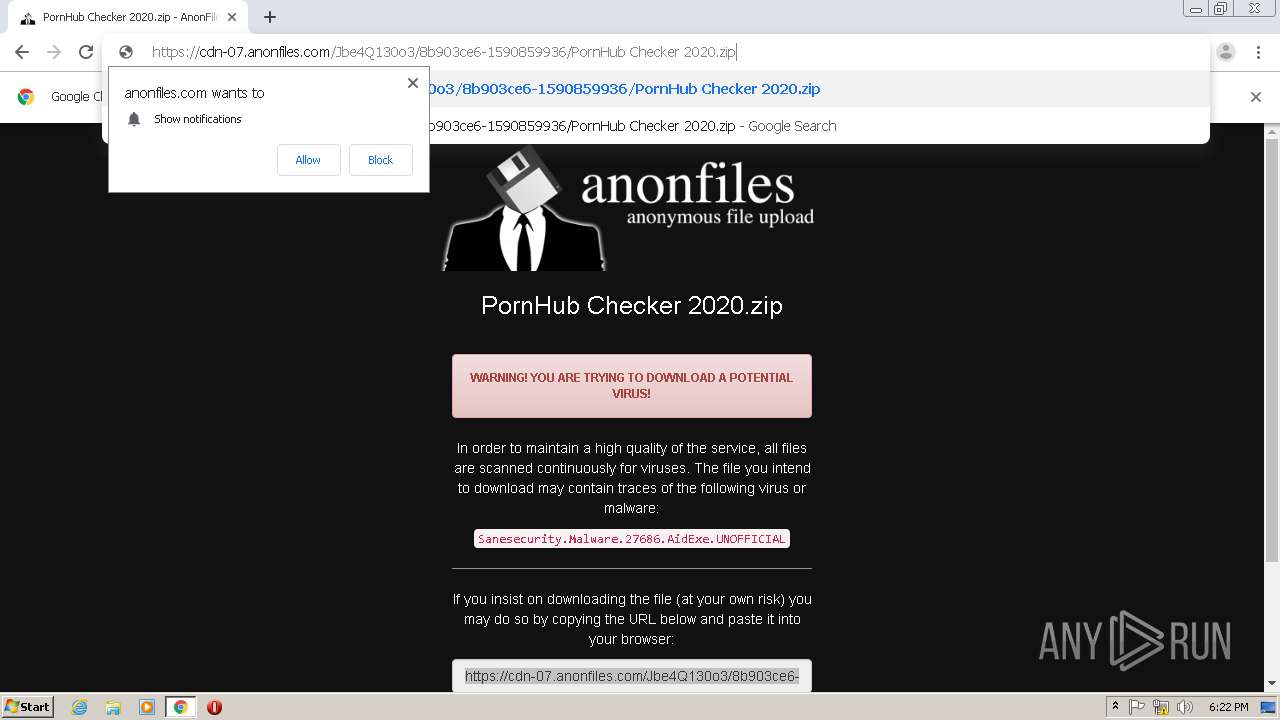
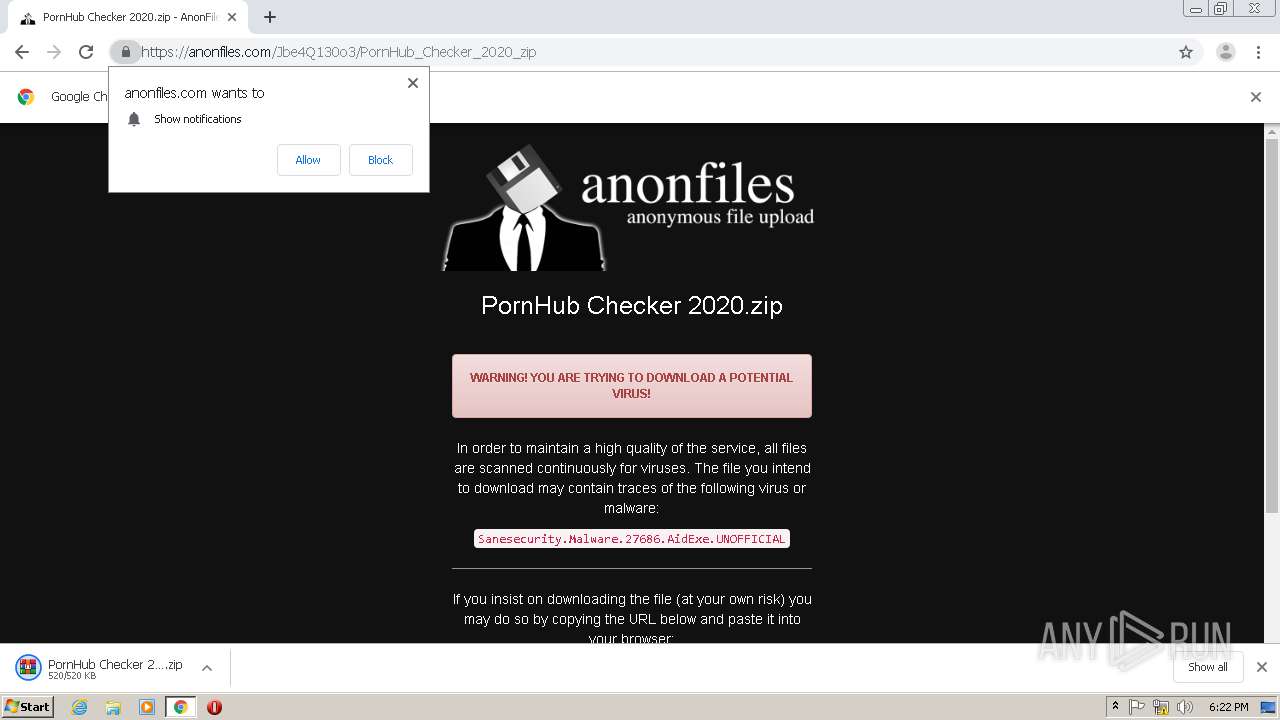
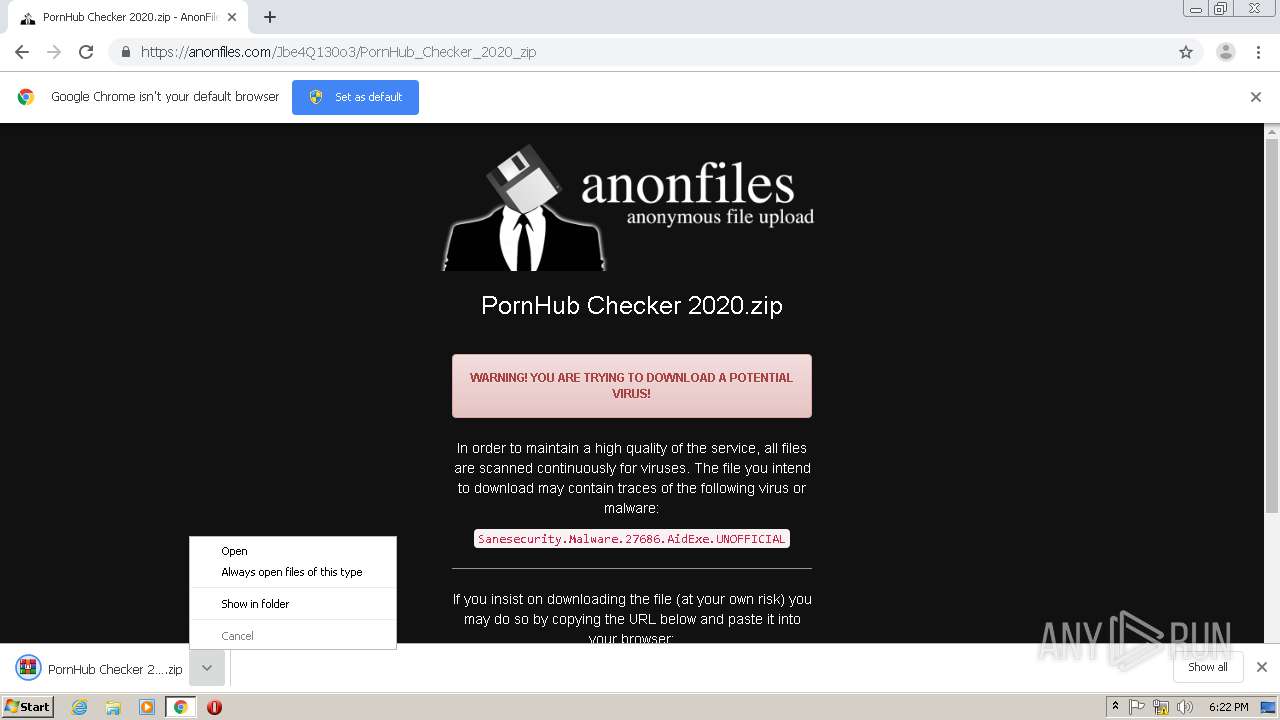
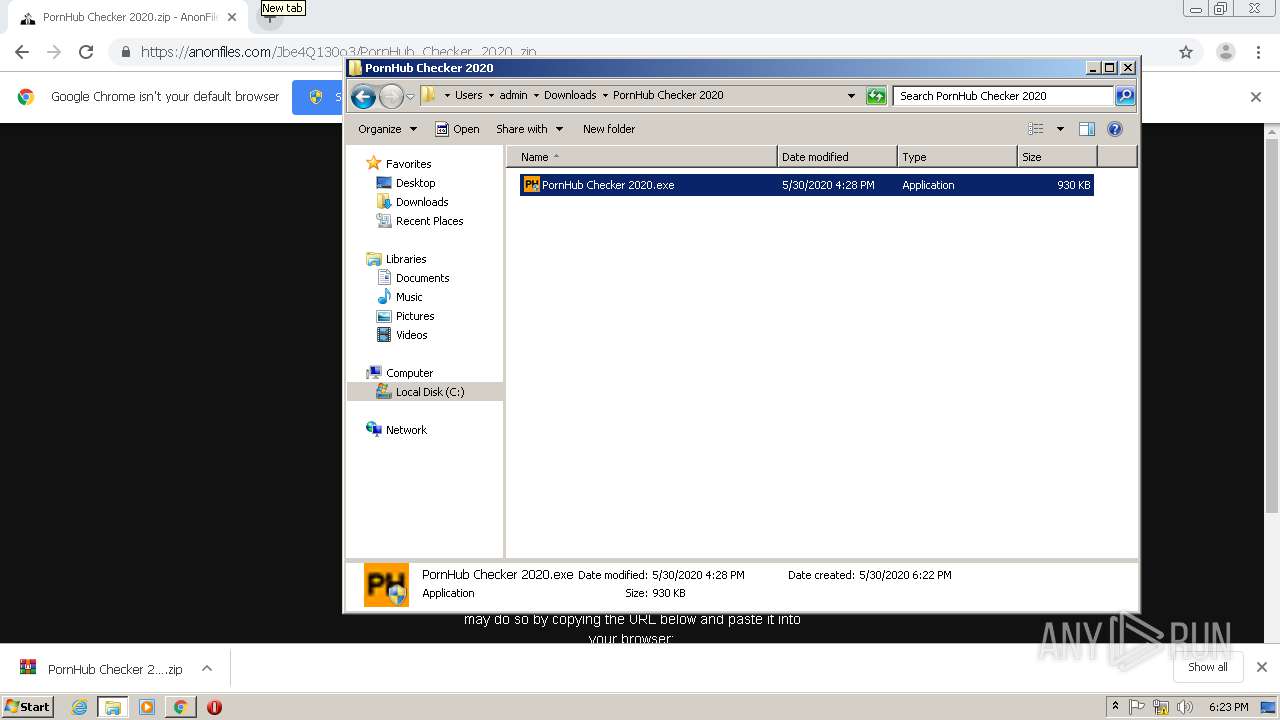
| URL: | https://anonfiles.com/Jbe4Q130o3/PornHub_Checker_2020_zip |
| Full analysis: | https://app.any.run/tasks/9b5ddcdb-1cc9-4fcc-b528-7101c3bc626c |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 17:21:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 24A1752CE47EF3555CB7C3319BBB7A03 |
| SHA1: | 0CC08D29BB4D587BE1463A1540B09EFD9A8CC9B3 |
| SHA256: | 343DF6F23DDF606D2DC593FC8FB4F4D000489994952FF2FA6513F15E0D6E577C |
| SSDEEP: | 3:N8M2+AIFXIqp0U:2M2/idGU |
MALICIOUS
Application was dropped or rewritten from another process
- PornHub Checker 2020.exe (PID: 3268)
- PornHub Checker 2020.exe (PID: 2988)
- MSBuild.exe (PID: 1912)
- MSBuild.exe (PID: 1992)
- server.exe (PID: 3572)
- MSBuild.exe (PID: 1504)
- server.exe (PID: 480)
- MSBuild.exe (PID: 3848)
- MSBuild.exe (PID: 1196)
- MSBuild.exe (PID: 3408)
- server.exe (PID: 1744)
- server.exe (PID: 2180)
- server.exe (PID: 1864)
- server.exe (PID: 1116)
- MSBuild.exe (PID: 2804)
Writes to a start menu file
- PornHub Checker 2020.exe (PID: 2988)
SUSPICIOUS
Executable content was dropped or overwritten
- PornHub Checker 2020.exe (PID: 2988)
- WinRAR.exe (PID: 696)
- MSBuild.exe (PID: 1992)
- MSBuild.exe (PID: 1912)
- MSBuild.exe (PID: 3848)
- MSBuild.exe (PID: 1504)
- MSBuild.exe (PID: 1196)
- MSBuild.exe (PID: 3408)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2388)
Creates files in the user directory
- PornHub Checker 2020.exe (PID: 2988)
Starts itself from another location
- MSBuild.exe (PID: 1992)
- MSBuild.exe (PID: 3848)
- MSBuild.exe (PID: 1504)
- MSBuild.exe (PID: 1912)
- MSBuild.exe (PID: 3408)
- MSBuild.exe (PID: 1196)
INFO
Reads the hosts file
- chrome.exe (PID: 1820)
- chrome.exe (PID: 2388)
Application launched itself
- chrome.exe (PID: 2388)
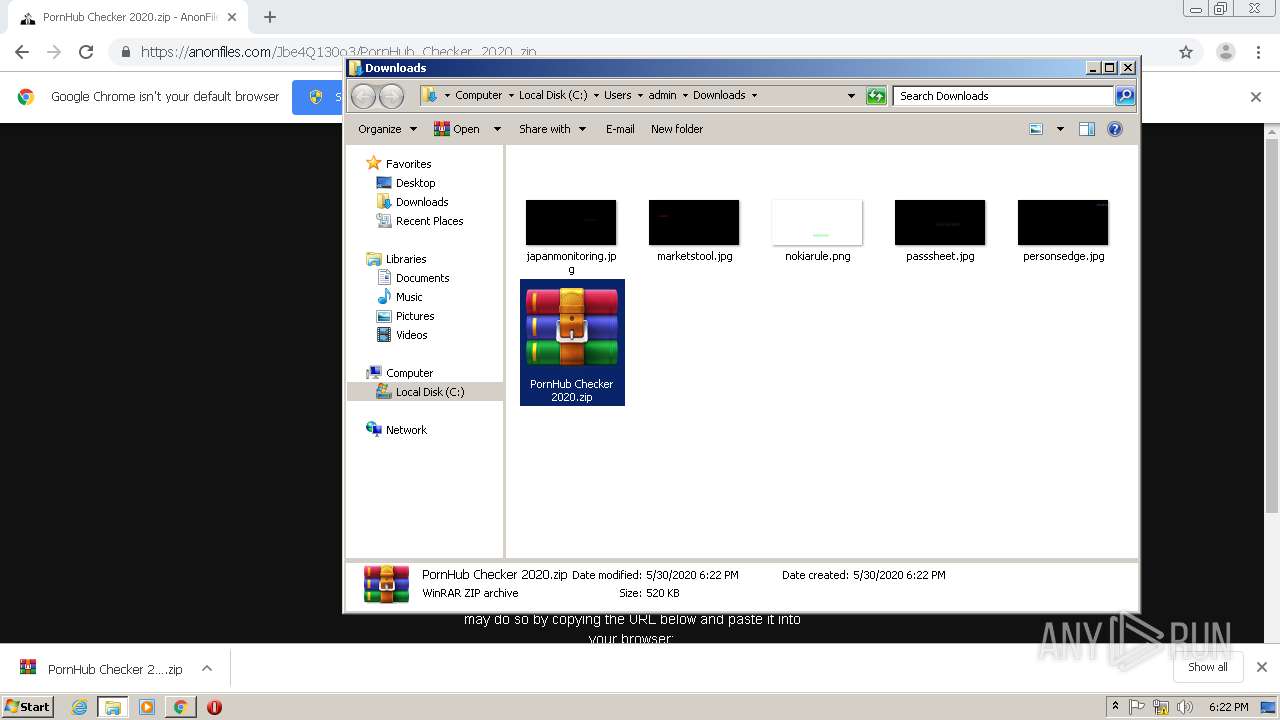
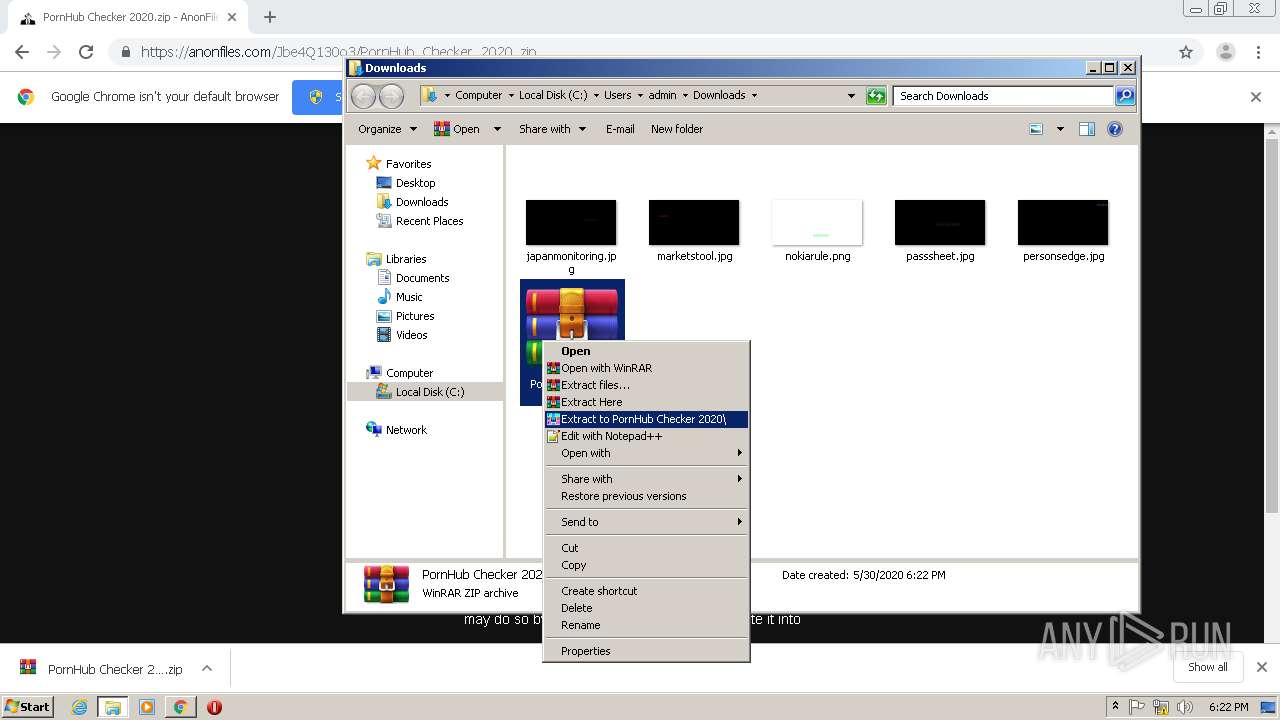
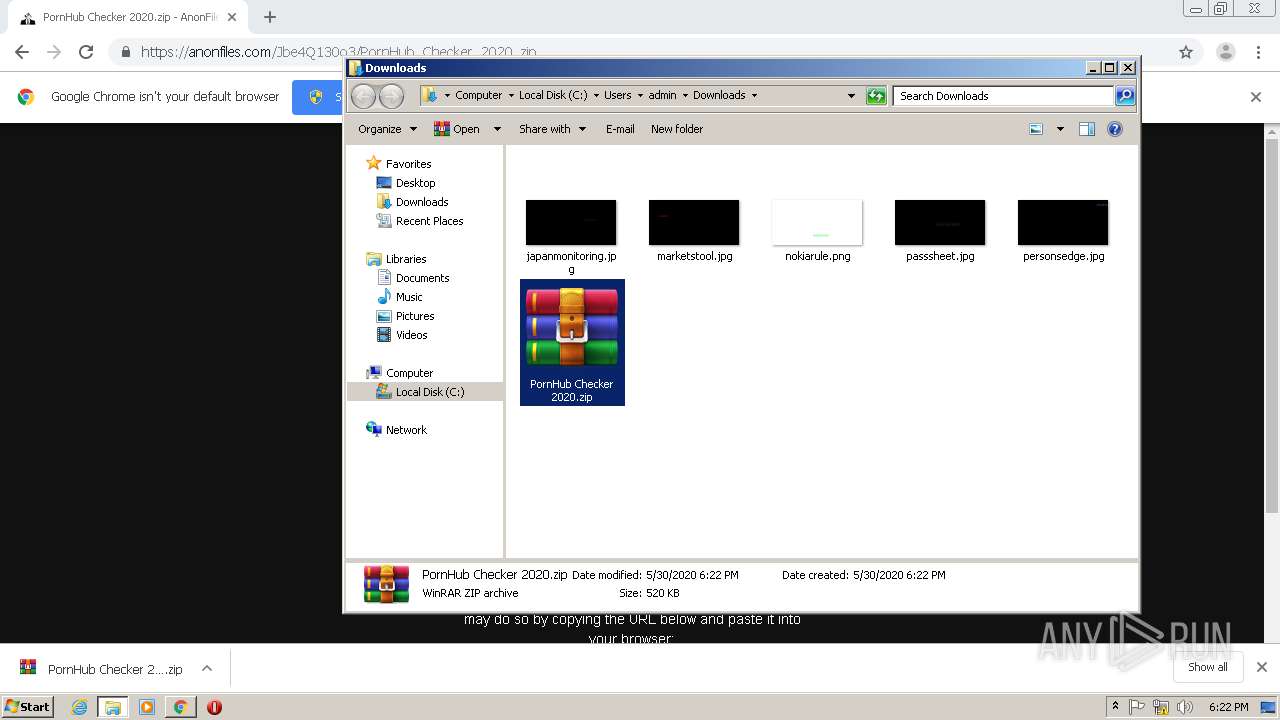
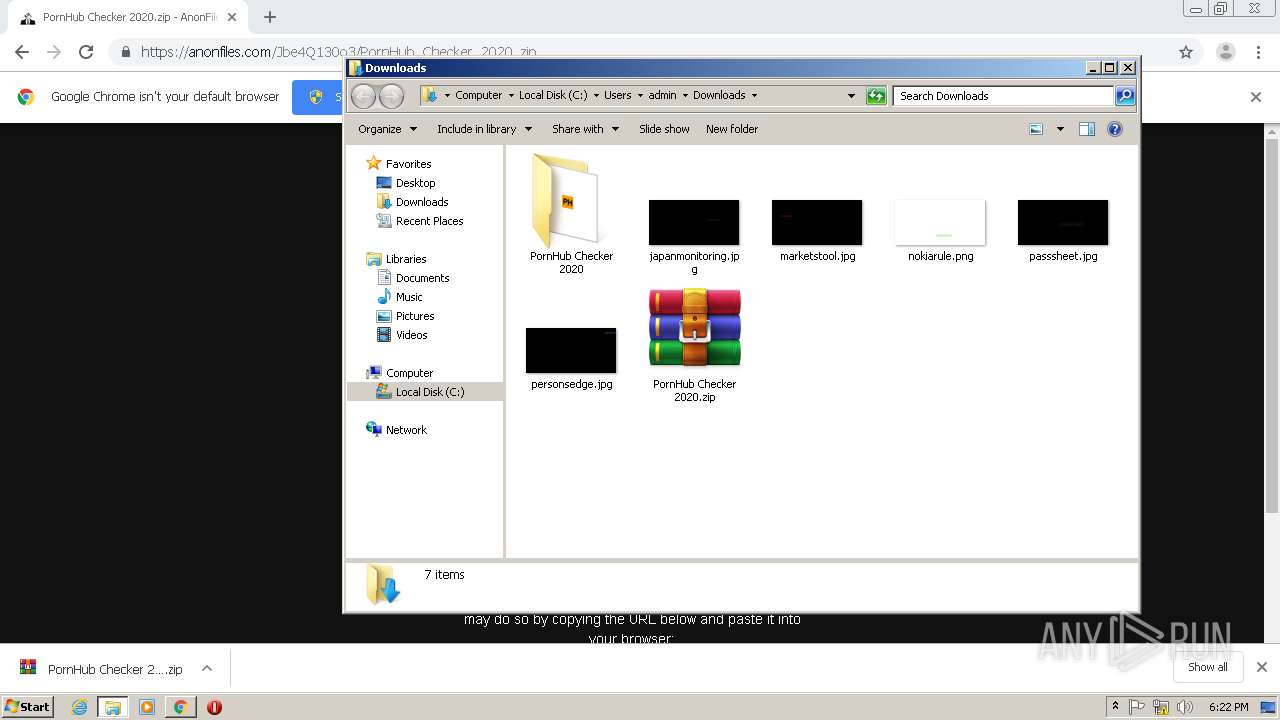
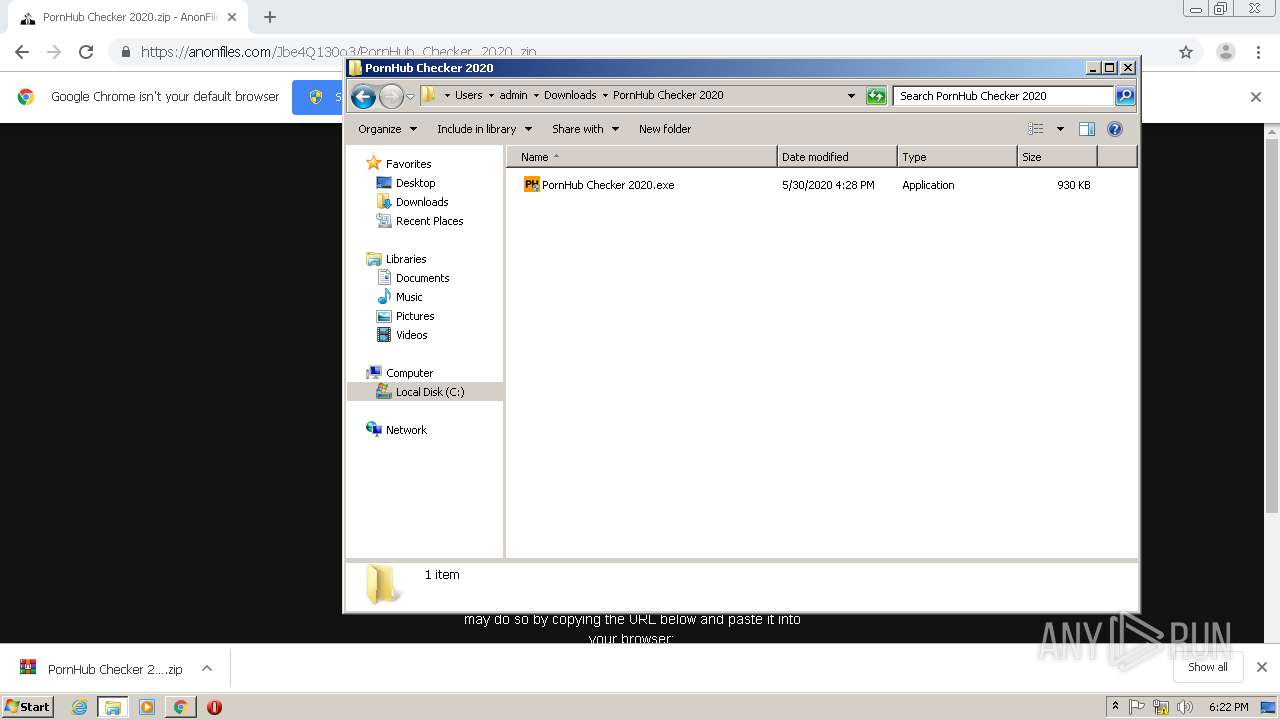
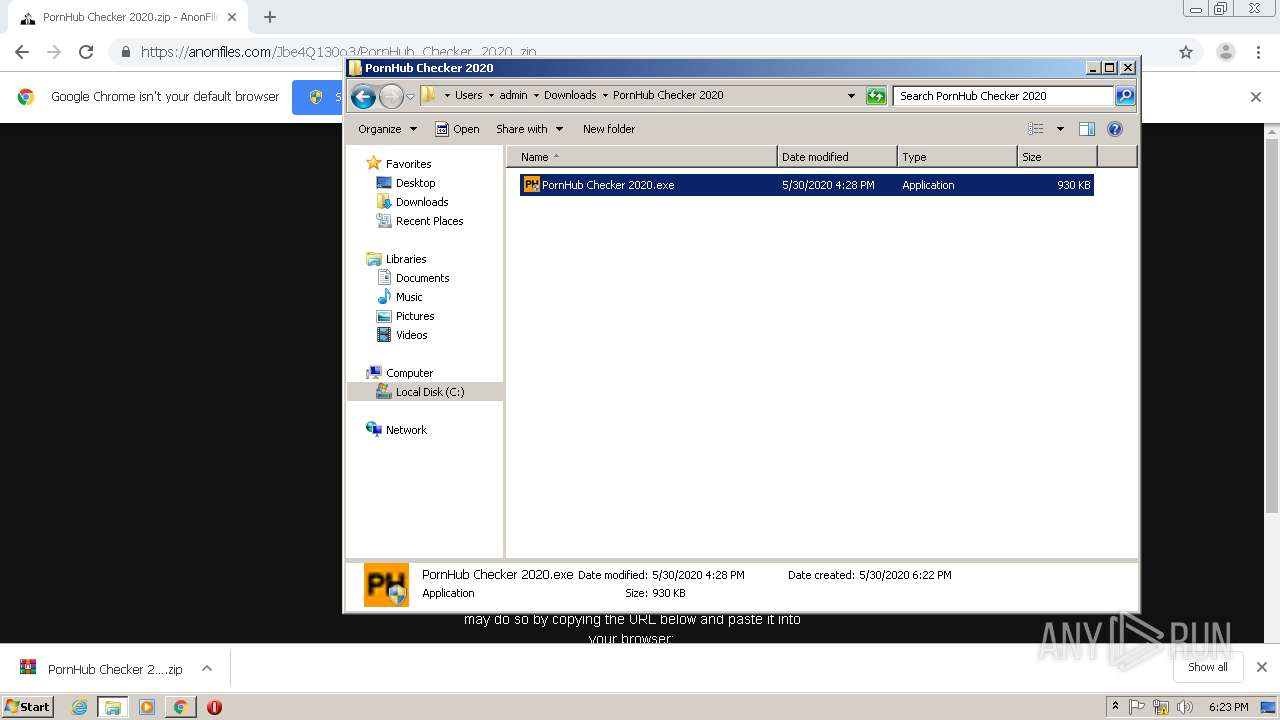
Manual execution by user
- WinRAR.exe (PID: 696)
- PornHub Checker 2020.exe (PID: 3268)
- PornHub Checker 2020.exe (PID: 2988)
Reads Internet Cache Settings
- chrome.exe (PID: 2388)
Reads settings of System Certificates
- chrome.exe (PID: 1820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
46
Malicious processes
2
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Users\admin\AppData\Local\Temp\server.exe" | C:\Users\admin\AppData\Local\Temp\server.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Exit code: 1 Version: 2.0.50727.5420 built by: Win7SP1 Modules
| |||||||||||||||
| 696 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\PornHub Checker 2020.zip" "C:\Users\admin\Downloads\PornHub Checker 2020\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,5358114119550674529,15313874335472119100,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18069997364070669633 --mojo-platform-channel-handle=3972 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,5358114119550674529,15313874335472119100,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11410212087082296689 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1116 | "C:\Users\admin\AppData\Local\Temp\server.exe" | C:\Users\admin\AppData\Local\Temp\server.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Exit code: 1 Version: 2.0.50727.5420 built by: Win7SP1 Modules
| |||||||||||||||
| 1196 | "C:\\\\Windows\\\\Microsoft.NET\\\\Framework\\\\v2.0.50727\\\\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\MSBuild.exe | PornHub Checker 2020.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Exit code: 0 Version: 2.0.50727.5420 built by: Win7SP1 Modules
| |||||||||||||||
| 1504 | "C:\\\\Windows\\\\Microsoft.NET\\\\Framework\\\\v2.0.50727\\\\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\MSBuild.exe | PornHub Checker 2020.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Exit code: 0 Version: 2.0.50727.5420 built by: Win7SP1 Modules
| |||||||||||||||
| 1744 | "C:\Users\admin\AppData\Local\Temp\server.exe" | C:\Users\admin\AppData\Local\Temp\server.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Exit code: 1 Version: 2.0.50727.5420 built by: Win7SP1 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,5358114119550674529,15313874335472119100,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6836641004390397765 --mojo-platform-channel-handle=1668 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1864 | "C:\Users\admin\AppData\Local\Temp\server.exe" | C:\Users\admin\AppData\Local\Temp\server.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Exit code: 1 Version: 2.0.50727.5420 built by: Win7SP1 Modules
| |||||||||||||||
Total events
3 302
Read events
3 166
Write events
131
Delete events
5
Modification events
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2388-13235332934361875 |
Value: 259 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
8
Suspicious files
42
Text files
221
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED29646-954.pma | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF20a1c2.TMP | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF20a1c2.TMP | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1beecd60-050b-4f08-9b6e-242f35f84a99.tmp | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF20a3e5.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
35
DNS requests
26
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1820 | chrome.exe | GET | 200 | 173.194.5.185:80 | http://r3---sn-aigl6n7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.217.117.55&mm=28&mn=sn-aigl6n7z&ms=nvh&mt=1590858958&mv=u&mvi=2&pl=25&shardbypass=yes | US | crx | 816 Kb | whitelisted |
1820 | chrome.exe | GET | 200 | 173.194.183.73:80 | http://r4---sn-aigl6ned.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.217.117.55&mm=28&mn=sn-aigl6ned&ms=nvh&mt=1590858958&mv=u&mvi=3&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
1820 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
1820 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1820 | chrome.exe | 216.58.212.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1820 | chrome.exe | 104.31.92.18:443 | anonfiles.com | Cloudflare Inc | US | shared |
1820 | chrome.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
— | — | 216.58.212.164:443 | www.google.com | Google Inc. | US | whitelisted |
1820 | chrome.exe | 104.16.108.36:443 | providentsopport.site | Cloudflare Inc | US | unknown |
1820 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1820 | chrome.exe | 13.249.102.3:443 | appearedsoci.fun | — | US | unknown |
1820 | chrome.exe | 13.224.196.32:443 | traintincre.fun | — | US | unknown |
1820 | chrome.exe | 54.144.3.29:443 | baconaces.pro | Amazon.com, Inc. | US | suspicious |
1820 | chrome.exe | 178.62.225.201:443 | cloudstream.online | Digital Ocean, Inc. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
baconaces.pro |
| shared |
www.google.com |
| malicious |
appearedsoci.fun |
| malicious |
traintincre.fun |
| suspicious |
providentsopport.site |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |