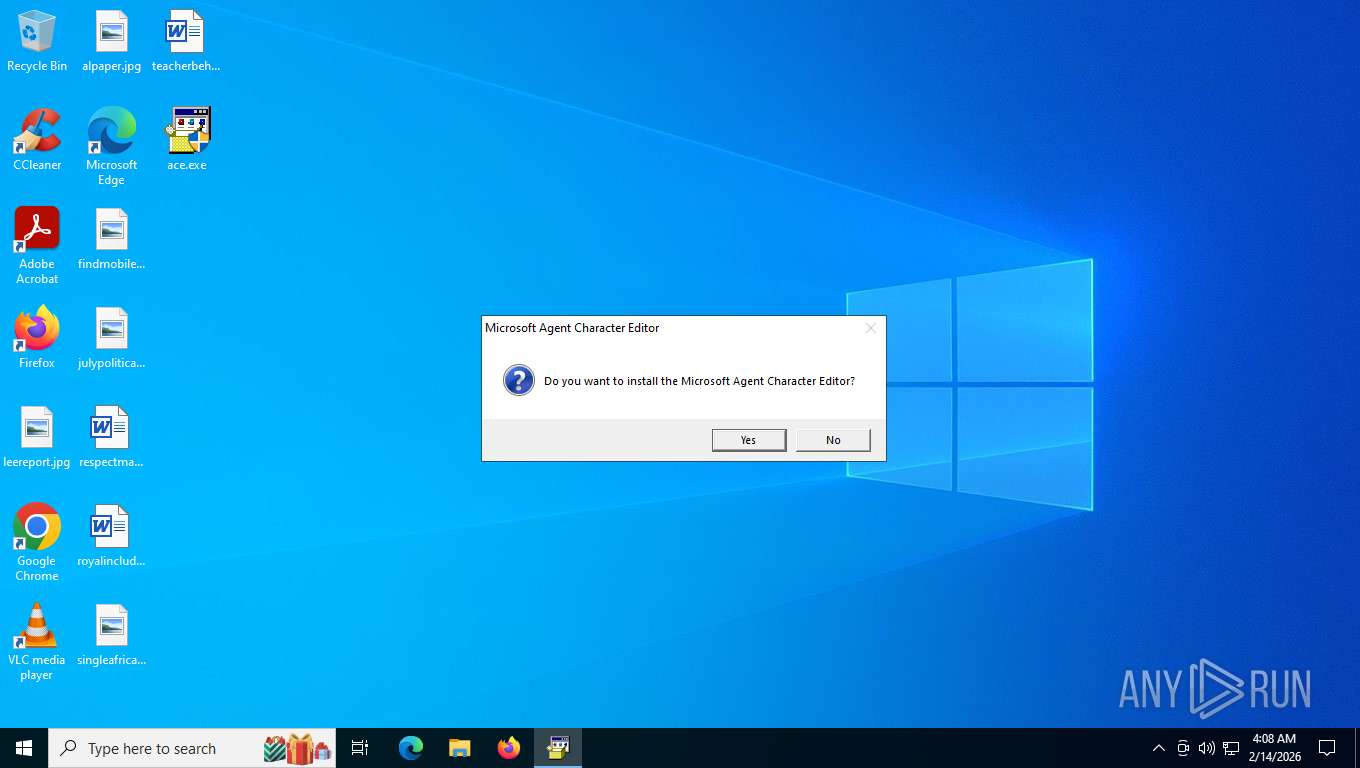
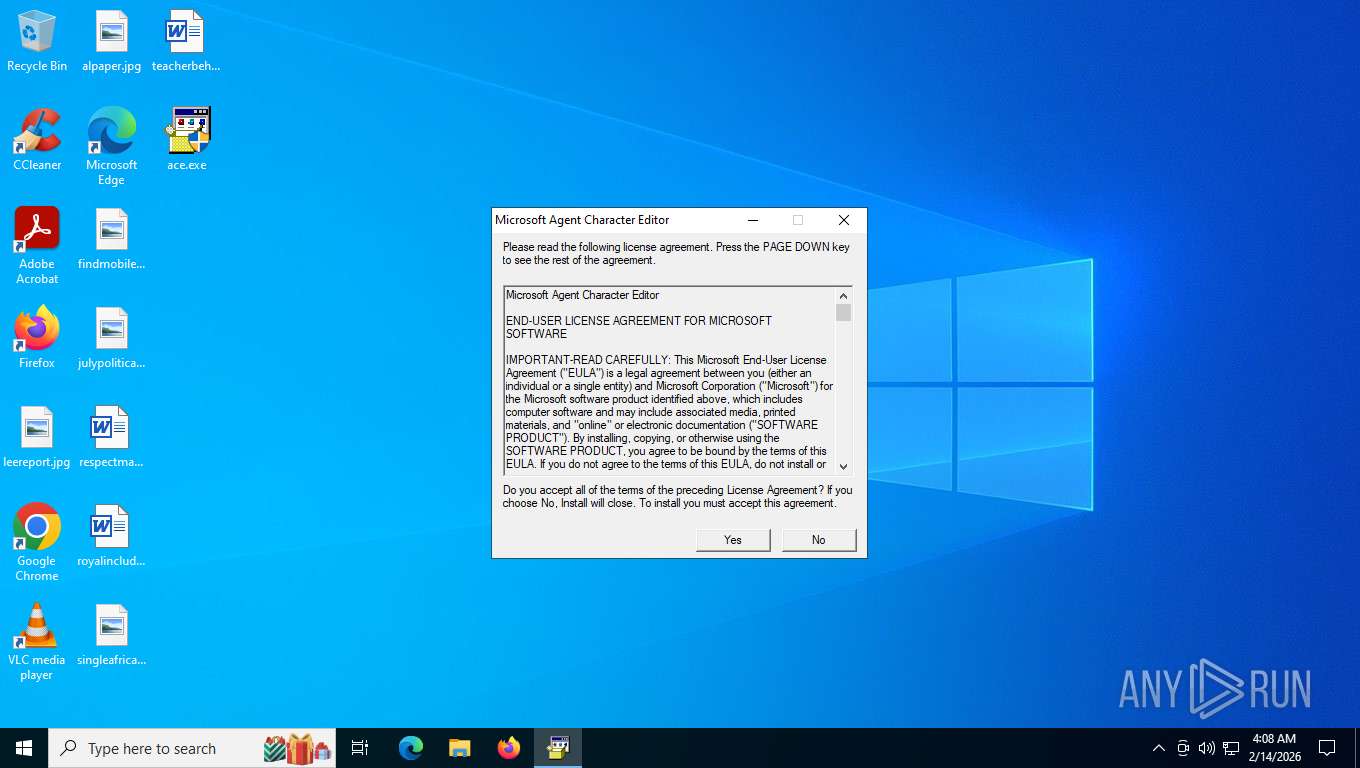
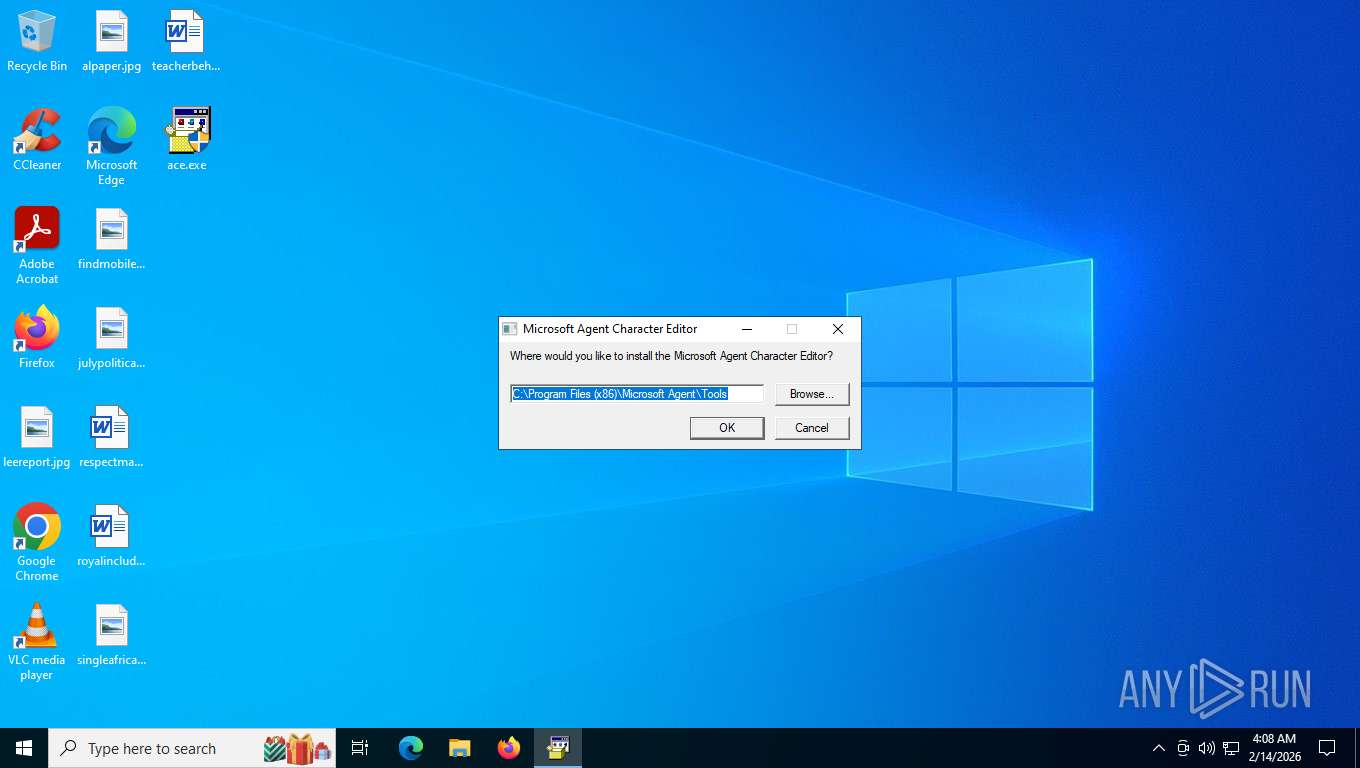
| File name: | ace.exe |
| Full analysis: | https://app.any.run/tasks/2e48c4b4-0b2c-421f-b6f0-1fa960da42b3 |
| Verdict: | Malicious activity |
| Analysis date: | February 14, 2026, 09:08:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, MS CAB-Installer self-extracting archive, 3 sections |
| MD5: | 3DFA2B4FB5C832990E27492B678690A3 |
| SHA1: | 95EB27730CD61BBB06AA39A24CDC56D85B7694CA |
| SHA256: | 341759E96378801C9CA273F5FE8A0DEFC6F622948C3A1CA15760F19895FB9BE7 |
| SSDEEP: | 49152:BmdFrMM9AouMwFePn7KwnozhI3AJAhtBCjEJGSaKw9IA76f1EUi+uk4vjJpOWnWi:IHM0vubqCVm5tBCjEJGSJ2M+TpOWWcbN |
MALICIOUS
Executing a file with an untrusted certificate
- ace.exe (PID: 6156)
- ace.exe (PID: 9204)
SUSPICIOUS
Starts a Microsoft application from unusual location
- ace.exe (PID: 9204)
- SPCHAPI.EXE (PID: 6644)
- SPCHAPI.EXE (PID: 7464)
Process drops legitimate windows executable
- ace.exe (PID: 6156)
- SPCHAPI.EXE (PID: 6644)
- SPCHAPI.EXE (PID: 7464)
Executable content was dropped or overwritten
- ace.exe (PID: 6156)
- SPCHAPI.EXE (PID: 6644)
- SPCHAPI.EXE (PID: 7464)
The process creates files with name similar to system file names
- SPCHAPI.EXE (PID: 6644)
- SPCHAPI.EXE (PID: 7464)
Creates/Modifies COM task schedule object
- SPCHAPI.EXE (PID: 6644)
- SPCHAPI.EXE (PID: 7464)
INFO
The sample compiled with english language support
- ace.exe (PID: 6156)
- SPCHAPI.EXE (PID: 6644)
- SPCHAPI.EXE (PID: 7464)
Checks supported languages
- ace.exe (PID: 6156)
- ACEINST.EXE (PID: 8784)
- SPCHAPI.EXE (PID: 6644)
- SPCHAPI.EXE (PID: 7464)
Reads the computer name
- ace.exe (PID: 6156)
- SPCHAPI.EXE (PID: 6644)
- SPCHAPI.EXE (PID: 7464)
Create files in a temporary directory
- ace.exe (PID: 6156)
- SPCHAPI.EXE (PID: 6644)
- SPCHAPI.EXE (PID: 7464)
Creates files in the program directory
- ace.exe (PID: 6156)
Checks proxy server information
- slui.exe (PID: 2752)
Creates files or folders in the user directory
- grpconv.exe (PID: 8156)
Creates a software uninstall entry
- ace.exe (PID: 6156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (81.3) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.3) |
| .exe | | | Win64 Executable (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (1.2) |
| .exe | | | Win16/32 Executable Delphi generic (0.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1997:07:15 11:48:12+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 36864 |
| InitializedDataSize: | 1024000 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2723 |
| OSVersion: | 5 |
| ImageVersion: | 5 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.71.1015.0 |
| ProductVersionNumber: | 4.71.1015.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 4.71.1015.0 |
| InternalName: | Wextract |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1995 |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Microsoft(R) Windows NT(R) Operating System |
| ProductVersion: | 4.71.1015.0 |
Total processes
152
Monitored processes
9
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2752 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4624 | grpconv.exe -o | C:\Windows\SysWOW64\grpconv.exe | — | SPCHAPI.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5536 | grpconv.exe -o | C:\Windows\SysWOW64\grpconv.exe | — | ace.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6156 | "C:\Users\admin\Desktop\ace.exe" | C:\Users\admin\Desktop\ace.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.71.1015.0 Modules
| |||||||||||||||
| 6644 | spchapi.exe /R:N | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\SPCHAPI.EXE | ACEINST.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.71.1015.0 Modules
| |||||||||||||||
| 7464 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\spchapi.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\SPCHAPI.EXE | ace.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.71.1015.0 Modules
| |||||||||||||||
| 8156 | grpconv.exe -o | C:\Windows\SysWOW64\grpconv.exe | — | SPCHAPI.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8784 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\aceinst.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ACEINST.EXE | — | ace.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 9204 | "C:\Users\admin\Desktop\ace.exe" | C:\Users\admin\Desktop\ace.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 3221226540 Version: 4.71.1015.0 Modules
| |||||||||||||||
Total events
3 918
Read events
3 811
Write events
107
Delete events
0
Modification events
| (PID) Process: | (6644) SPCHAPI.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{D67C0280-C743-11cd-80E5-00AA003E4B50}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (6644) SPCHAPI.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{554667BB-7213-11cf-B210-00AA00A215ED}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (6644) SPCHAPI.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{CB96B400-C743-11cd-80E5-00AA003E4B50}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (6644) SPCHAPI.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{E02D16C0-C743-11cd-80E5-00AA003E4B50}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (6644) SPCHAPI.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{D24FE500-C743-11cd-80E5-00AA003E4B50}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (6644) SPCHAPI.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{D4023720-E4B9-11cf-8D56-00A0C9034A7E}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (6644) SPCHAPI.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{D4123720-E4B9-11cf-8D56-00A0C9034A7E}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (6644) SPCHAPI.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{D4523720-E4B9-11cf-8D56-00A0C9034A7E}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (6644) SPCHAPI.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{D4623720-E4B9-11cf-8D56-00A0C9034A7E}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (6644) SPCHAPI.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{B9F11A90-90E3-11d0-8D77-00A0C9034A7E}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
Executable files
103
Suspicious files
14
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6156 | ace.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ACEINST.INF | binary | |
MD5:3FBD4A2ADDB1AE647AED180BCDEEB25D | SHA256:2D2568BFCBAADB2847DF9EADCF57869CA66BC8EF414A3168DC10CB13524E8899 | |||
| 6156 | ace.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ADVPACK.DLL | executable | |
MD5:81E5C8596A7E4E98117F5C5143293020 | SHA256:7D126ED85DF9705EC4F38BD52A73B621CF64DD87A3E8F9429A569F3F82F74004 | |||
| 6156 | ace.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ACE.HLP | binary | |
MD5:FBB2893CE7927D609040718F89AA5E20 | SHA256:837F29C488AA932AFB744765EA1D3B37CDB9270578E1DCB5A56AA4640FFD3855 | |||
| 6156 | ace.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ACE.EXE | executable | |
MD5:4FF6F3B71AC5C09973415B0C7B22DFAE | SHA256:1F2856E79F764EB8A6DFB259CC47240E929DB412E10BA512790D69367CEF20A2 | |||
| 6156 | ace.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ACEINST.EXE | executable | |
MD5:55CB95174E0751849899AA36299E443B | SHA256:518E99B1134023C26920EDC186CDD5639A6865CA2427A8F79D9620461FCC483A | |||
| 6156 | ace.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\W95INF16.DLL | executable | |
MD5:7210D5407A2D2F52E851604666403024 | SHA256:337D2FB5252FC532B7BF67476B5979D158CA2AC589E49C6810E2E1AFEBE296AF | |||
| 6156 | ace.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ACE.CNT | text | |
MD5:D0EA4363026B11EDC0751942E41D41AF | SHA256:F901798ECA7D5764887E391C0198C4FD0A72AEA7F1B4C5AD3FEDE1D7B89B3088 | |||
| 6156 | ace.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\W95INF32.DLL | executable | |
MD5:4BE7661C89897EAA9B28DAE290C3922F | SHA256:E5E9F7C8DBD47134815E155ED1C7B261805EDA6FDDEA6FA4EA78E0E4FB4F7FB5 | |||
| 6156 | ace.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\SPCHAPI.EXE | executable | |
MD5:E2B0921F488B7CA977A65B5B0B3794DF | SHA256:BBF568FEEC587287131BC88BFAC813613588CBA4F544839EBFDE5AE1344DE6CC | |||
| 6644 | SPCHAPI.EXE | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\VTXTAUTO.TLB | executable | |
MD5:283C7D582752FC0C025421FCA7B7E1D0 | SHA256:544B33CF240A425CCCC910269C68B99B411B2374571AB8AF51A490F9CC277F77 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
29
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7304 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.204.160:443 | https://th.bing.com/th?id=OCGE.9plgt00f15xs_abtesting_835b67e1-8ab1-490d-a6ab-e8840fad9bde&w=80&h=80&c=1&rs=1&p=0 | unknown | — | — | — |
8176 | RUXIMICS.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.204.160:443 | https://th.bing.com/th?id=OVP.Pp_dUBNtoGoXPjfmh-YVswHgFo&w=188&h=110&c=1&rs=1&p=0 | unknown | binary | 6.25 Kb | unknown |
— | — | GET | 200 | 2.16.204.160:443 | https://th.bing.com/th?id=OCGE.9pltx207s22g_v4_main&w=80&h=80&c=1&rs=1&p=0 | unknown | image | 16.3 Kb | unknown |
— | — | GET | 200 | 2.16.204.160:443 | https://th.bing.com/th?id=OCGE.9nq9j864v30w_v5_main&w=80&h=80&c=1&rs=1&p=0 | unknown | text | 17.4 Kb | unknown |
— | — | GET | 200 | 2.16.204.160:443 | https://th.bing.com/th?id=ODSWG.1aaabb19-3ace-419f-9d51-88be800c546e&w=132&h=154&c=1&rs=1&p=0 | unknown | image | 4.04 Kb | unknown |
— | — | GET | 200 | 2.16.204.141:443 | https://th.bing.com/th?id=ODSWG.d0c90ac9-6e04-4677-bb6b-a7c69af4de98&w=132&h=154&c=1&rs=1&p=0 | unknown | — | 6.19 Kb | — |
— | — | POST | — | 2.16.204.161:443 | https://www.bing.com/threshold/xls.aspx?t=5&dl=1&wsbc=1 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7304 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8176 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
7304 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
8176 | RUXIMICS.exe | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7304 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |